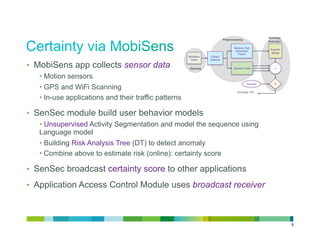
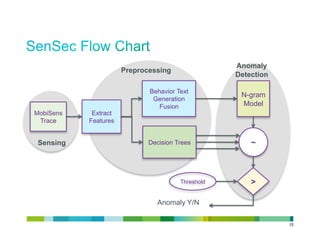
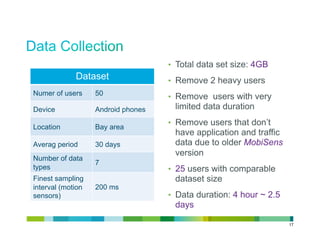
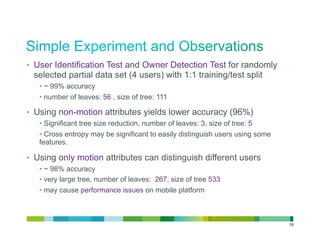
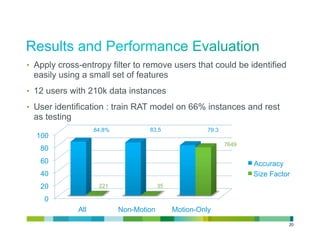
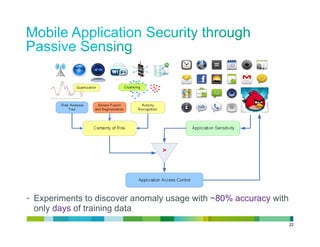
The document proposes a smartphone-based behavioral authentication system called SenSec. It collects sensor data to build user behavior models. Features are extracted from the sensor data and used to build risk analysis trees to detect anomalies. When anomalies are detected, a certainty score is broadcast and can trigger authentication for sensitive applications. The system was tested on a dataset of 25 users, achieving over 98% accuracy in user identification. Extensions and integrations with other systems are discussed to enhance security, privacy, and energy efficiency.



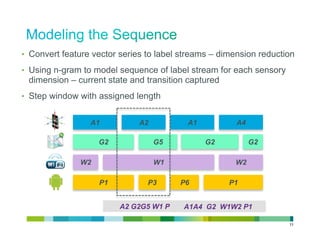
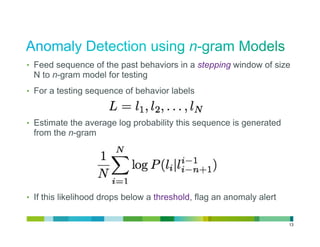
![• Feature vector calculated from a step window represent the
behavior state within a given time window
• surrounding environment: GPS location, WiFi signal
• activity: motions, applications in use
• communication: network traffic
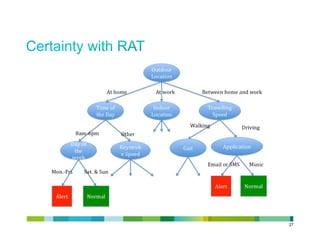
• Using Decision Tree to detect anomaly in behaviors
• Each node represents a feature dimension
• Leaves can be one of the following
• Owner Detection: owner [0,1], 0: Anomaly, 1: Normal
• User Identification: user id [0,1,…. N], user’s identification, i.e. IMEI
• Multiple trees can be built with subset of feature space
• Weighted average
• Voting
10](https://image.slidesharecdn.com/sensecfinal-120821002453-phpapp02/85/SenSec-Mobile-Application-Security-through-Passive-Sensing-10-320.jpg)
![• Motion Sensors (100)
• Used to summarize
acceleration stream
• Calculated separately for each
dimension [x,y,z,m]
• GPS: location label via density based clustering (1)
• WiFi: (SSIDs, RSSIs) pairs ranked by signal strength (6)
• Applications: Bitmap of well-known applications (60 + 1)
• Application Traffic Pattern: Tx/Rx traffic vectors (120 + 2)
• Step Window Size: 5 seconds
18](https://image.slidesharecdn.com/sensecfinal-120821002453-phpapp02/85/SenSec-Mobile-Application-Security-through-Passive-Sensing-18-320.jpg)



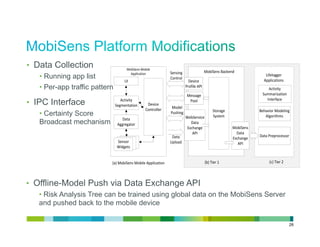
![• Reactive API to Team Access
API call from Team Access to SenSec to retrieve the current Certainty Score
given the context
getCertaintyScore(SenSecContextType ctx, count)
• Proactive API to Team Acess and other equivalent modules
Broadcast Receiver on Certainty Score
certaintyScore{
CertaintyScoreType scores[];
WindowSizeType window_size;
SenSecContextType ctx;
}
30](https://image.slidesharecdn.com/sensecfinal-120821002453-phpapp02/85/SenSec-Mobile-Application-Security-through-Passive-Sensing-30-320.jpg)