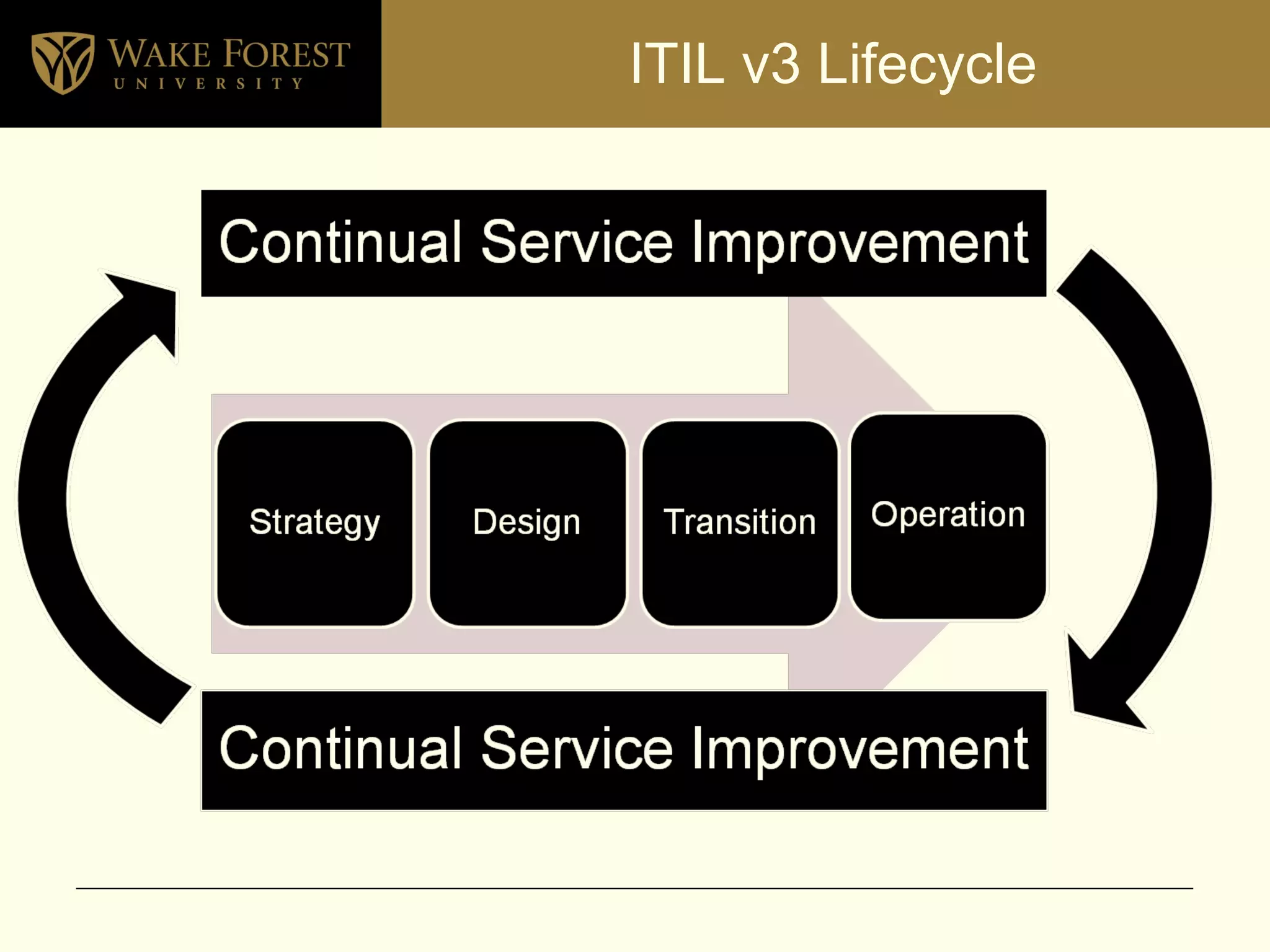
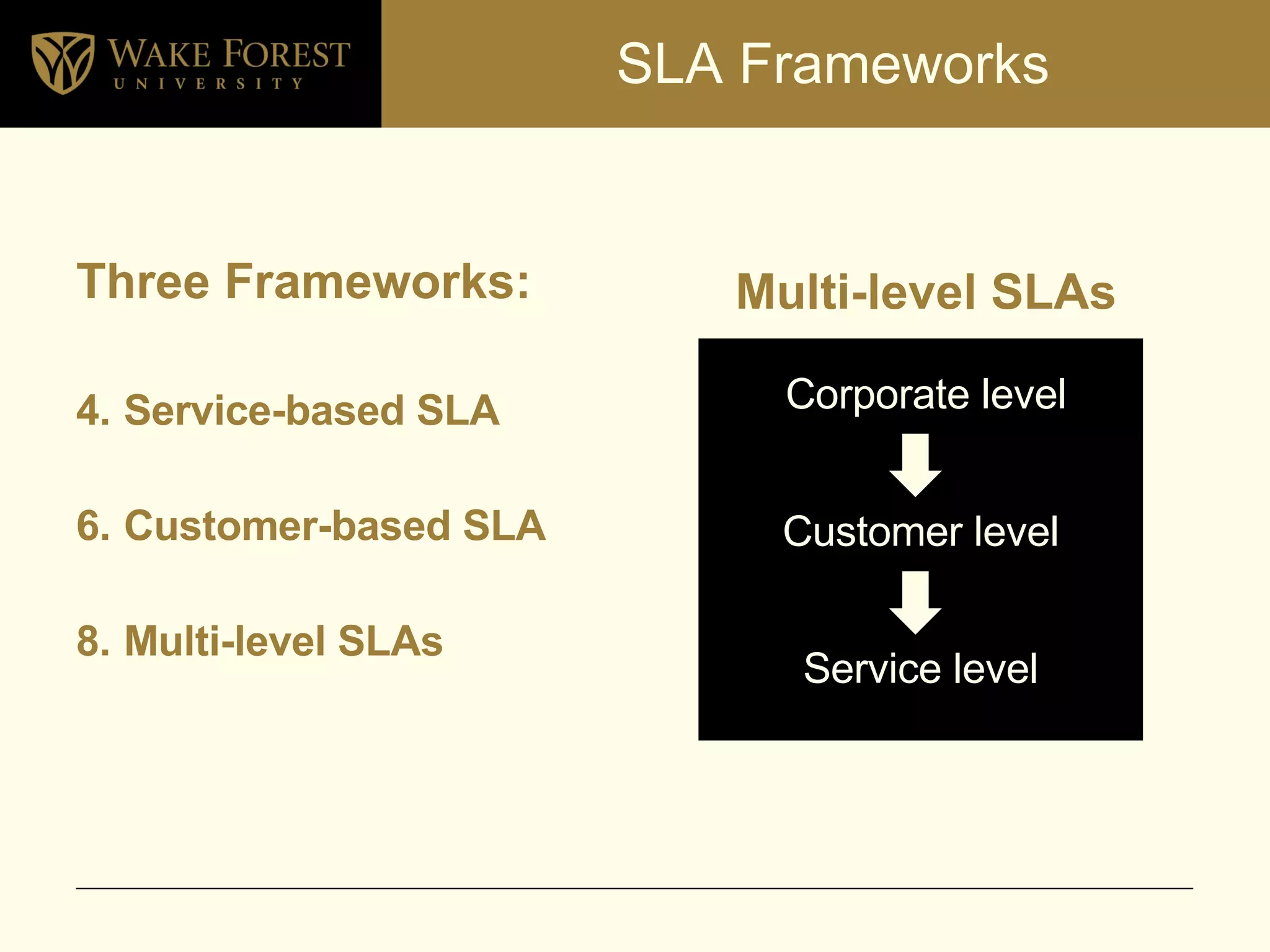
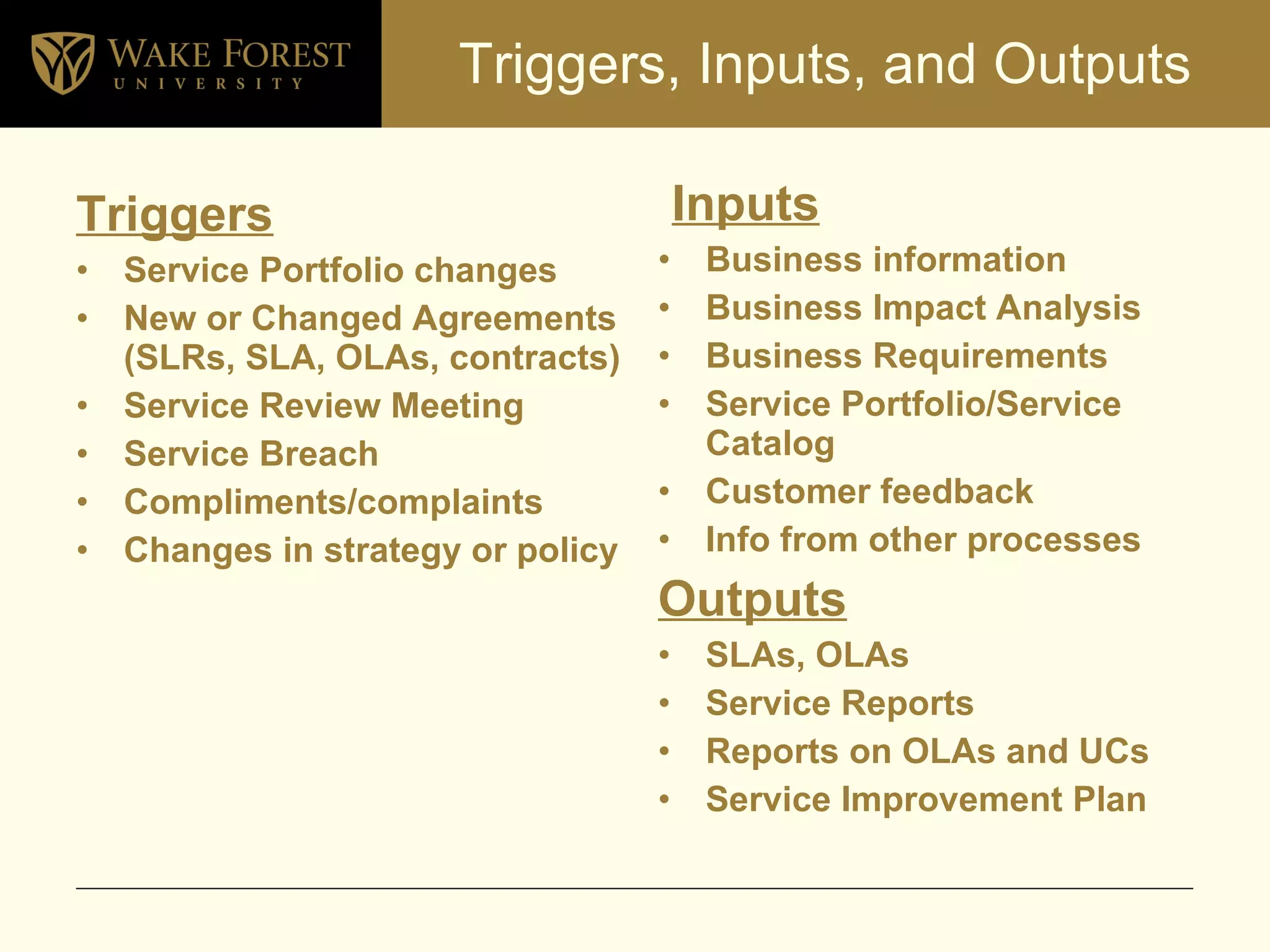
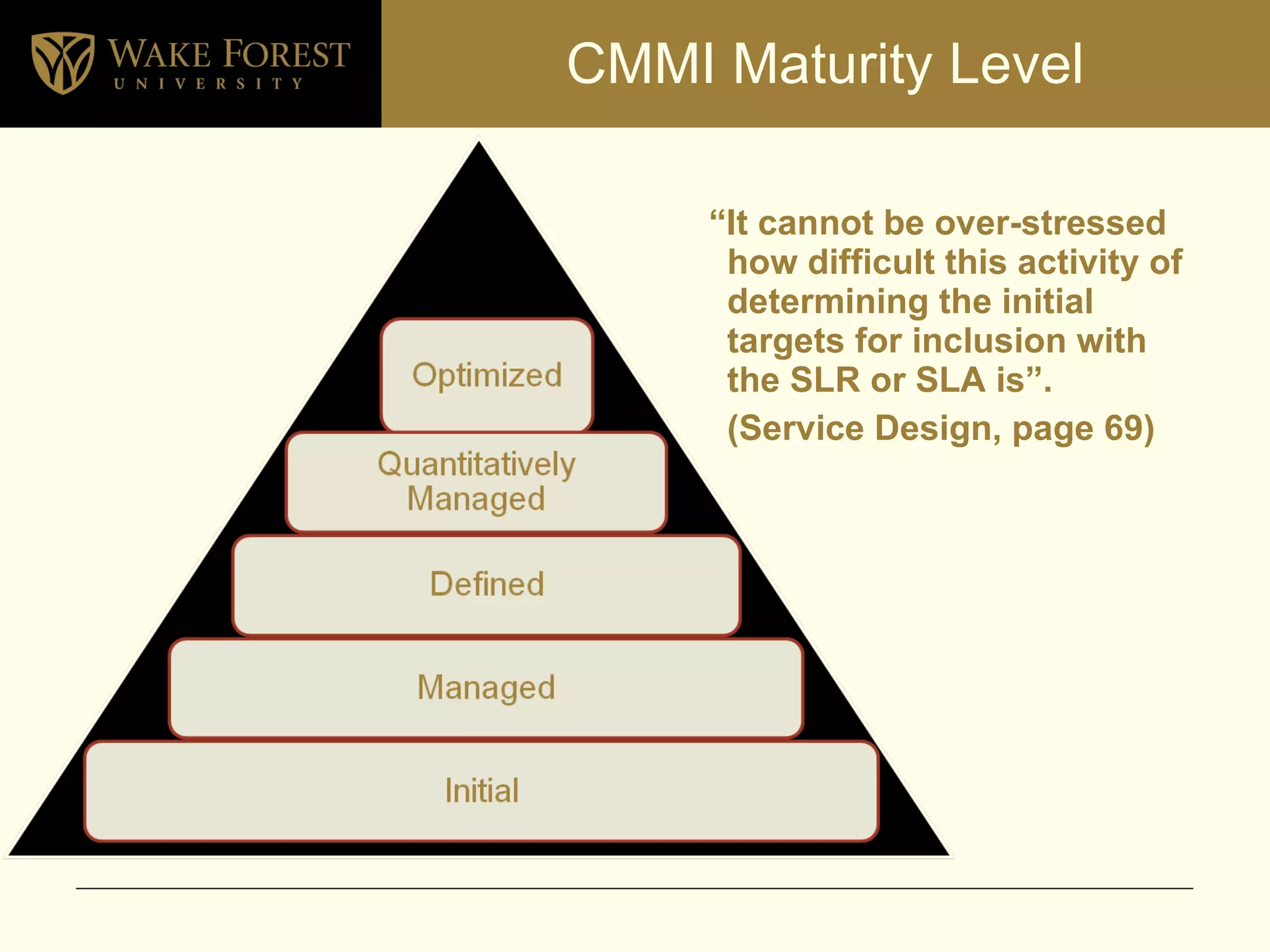
The document outlines an agenda for a service level management meeting, featuring a presentation on the current status at Wake Forest and a group discussion on improvements. It emphasizes the goals and objectives of service level management, including the negotiation and documentation of service targets, monitoring service delivery, and enhancing customer satisfaction. Key performance indicators and various service level agreement frameworks are also discussed to assess and improve service quality.