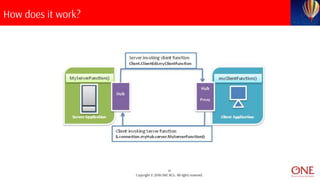
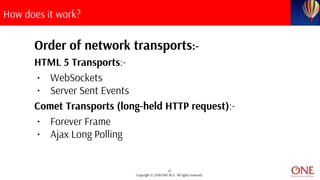
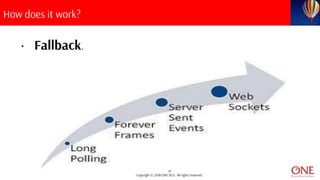
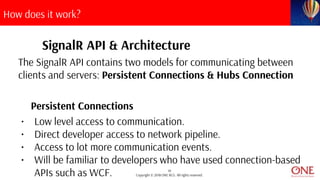
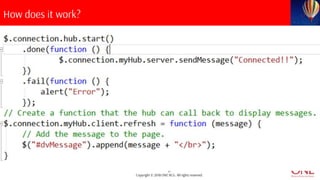
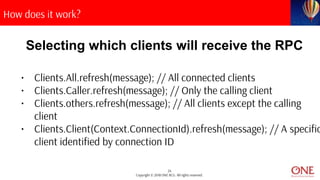
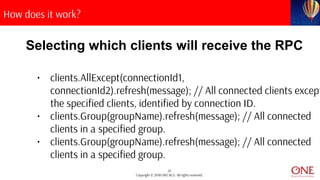
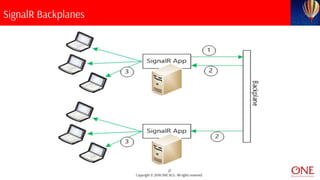
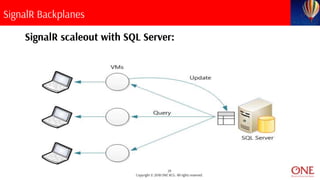
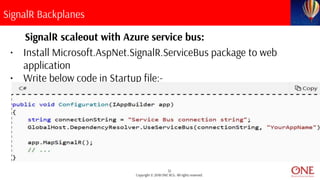
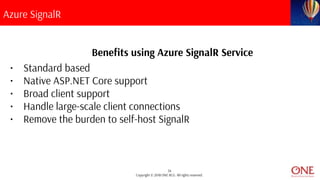
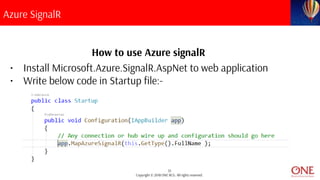
The document provides an overview of SignalR, a real-time library for .NET that enables server-to-client remote procedure calls with a simple API and automatic connection management. It discusses its architecture, including persistent connections and hubs, as well as the various transport methods like websockets and long polling. Additionally, it covers the use of backplanes for scaling in distributed environments and introduces Azure SignalR service for simplifying real-time web functionality.