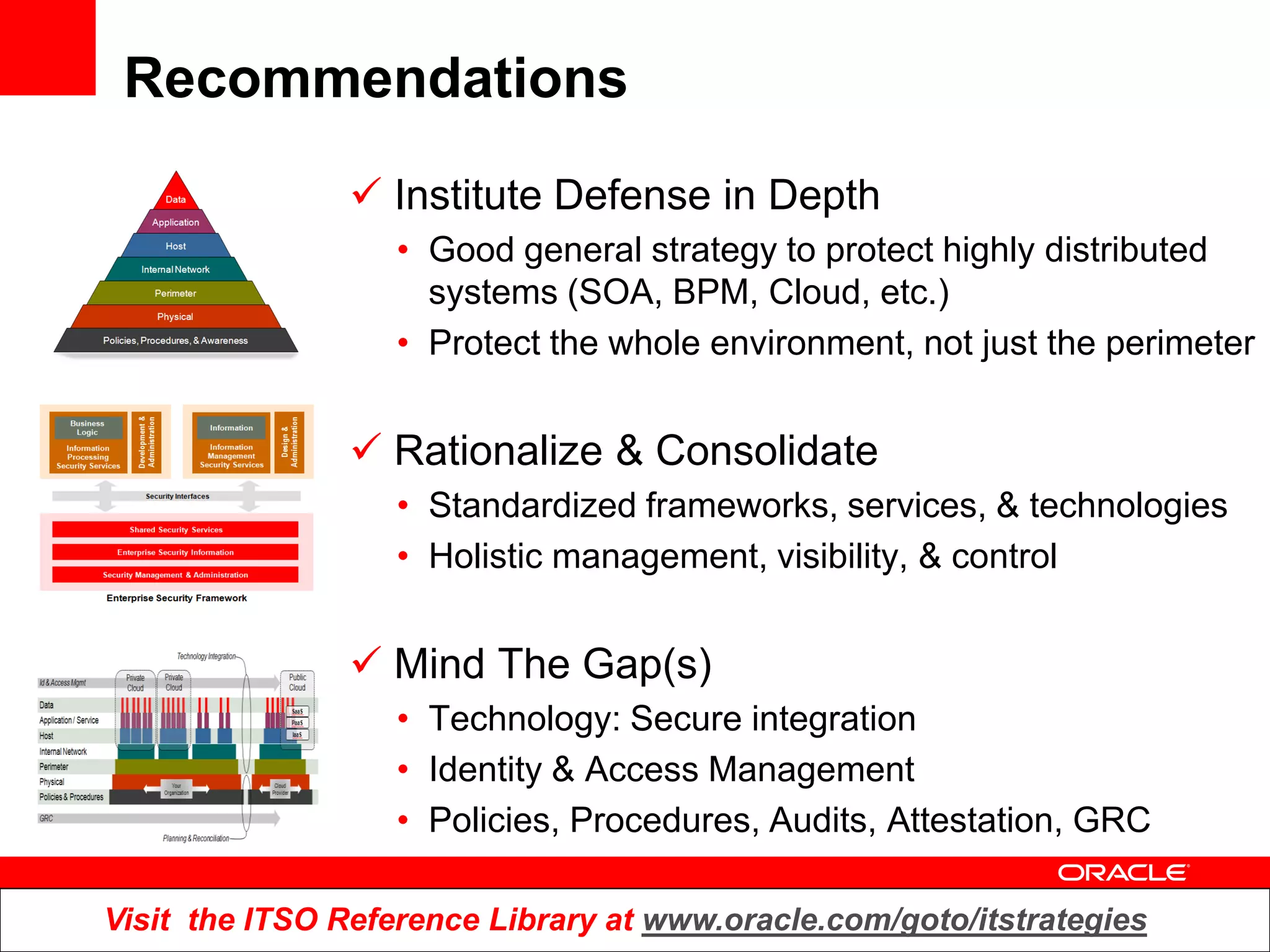
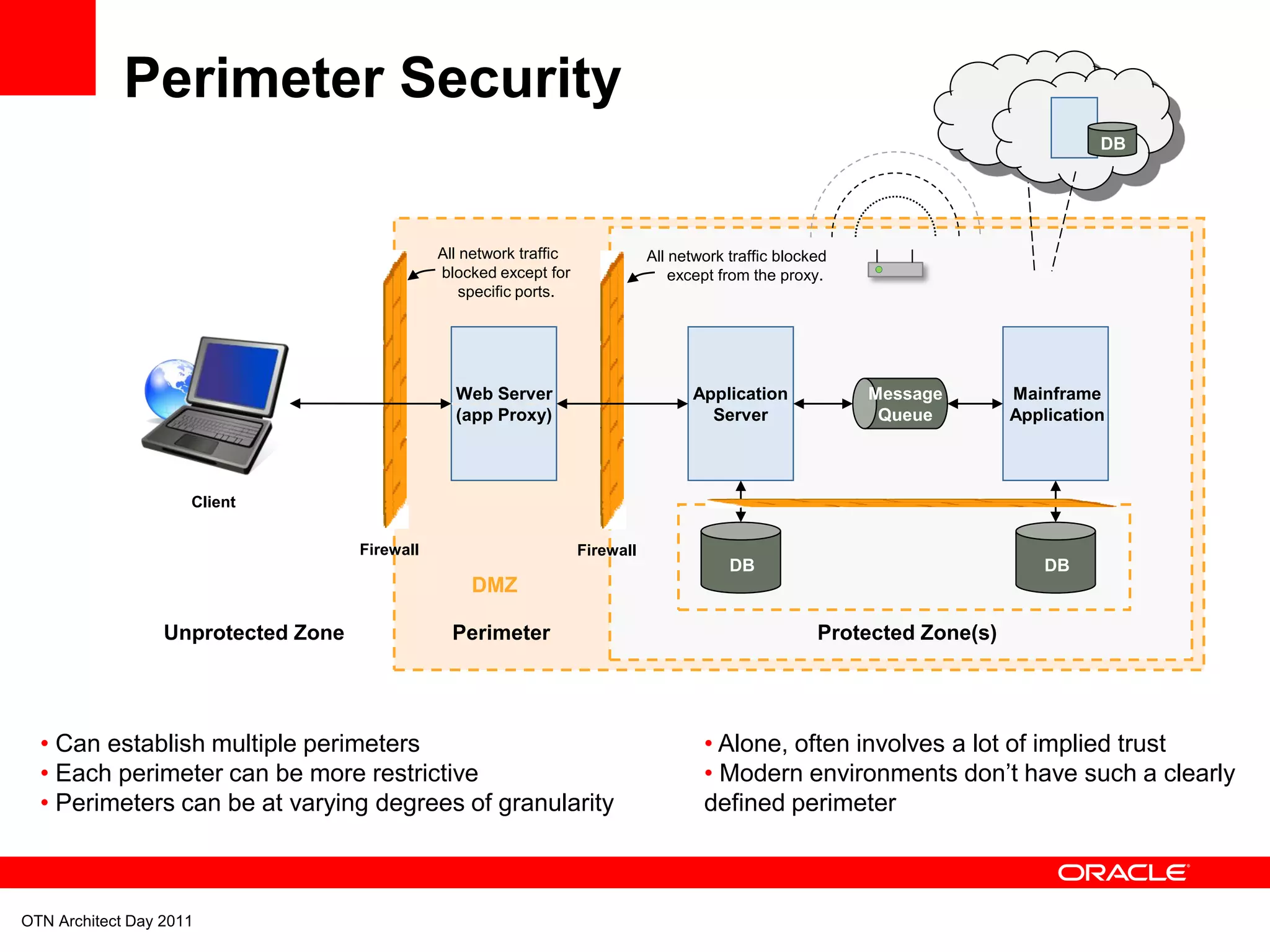
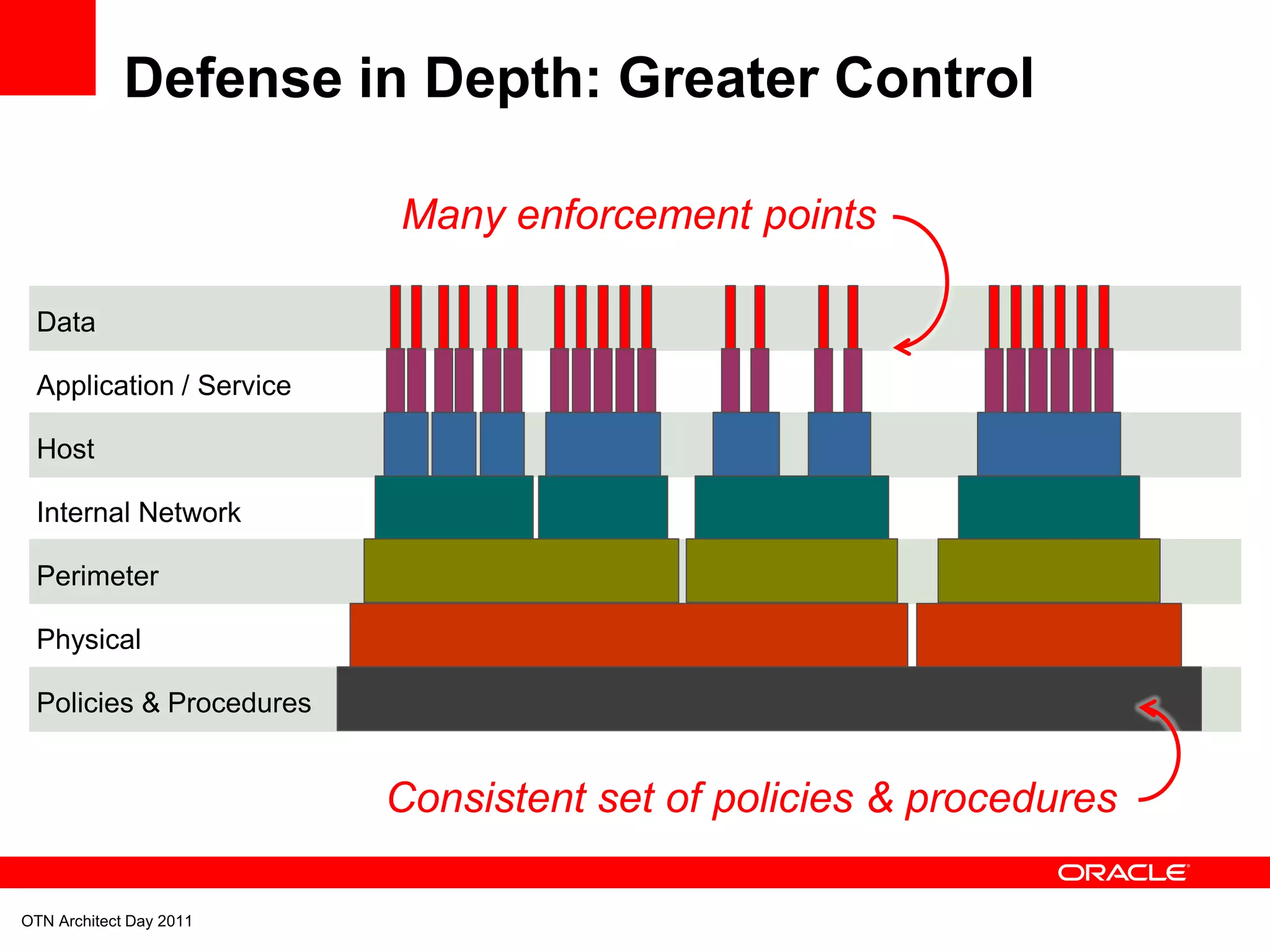
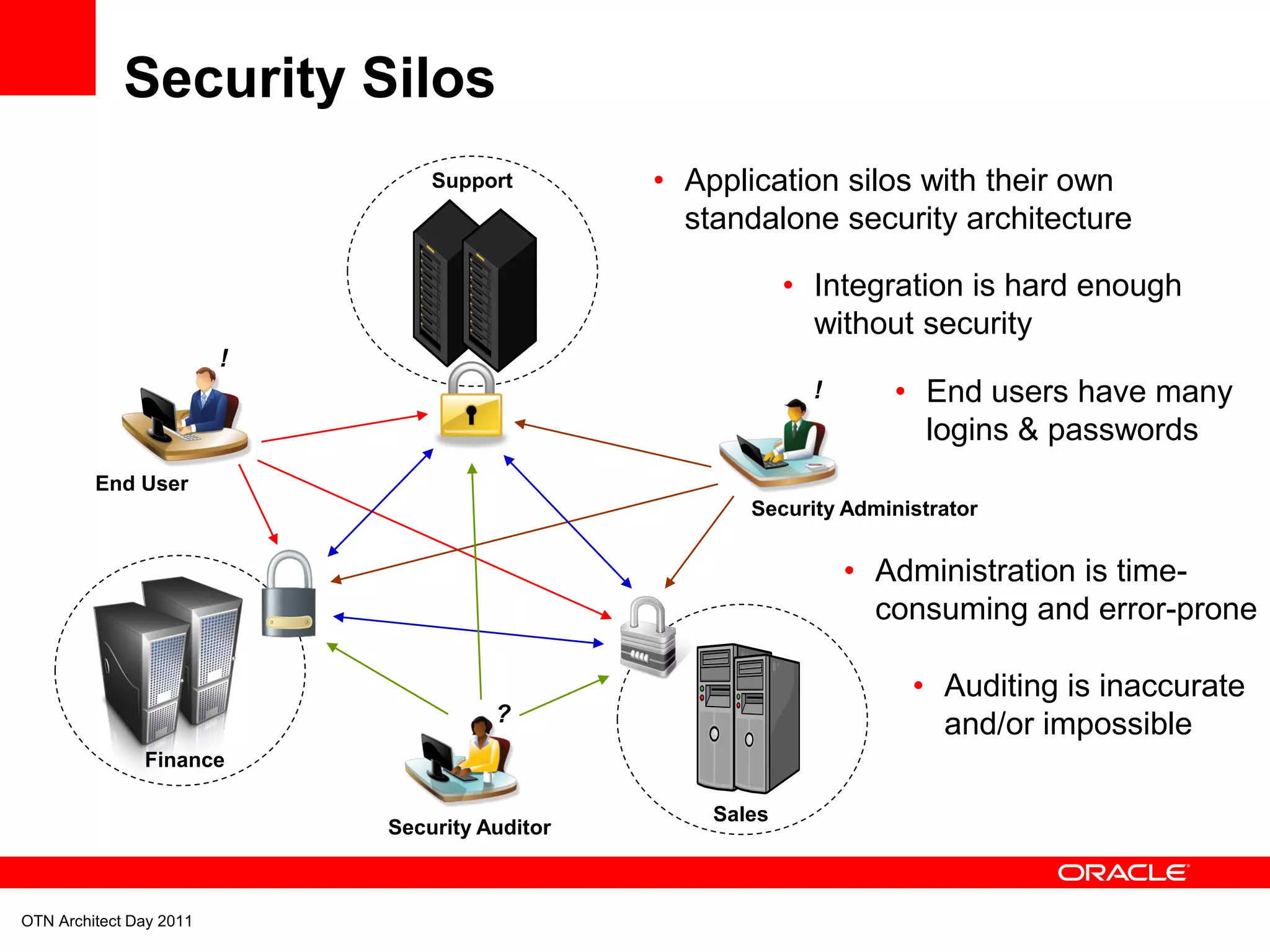
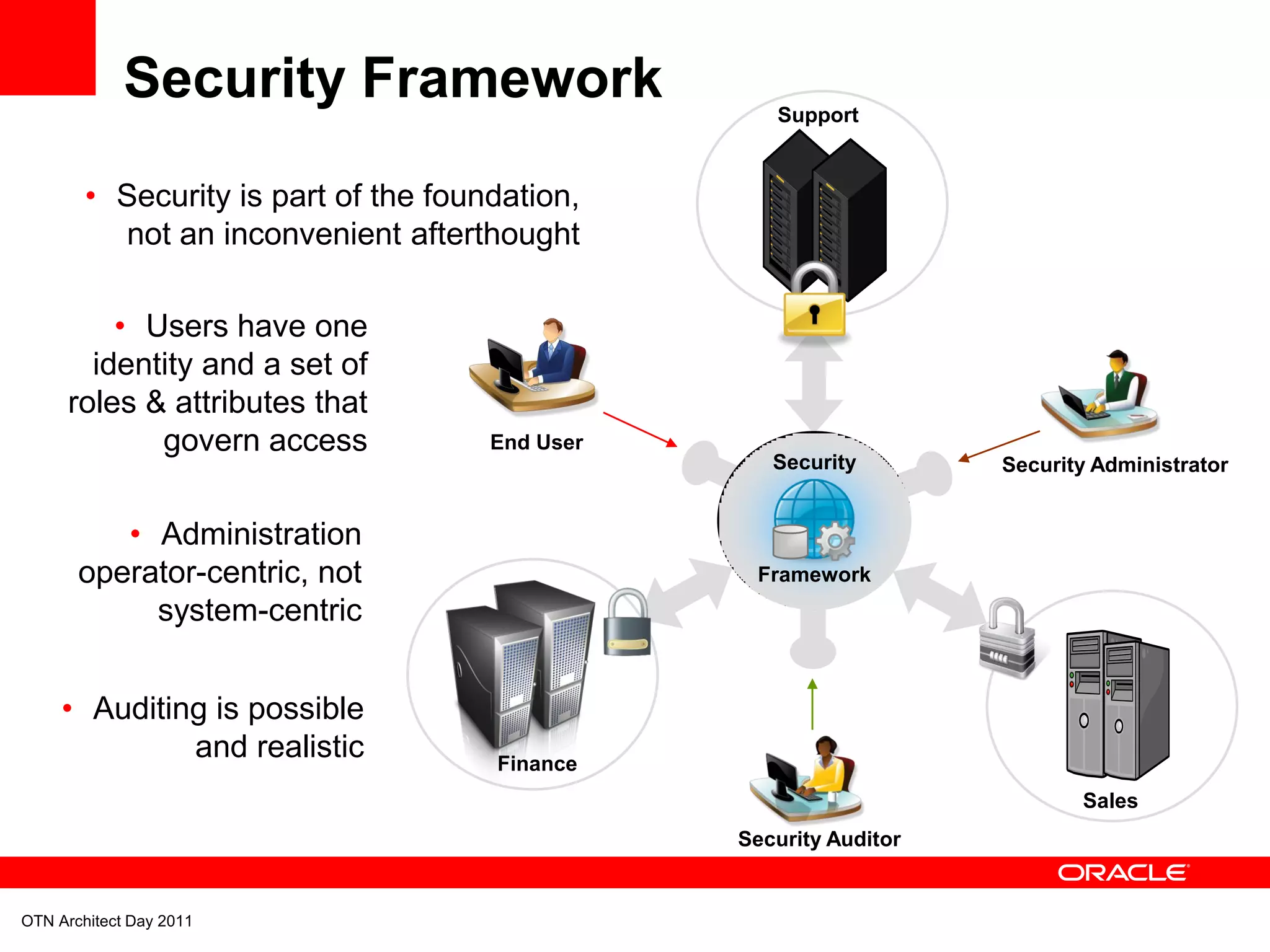
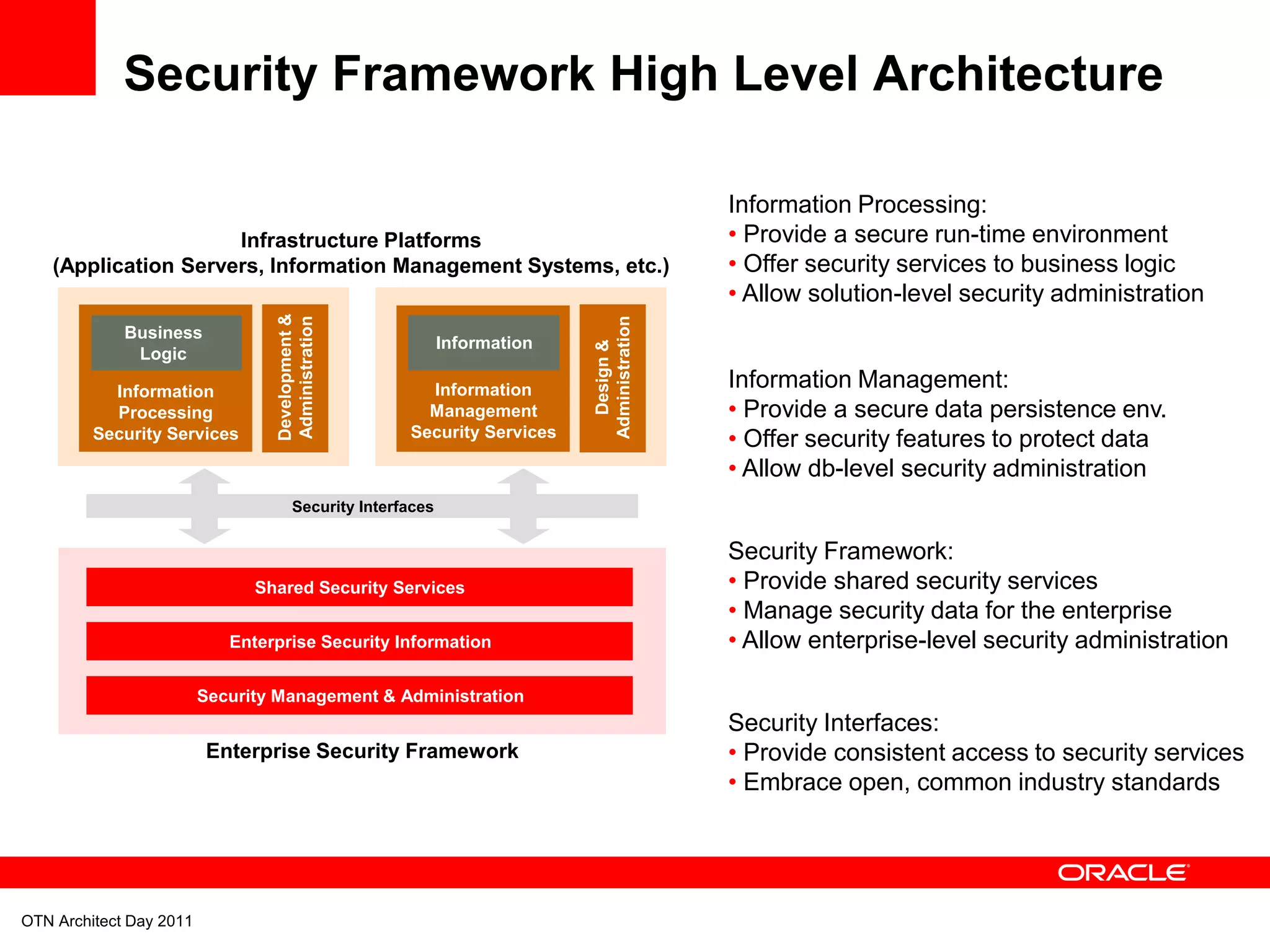
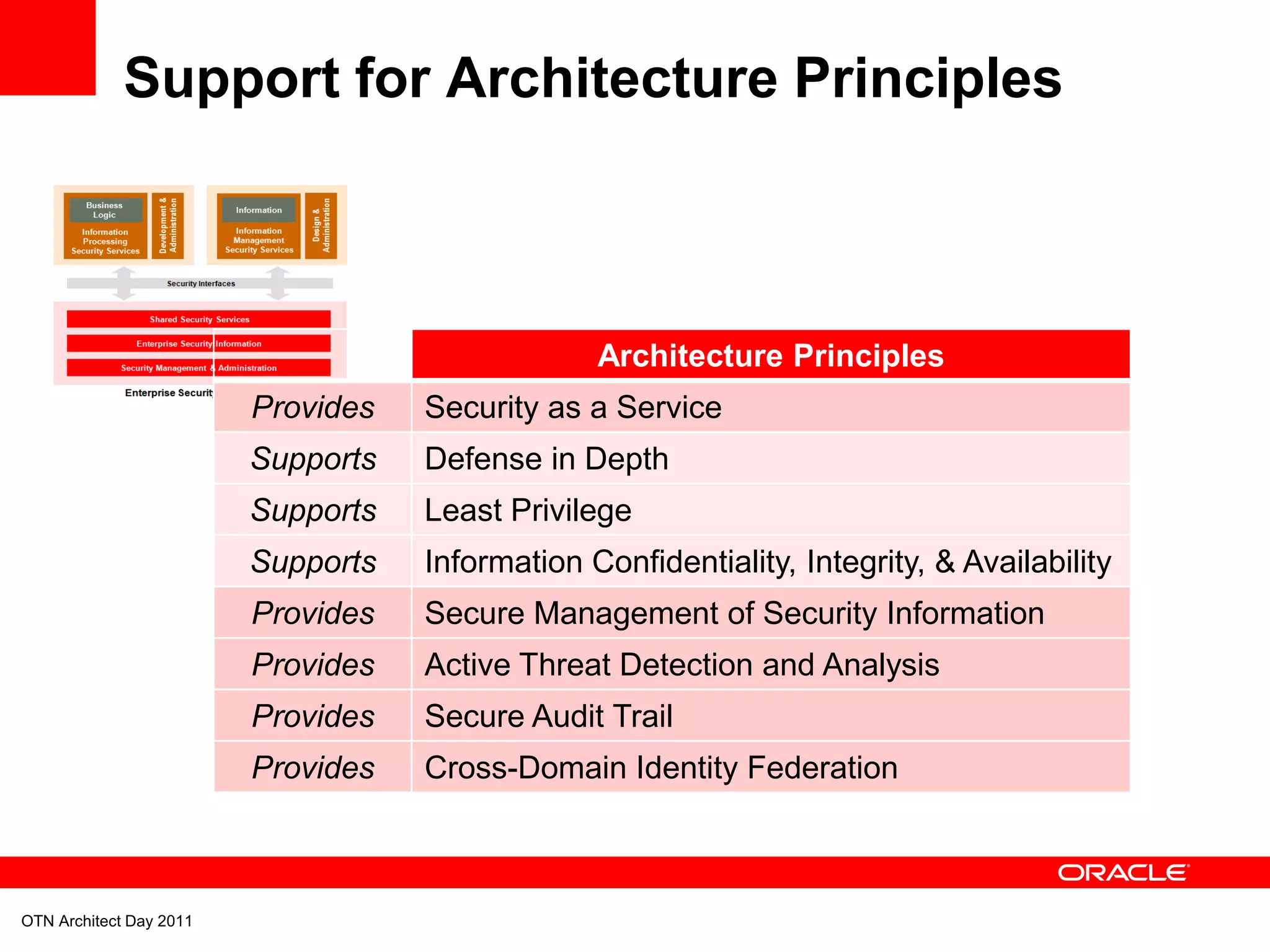
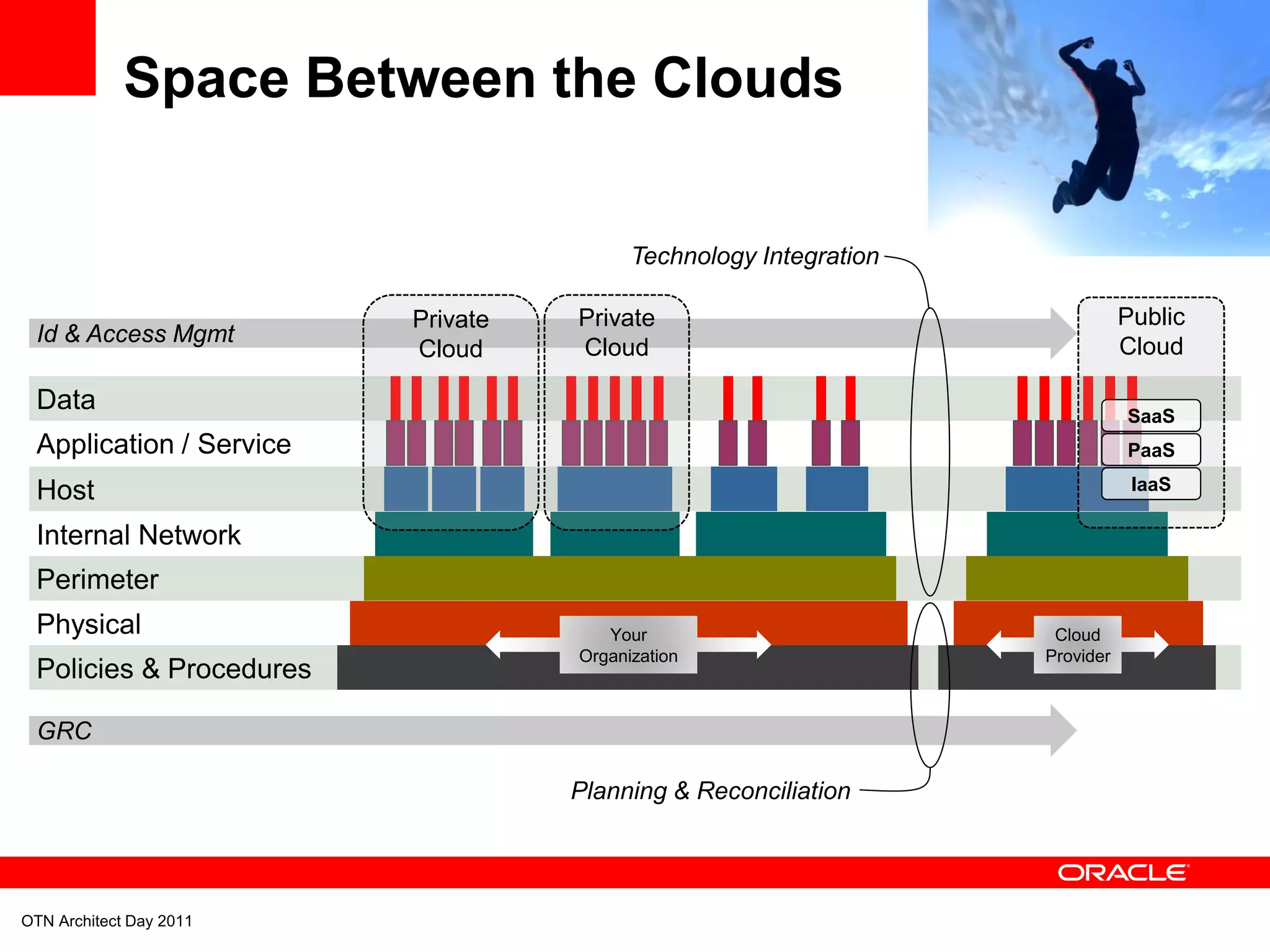
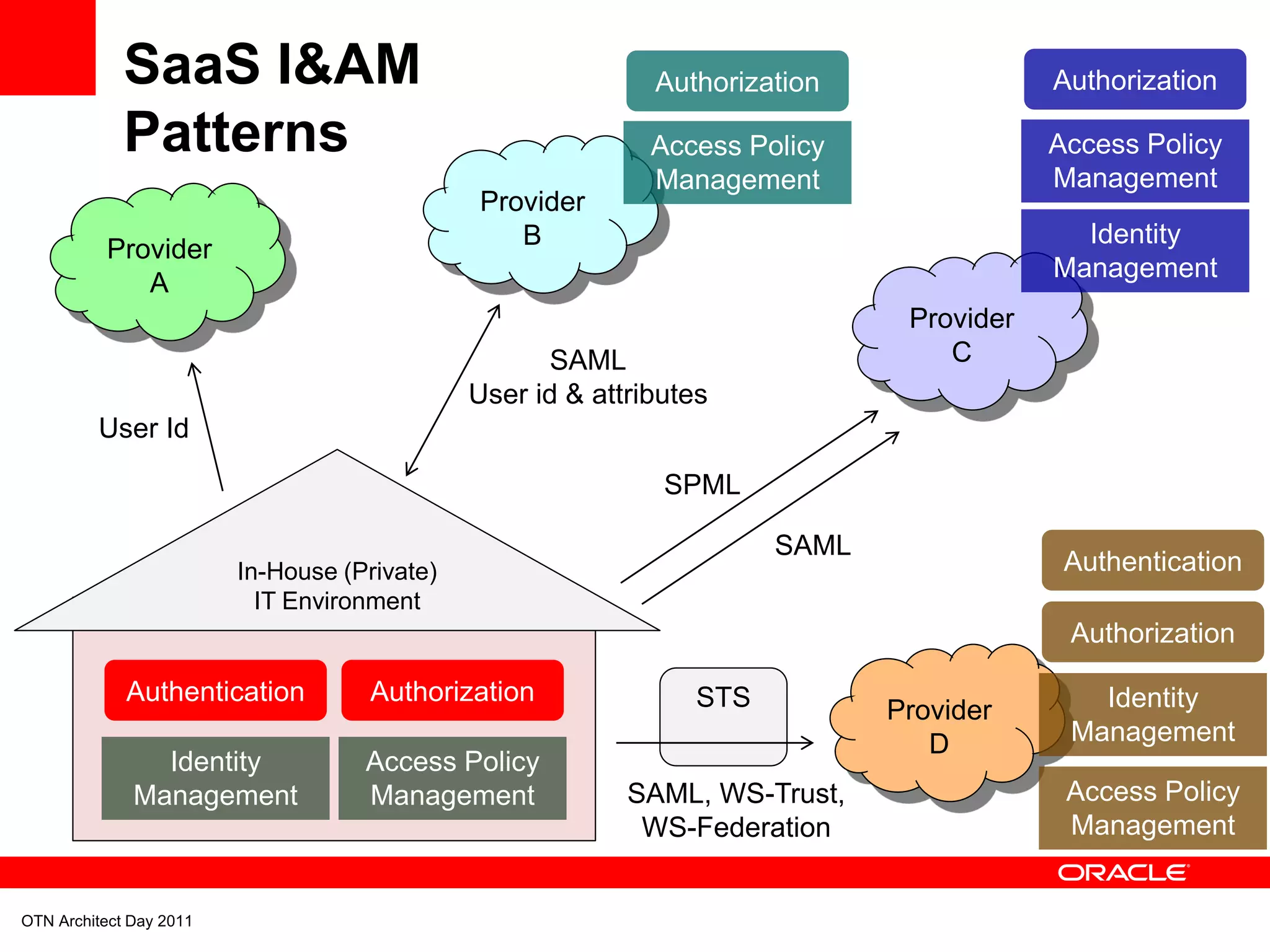
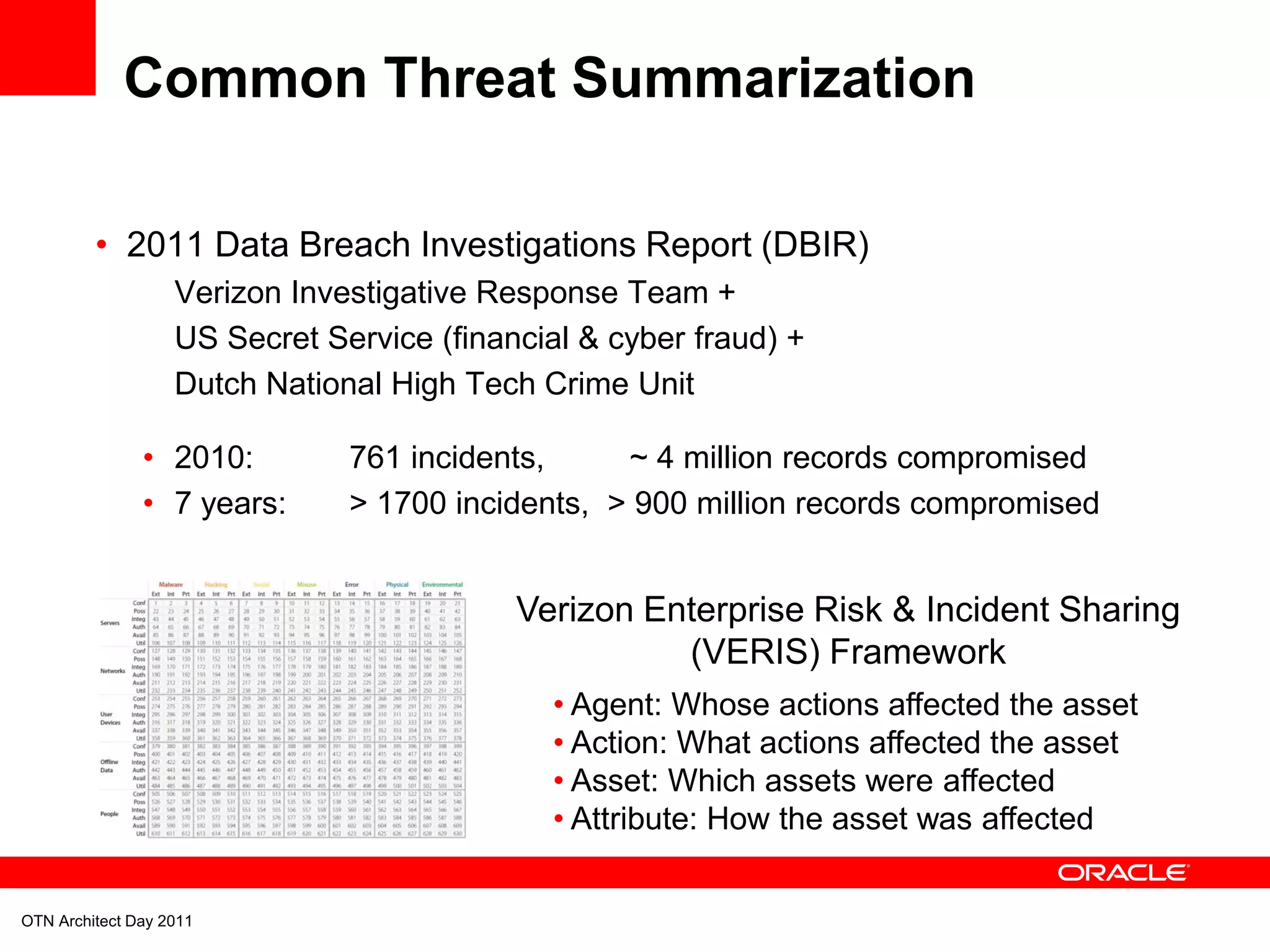
The document discusses security strategies focused on defense in depth and perimeter security for IT environments, especially in cloud computing contexts. It highlights the importance of multiple security layers, governance, and integrated security frameworks to protect against various types of attacks, including external and internal threats. Recommendations emphasize consolidating security practices, managing identities and access, and addressing potential gaps to enhance overall security resilience.
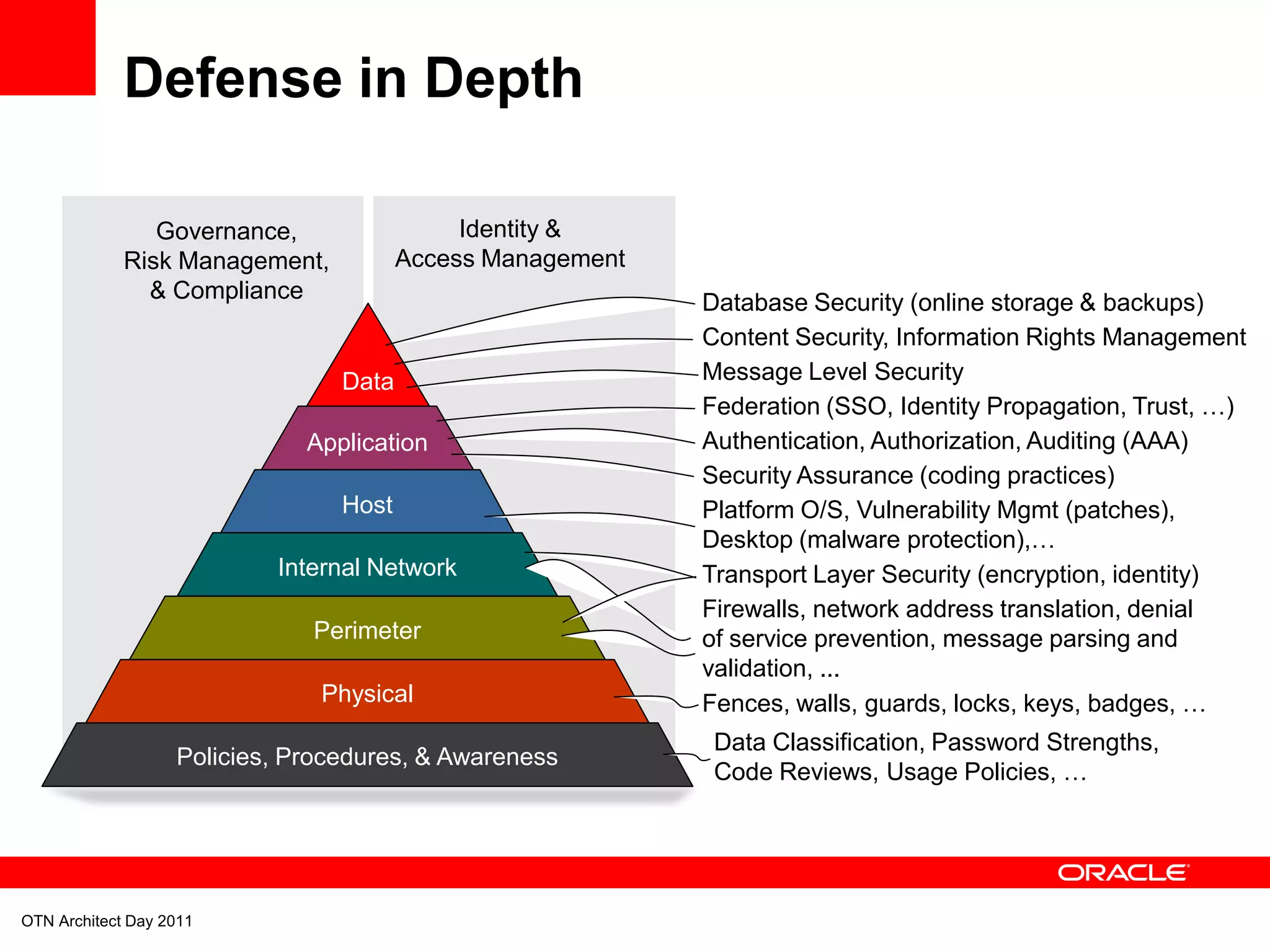
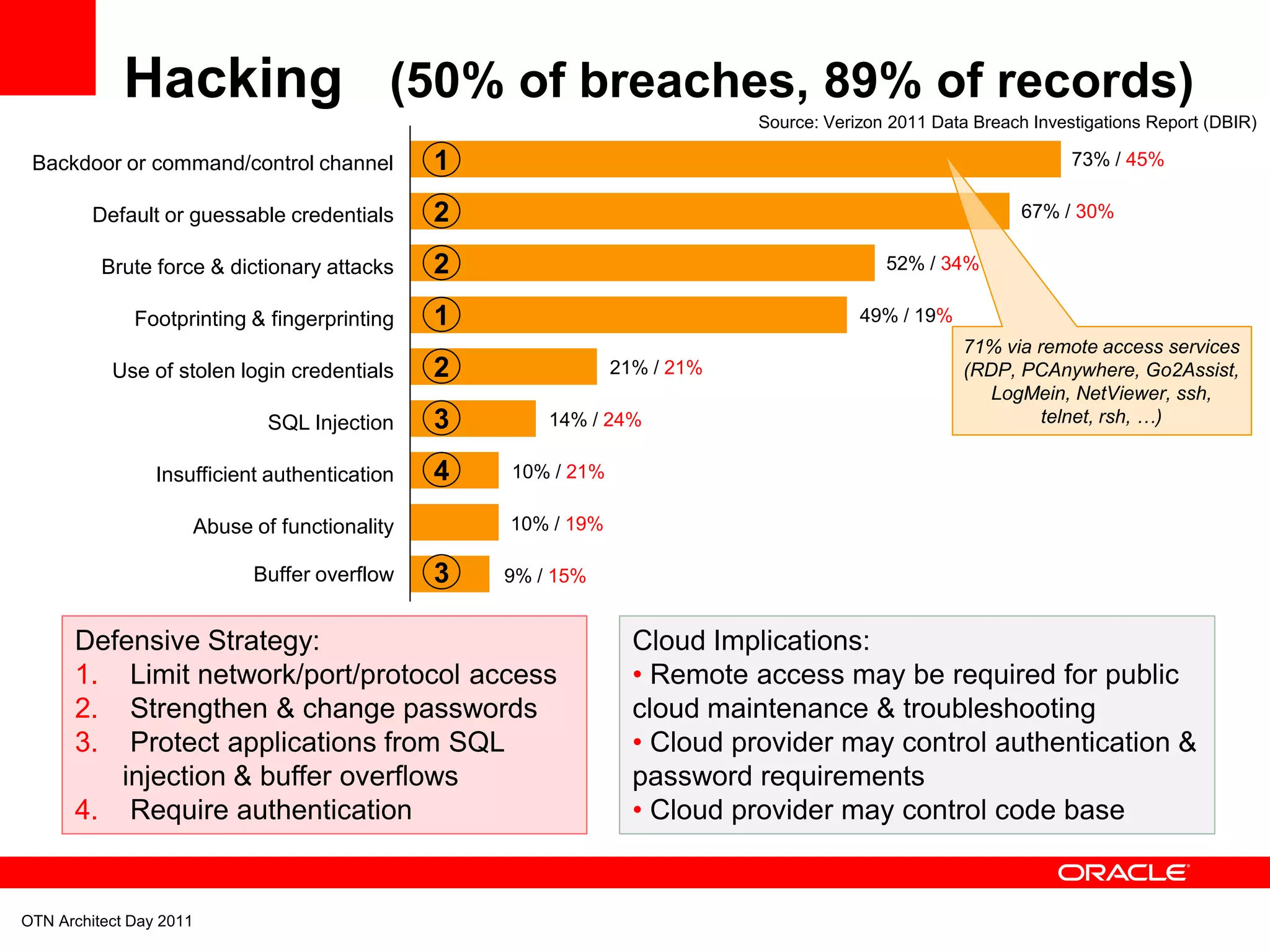
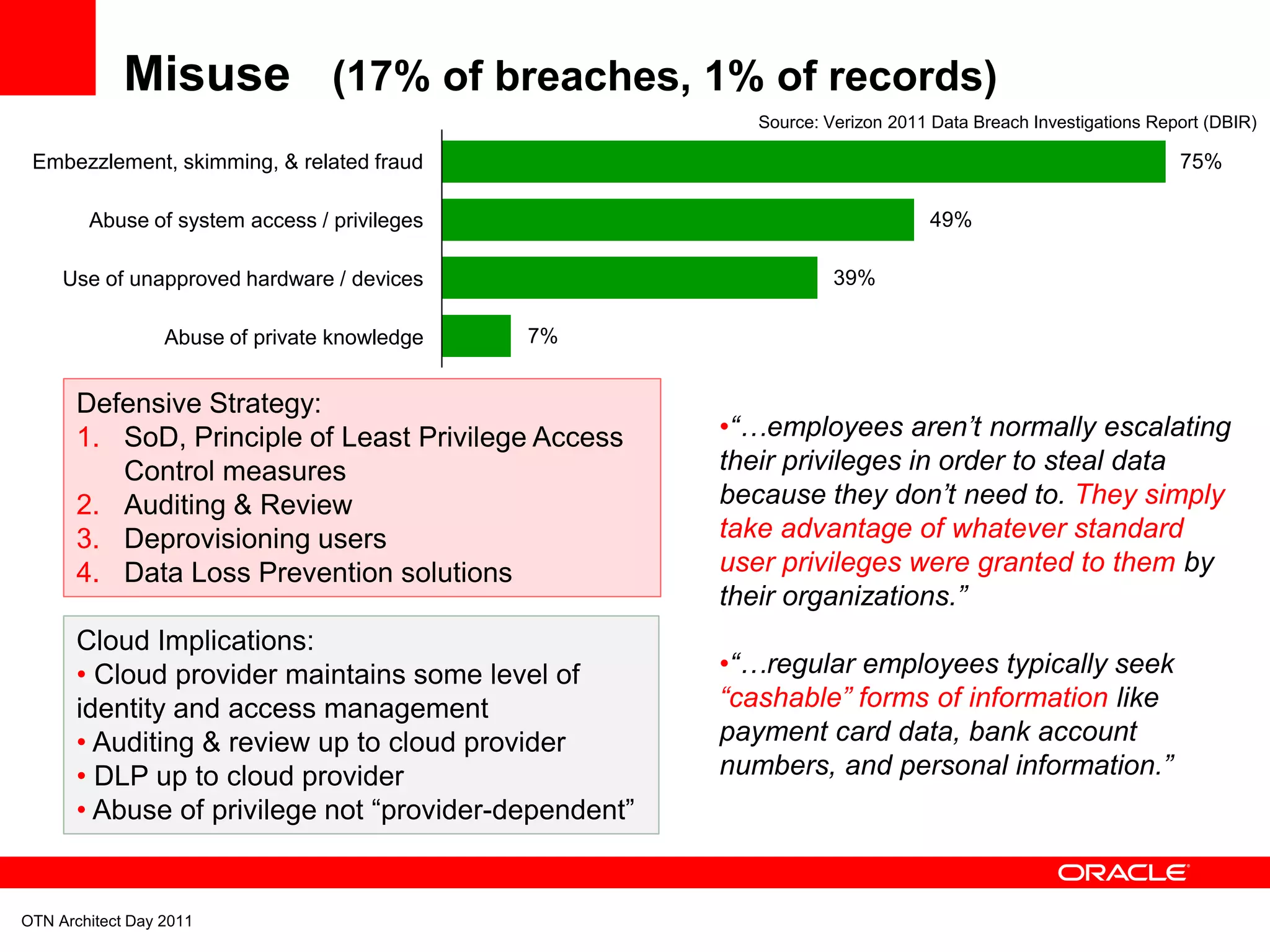
![Threat Agents - External
1. External
Agents
91% / 99%
2. Internal 16% / 1%
3. Partner <1% / <1%
External
“[External Agents] created economies of
58% Organized Criminal Groups scale by refining standardized,
40% Unaffiliated individuals automated, and highly repeatable
2% Former Employees attacks directed at smaller, vulnerable,
and largely homogenous targets.”
1% Competitors
1. Malware
Actions
49% / 79%
2. Hacking 50% / 89%
3. Misuse 17% / 1%
Source: Verizon 2011 Data Breach Investigations Report (DBIR)
OTN Architect Day 2011](https://image.slidesharecdn.com/archday-phoenix-2011-chappelle-111213153431-phpapp01/75/Rationalization-and-Defense-in-Depth-Two-Steps-Closer-to-the-Clouds-15-2048.jpg)