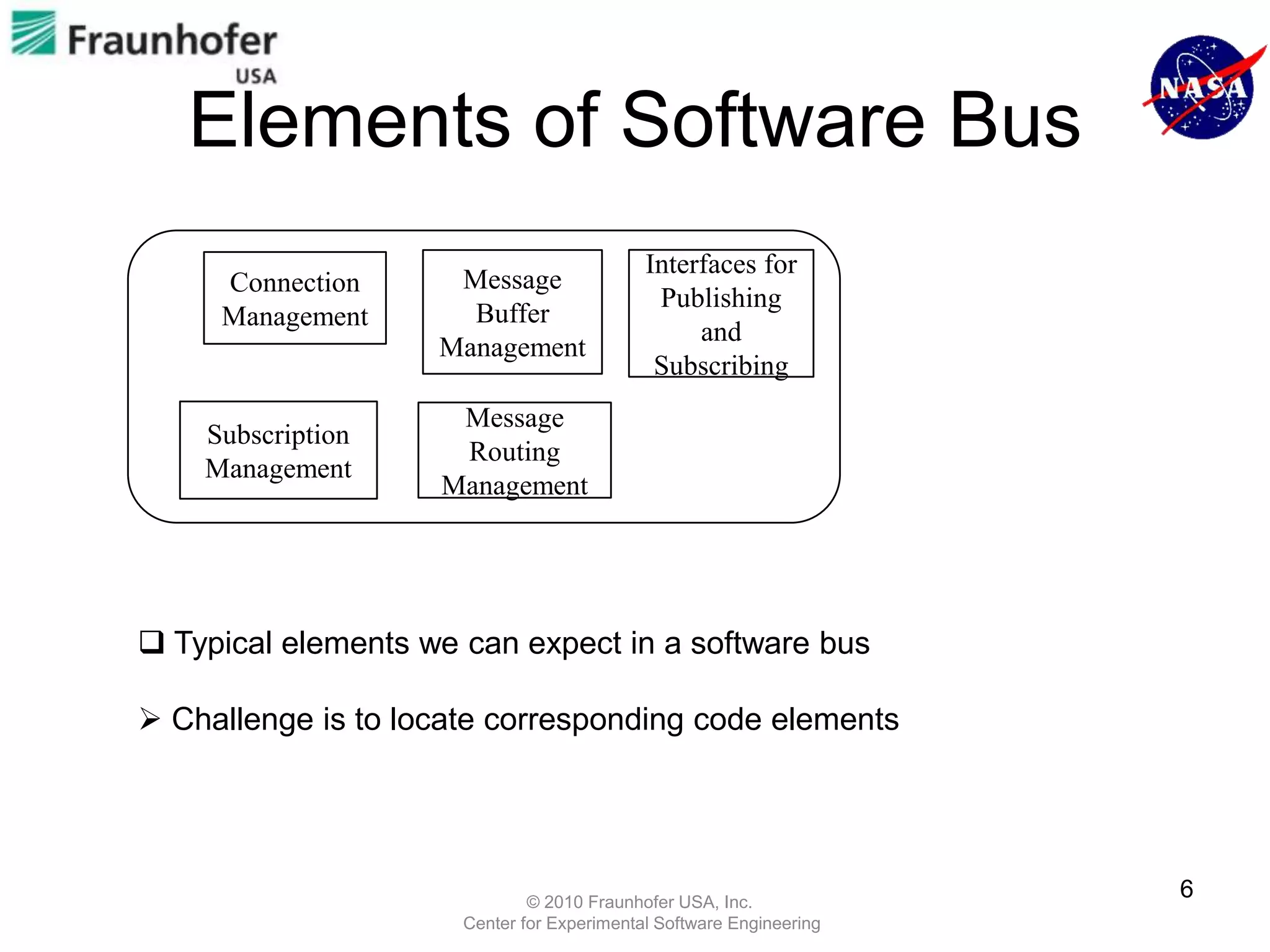
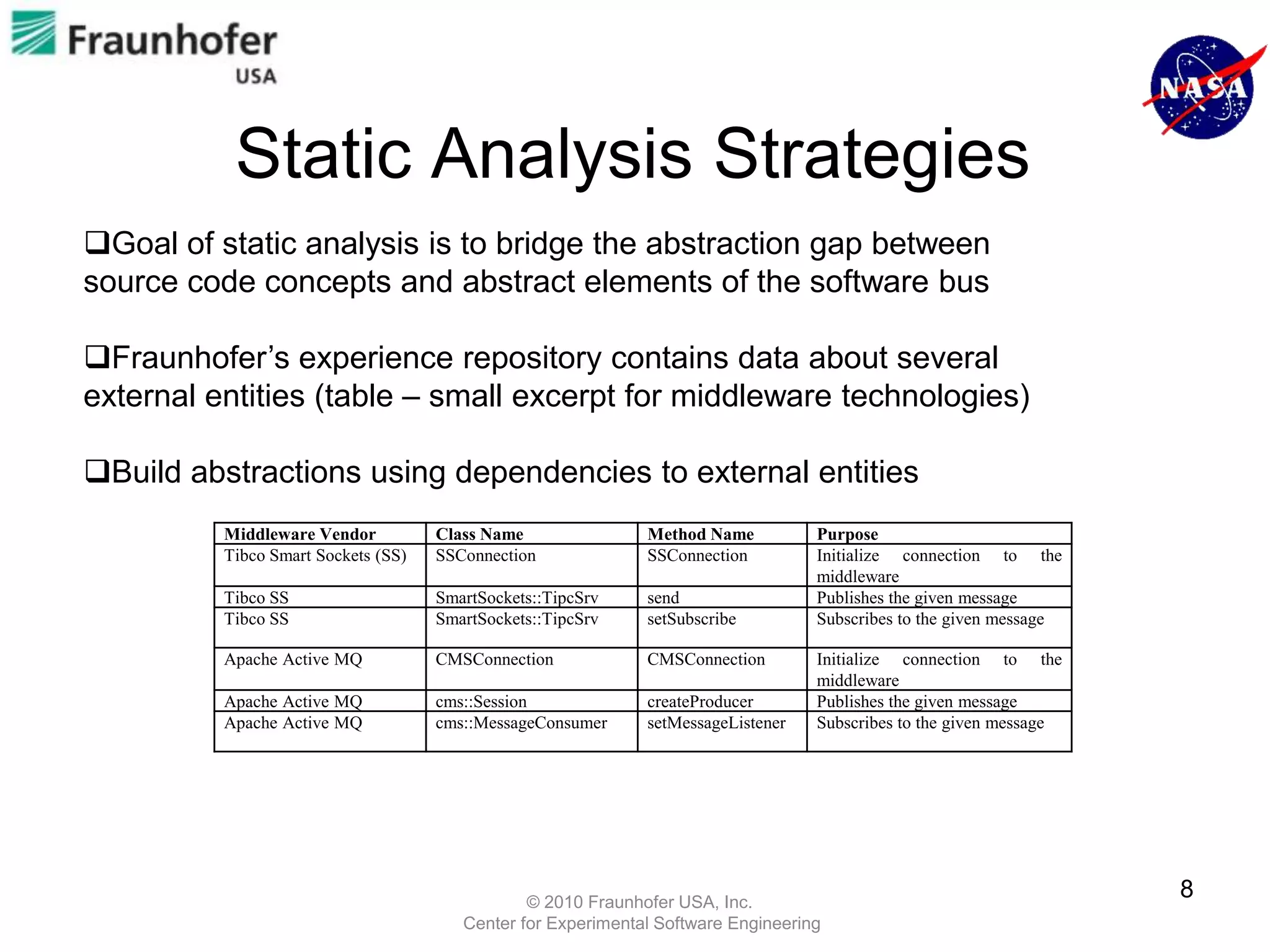
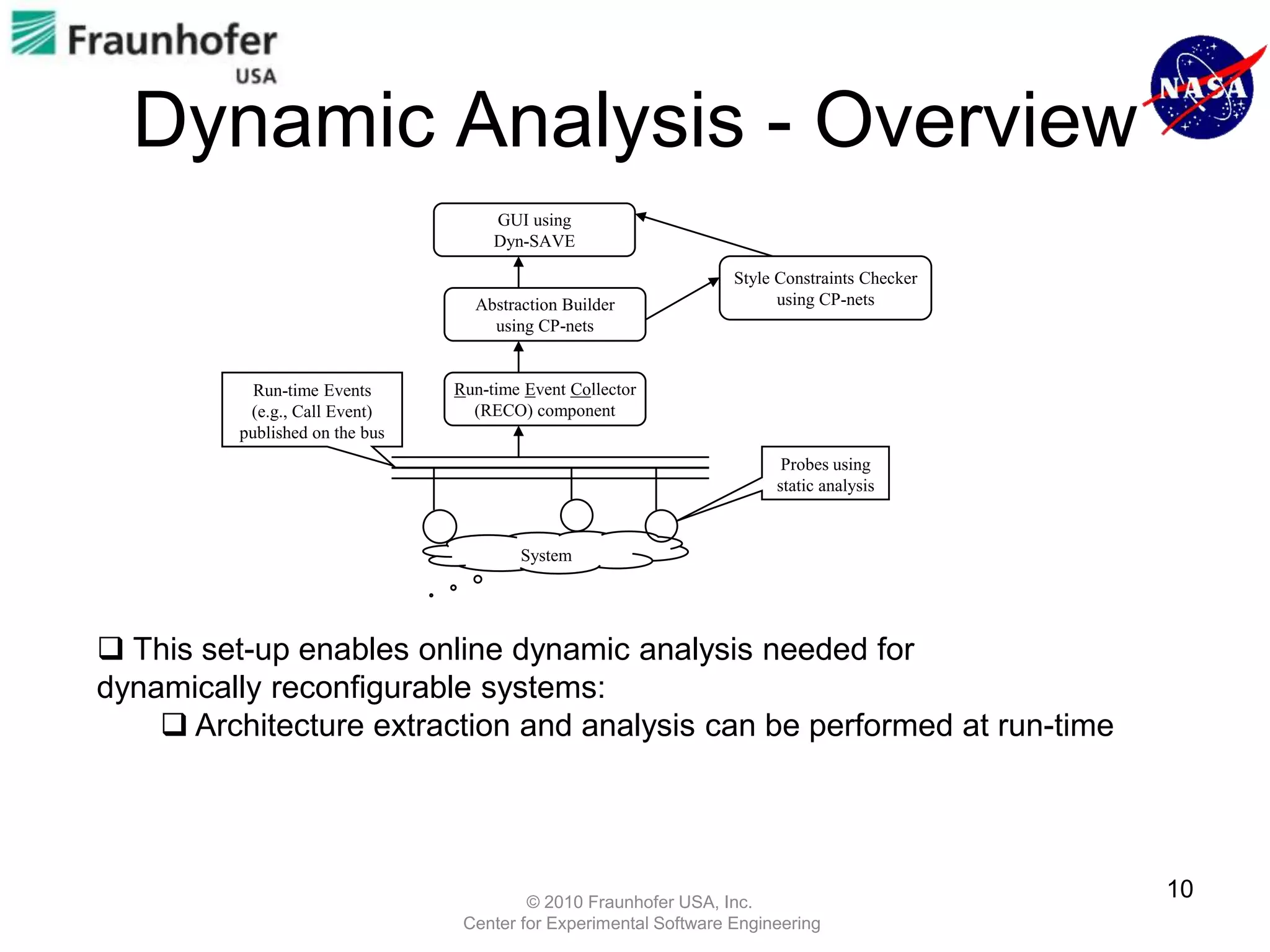
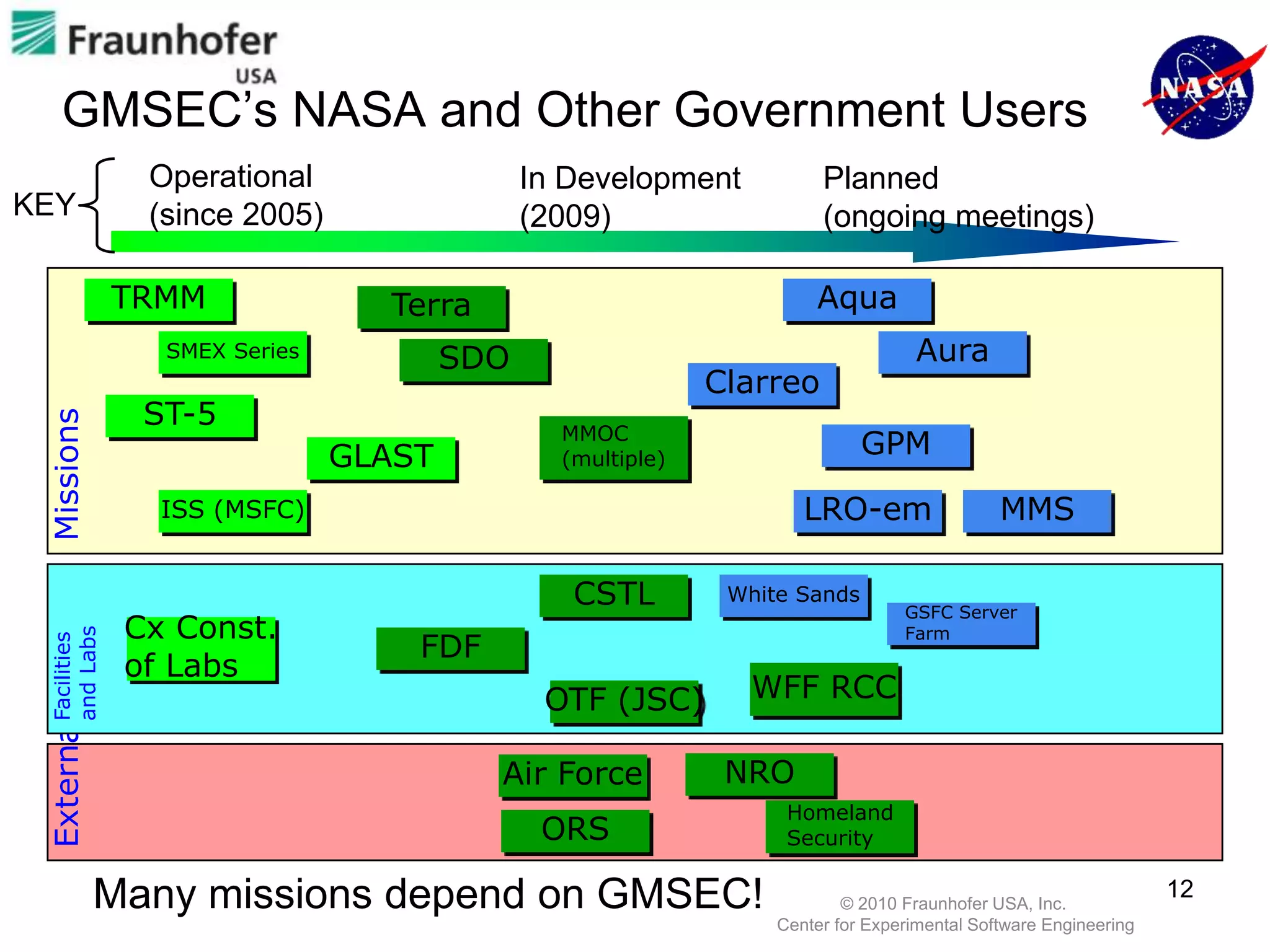
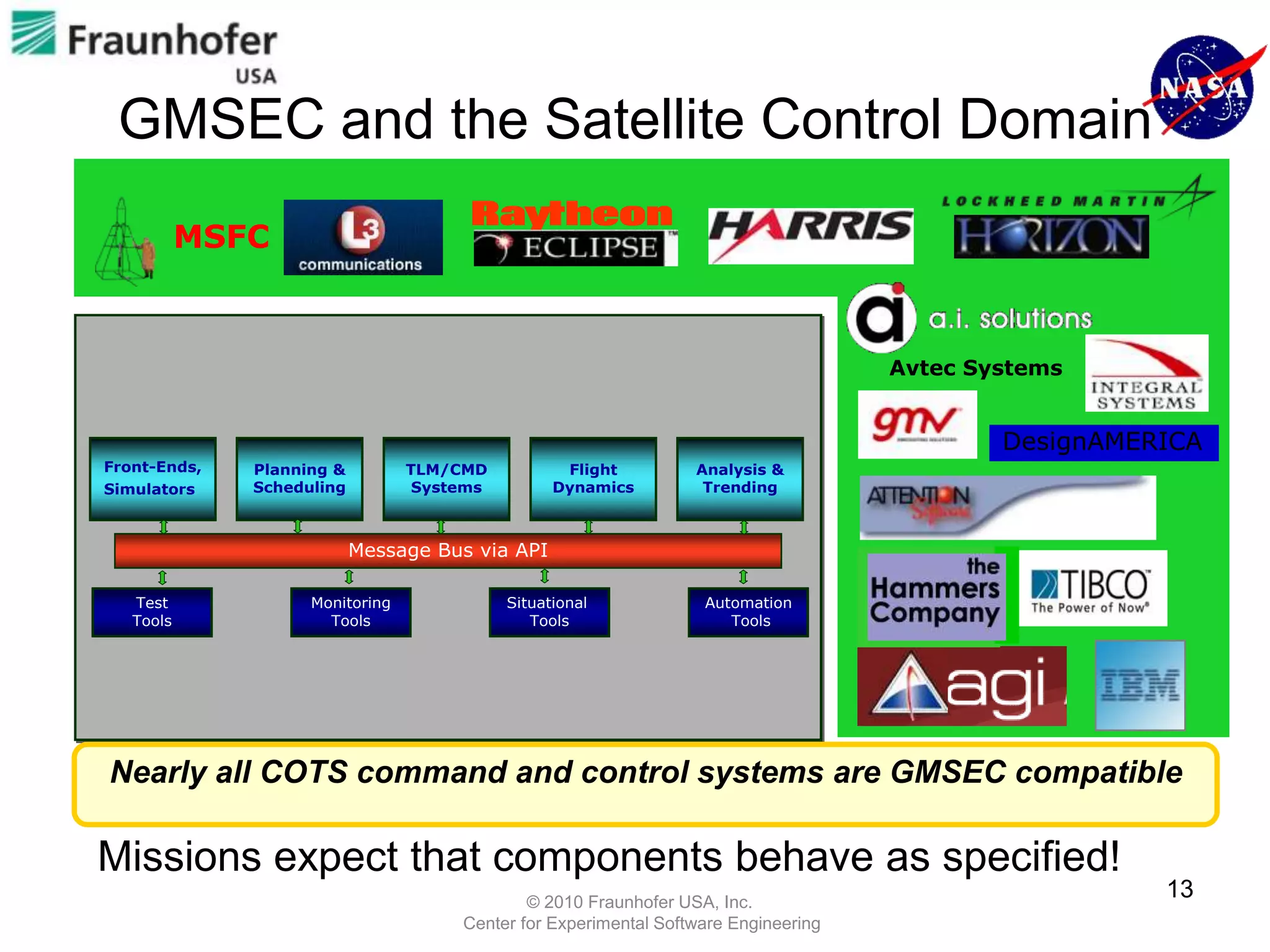
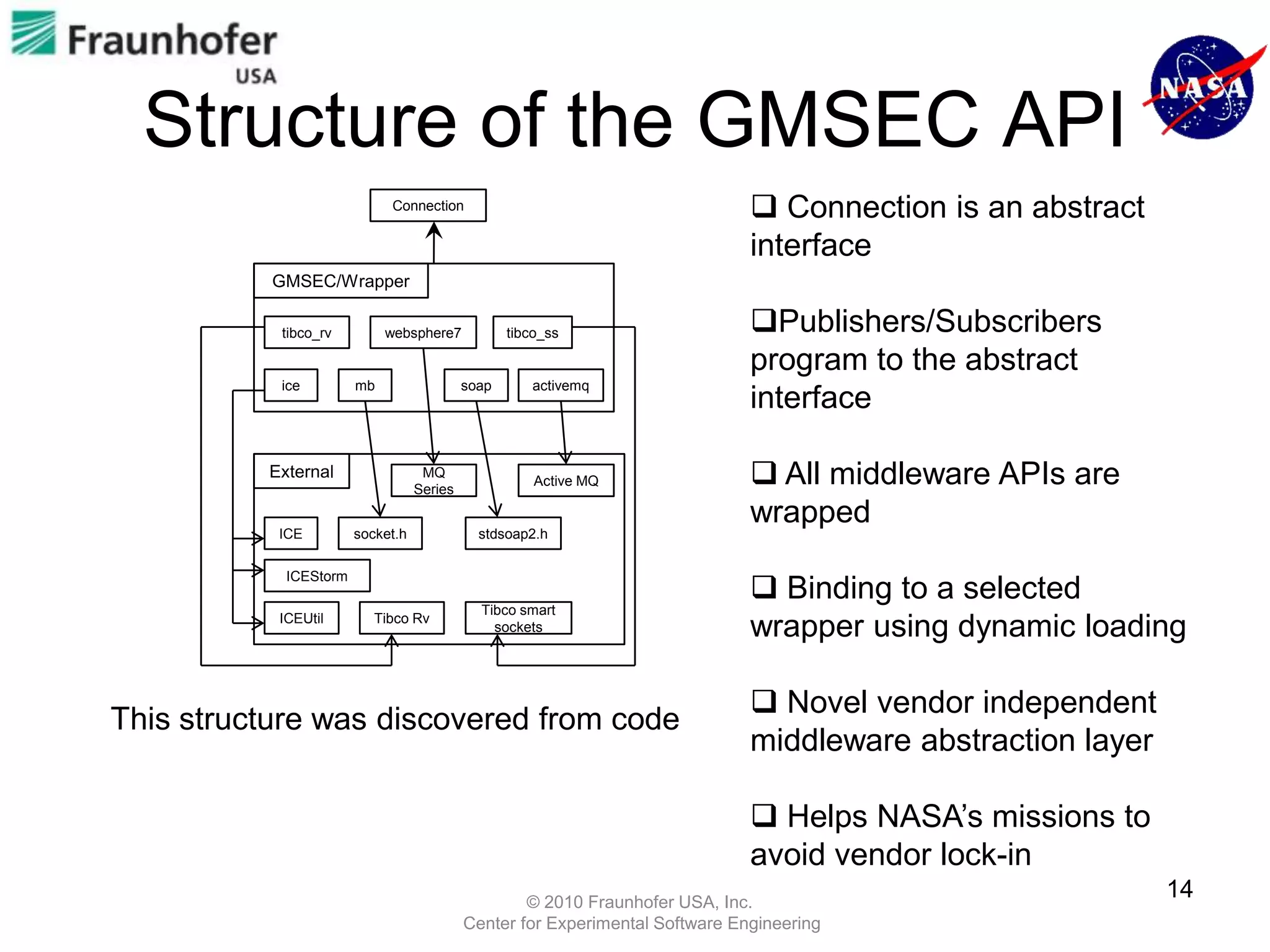
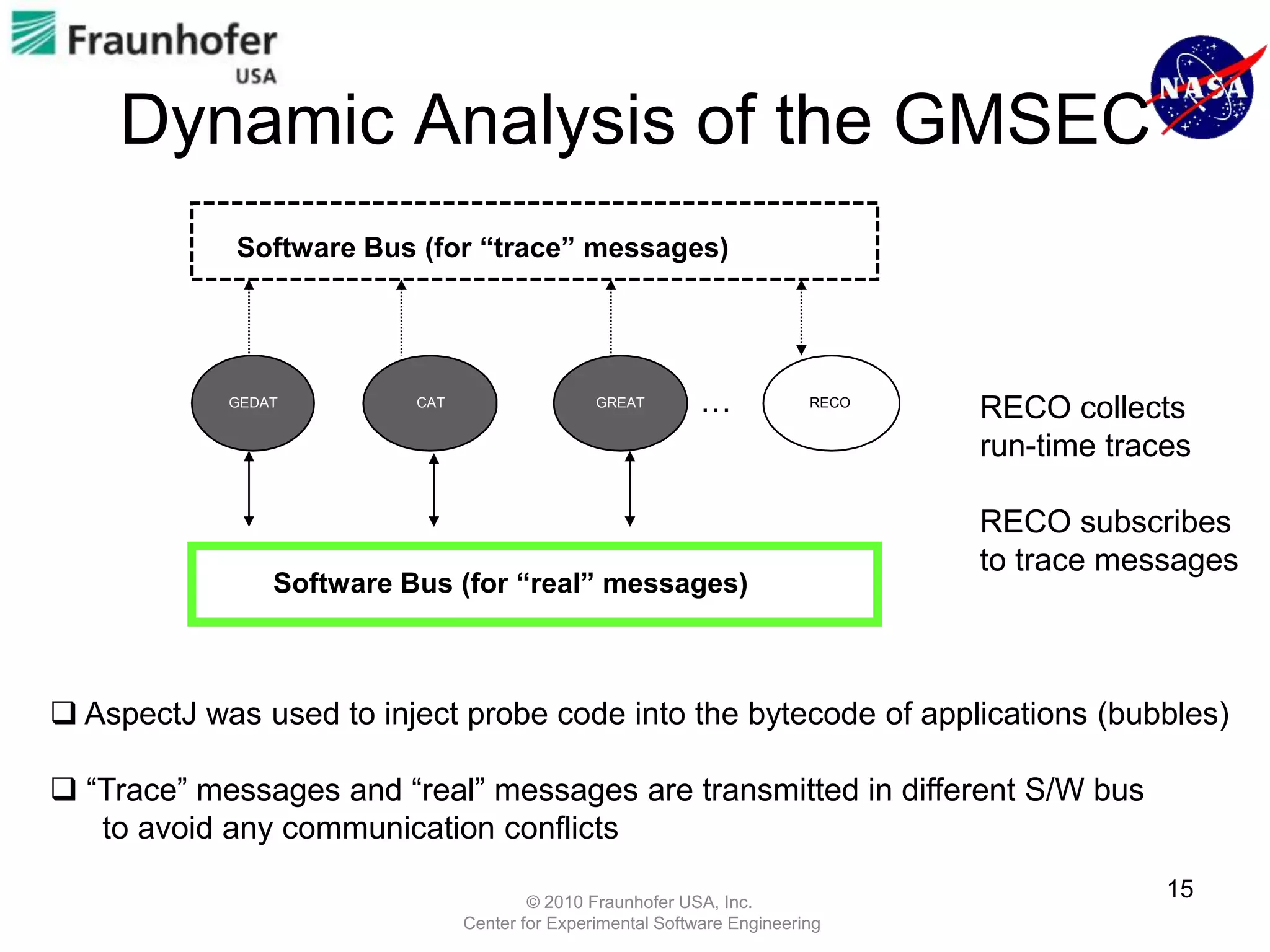
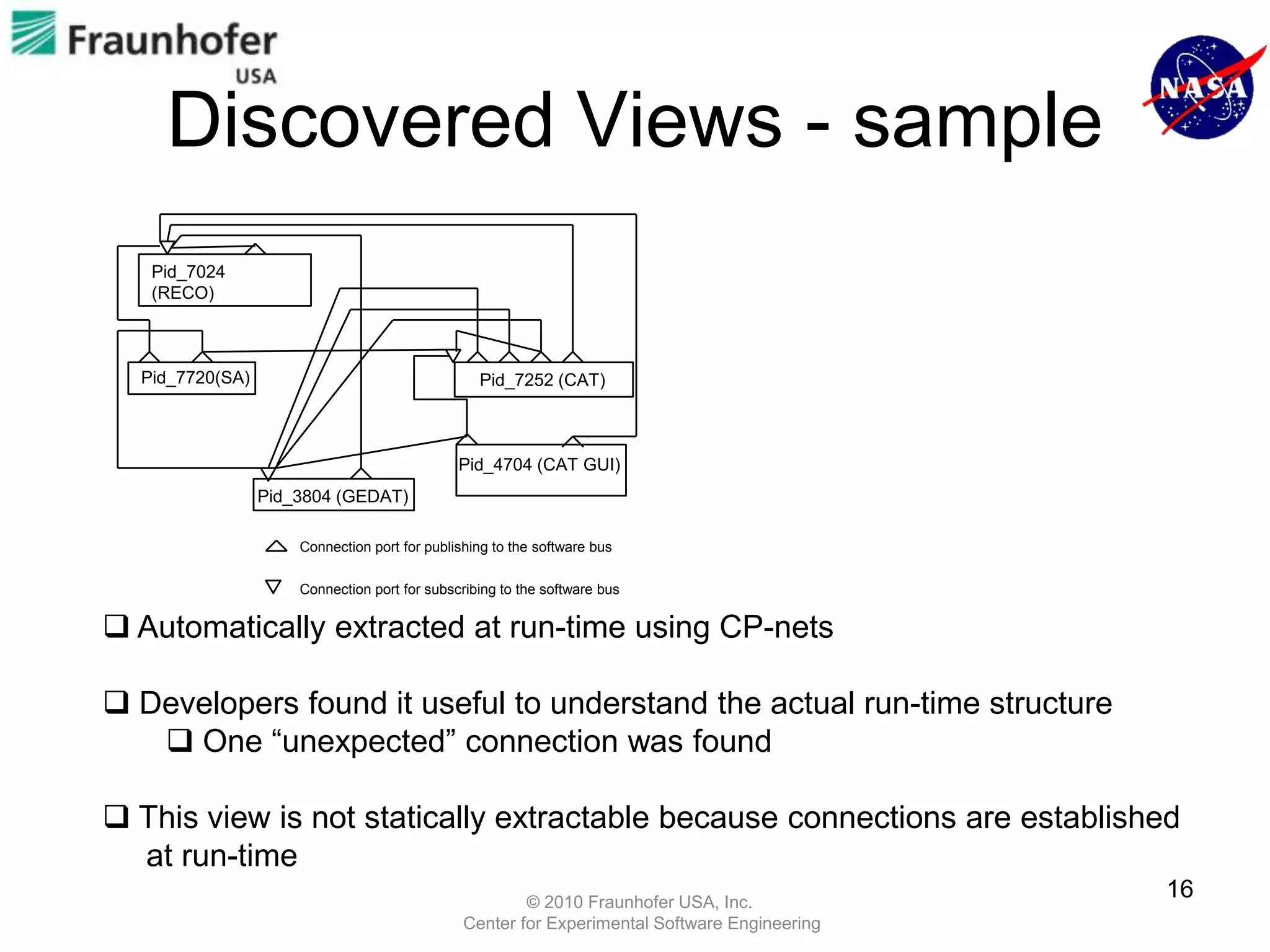
This document discusses analyzing systems based on the publisher-subscriber architectural style. It describes analyzing a NASA system called GMSEC that uses this style. Static analysis is used to understand how components connect and communicate. Dynamic analysis involves monitoring a running system to understand behavior, such as which subscribers receive messages from which publishers. This analysis uncovered a high-priority bug and provided valuable insights into GMSEC.