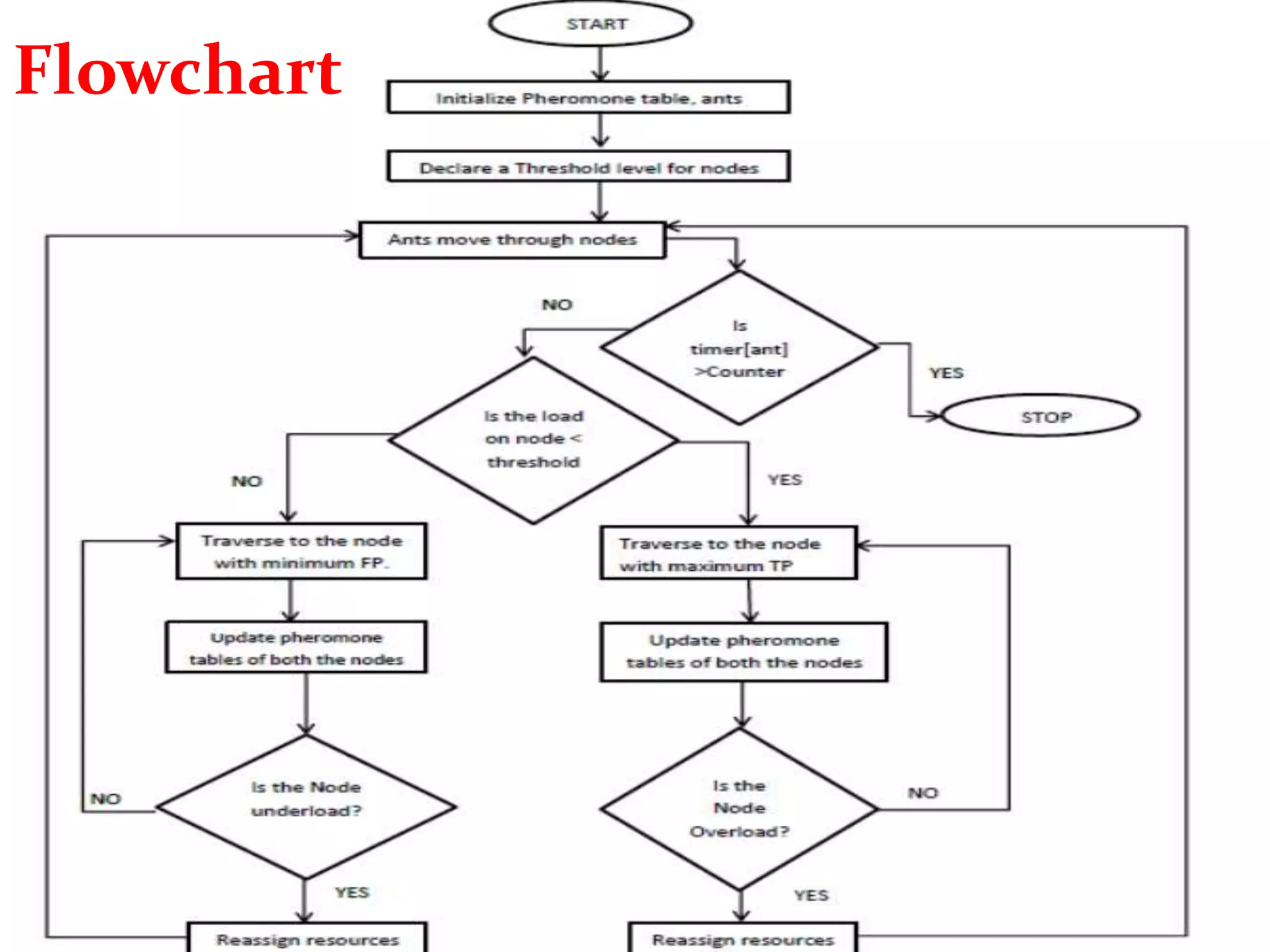
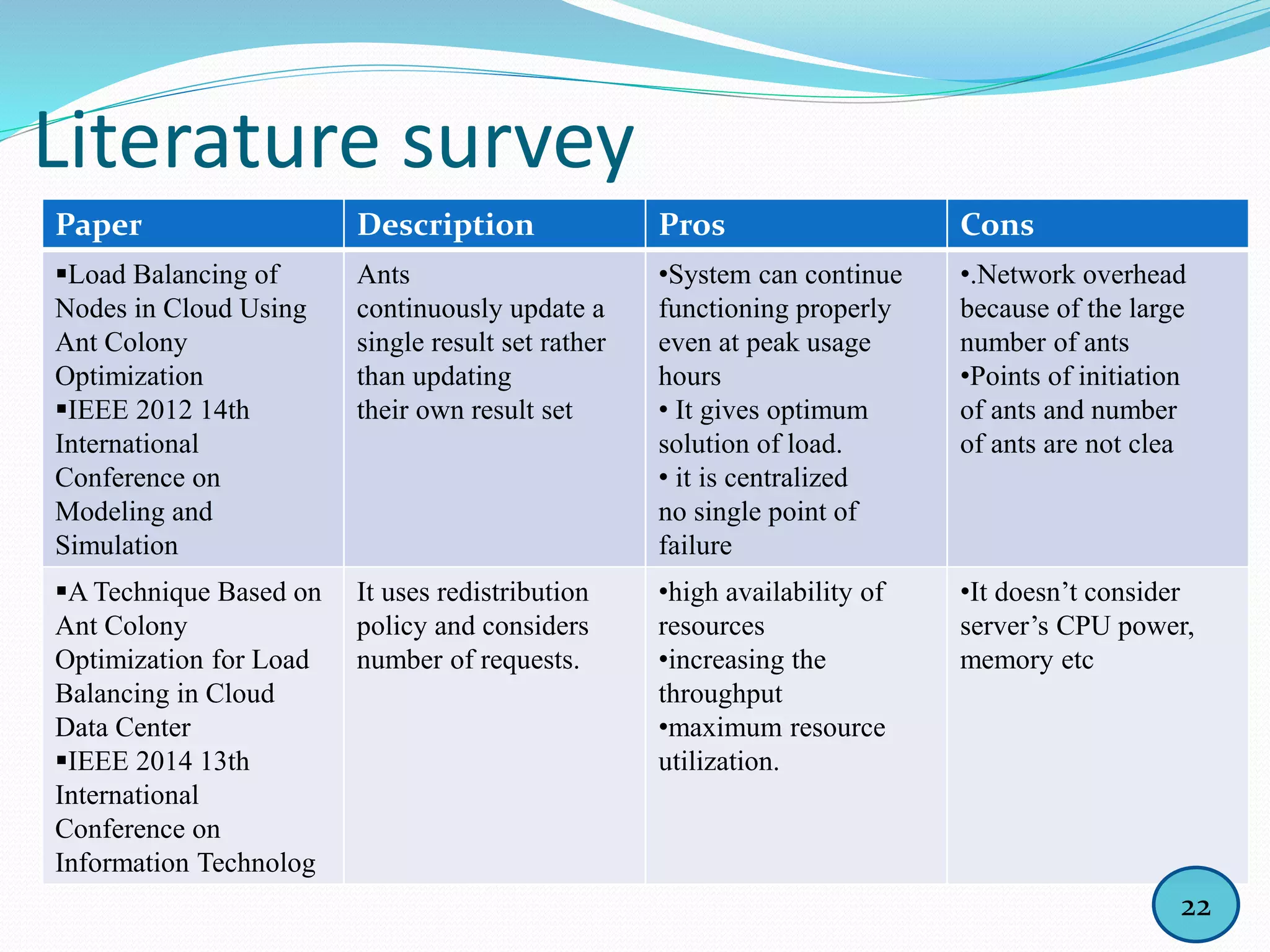
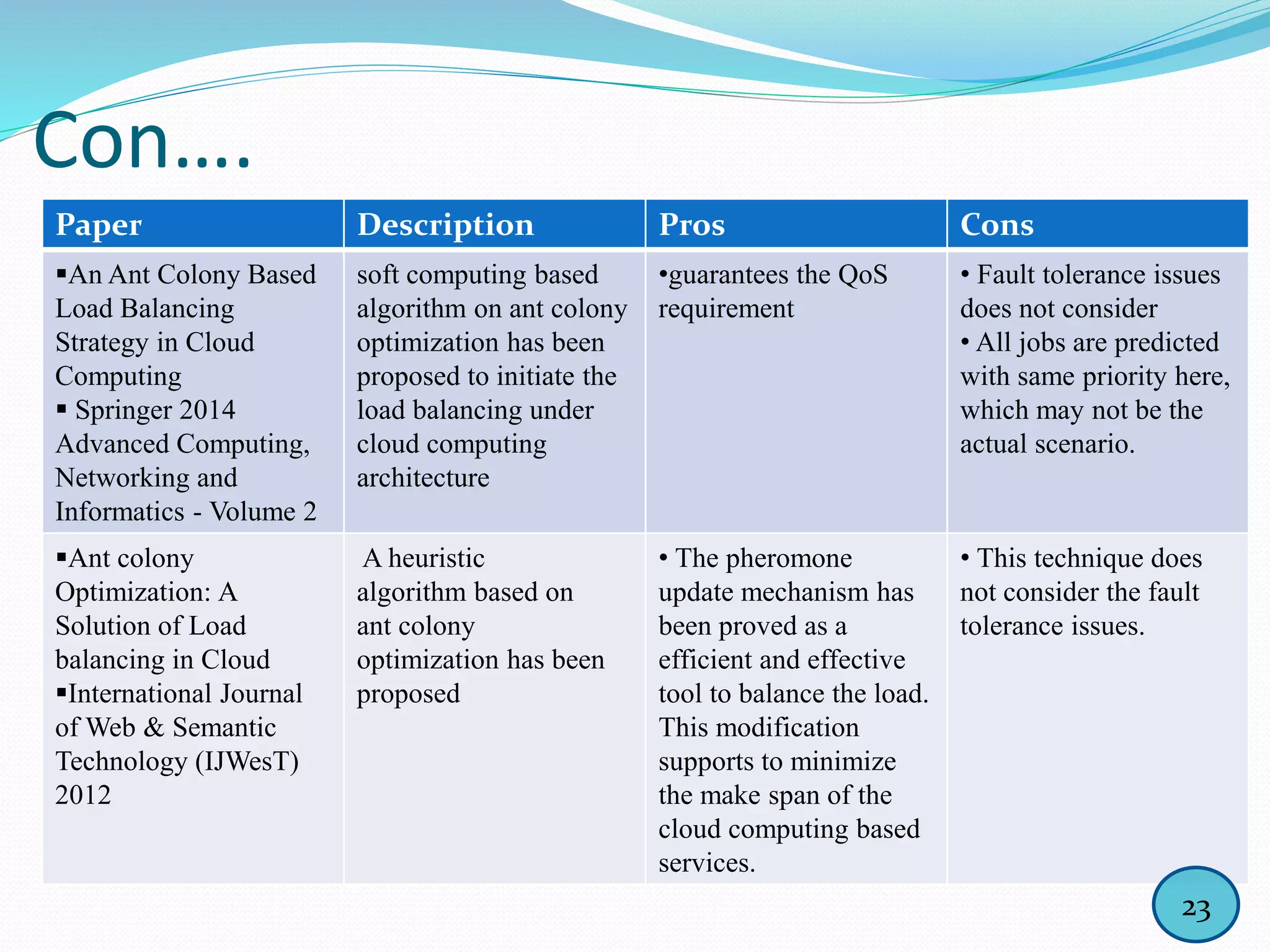
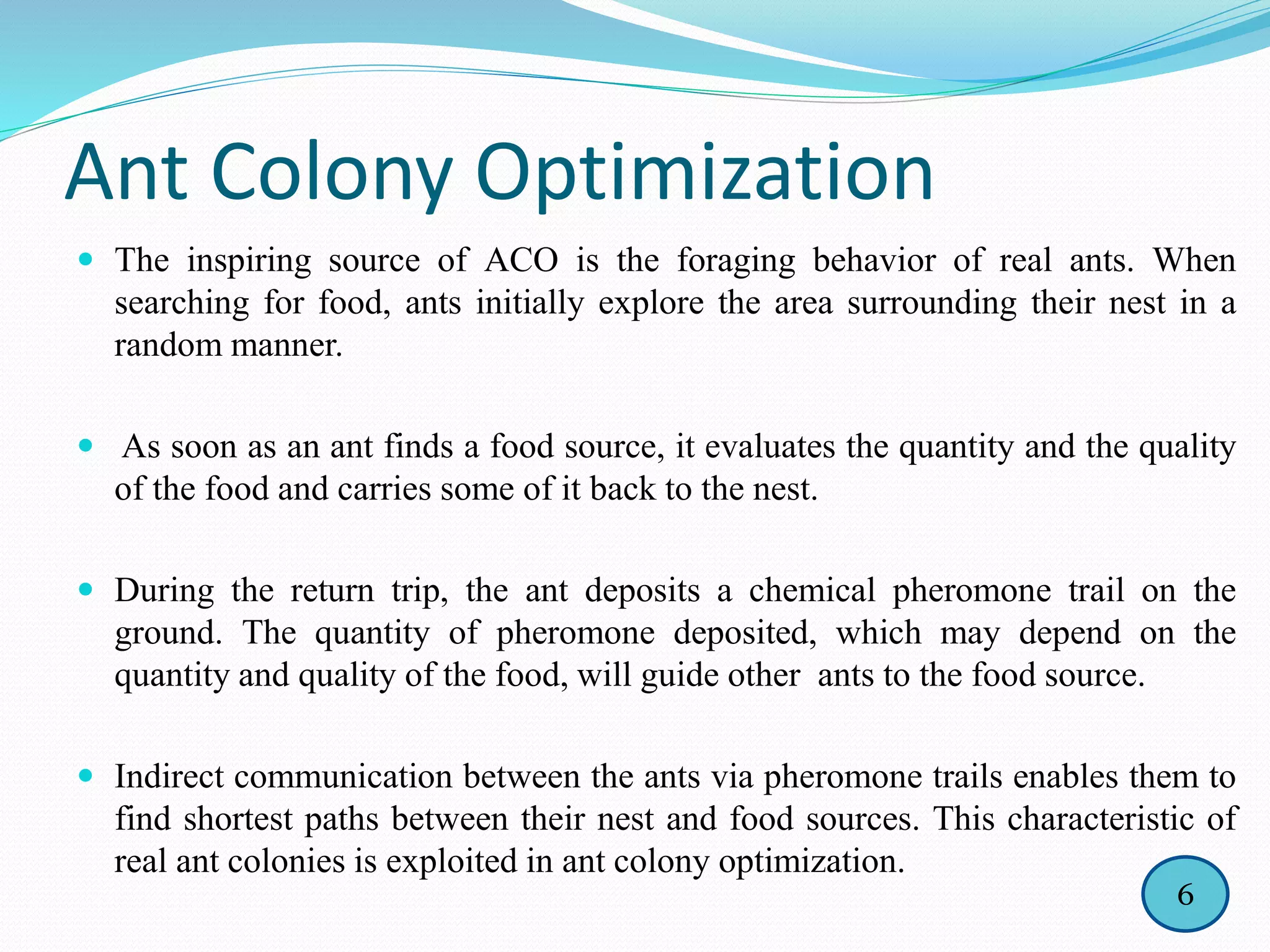
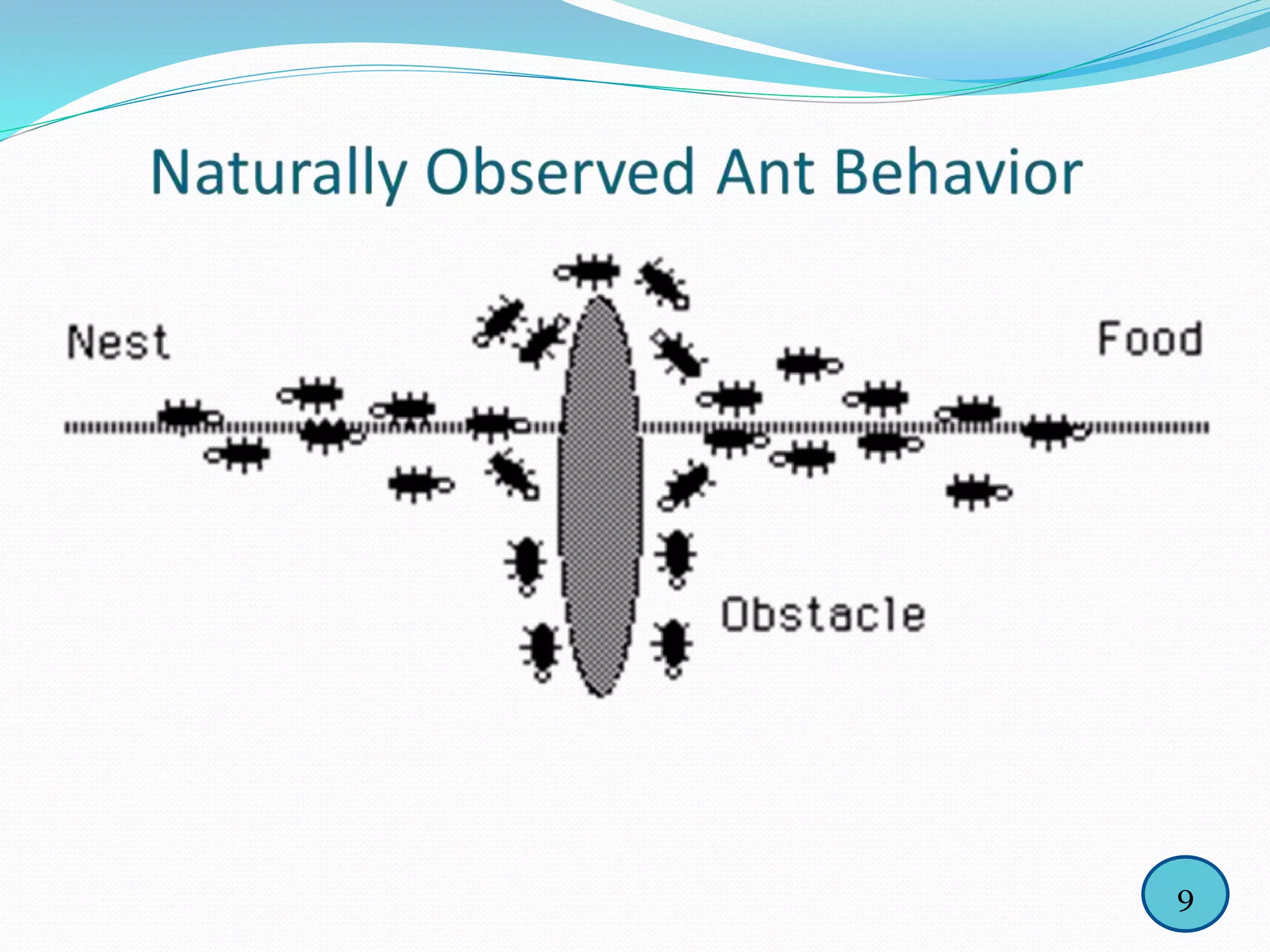
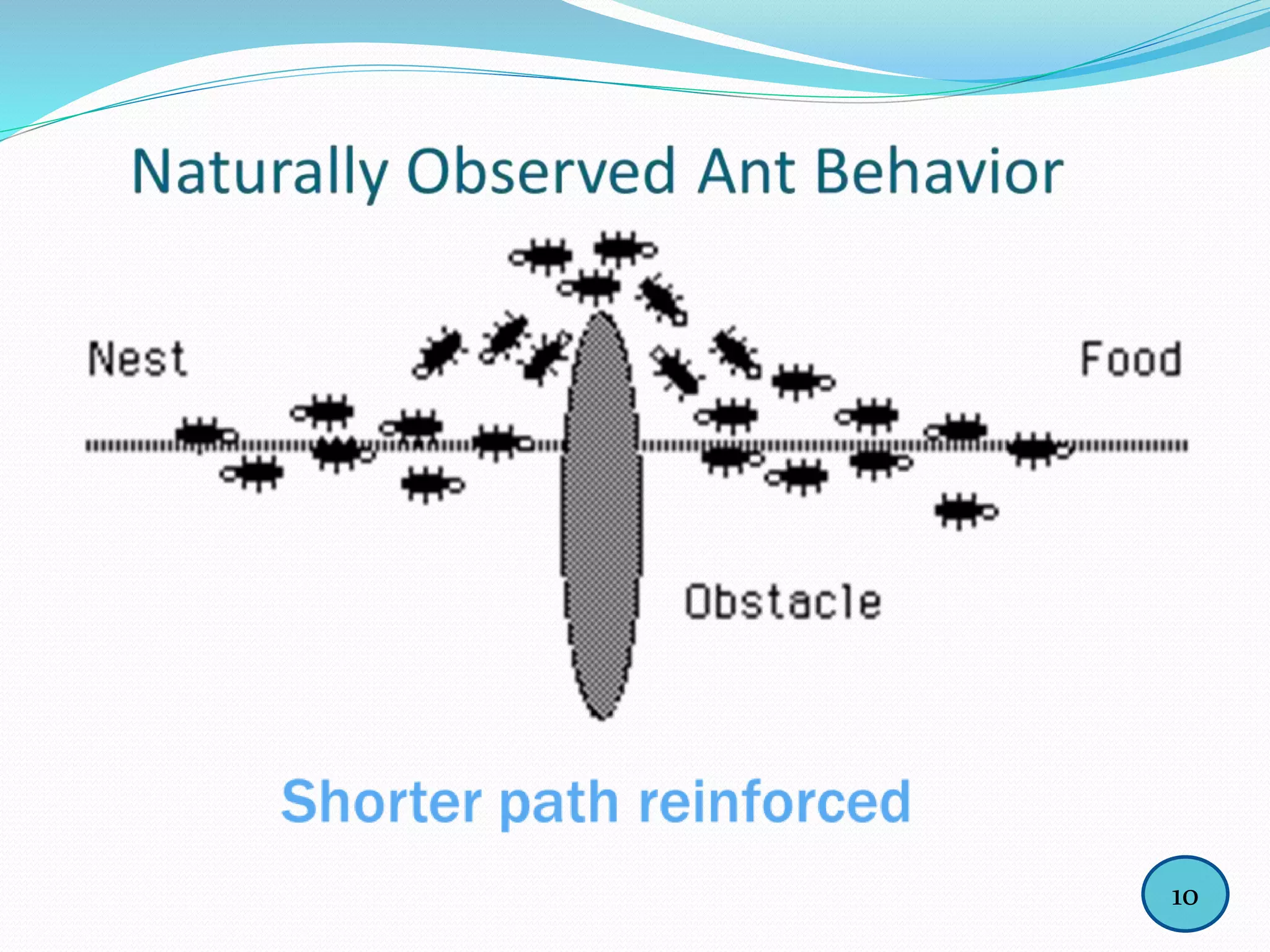
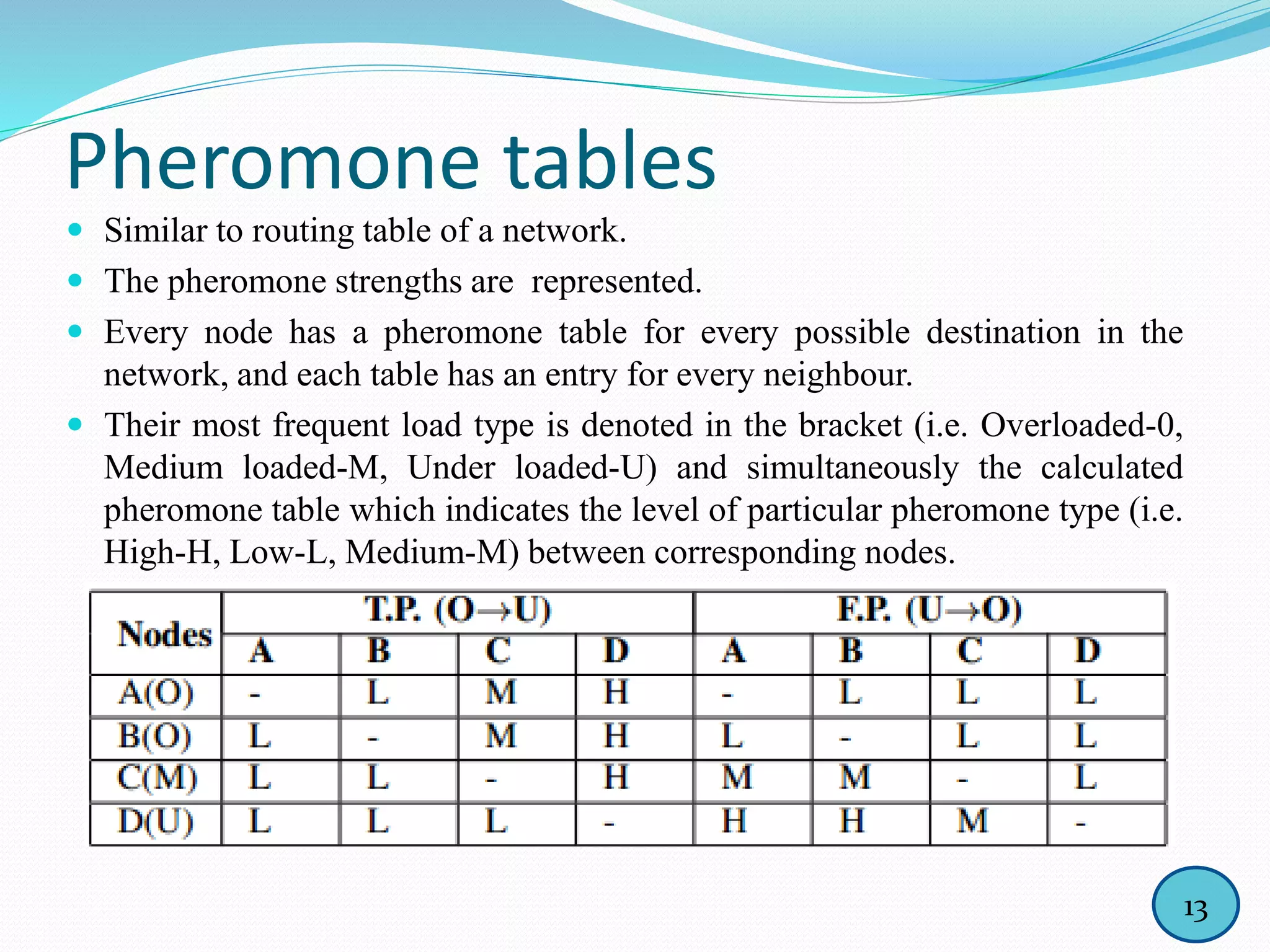
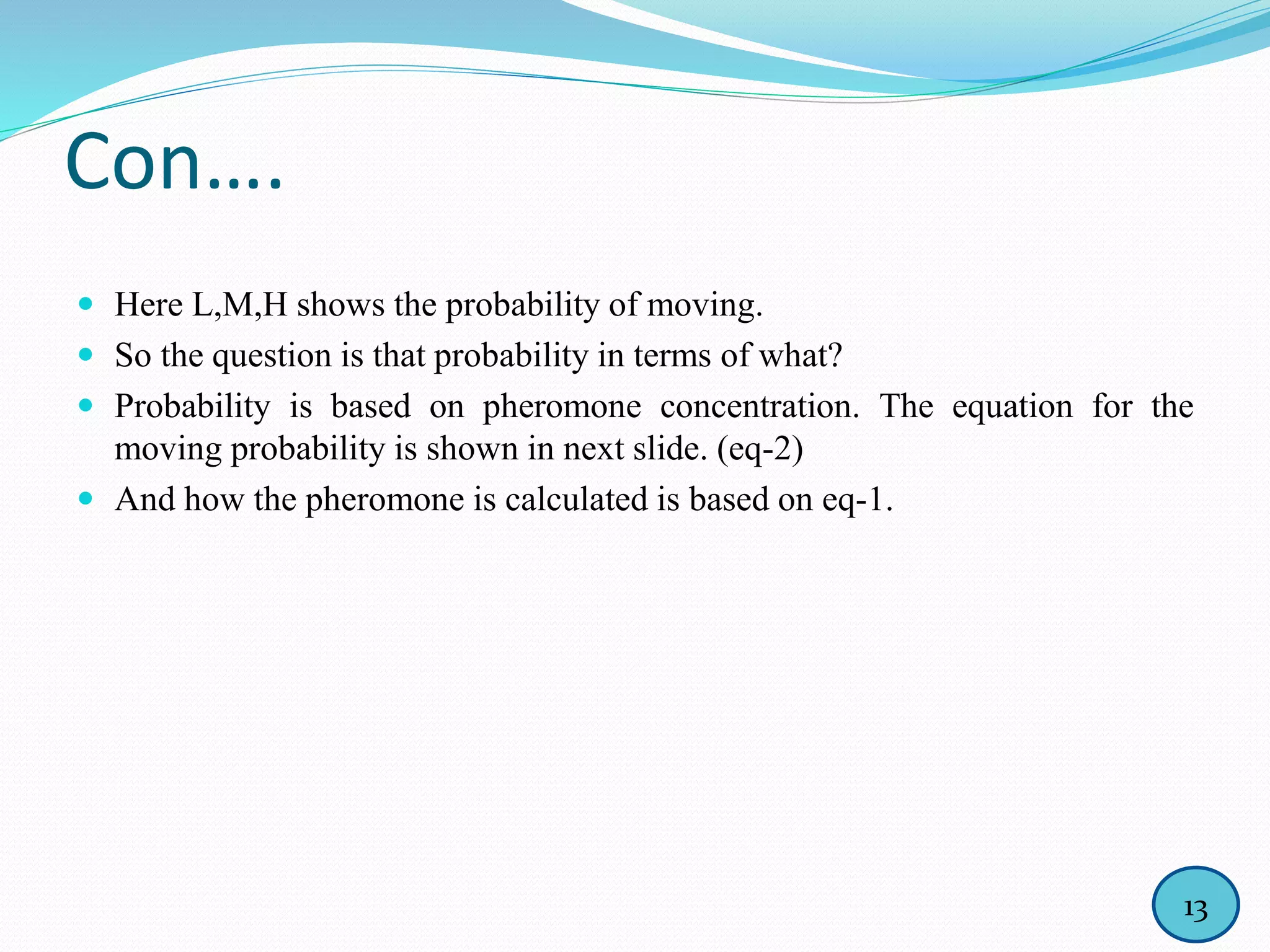
The document discusses the application of ant colony optimization (ACO) for load balancing in cloud computing, explaining the nature of cloud computing and the principles of ACO inspired by the foraging behavior of ants. It details the process of redistributing workloads among overloaded and underloaded nodes within a cloud network using pheromone tables to guide decision-making. The conclusion emphasizes the potential for optimal resource utilization and increased throughput, alongside suggestions for future improvements involving server capabilities.
![Con…..
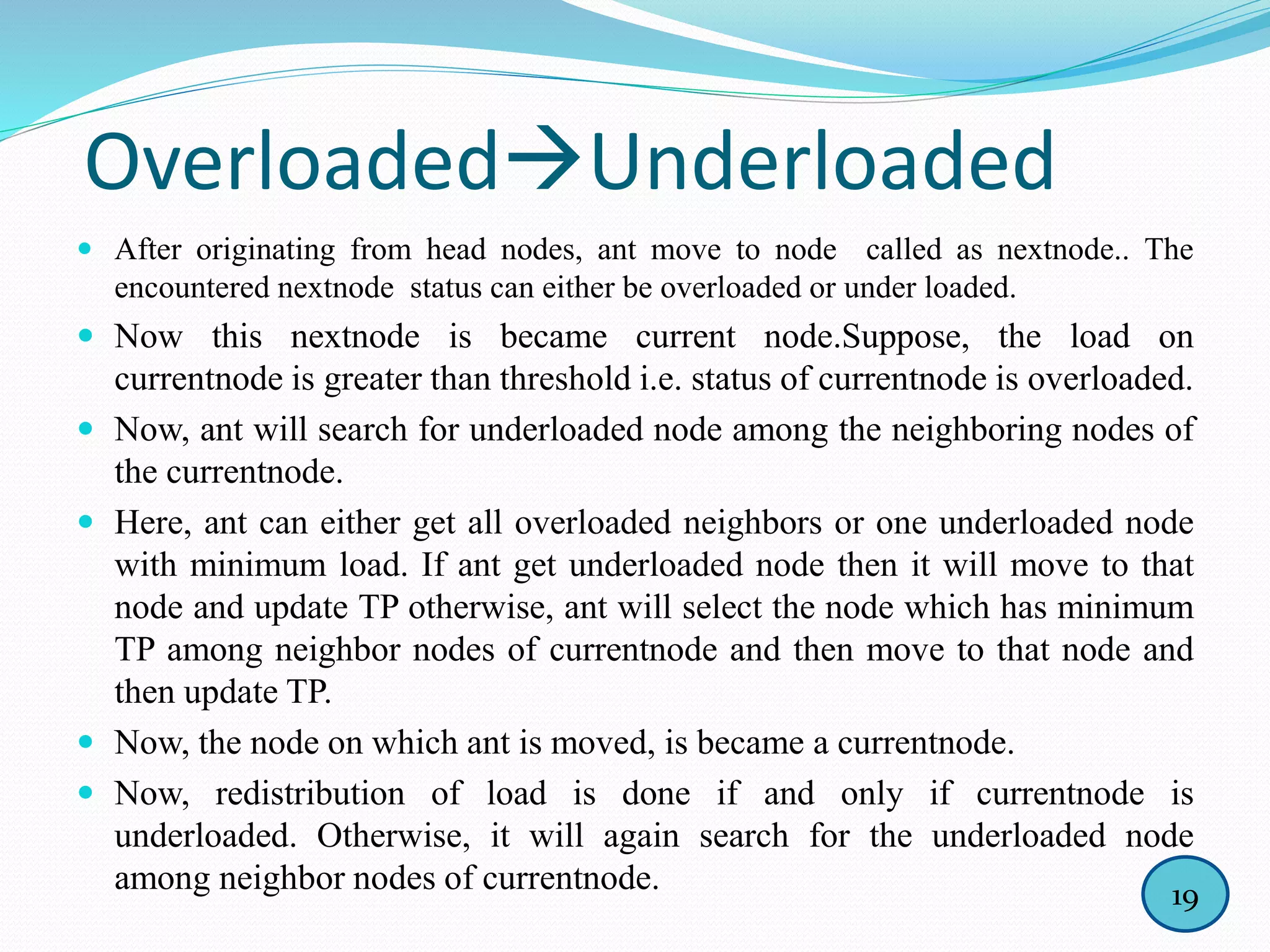
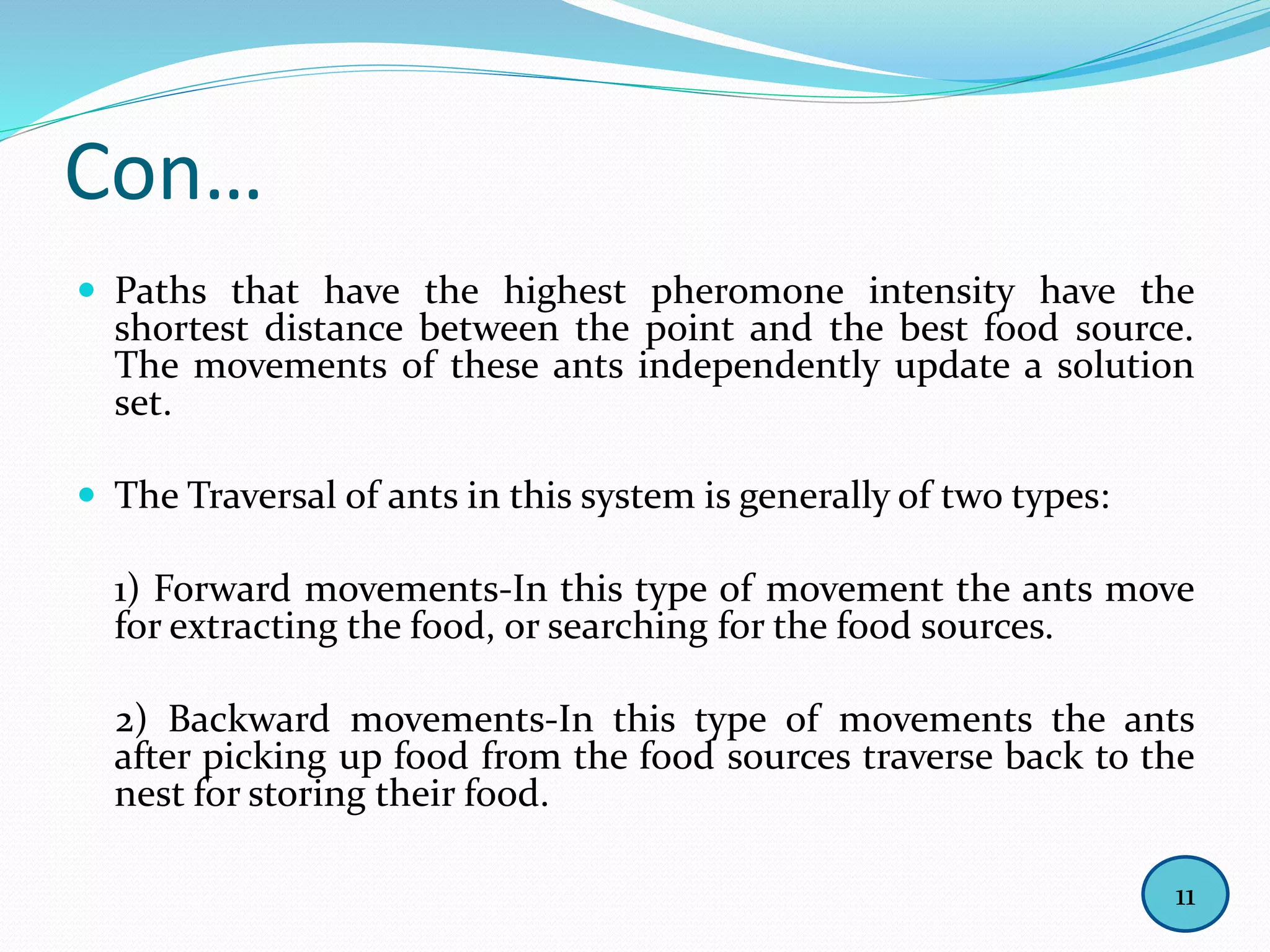
The ants traverse the cloud network, selecting nodes for their next step
through the classical formula given below, where the probability Pk of an
ant,which is currently on node r selecting the neighboring nodes for
traversal, is:
Pk(r, s) =[ τ(r, s)][η(r, s)]^β …………………….eq-2
[τ (r,u)][η(r, u)] ^β
where, r = Current node,
s = Next node,
τ= Pheromone concentration of the edge,
η = The desirability of the move for the ant (if the move is from an
under loaded node to overloaded node or vice-versa the move
will be highly desirable),
β= Depends upon the relevance of the pheromone con-centration
with the move distance.
15](https://image.slidesharecdn.com/aco-150801153817-lva1-app6892/75/Ant-Colony-Optimization-for-Load-Balancing-in-Cloud-17-2048.jpg)
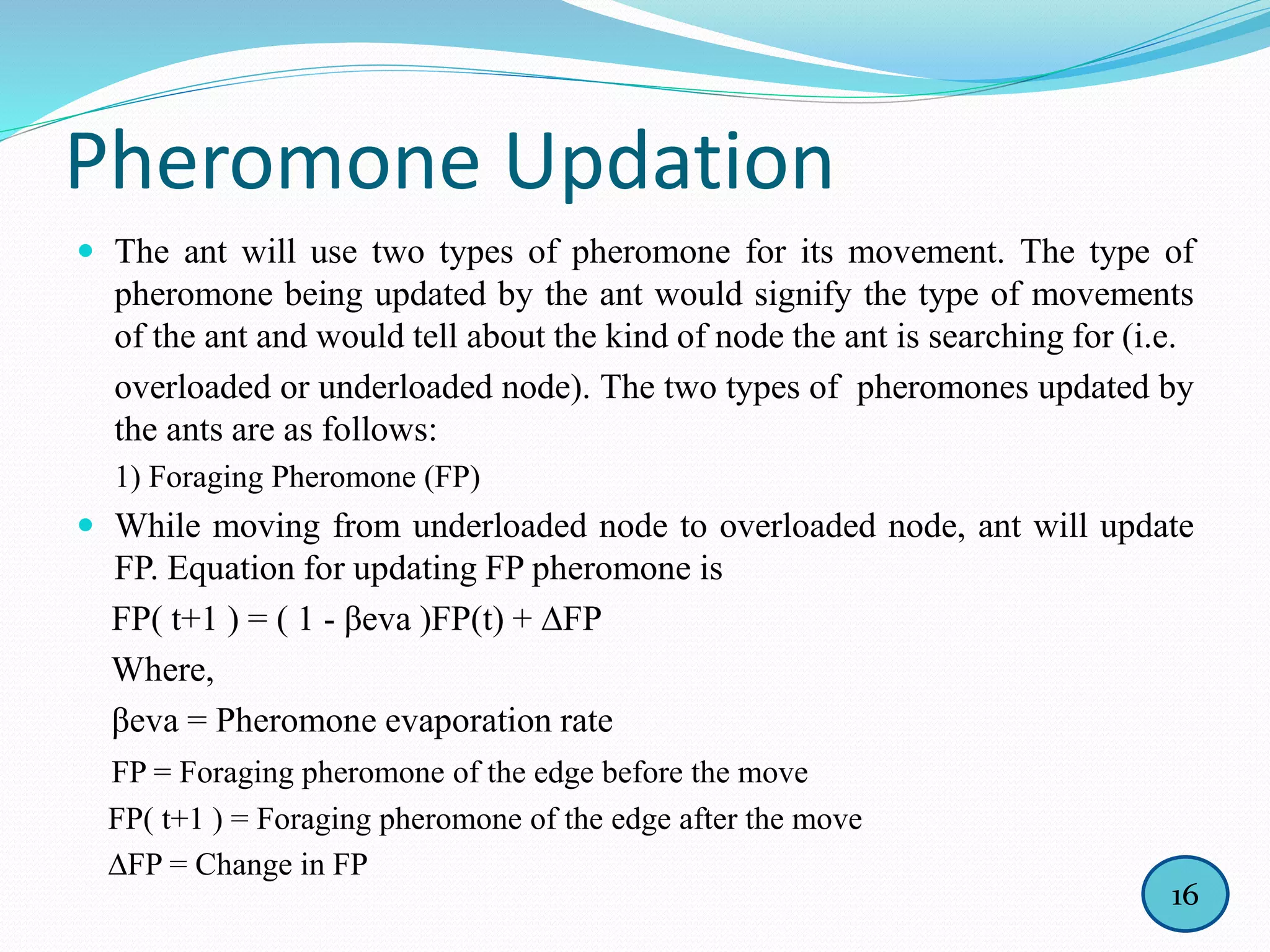
![Con….
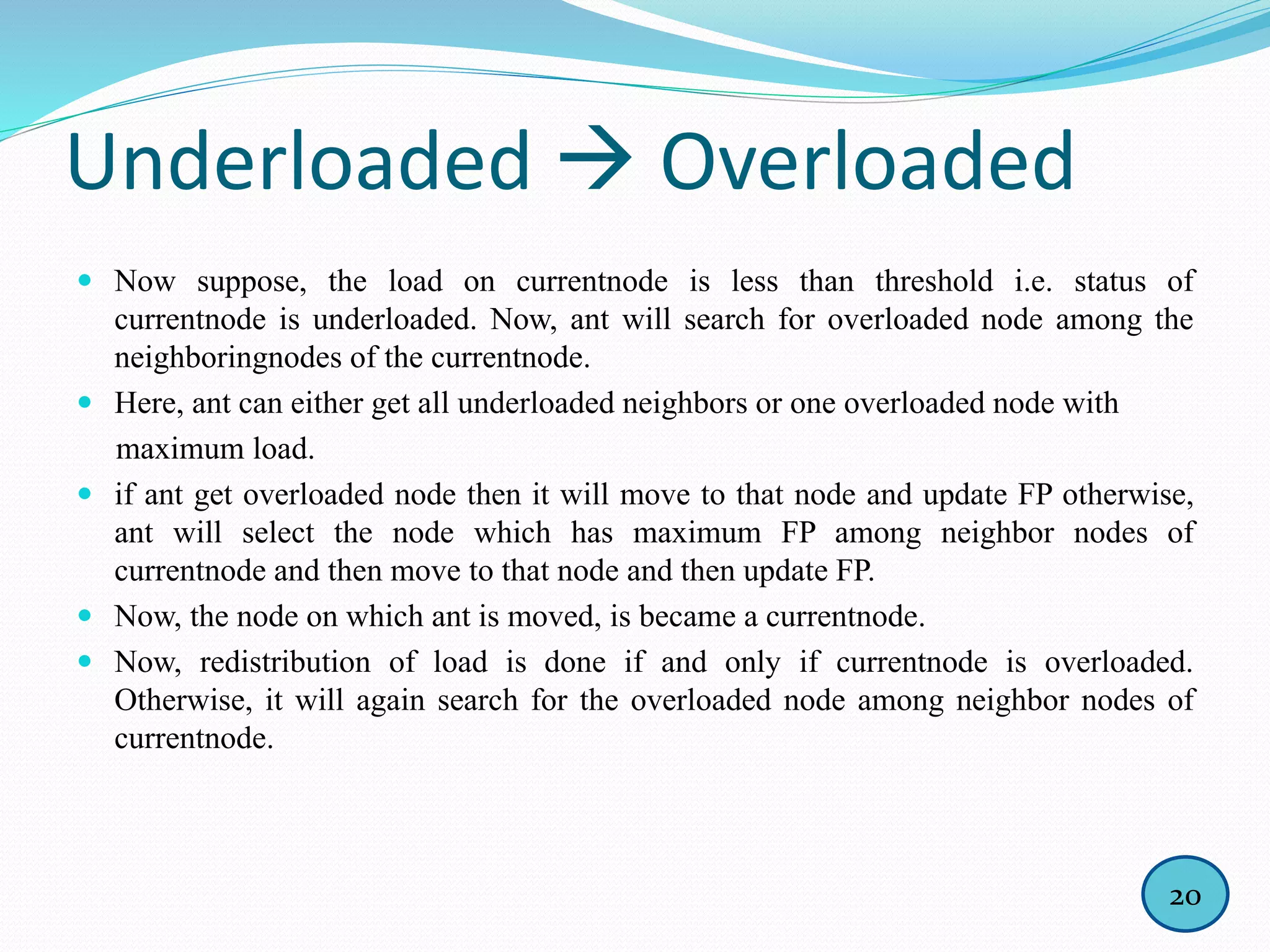
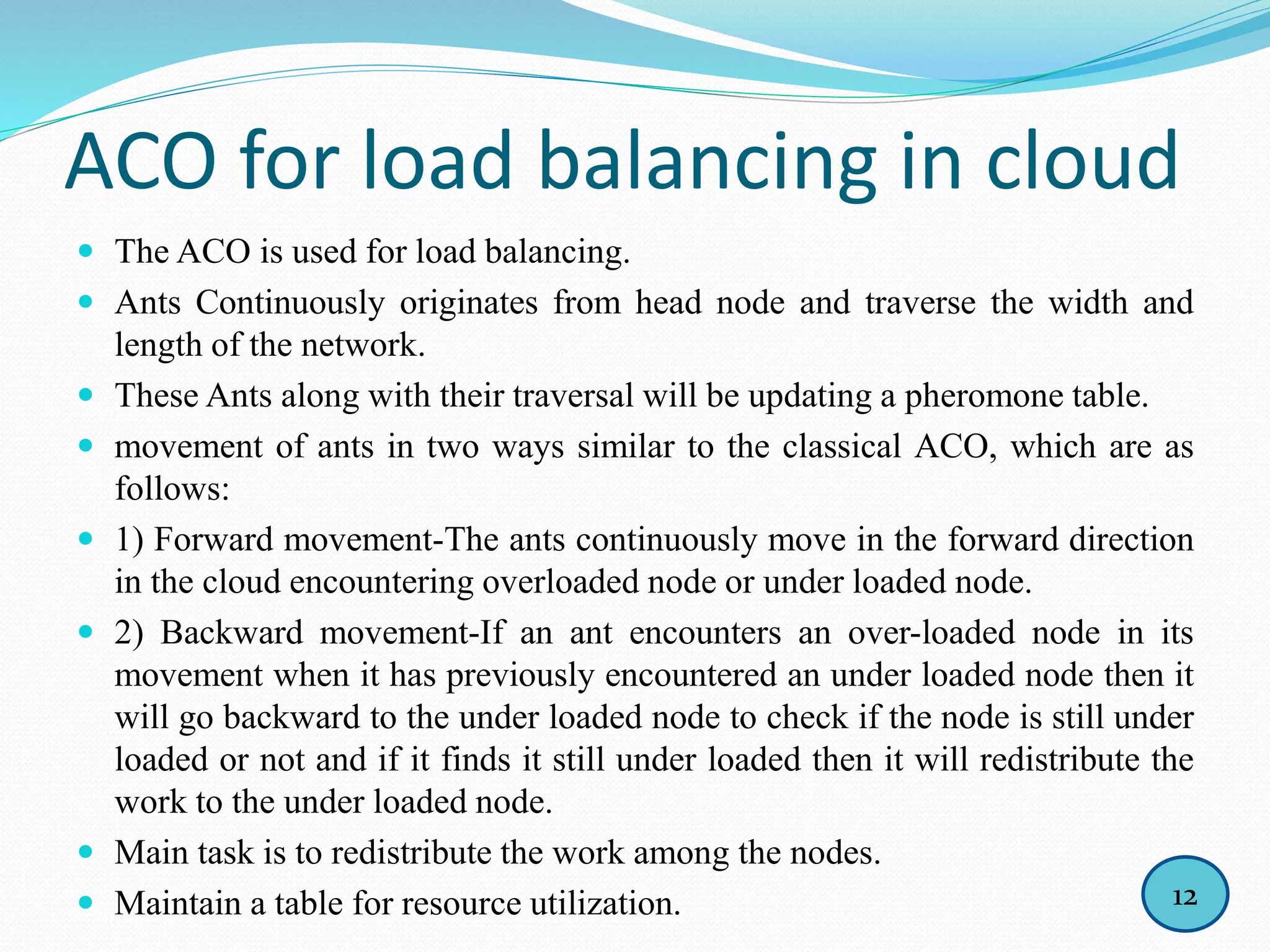
βeva is pheromone evaporation factor which represents the pheromone volatilization
degree during unit time. Correspondingly, (1- βeva) represents the degree of residual
pheromone. The value of βeva is between [0, 1].
The greater the value of βeva , pheromone evaporate faster, and past searches has a
small influence on next step searching
18](https://image.slidesharecdn.com/aco-150801153817-lva1-app6892/75/Ant-Colony-Optimization-for-Load-Balancing-in-Cloud-20-2048.jpg)