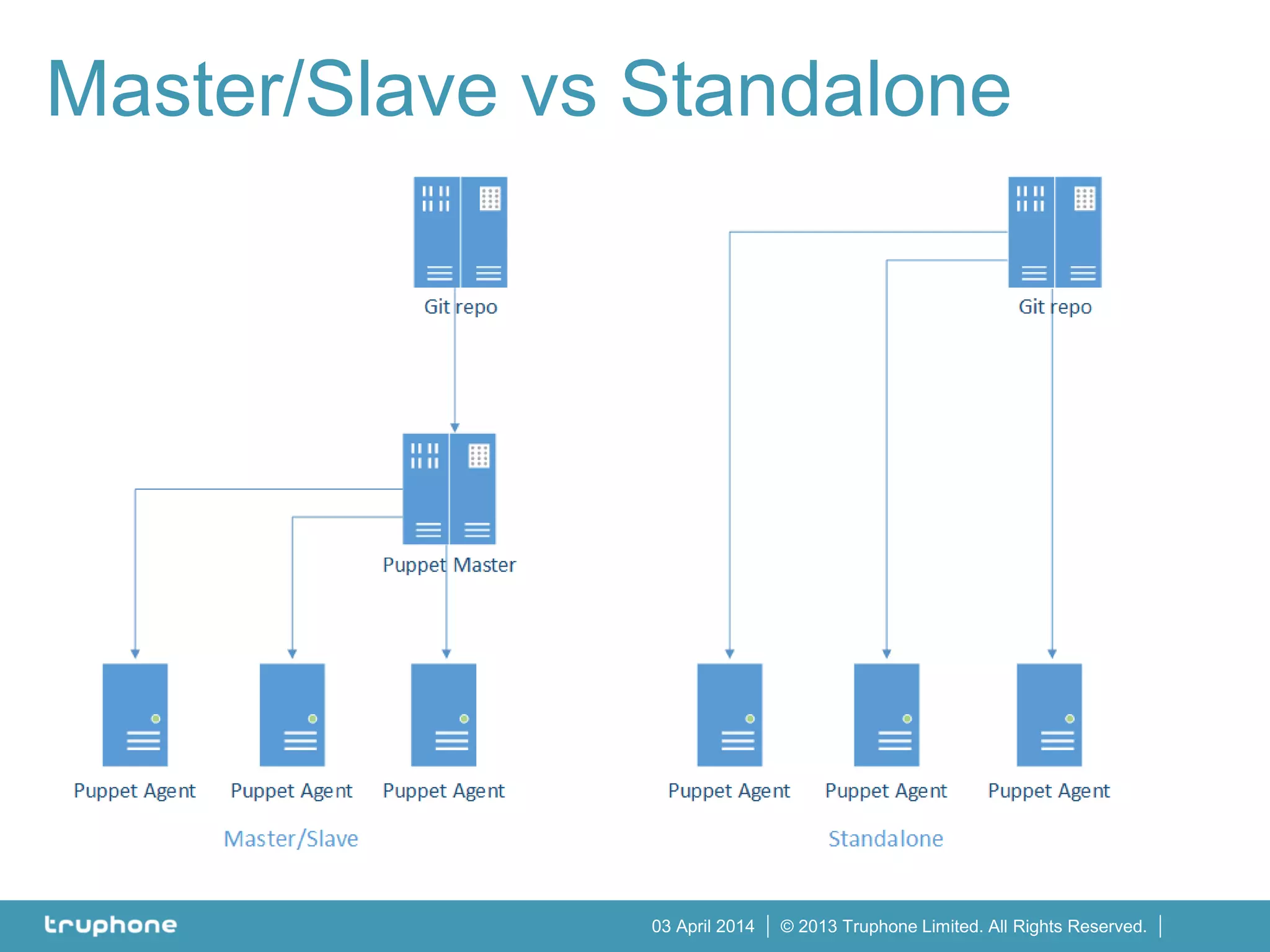
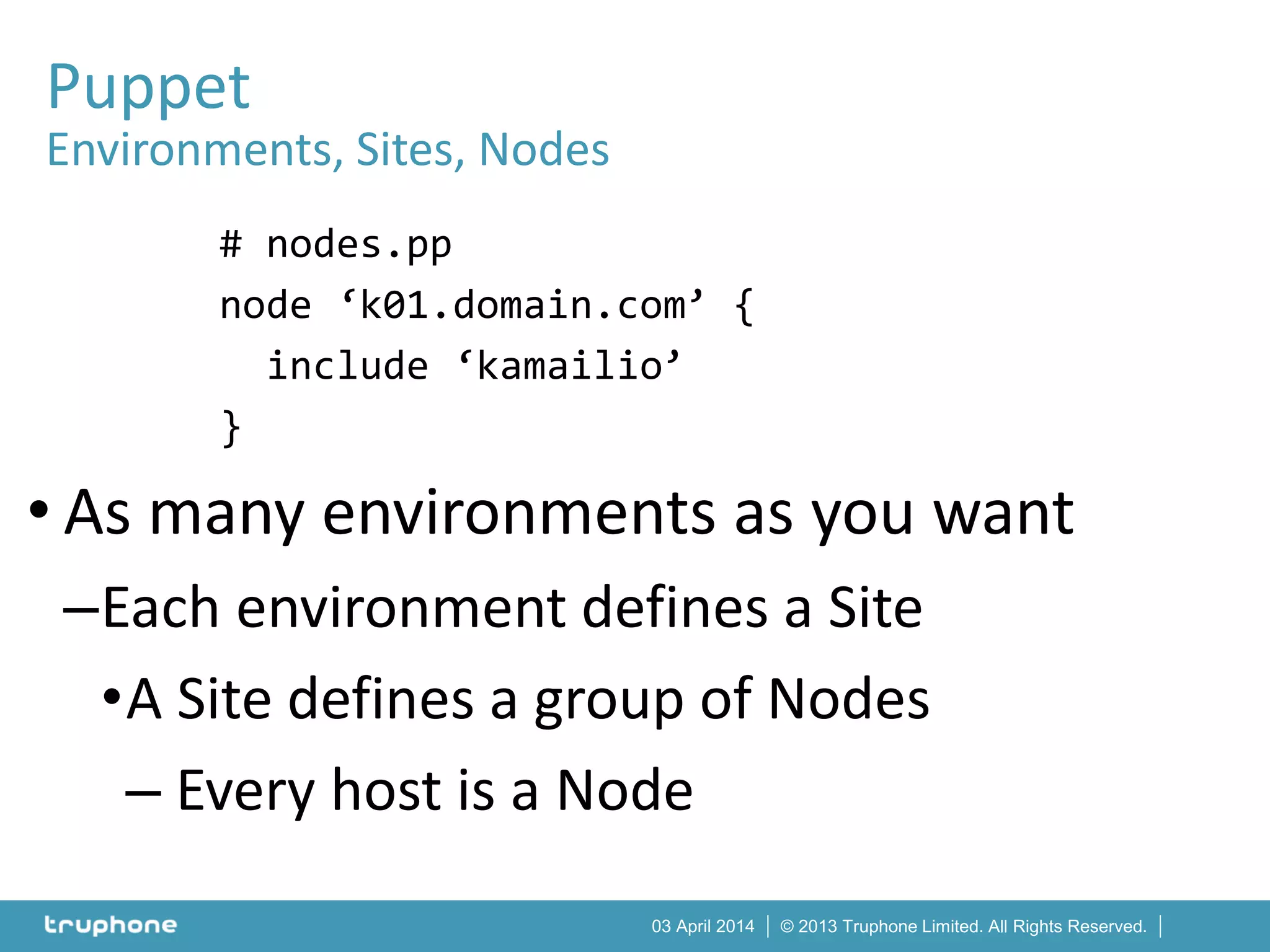
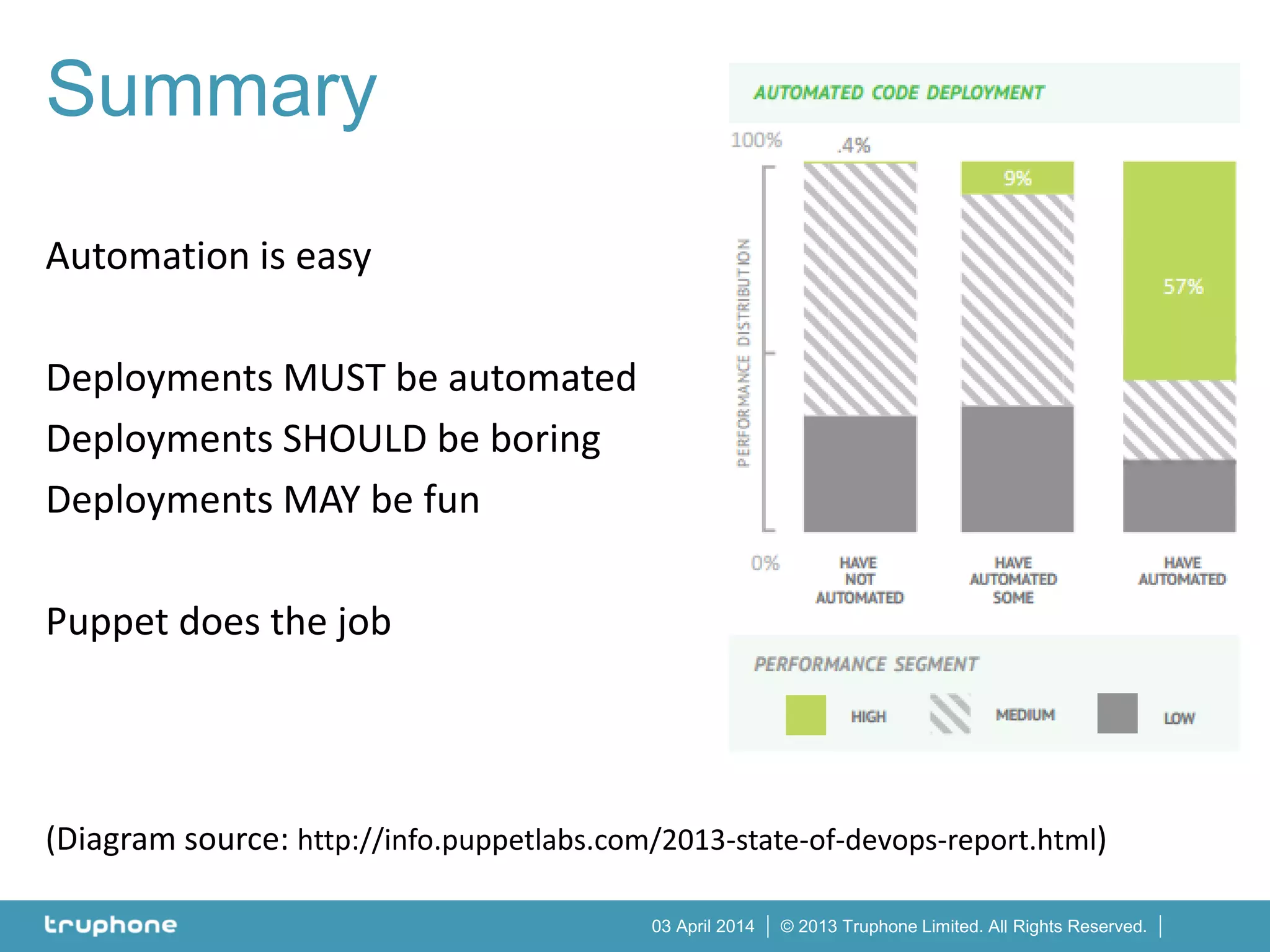
The document discusses the use of Puppet for automating the deployment of Kamailio, an open-source SIP server, by encapsulating configurations in manifests and modules for simplicity and efficiency. It emphasizes the importance of automation in deployments and provides guidance on setting up the system, managing configurations, and integrating with other tools. Additionally, it includes links to resources and tools to ensure best practices are followed during deployment.

![© 2013 Truphone Limited. All Rights Reserved.03 April 2014
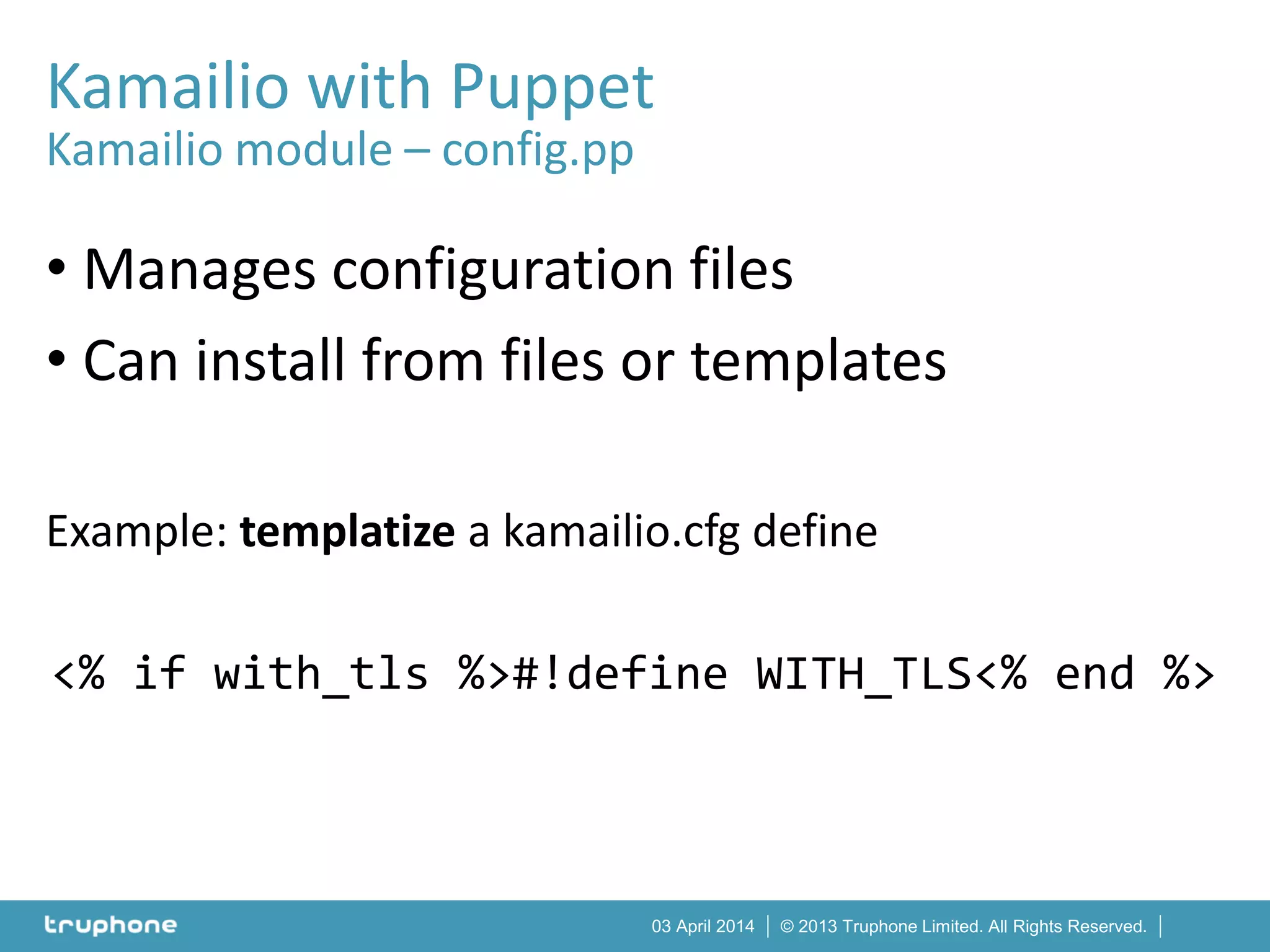
Kamailio with Puppet
Kamailio module – repo/apt.pp
class kamailio::repo::apt inherits kamailio::repo {
include '::apt'
# Note the 40!
apt::source { 'kamailio40_wheezy':
location => 'http://deb.kamailio.org/kamailio40',
release => 'wheezy',
repos => 'main',
required_packages => 'debian-keyring debian-archive-keyring',
key => '07D5C01D',
key_server => 'http://deb.kamailio.org/kamailiodebkey.gpg',
include_src => true,
}
Apt::Source['kamailio40_wheezy'] -> Package<|tag == 'kamailio'|>
}](https://image.slidesharecdn.com/automatickamailiodeploymentswithpuppet-140403092105-phpapp02/75/Automatic-Kamailio-Deployments-With-Puppet-18-2048.jpg)