The document discusses various AWS services for containerized applications and serverless architectures. It covers ECS, EKS, Lambda, serverless patterns, microservices, data lakes, machine learning, and Kubernetes. Key points include:
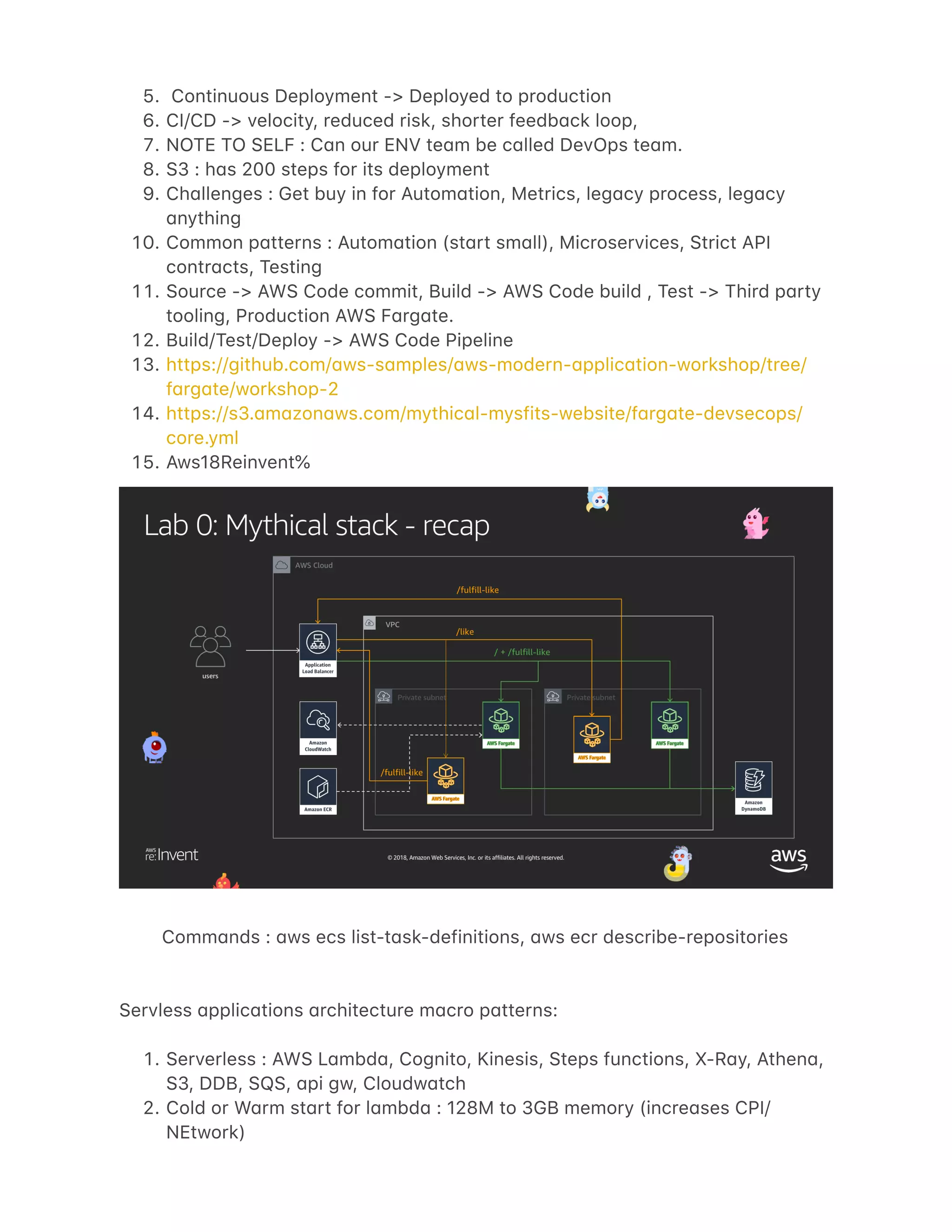
- ECS uses containers wrapped in task definitions and services wrapped in clusters. EKS launches Kubernetes clusters on EC2 instances in AWS accounts.
- Serverless patterns discussed include web applications using API Gateway and Lambda, stream processing with Kinesis, and data lakes using S3 and Athena.
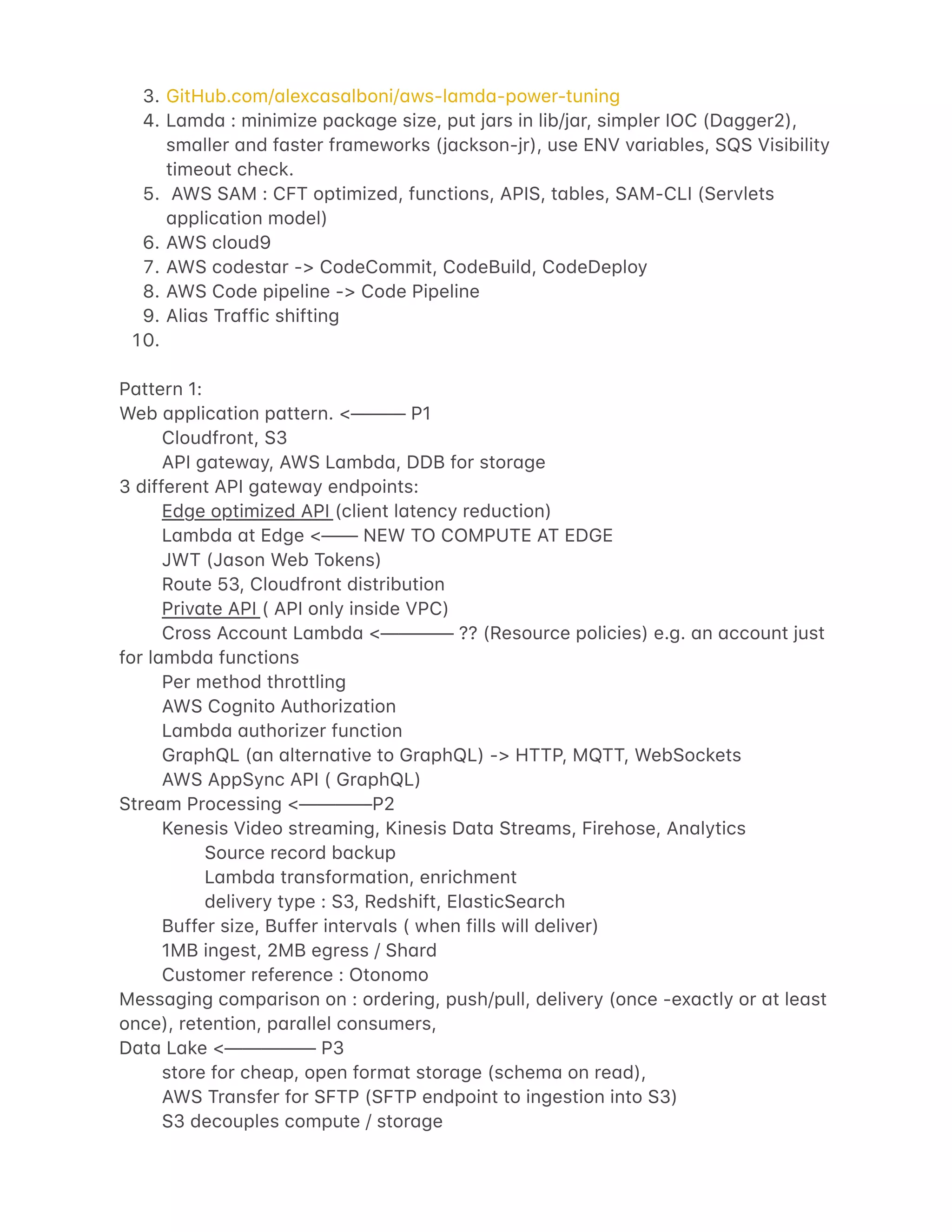
- Best practices for serverless include avoiding hardcoding orchestration, using Step Functions, monitoring and testing, and considering costs of data and services used.
- Microservices tend to
![S3 select, New Block Public Access
Dyn4moDB 4s D4t4 C4t4log (Met4 d4t4) <- using L4mbd4 ( Glue (hive
comp4tibility), Redshift)
Athen4 : serverless query service, (P4rquet, AVRO, ORC)
Blog for Athen4 best pr4ctice.
L4mbd4 : 15 mins
Pywren (custom python 4nd sends to l4mbd4 in p4r4llel) <- pywren.io
ML P4ttern <————— P4
Vision, L4ngu4ge,
Im4ge processing : Am4zon Rekognition Im4ge
Medi4 4n4lysis solution
Am4zon Connect <- AWS c4ll center service
Lex ch4tbot
Glue fine gr4ined 4ccess control:
Access control for d4t4 c4t4logs
Identity 4nd resource b4sed policies (en4ble cross 4ccount 4ccess)
C4t4log / region / 4ccount
Resources 4re : c4t4log, d4t4b4se, connection, t4ble, function
Only one policy per c4t4log
IAM policy to user, Glue resource policy on c4t4log <- to get him 4ccess.
Access gr4nts up to t4bles 4nd not p4rtitions (e.g. if t4ble h4s both PII 4nd non-
PII this will be 4n issue)
WIP : T4g b4sed 4nd p4rtition b4sed ACL, N4tive support for View, EMR 4ccess
using IAM profile.
E2E encryption is support, KMS is supported.
EMR : Ap4che R4nger : https://4ws.4m4zon.com/blogs/big-d4t4/implementing-
4uthoriz4tion-4nd-4uditing-using-4p4che-r4nger-on-4m4zon-emr/
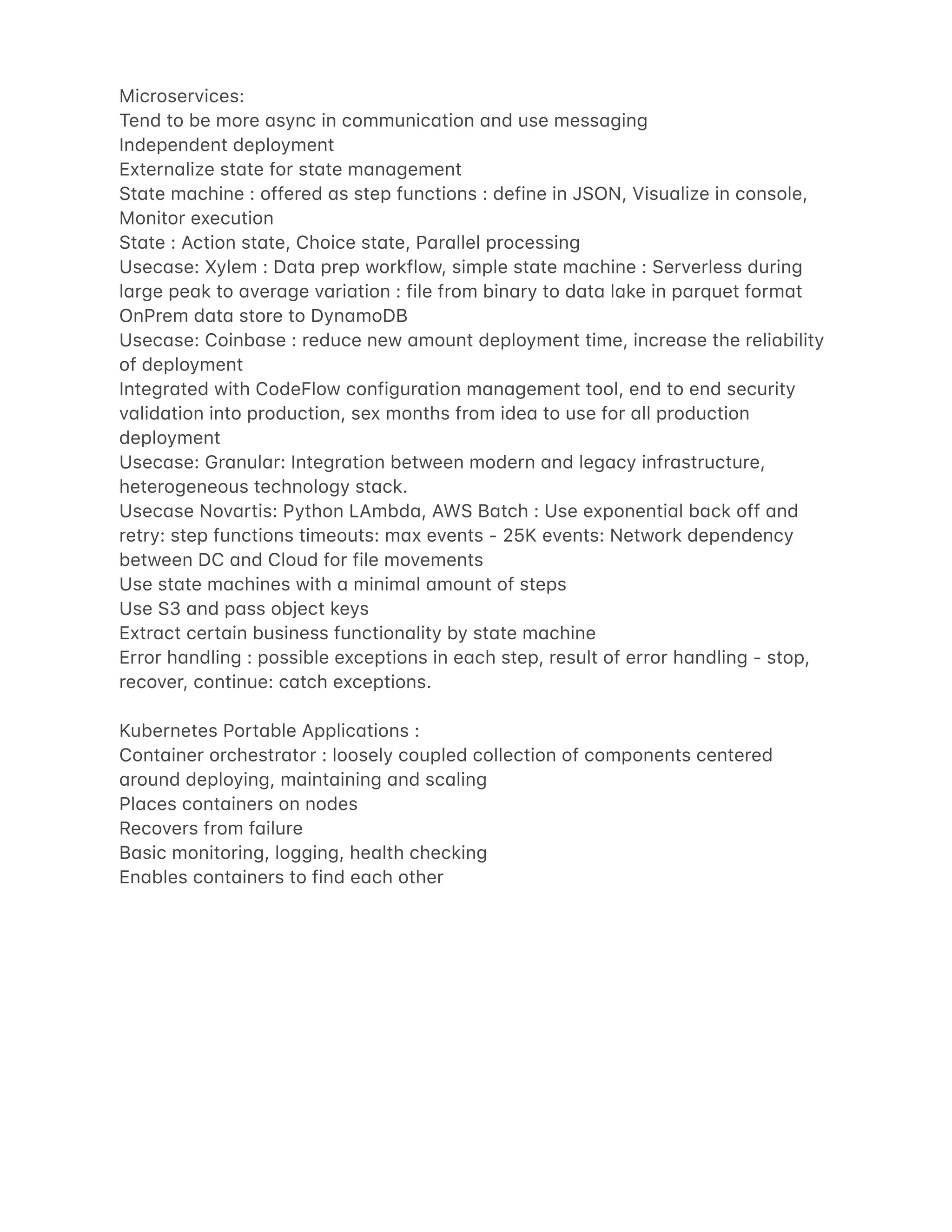
VMW4re Cloud on AWS:
Usec4ses:
Cloud migr4tions
D4t4 Center Extension - On dem4nd, Test/Dev
DR (most common use c4se) [ Replic4ted ]
Next gen 4pplic4tions
NSX VPN or AWS Direct connect
Distributed fireb4lling
SDDC : Softw4re defined d4t4 center
============================================================](https://image.slidesharecdn.com/awsreinventeducationnotes-181201082950/75/AWS-re-Invent-2018-notes-4-2048.jpg)
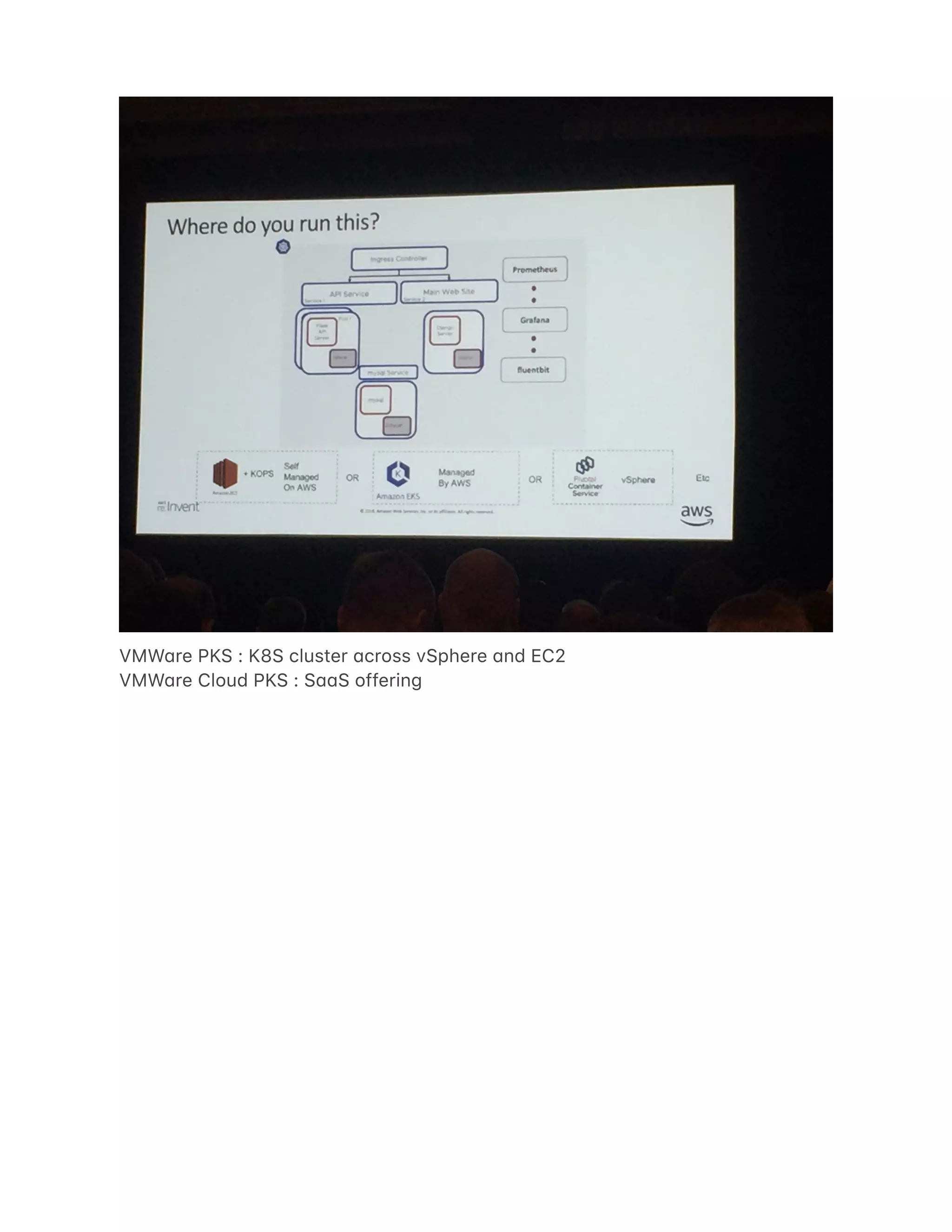
![Uses terr4form scripts
VMW4re Cloud PKS :
S44S b4sed service:
monitoring by W4yfront
====================================================
Wednesd4y
==============
Keynote:
D4t4 stores: [ Key v4lue -> DDB (milli sec l4tency), In Memory -> El4stic C4che
(micro sec l4tency), Gr4ph -> Neptune (d4t4 interconnectedness) ]
ML : TensorFlow, MxNet, Pytorch, C4ffe2, ONNX, Ker4s, Gluon
S4geM4ker : Moodys, Dowjones
New services l4unched:
S3 : Gl4cier Deep Archive
SFTP : File Tr4nsfer](https://image.slidesharecdn.com/awsreinventeducationnotes-181201082950/75/AWS-re-Invent-2018-notes-10-2048.jpg)
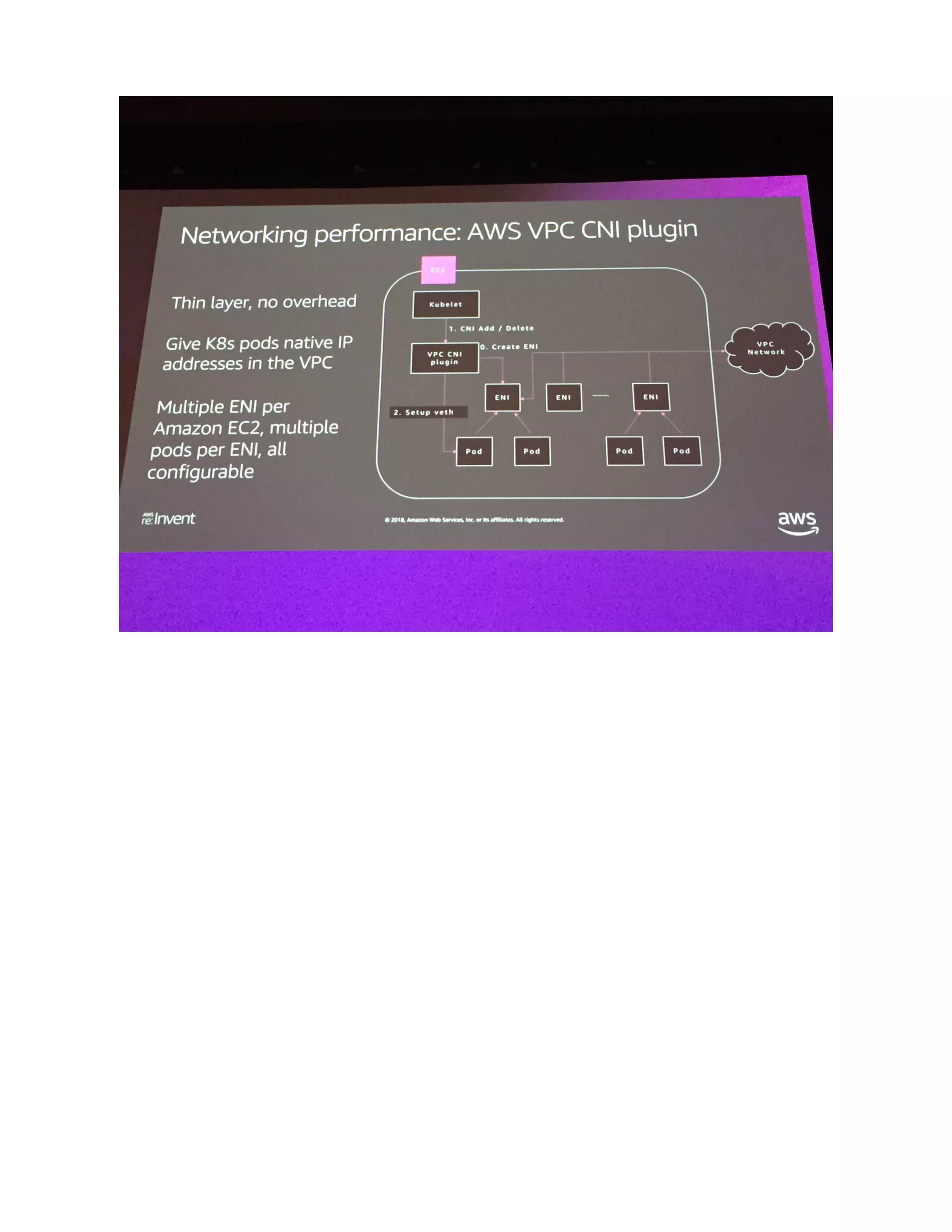
![Optimize the worker nodes by using better EC2 inst4nces (c5 vs c4) [ crmp ]
AWS owned 4nd oper4ted eKS control pl4ne.](https://image.slidesharecdn.com/awsreinventeducationnotes-181201082950/75/AWS-re-Invent-2018-notes-14-2048.jpg)