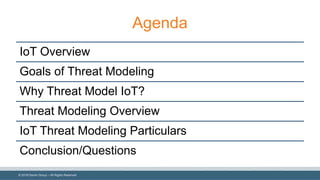
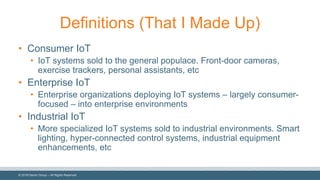
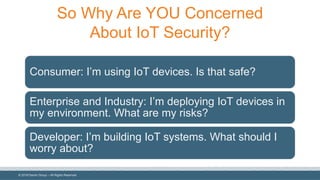
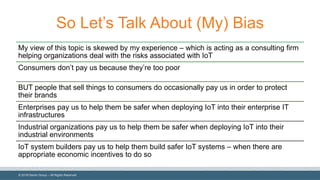
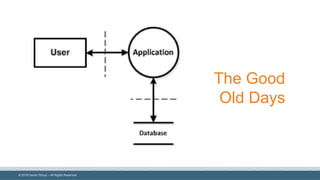
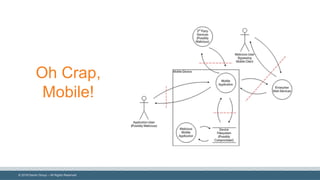
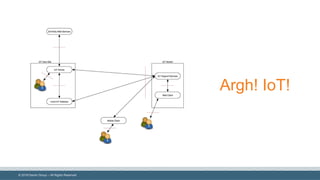
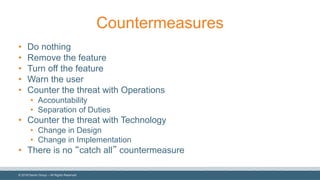
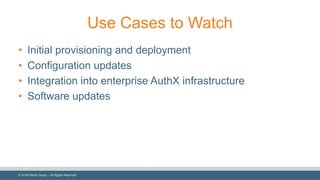
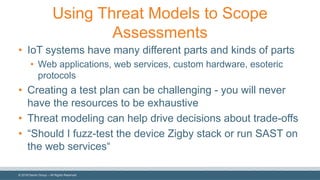
The document discusses the importance of threat modeling for Internet of Things (IoT) systems, highlighting the various complexities and security concerns associated with consumer, enterprise, and industrial IoT. It emphasizes the necessity of proactive vulnerability identification during the design phase and provides an overview of threat modeling techniques and best practices. The document concludes that effective threat modeling can help avoid introducing vulnerabilities and guide assessments to ensure safer IoT deployments.