This document presents a framework for collecting and evaluating fall-related data using mobile devices. The framework includes a test client application for mobile devices that allows clinical mobility tests to be performed and acceleration data to be recorded. A proof-of-concept was developed using an iPhone to record acceleration data during mobility tests. The recorded data was then analyzed to evaluate the potential for fall detection using mobile devices. The framework is intended to support integration of various sensor-enabled devices and allow collected data to be accessed for further analysis.
![Assessment Test Framework for Collecting and Evaluating Fall-Related Data Using Mobile Devices 3
Introduction
• Motivated by the demographic trend
[van den Broek et al., 2009]
• average age will increase
• impact on healthcare systems, retirement plans
• more people will need assistance or support
• Falls and fall-related injuries
• Mobile Devices
• device of the future: “the steady companion”
Stefan Almer July 11th, 2012](https://image.slidesharecdn.com/presentation-120705121358-phpapp01/75/Assessment-Test-Framework-for-Collecting-and-Evaluating-Fall-Related-Data-using-Mobile-Devices-3-2048.jpg)
![Assessment Test Framework for Collecting and Evaluating Fall-Related Data Using Mobile Devices 4
Fall Prevention
[Todd and Skelton, 2004; WHO, 2007; Tremblay Jr. and Barber, 2005; LeMier et al., 2002; BRAID, 2010]
• Common methods
• assessment tests
• adjustment of environment and walking aids
• gait analysis
• education
• exercise/training
• Differ in usage based on context
Stefan Almer July 11th, 2012](https://image.slidesharecdn.com/presentation-120705121358-phpapp01/75/Assessment-Test-Framework-for-Collecting-and-Evaluating-Fall-Related-Data-using-Mobile-Devices-4-2048.jpg)
![Assessment Test Framework for Collecting and Evaluating Fall-Related Data Using Mobile Devices 5
Fall Detection
• Five phases of a fall
1) Activity 2) Hard- 3) Free-fall 4) Impact 5) Optional
of daily living predictable event recovery
Fig. 1: Fall Phases [Abbate et al., 2010]
• Classification of fall detection methods [Yu, 2008]
• wearable device / camera-based / ambience device
• Important to differentiate between a fall and
activities of daily living
Stefan Almer July 11th, 2012](https://image.slidesharecdn.com/presentation-120705121358-phpapp01/75/Assessment-Test-Framework-for-Collecting-and-Evaluating-Fall-Related-Data-using-Mobile-Devices-5-2048.jpg)
![Assessment Test Framework for Collecting and Evaluating Fall-Related Data Using Mobile Devices 6
Mobile Devices for Fall Detection
[Columbus, 2011; Noury et al., 2007; Kangas et al., 2007]
• Classic approach
• “Individual” devices and sensors
• New approach: Mobile Devices
• equipped with required hardware: accelerometer
• software capabilities to read acceleration data
• Method: measure body acceleration
• fall has higher acceleration
• acceleration threshold to determine fall
• problem: position of sensor
Stefan Almer July 11th, 2012](https://image.slidesharecdn.com/presentation-120705121358-phpapp01/75/Assessment-Test-Framework-for-Collecting-and-Evaluating-Fall-Related-Data-using-Mobile-Devices-6-2048.jpg)
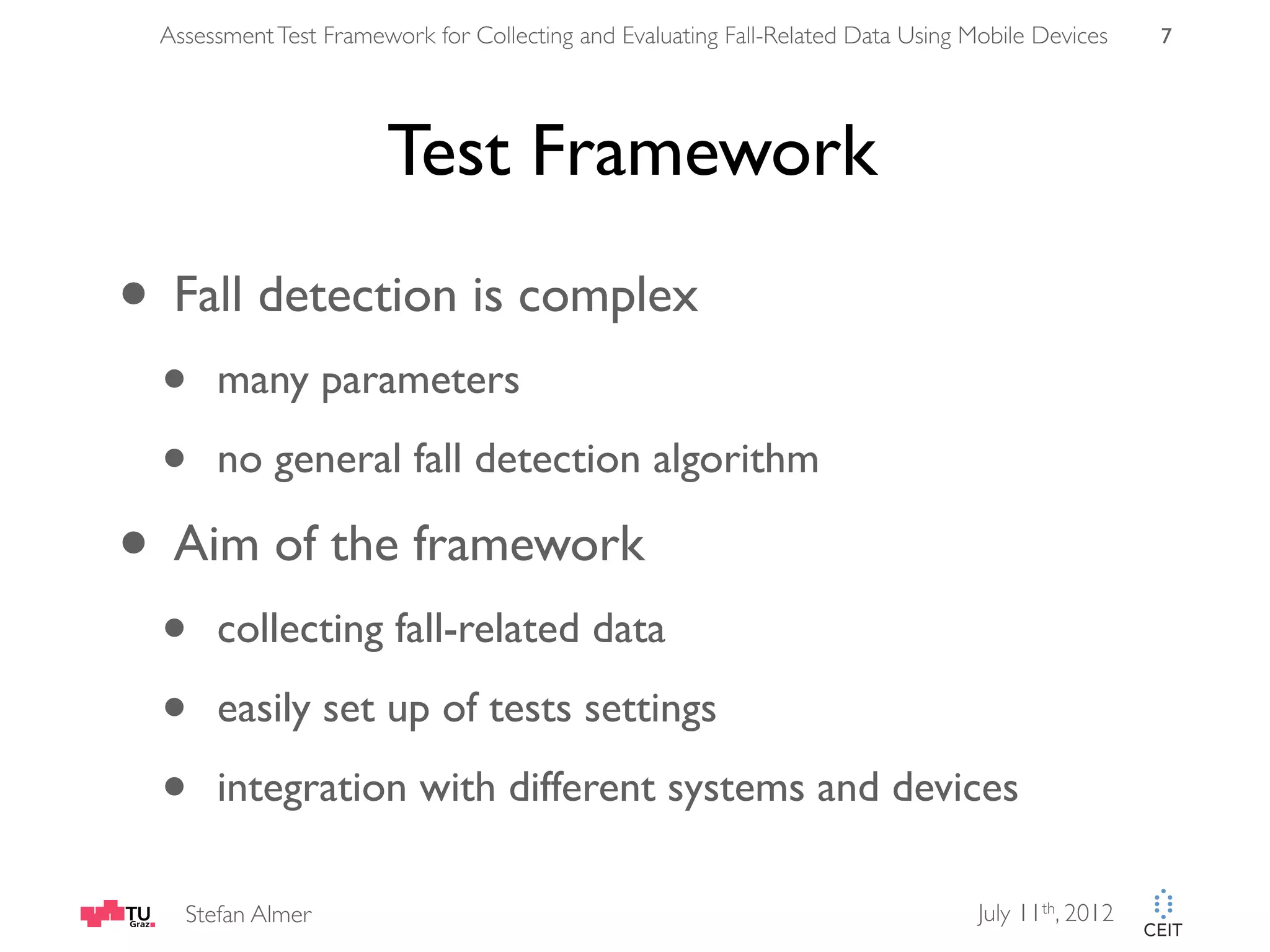
![Assessment Test Framework for Collecting and Evaluating Fall-Related Data Using Mobile Devices 9
Framework Architecture [Helic, 2008]
• Based on 3-tier architecture
Data Tier Application Tier Client Tier
Interface
HTTP
Database JDBC
Java (Web service)
Client
(Browser/
iOS)
Static Content HTTP
(Backend)
Fig. 3: Framework Architecture
Stefan Almer July 11th, 2012](https://image.slidesharecdn.com/presentation-120705121358-phpapp01/75/Assessment-Test-Framework-for-Collecting-and-Evaluating-Fall-Related-Data-using-Mobile-Devices-9-2048.jpg)
![Assessment Test Framework for Collecting and Evaluating Fall-Related Data Using Mobile Devices 11
Evaluation
• 3 clinical mobility tests were
performed
[Podsiadlo and Richardson, 1991; Whitney et al., 2005; Lewis and Shaw, 2005]
• “Sit-to-Stand 5”, “Timed Up and
Go”, “2-Minute-Walk”
• iPhone 4, worn on hip height,
50Hz sample rate
• Tests analyzed afterwards
Fig. 5: User wears Device while performing test
Stefan Almer July 11th, 2012](https://image.slidesharecdn.com/presentation-120705121358-phpapp01/75/Assessment-Test-Framework-for-Collecting-and-Evaluating-Fall-Related-Data-using-Mobile-Devices-11-2048.jpg)
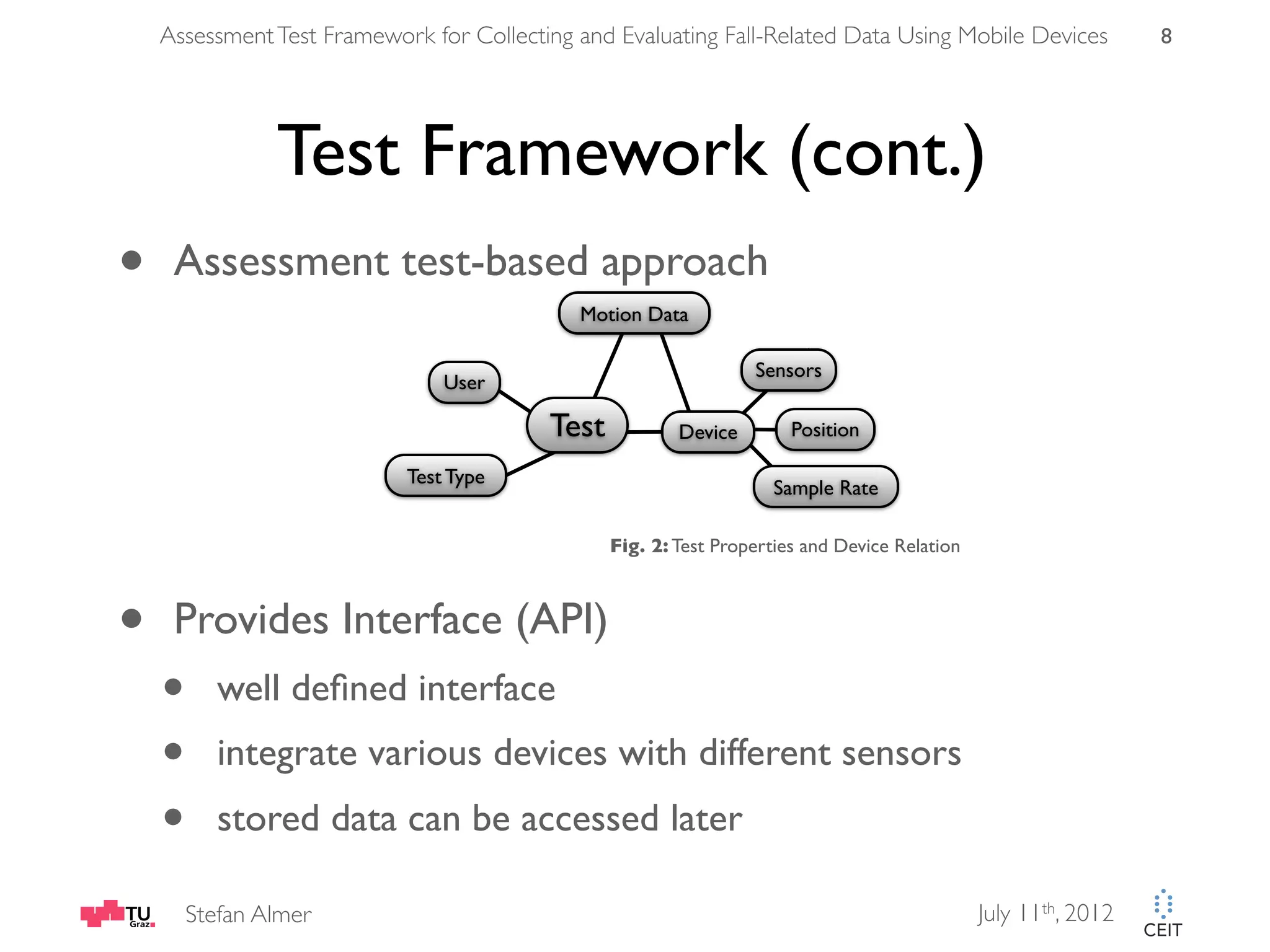
![Assessment Test Framework for Collecting and Evaluating Fall-Related Data Using Mobile Devices 12
Evaluation (cont.)
• Movement analysis of recorded gait data
• sensor accurate enough to perform fall detection
• Data analysis and future extraction (peak detection,
knowledge methods, statistical analysis)
1.4
3 m straight walk turn phase
1.2 3 m straight walk
sit phase
sit down phase sit phase
1
0.8
SVM [g]
0.6
0.4
0.2
0
0 100 200 300 400 500 600 700 800 900 1000
datapoints [n] - movement data recorded with 50 Hz
Fig.6: Timed Up and Go Test (Individual Phases)
Stefan Almer July 11th, 2012](https://image.slidesharecdn.com/presentation-120705121358-phpapp01/75/Assessment-Test-Framework-for-Collecting-and-Evaluating-Fall-Related-Data-using-Mobile-Devices-12-2048.jpg)
![[Abbate et al., 2010] Abbate, S., Avvenuti, M., Corsini, P., Vecchio, A., and Light, J., 2010. Monitoring of Human Movements for Fall Detection and Activities Recognition in
Elderly Care using Wireless Sensor Network: A Survey. InTech. ISBN 9789533073217.
[BRAID, 2010] BRAID, 2010. Falls Prevention. http://capsil.braidproject.eu/index.php?title=Falls_Prevention&oldid=6250. Last accessed November 2, 2011.
[Columbus, 2011] Columbus, L., 2011. Gartner Releases Hype Cycle for Networking and Communications, 2011. http://softwarestrategiesblog.com/2011/08/27/gartner-
releases-hype-cycle-for-networking-and-communications-2011/. Last accessed October 12, 2011.
[Helic, 2008] Helic, D., 2008. Software Architecture VO/KU. http://coronet.iicm.tugraz.at/sa/s5/sa_styles1.html. Last accessed October 6, 2011.
[Kangas et al., 2007] Kangas, M., Konttila, A., Winblad, I., Jämsa, T., 2007. Determination of Simple Thresholds for Accelerometry-Based Parameters for Fall Detection. In Proc.
of the 29th Annual International Conference of the Engineering in Medicine and Biology Society, volume 2007, pages 1367–1370. doi:10.1109/IEMBS.2007.4352552.
[LeMier et al., 2002] LeMier, M., Silver, I., Bowe, C., 2002. Falls Among Older Adults: Strategies for Prevention. Technical Report, Washington State Department of Health.
http://www.doh.wa.gov/hsqa/emstrauma/injury/pubs/FallsAmongOlderAdults.pdf. Last accessed November 2, 2011.
[Lewis and Shaw, 2005] Lewis, C., Shaw, K., 2005. Benefits of the 2-Minute Walk Test. Physical Therapy & Rehab Medicine, 16(16). http://physical-
therapy.advanceweb.com/Article/Benefits-of-the-2-Minute-Walk-Test.aspx. Last accessed October 1, 2011.
[Noury et al., 2007] Noury, N., Fleury, A., Rumeau, P., Bourke, A.K., Ó Laighin, G., Rialle V., Lundy, J.E., 2007. Fall Detection - Principles and Methods. In Proc. of the 29th
Annual International Conference of the Engineering in Medicine and Biology Society, pages 1663–1666. IEEE. doi:10.1109/IEMBS.2007.4352627.
[Podsiadlo and Richardson, 1991] Podsiadlo, D., Richardson, S., 1991. The Timed ’Up & Go’: A Test of Basic Functional Mobility for Frail Elderly Persons. American Geriatrics
Society, 39(2), pages 142–148. ISSN 00028614. http://www.ncbi.nlm.nih.gov/pubmed/1991946. Last accessed October 1, 2011.
[Todd and Skelton, 2004] Todd, C., Skelton, D., 2004. What are the main risk factors for falls among older people and what are the most effective interventions to prevent
these falls? Technical Report, WHO Regional Office for Europe. http://www.euro.who.int/document/E82552.pdf. Last accessed November 2, 2011.
[Tremblay Jr. and Barber, 2005] Tremblay Jr., K.R., Barber, C.E., 2005. Preventing Falls in the Elderly. http://www.ext.colostate.edu/pubs/consumer/10242.pdf. Last accessed
November 2, 2011.
[van den Broek et al., 2009] van den Broek, G., Cavallo, F., Odetti, L., Wehrmann, C., 2009. Ambient Assisted Living Roadmap. http://www.aaliance.eu/public/documents/
aaliance-roadmap/aaliance-aal-roadmap.pdf. Last accessed October 20, 2011.
[WHO, 2007] WHO, 2007. WHO Global Report on Falls Prevention in Older Age. http://www.who.int/ageing/publications/Falls_prevention7March.pdf. Last accessed
November 2, 2011.
[Whitney et al., 2005] Whitney, S., Wrisley, D.M., Marchetti, G.F., Gee, M.A., Redfern, S.M., Furman J.M., 2005. Clinical Measurement of Sit-To-Stand Performance in People
With Balance Disorders: Validity of Data for the Five-Times Sit-To-Stand Test. Physical Therapy, 85(10), pages 1034–1045. ISSN 00319023. http://www.ncbi.nlm.nih.gov/
pubmed/16180952. Last accessed October 1, 2011.
[Yu, 2008] Yu, X., 2008. Approaches and Principles of Fall Detection for Elderly and Patient. In Proc. of the 10th International Conference on e-Health Networking,
Applications and Services, pages 42–47. IEEE. doi:10.1109/HEALTH.2008.4600107.](https://image.slidesharecdn.com/presentation-120705121358-phpapp01/75/Assessment-Test-Framework-for-Collecting-and-Evaluating-Fall-Related-Data-using-Mobile-Devices-15-2048.jpg)