Embed presentation
Download as PDF, PPTX
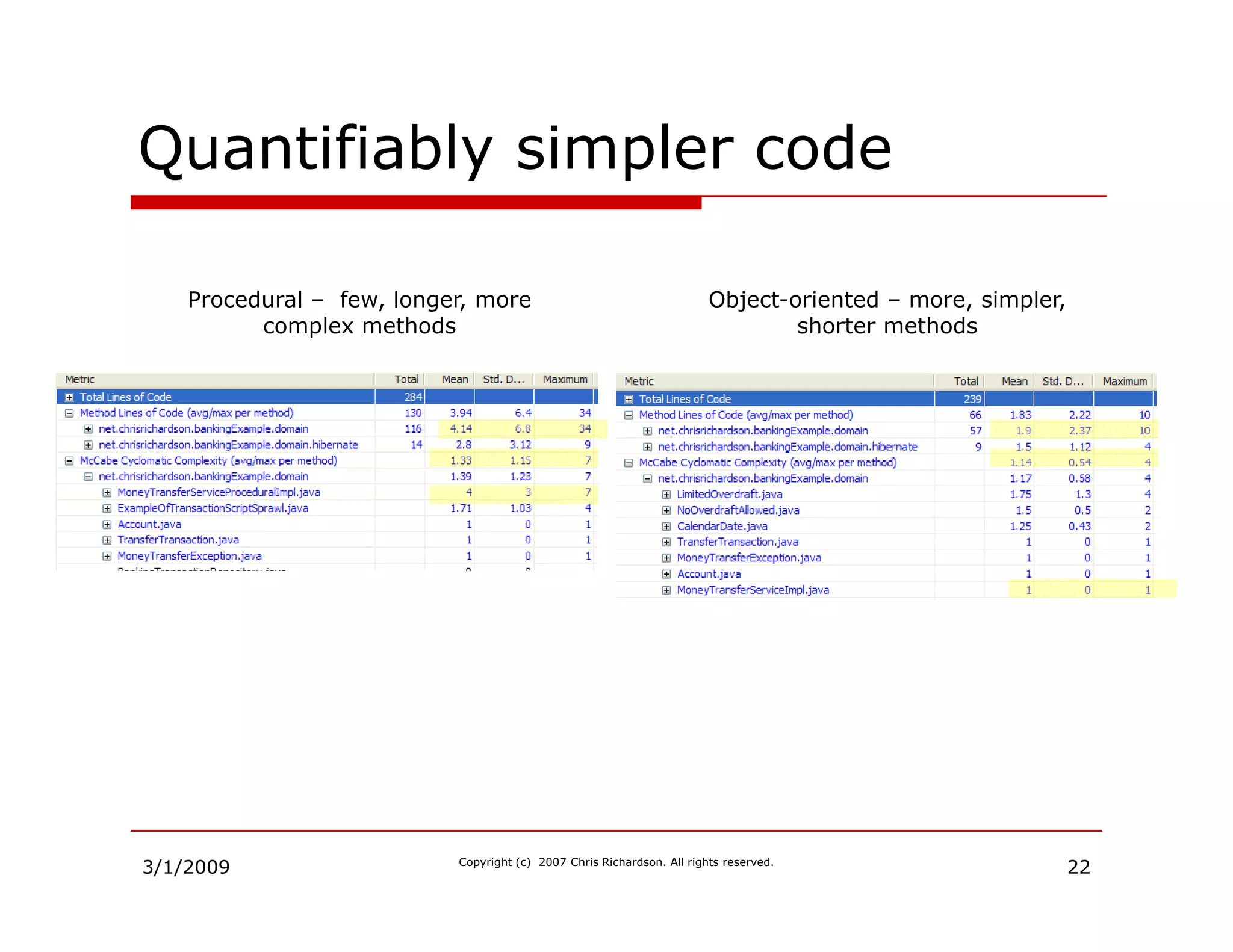

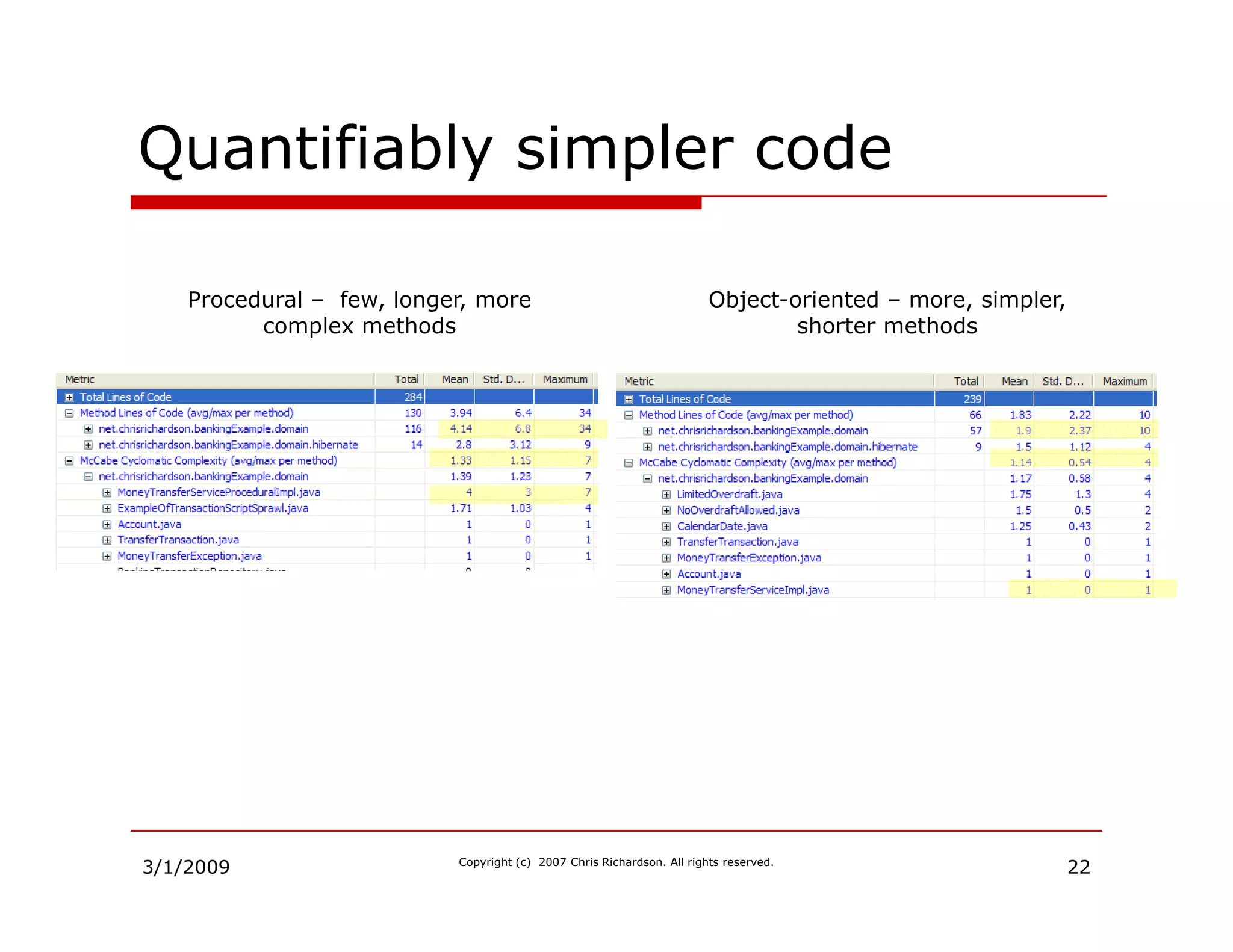
The document discusses improving application design by utilizing a rich domain model that emphasizes object-oriented business logic. It presents the domain model pattern, building blocks, and highlights the benefits of using Plain Old Java Objects (POJOs) along with object-relational mapping frameworks. The document also addresses common challenges in adopting object-oriented practices and outlines the advantages of modularity, maintainability, and testability that come with rich domain modeling.
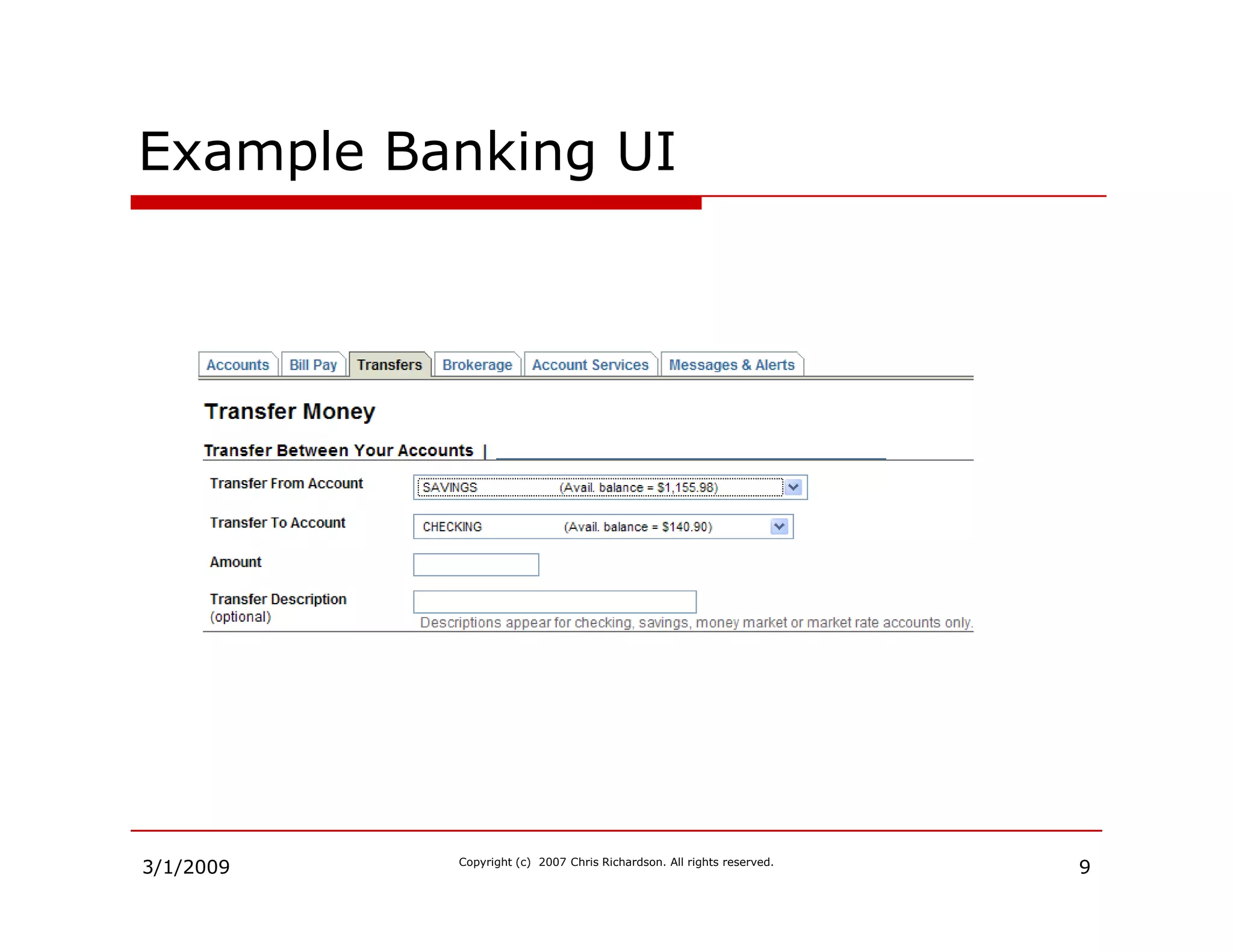
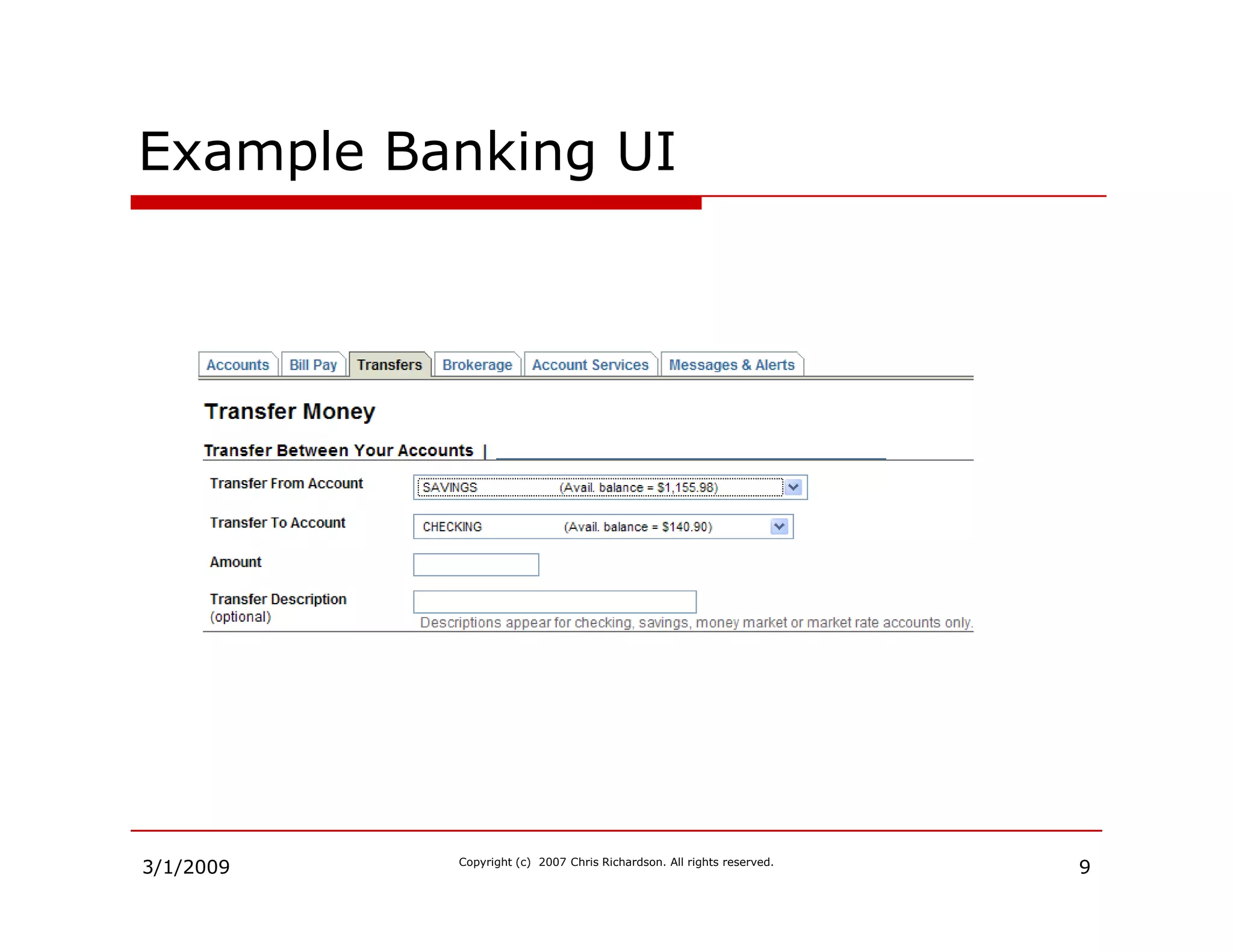
Introduction to improving application design using a rich domain model and object-oriented principles.
Chris Richardson, an expert with over 20 years of experience in software development and author of POJOs in Action.
Outlines the topics covered in the presentation including object representation, domain model patterns, code smells, and refactoring.
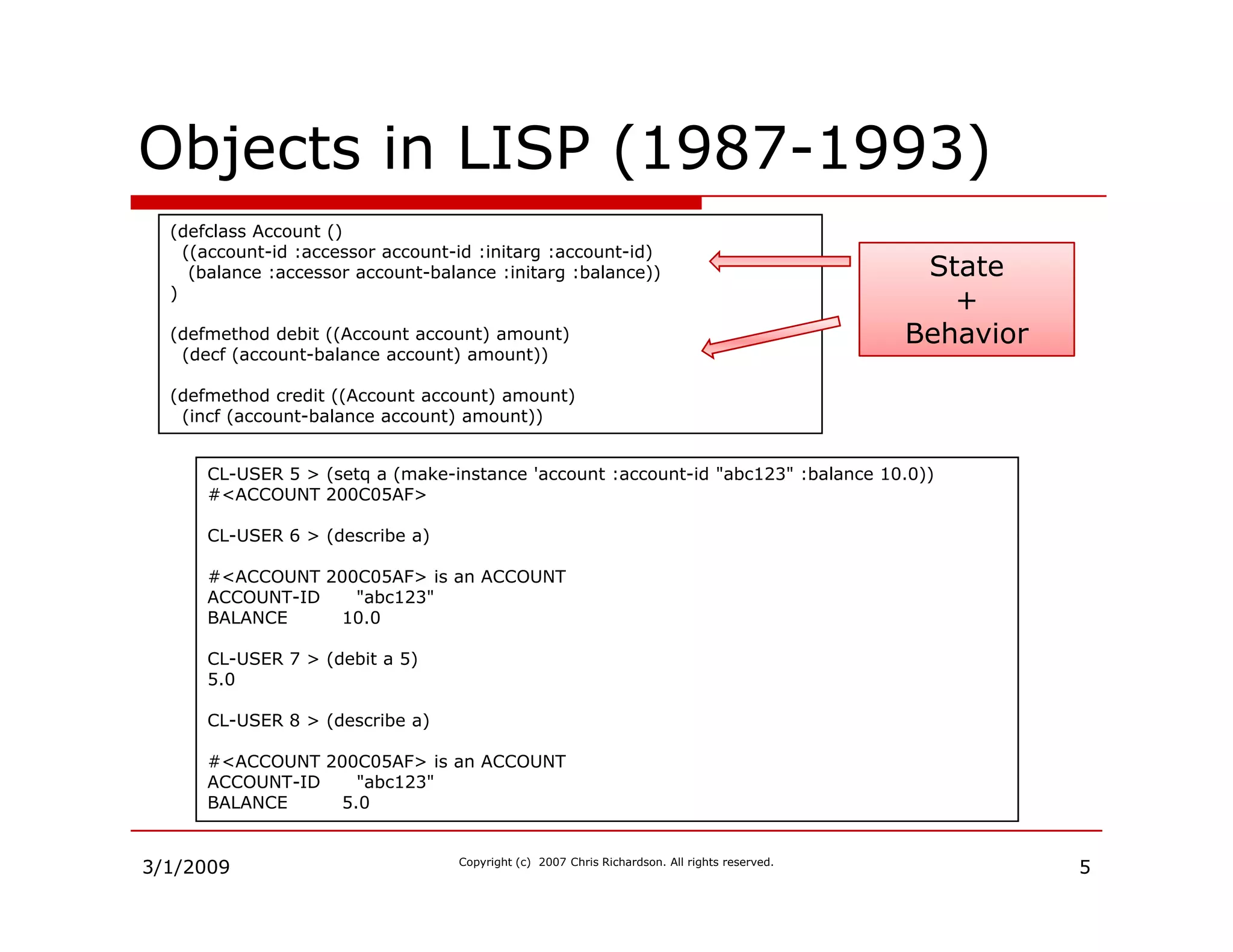
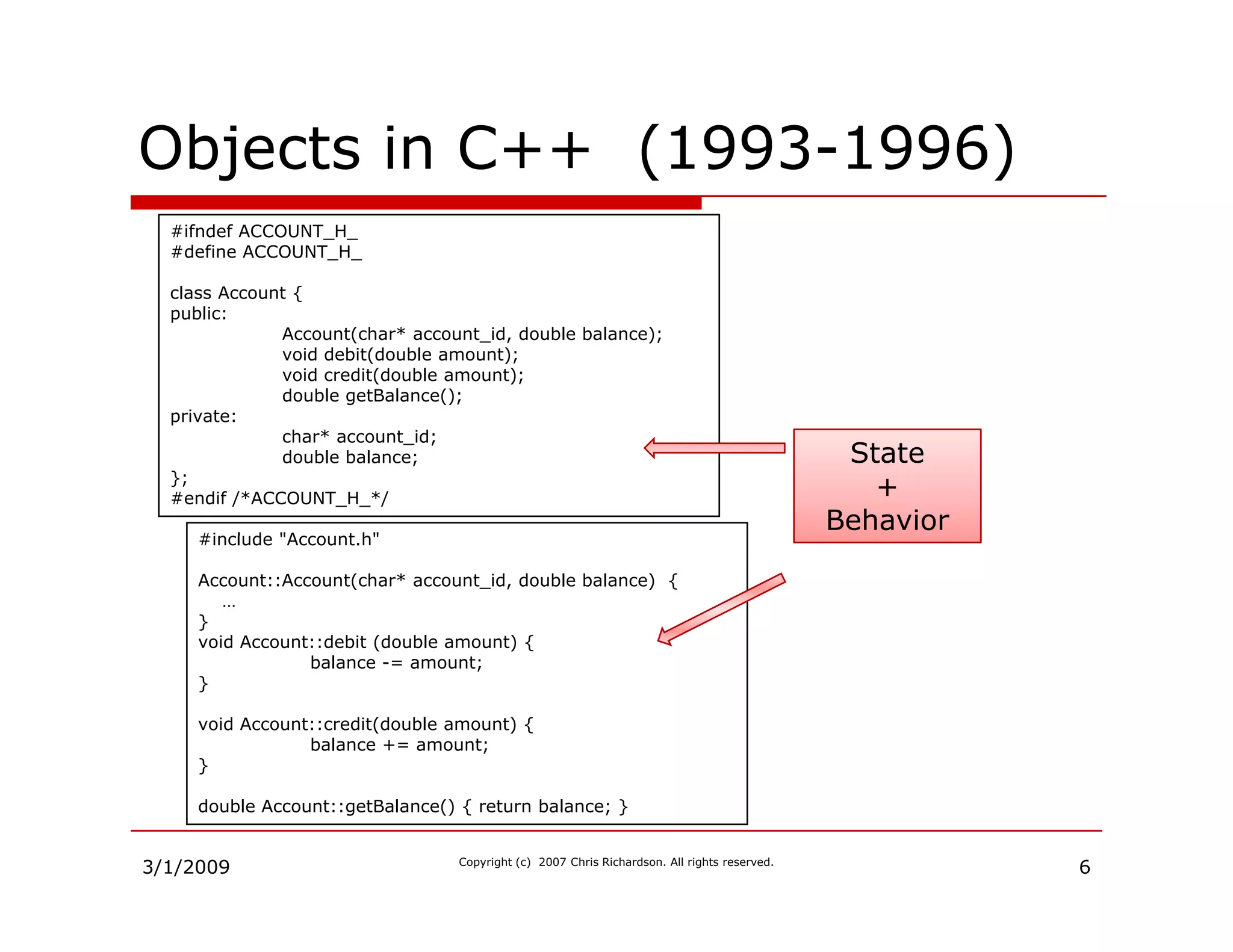
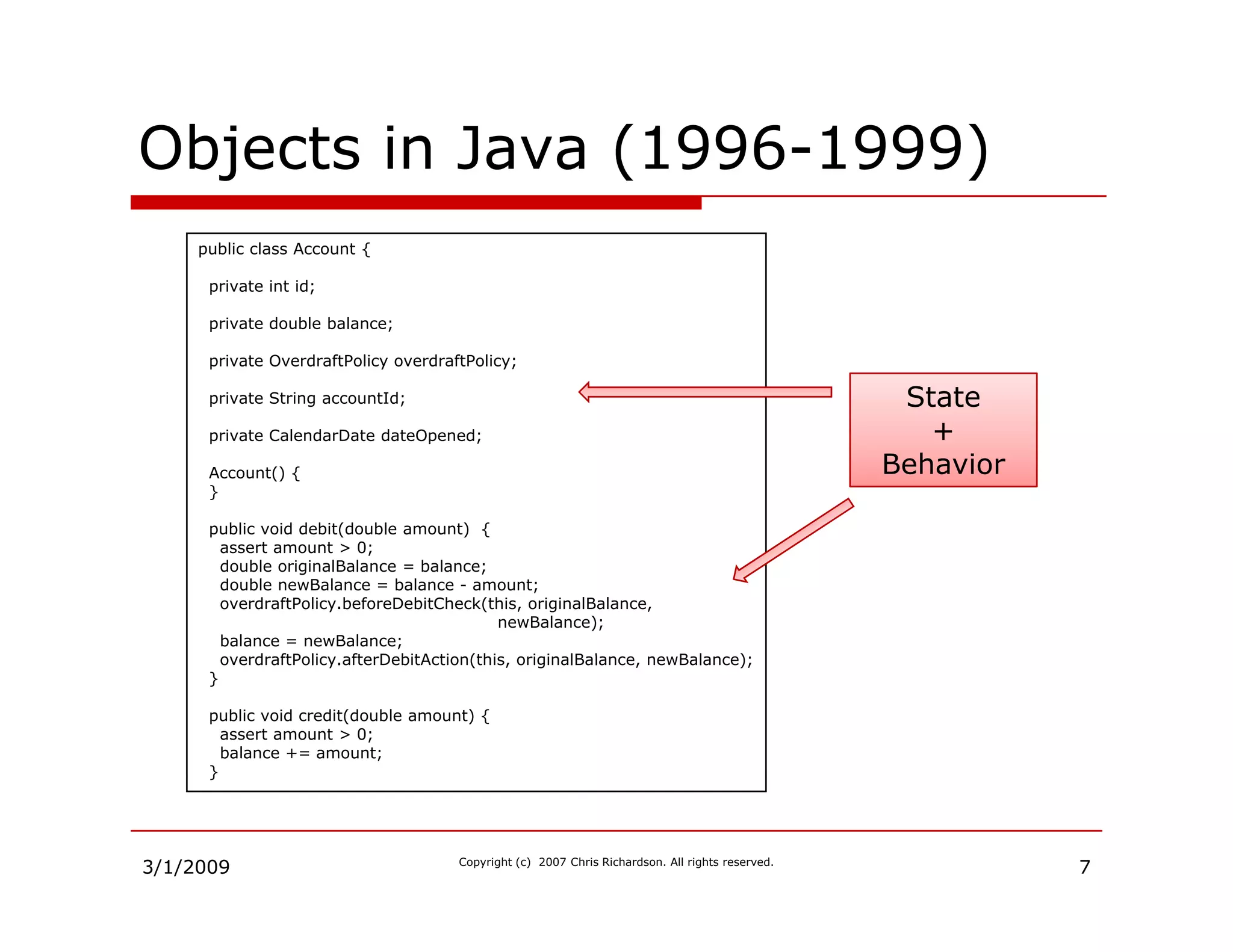
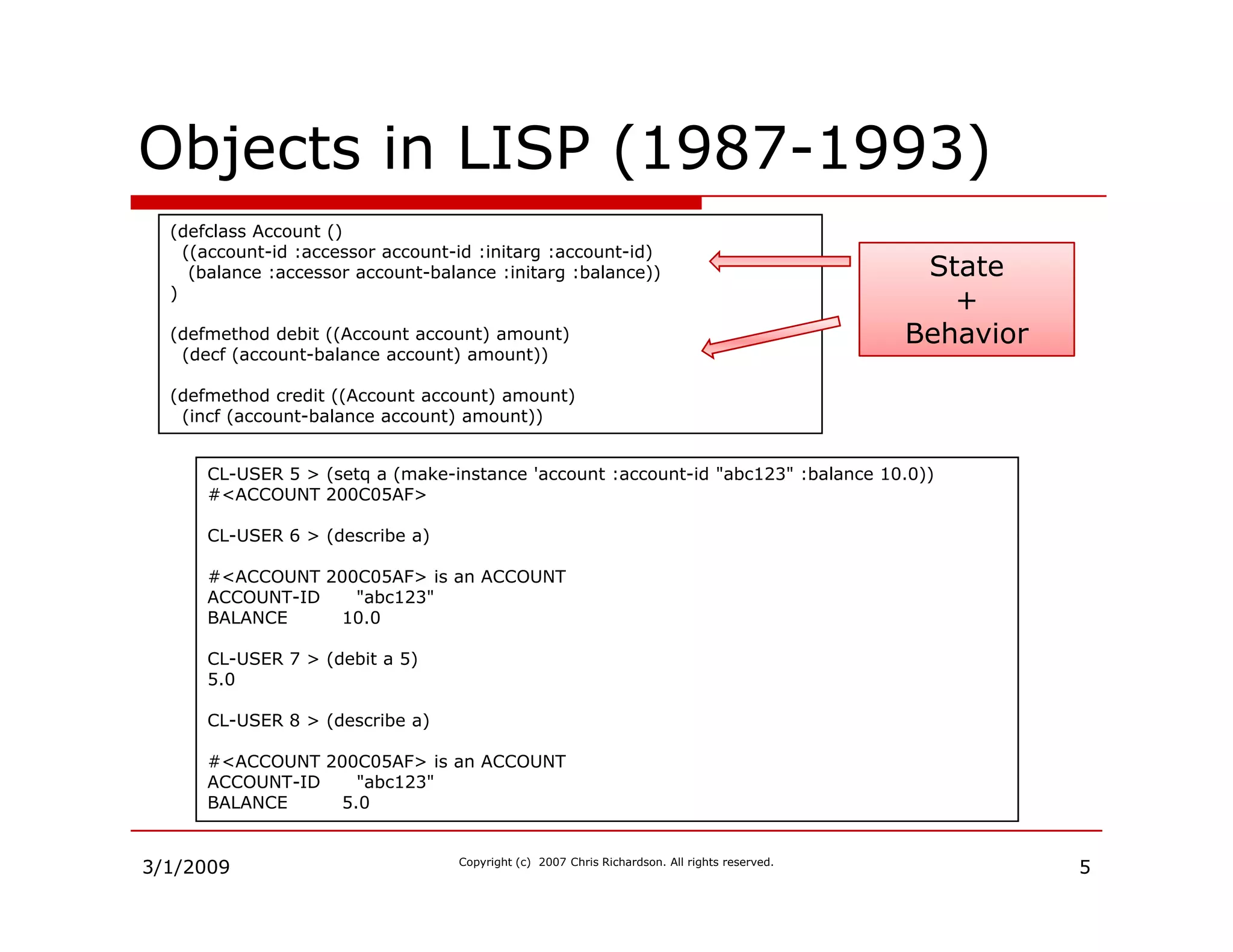
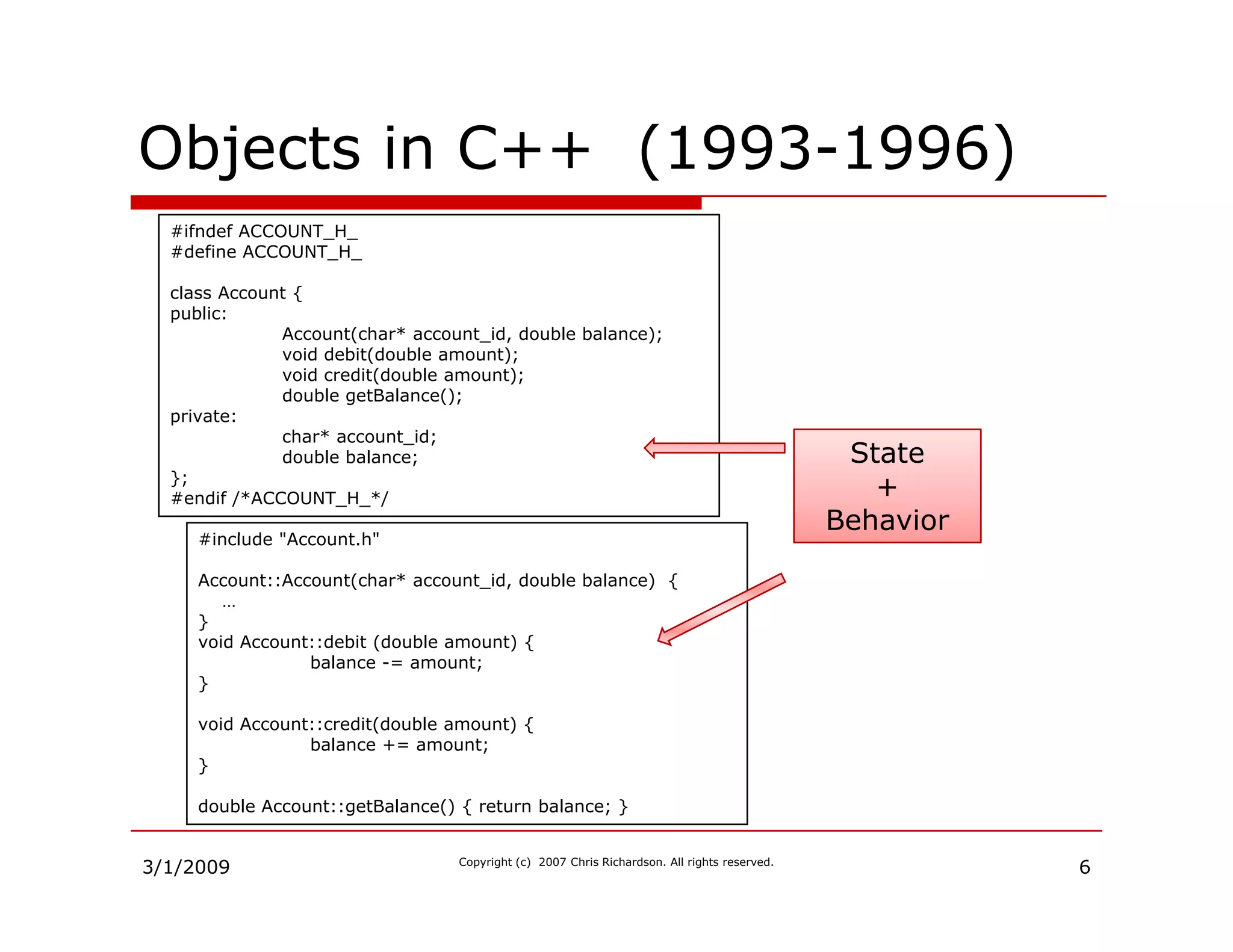
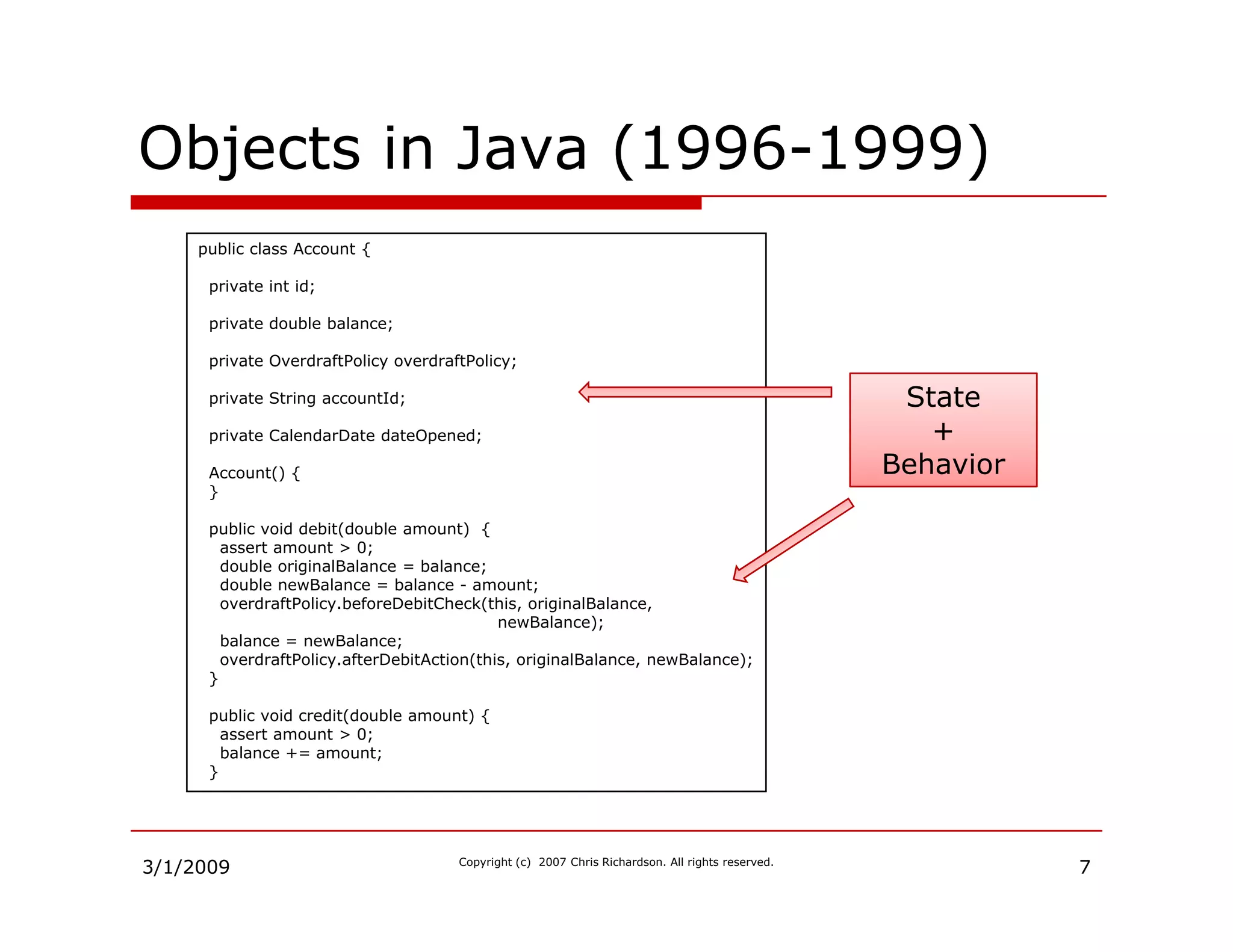
Demonstrates the implementation of objects in LISP, C++, and Java, highlighting the state and behavior.
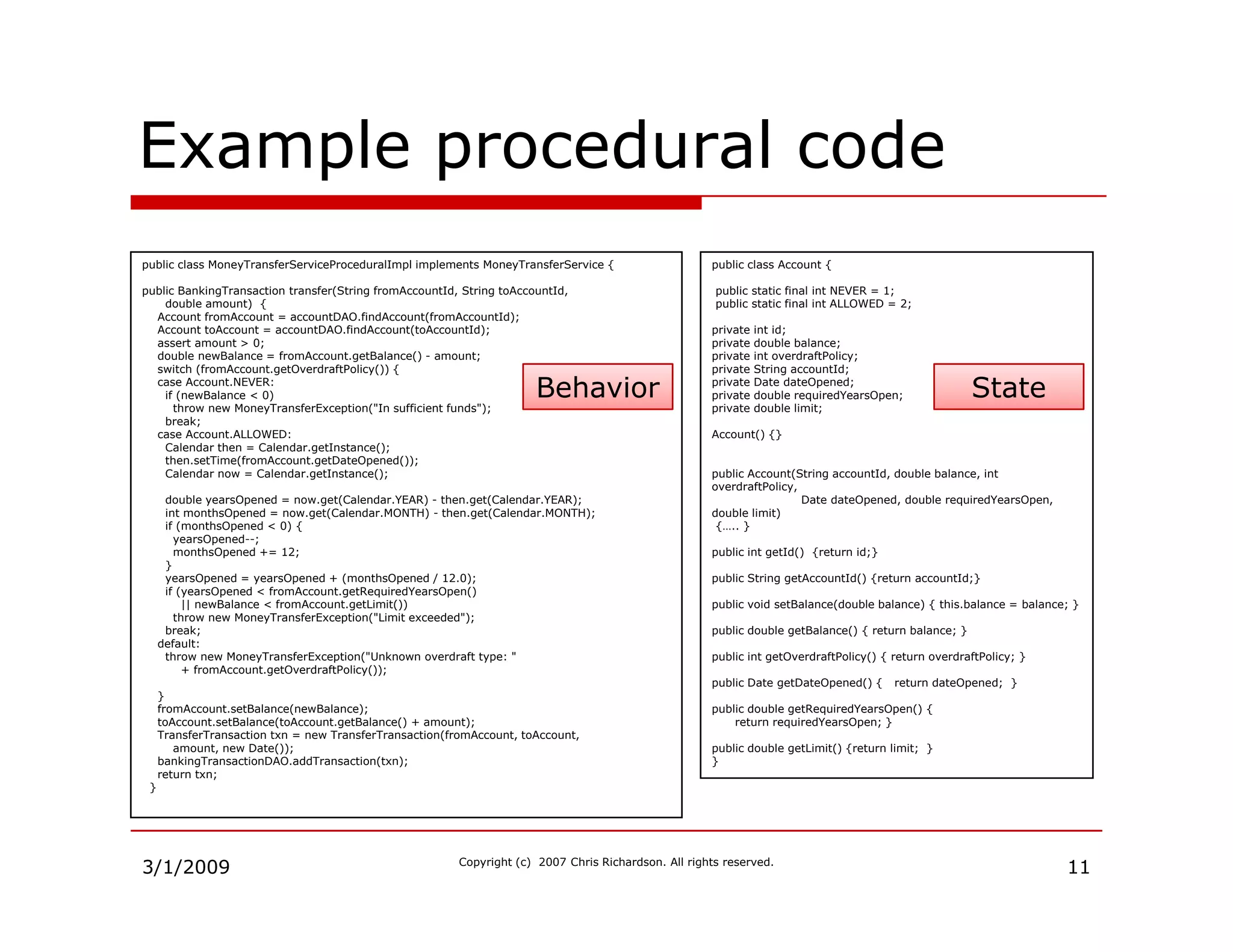
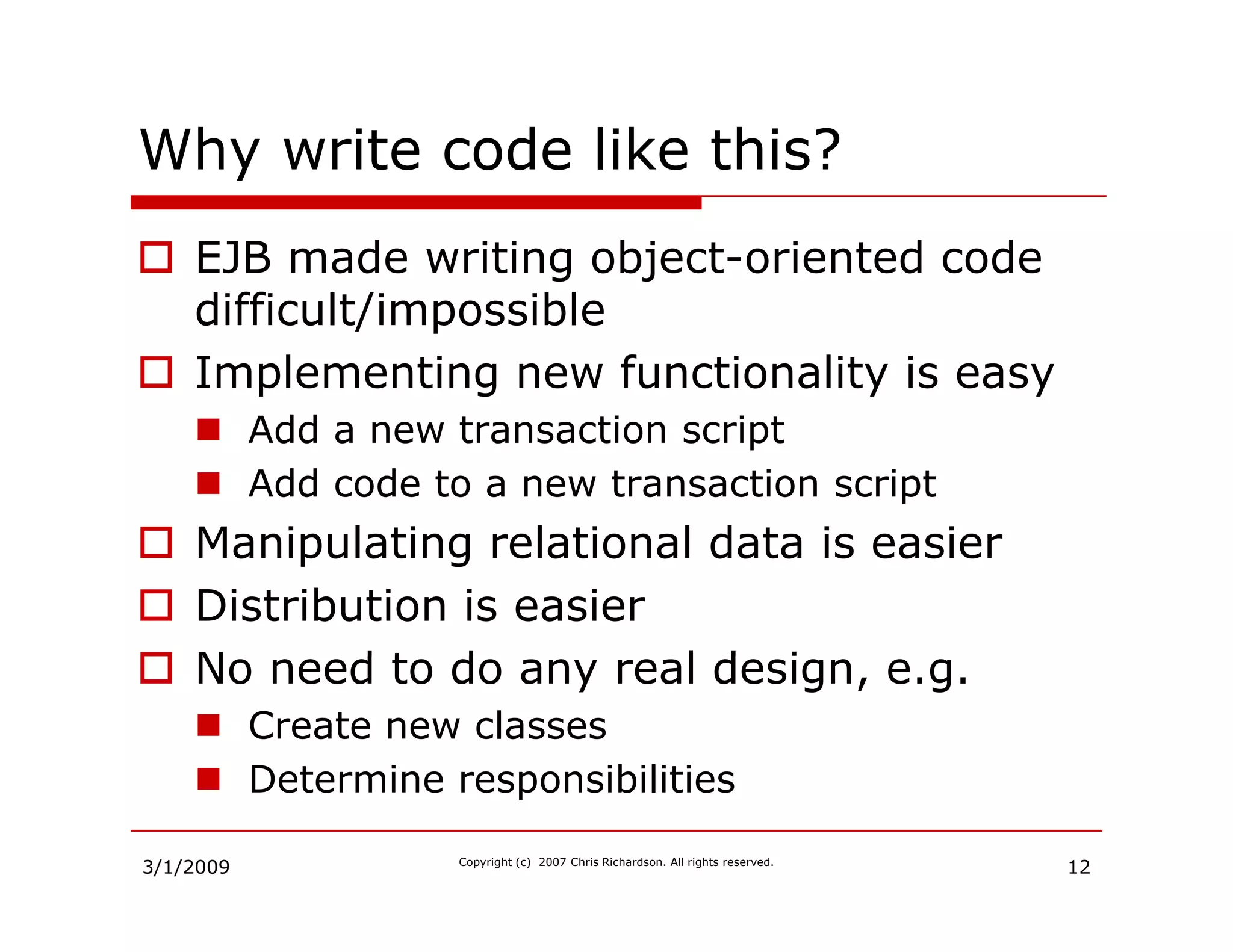
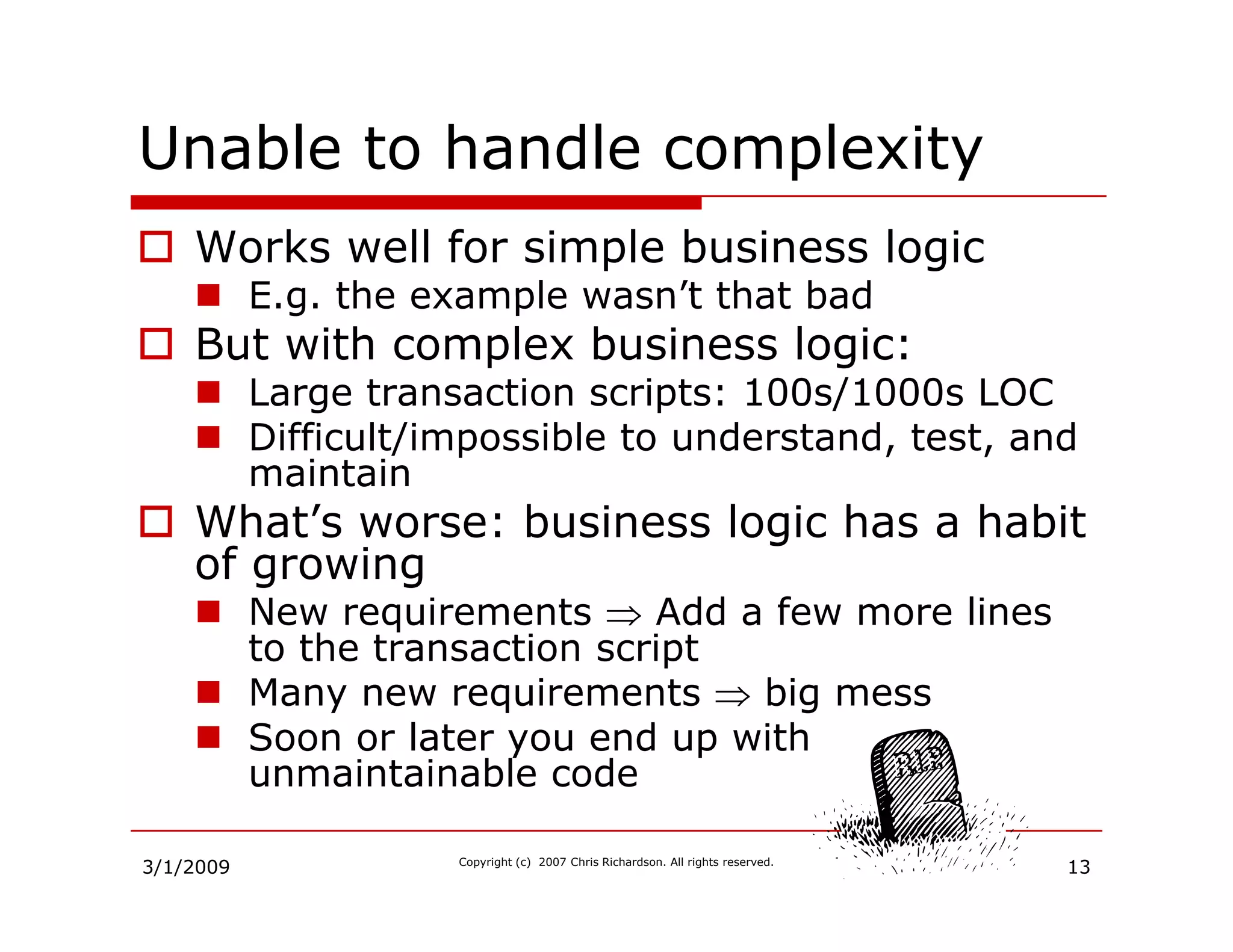
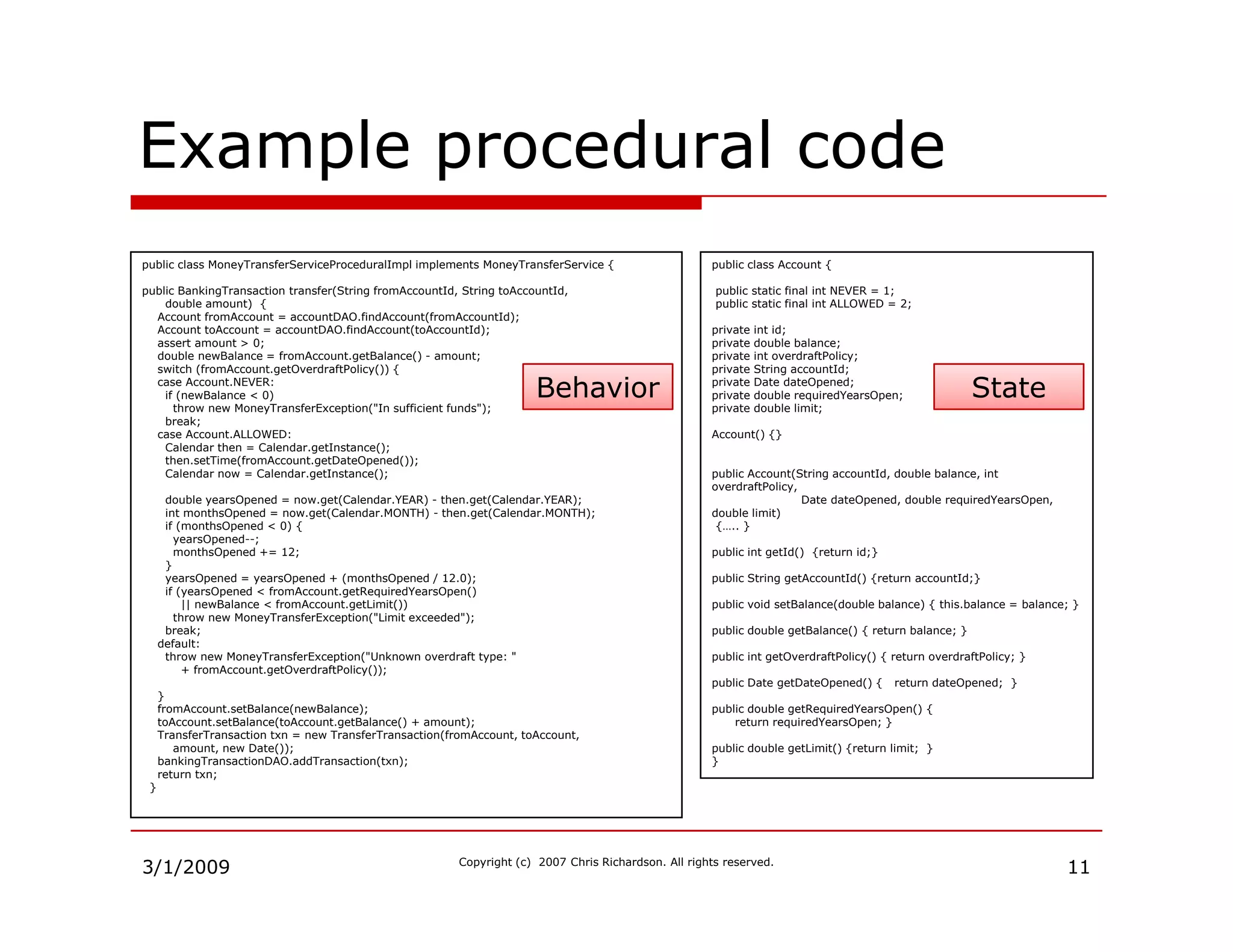
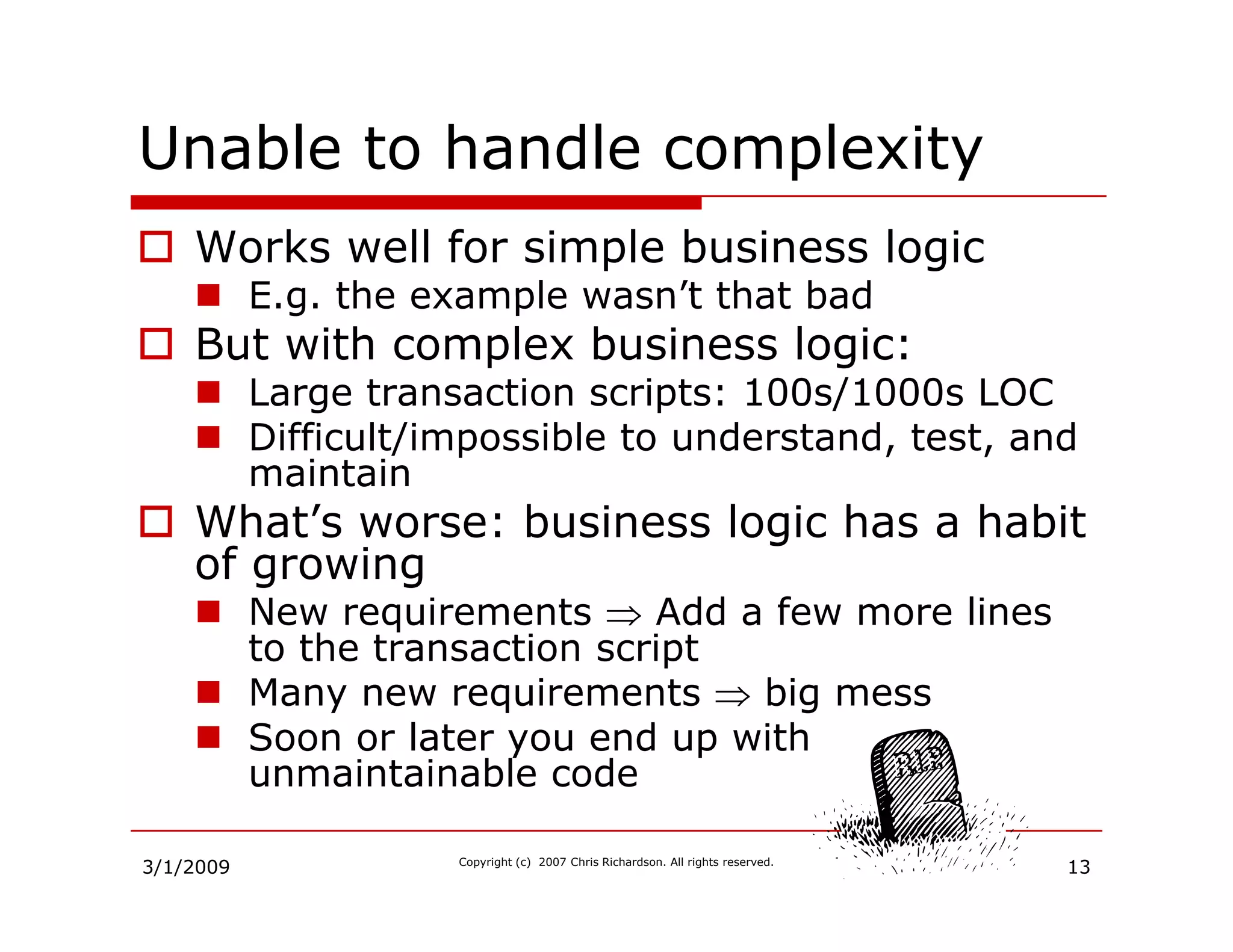
Describes the challenges posed by EJB in writing object-oriented code and the complexity of legacy systems.
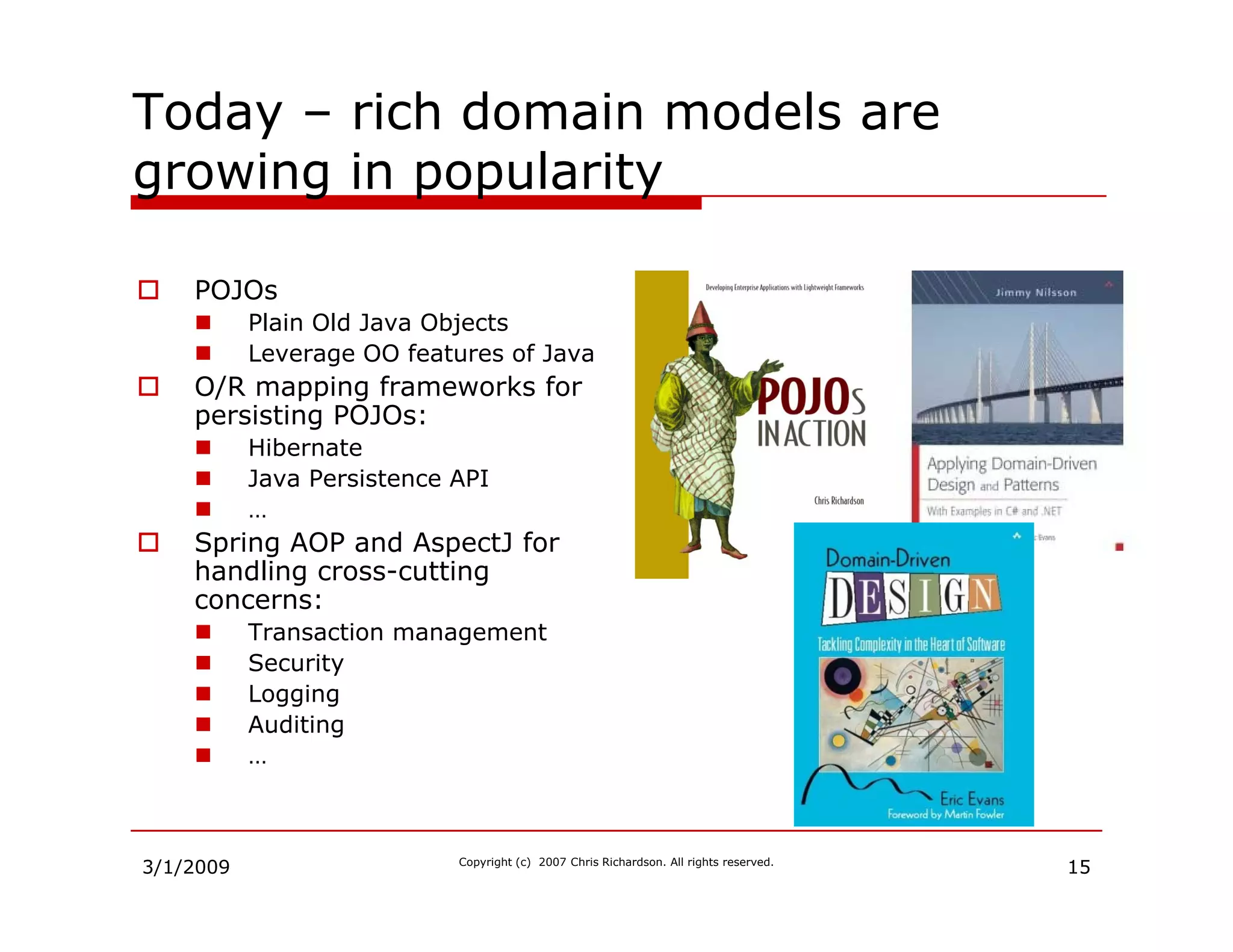
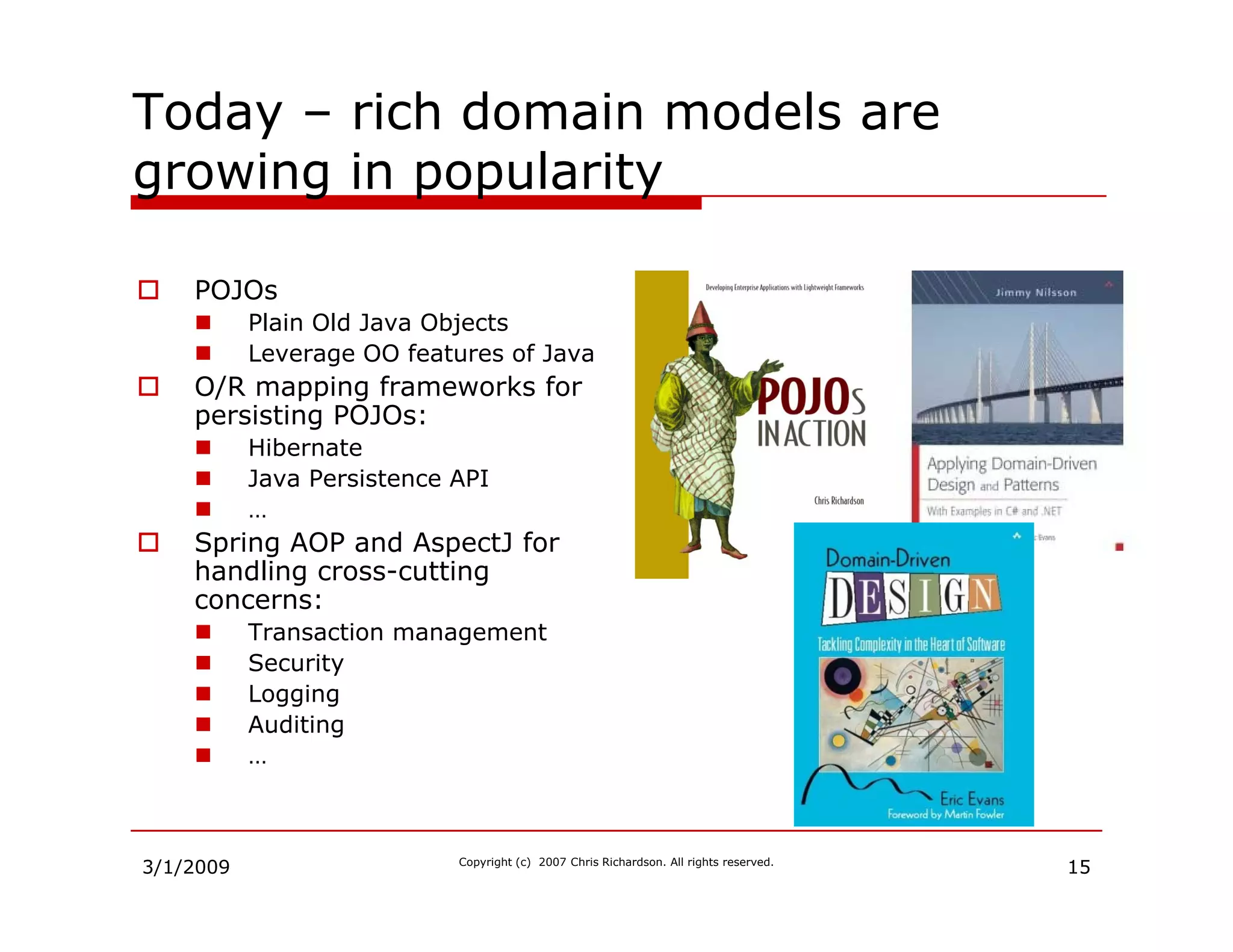
Introduction to the concept of Plain Old Java Objects (POJOs) and the benefits of using rich domain models.
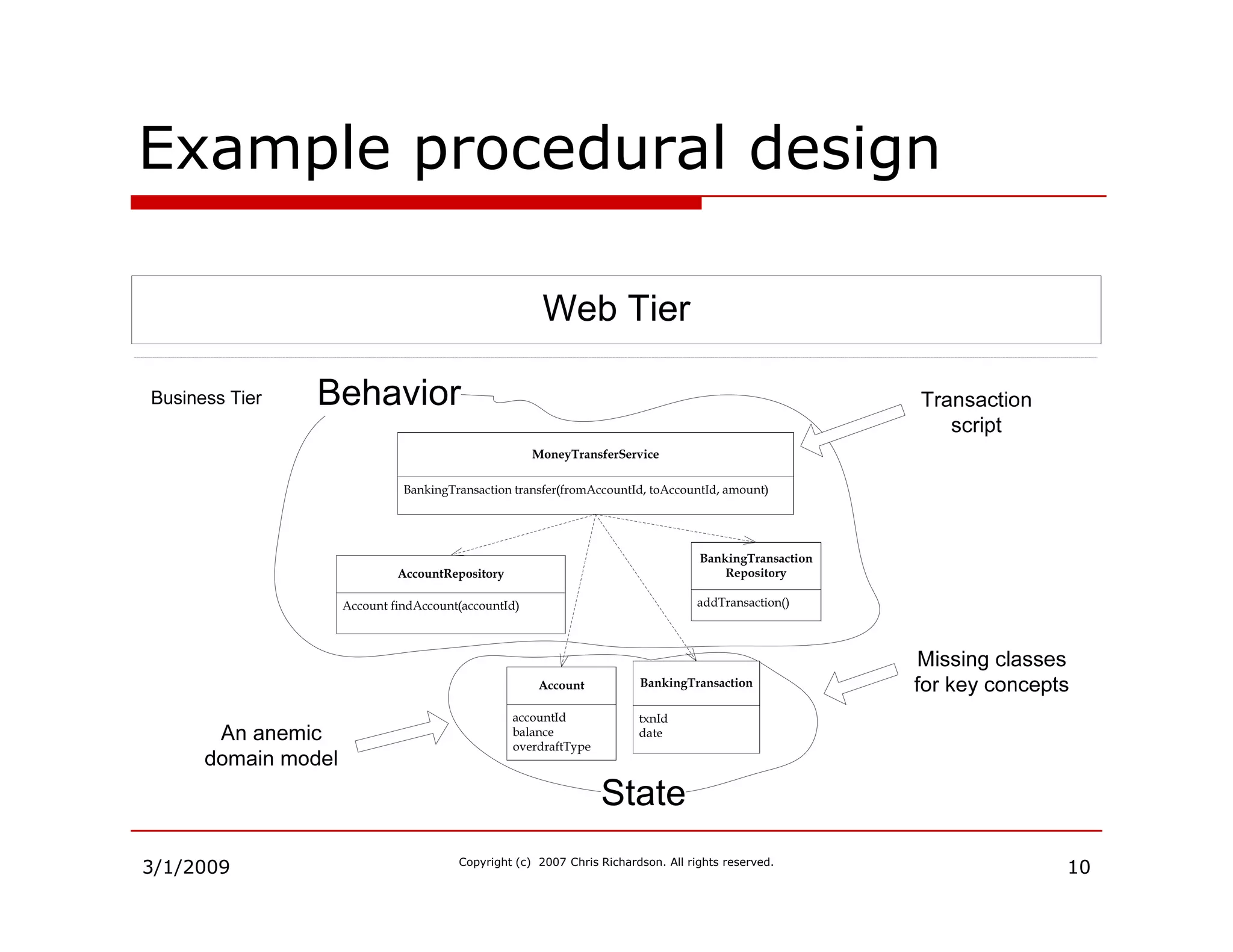
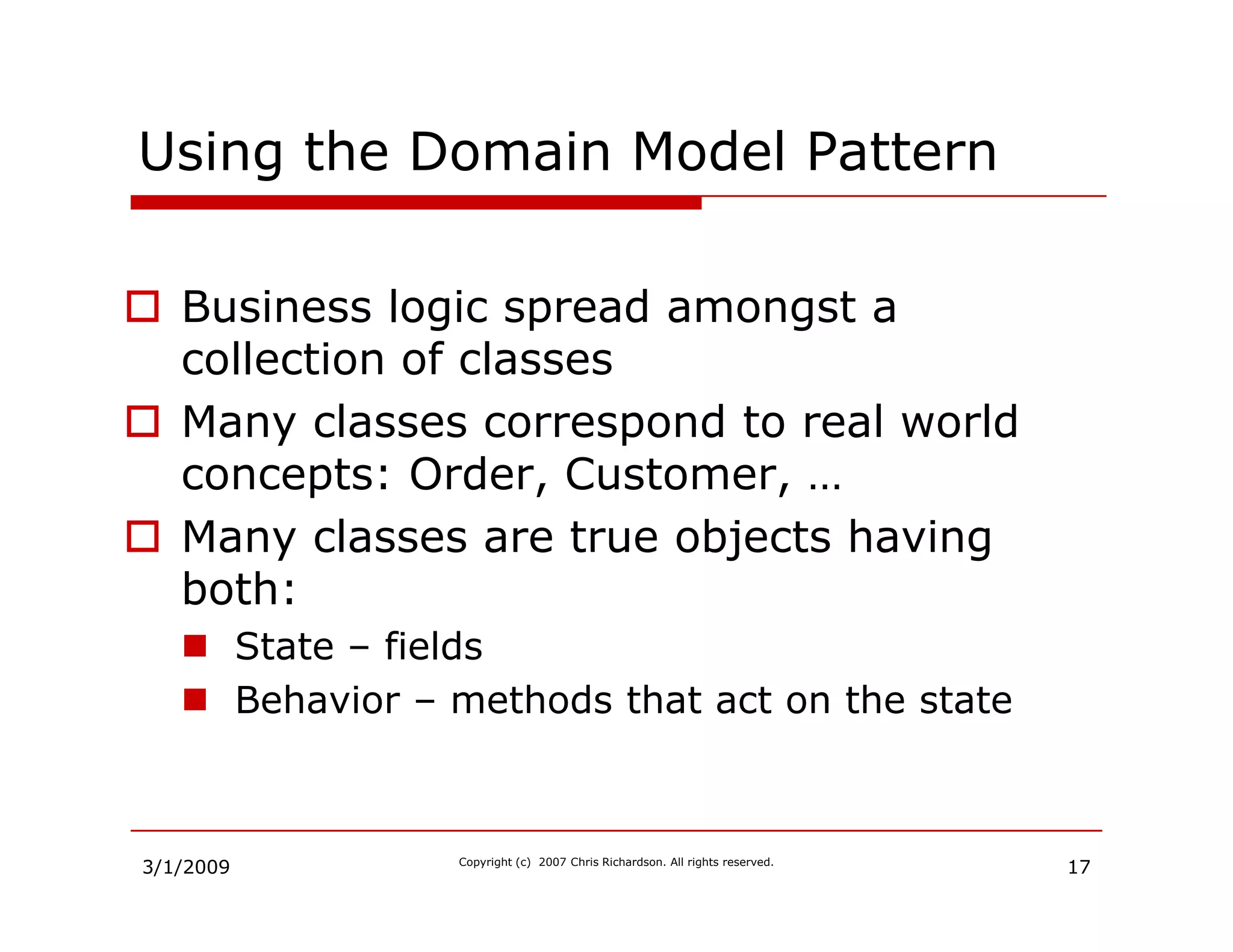
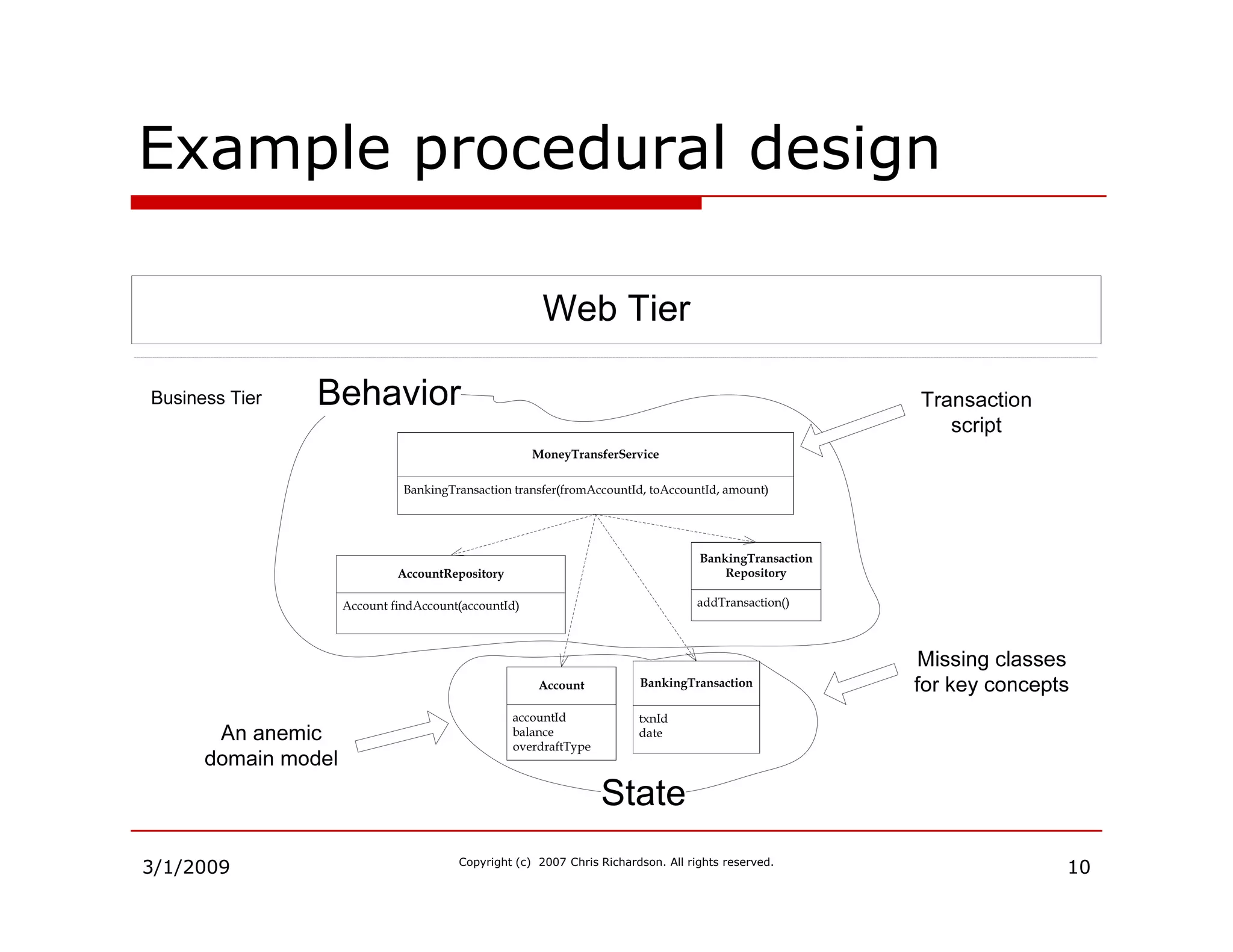
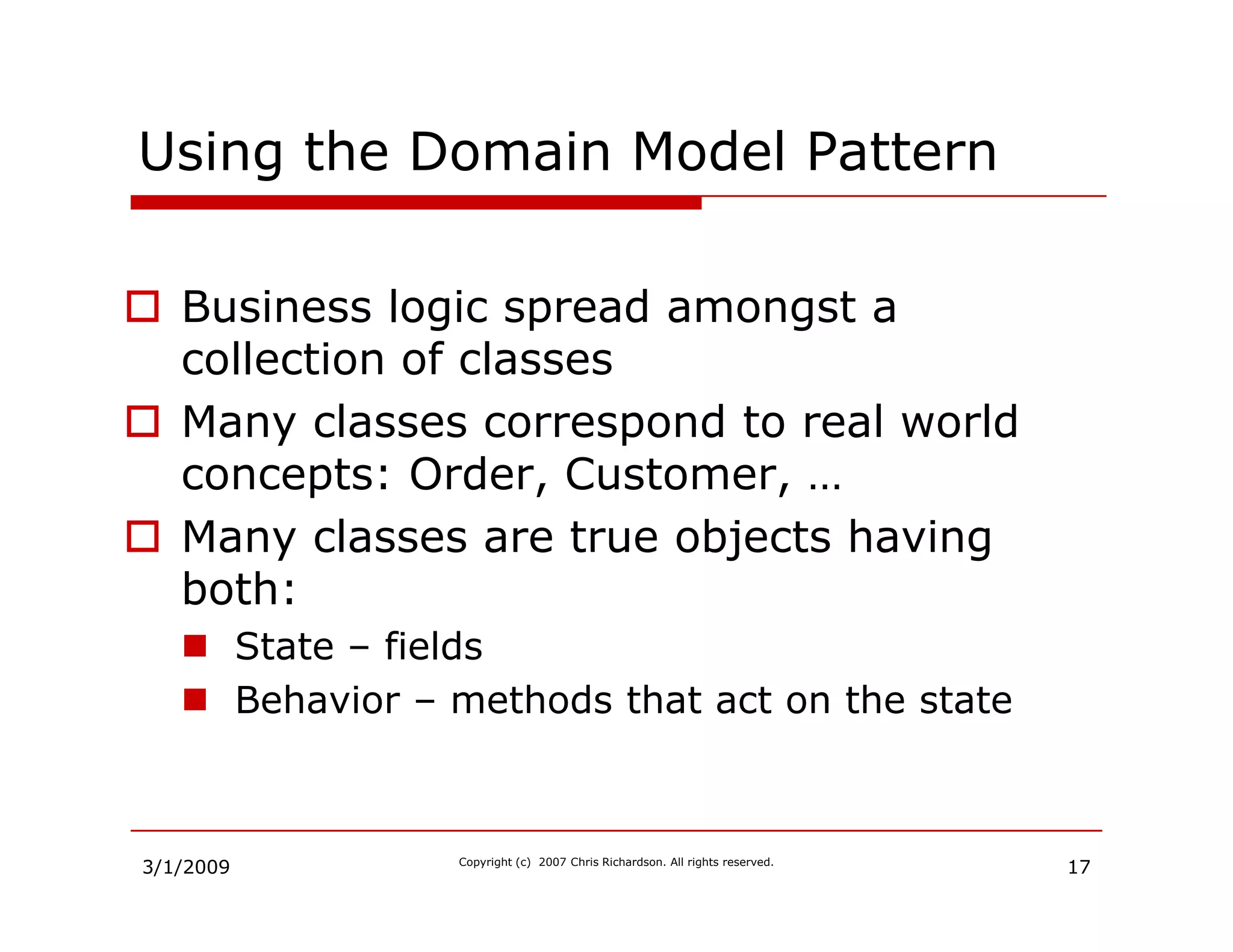
Introduction to the domain model design pattern and when to apply it based on business complexity.
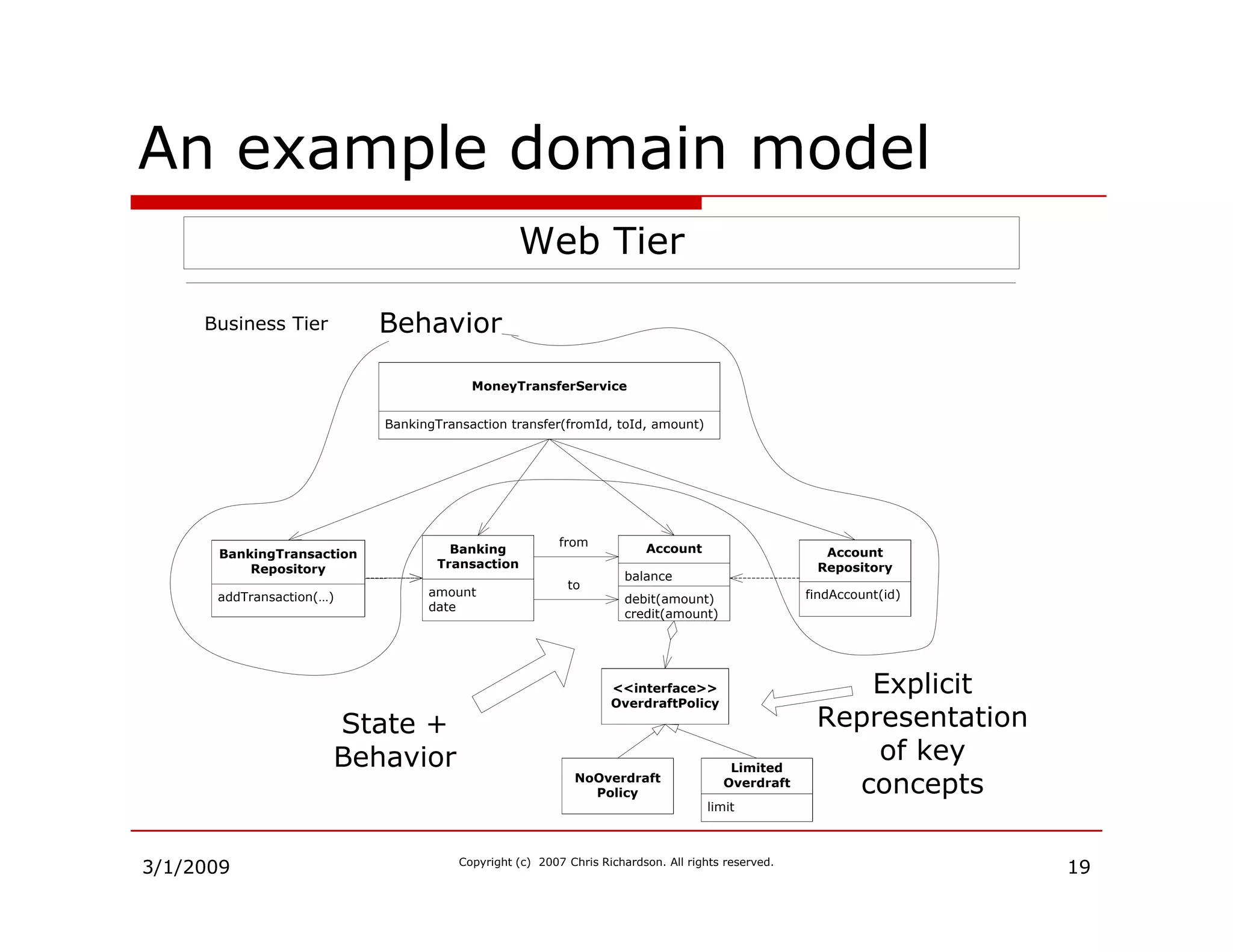
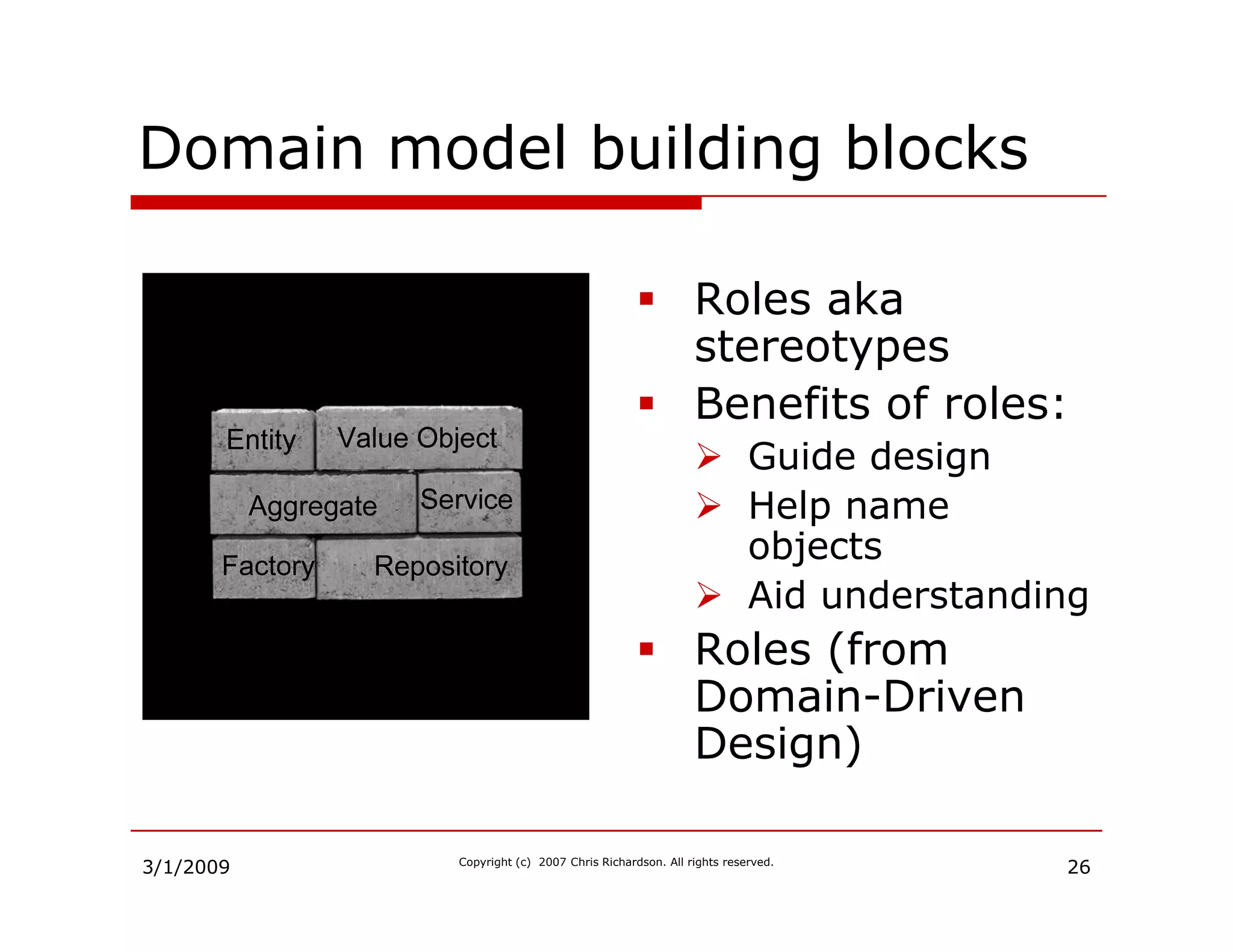
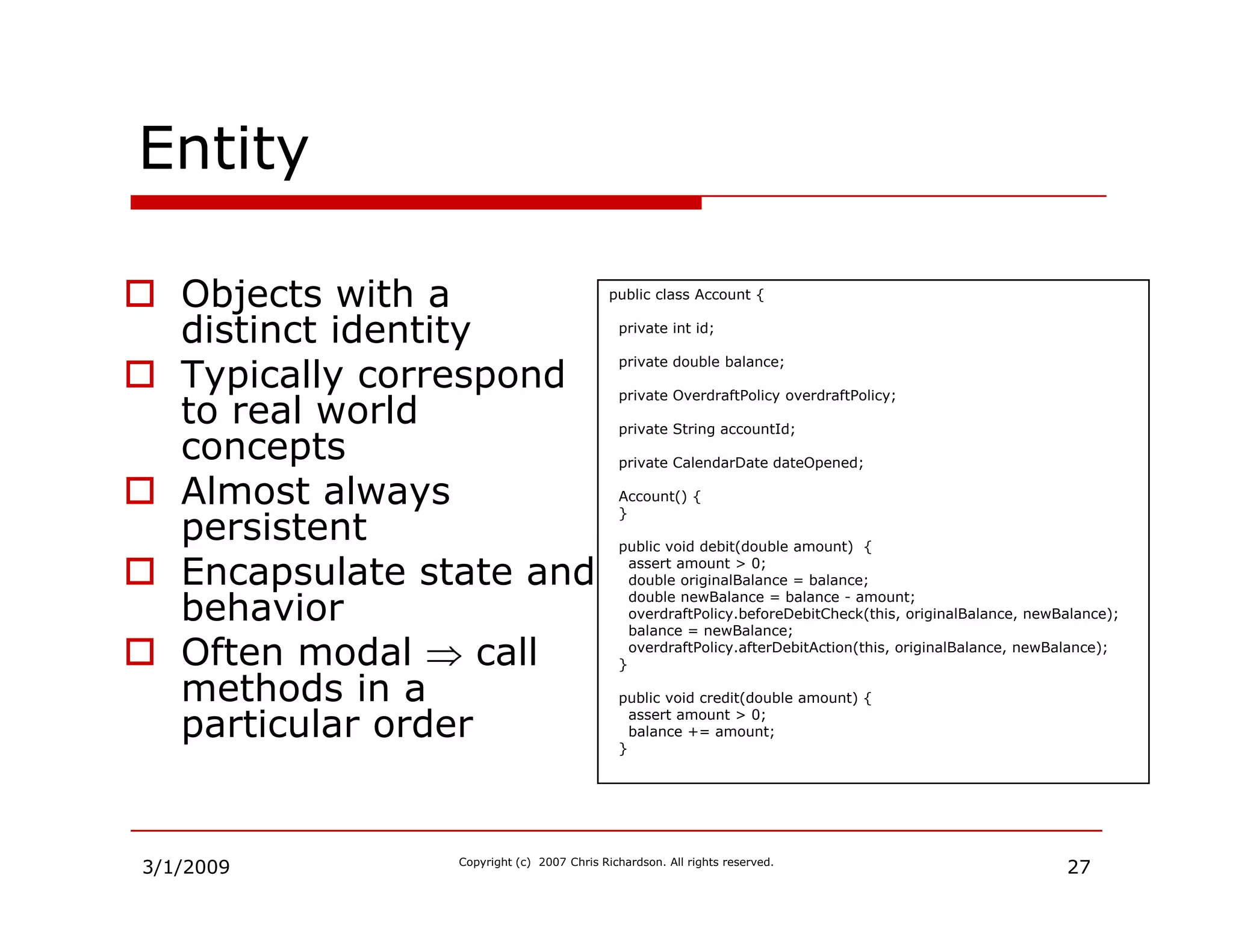
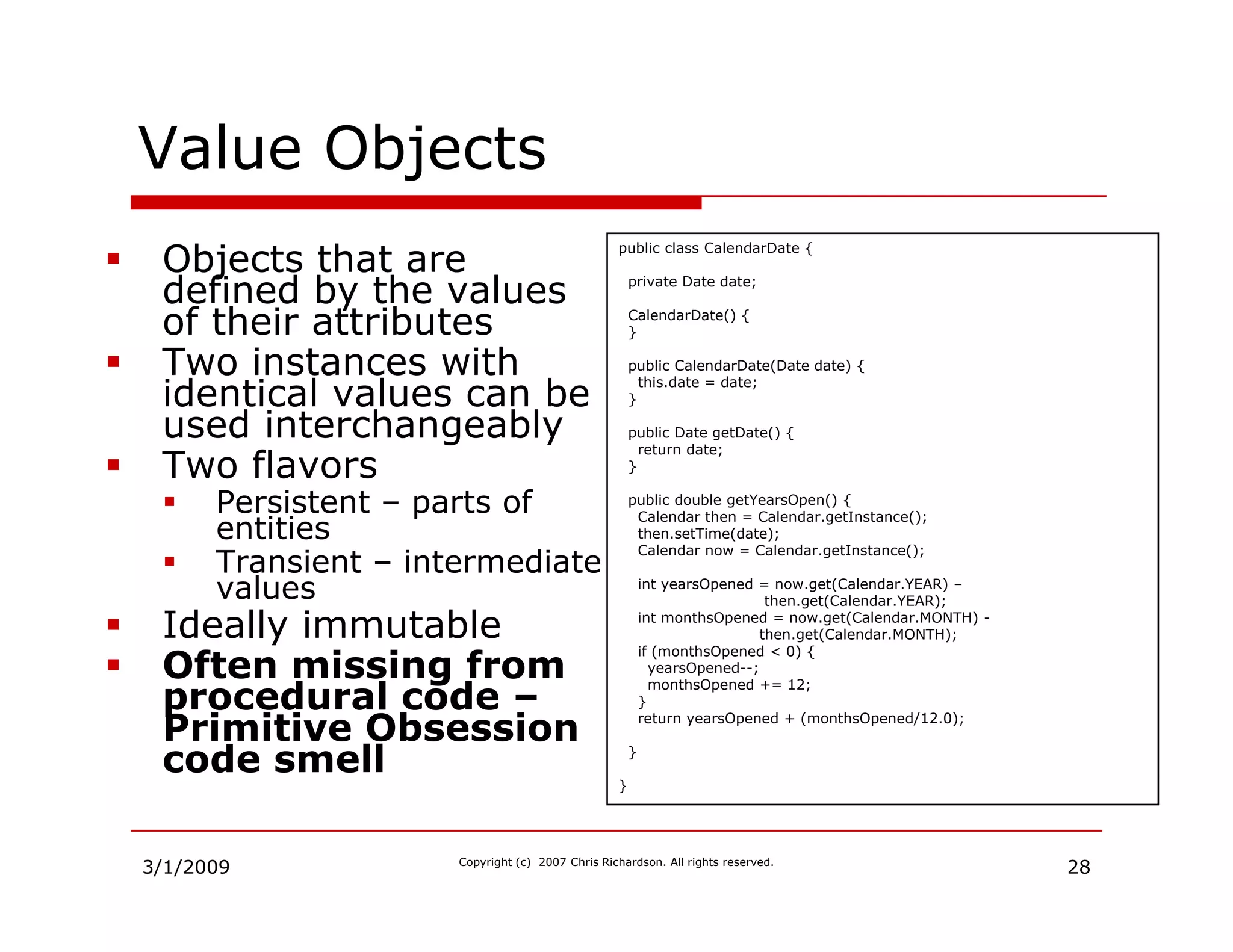
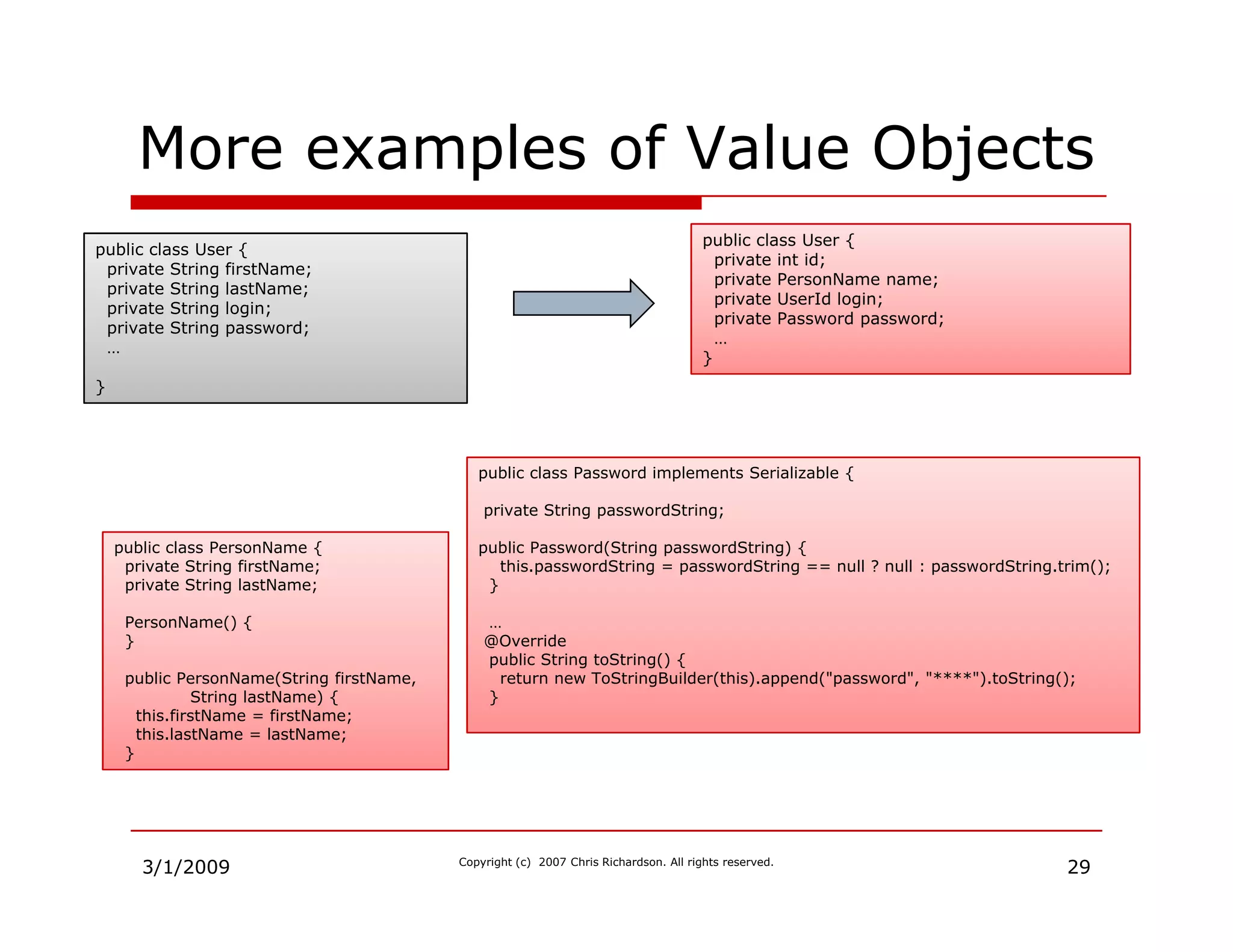
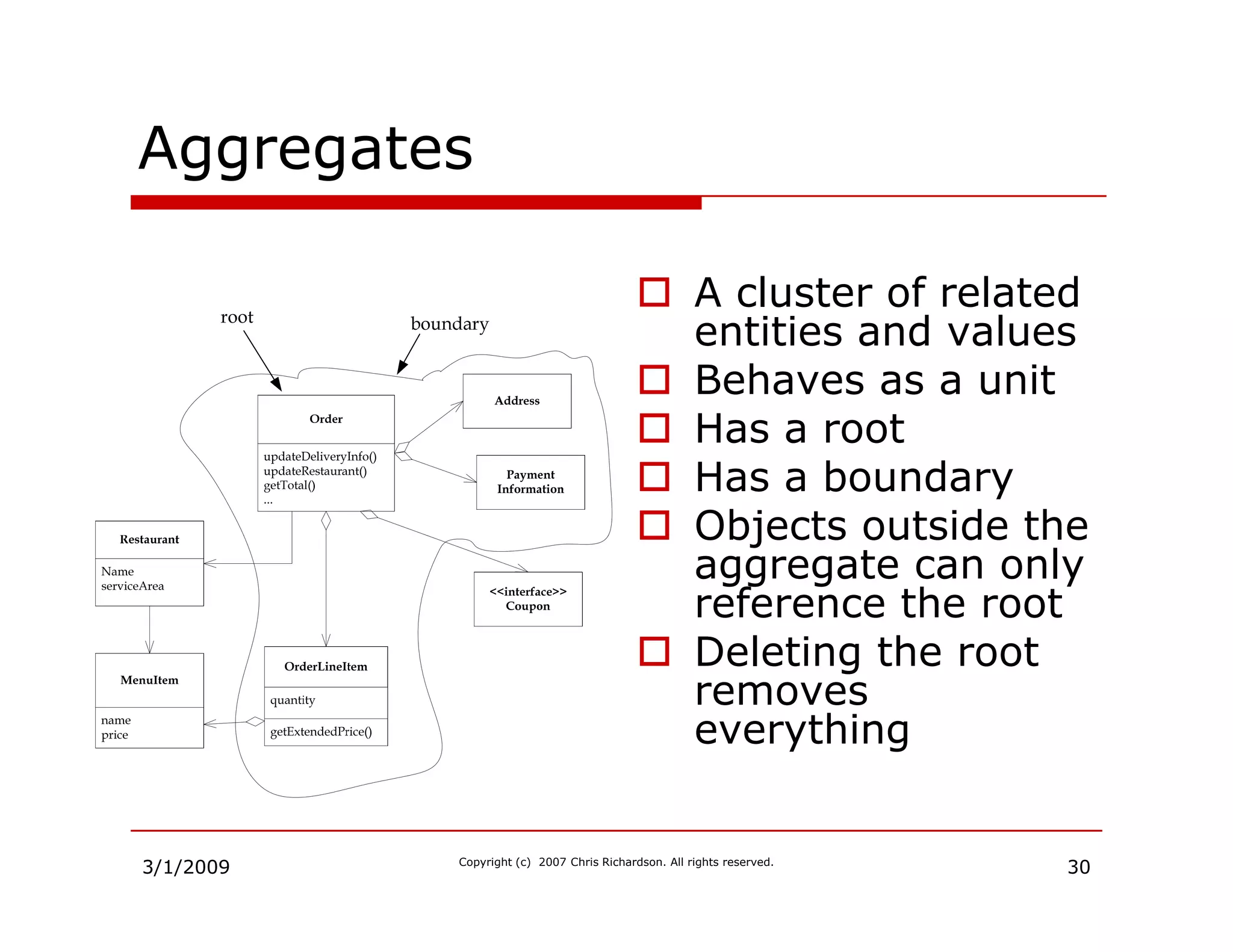
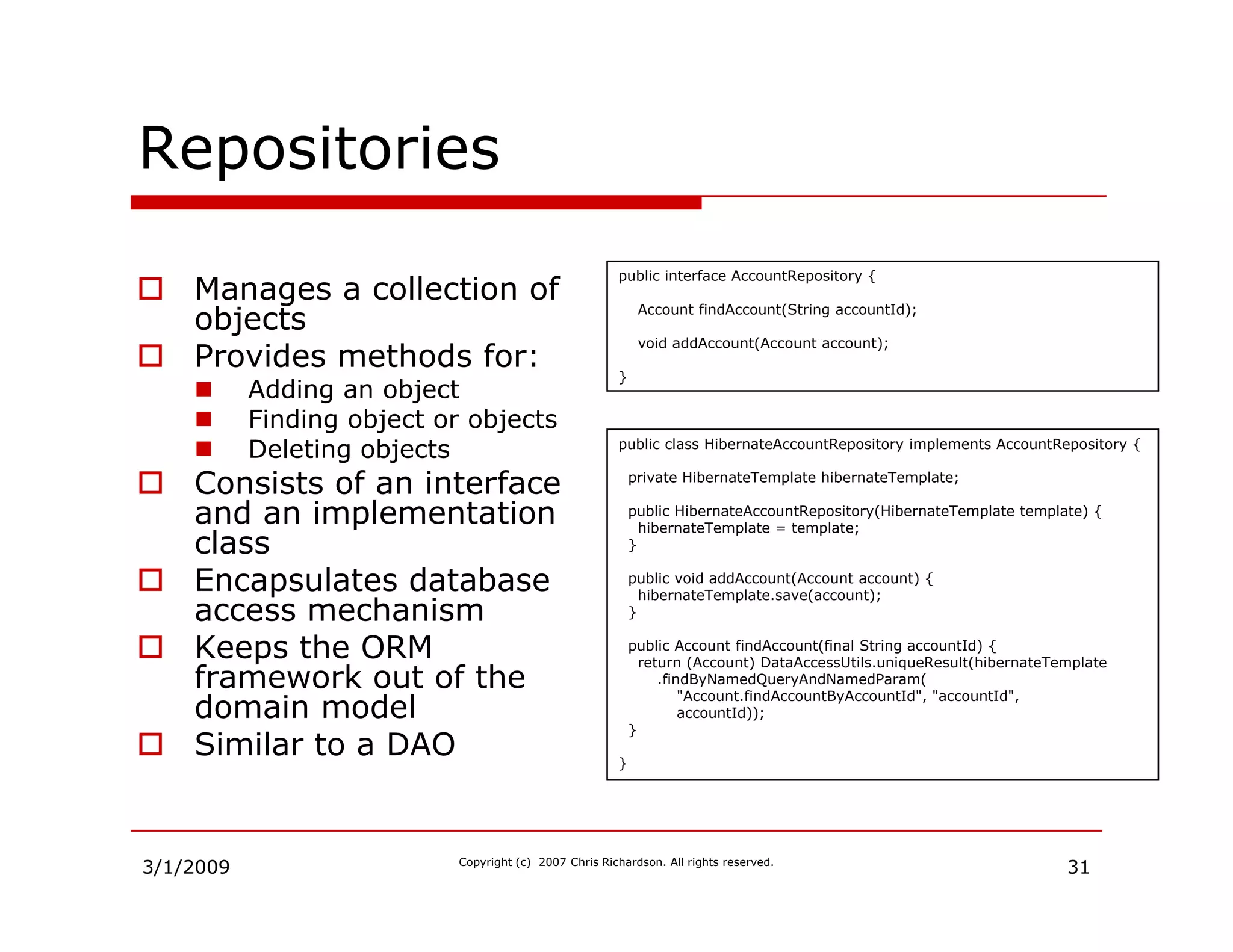
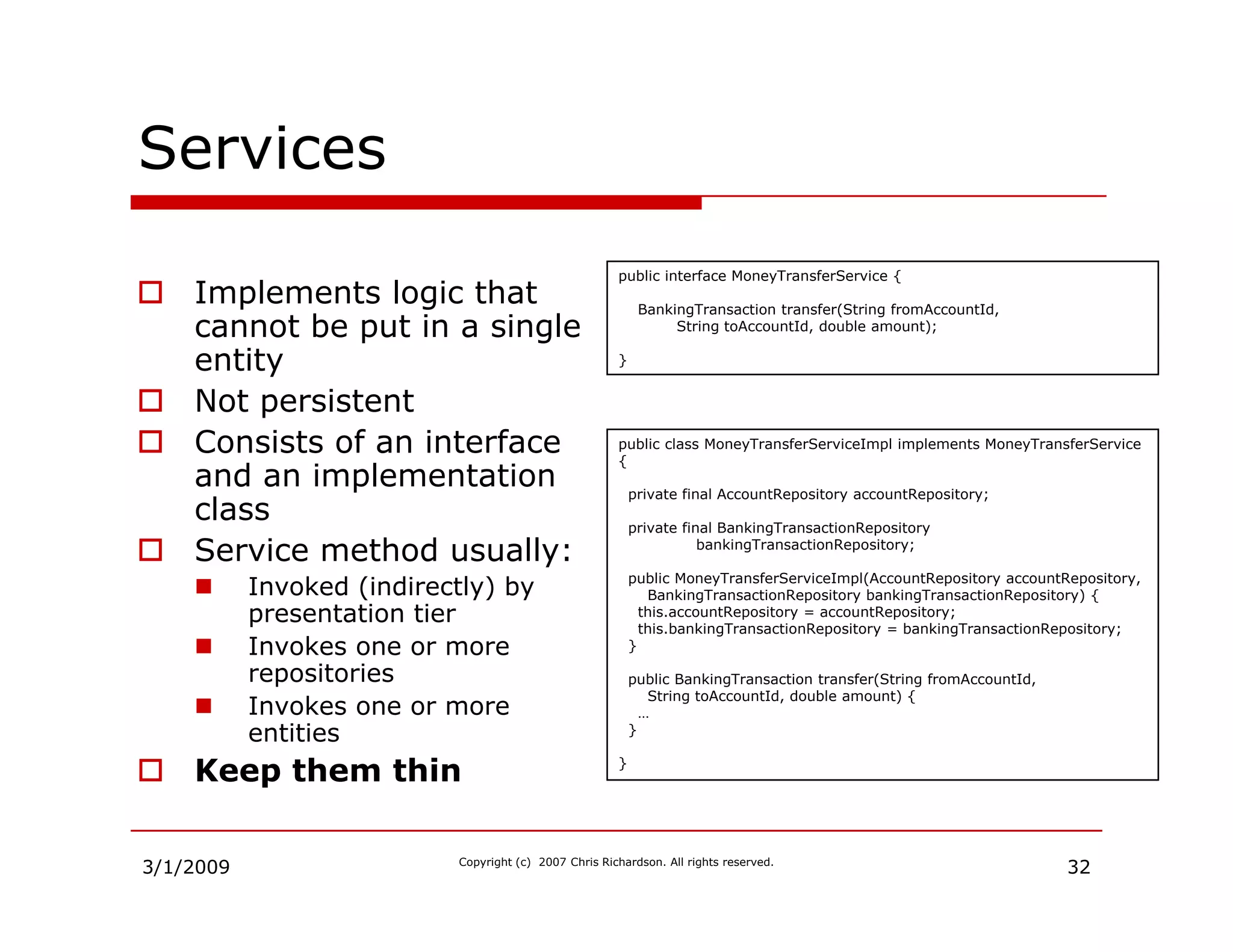
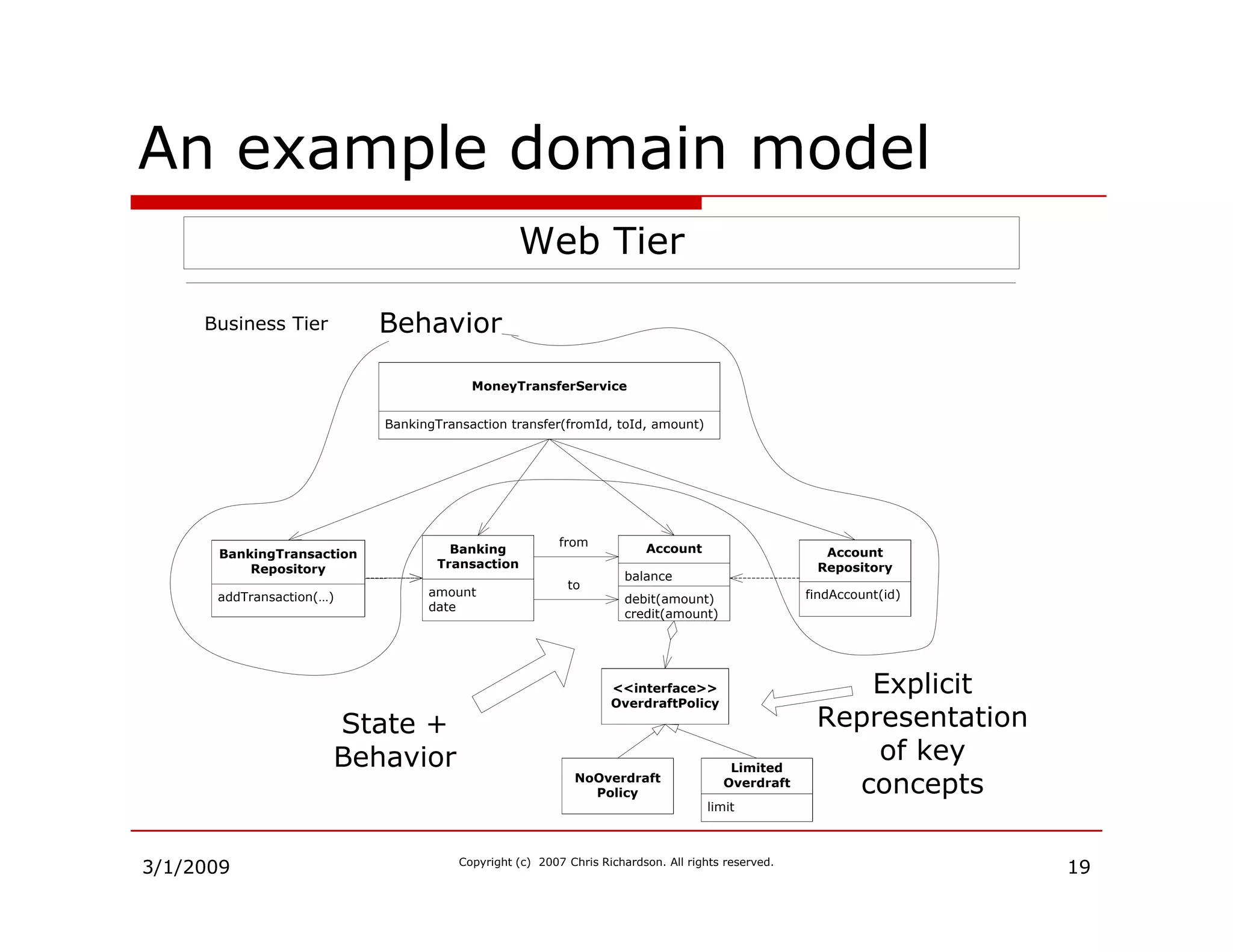
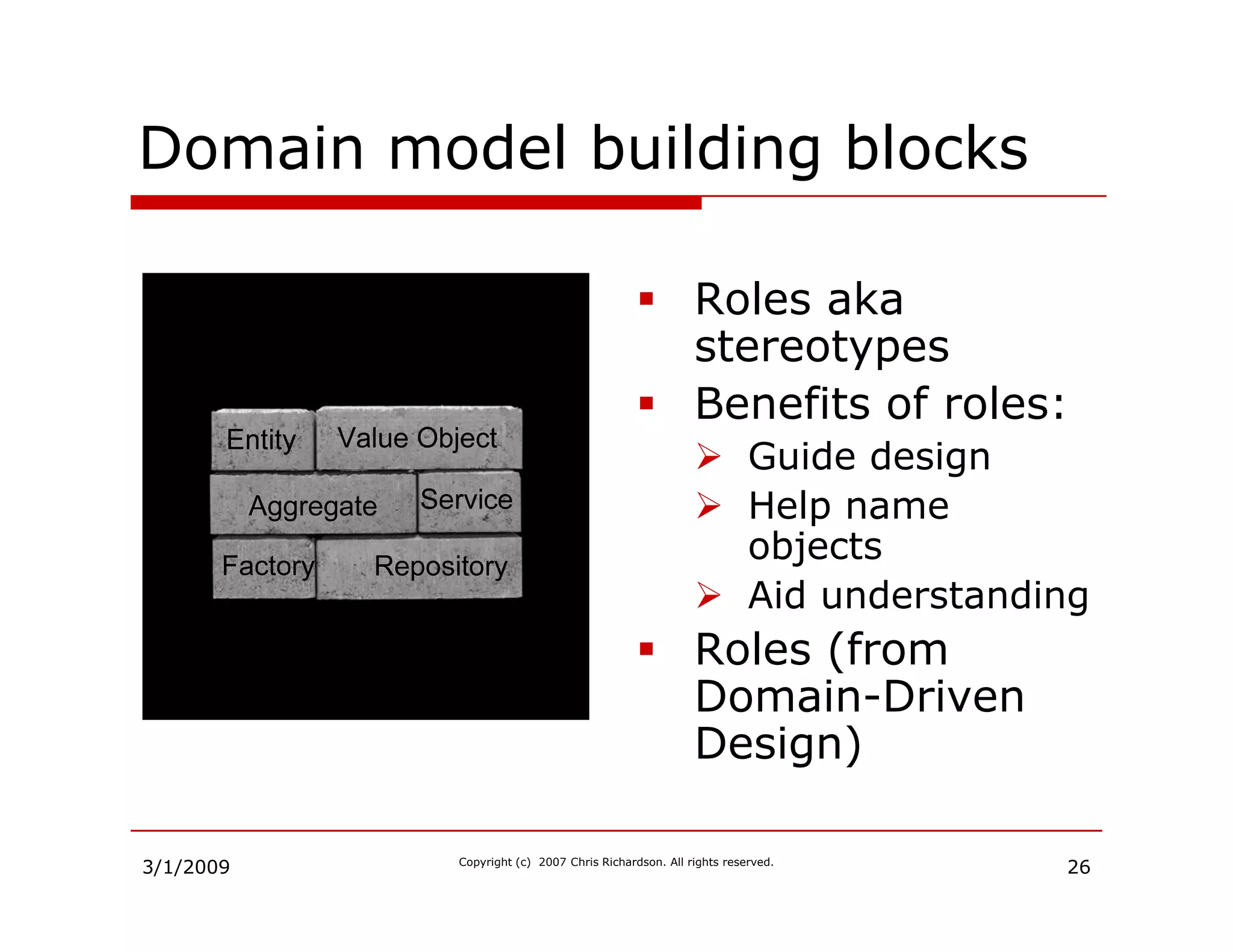
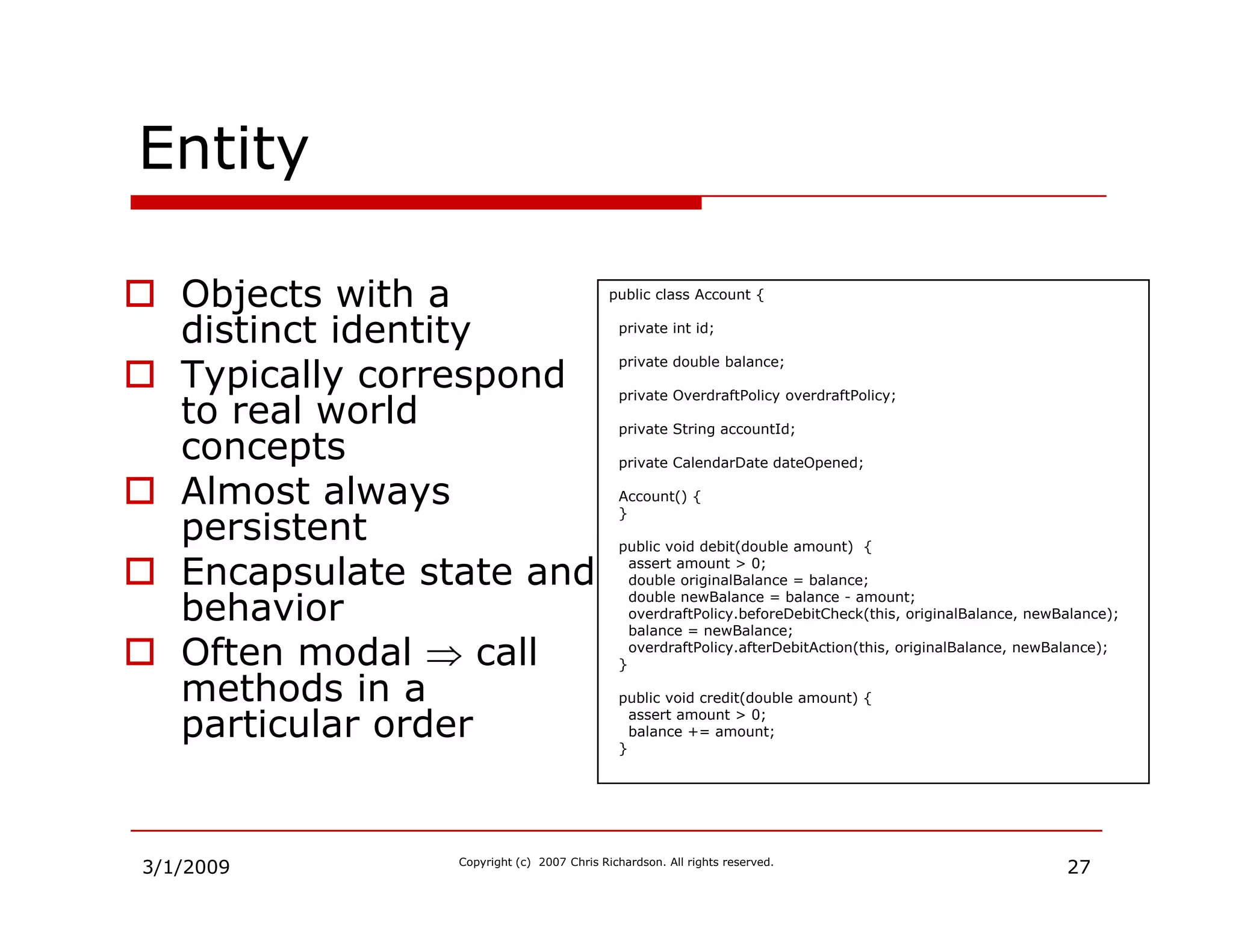
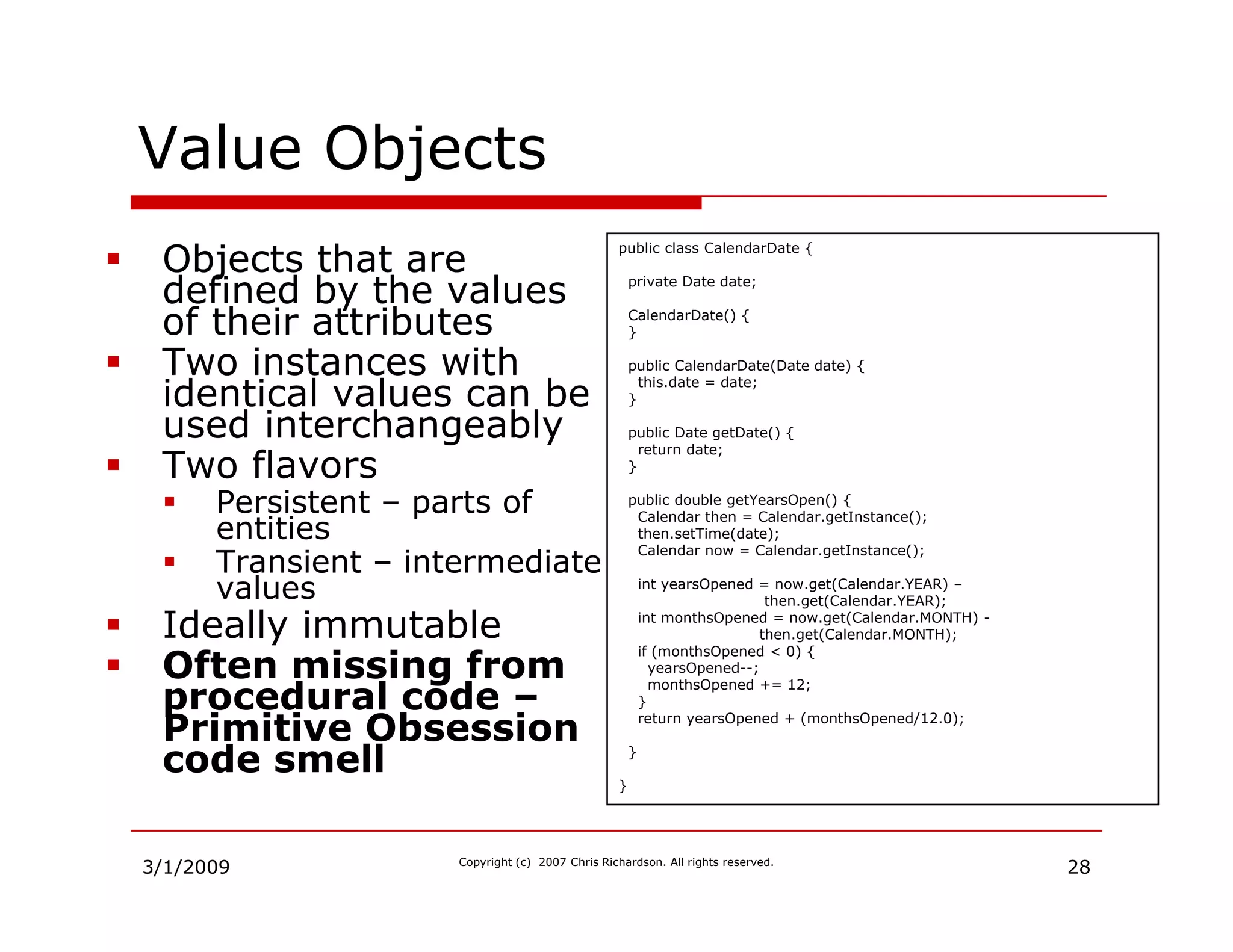
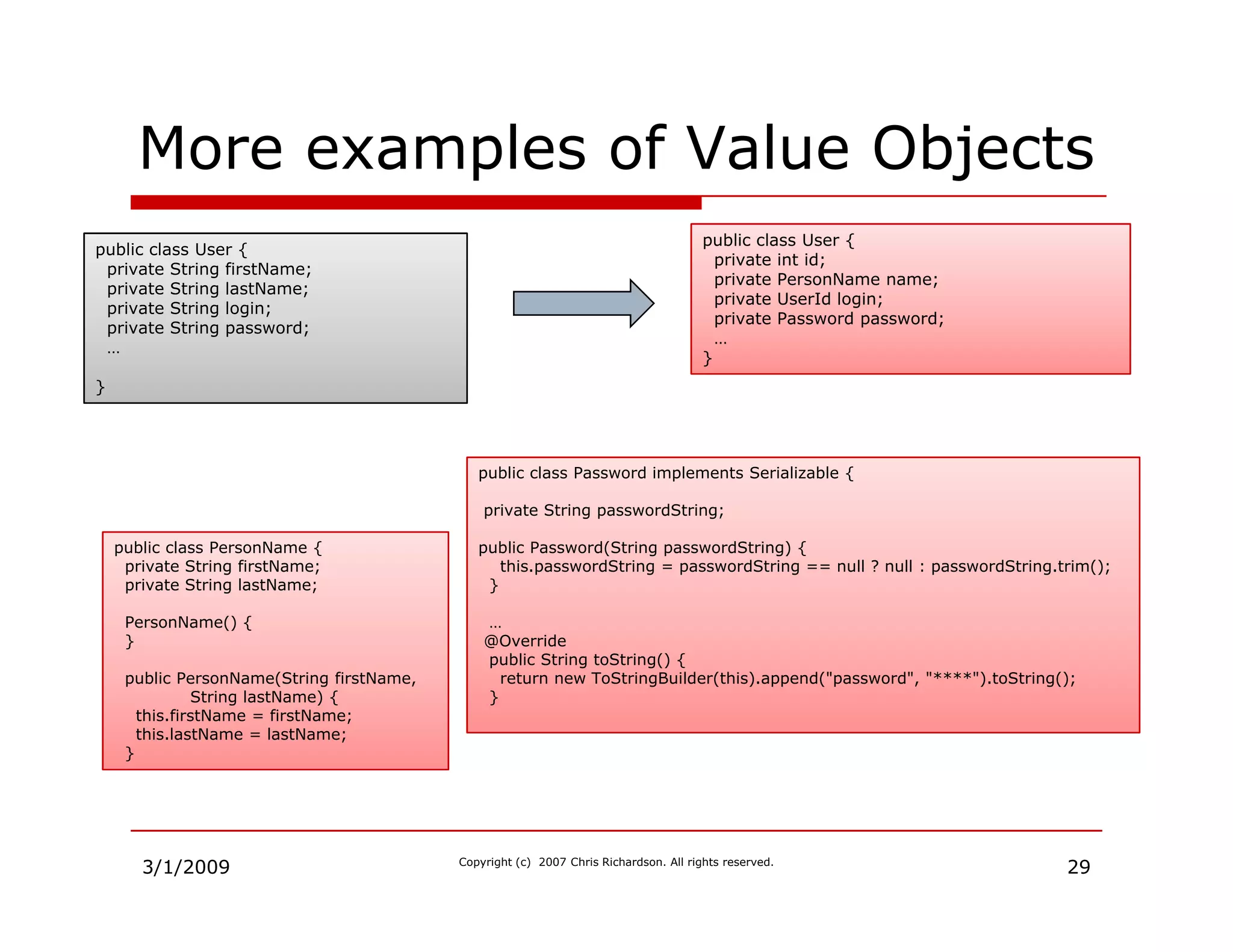
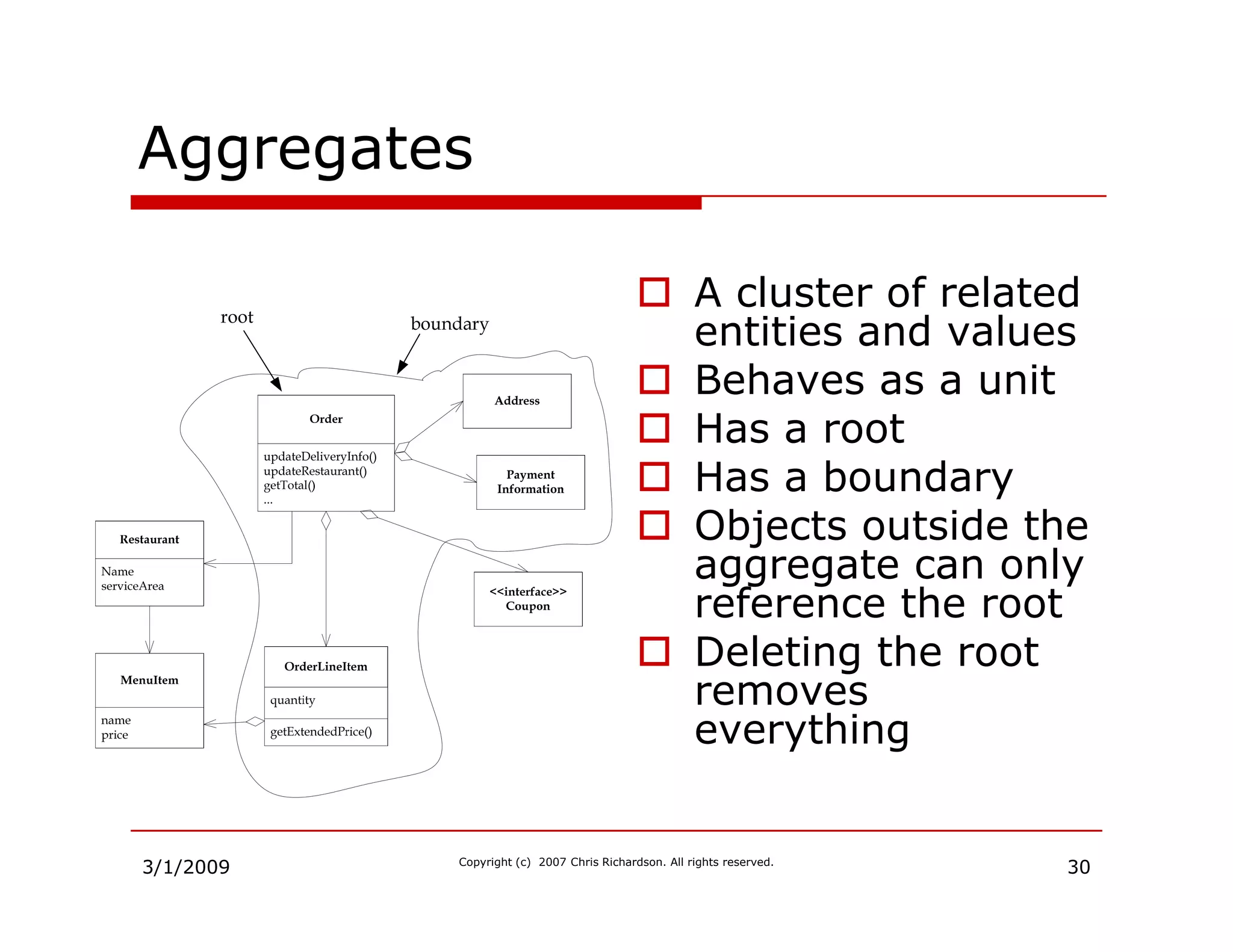
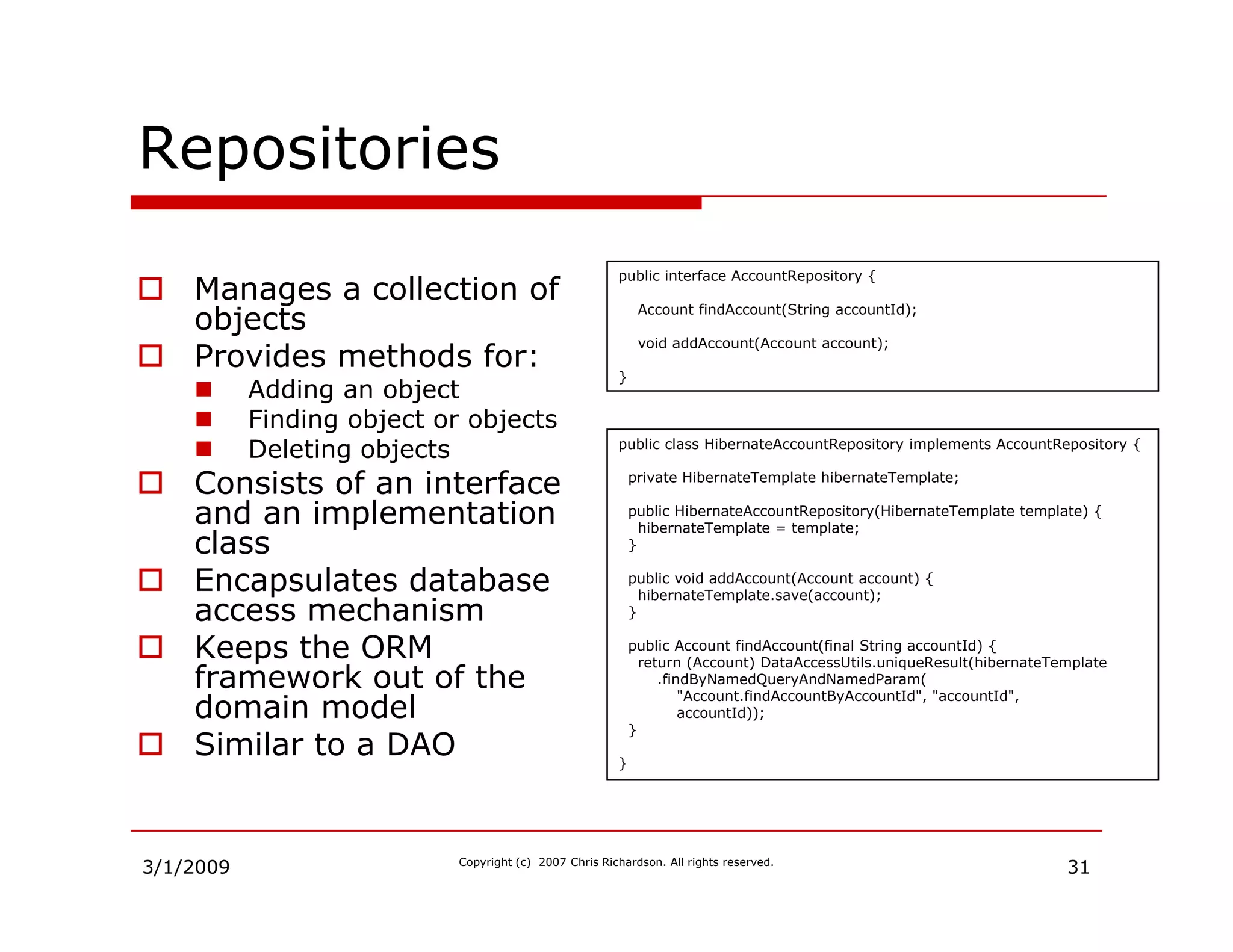
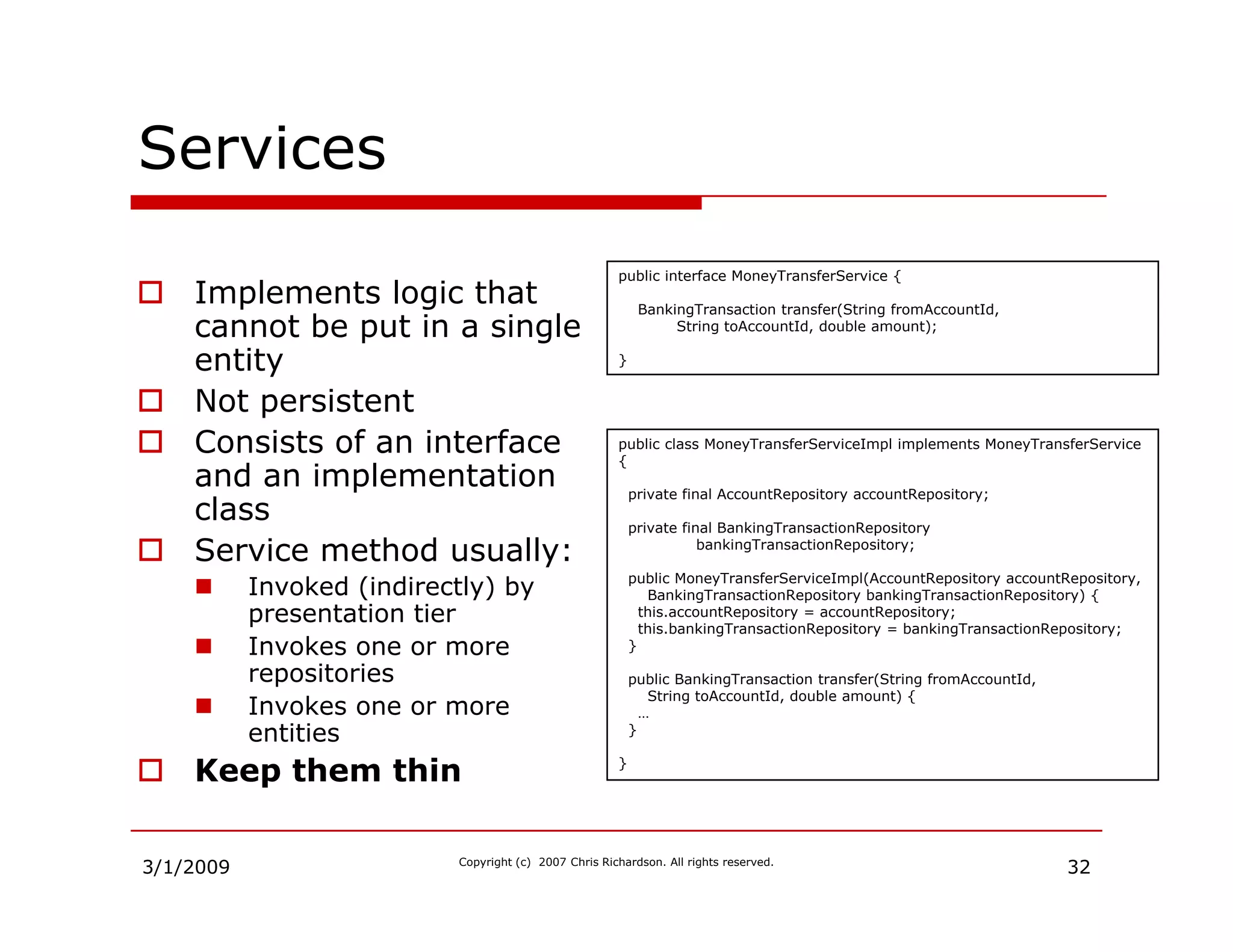
Explains roles, entities, value objects, aggregates, repositories, and services within a domain model.
Details the service layer's role, including the use of factories for complex object creation.
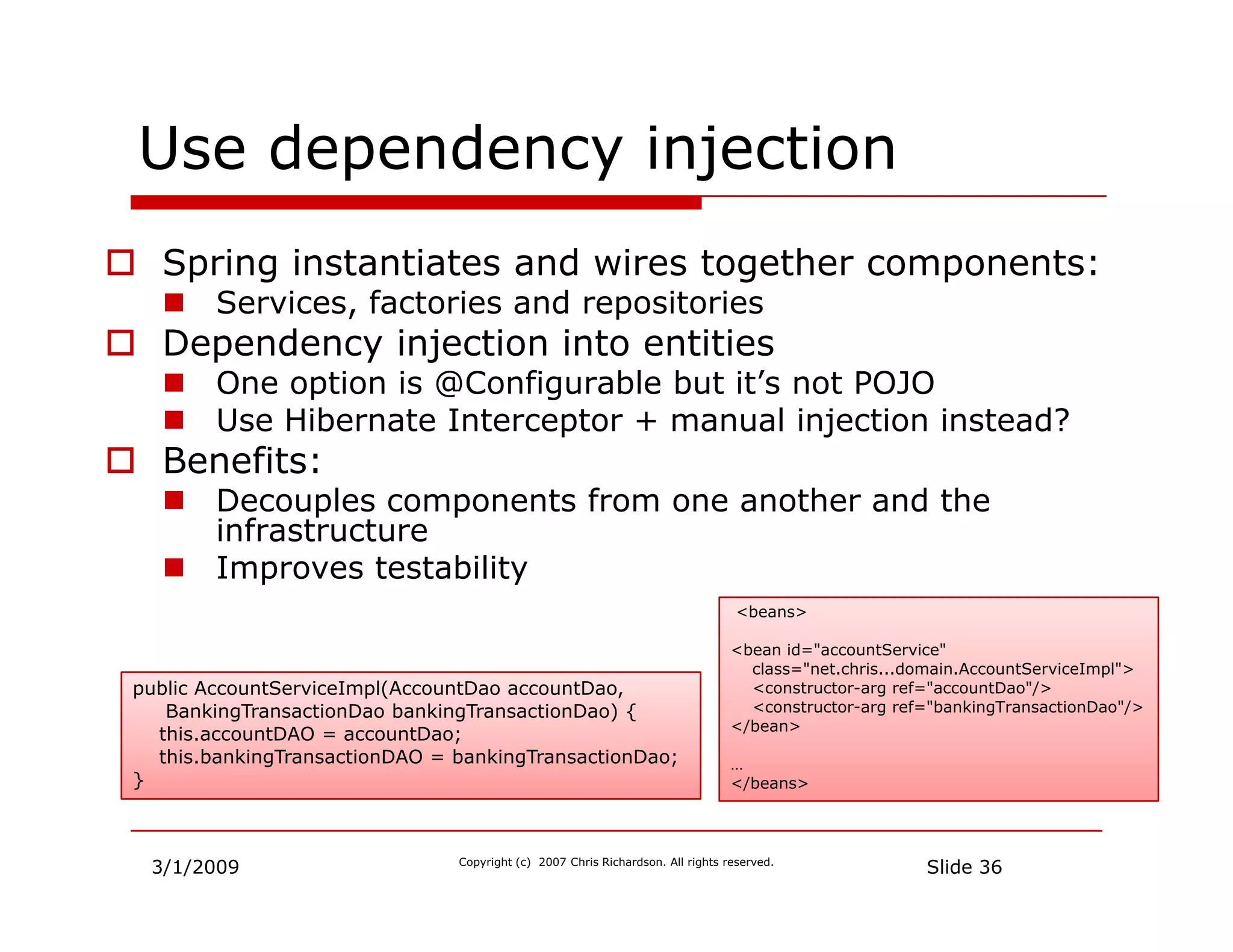
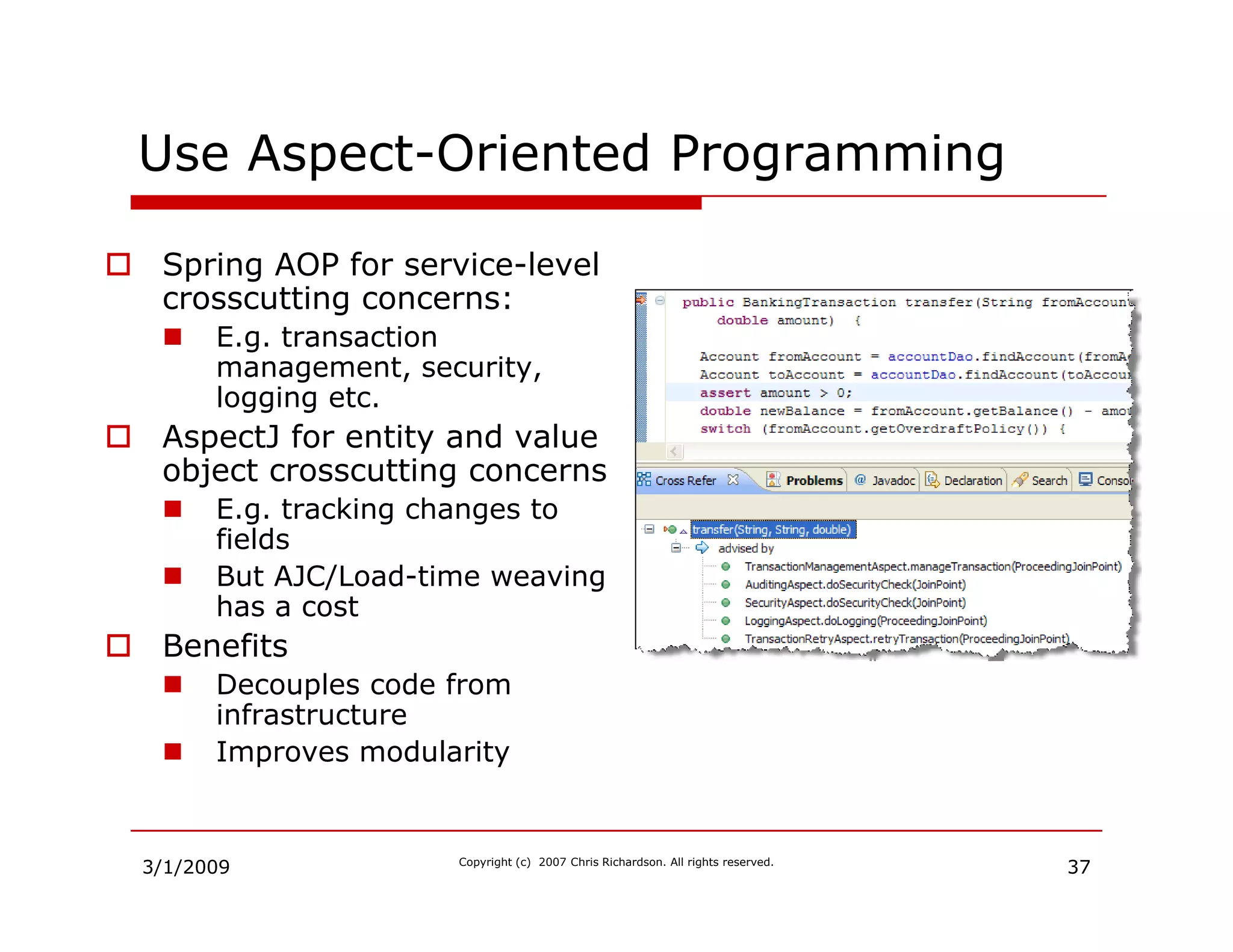
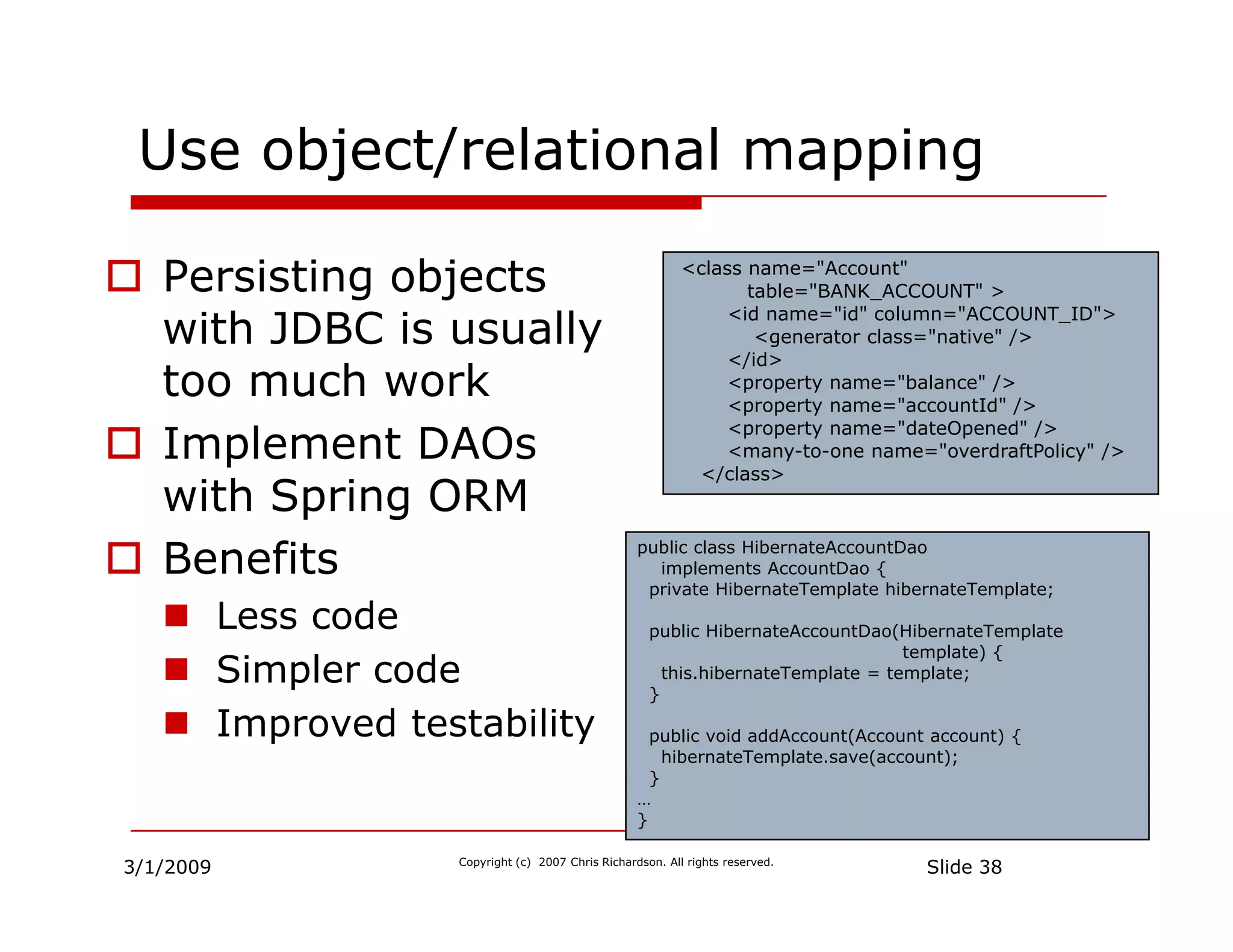
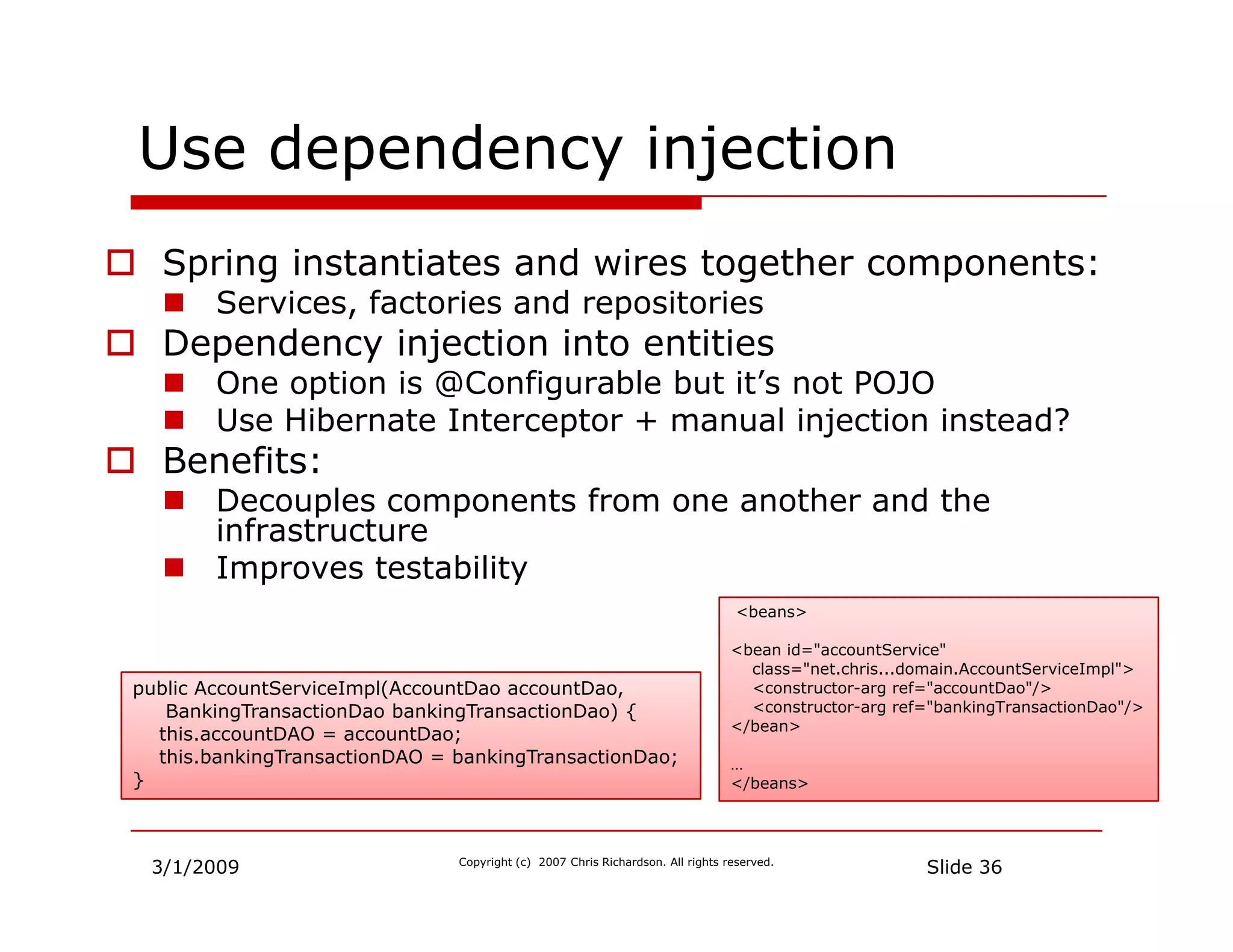
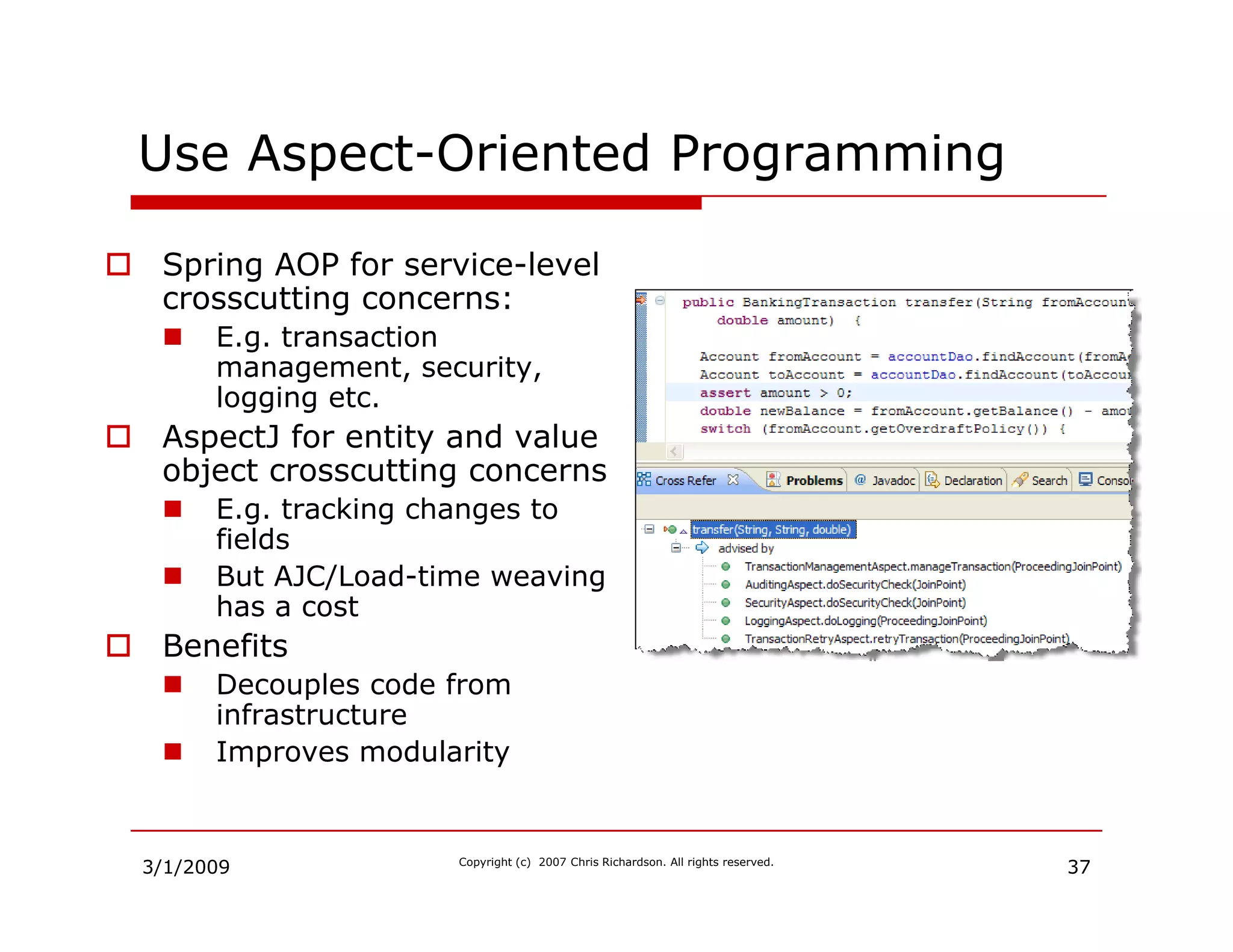
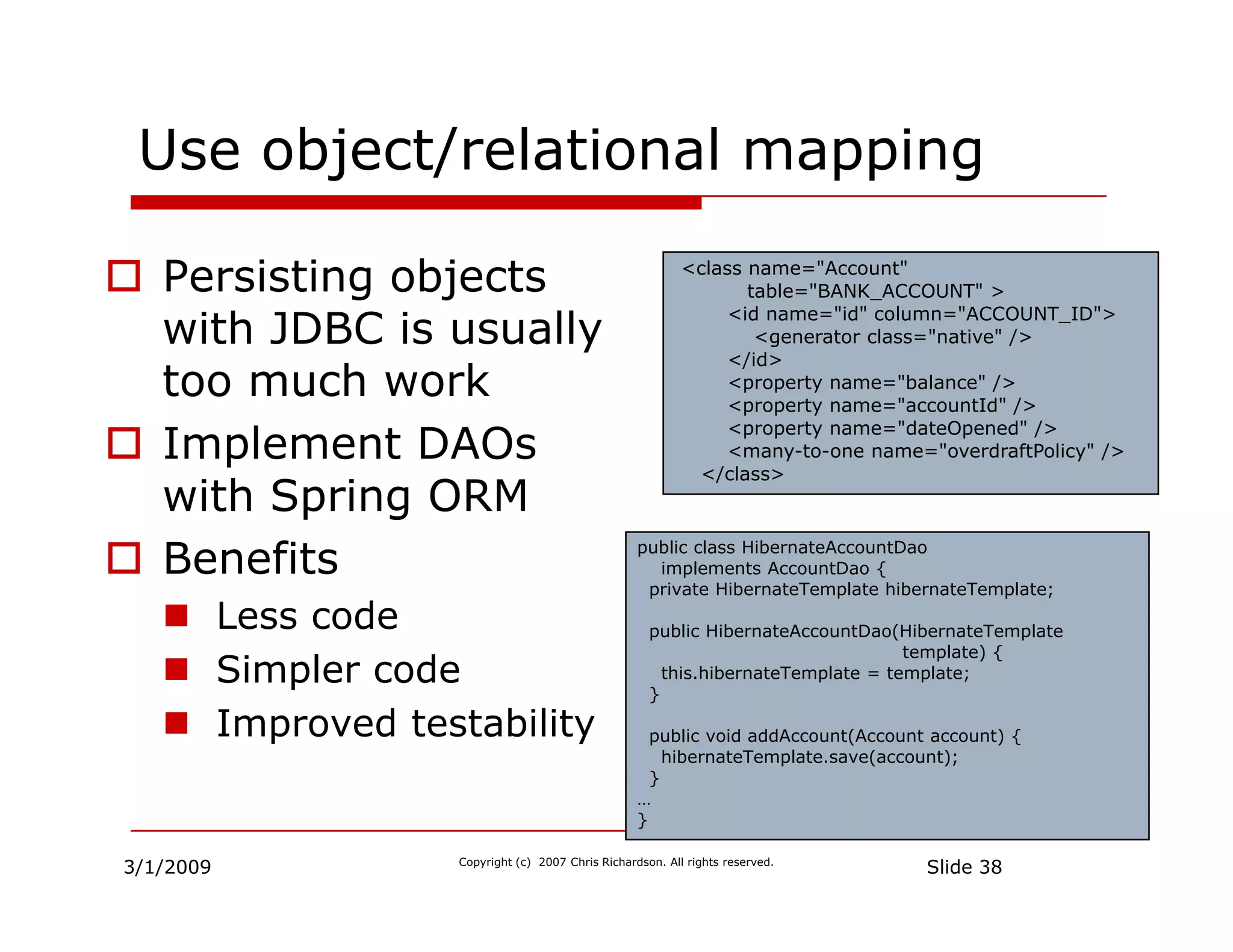
The importance of using POJOs, dependency injection, and aspect-oriented programming in modern applications.
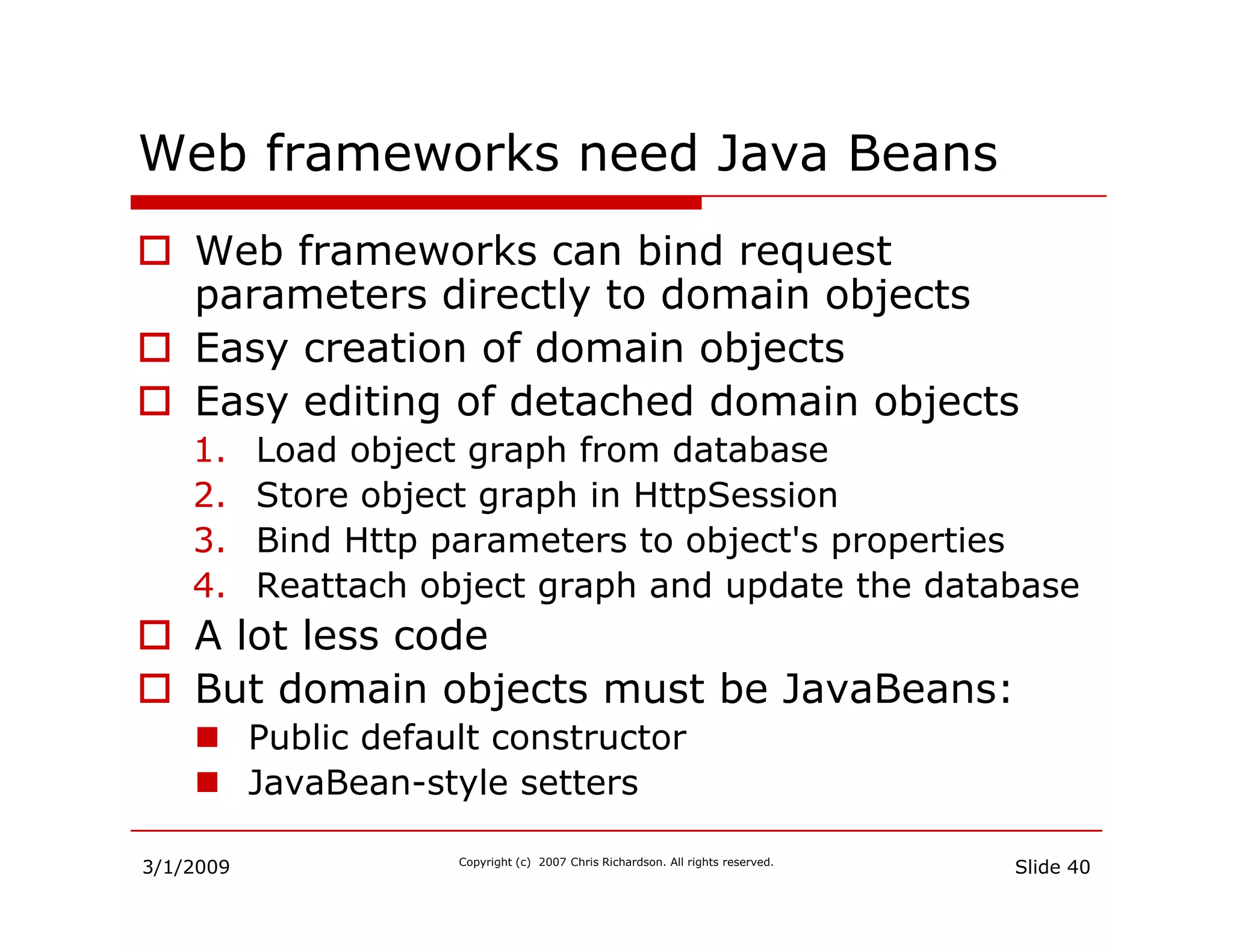
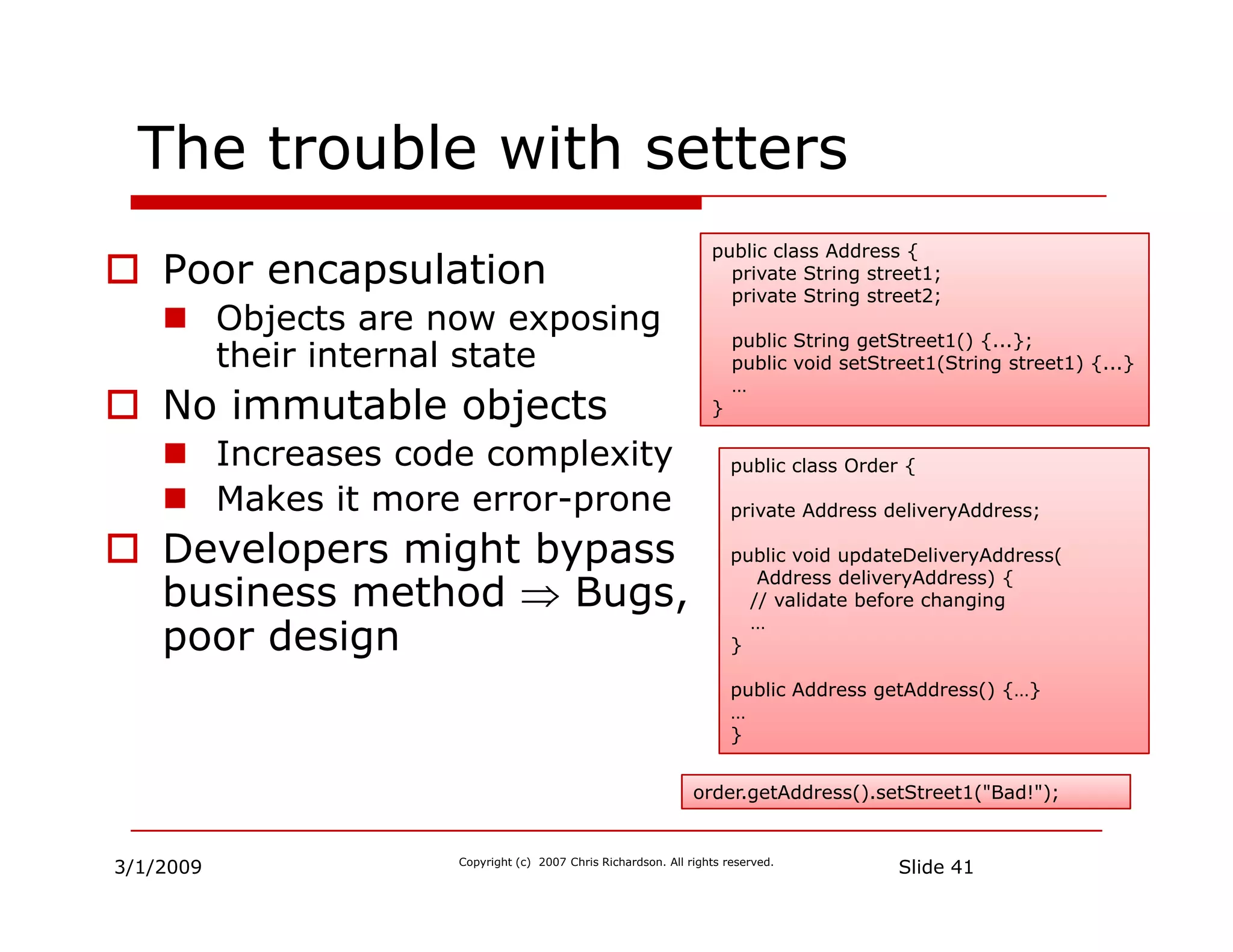
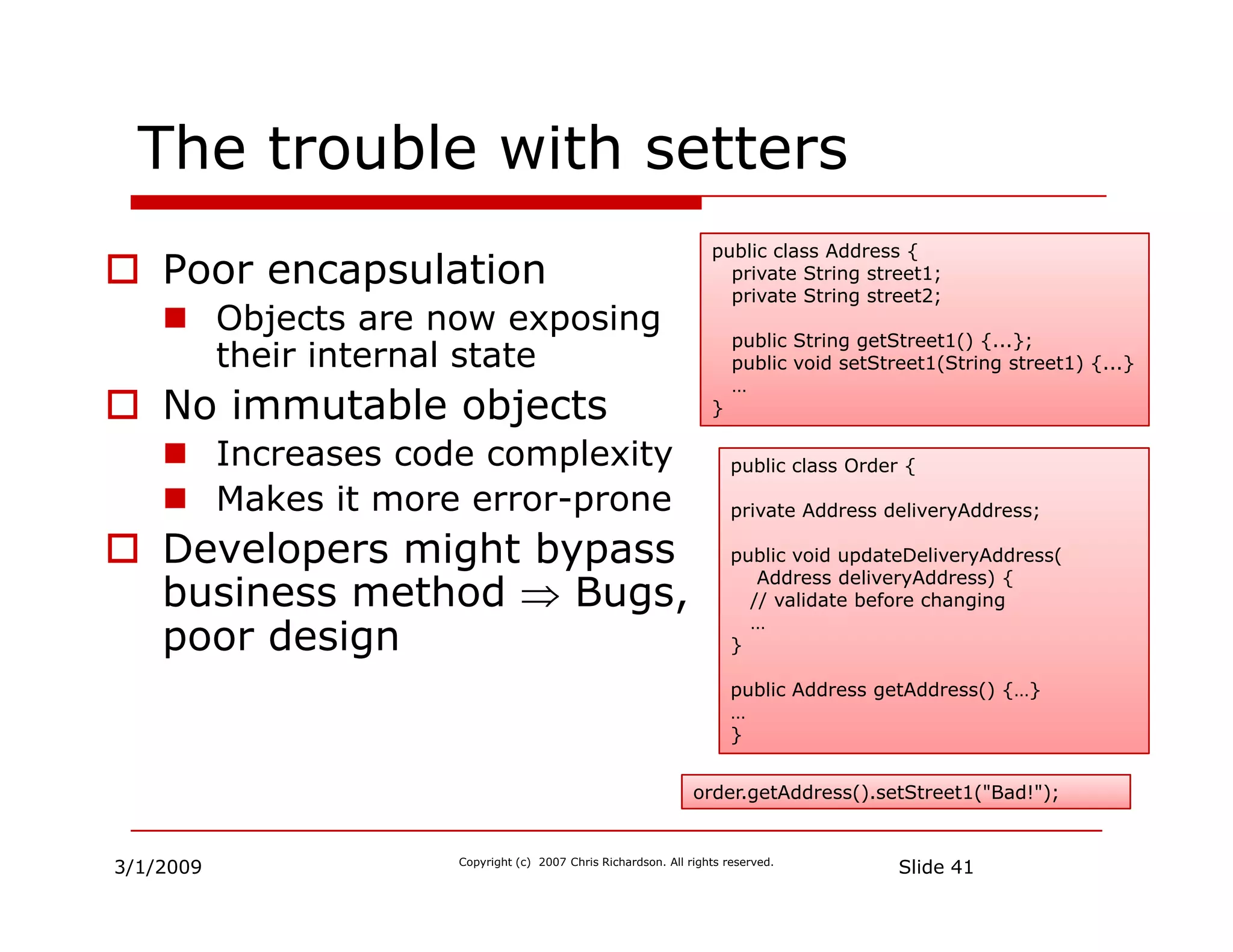
Discusses the need for JavaBeans in web frameworks and concerns regarding encapsulation and setters.
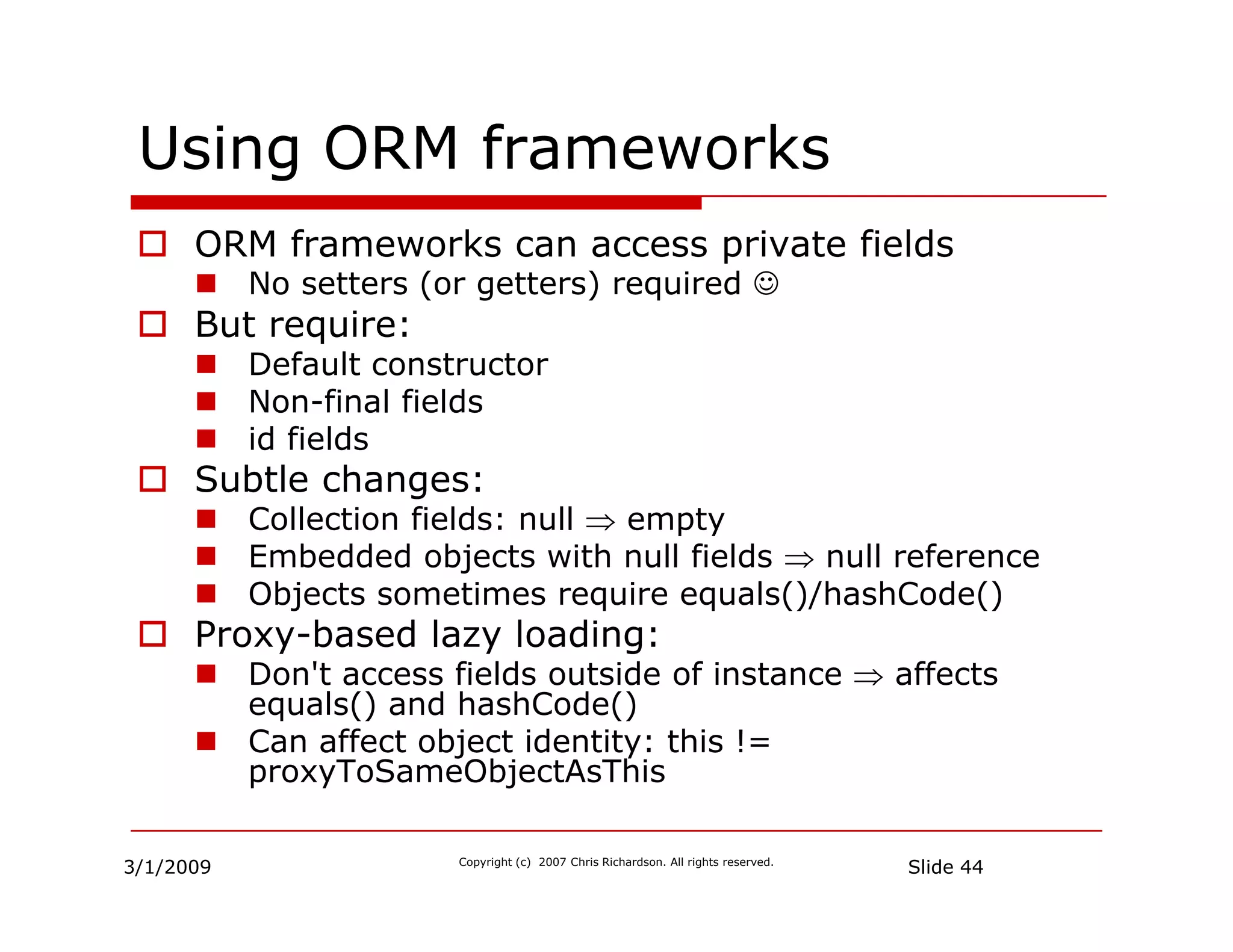
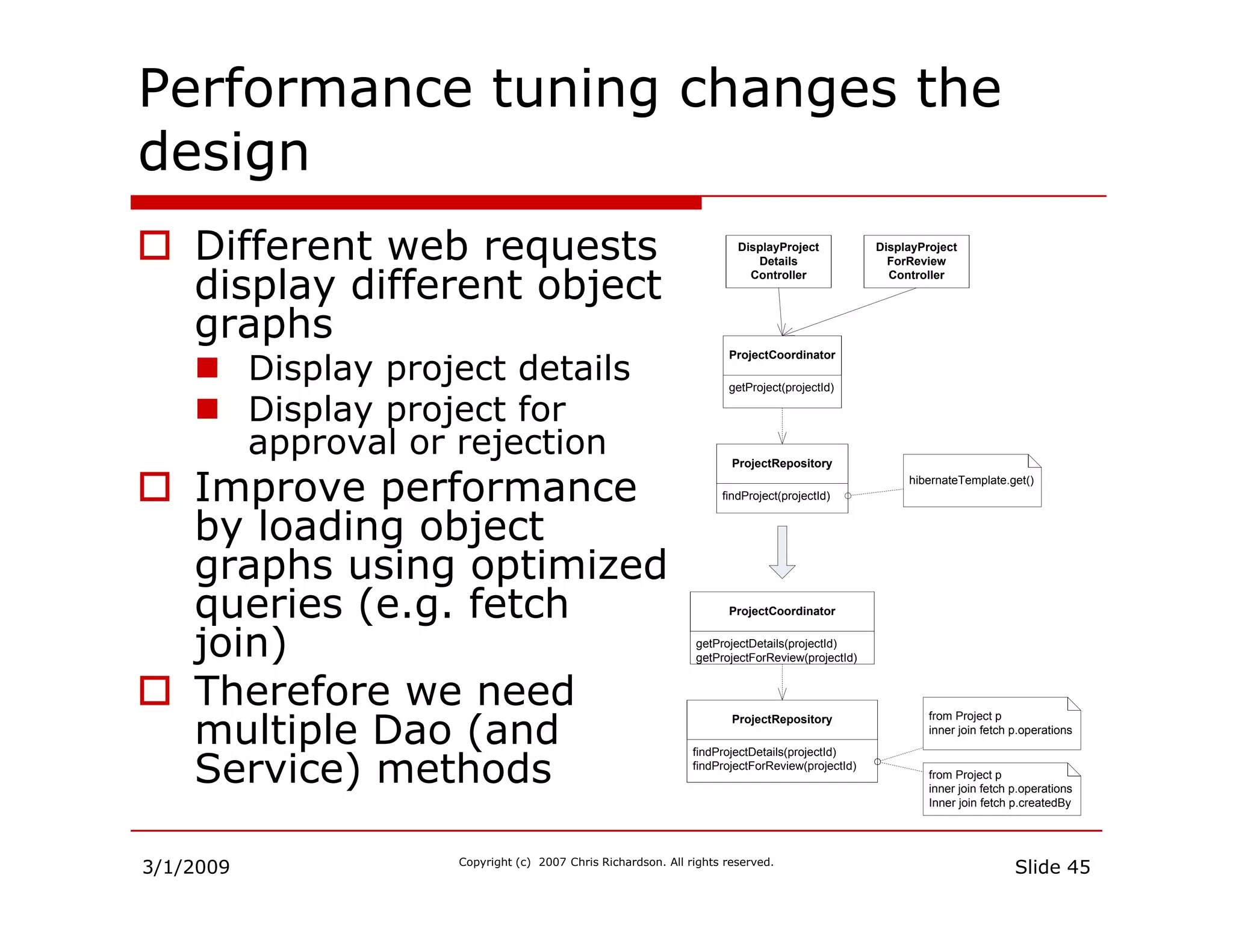
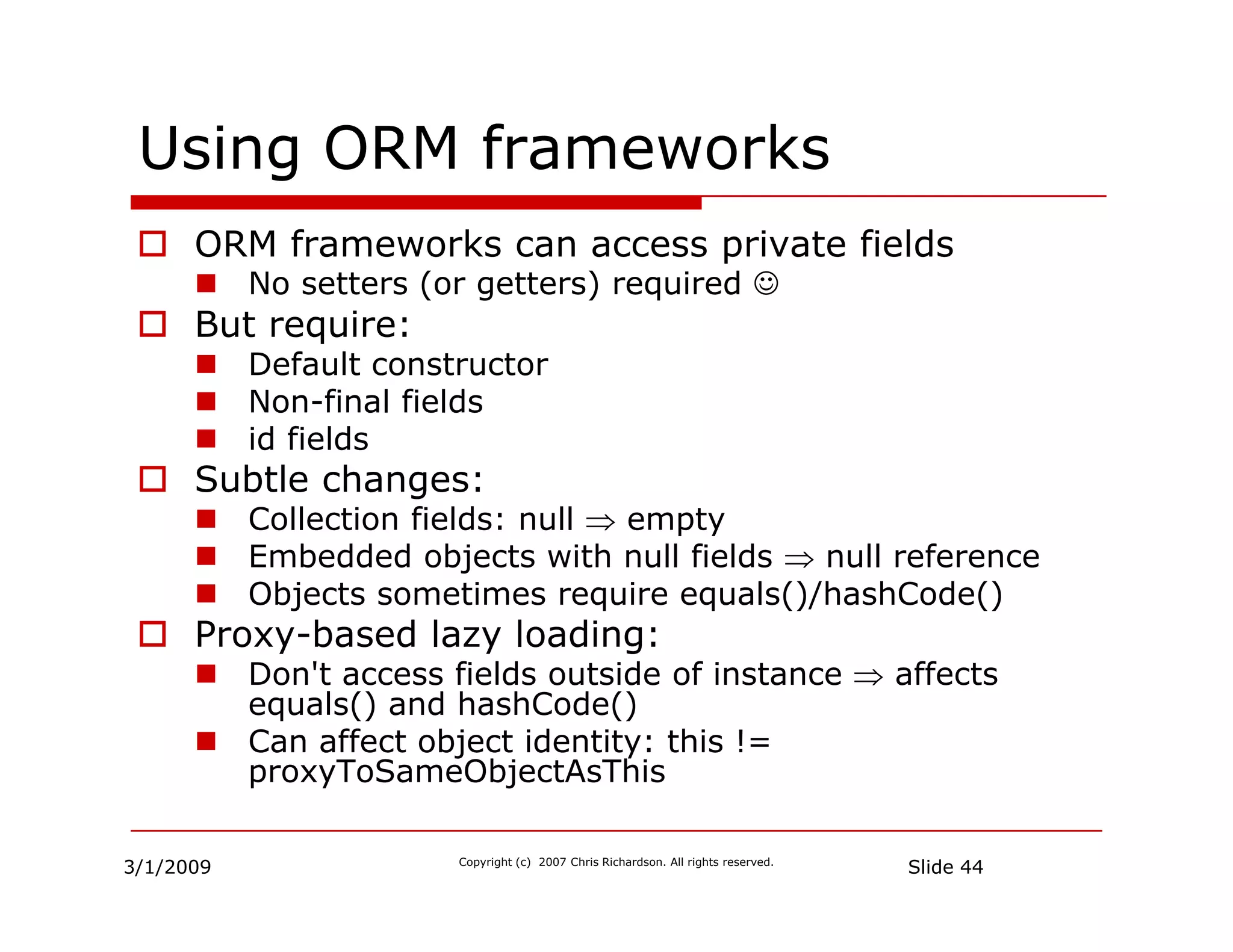
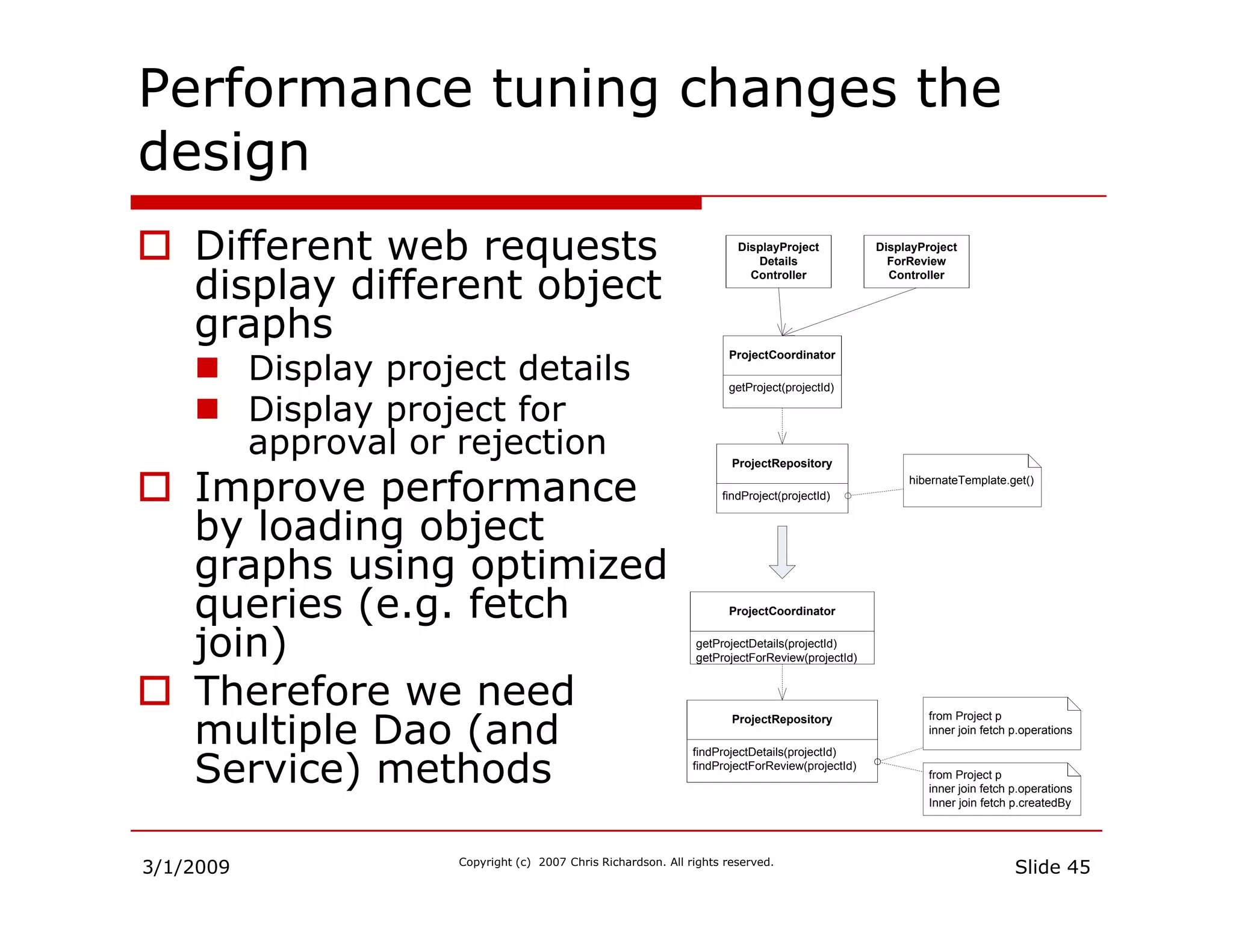
Addresses how ORM frameworks can affect performance and the importance of data loading strategies.
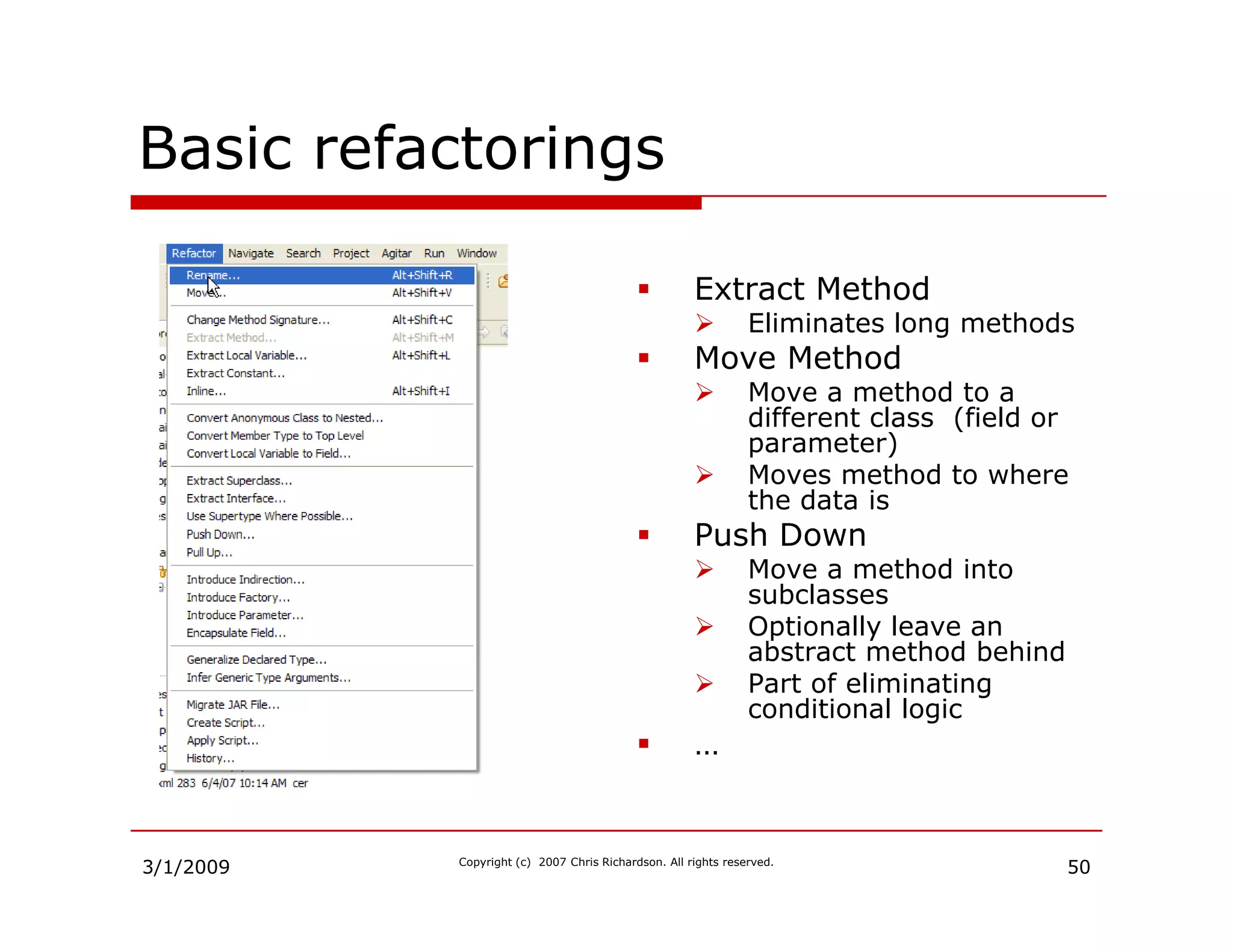
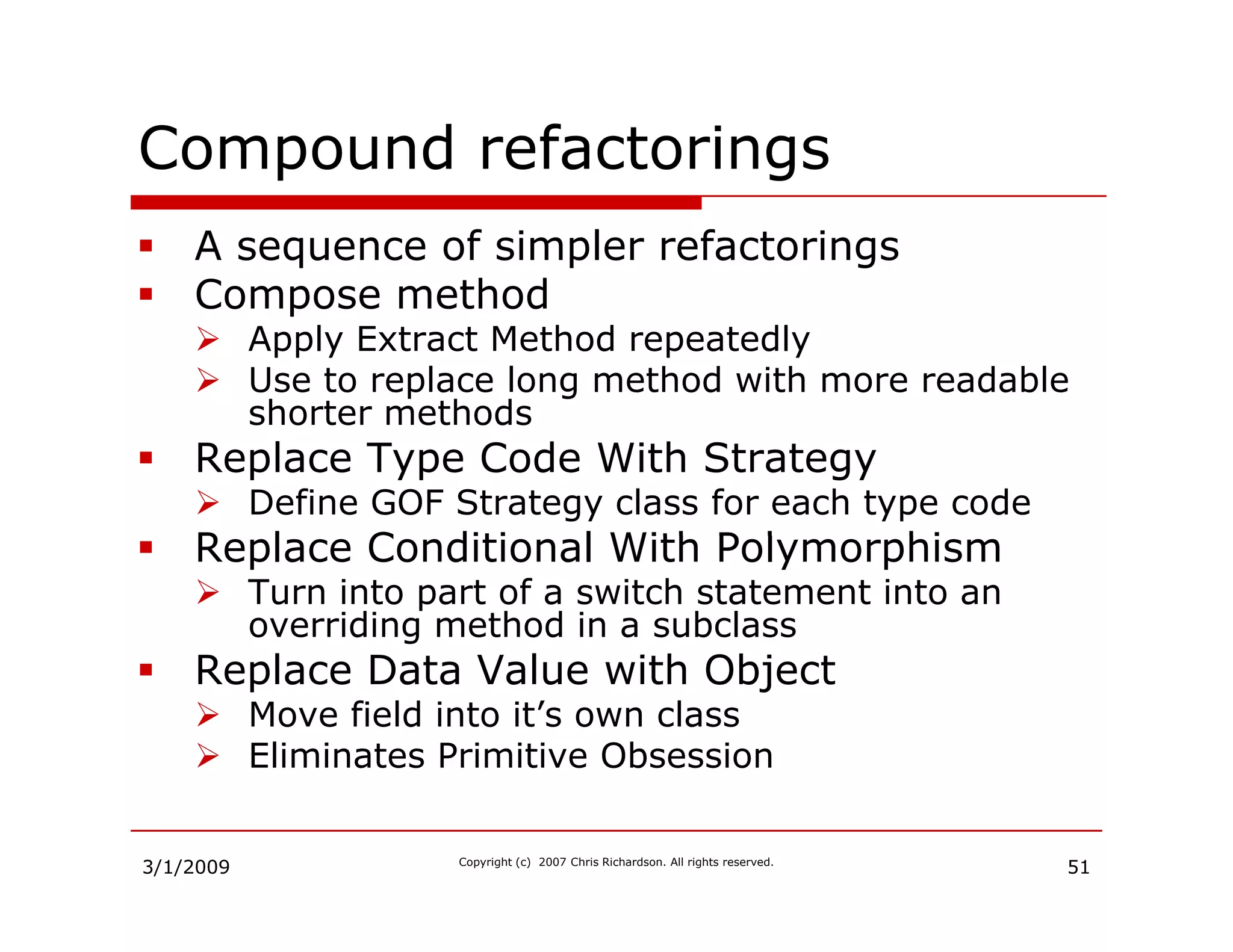
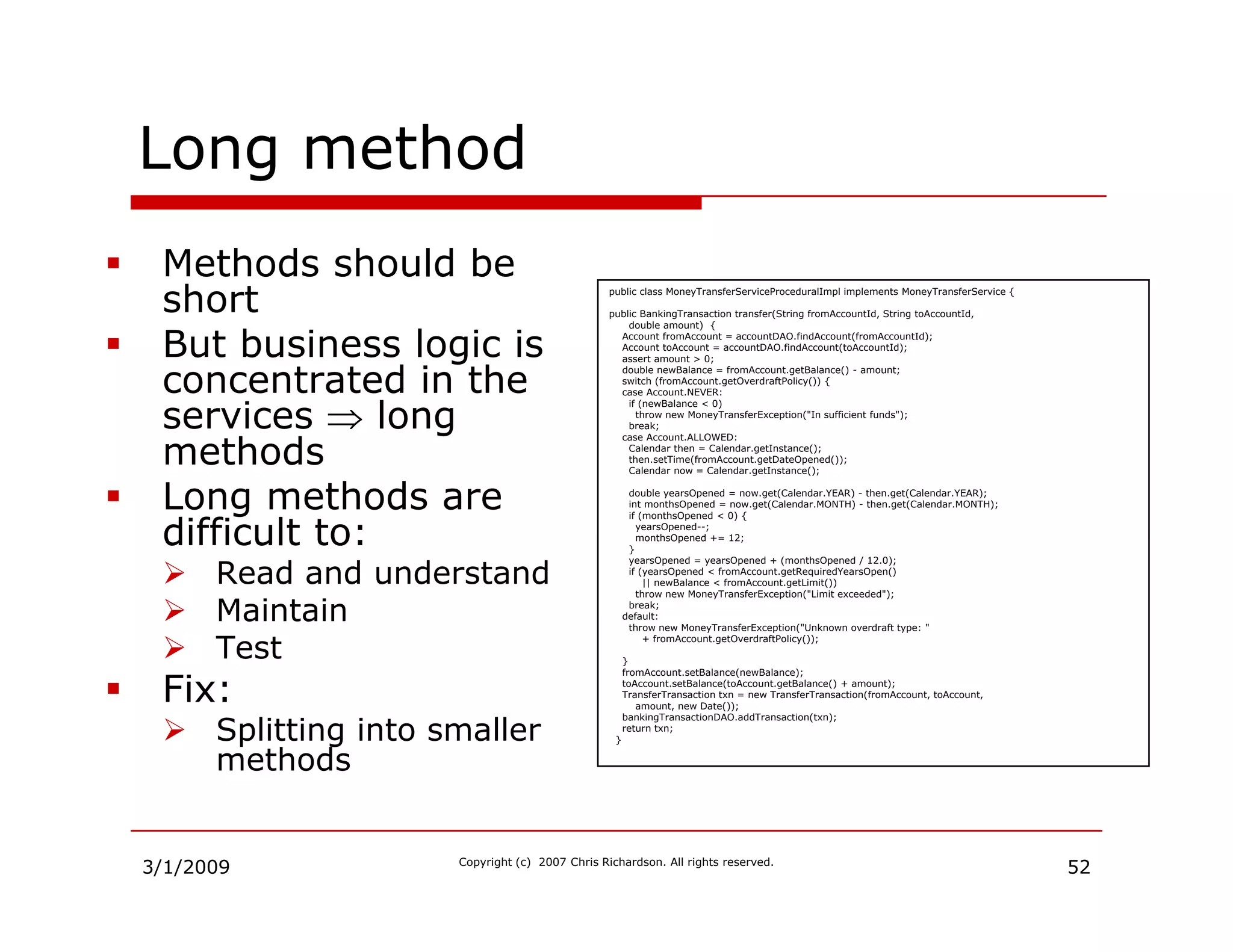
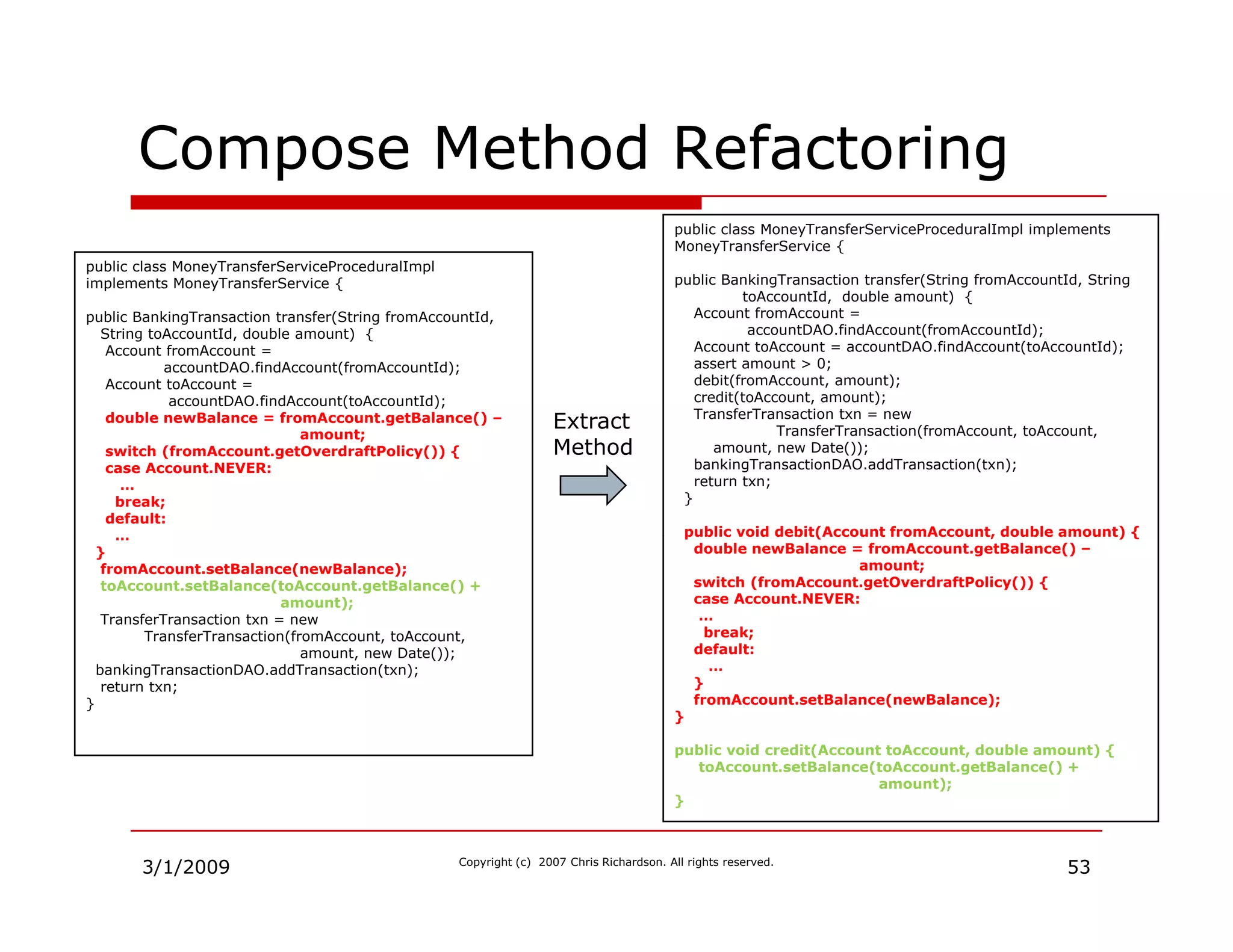
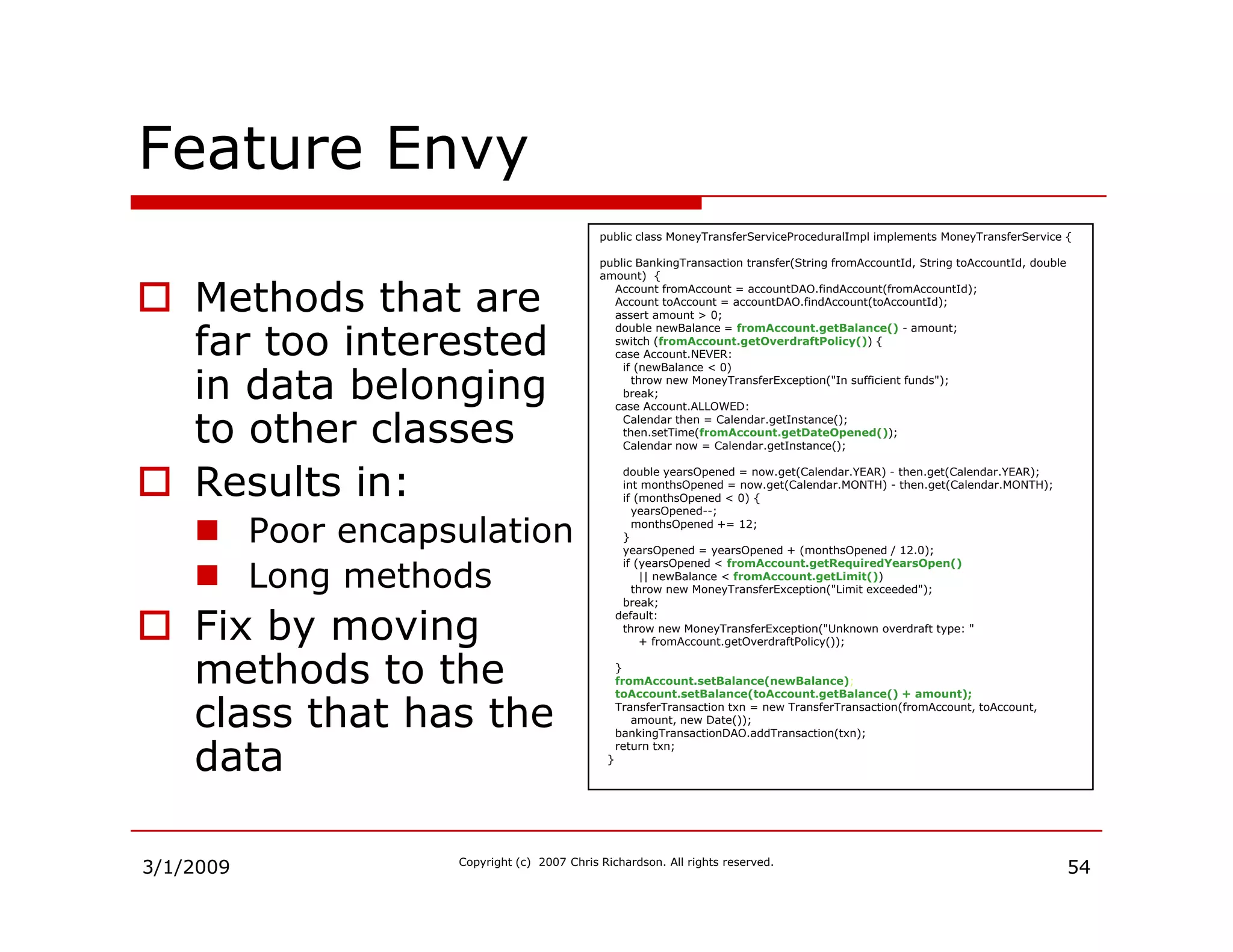
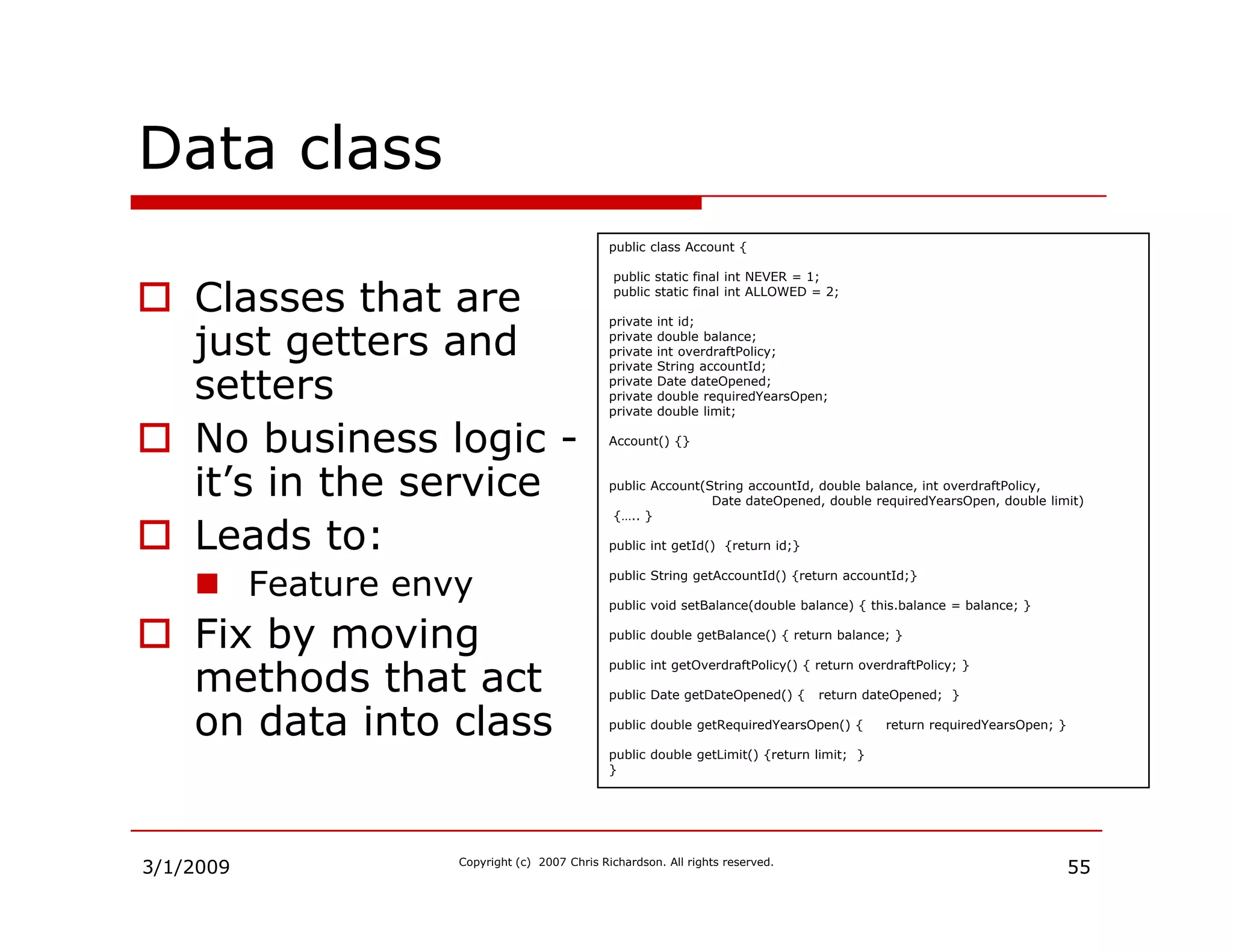
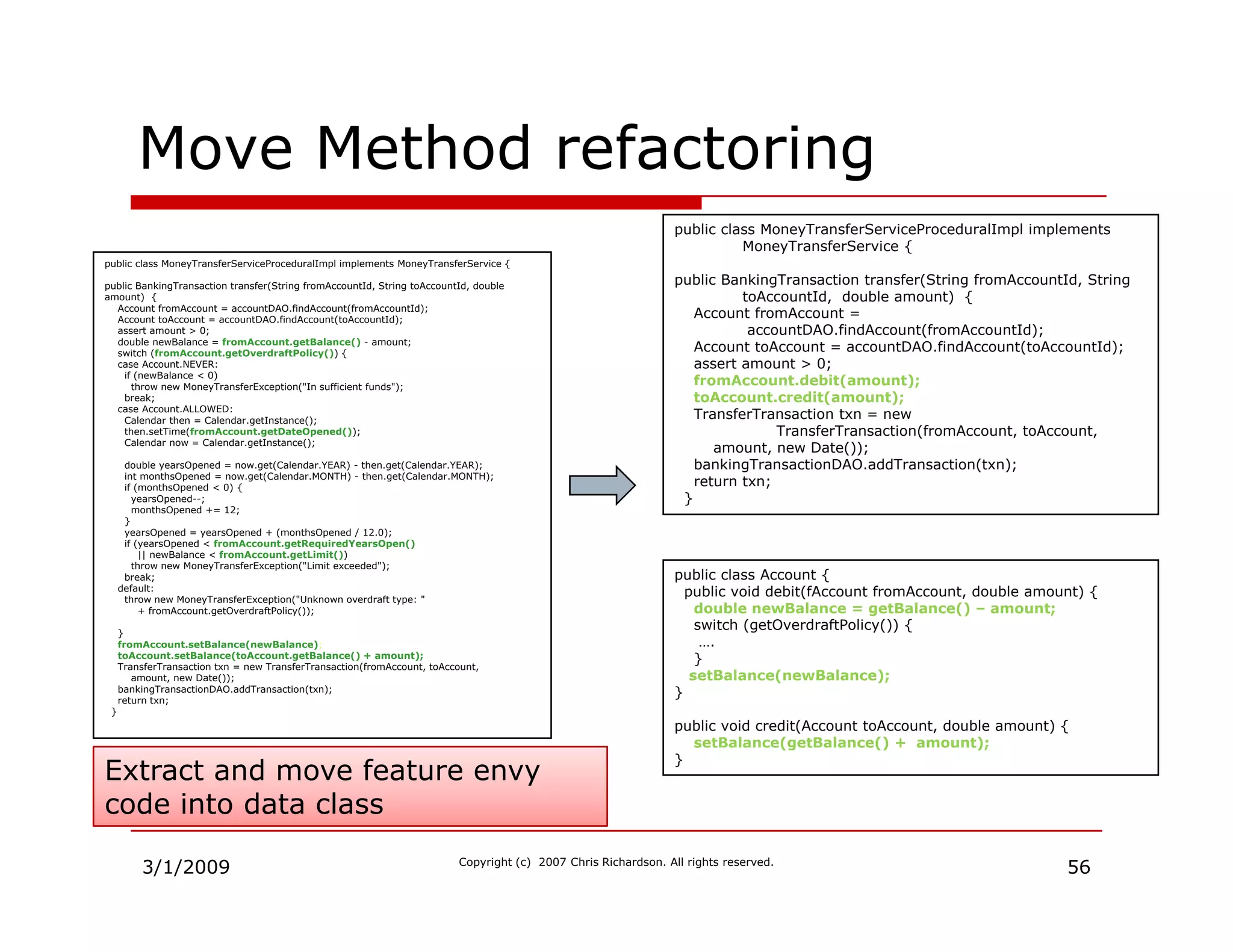
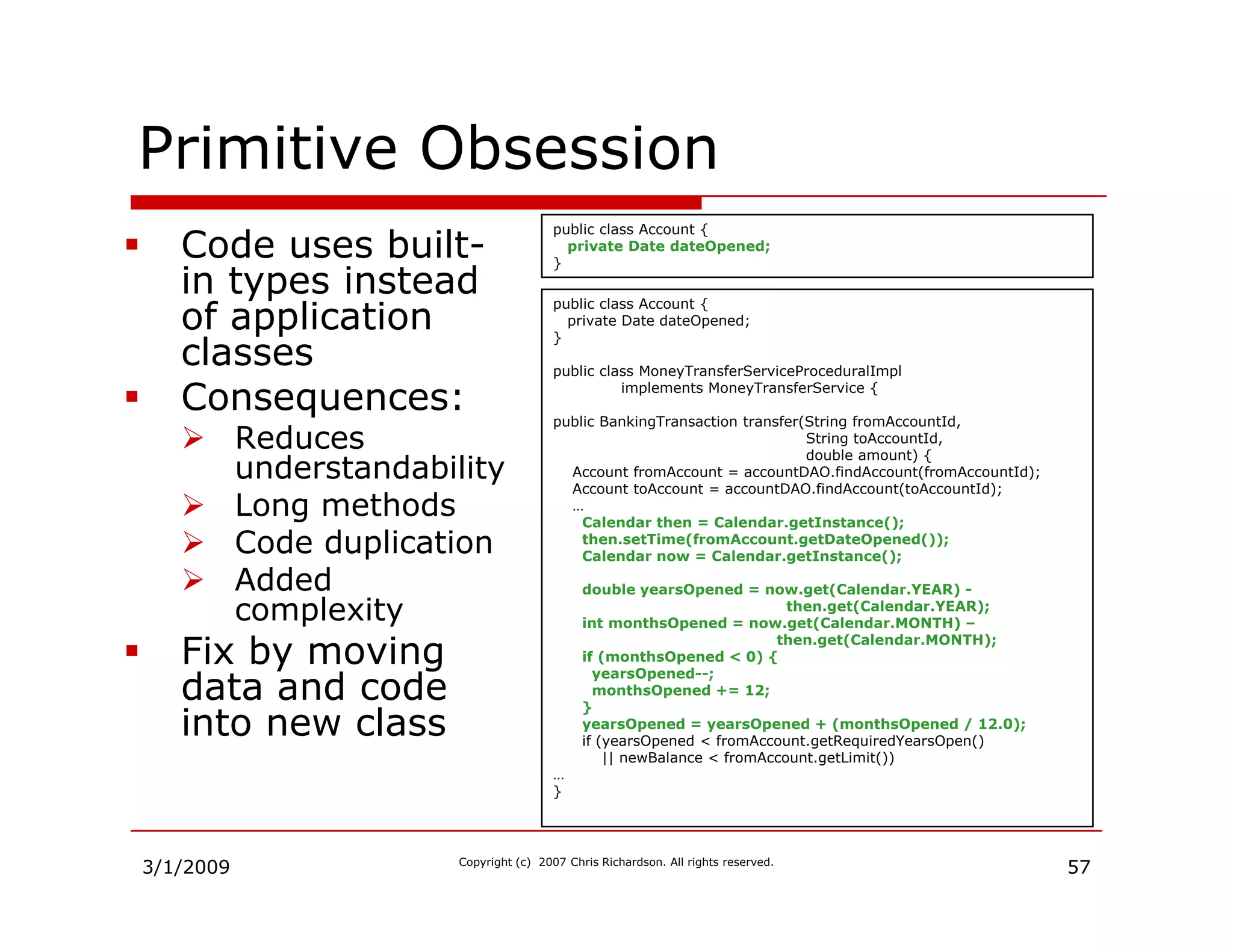
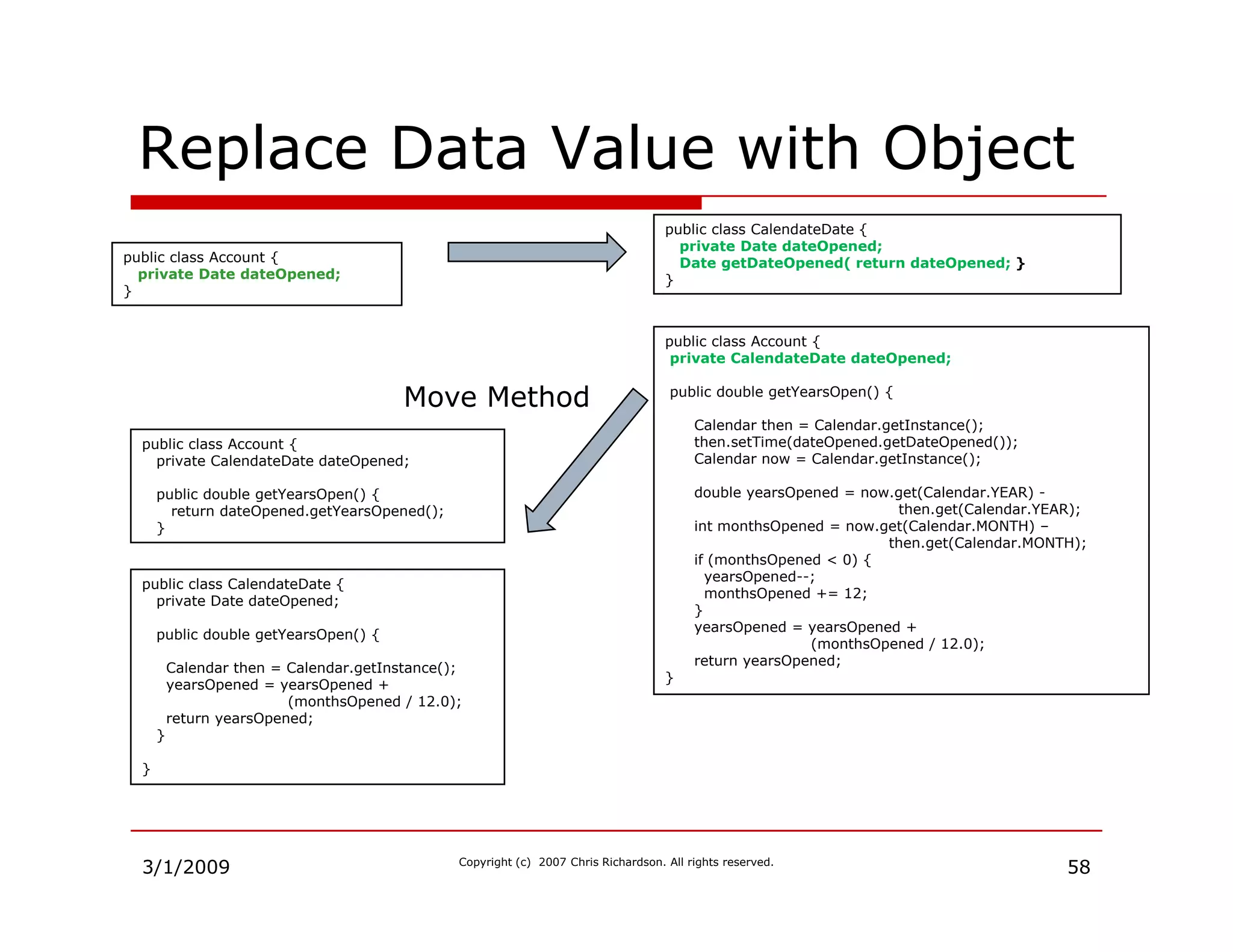
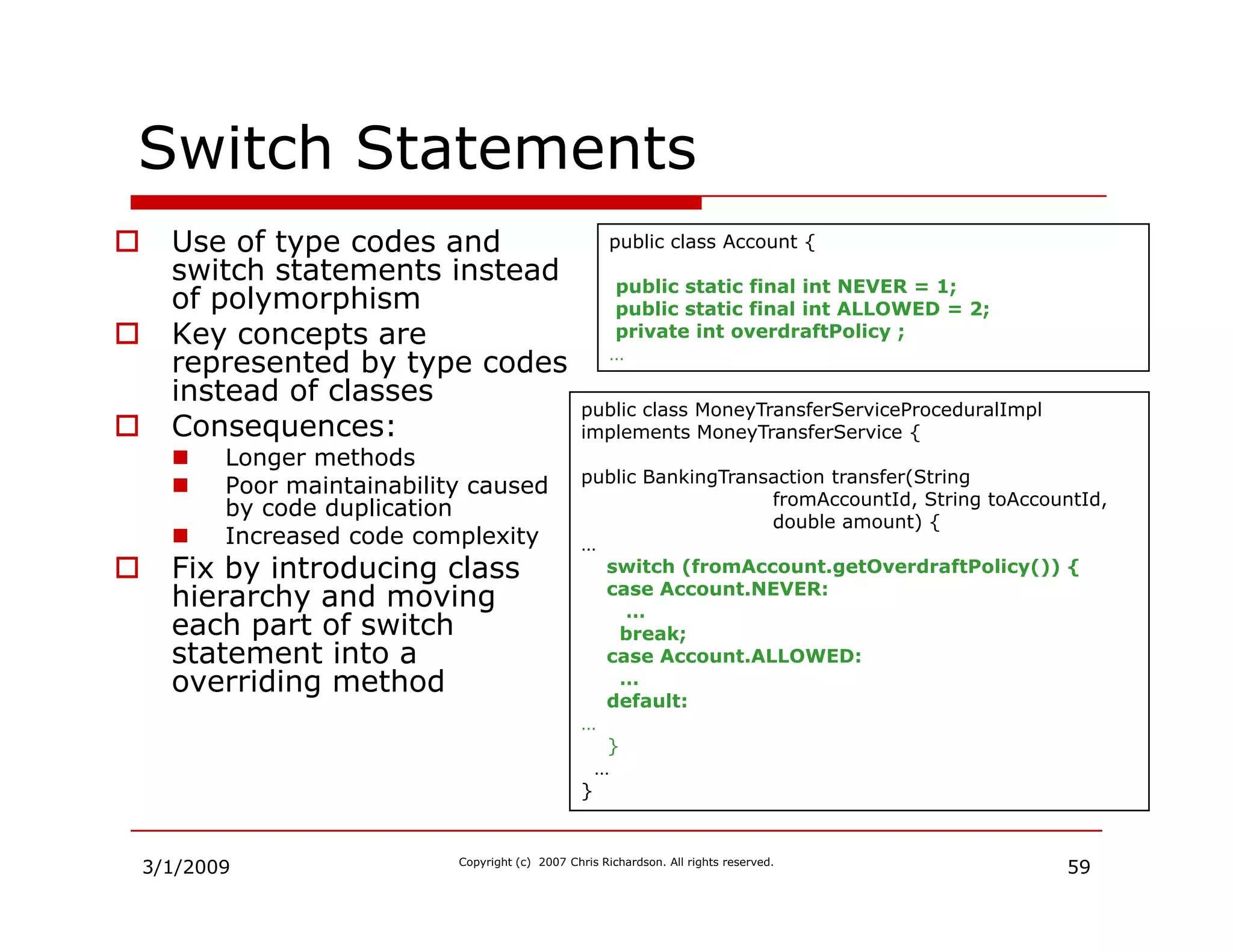
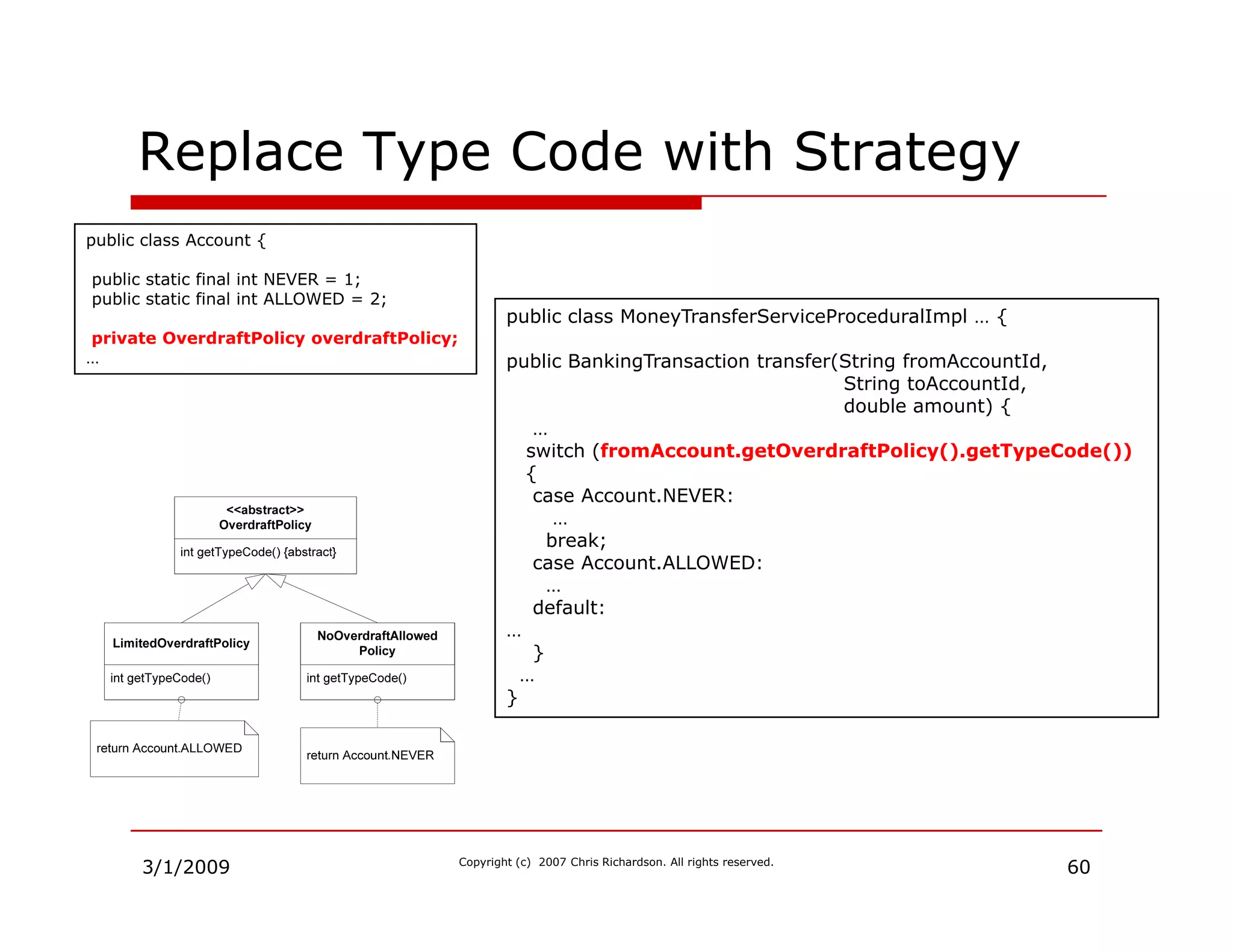
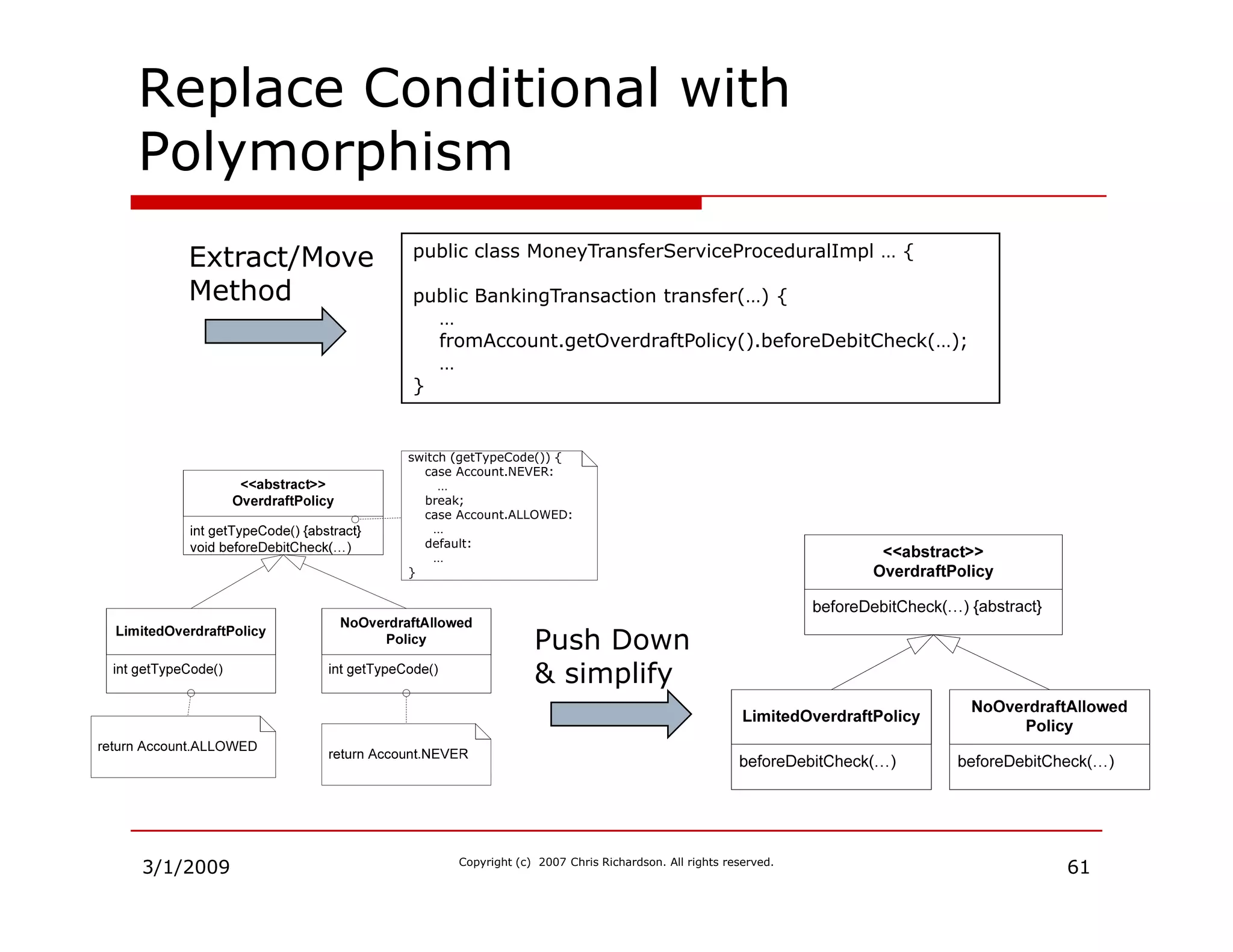
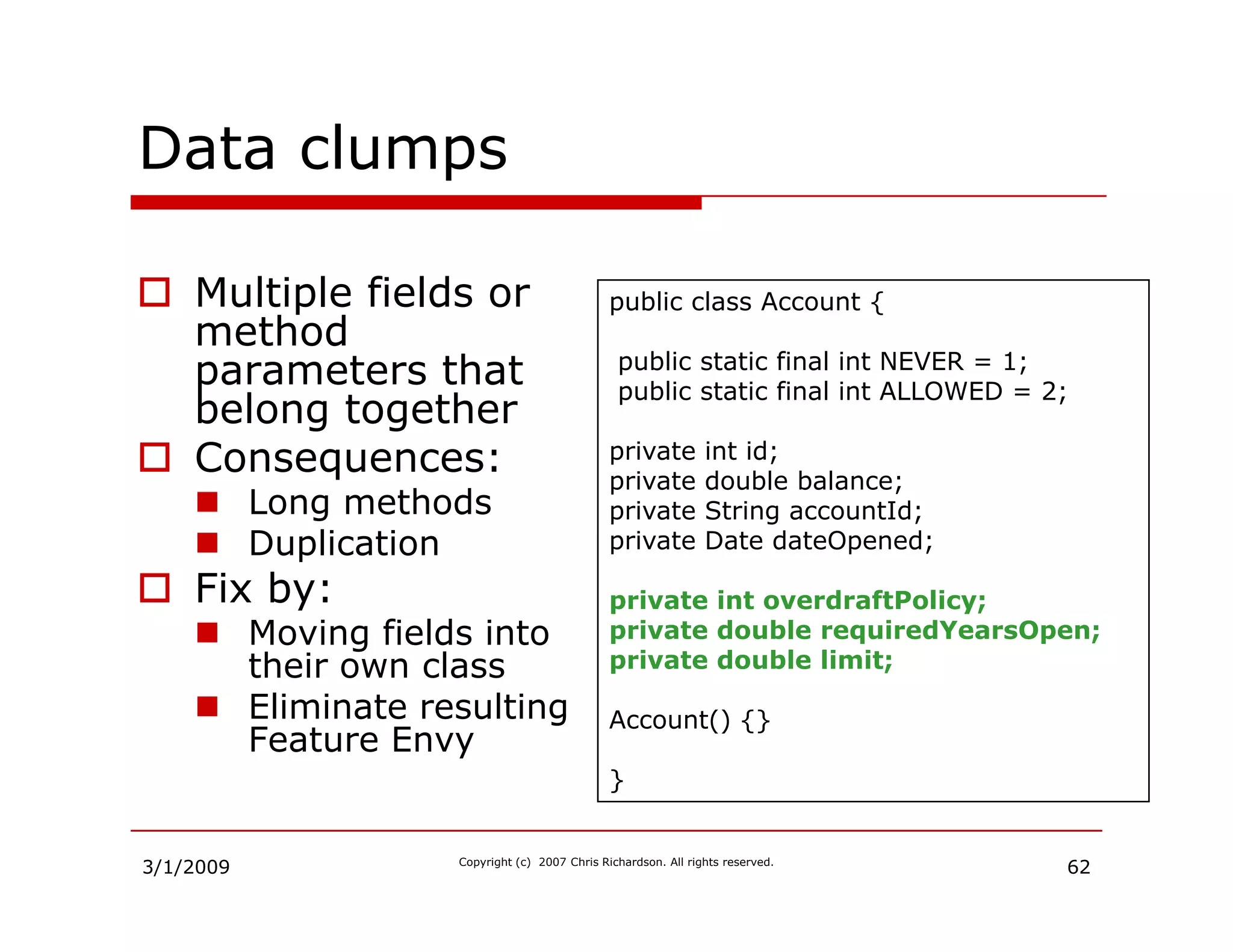
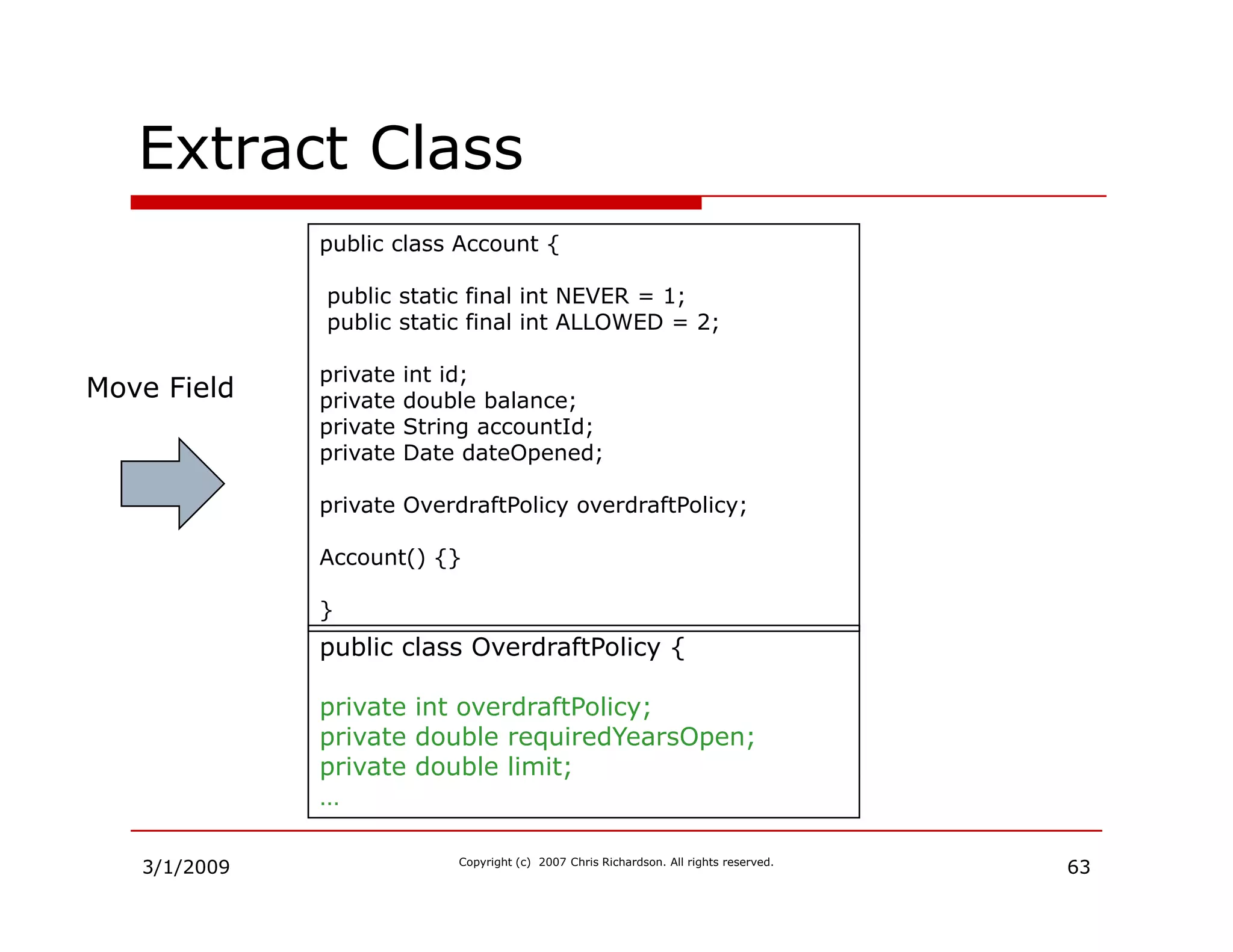
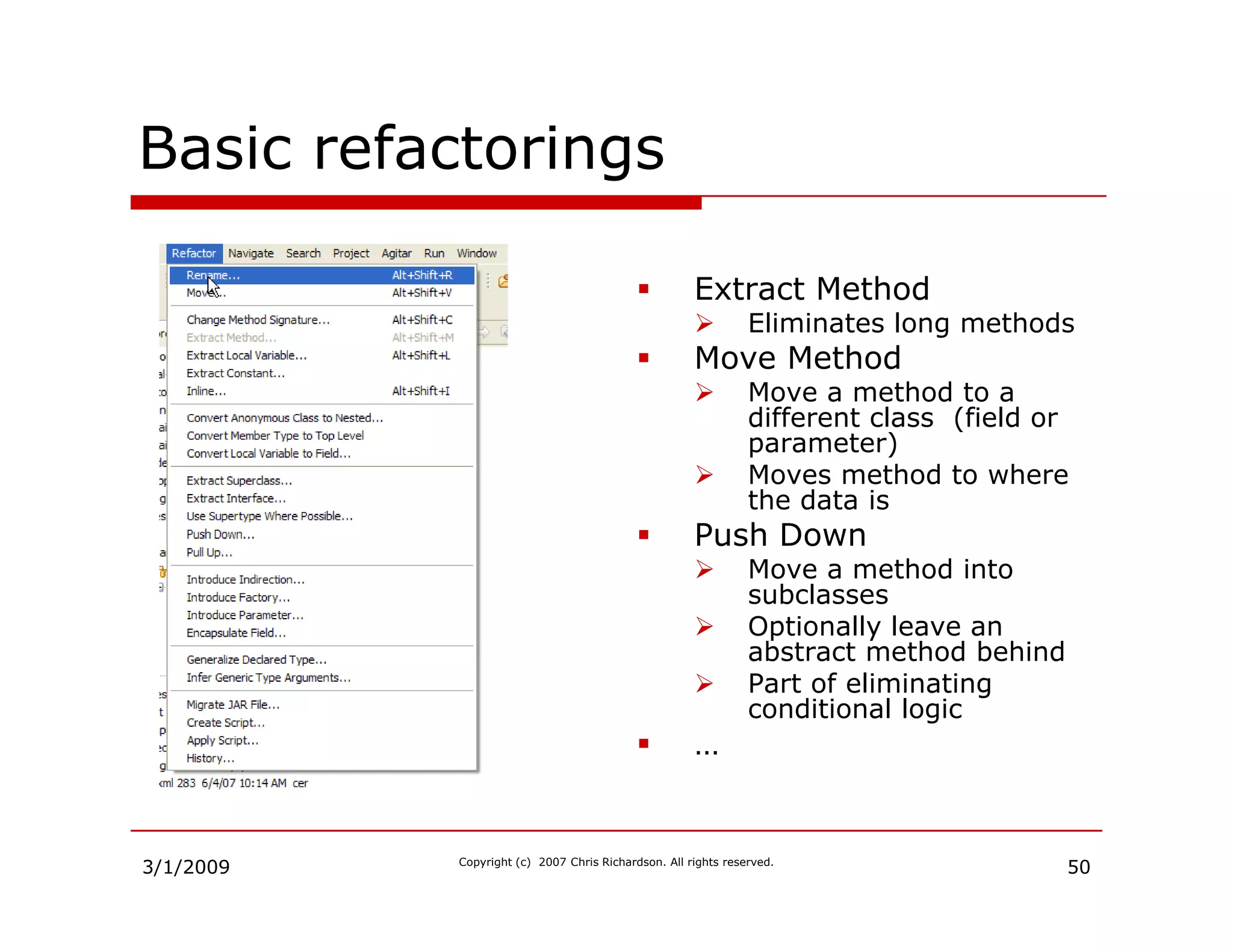
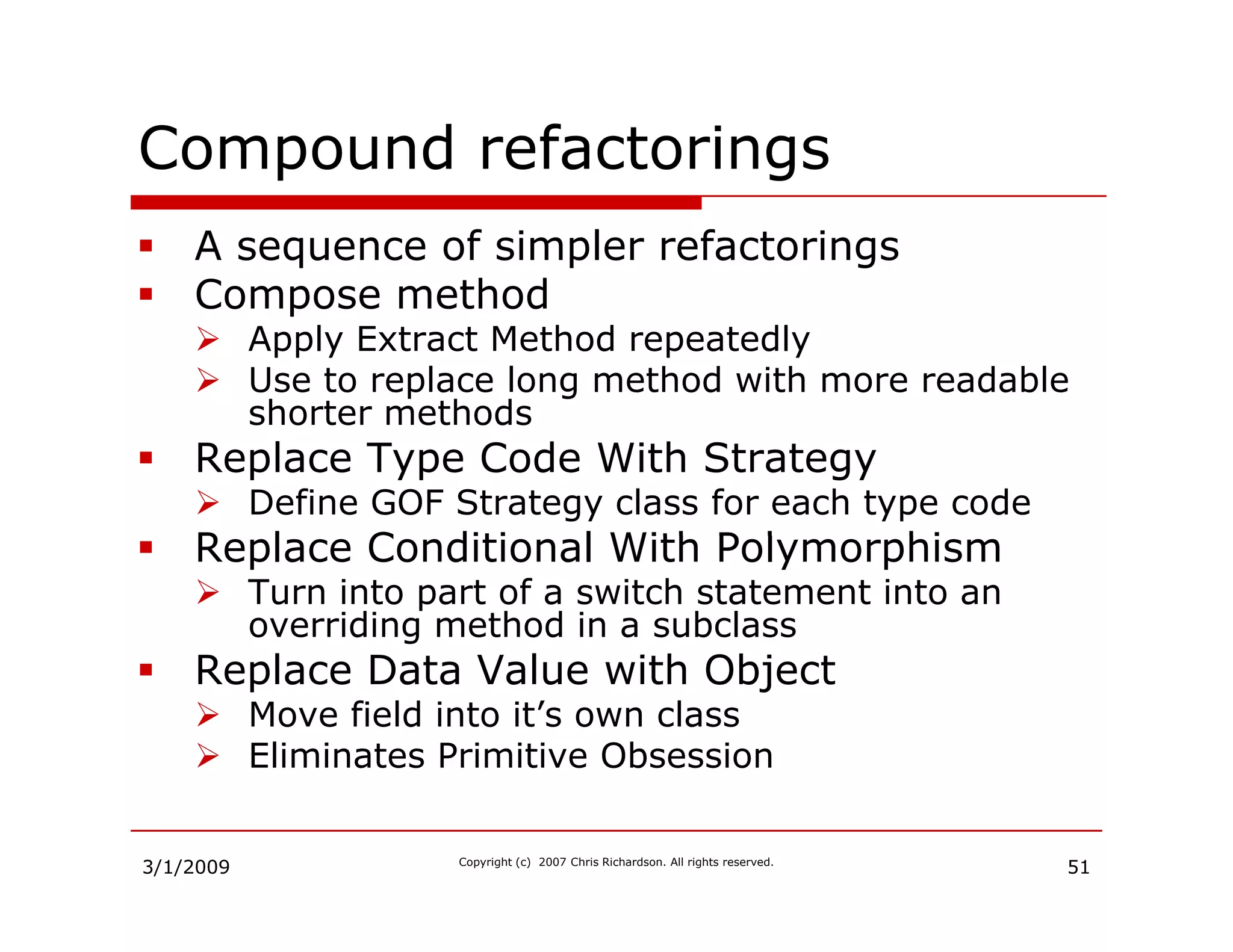
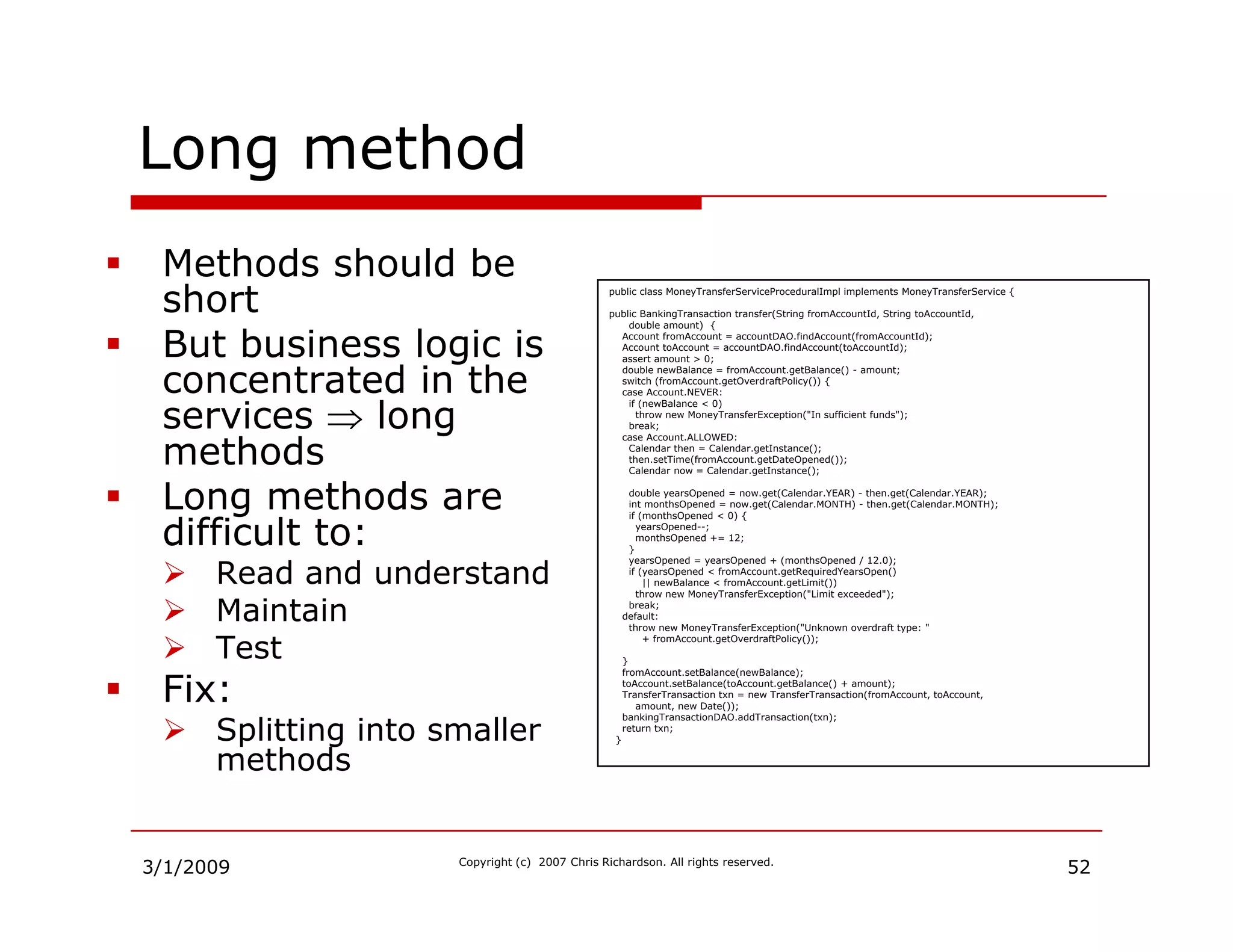
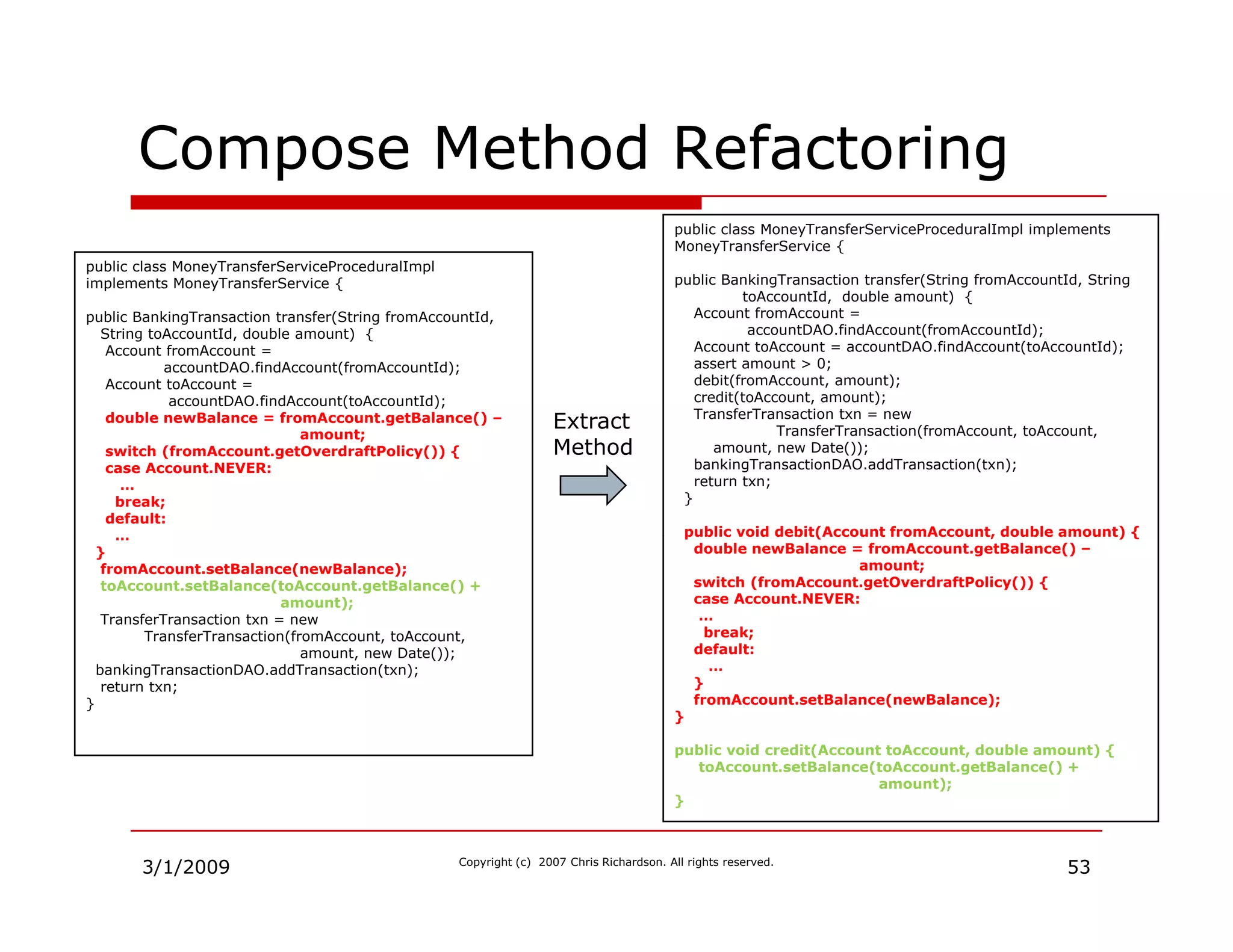
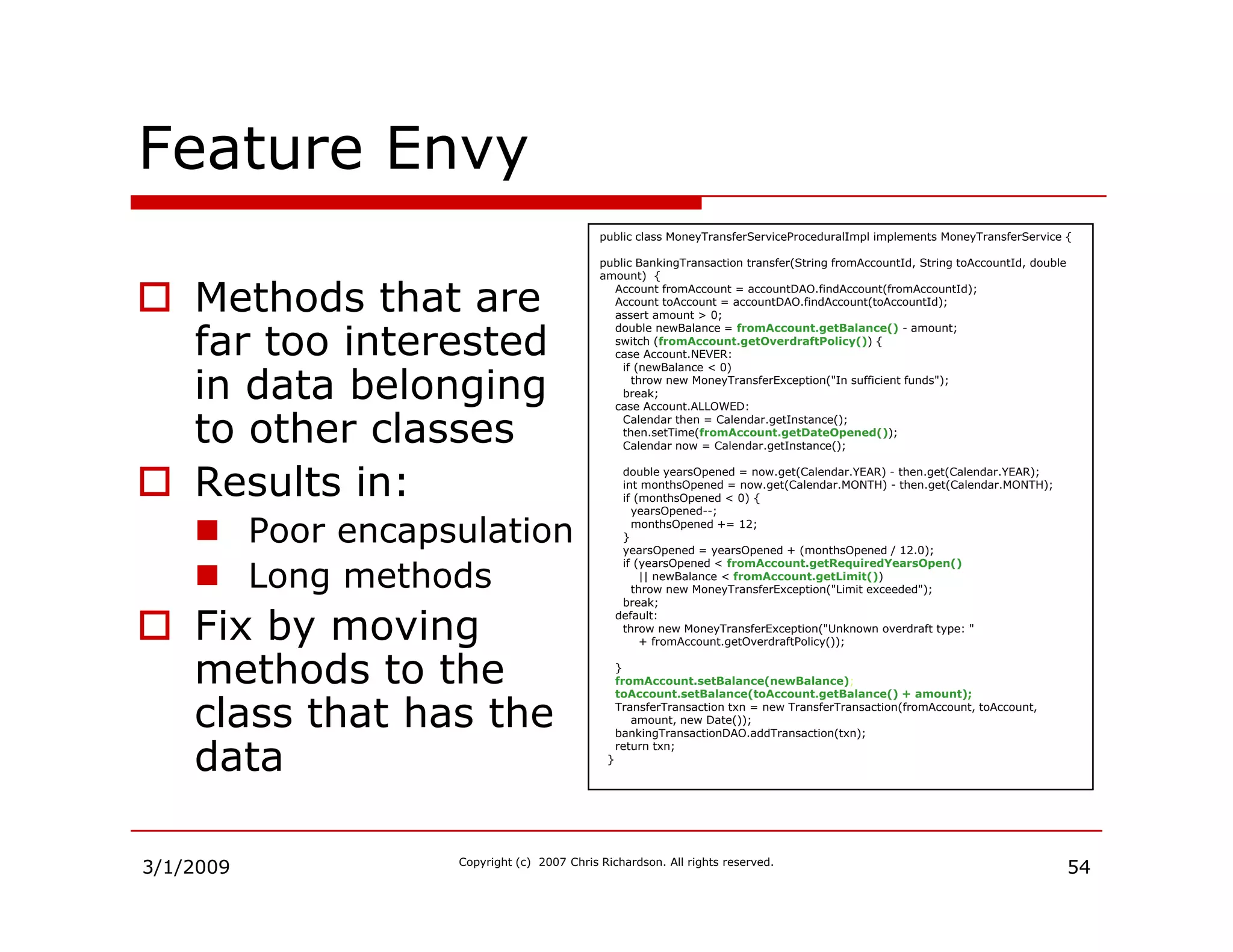
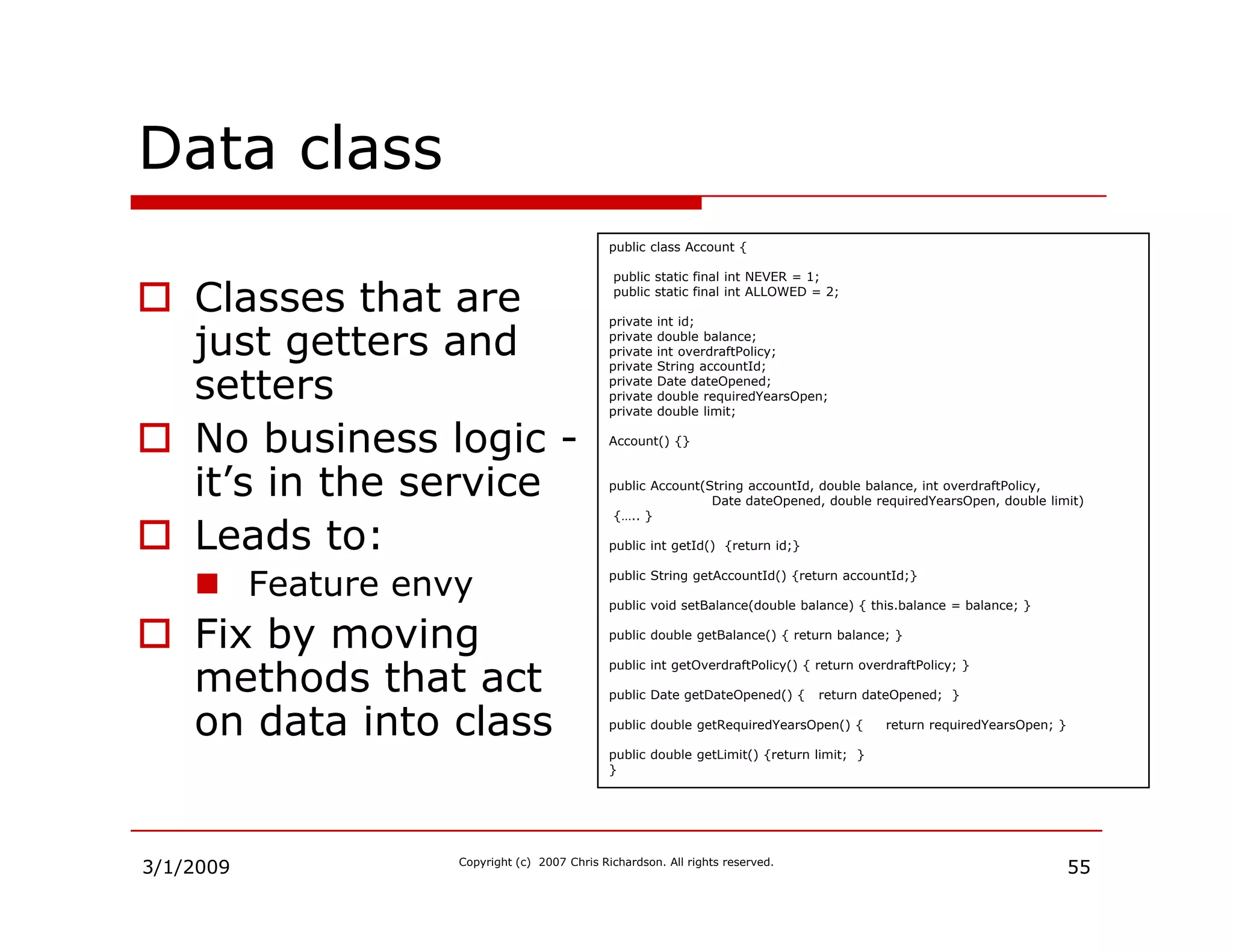
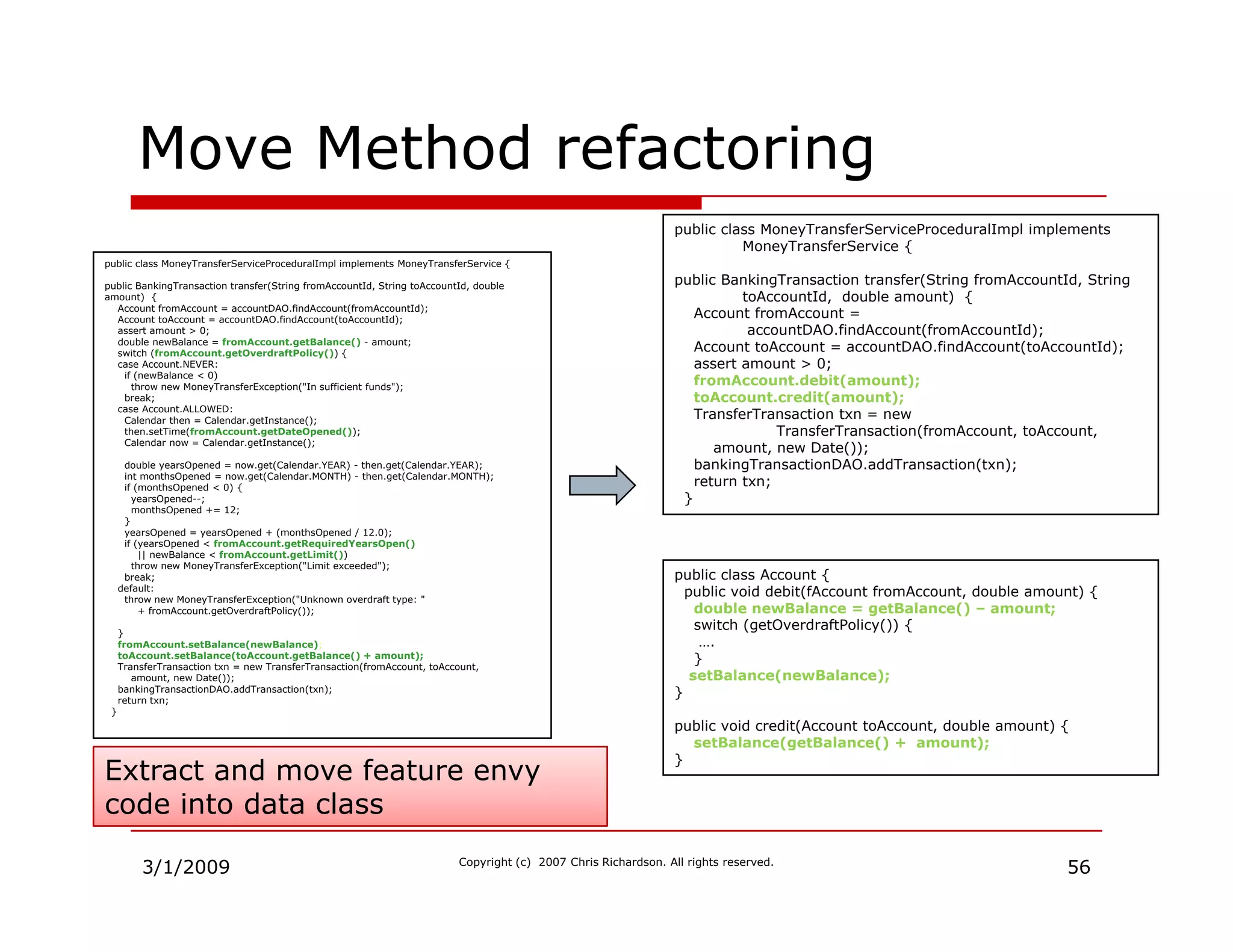
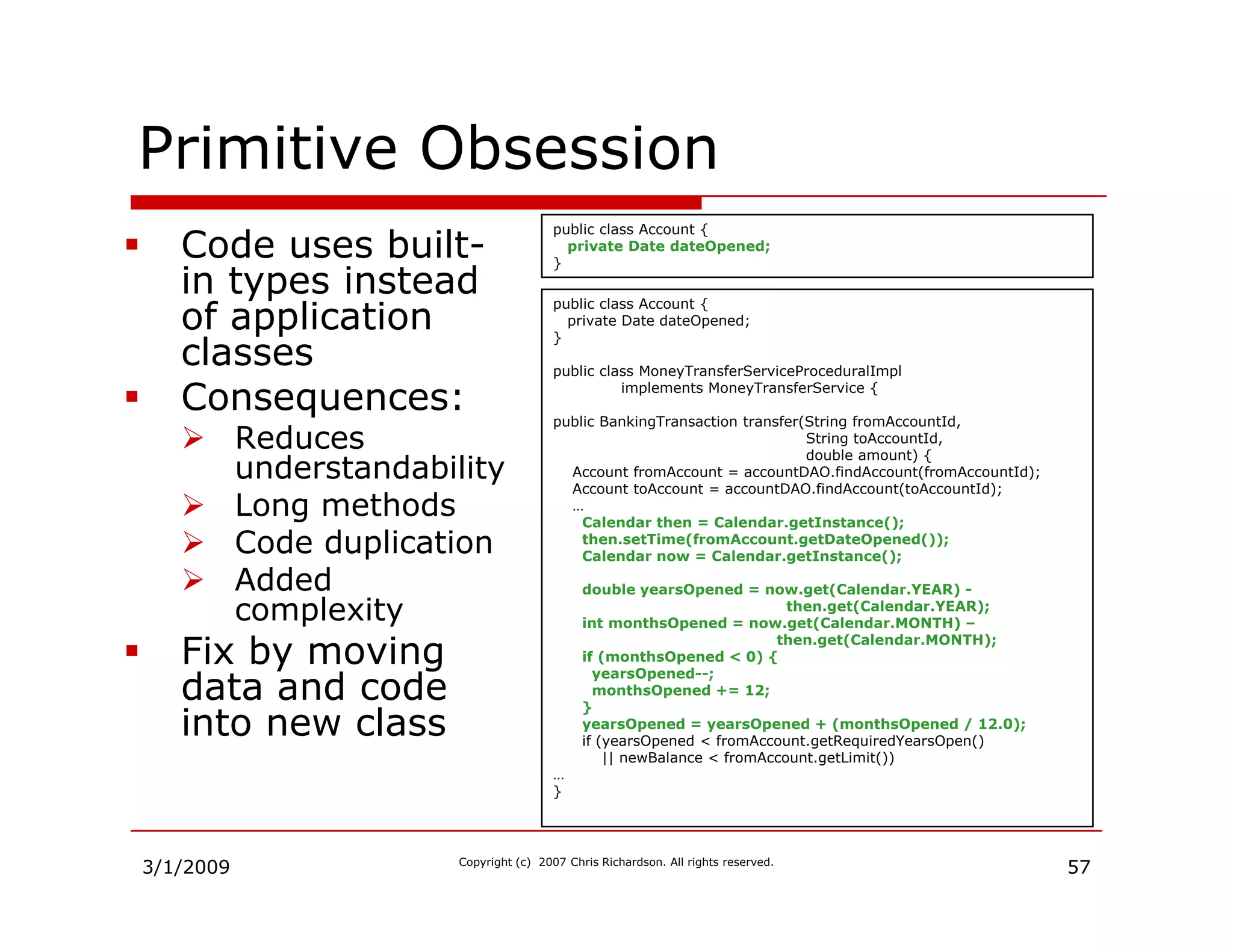
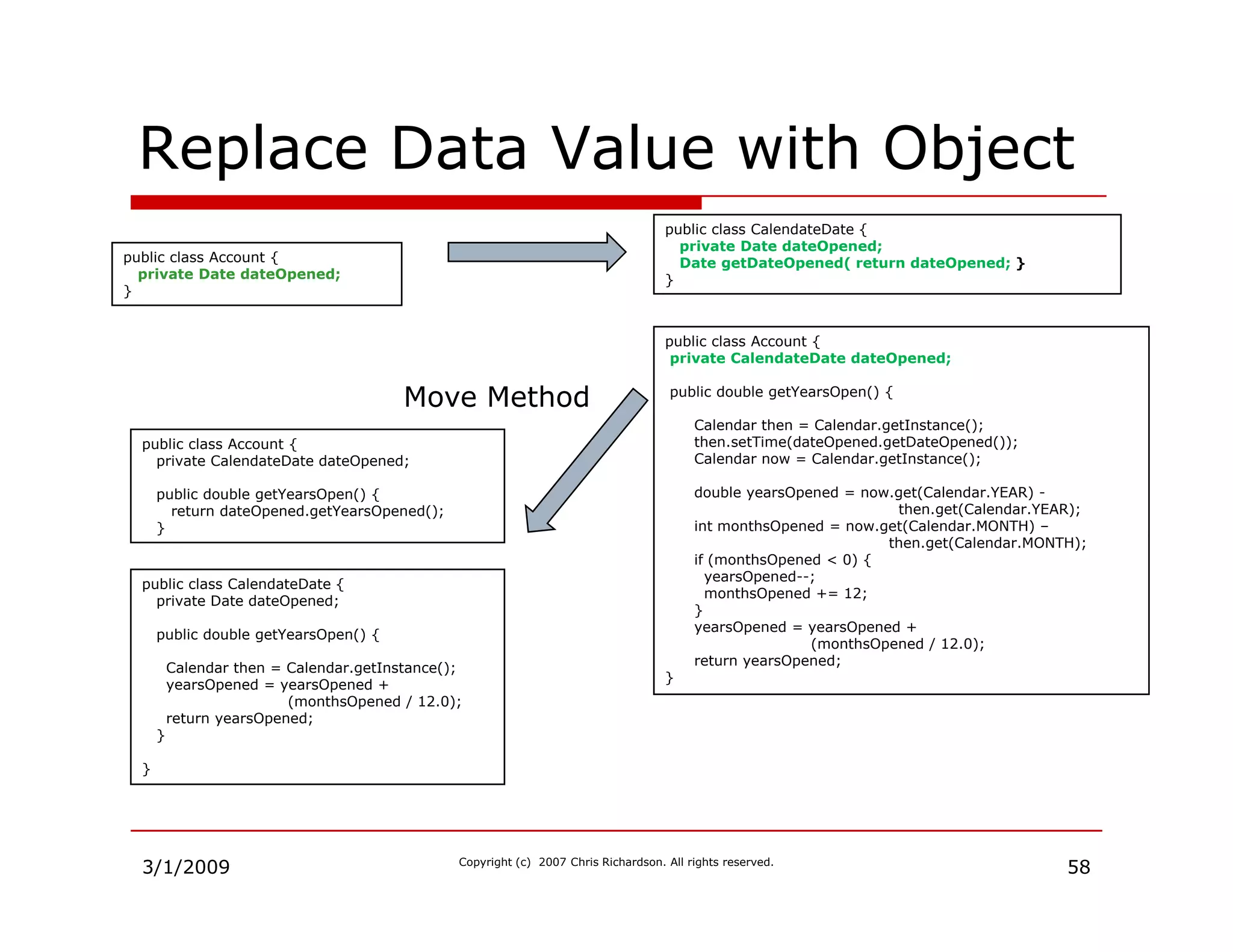
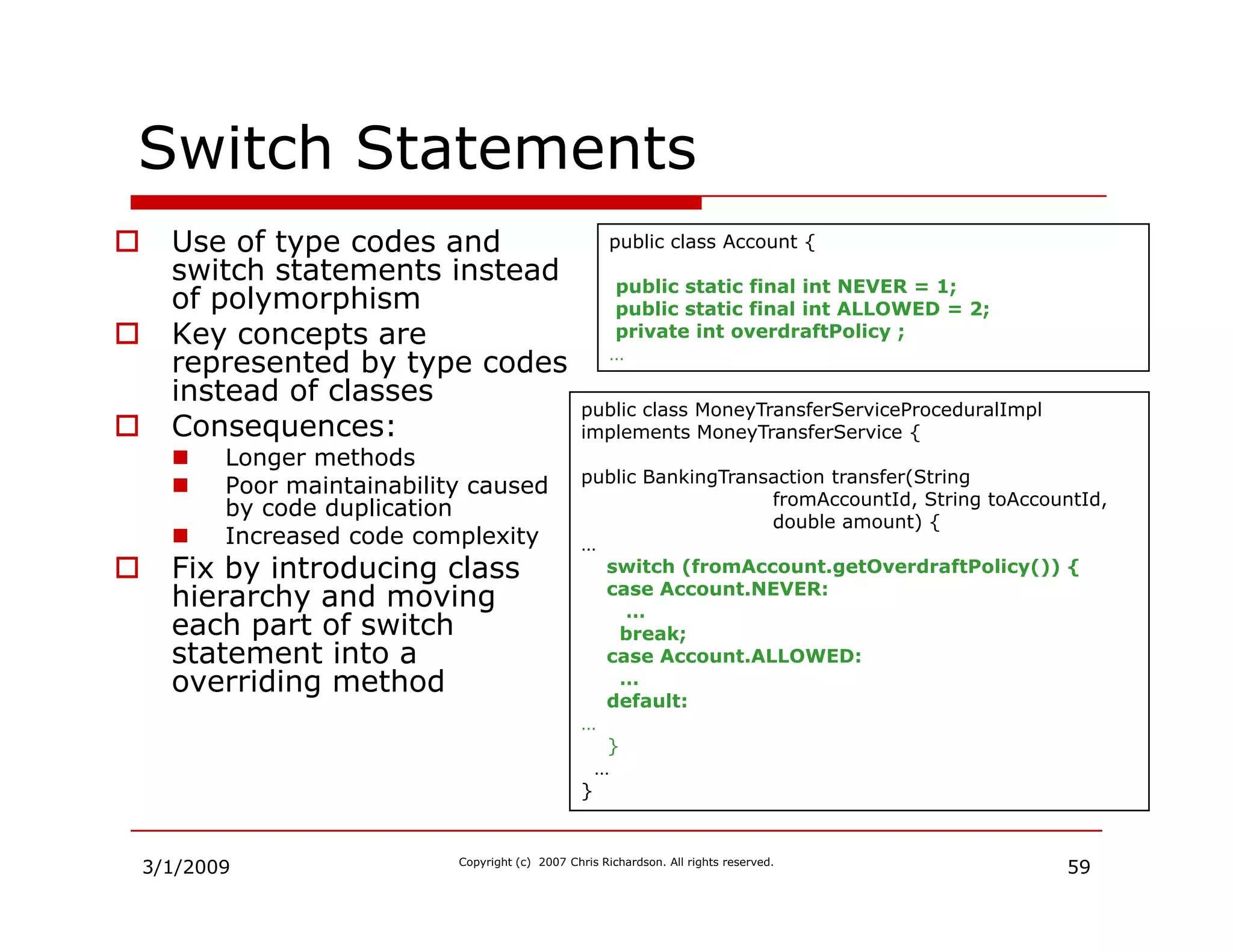
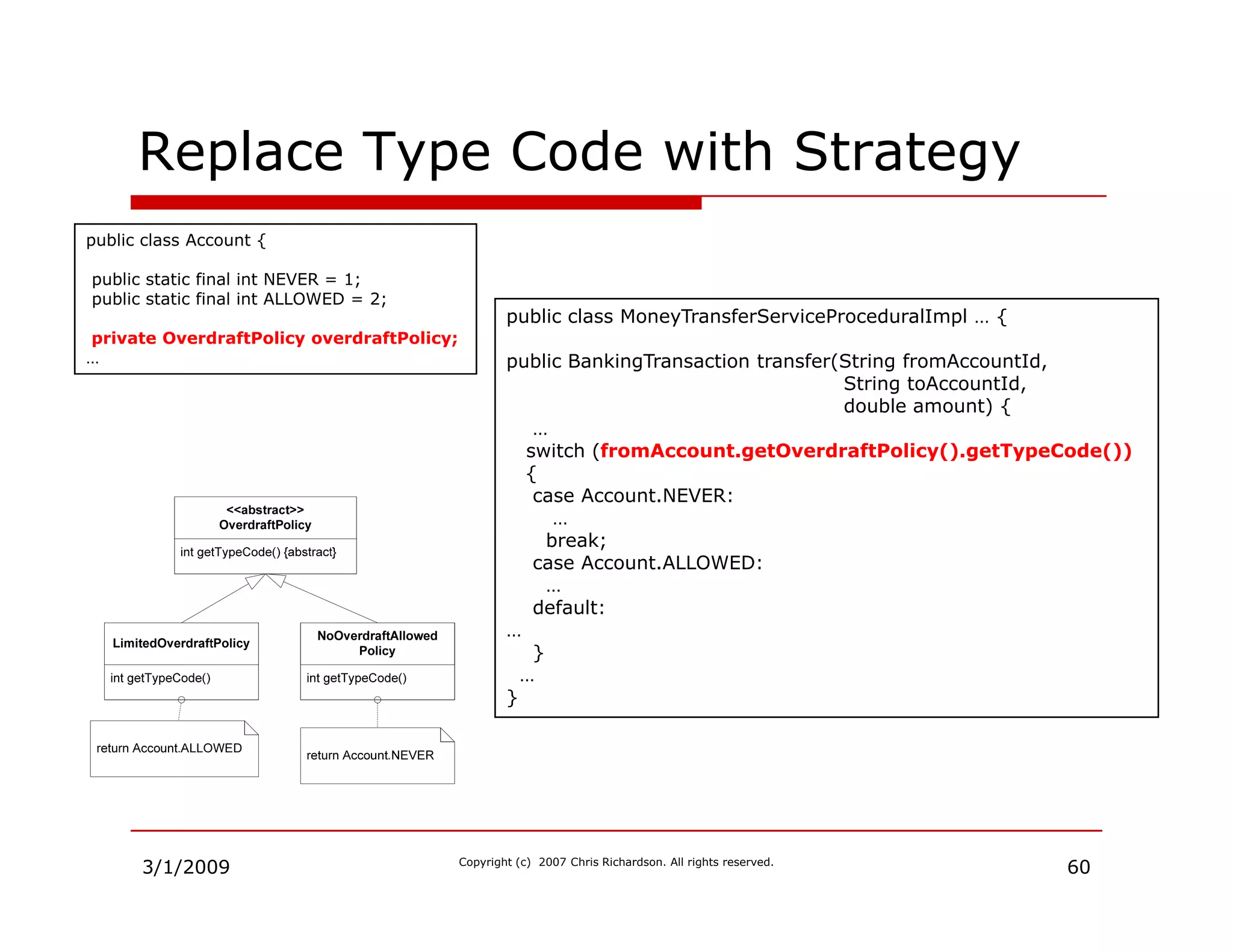
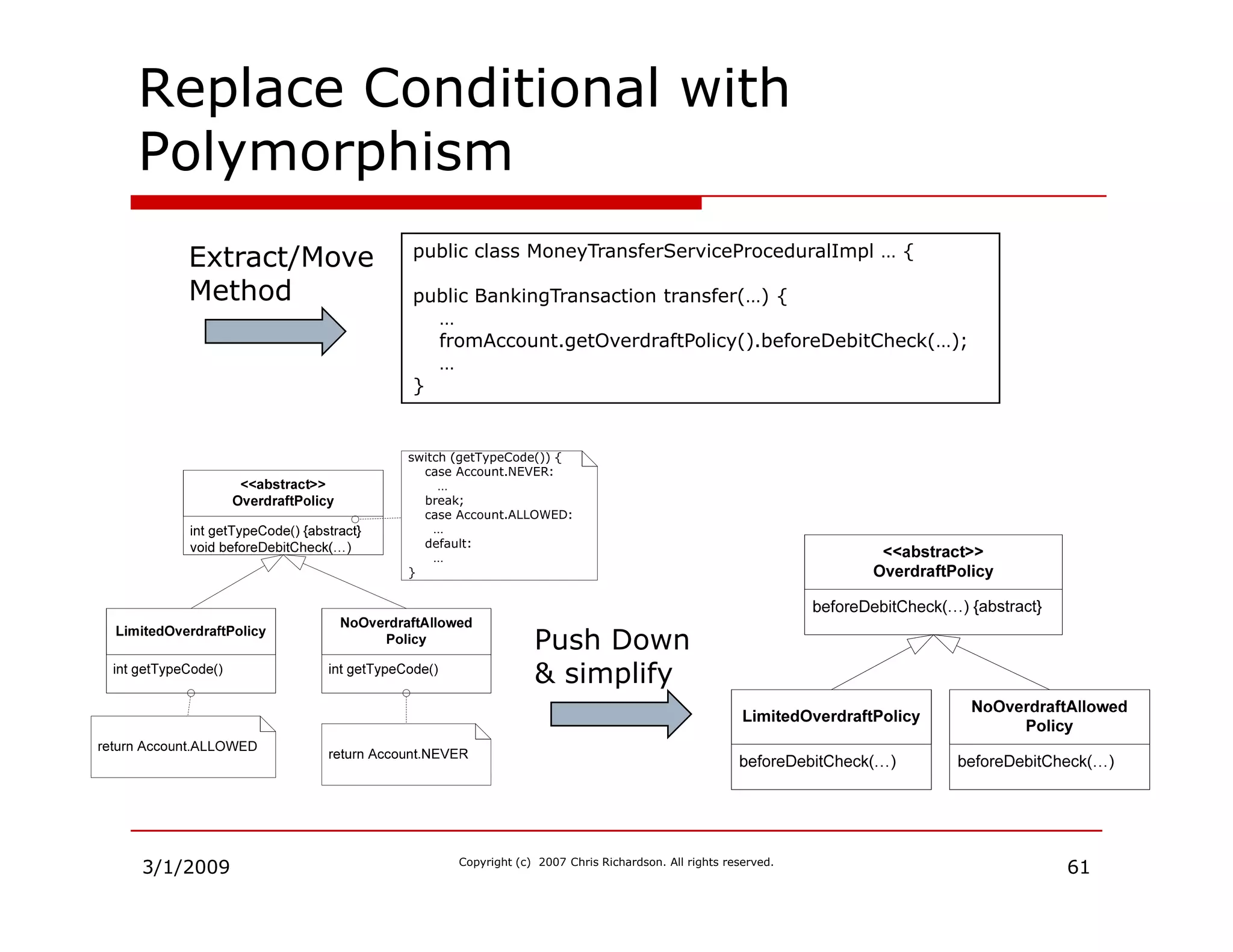
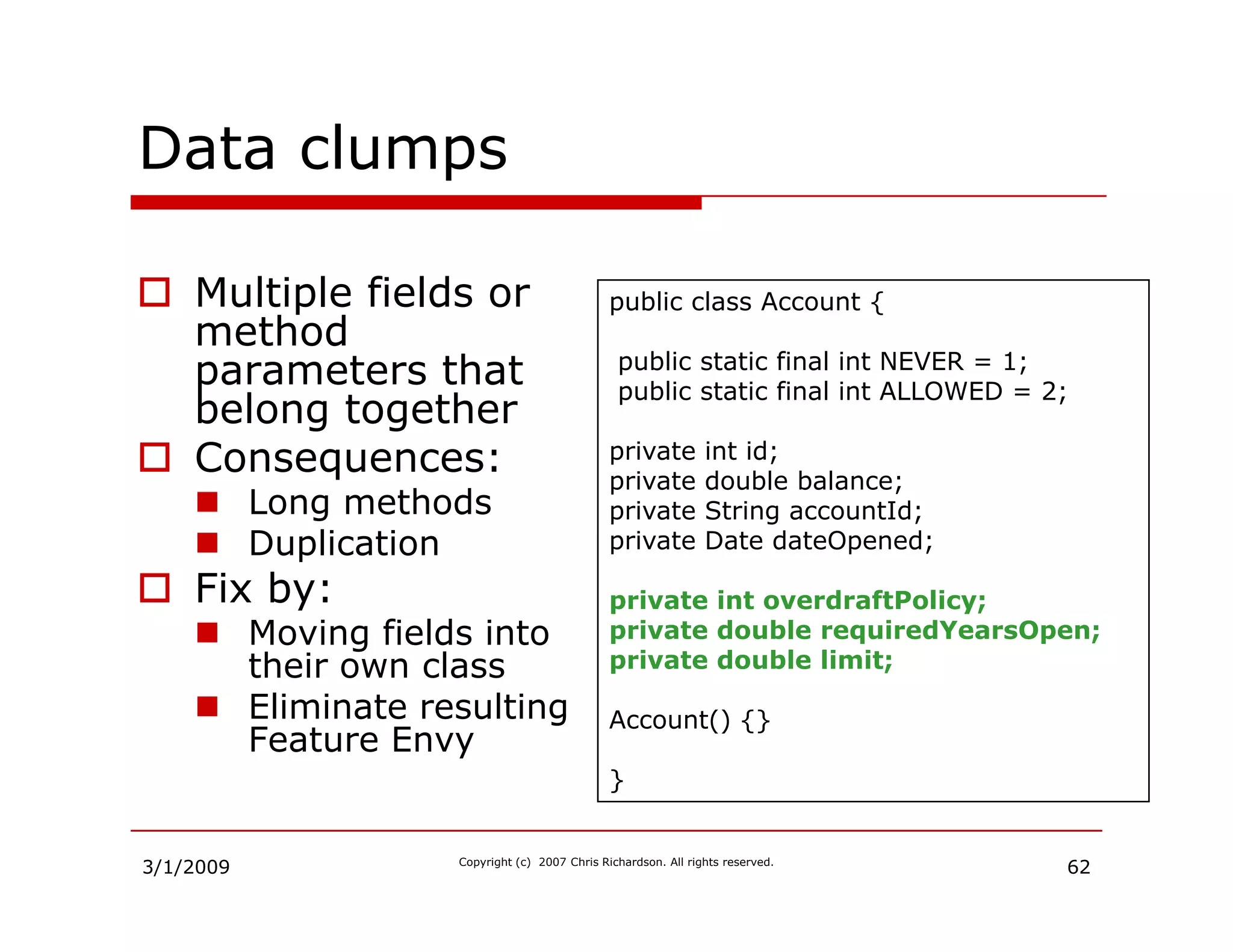
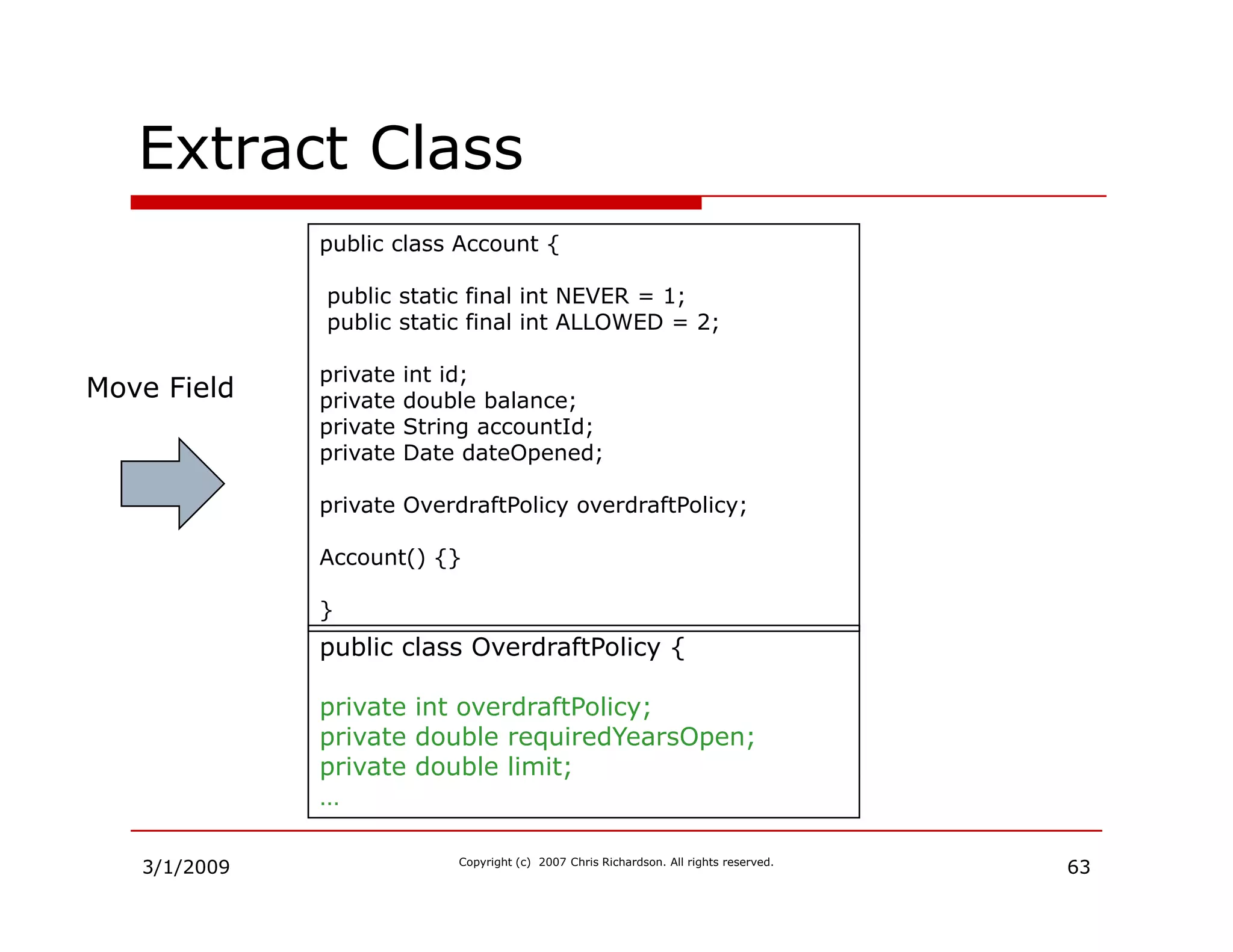
Overview of code smells and various refactoring techniques to improve maintainability and readability.
Discussion on common refactoring issues such as primitive obsession, data classes, and switch statements.
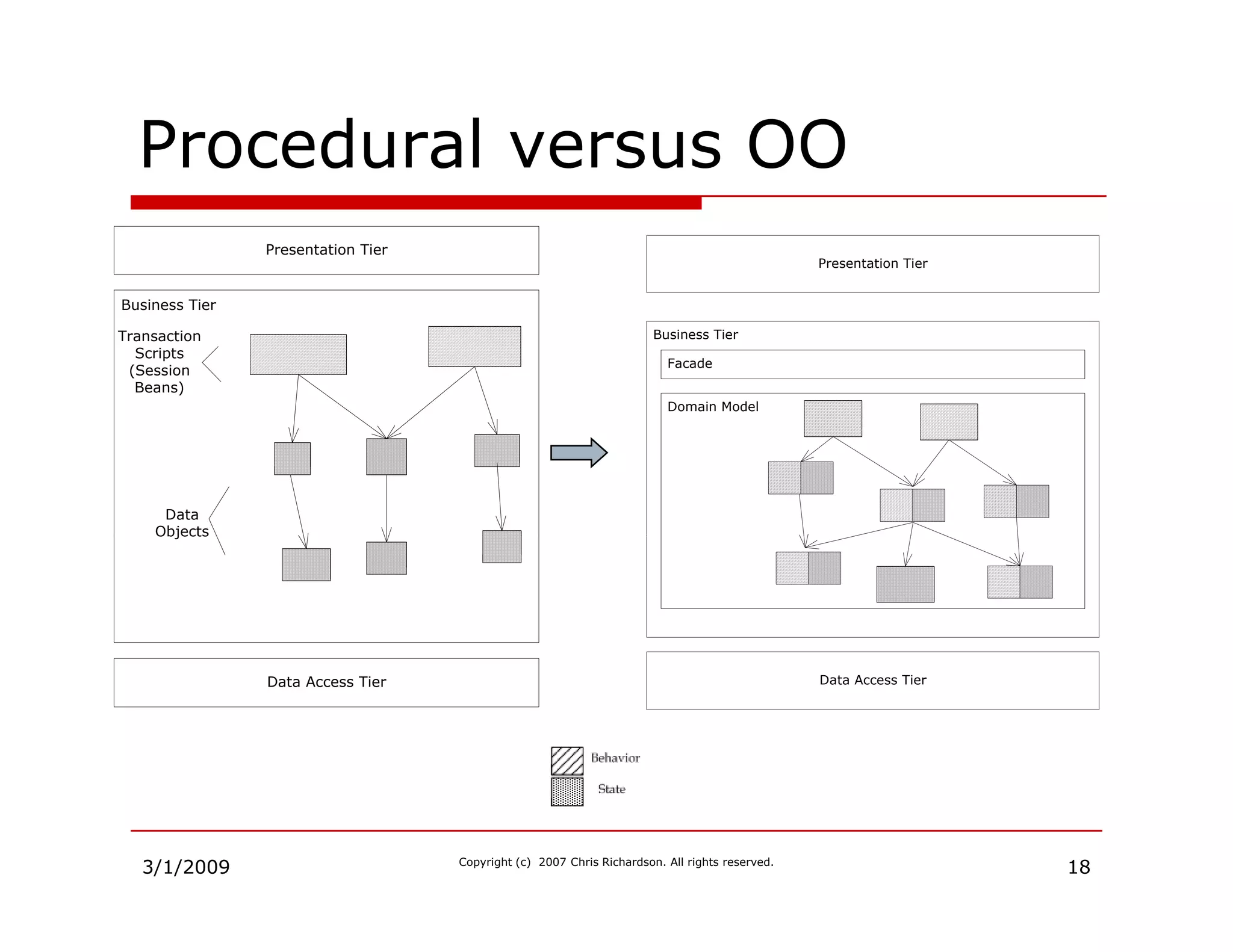
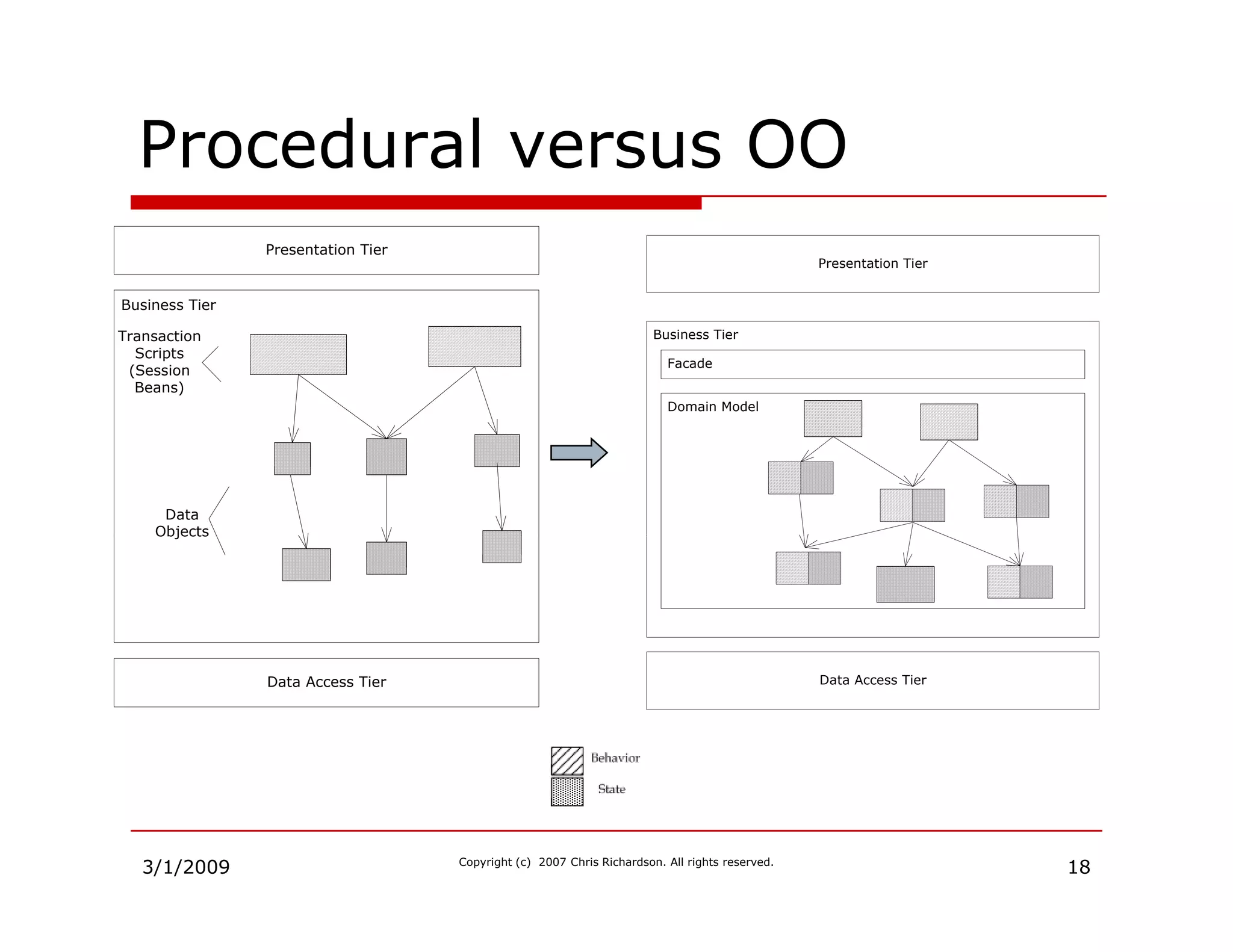
Strategies for transitioning procedural designs into object-oriented designs incrementally.
Summarizes the benefits of rich domain models and provides contact information for further engagement.