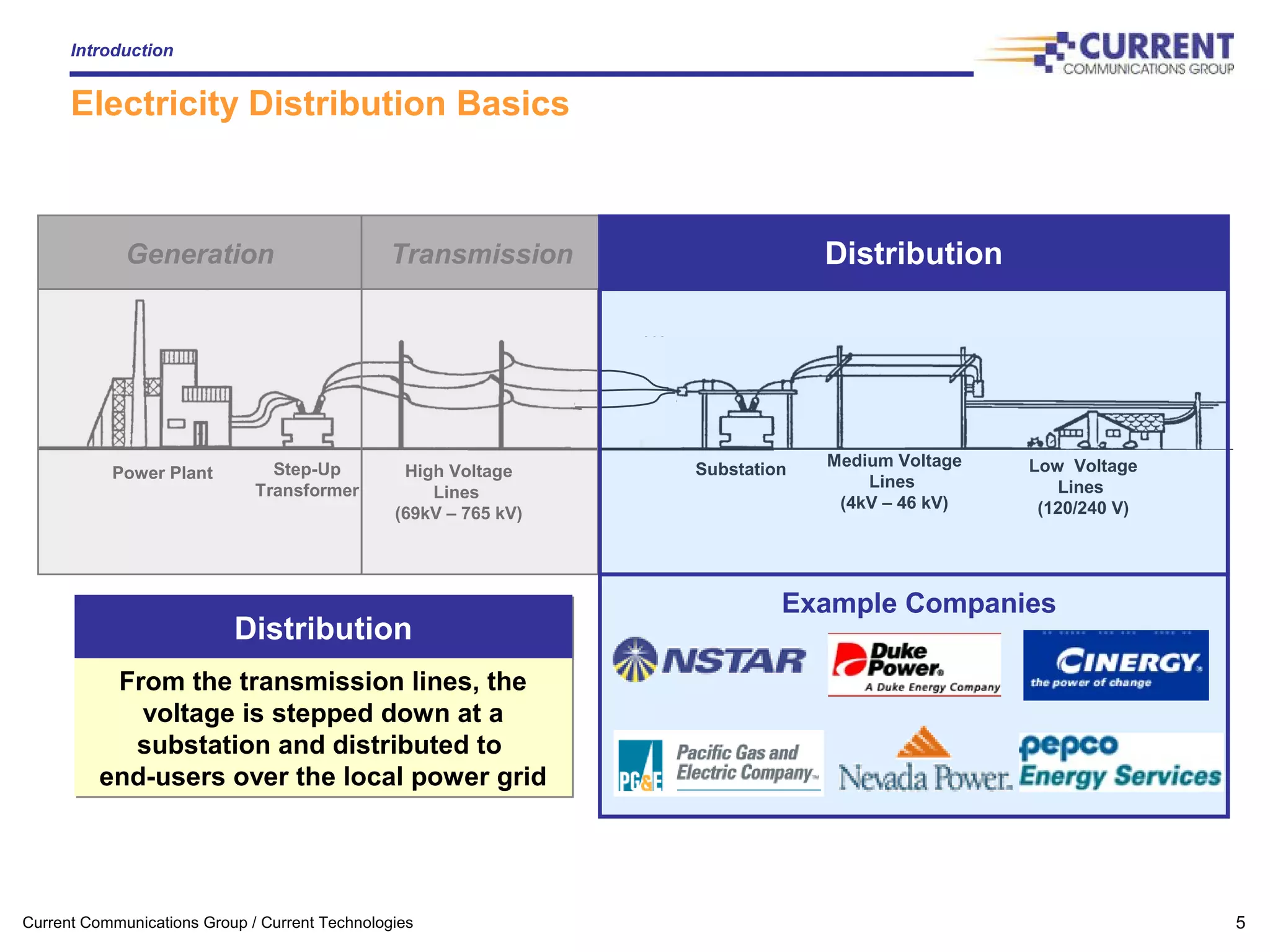
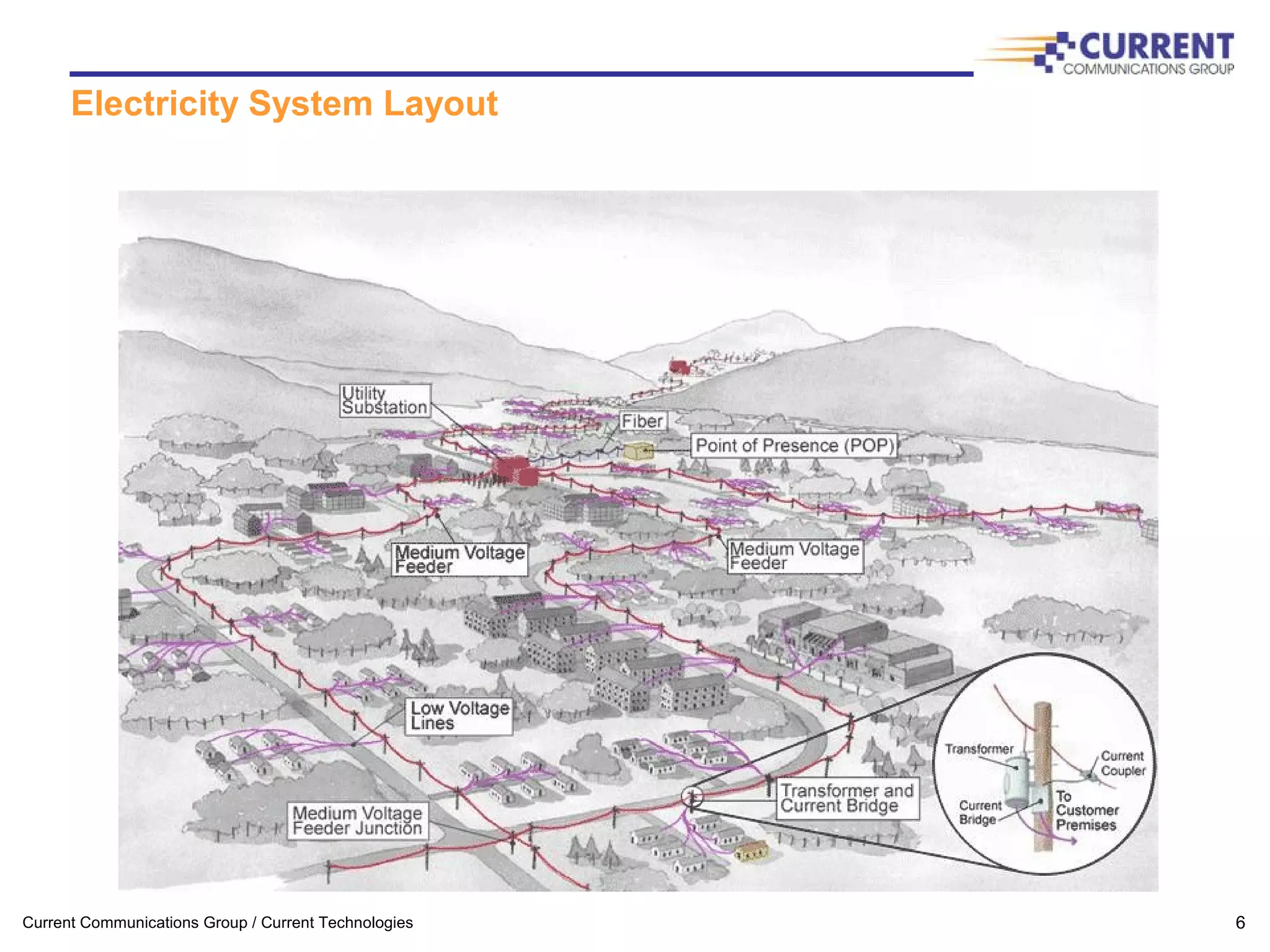
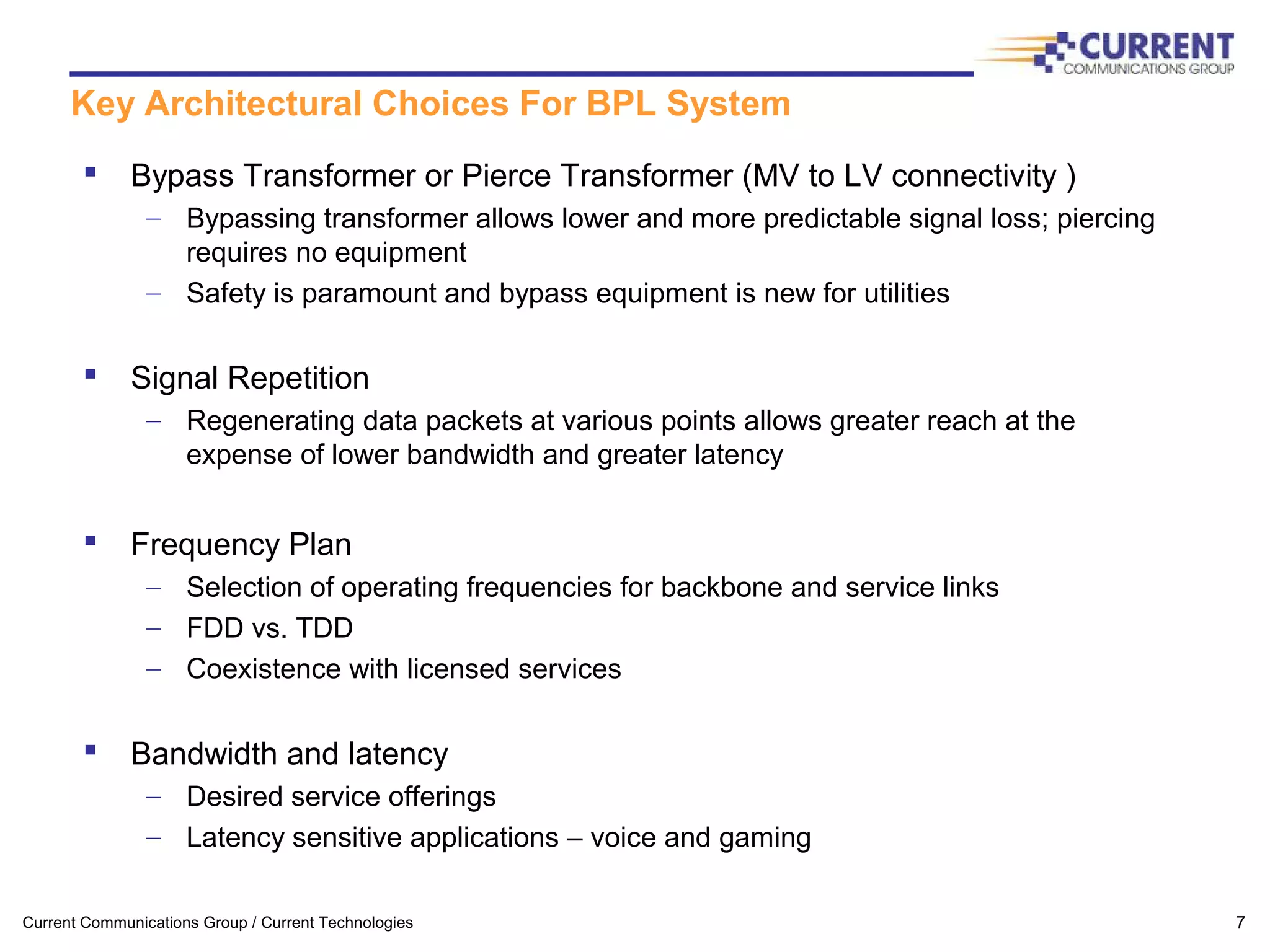
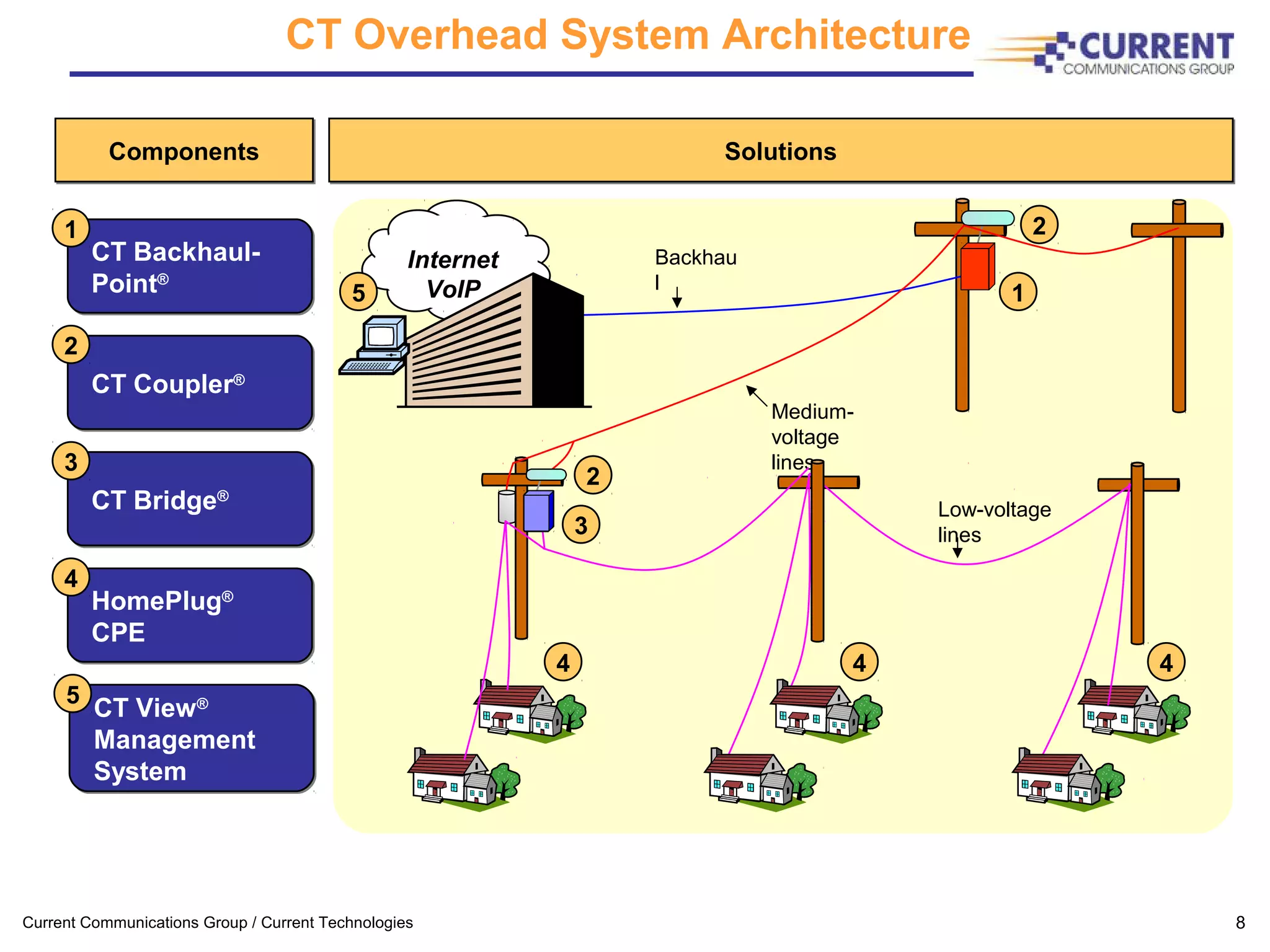
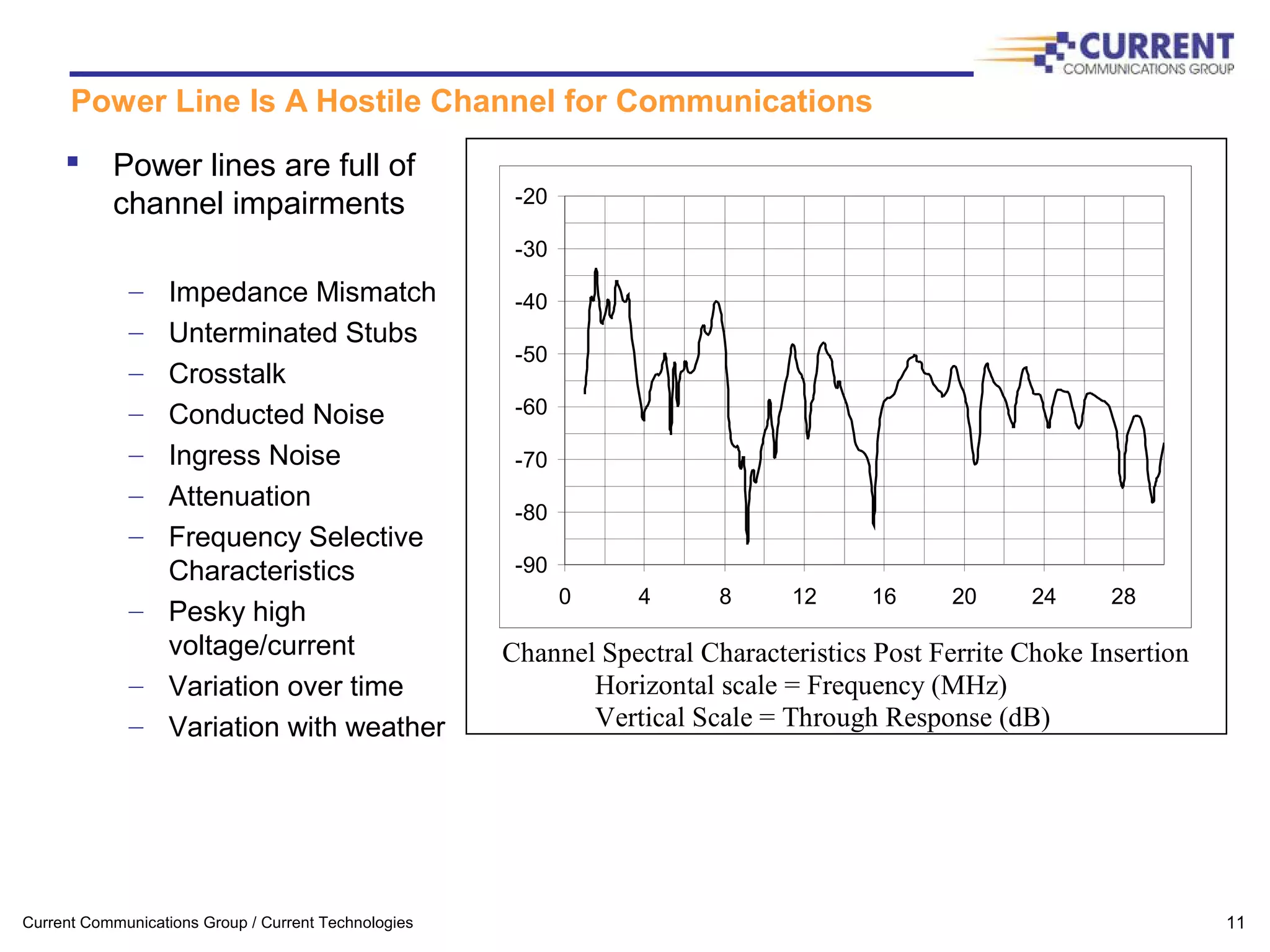
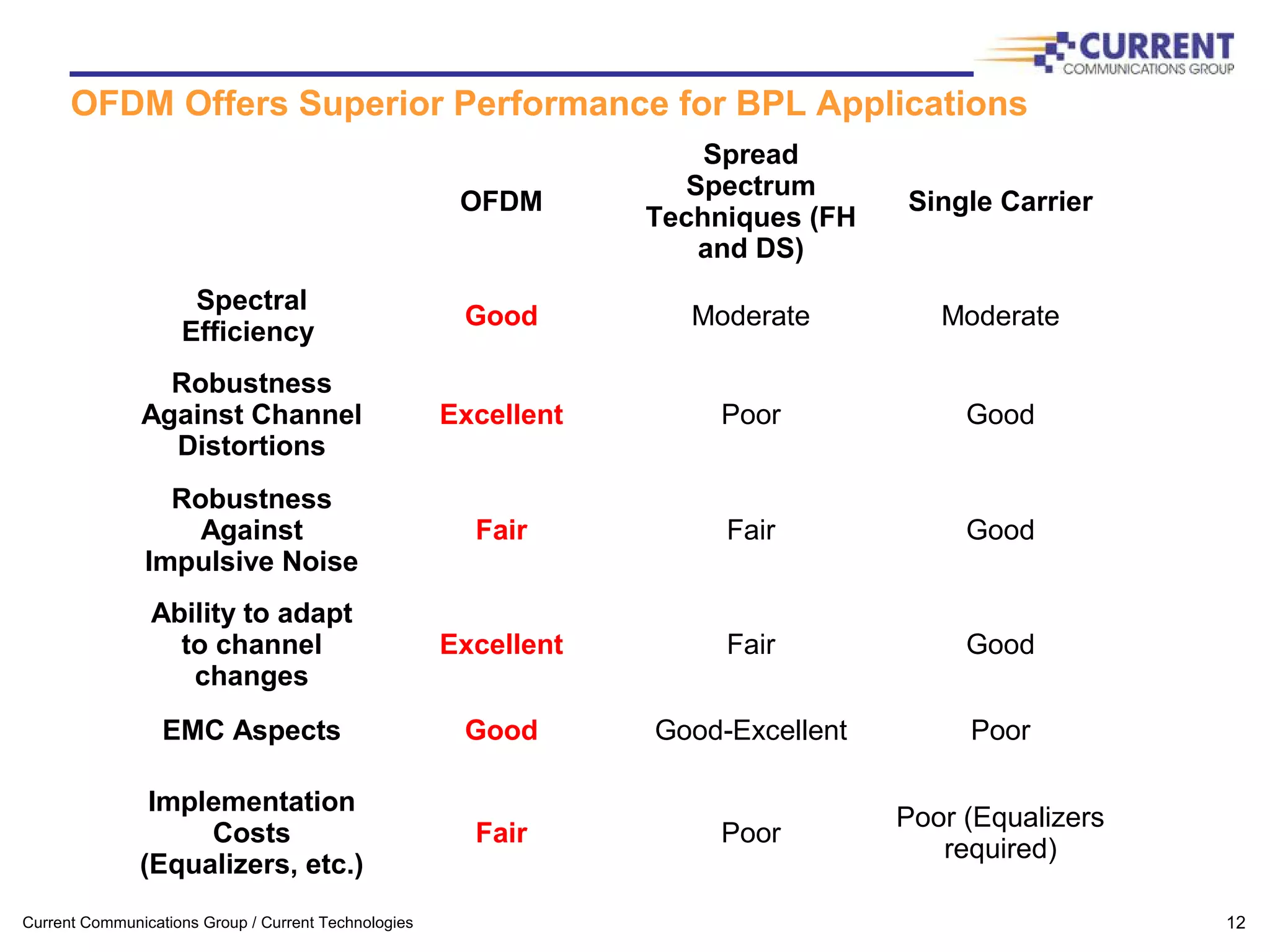
The document summarizes a presentation on broadband over power line (BPL) technology given to the Washington Area CTO Roundtable. It provides an overview of BPL, describes how power lines can be used as a communications medium, discusses key aspects of BPL system architecture like frequency planning and components, and addresses challenges like the noisy power line channel environment. It also reviews the status of the BPL industry and big questions still facing commercialization efforts.
![Current Communications Group / Current Technologies 19
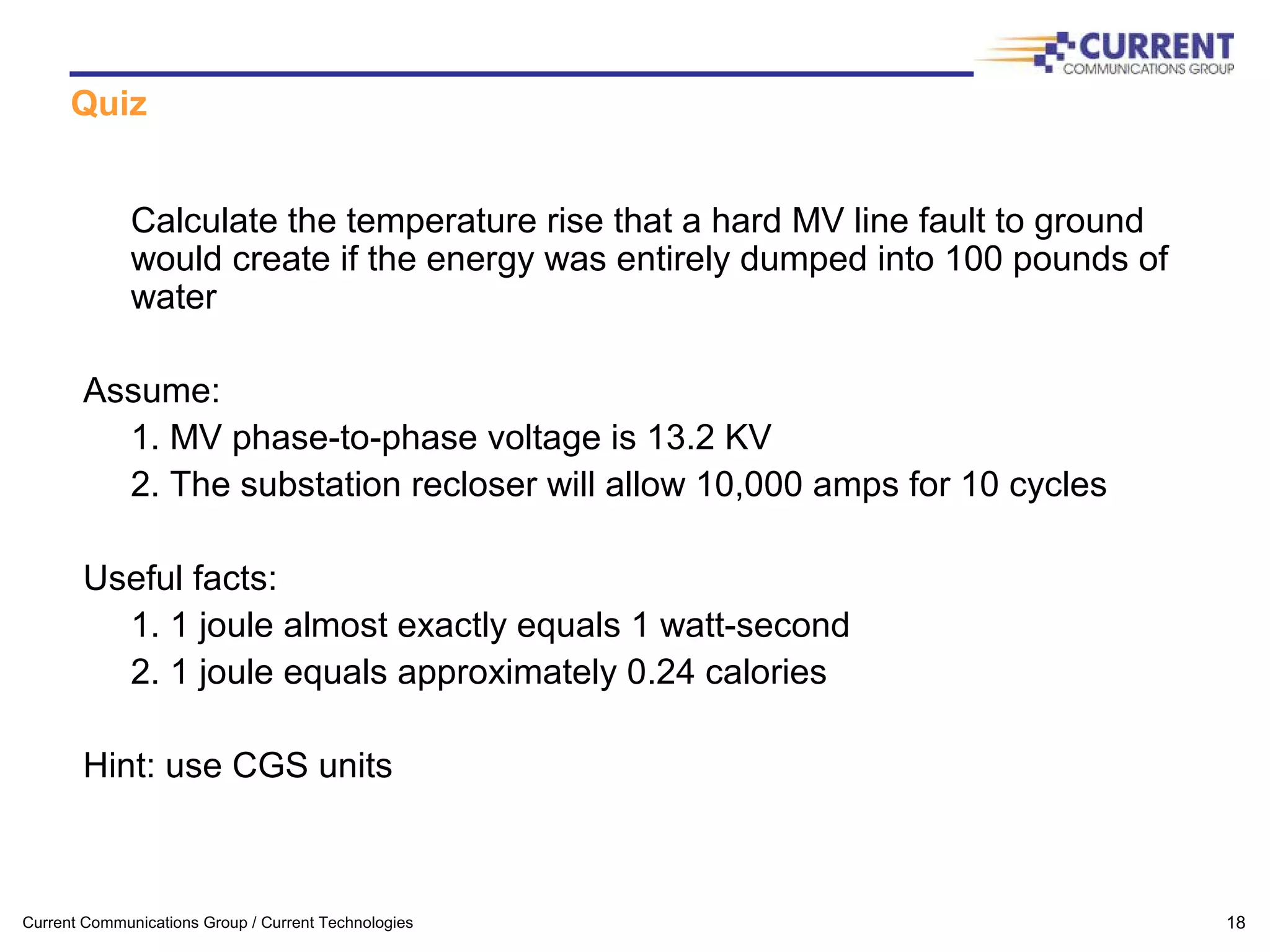
Quiz solution
The total energy Q dissipated as heat:
Q = (phase-ground voltage) * (current) * (time interval) [watt-seconds]
Q = (13.2 KV / 1.732) * (10,000 amps) * (160 msec) * (0.24) [calories]
Q = 2.93E06 calories
If that total energy is dumped into 100 pounds of water:
dT = Q / (mass of water * specific heat)
dT = 2.93E06 / (100 [lbs] * 454 [grams/lb] * 1 [cal/gram/deg C])
dT = 64.5C or 148F
It’s also interesting to note that:
dT/dt = (64.5/0.16) or about 400 degrees C / sec !](https://image.slidesharecdn.com/broadbandtech2005-140626164533-phpapp01/75/Broadband-tech-2005-19-2048.jpg)