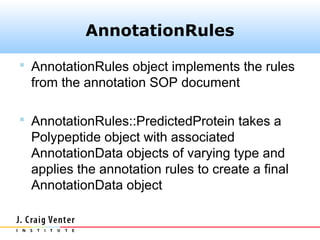
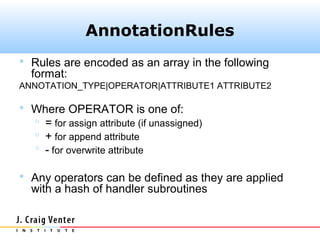
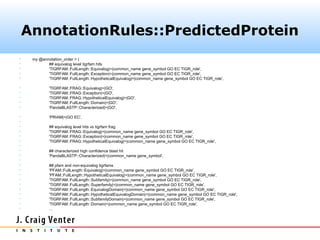
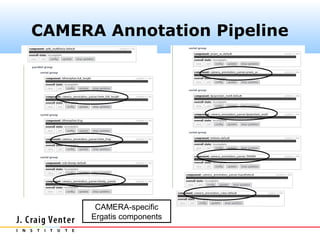
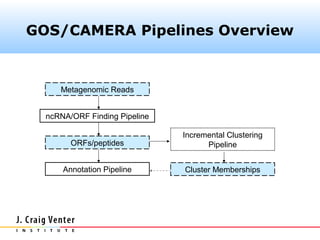
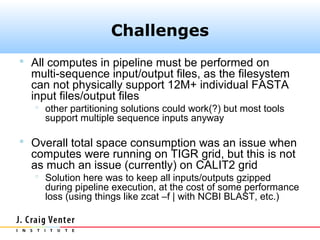
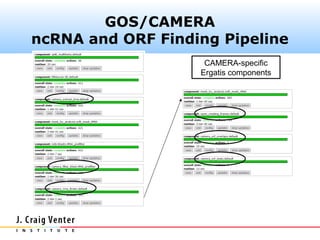
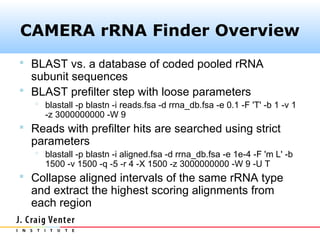
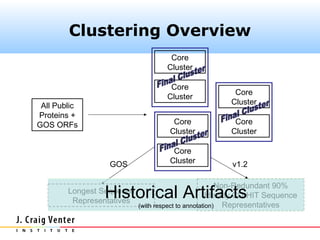
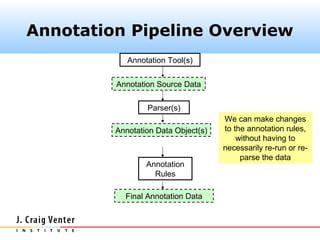
The document describes the CAMERA annotation pipelines and related infrastructure. It discusses the compute infrastructure including the CALIT2 compute grid and SOS cluster. It then describes the GOS/CAMERA ncRNA and ORF finding pipeline, including the rRNA finding pipeline, ORF calling, and tRNA extraction. It also discusses the GOS incremental protein clustering pipeline and the CAMERA annotation pipeline, including specifications and implementation. Finally, it provides thoughts on object-oriented design approaches for the annotation pipeline to support changing annotation rules and data sources over time.
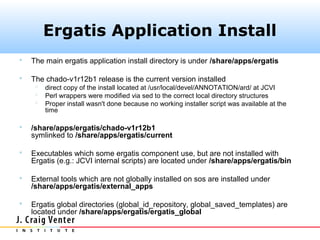
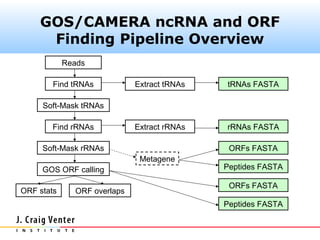

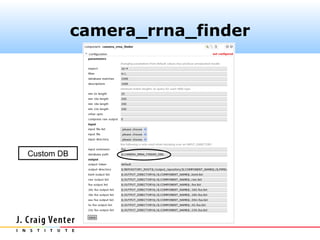
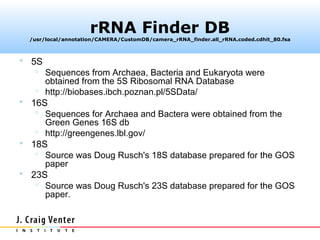
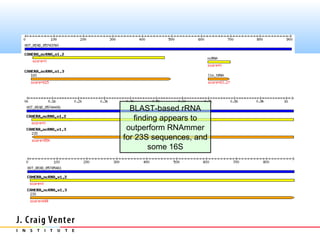
![rRNA Finder DB
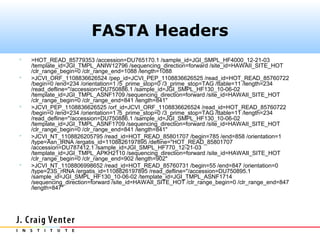
Fasta headers were coded as follows:
>#S [D] ...original.header...
where # is one of (5, 16, 18, 23) and D is one of
(A, B, E). The camera_rrna_finder
component expects this format.](https://image.slidesharecdn.com/cameraannotationpipeline-130410151041-phpapp02/85/CAMERA-metagenomic-annotation-pipeline-26-320.jpg)

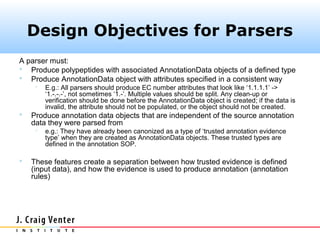
![AnnotationData Objects
AnnotationData
AnnotationData::Polypeptide
Polypeptide
type:
[some string]
attributes: AnnotationData Object(s)
common_name
gene_symbol
EC
GO
TIGR_role
…](https://image.slidesharecdn.com/cameraannotationpipeline-130410151041-phpapp02/85/CAMERA-metagenomic-annotation-pipeline-45-320.jpg)