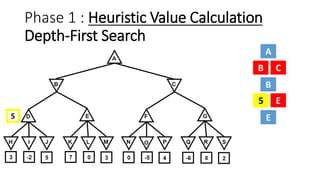
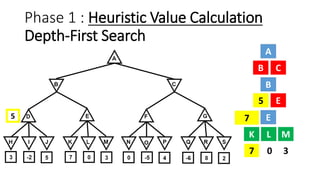
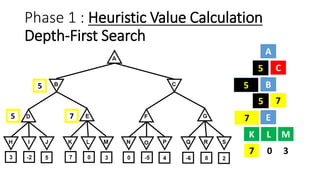
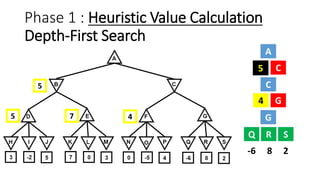
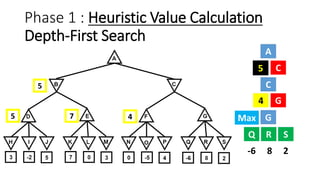
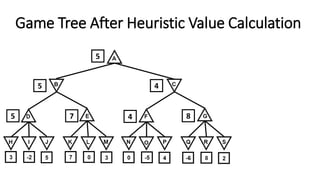
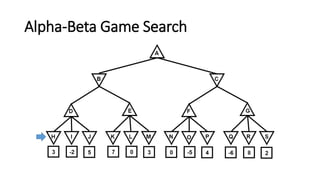
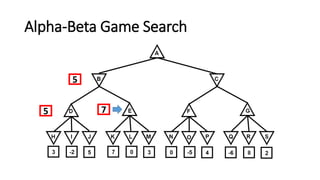
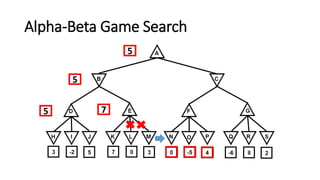
The document discusses the minimax game search algorithm used in artificial intelligence, explaining how two players (max and min) take turns to optimize their scores. It details the process of finding heuristic values for nodes, the steps involved in the search, and introduces alpha-beta pruning as a more efficient modification that avoids exploring less useful nodes. The text concludes by highlighting that if both players play optimally, max will win with a specific score, emphasizing the benefits of using alpha-beta pruning over traditional minimax.