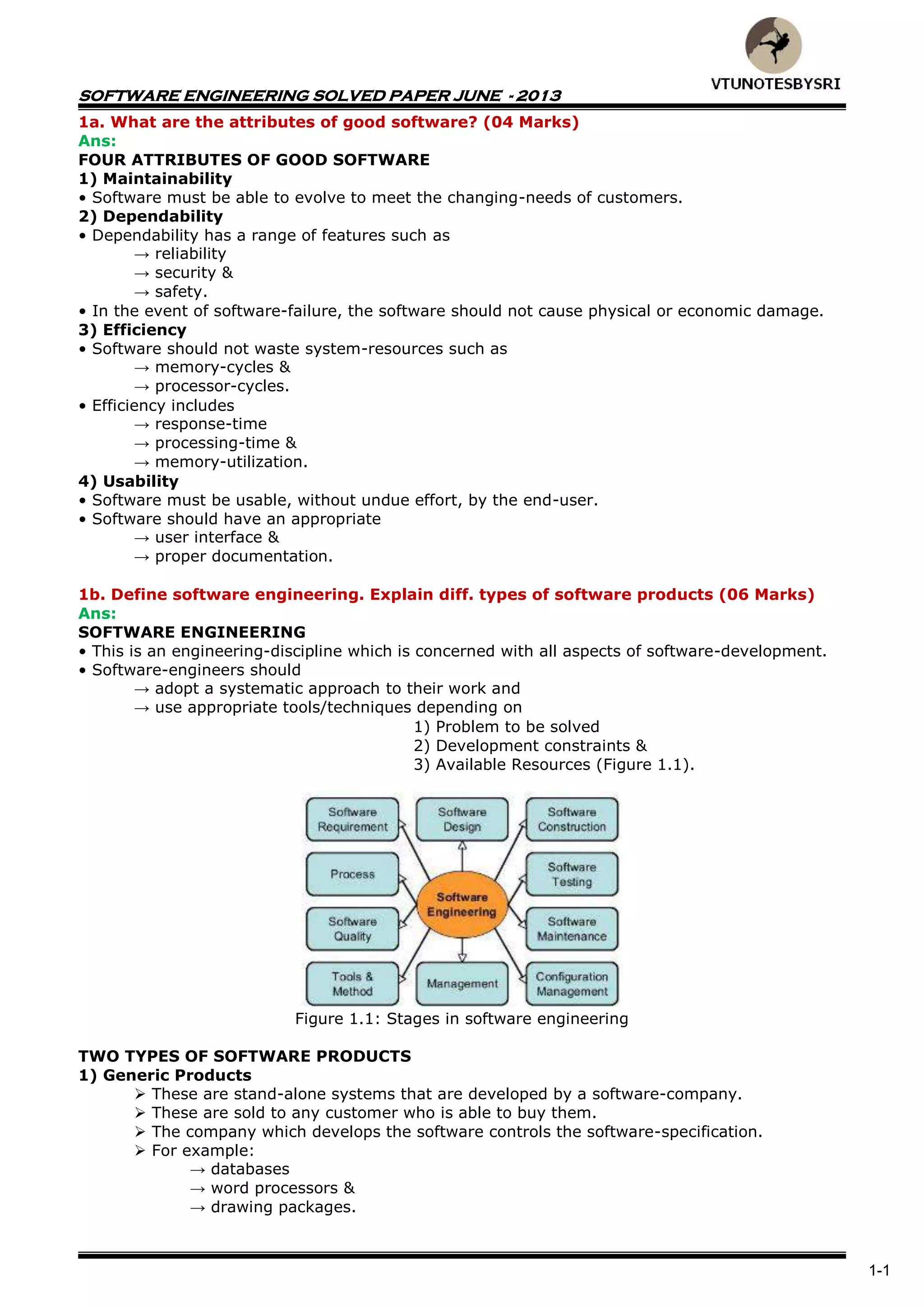
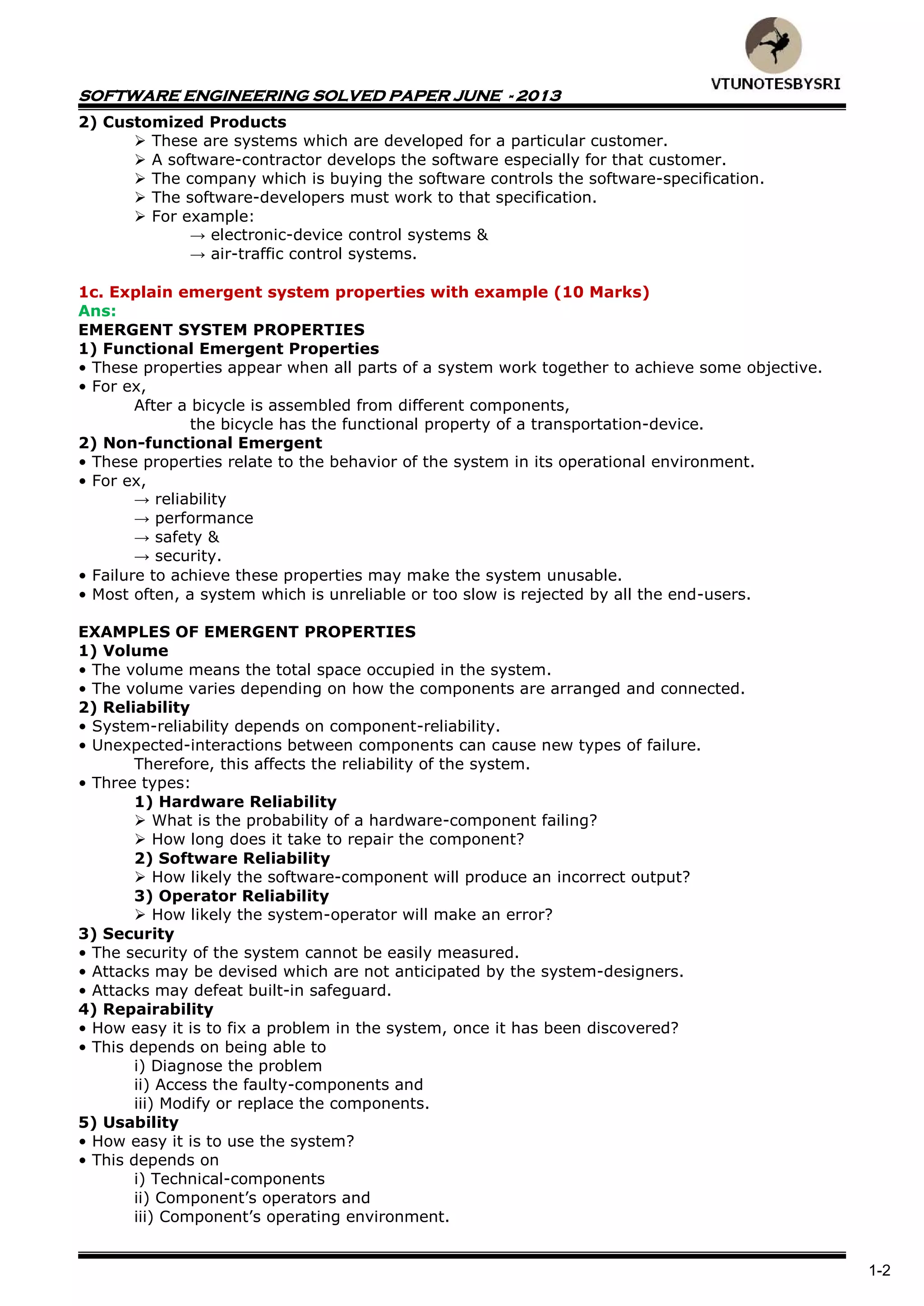
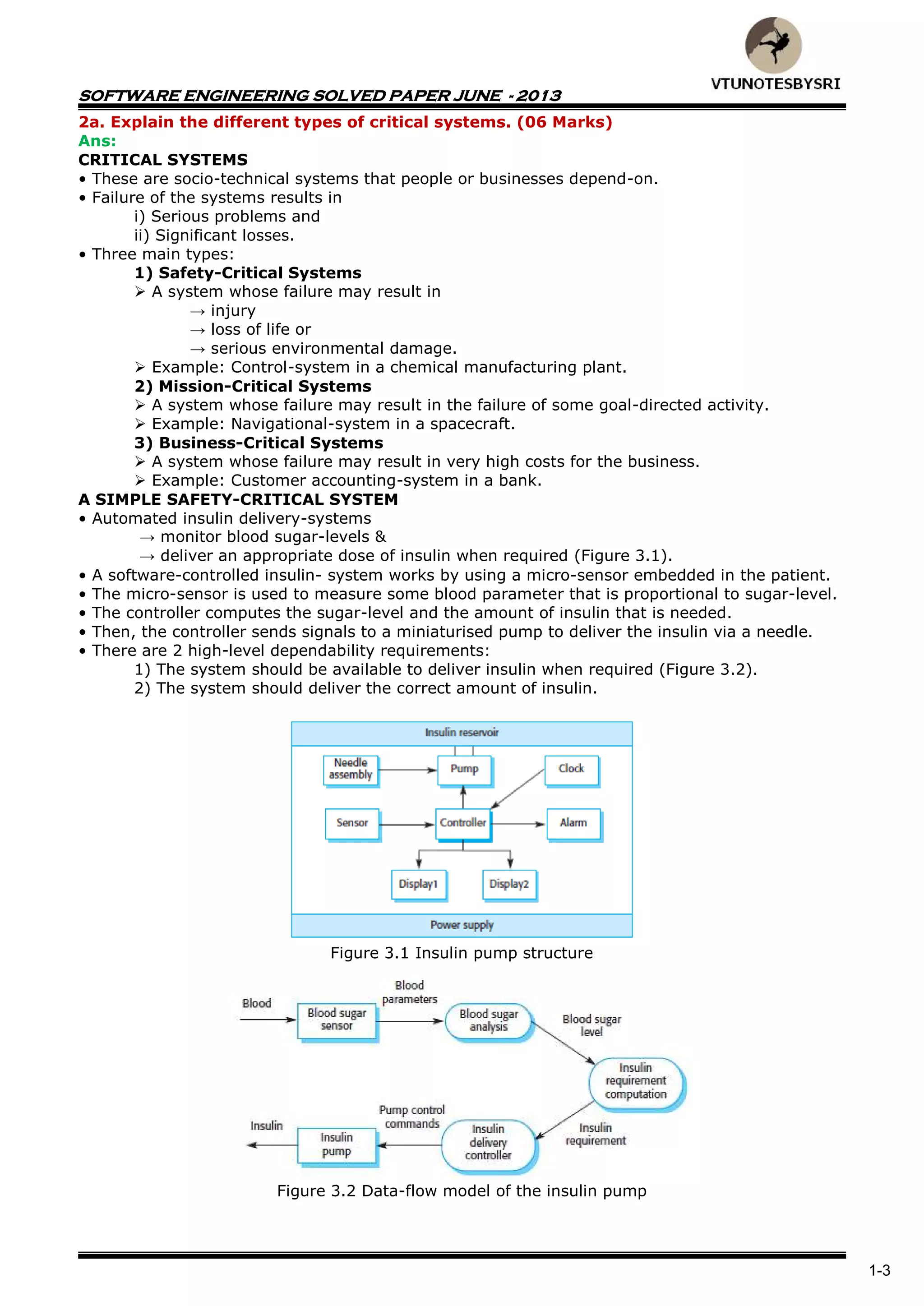
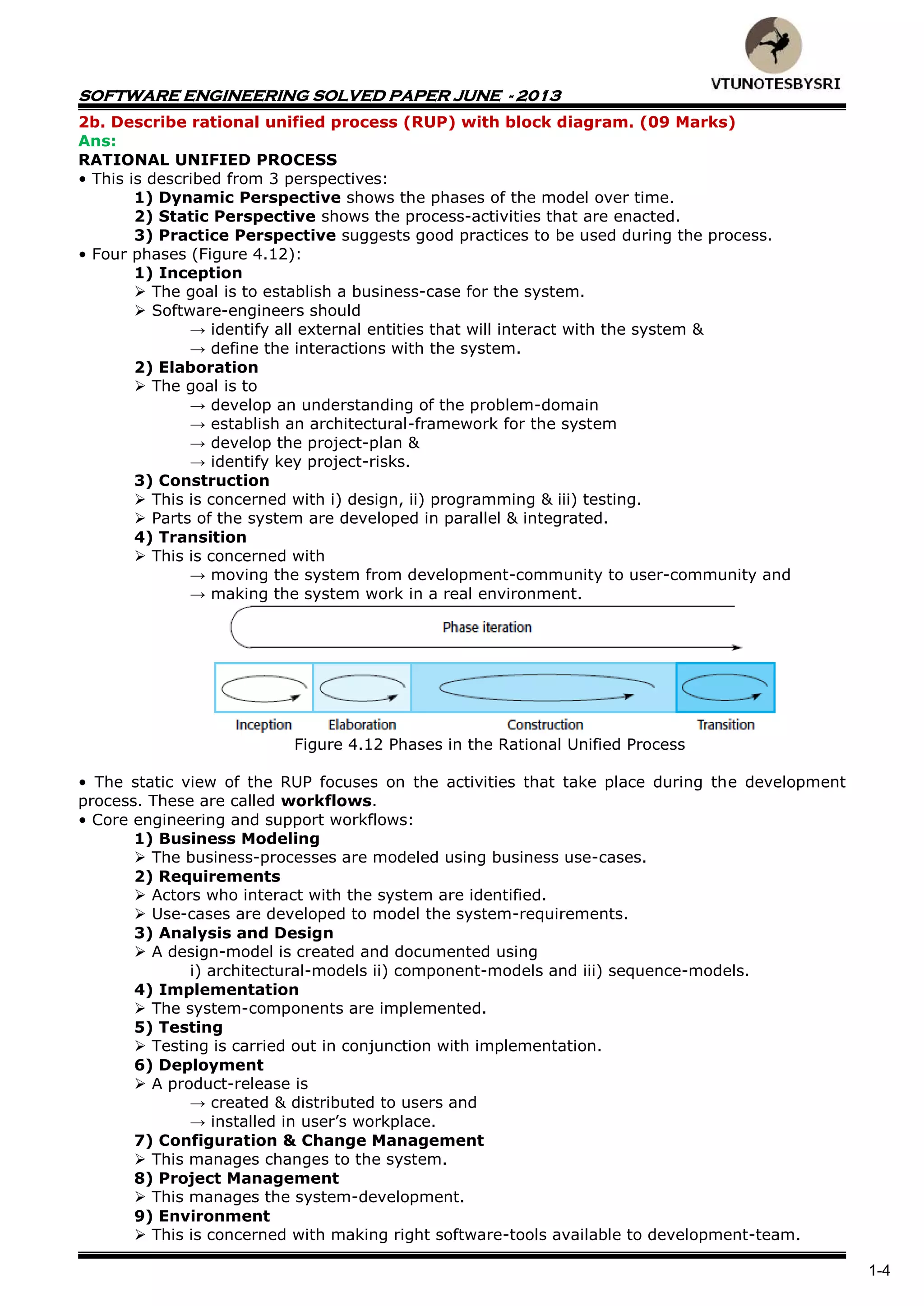
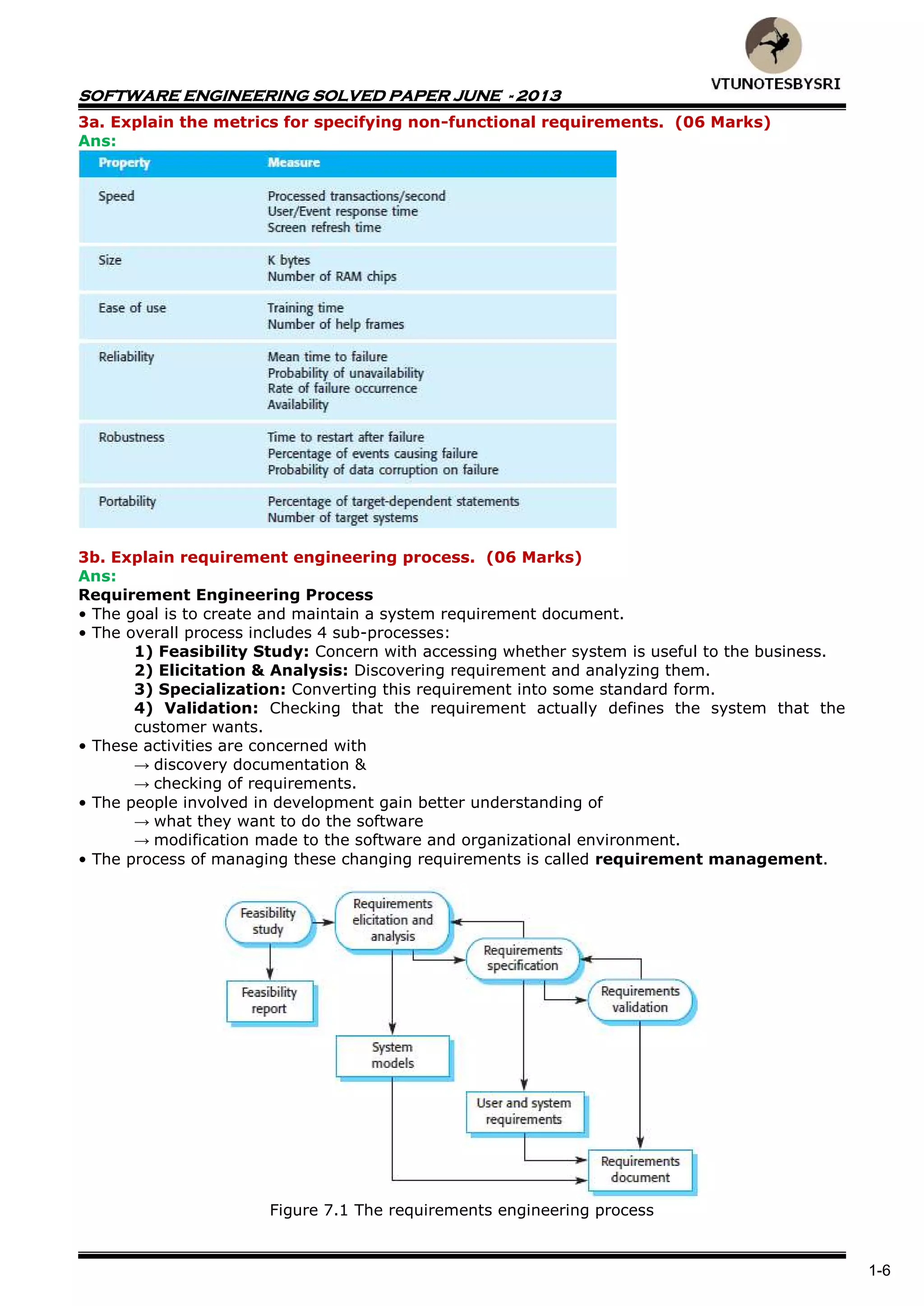
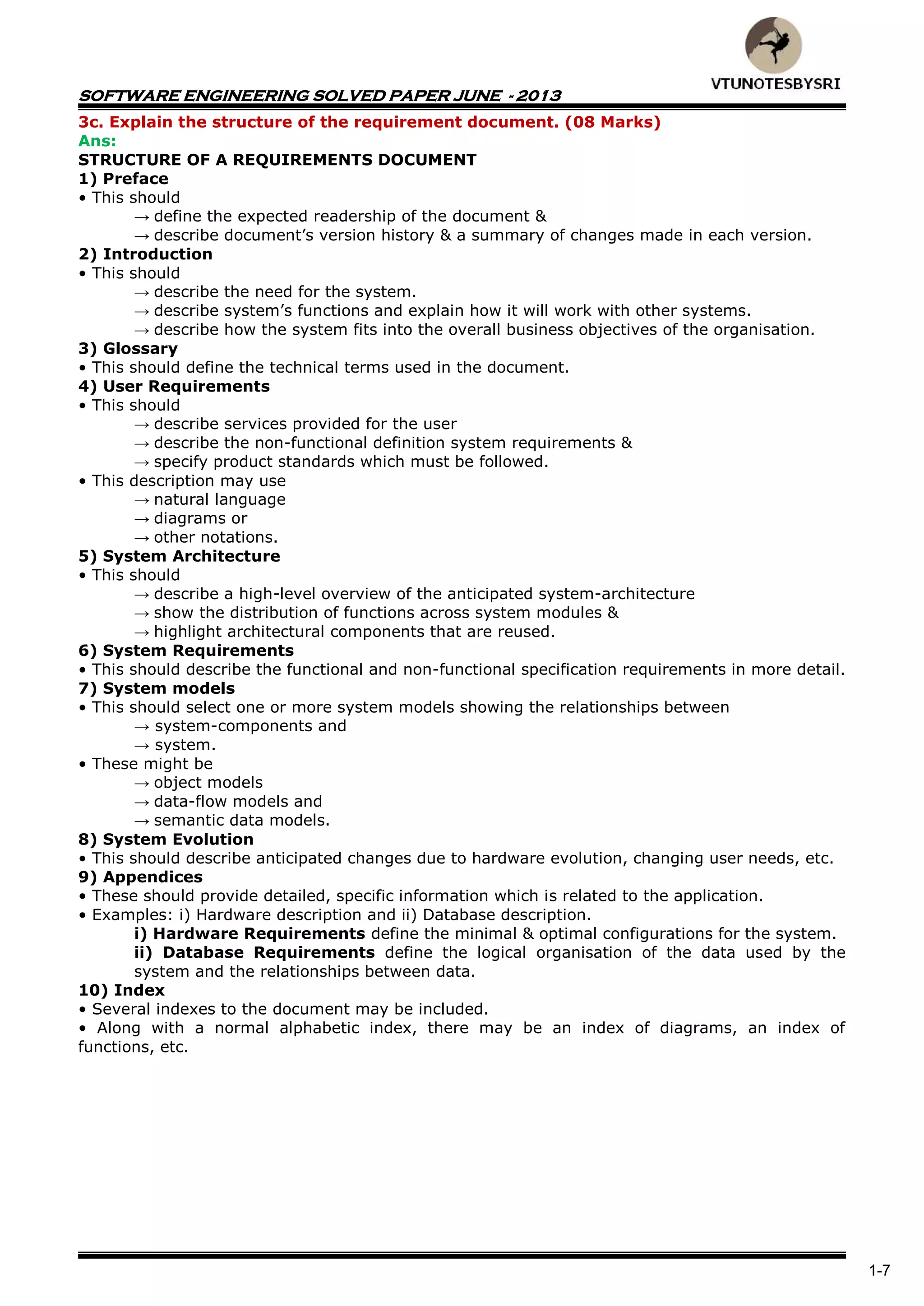
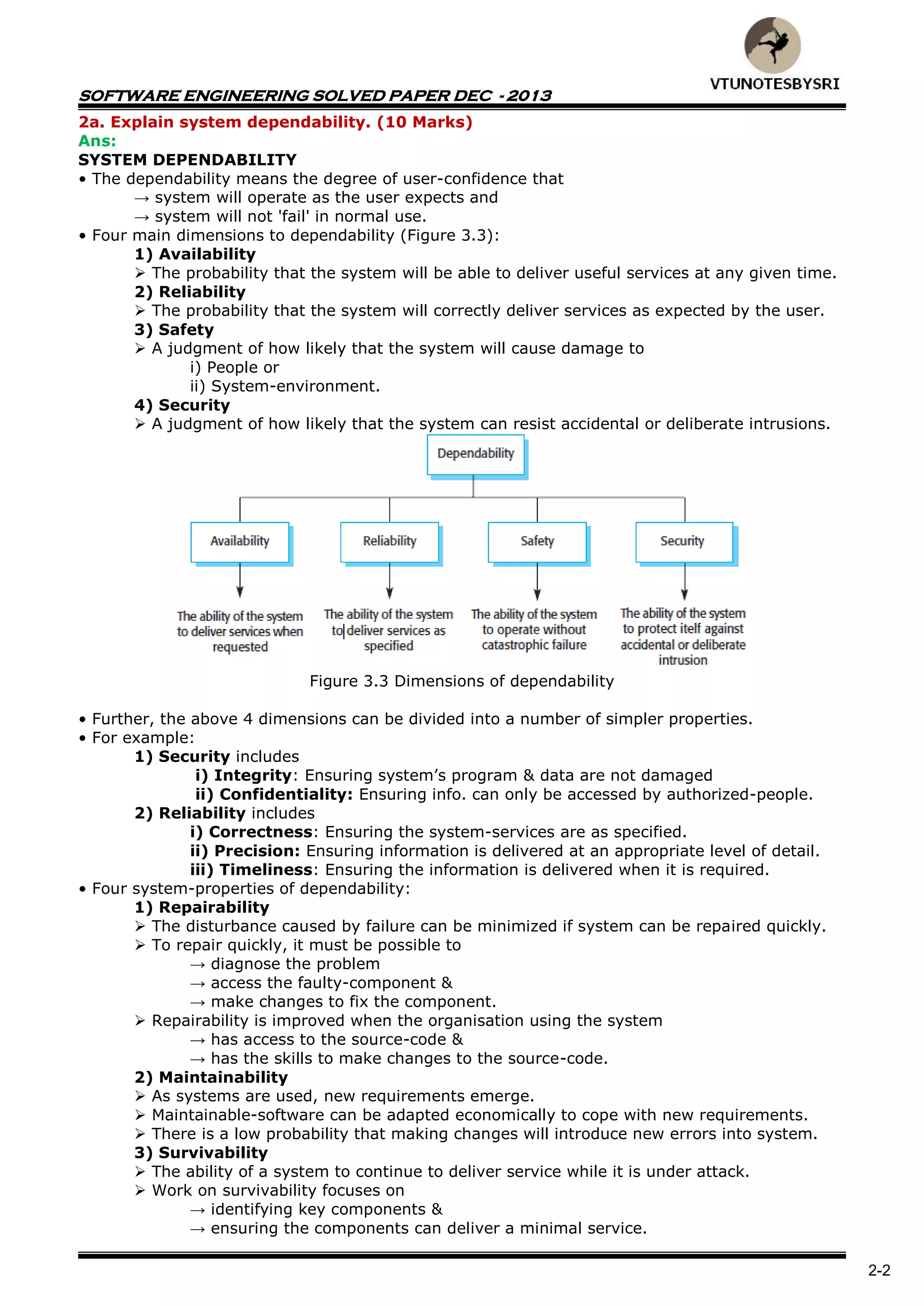
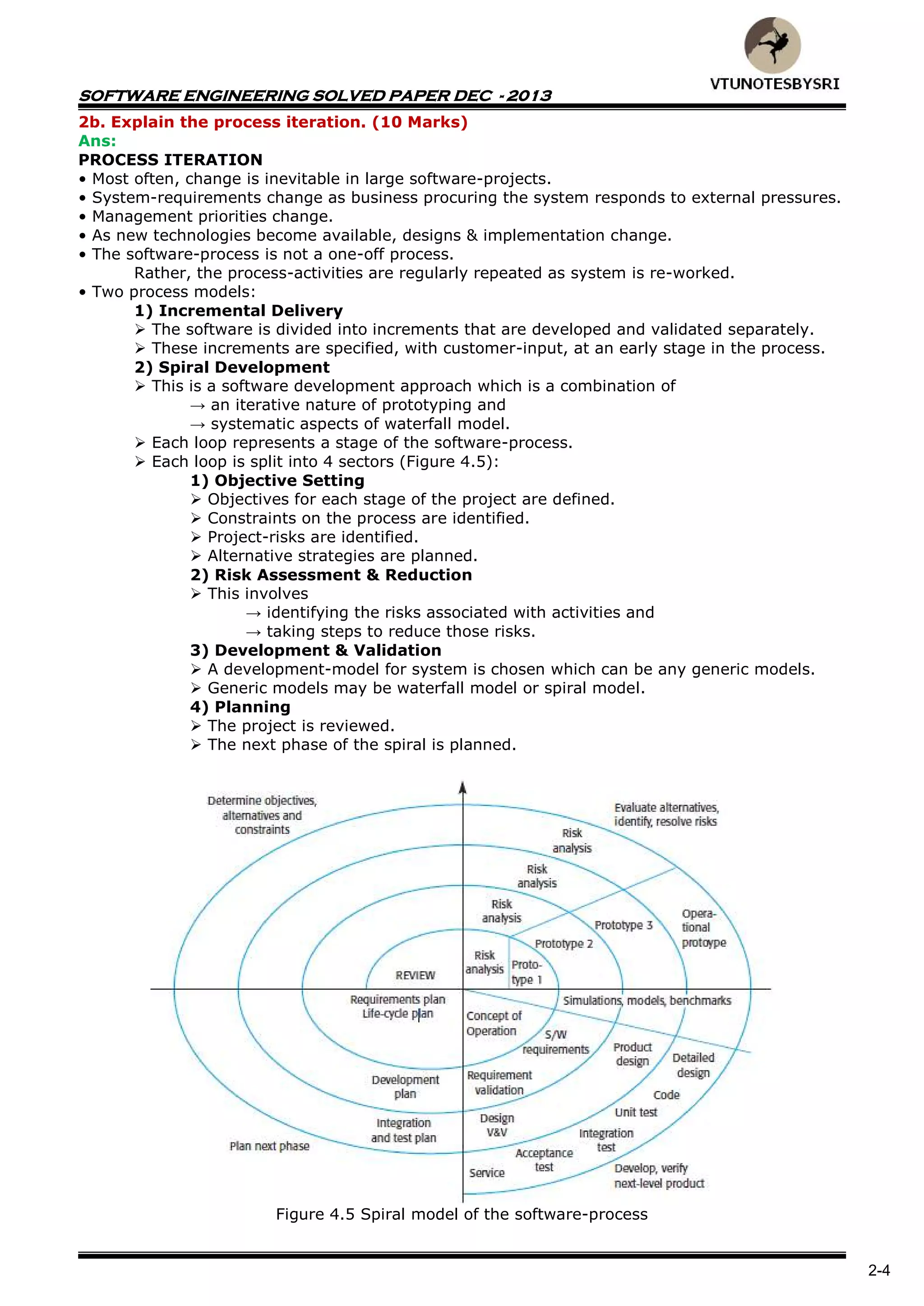
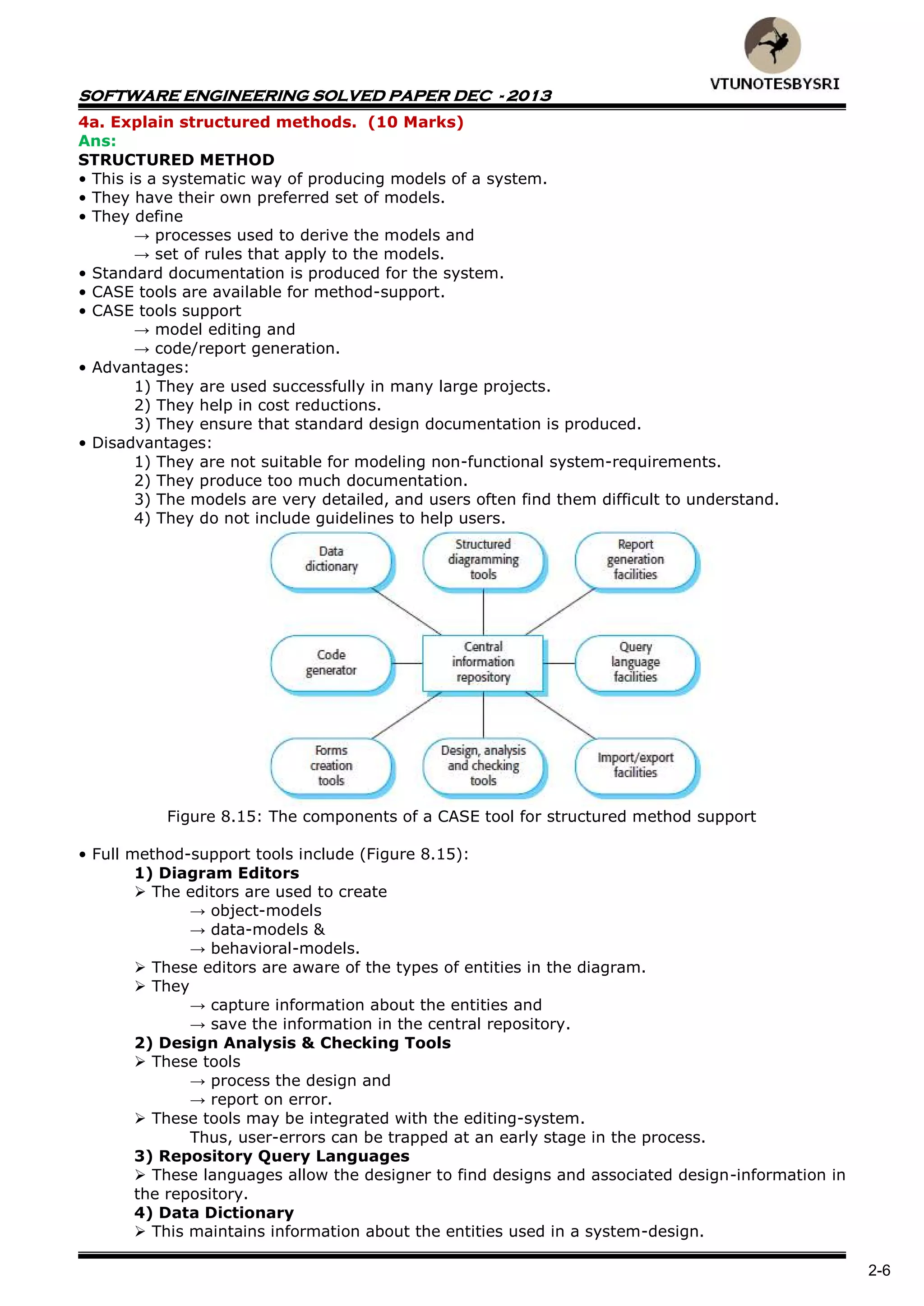
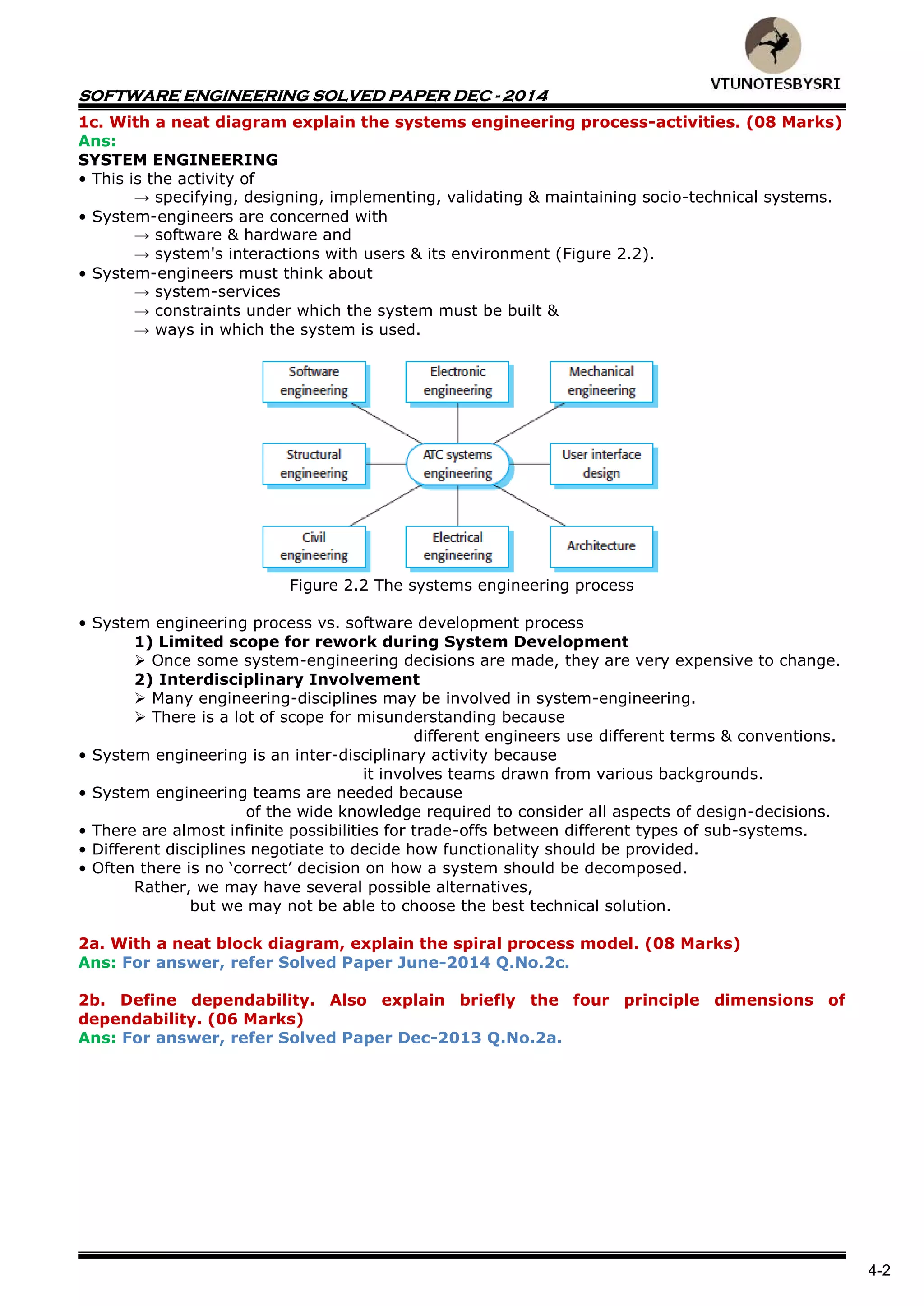
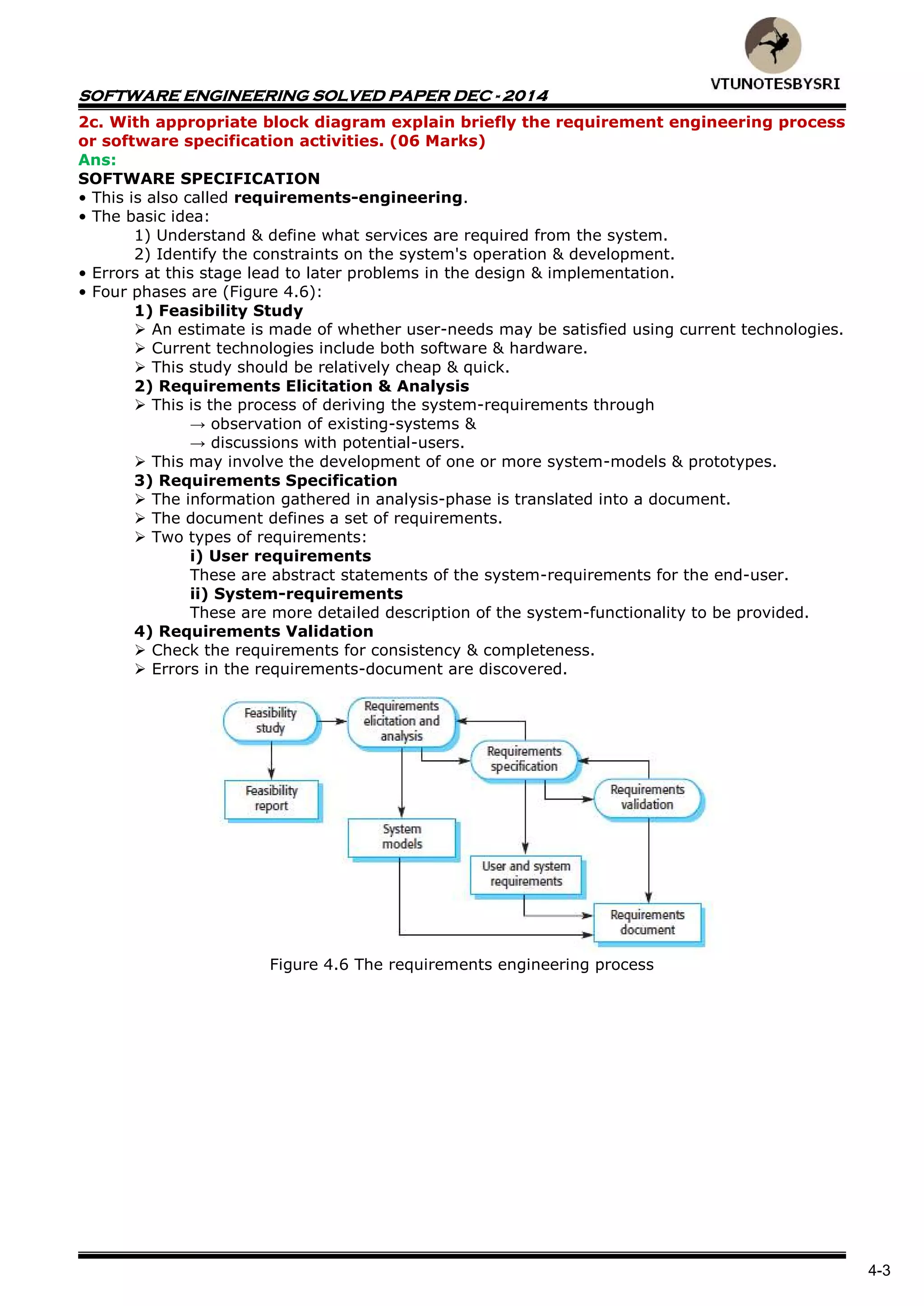
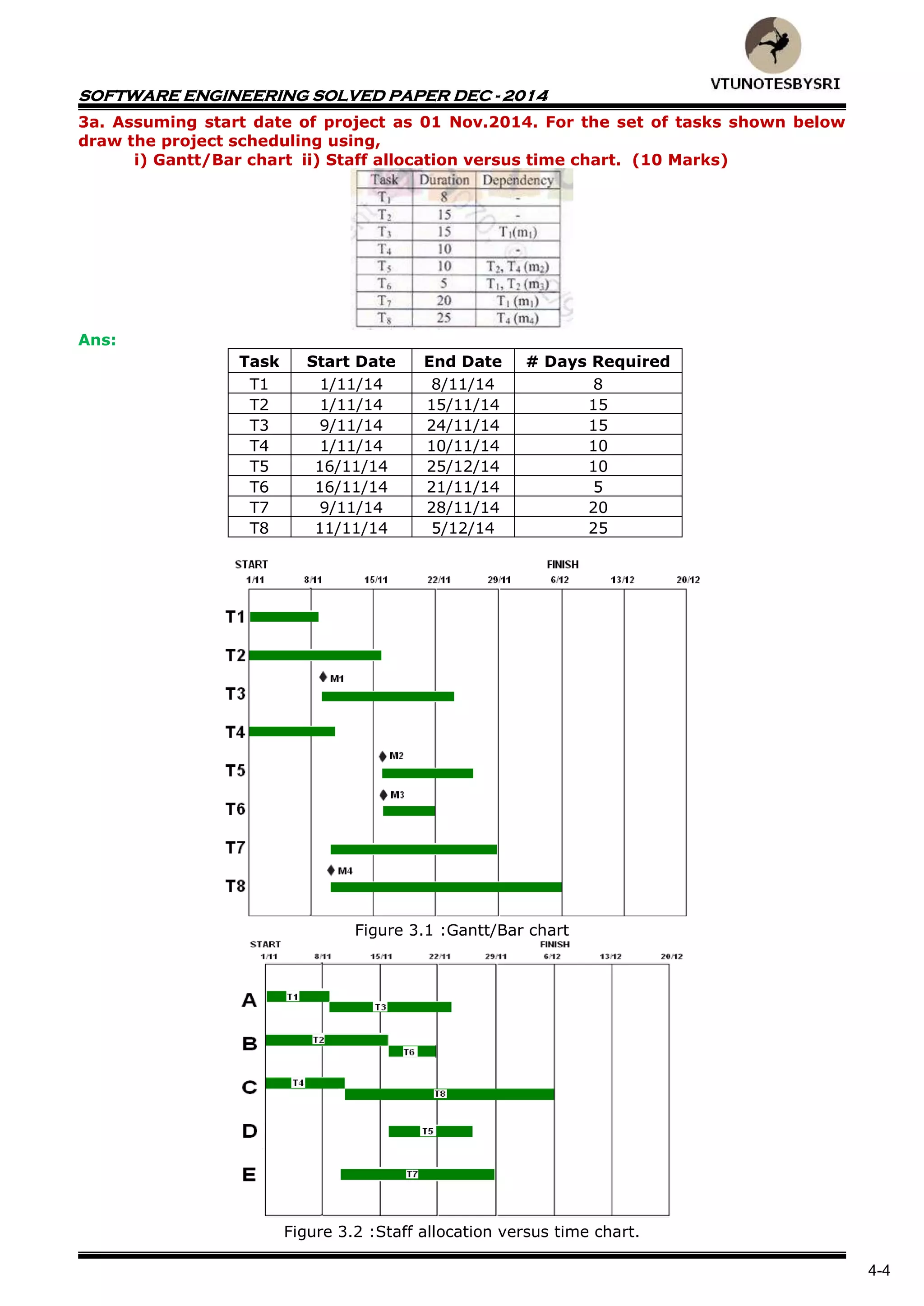
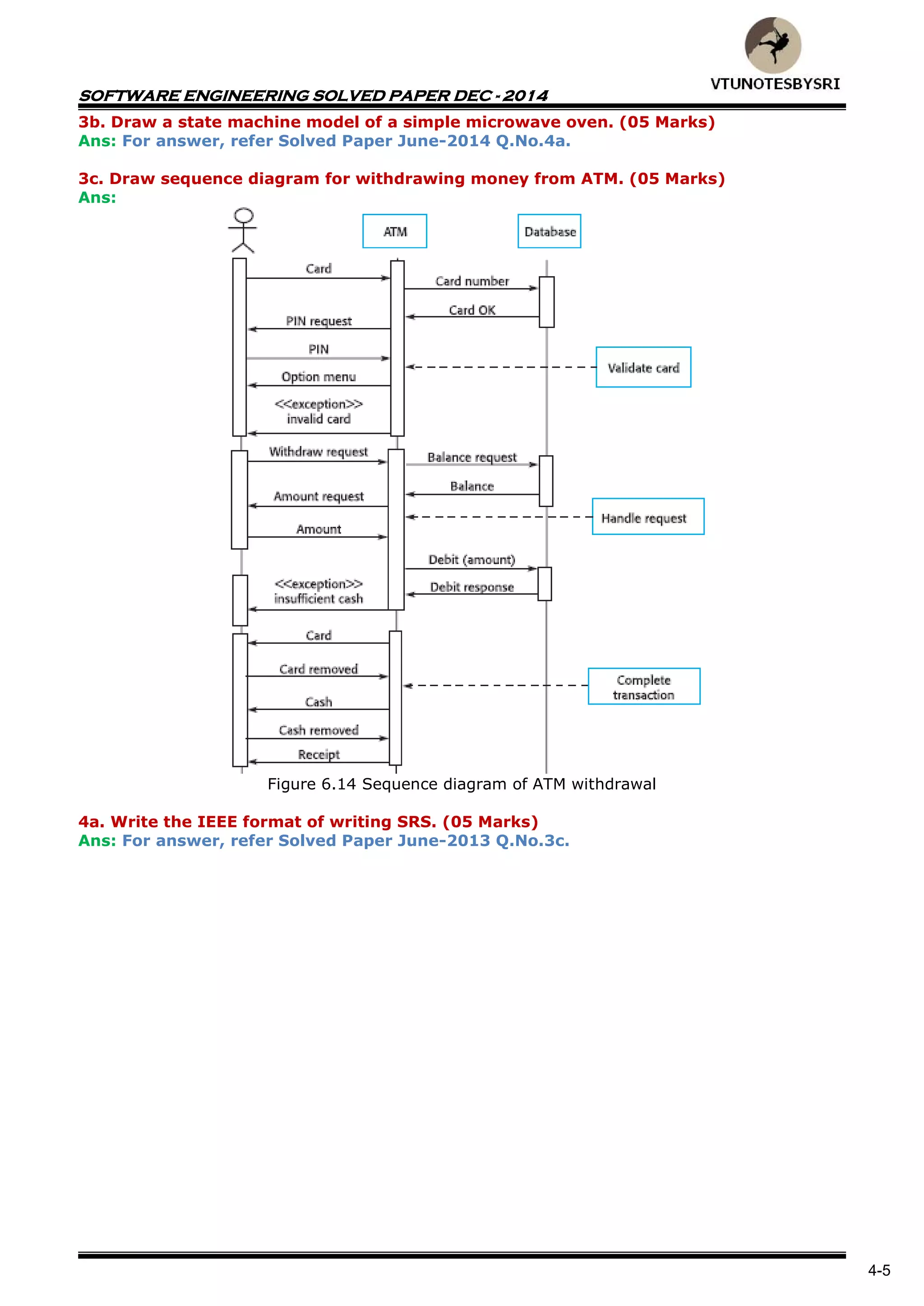
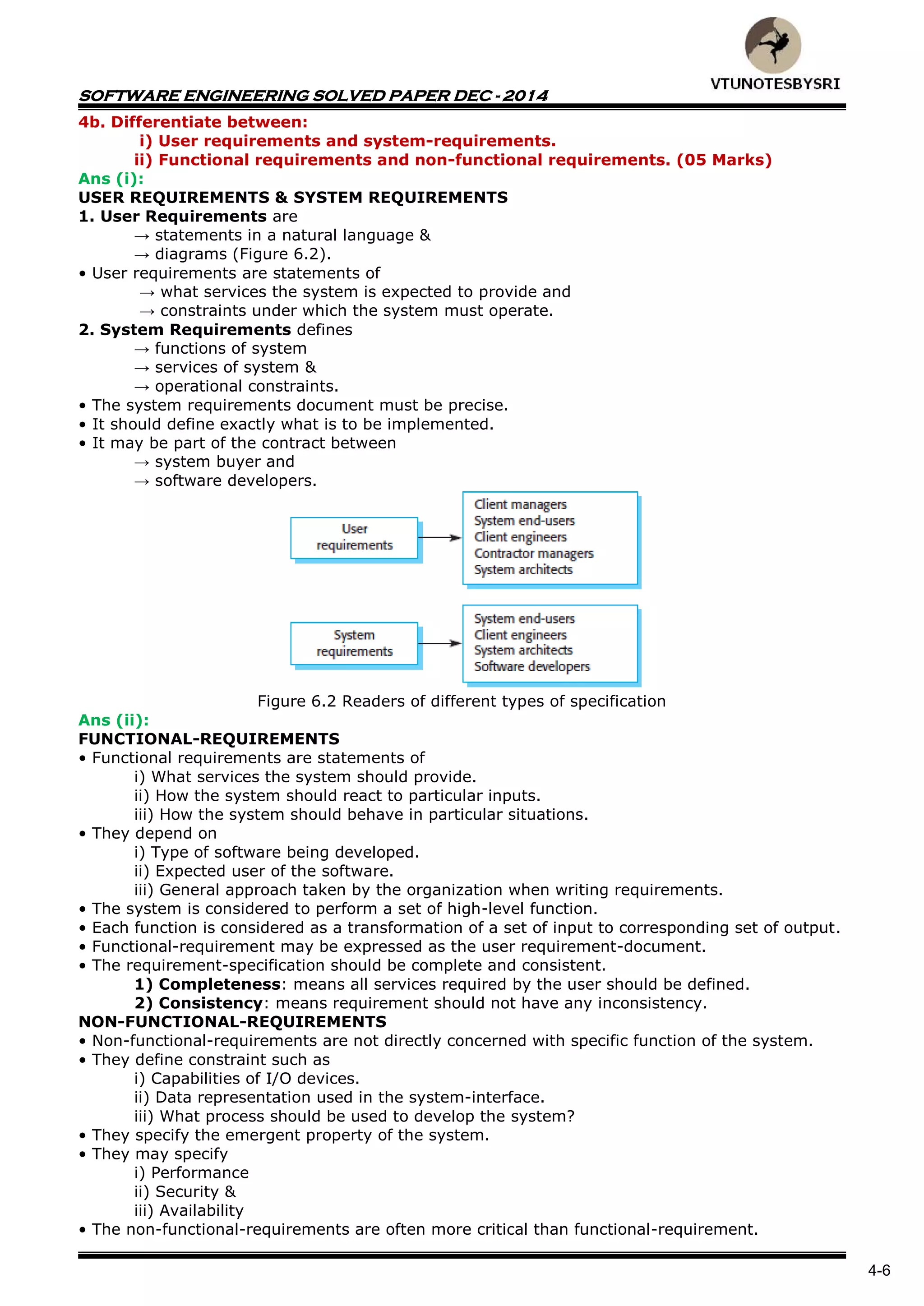
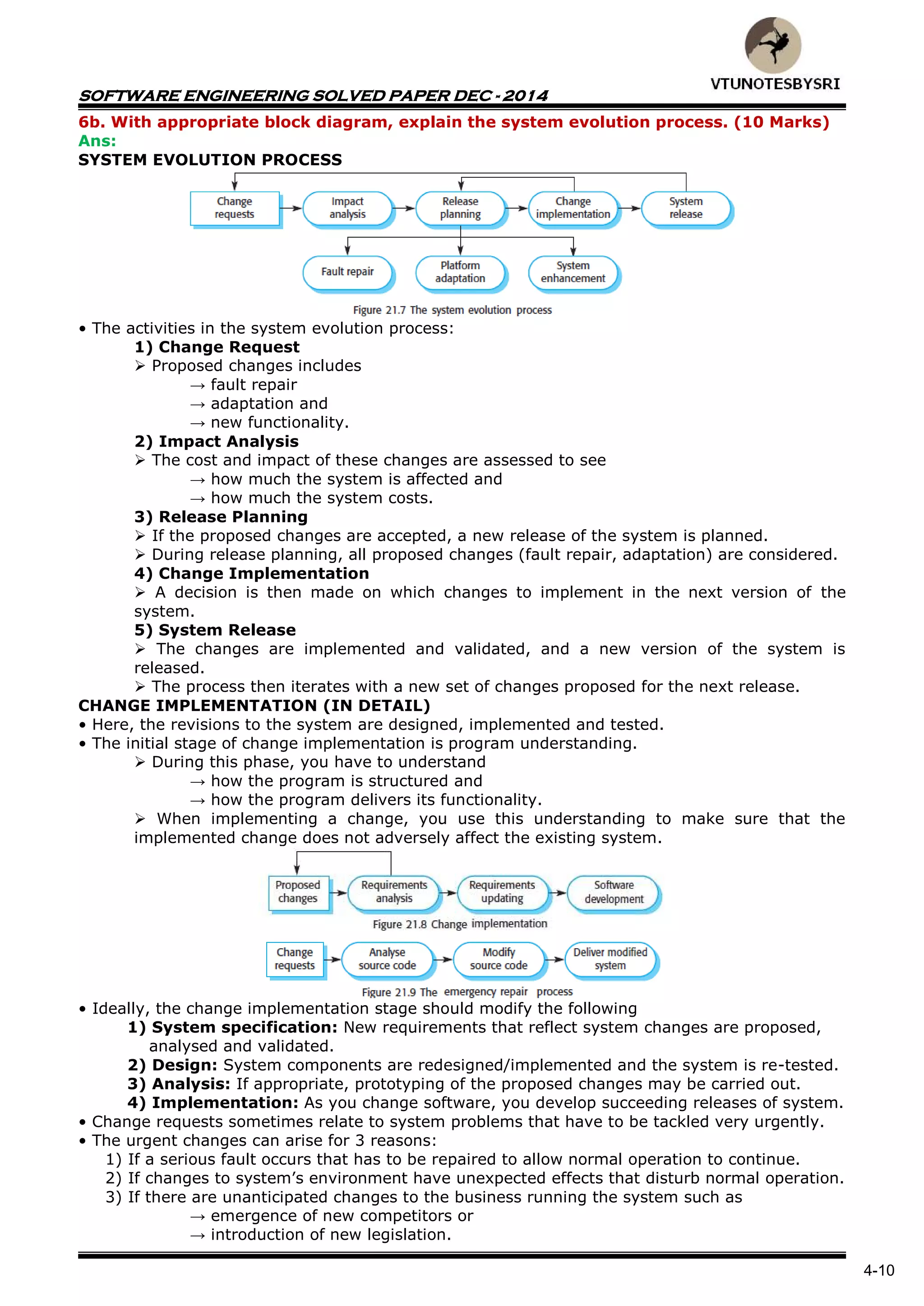
This document summarizes a software engineering solved paper from June 2013. It discusses various topics in software engineering including attributes of good software, definitions of software engineering and different types of software products, emergent system properties with examples, critical systems and their types, the Rational Unified Process (RUP) methodology with block diagrams, security terminology, and metrics for specifying non-functional requirements. The requirement engineering process is also explained with the main goal being to create and maintain a system requirement document through various sub-processes like feasibility study, elicitation and analysis, validation, and management of requirements.