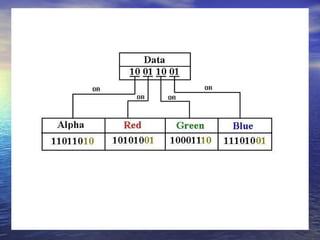
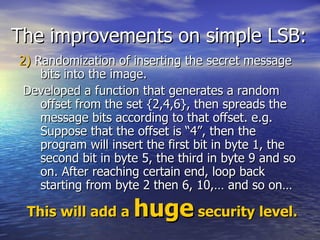
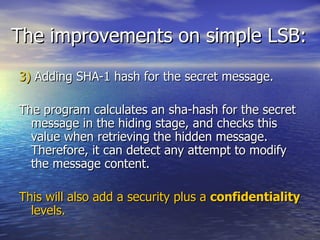
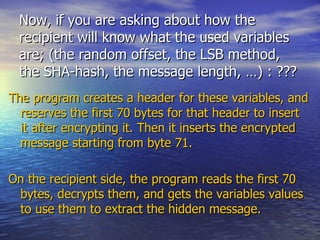
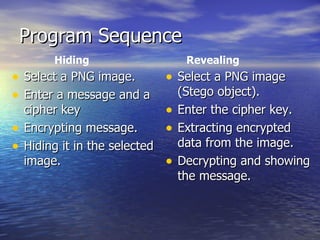
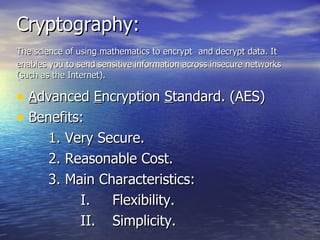
The document discusses combining cryptography and steganography techniques for secure communication. It proposes encrypting a message before hiding it in a digital object like an image file. This provides two layers of security since an extracted hidden message would still be encrypted. The document outlines the cryptography and steganography algorithms to be used, including AES encryption and least significant bit steganography with improvements like randomization and hashing.
![The improvements on simple LSB: I have added an option that allows the user to insert data into the two “least significant bits”. It is a little bit less secure, because there will be more modification. On the other hand, we can double the secret message size. [it’s up to the user]](https://image.slidesharecdn.com/c3s-110124133402-phpapp01/85/C3-s-10-320.jpg)