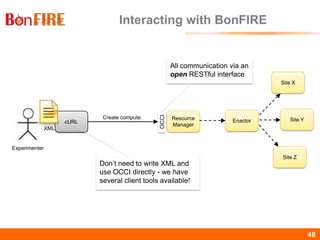
The document outlines the procedures and functionalities related to building service testbeds on the Bonfire platform, delivered in a webinar by Kostas Kavoussanakis. It includes information on the experiment lifecycle, prerequisites, resource management, and the use of client tools for creating and managing experiments. Additionally, it covers aspects such as monitoring, configuration, and the various testbed sites available within the Bonfire initiative.





![BonFIRE38 38
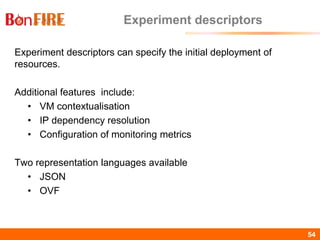
Experiment Descriptor
{
"name": "myExperiment", "description": “Controlled Network", "duration": 60,
"resources": [
{ "network": { "name": "myNetwork", "locations": ["be-ibbt"],
"address": "192.168.0.0", "size": "C",
"lossrate": 0, "bandwidth": 700, "latency": 0 }
},
{ "compute": { "name": "server", "locations": ["be-ibbt"],
"instanceType": "Large-EN", "min": 1,
"resources": [
{"storage": "@iperf-demo2"},
{"network": "@BonFIRE WAN"},
{"network": "myNetwork"}
],
"contexts": [] }
},
{ "compute": { "name": "client", "locations": ["be-ibbt"],
"instanceType": "Large-EN", "min": 1,
"resources": [
{"storage": "@iperf-demo2"},
{"network": "@BonFIRE WAN"},
{"network": "myNetwork"}
],
"contexts": [ {"IPERF_SERVER": ["server","myNetwork"]} ] }
}
]
}](https://image.slidesharecdn.com/bonfire-features-sites-tools-130529061555-phpapp02/85/BonFIRE-features-sites-and-tools-38-320.jpg)




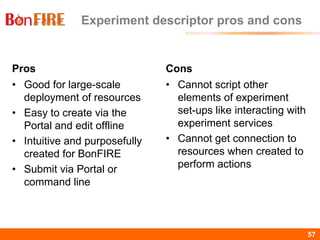
![BonFIRE56 56
JSON experiment description snippet
{
"name": "An experiment",
"description": "An experiment description ",
"duration": 60,
"resources": [
{
"compute": {
"name": "VM",
"locations": [
"fr-inria"
],
"instanceType": "small",
"min": 1,
...
20,](https://image.slidesharecdn.com/bonfire-features-sites-tools-130529061555-phpapp02/85/BonFIRE-features-sites-and-tools-56-320.jpg)
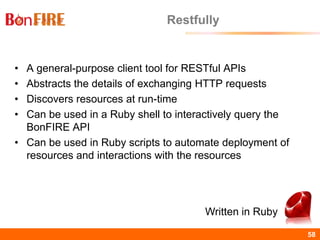
![BonFIRE60 60
Ruby script example
session = Restfully::Session.new(
:configuration_file => "~/.restfully/api.bonfire-project.eu.yml",
:gateway => "ssh.bonfire.grid5000.fr",
:keys => ["~/.ssh/id_rsa"])
begin
experiment = session.root.experiments.find{|e|
e['name'] == "Demo SSH" && e['status'] == "running"
} || session.root.experiments.submit(
:name => "Demo SSH",
:description => "SSH demo using Restfully - #{Time.now.to_s}",
:walltime => 8*3600 # 8 hours
)](https://image.slidesharecdn.com/bonfire-features-sites-tools-130529061555-phpapp02/85/BonFIRE-features-sites-and-tools-60-320.jpg)
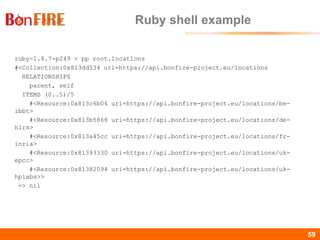
![BonFIRE63 63
Command line tools examples
Create experiment
• bfexperiment create <name> [-D <description>] [-W <walltime>]
[-G <group> ...]
• bfexperiment create my-experiment -D description -W 60 -G
bonfire
Create storage resource
• bfstorage create <name> <location> [<experiment>] [-D
<description>] [-S <size>] [-T {datablock|shared}] [-F <fstype>] [-
G <group> ...] [-P] [-R]
• bfstorage create my-storage fr-inria 42 -D storage-desc -S 1024
-T datablock -F ext3 -G bonfire](https://image.slidesharecdn.com/bonfire-features-sites-tools-130529061555-phpapp02/85/BonFIRE-features-sites-and-tools-63-320.jpg)