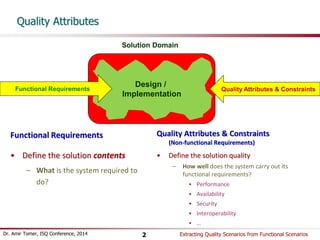
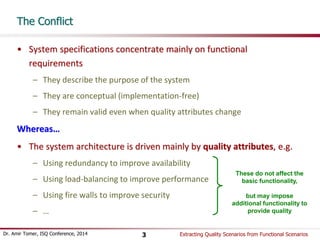
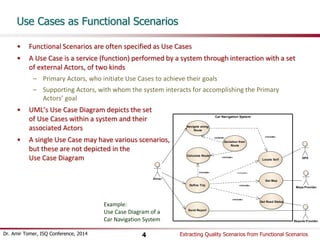
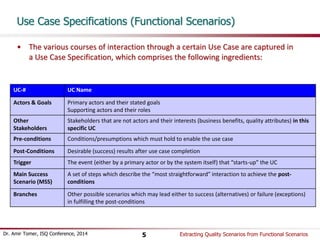
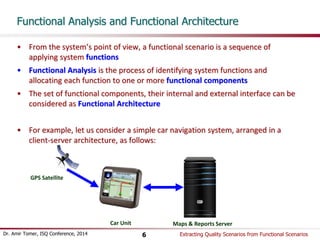
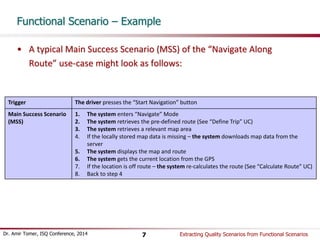
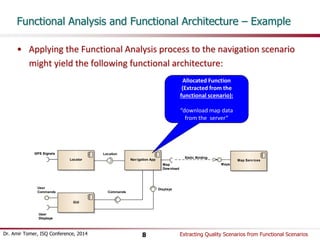
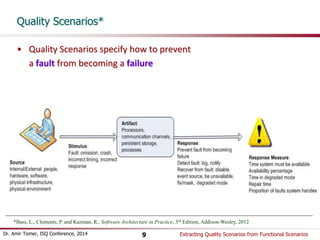
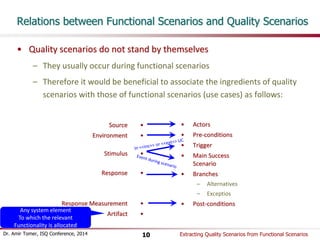
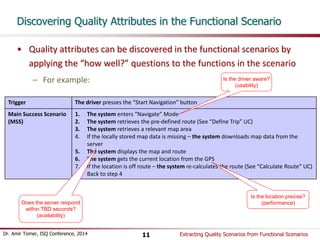
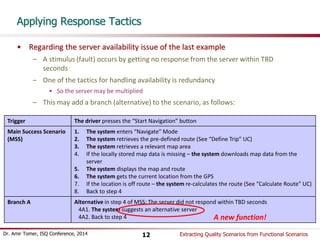
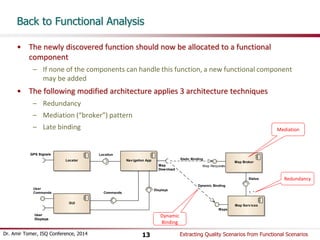
Dr. Amir Tomer's presentation discusses the importance of defining quality attributes (non-functional requirements) alongside functional requirements in software systems, particularly in the context of extracting quality scenarios from functional use cases. It emphasizes how system architecture is heavily influenced by quality attributes such as performance and security, which may necessitate architectural changes or additional functionality. The document outlines a process for identifying quality scenarios through functional analysis, using a car navigation system as a practical example.