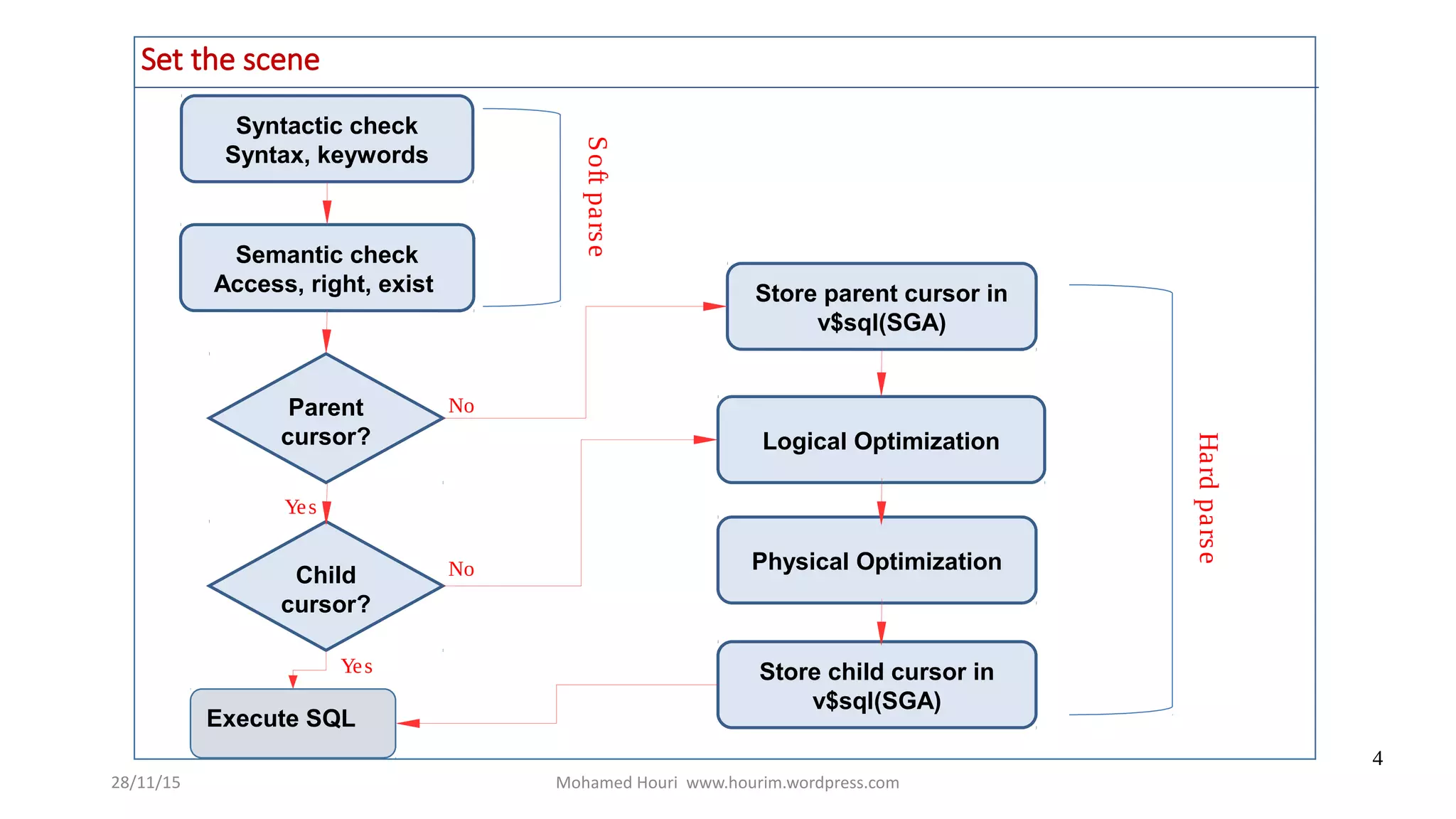
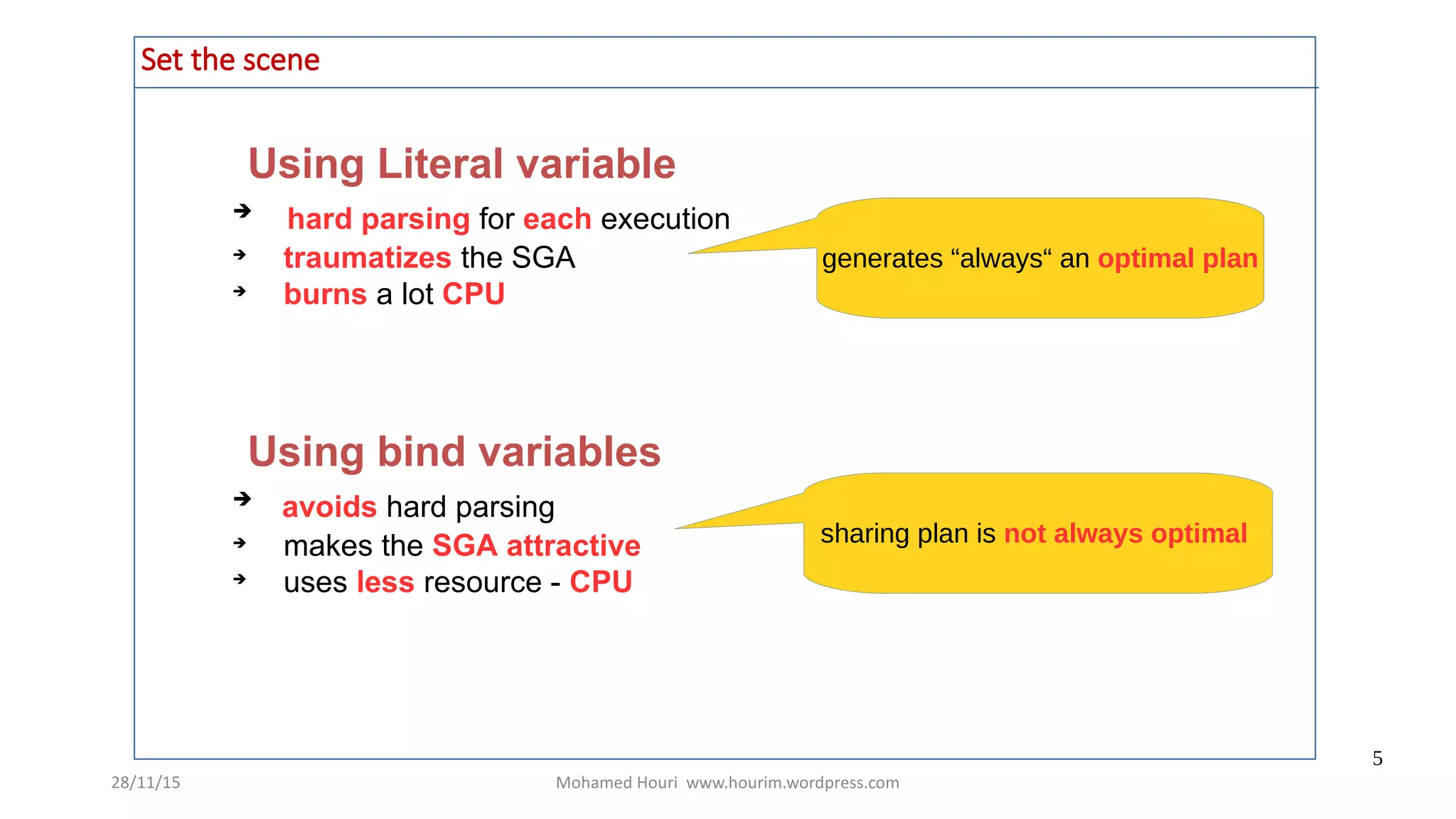
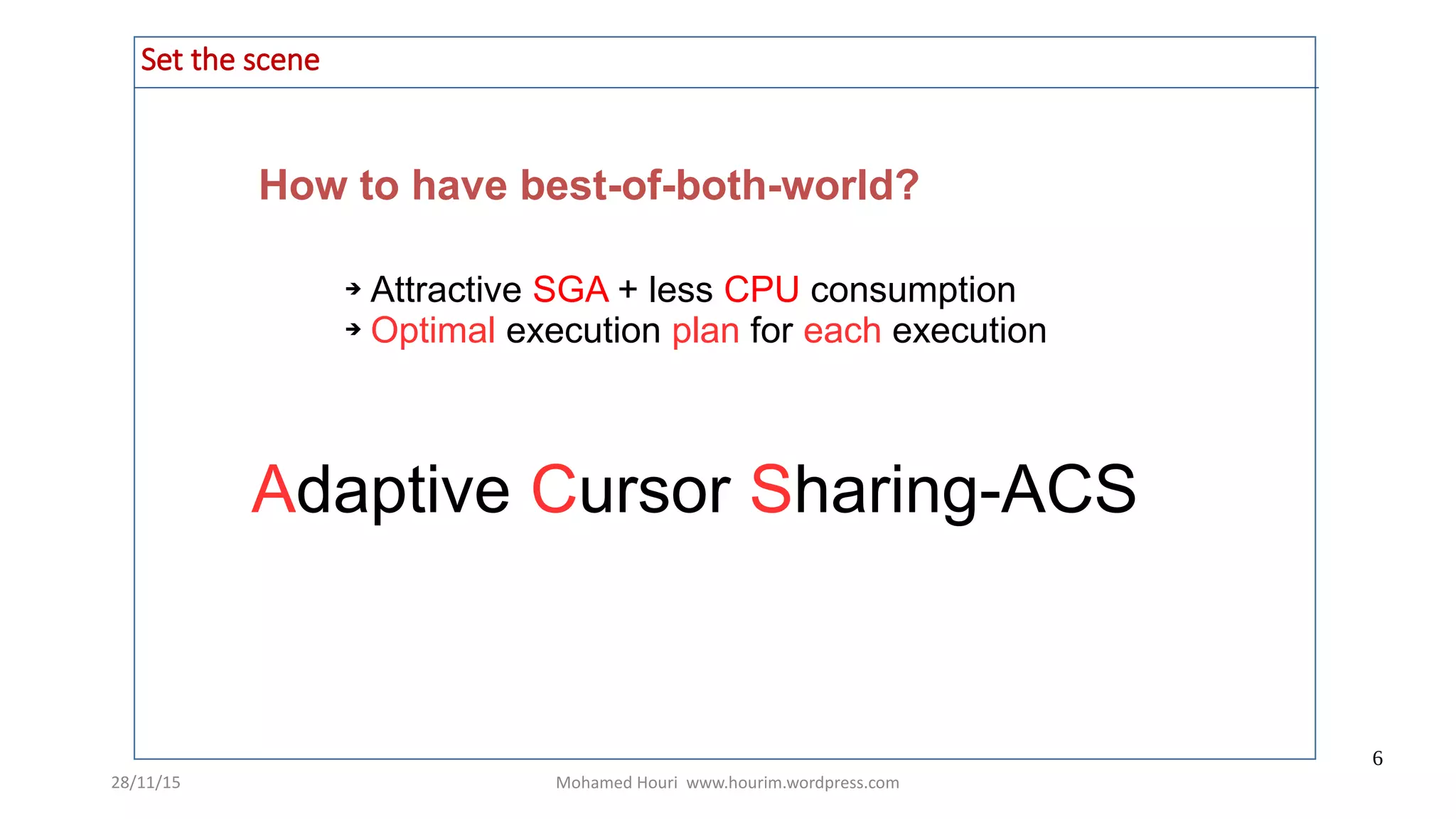
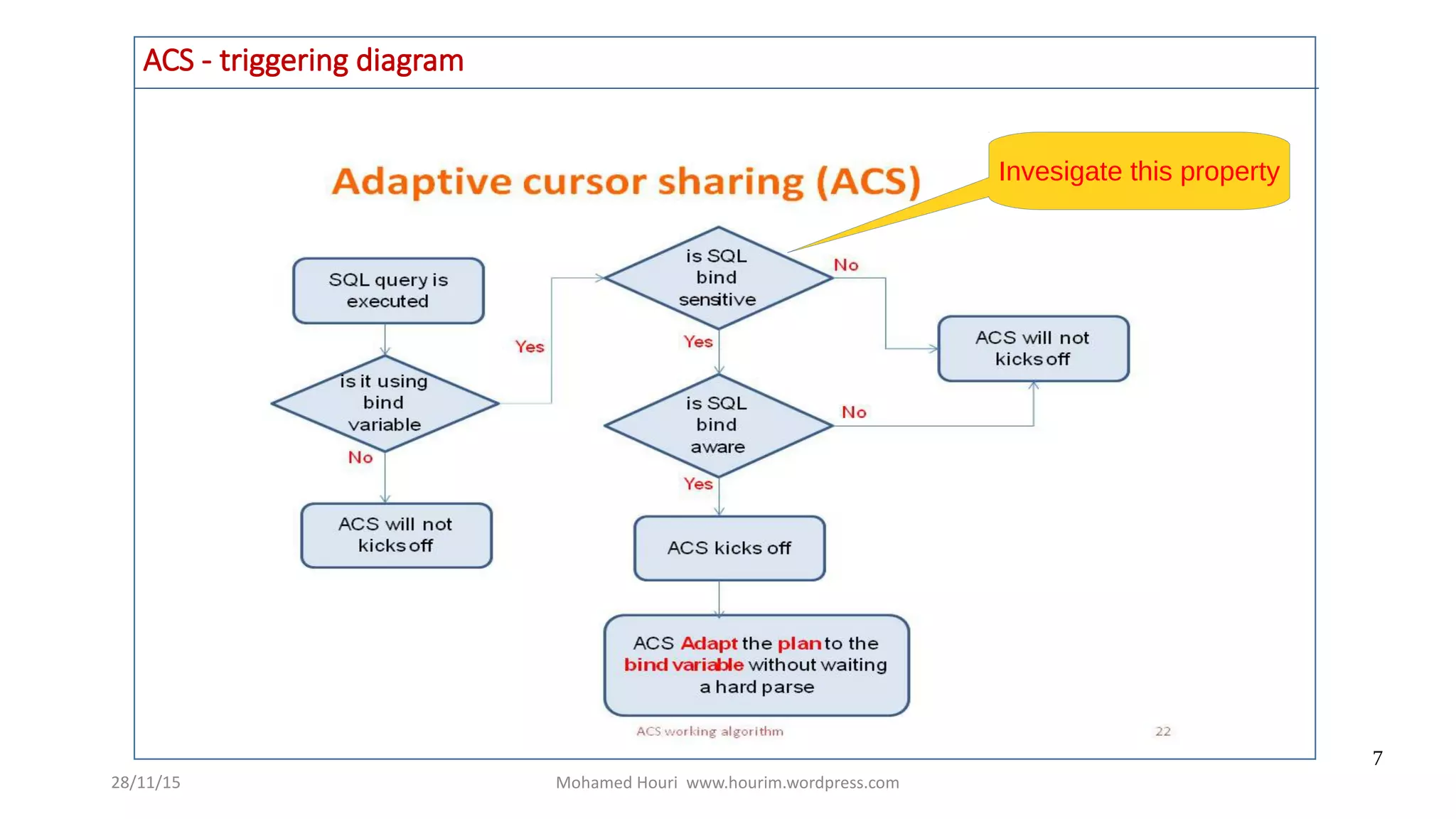
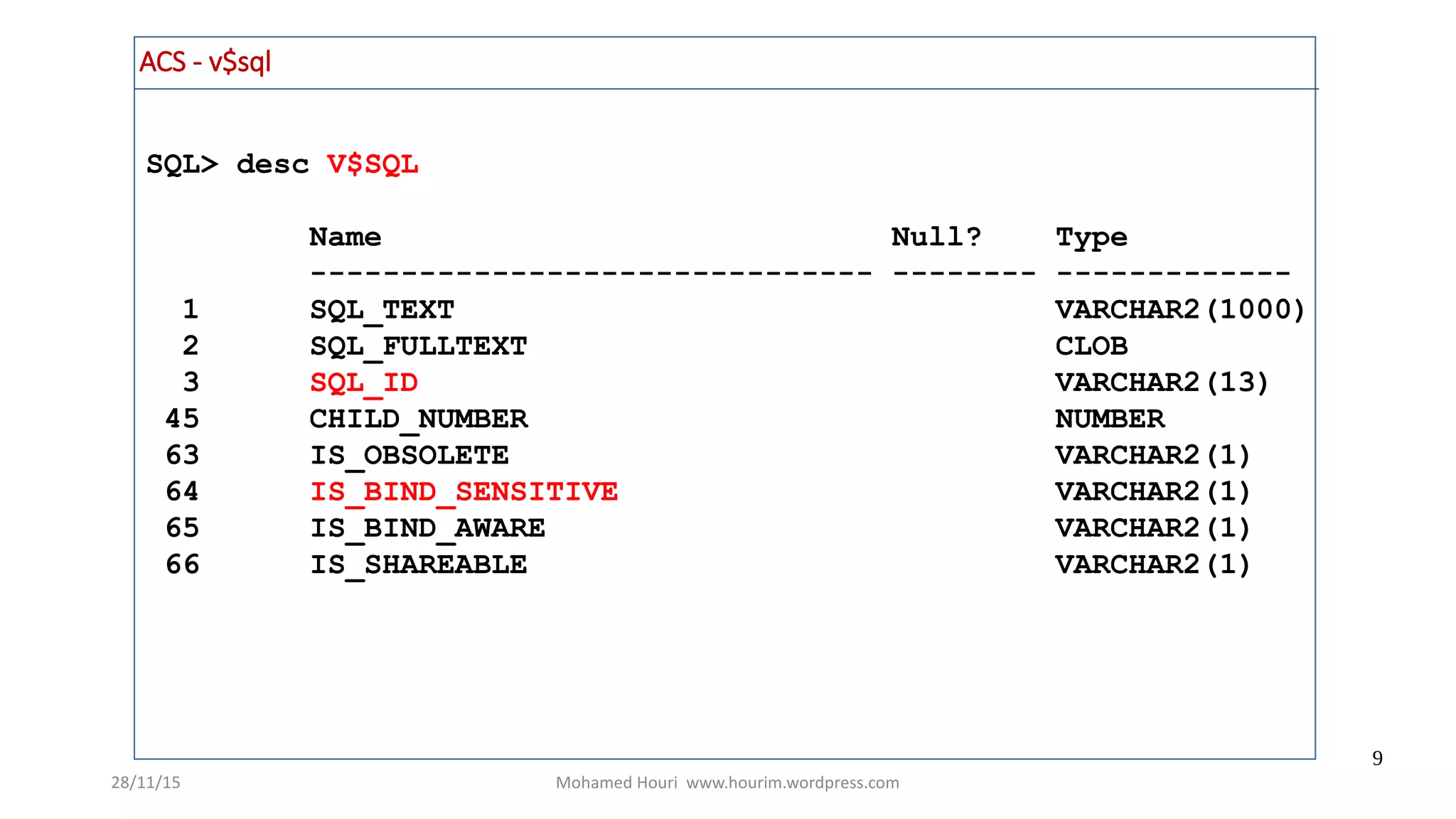
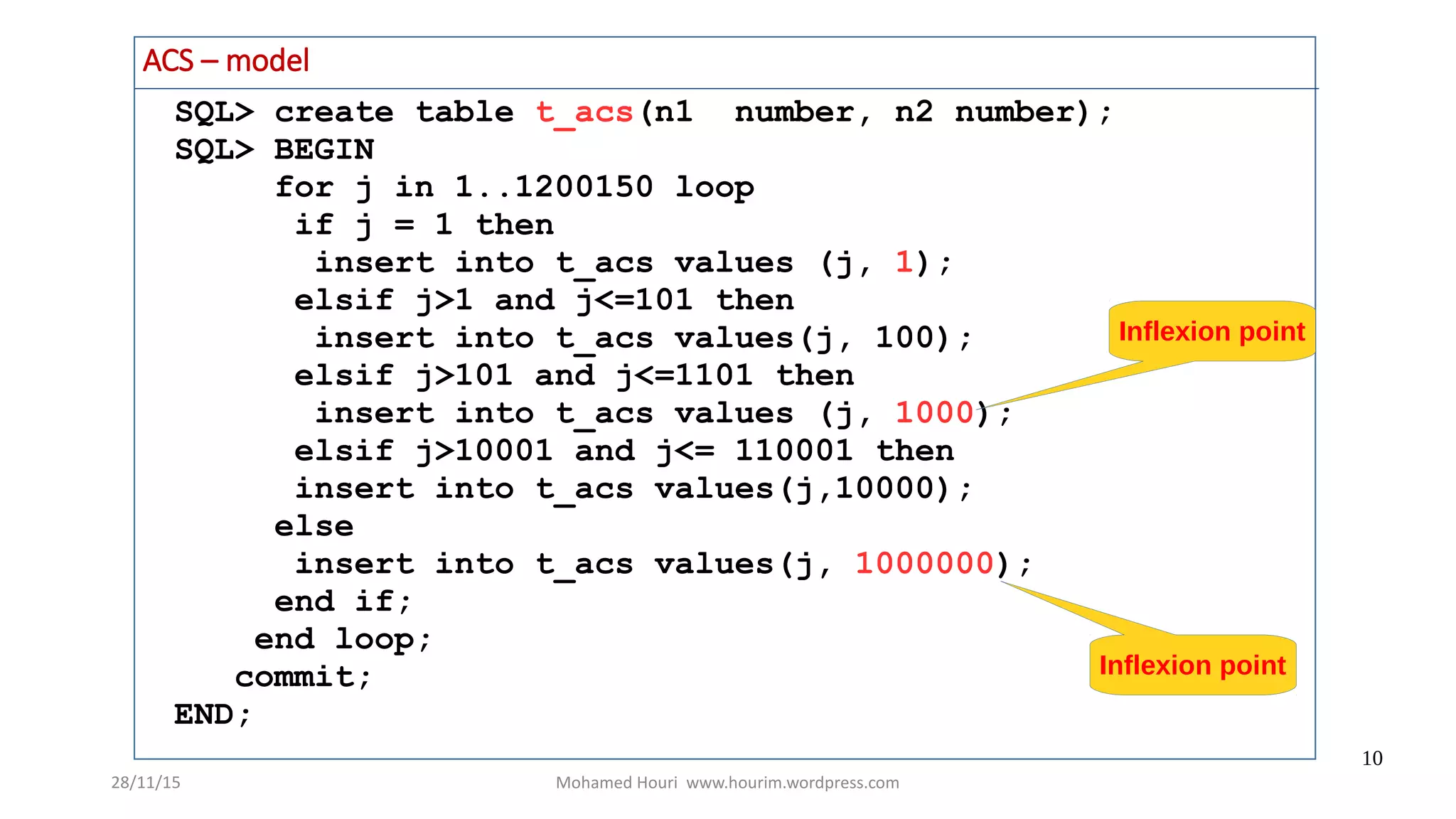
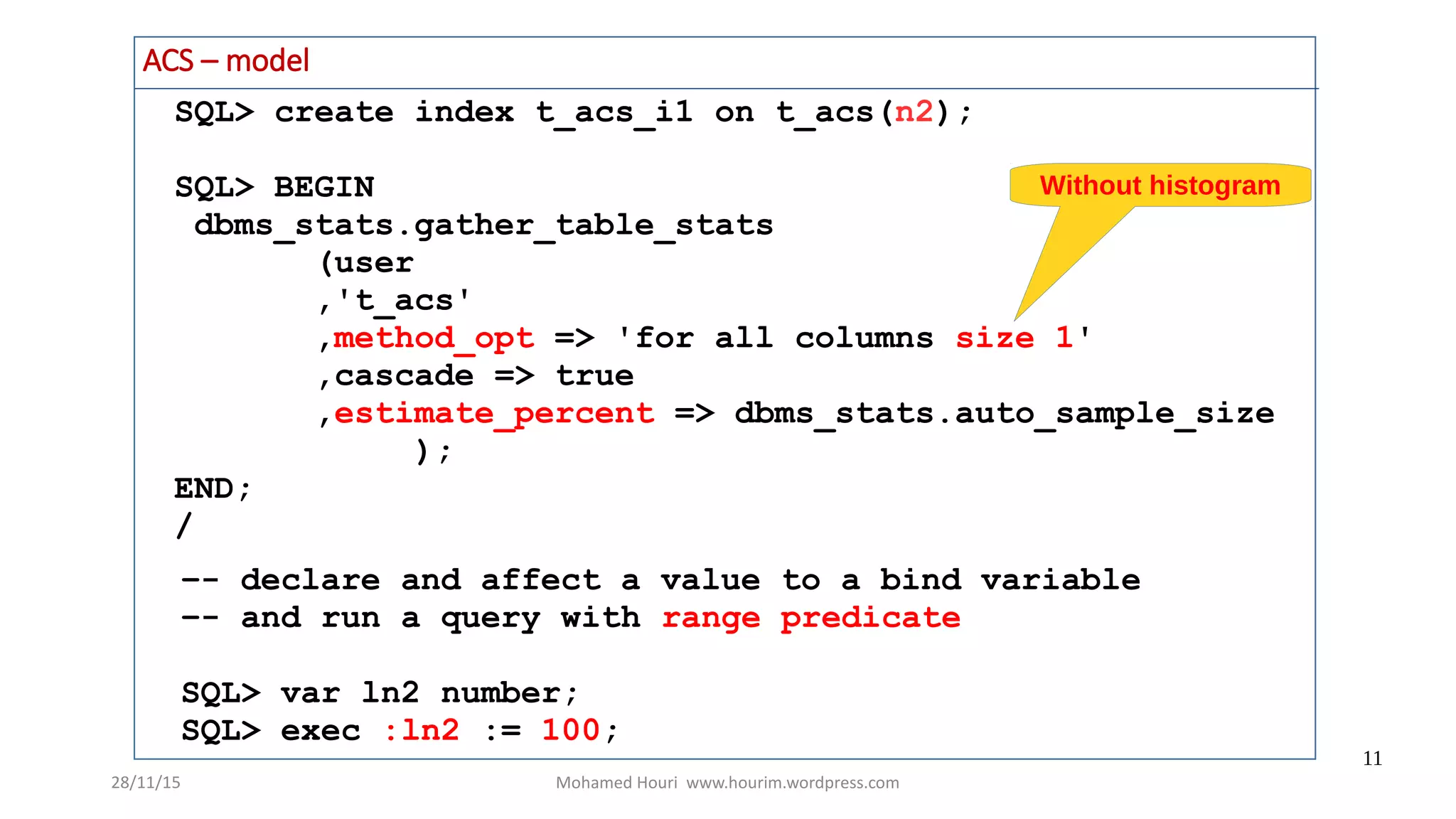
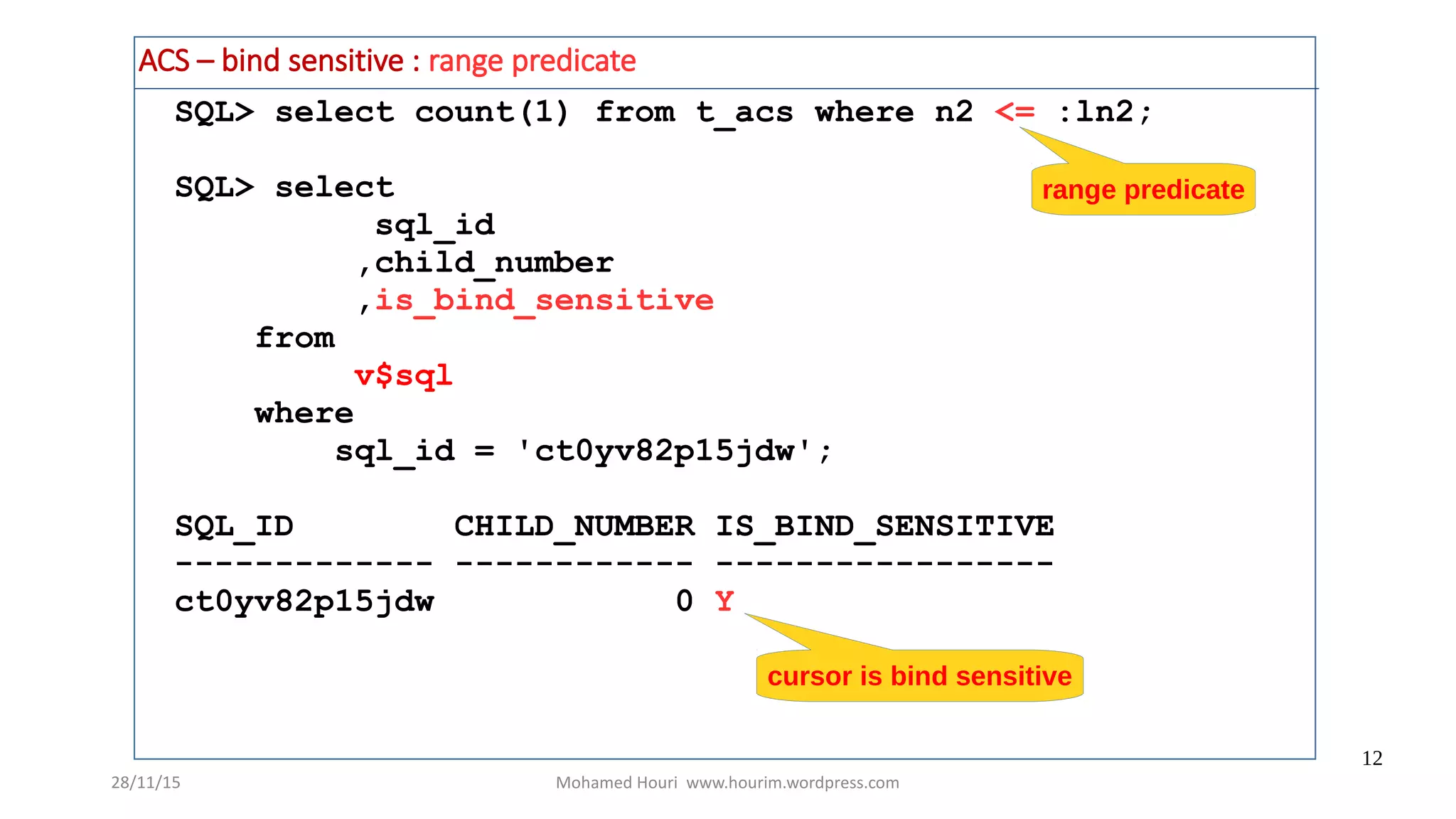
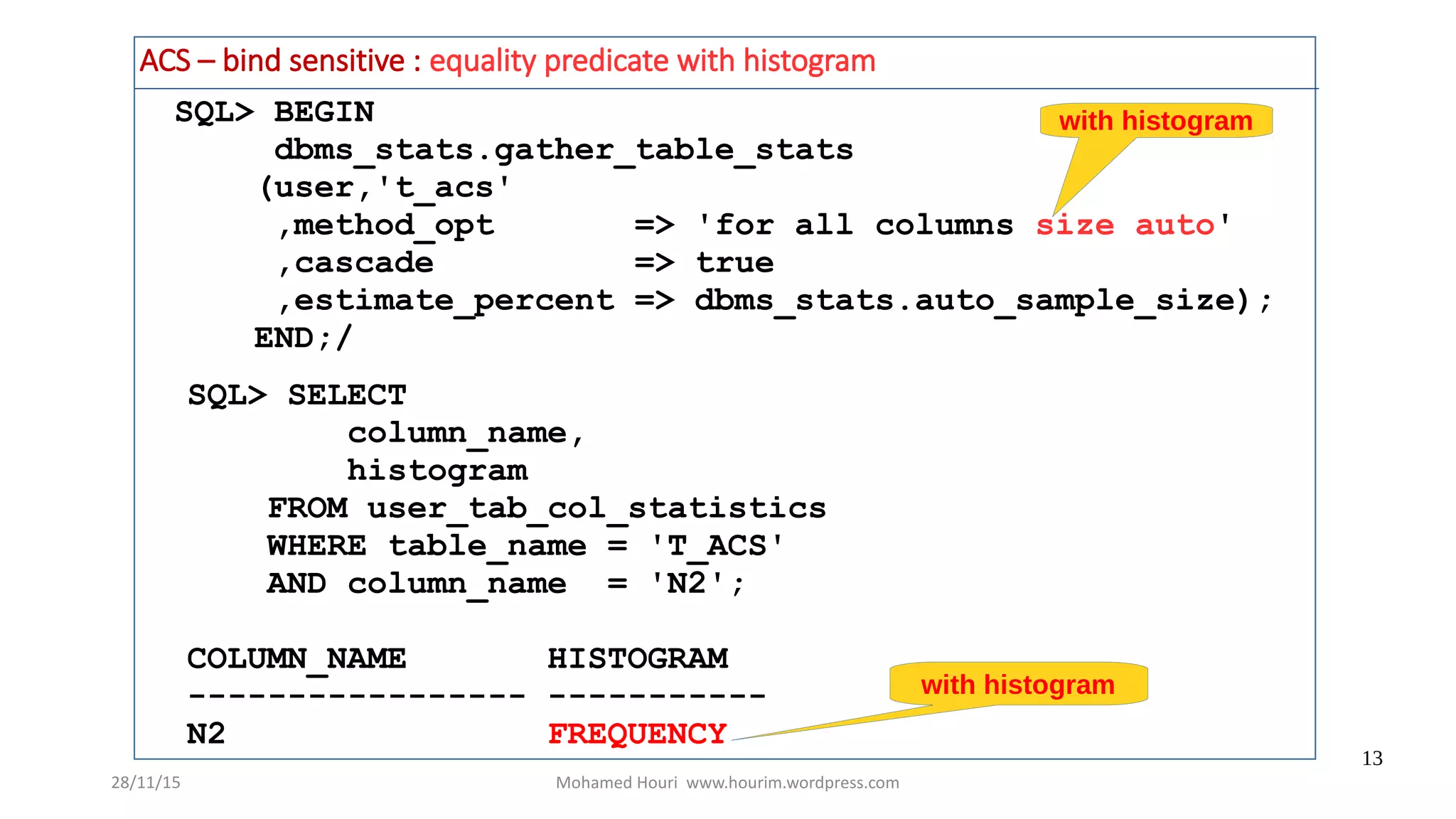
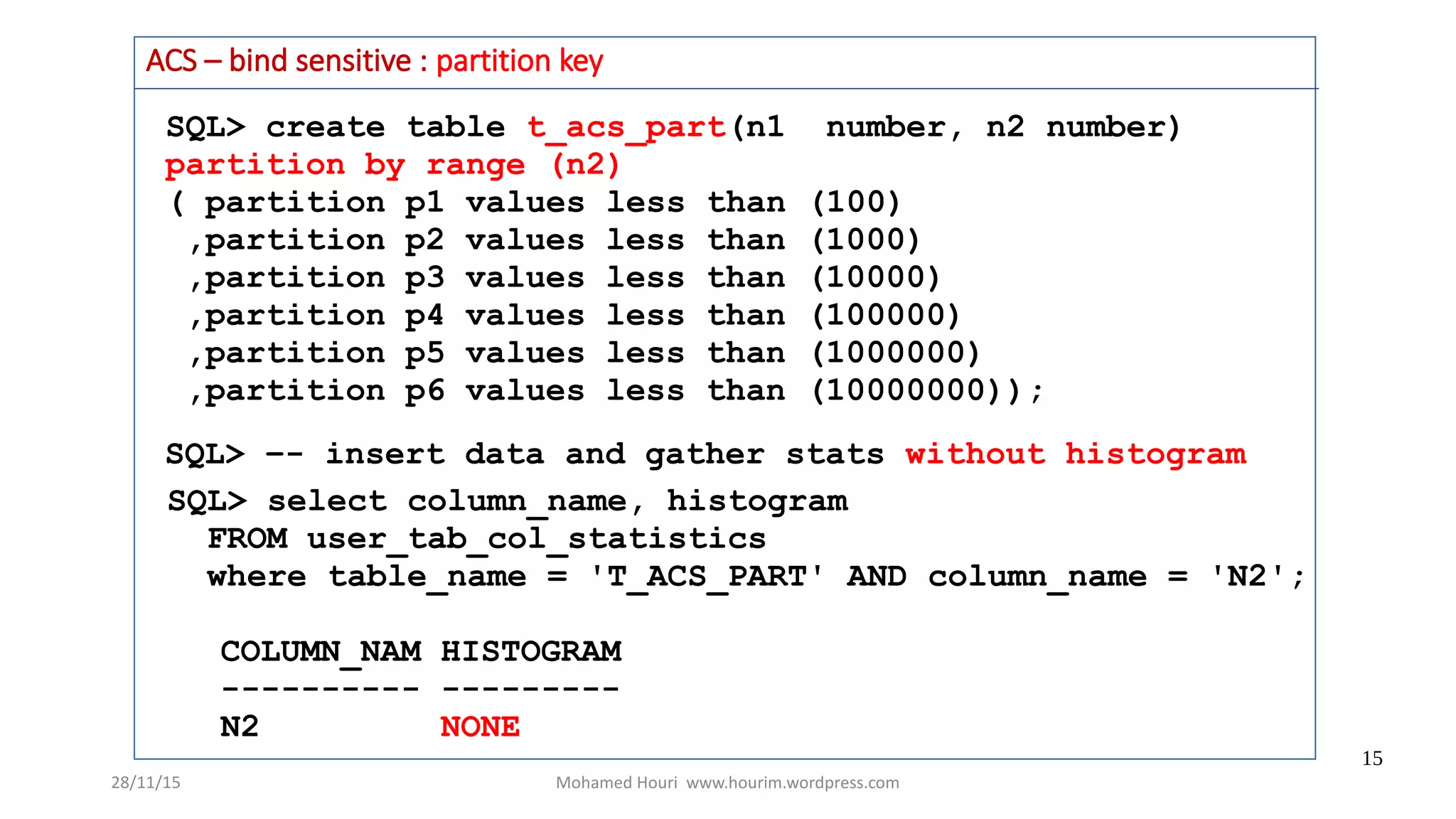
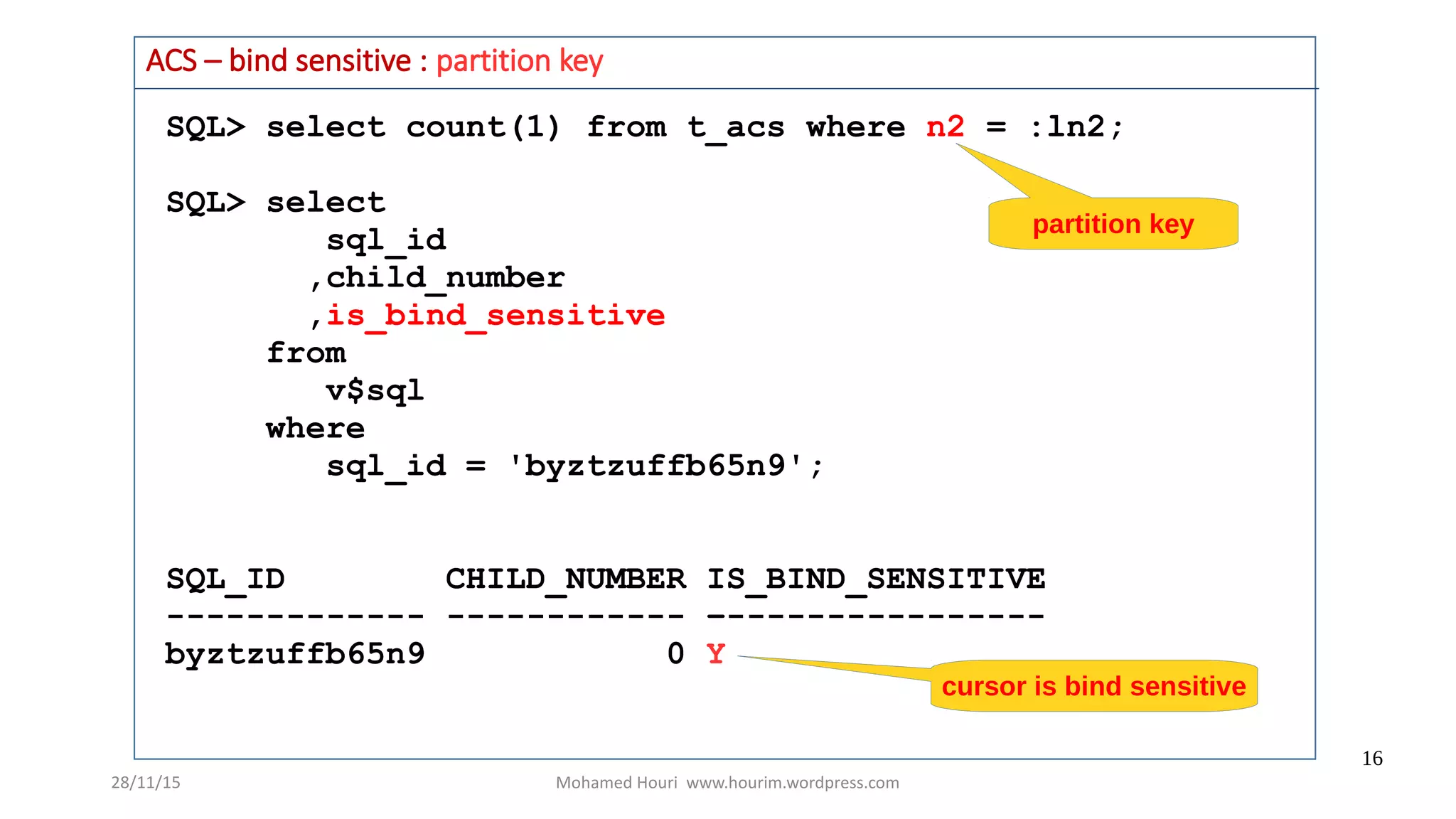
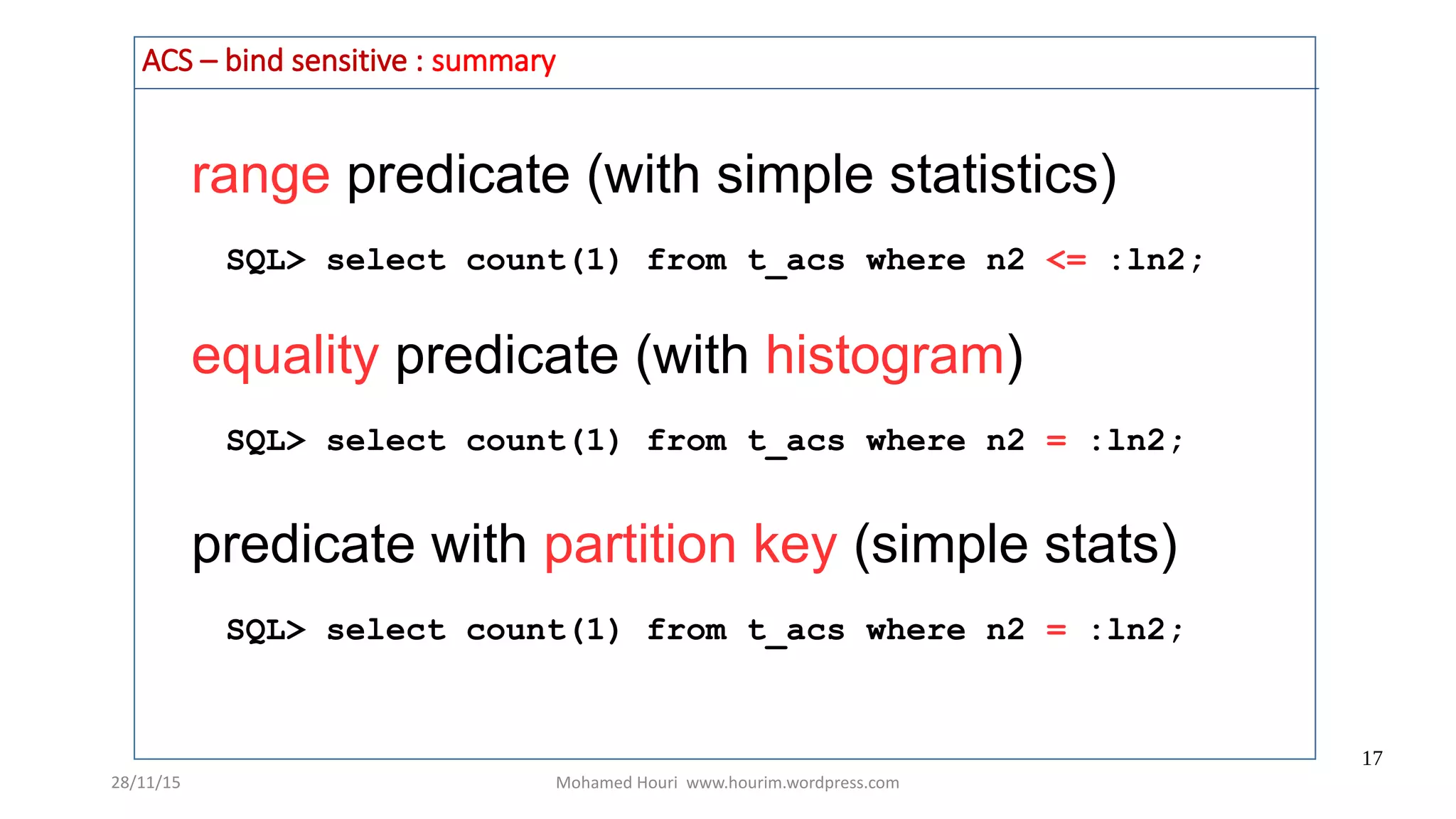
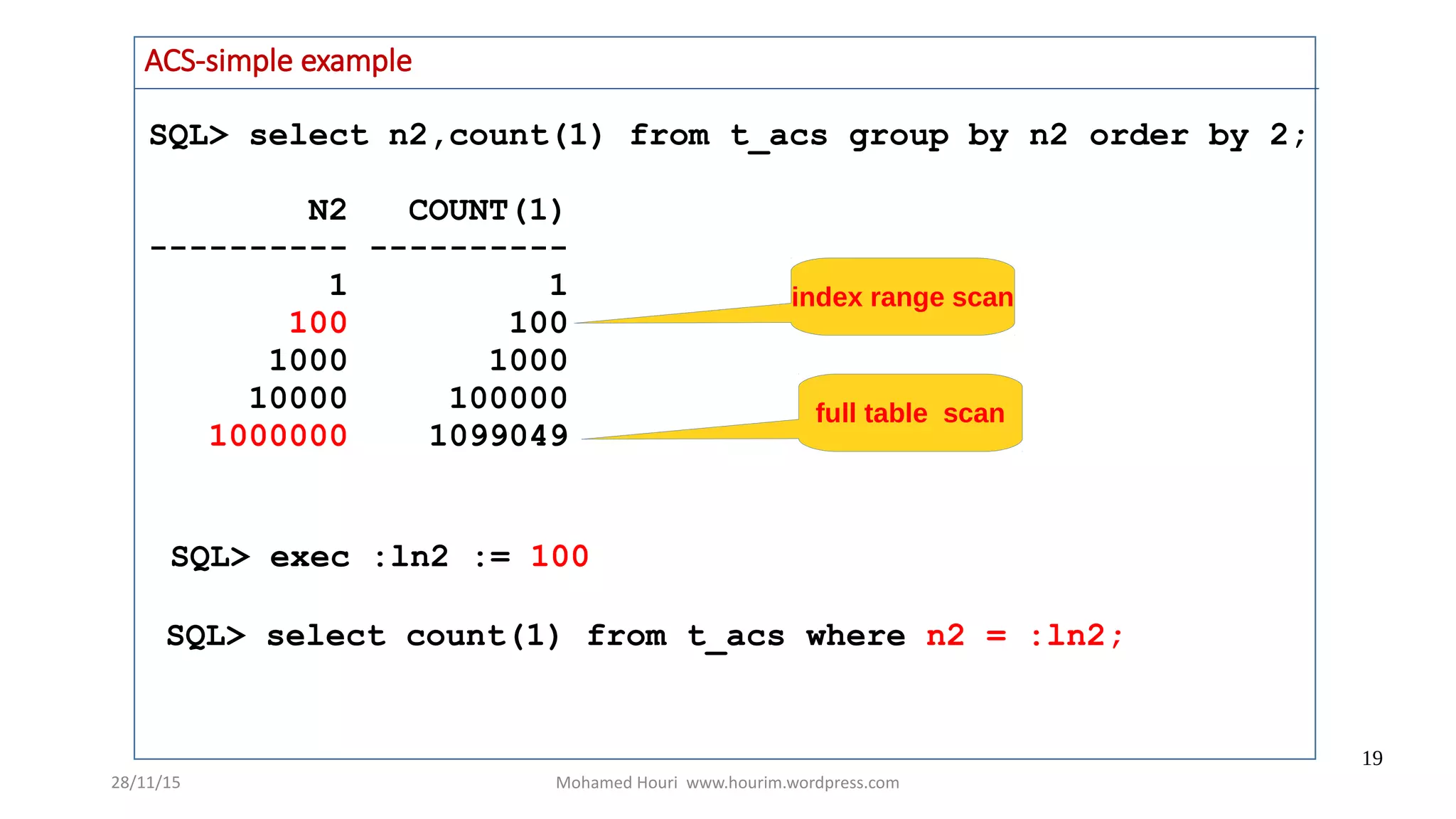
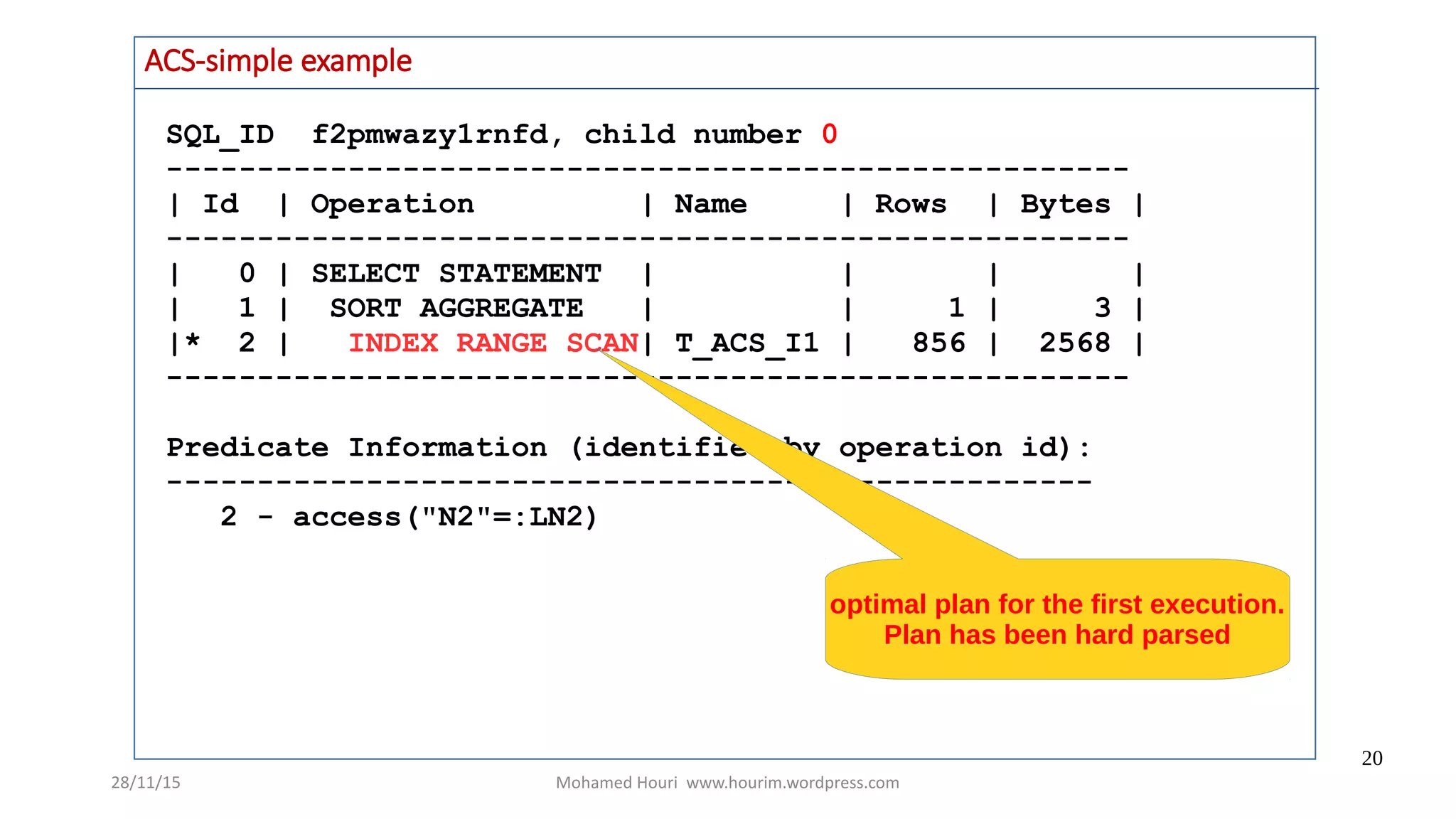
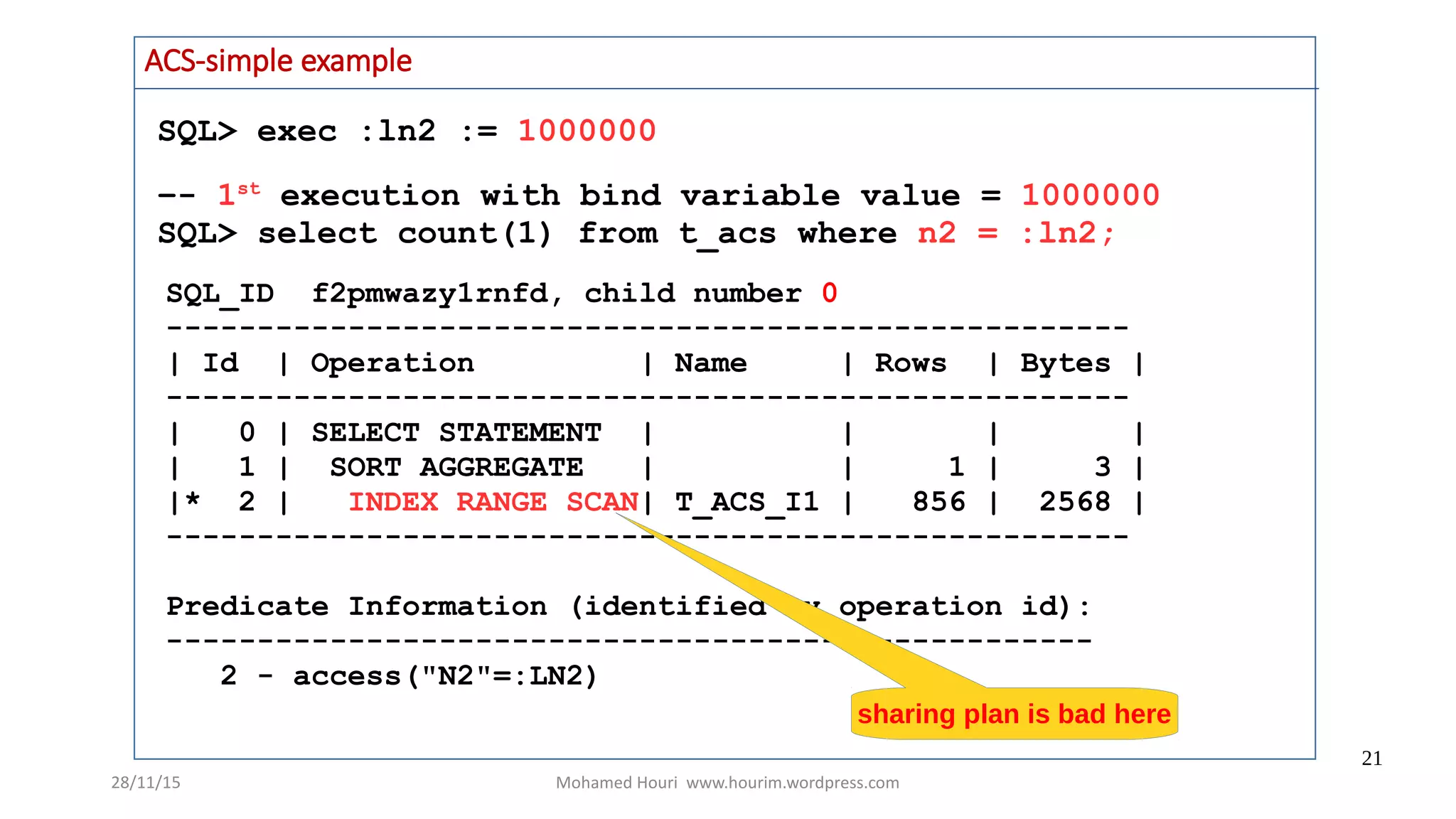
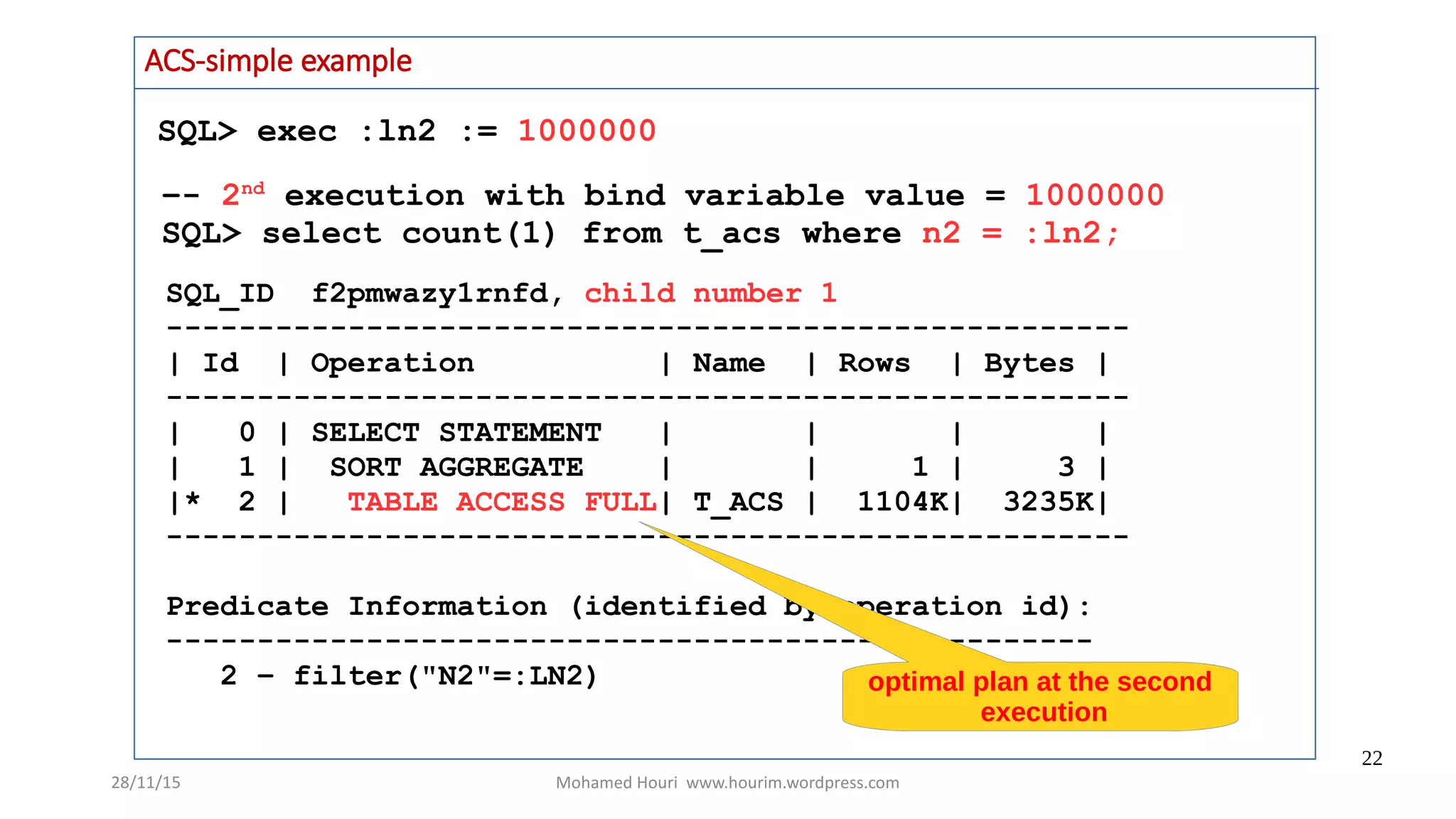
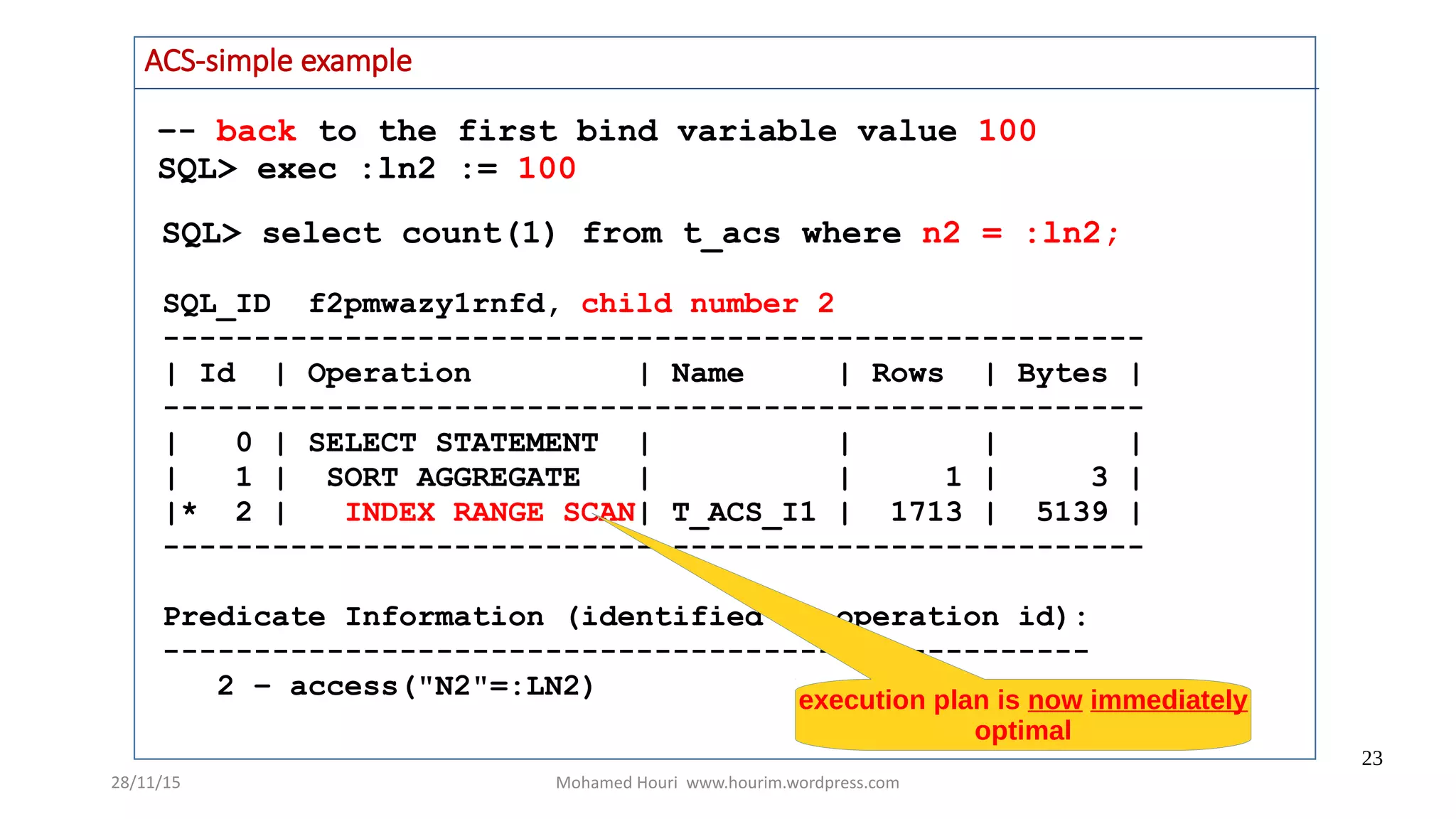
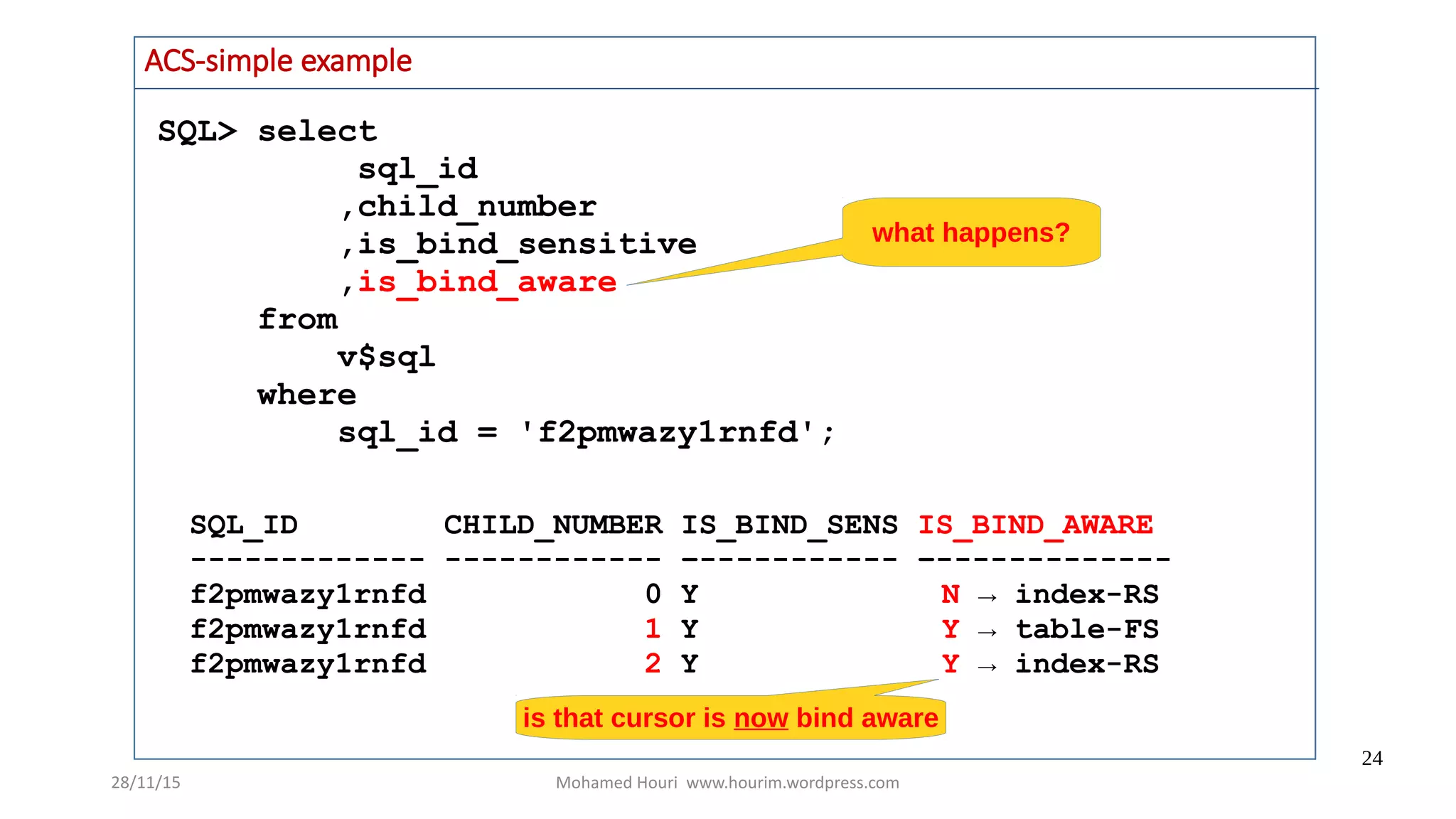
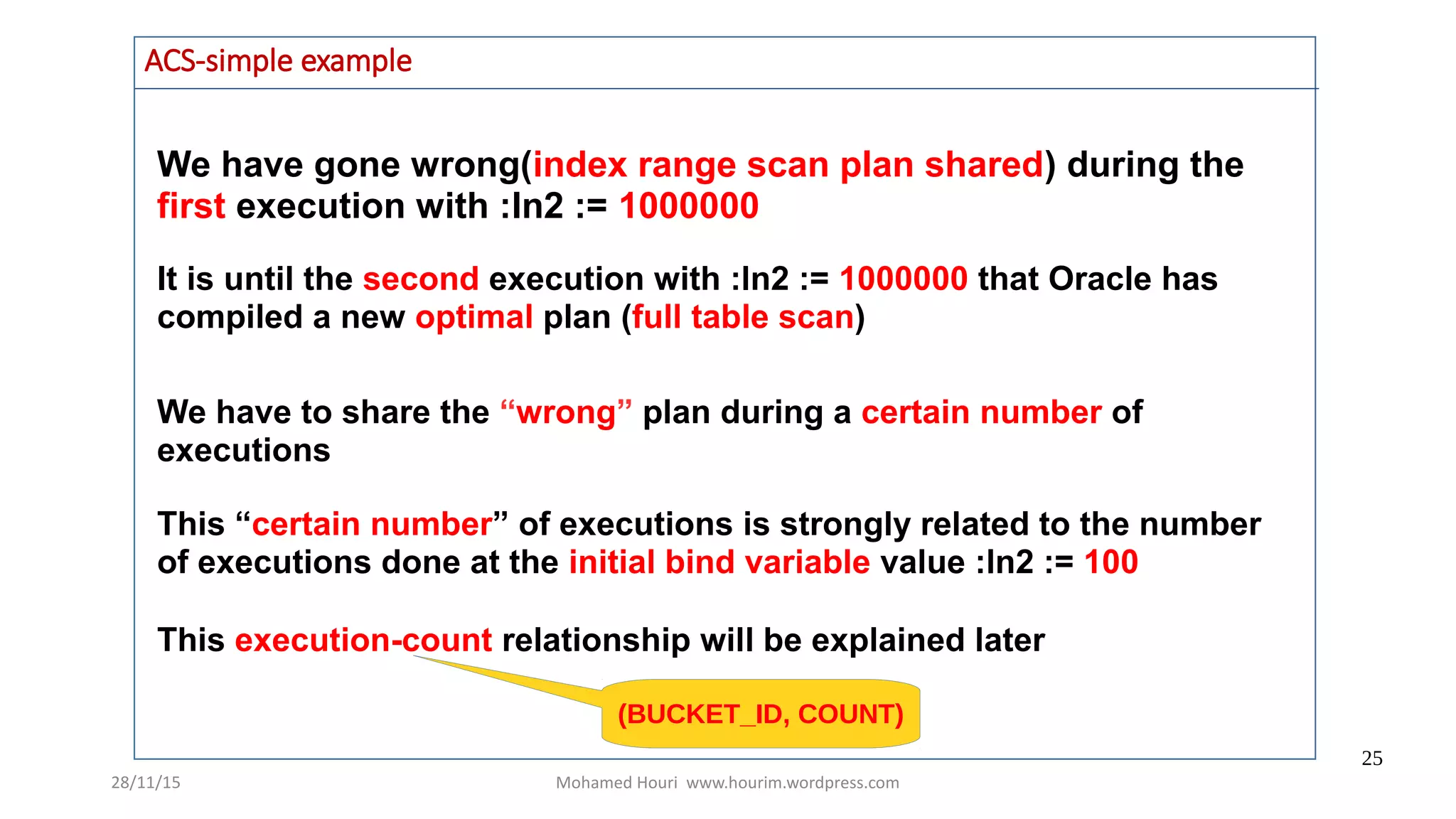
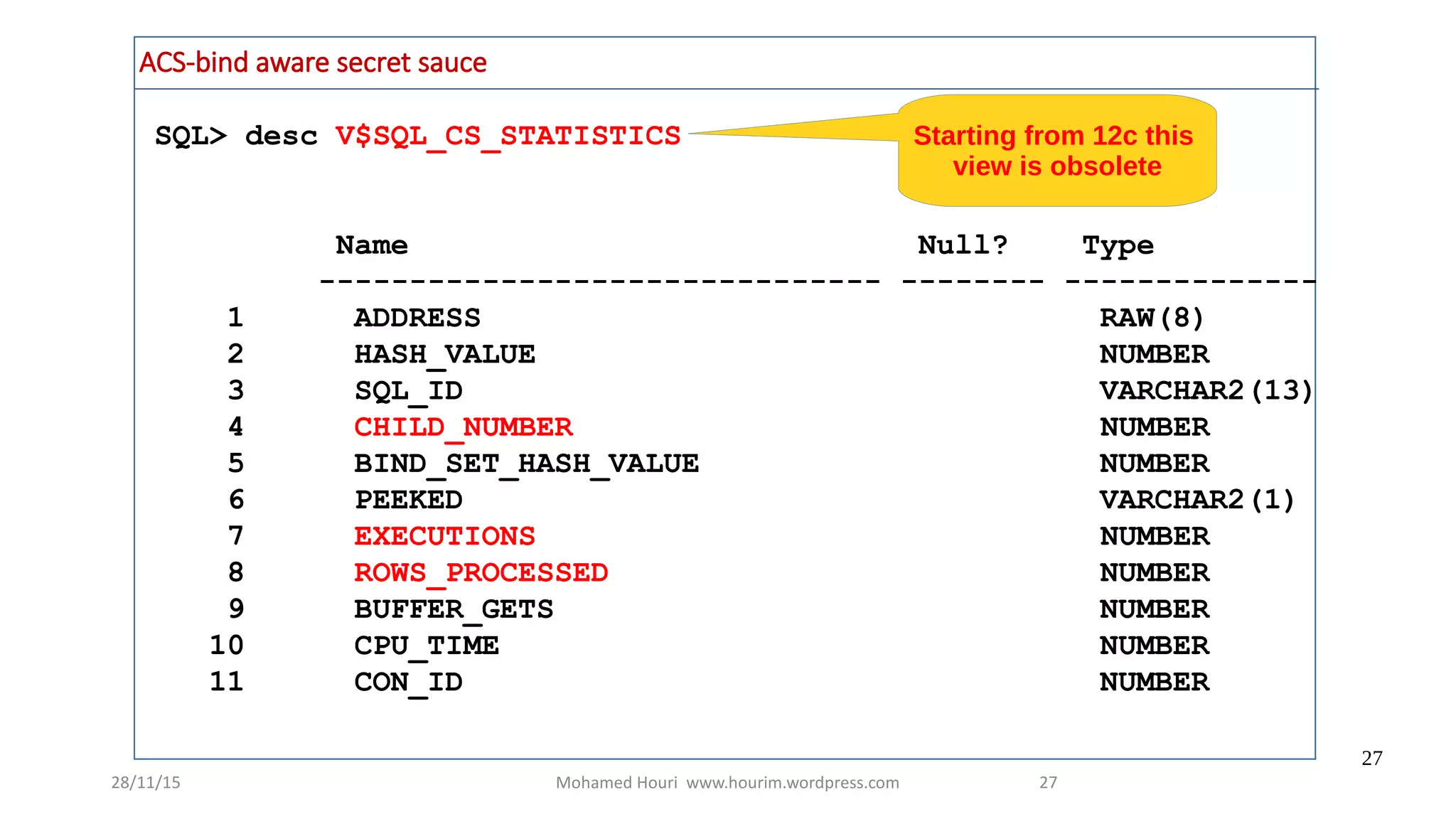
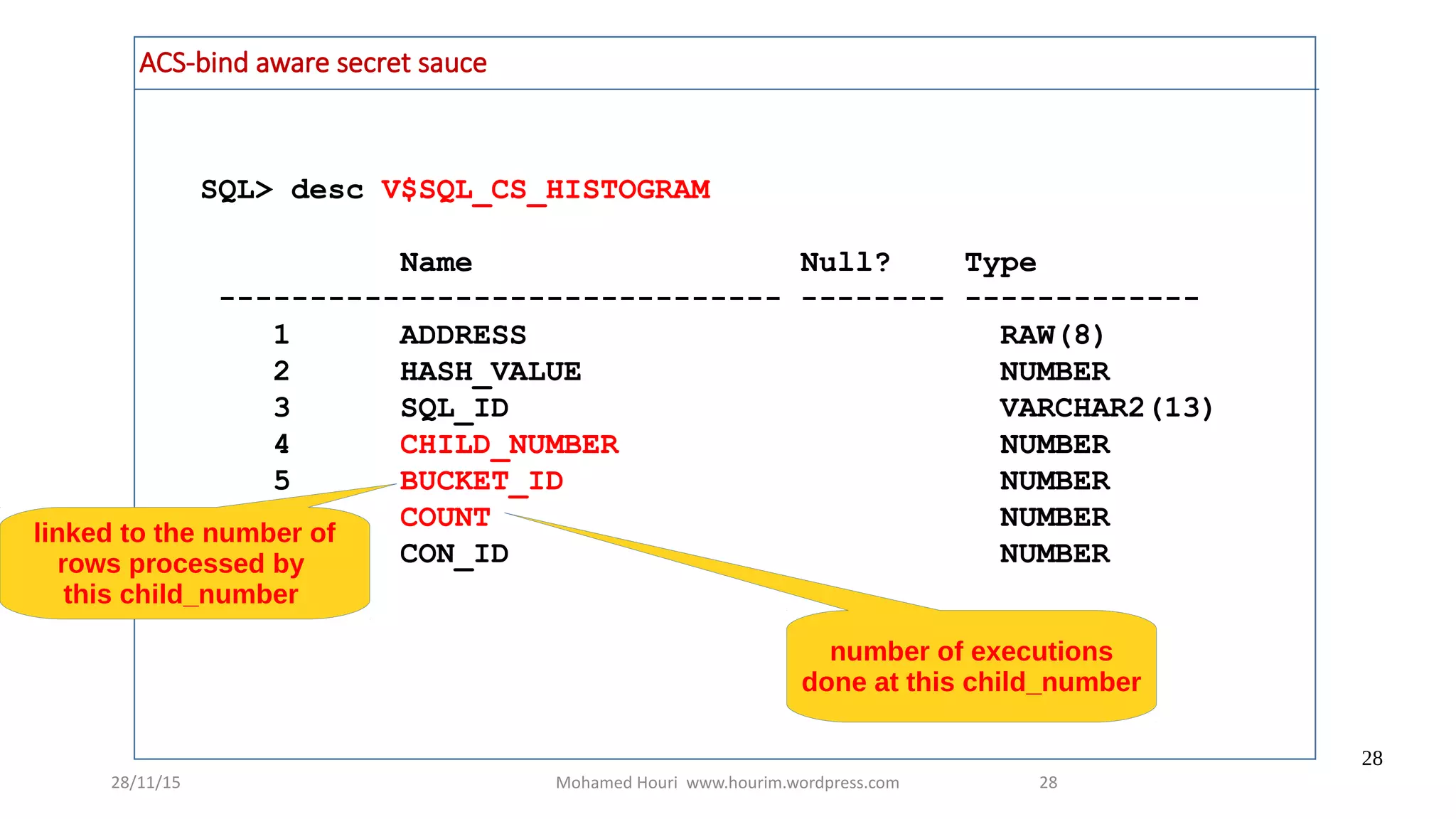
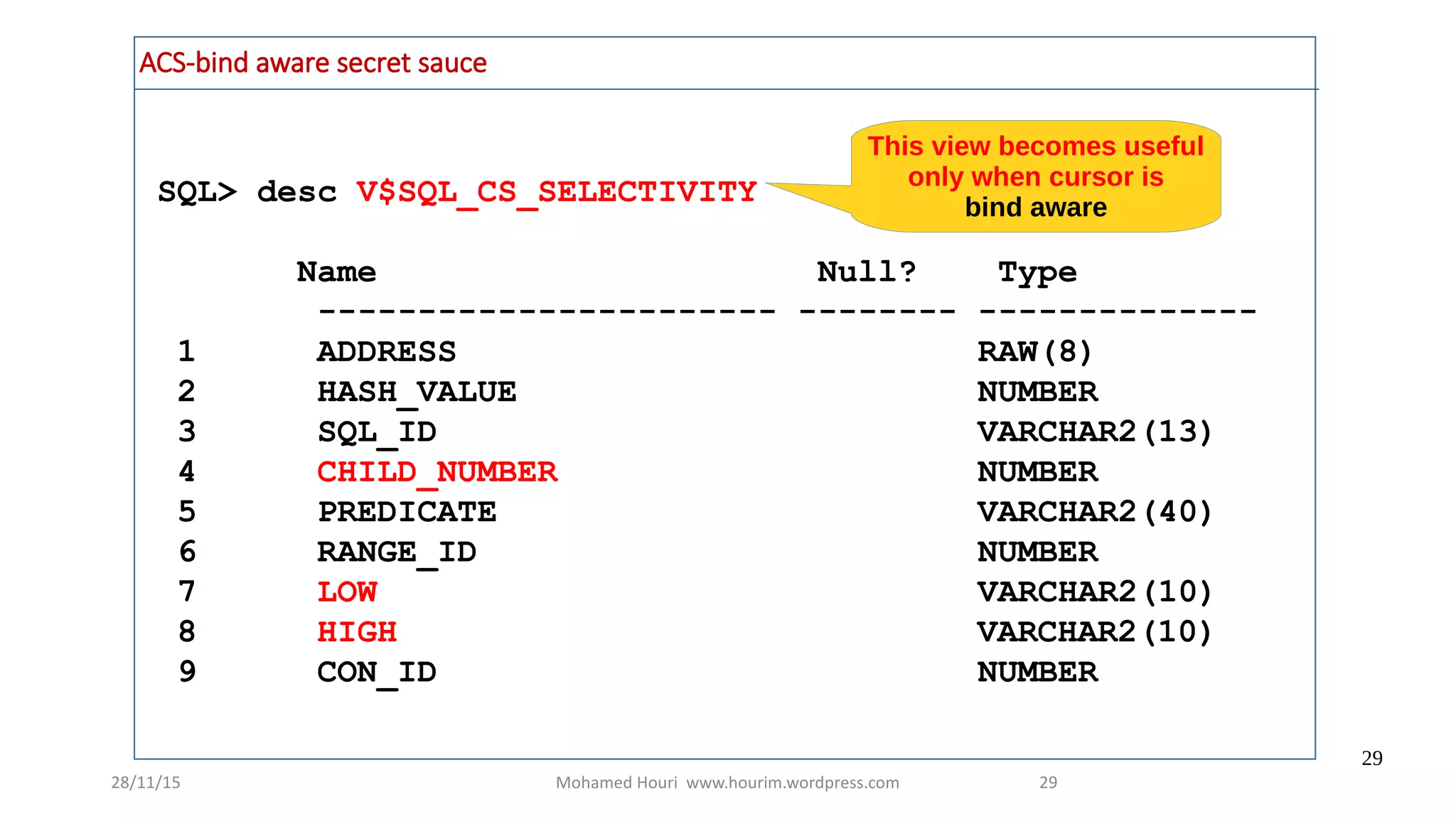
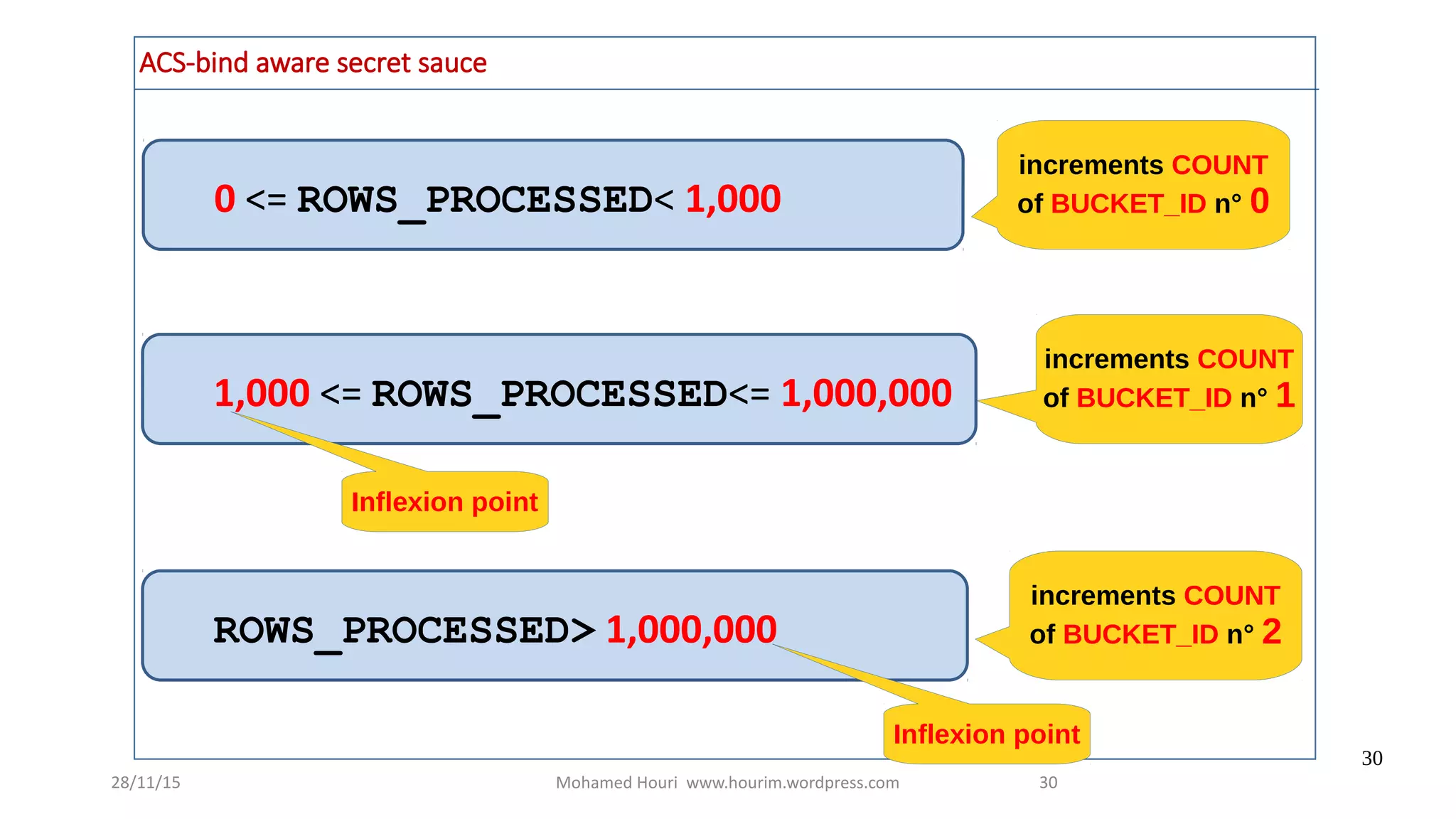
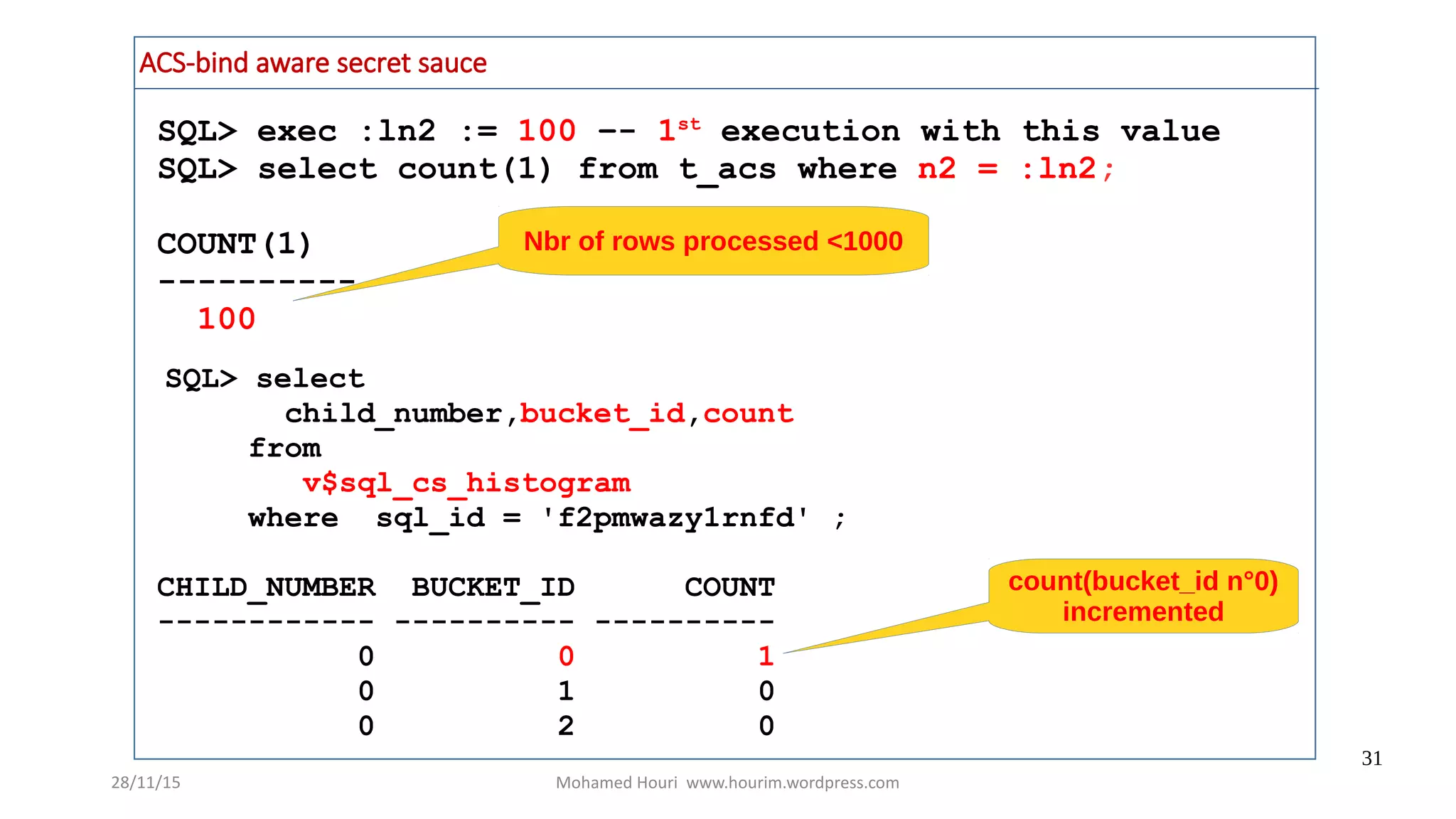
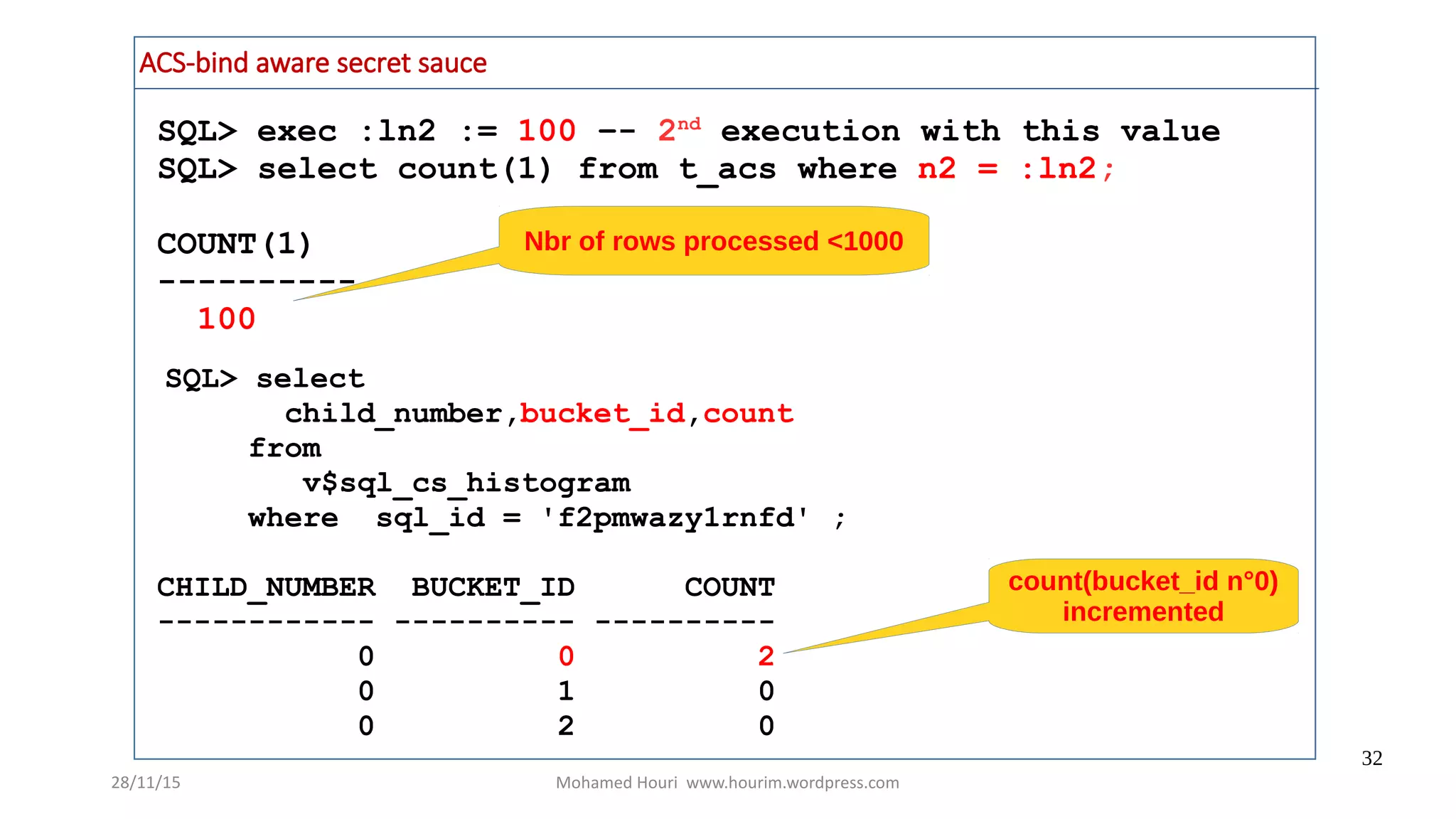
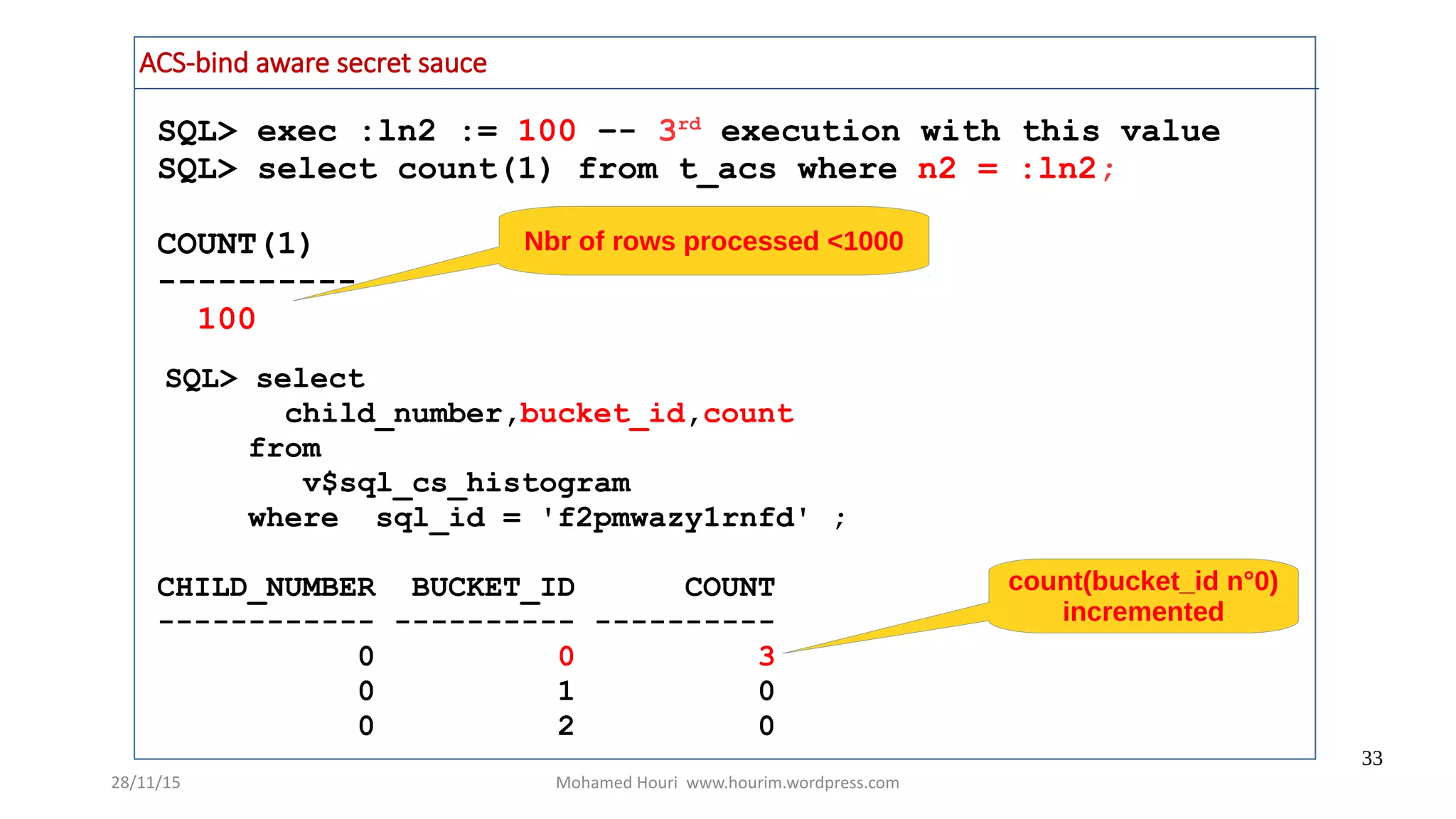
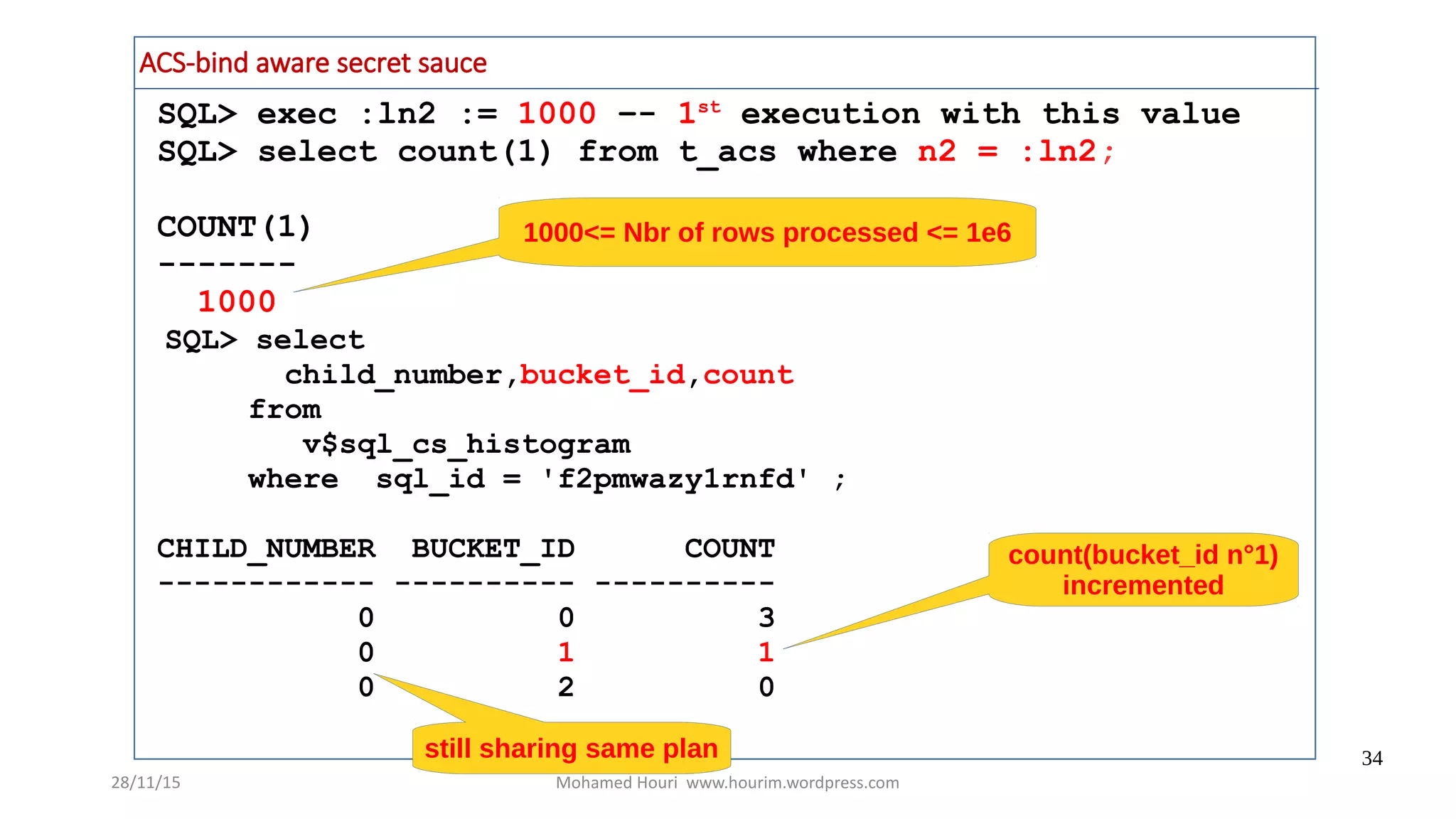
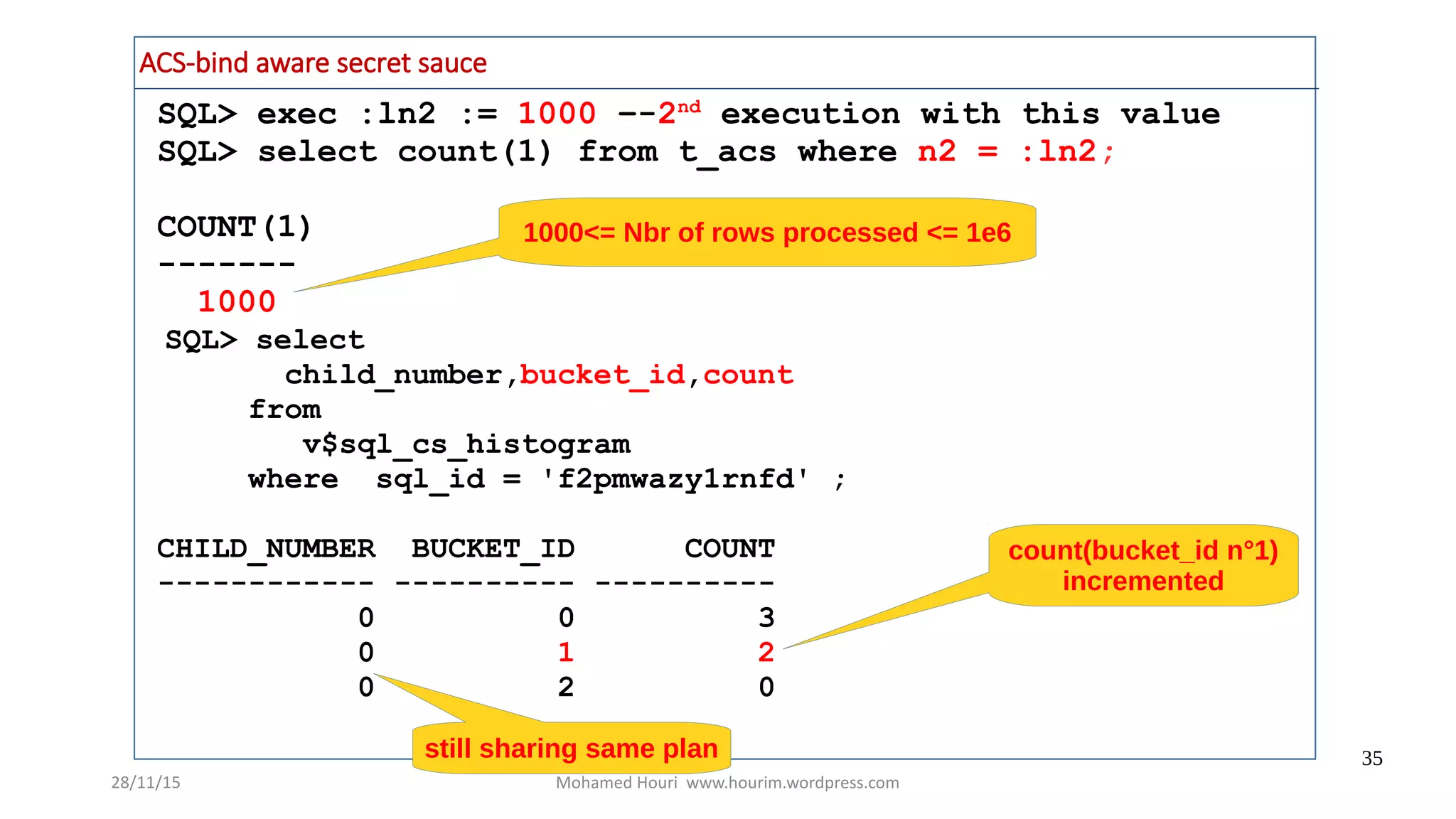
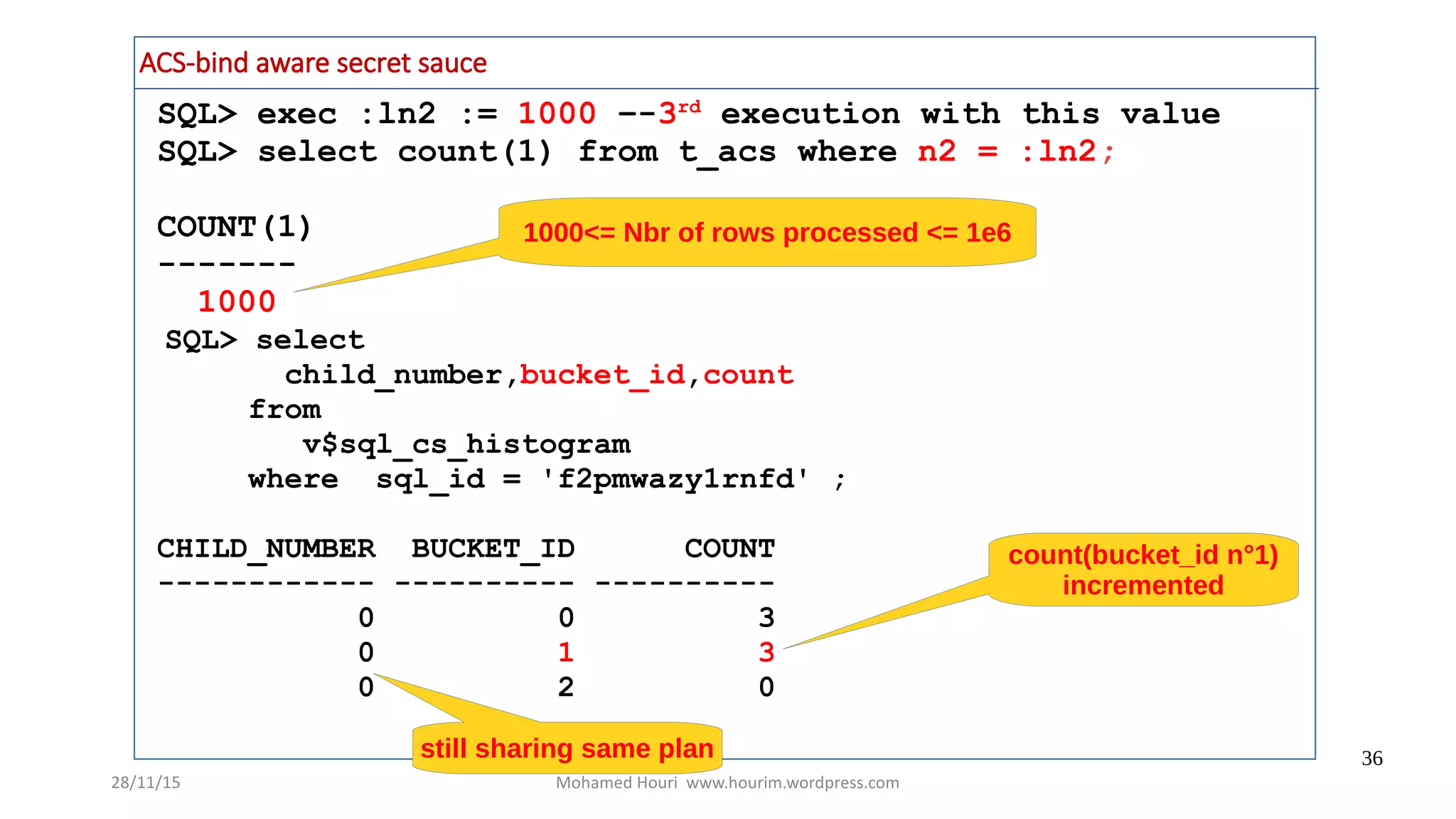
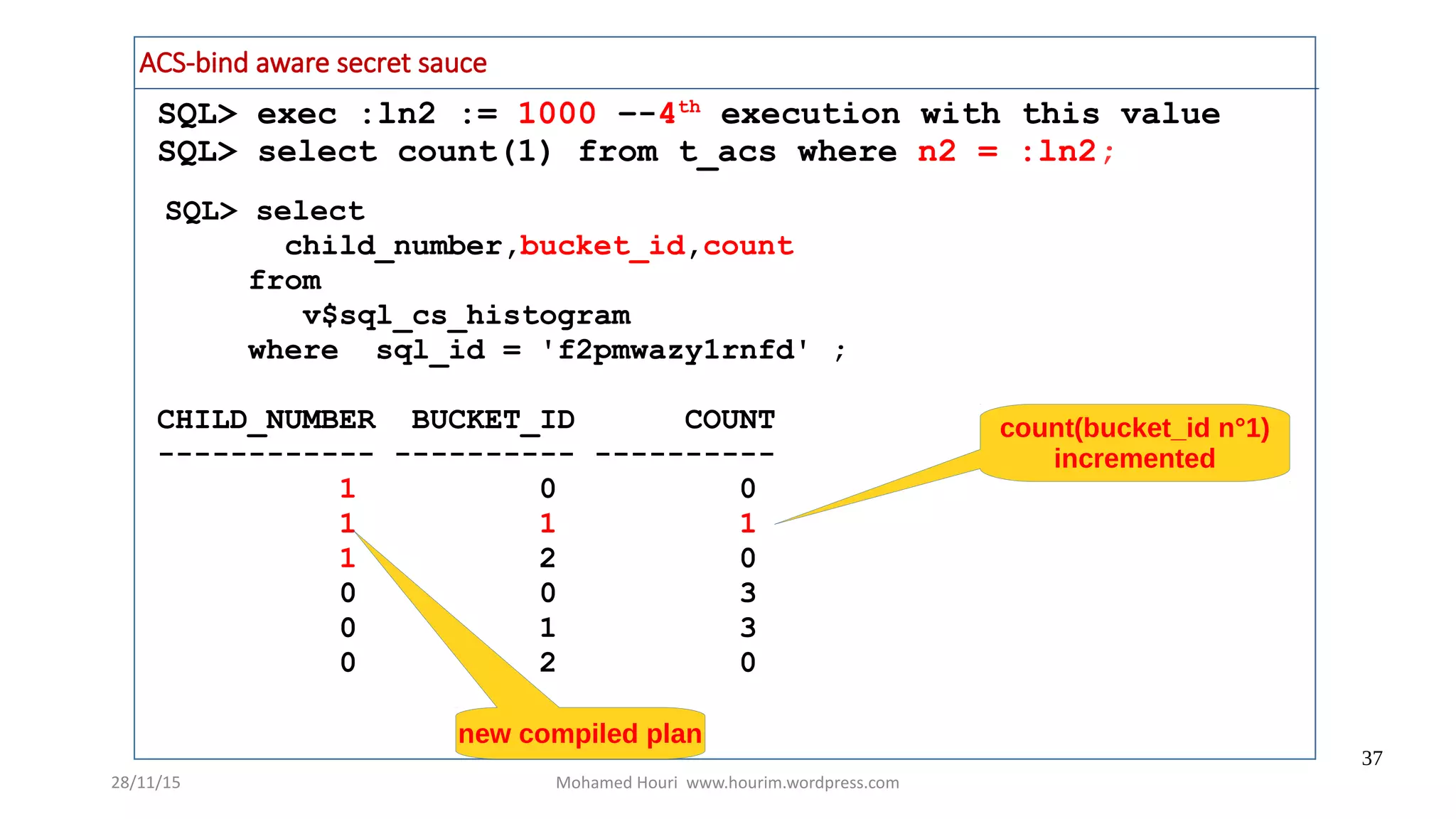
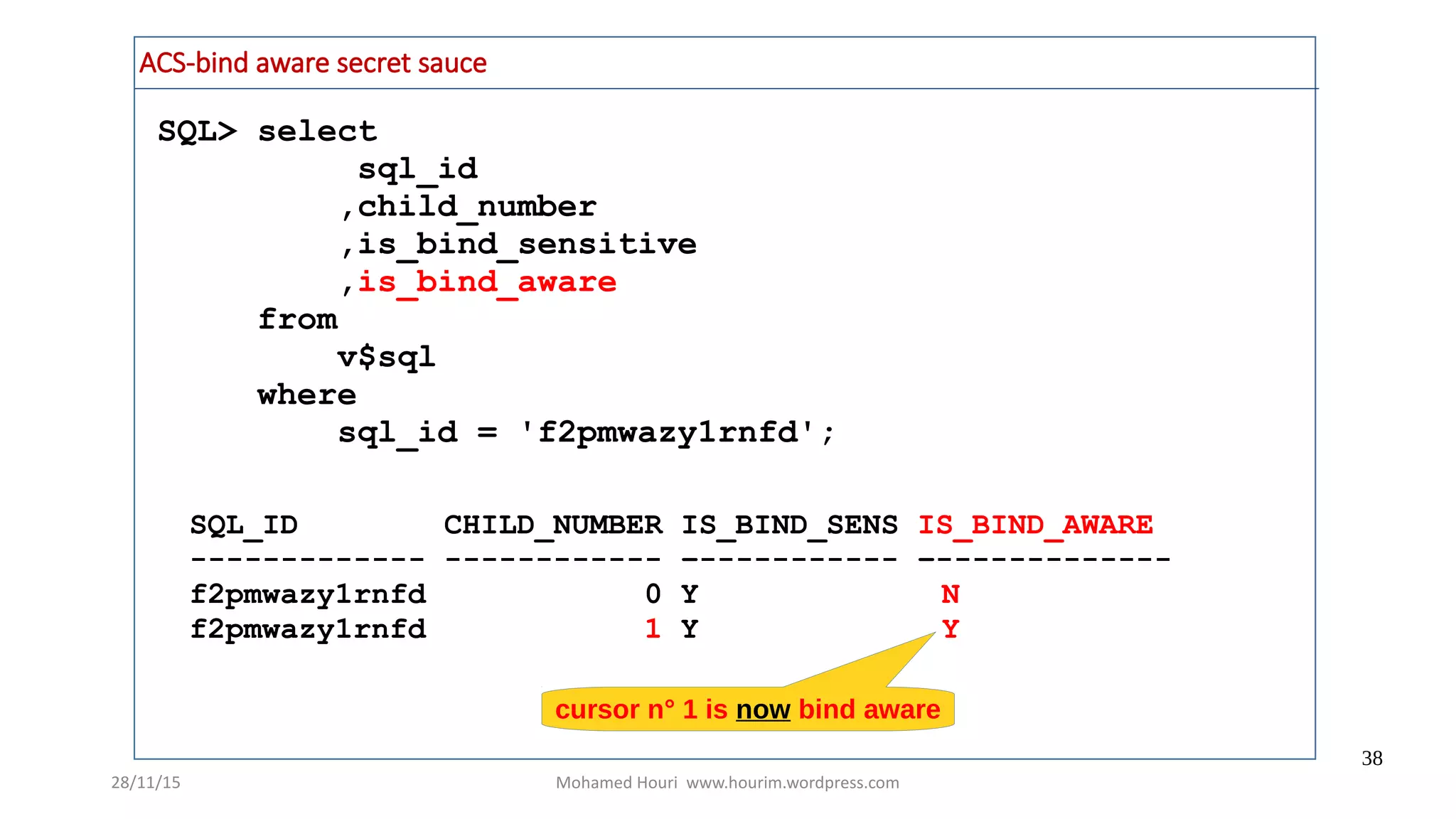
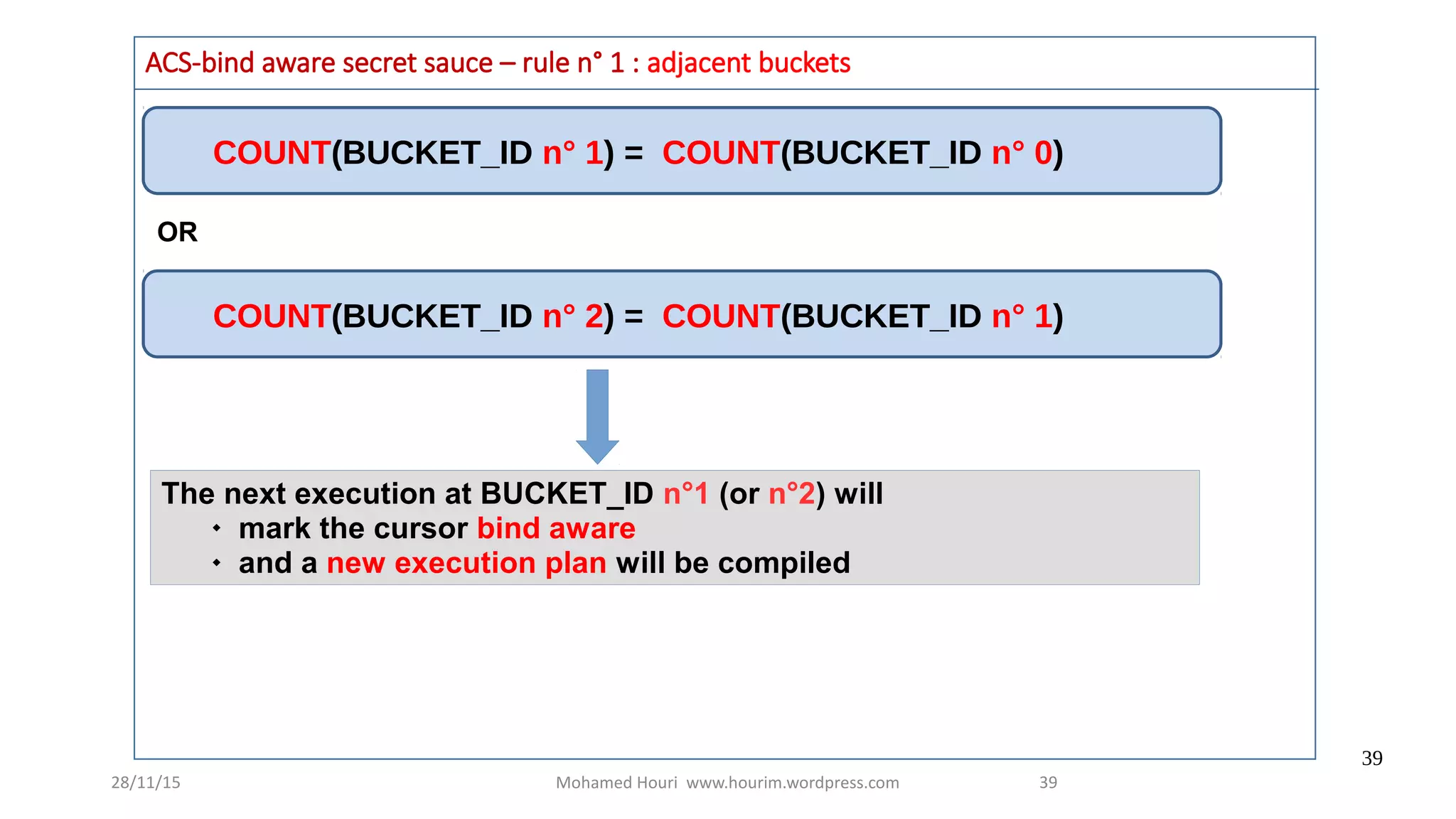
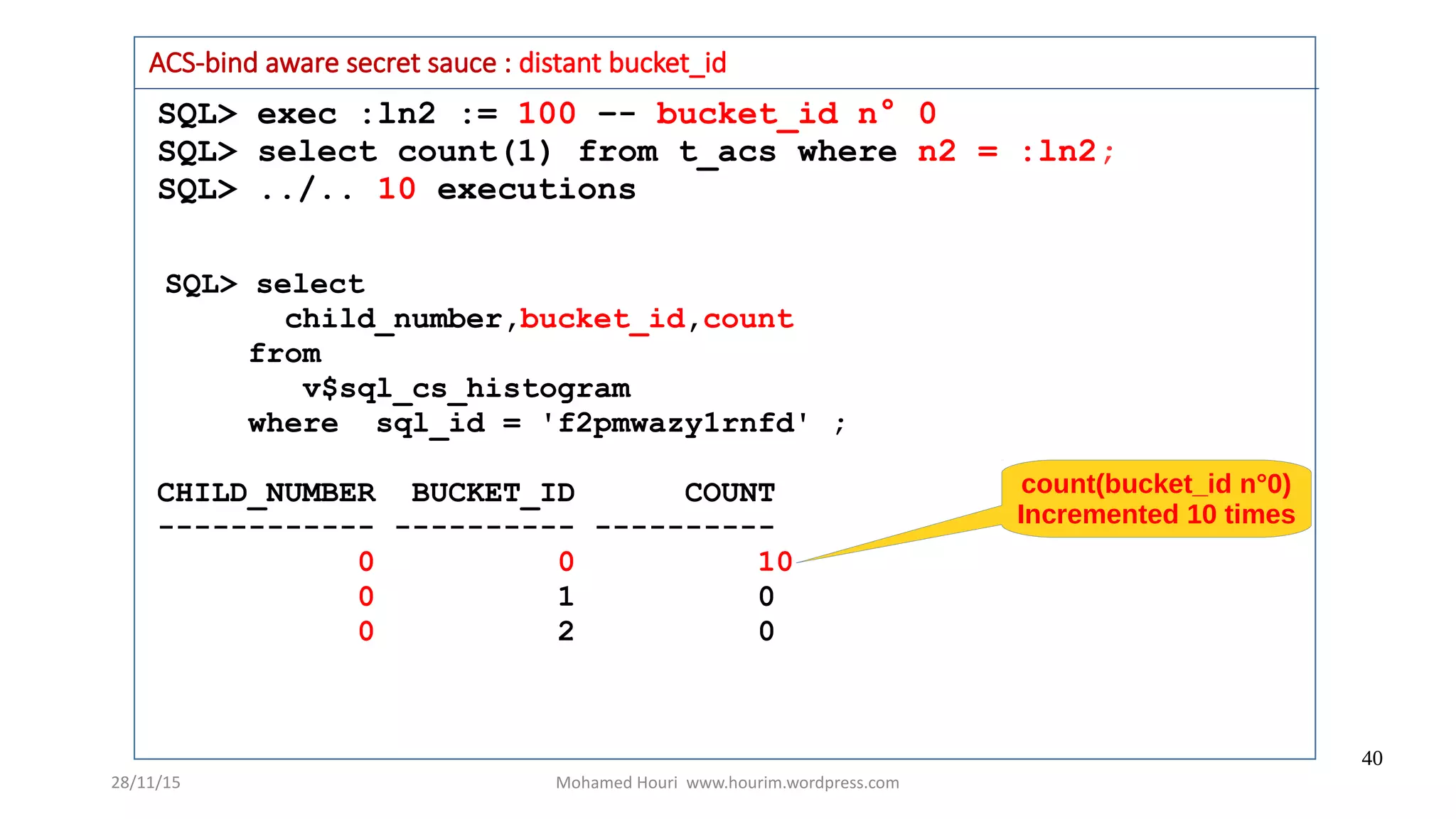
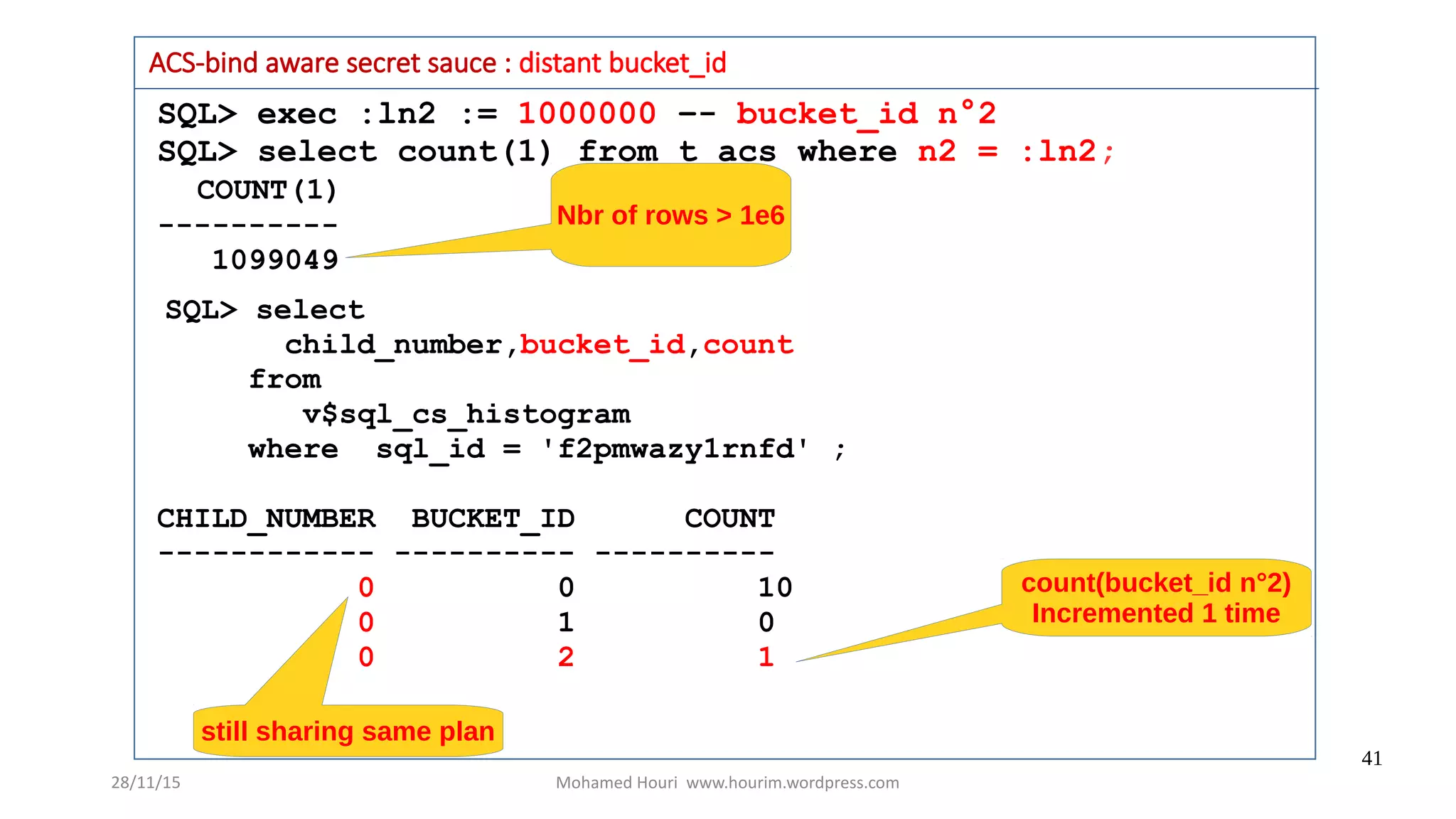
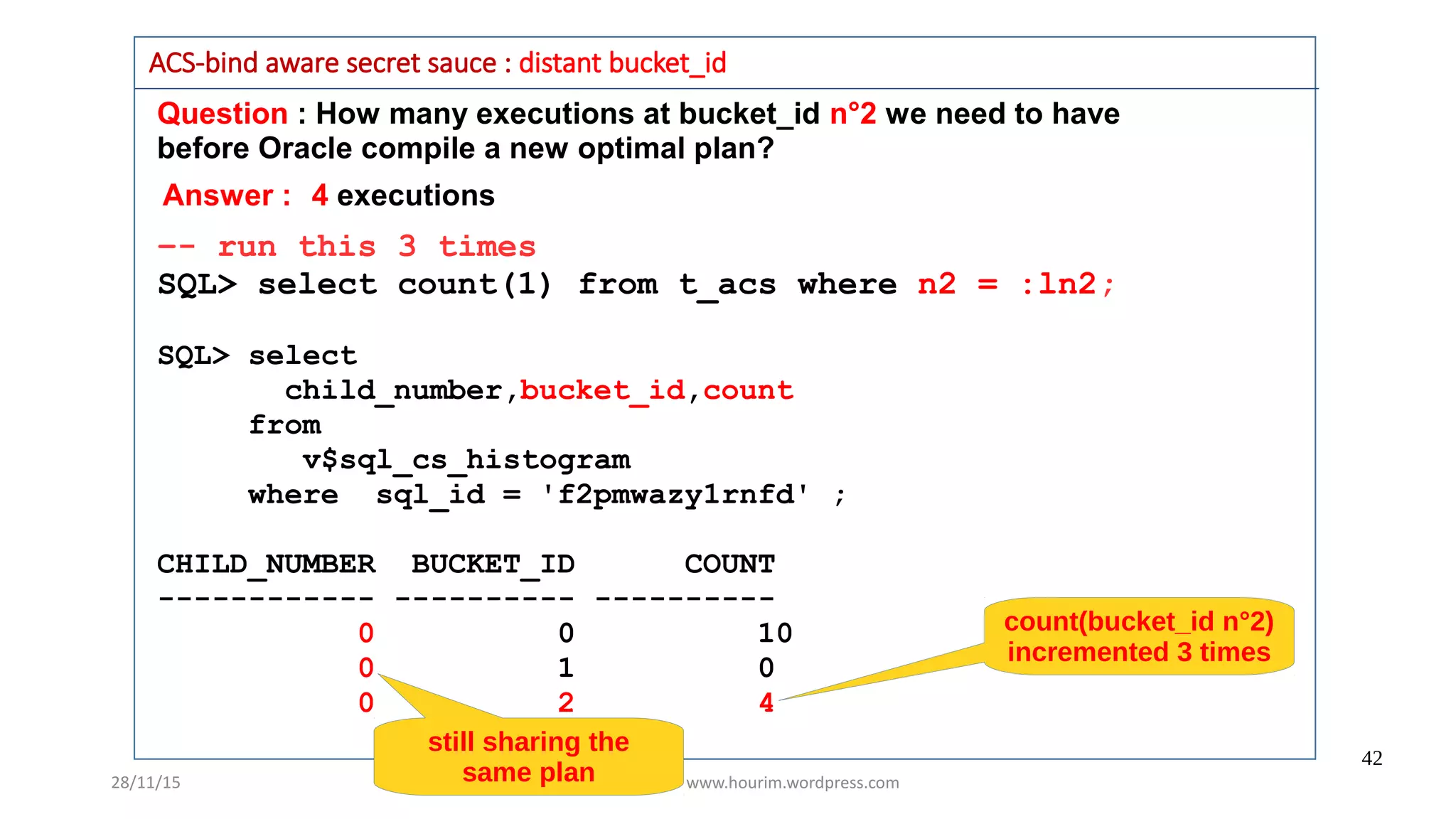
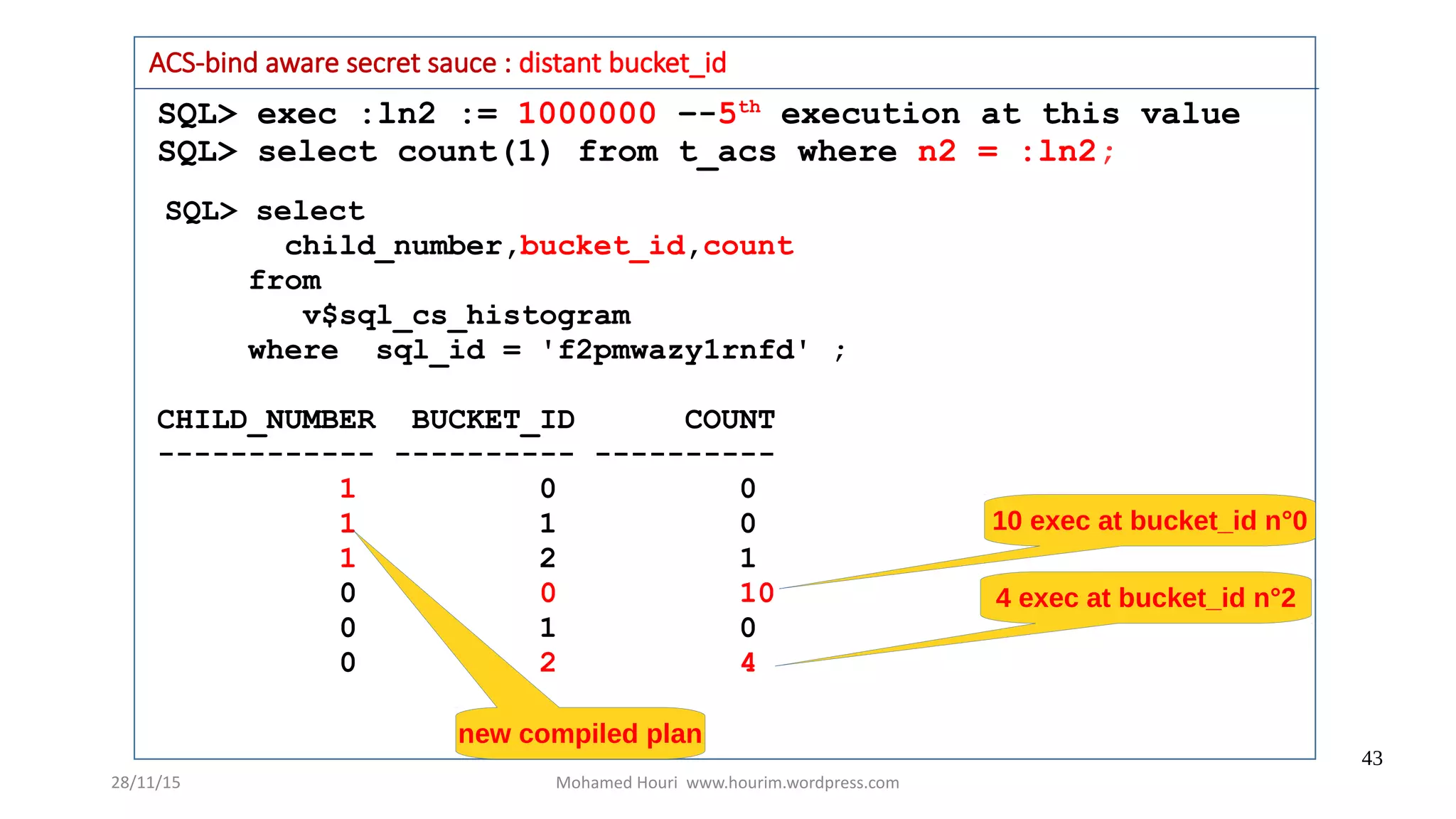
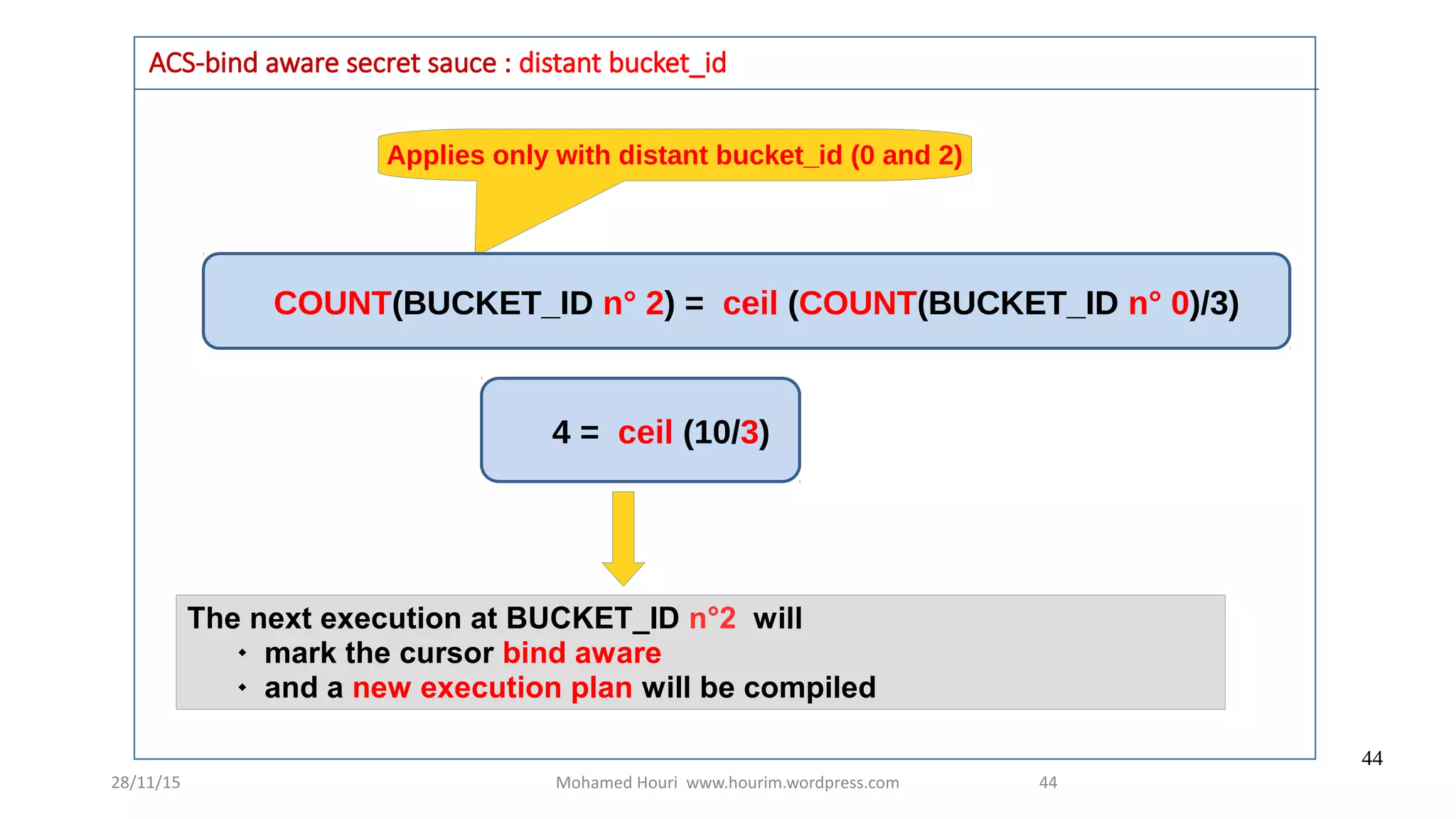
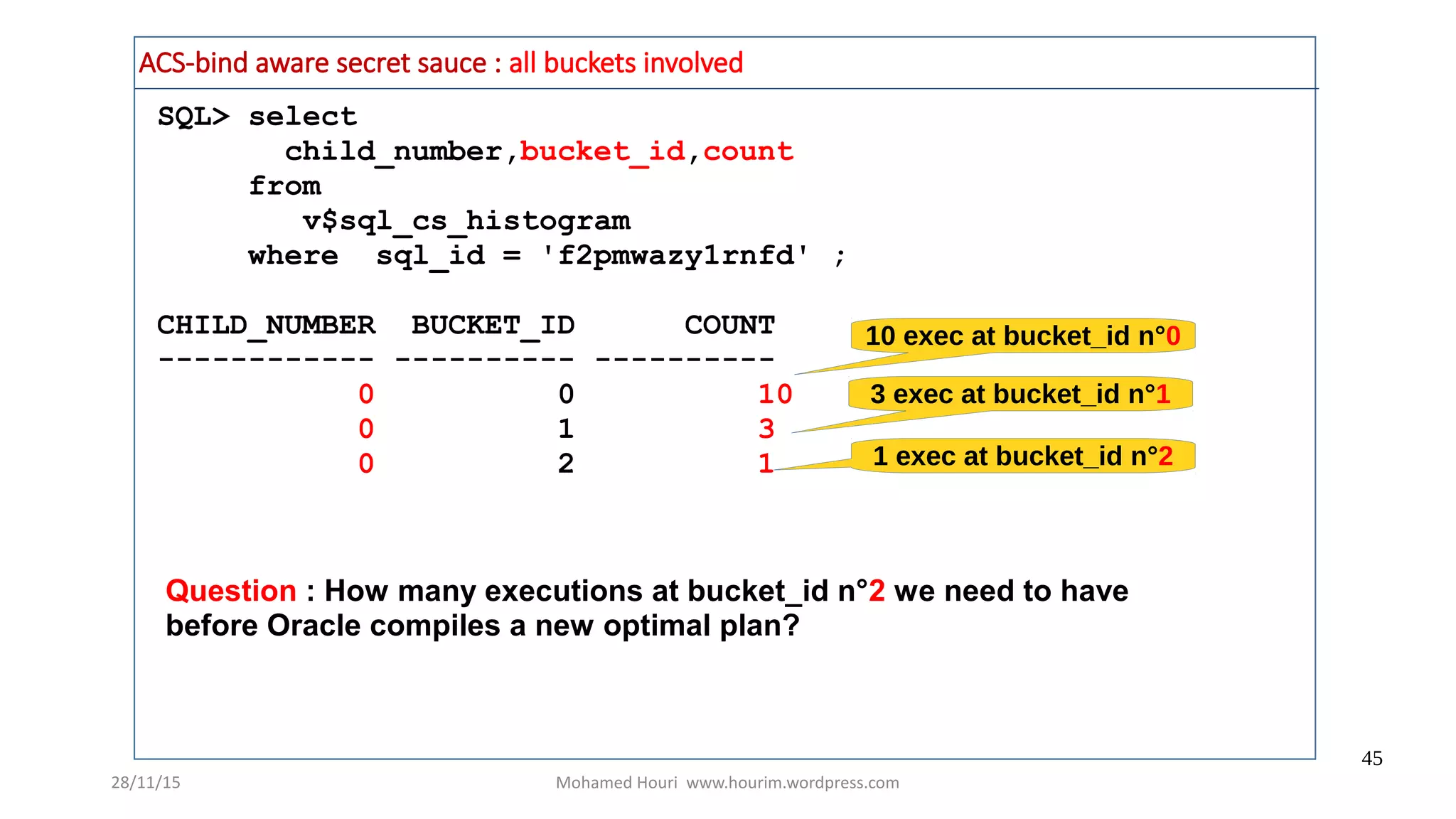
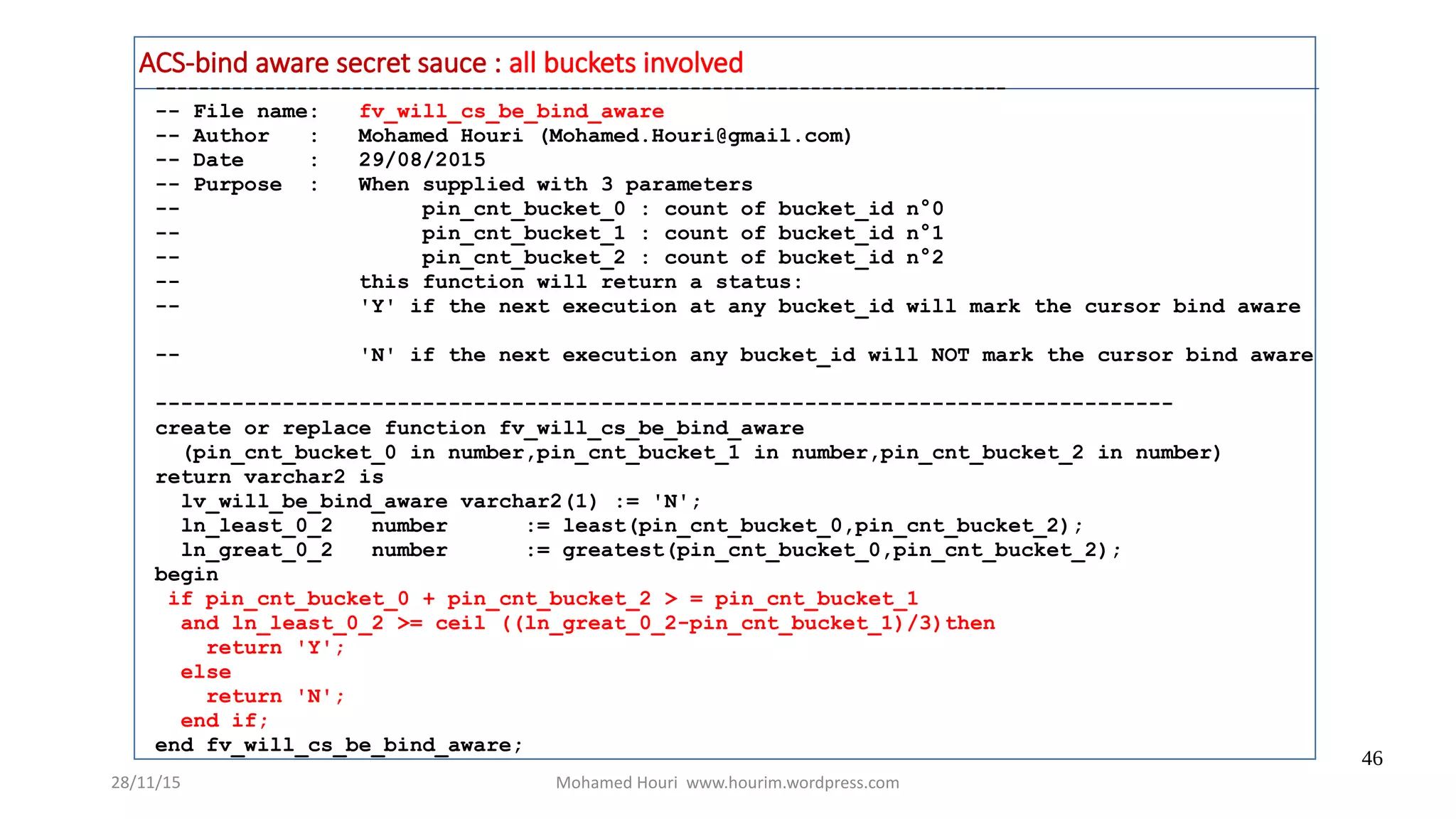
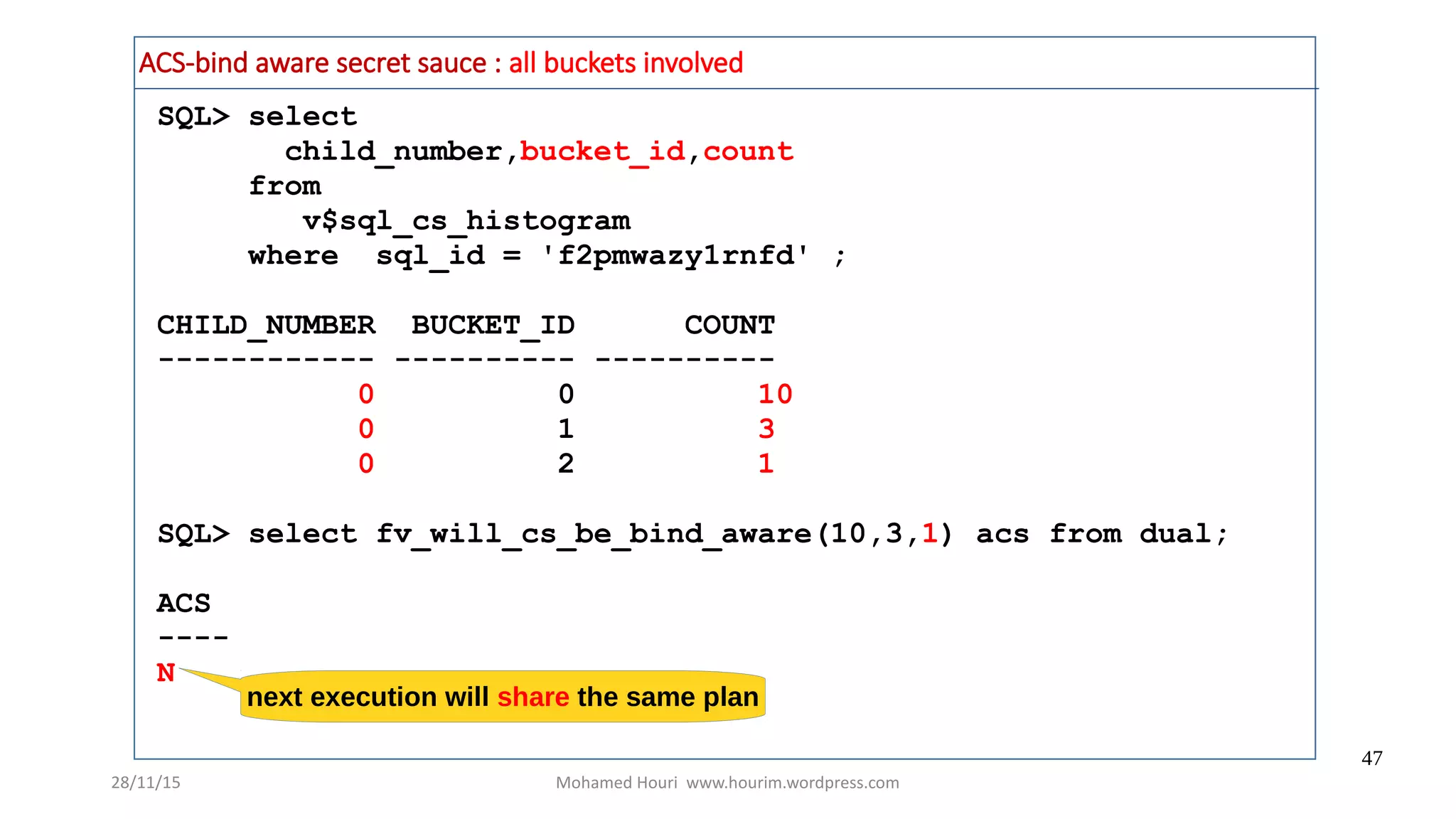
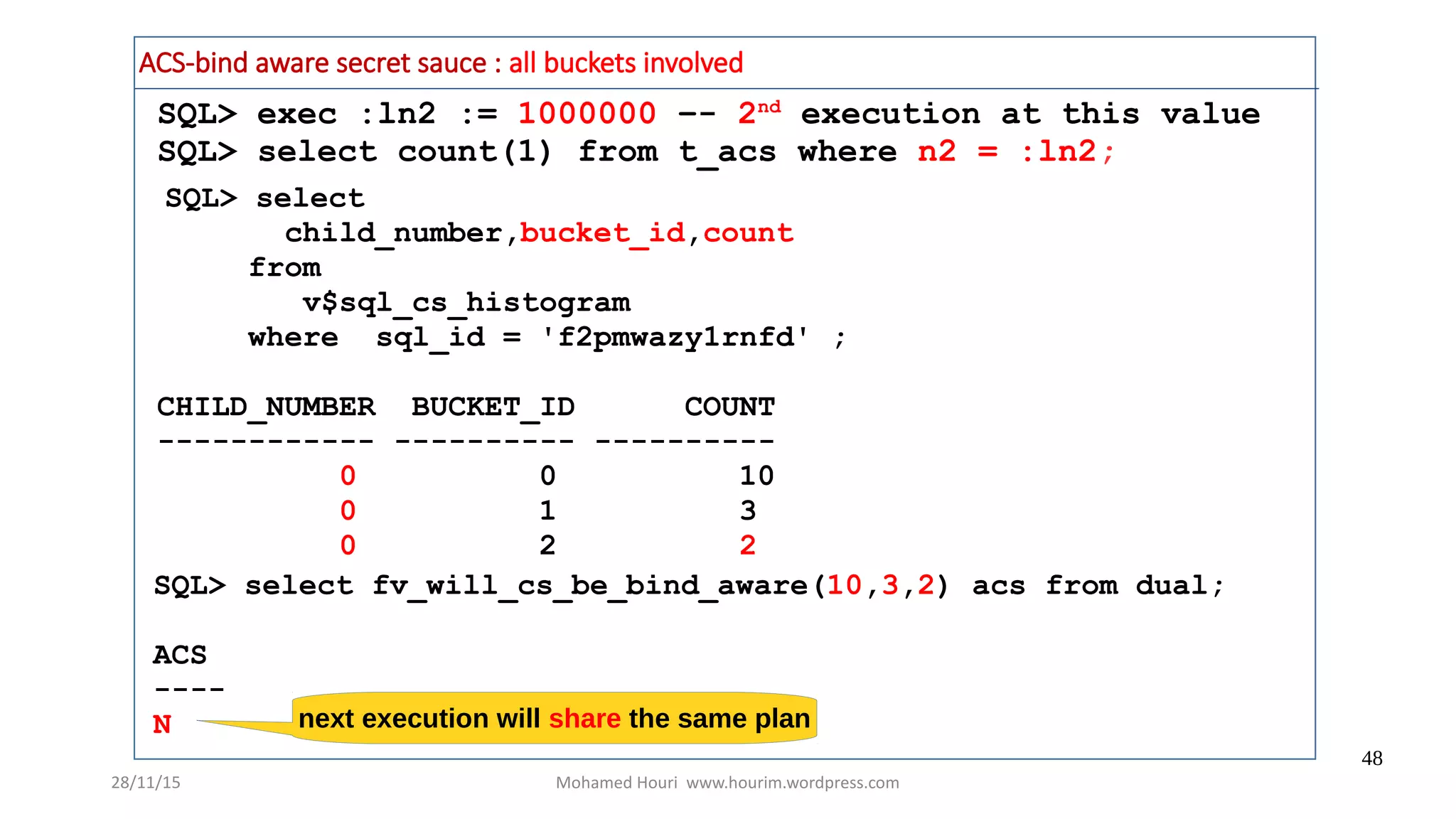
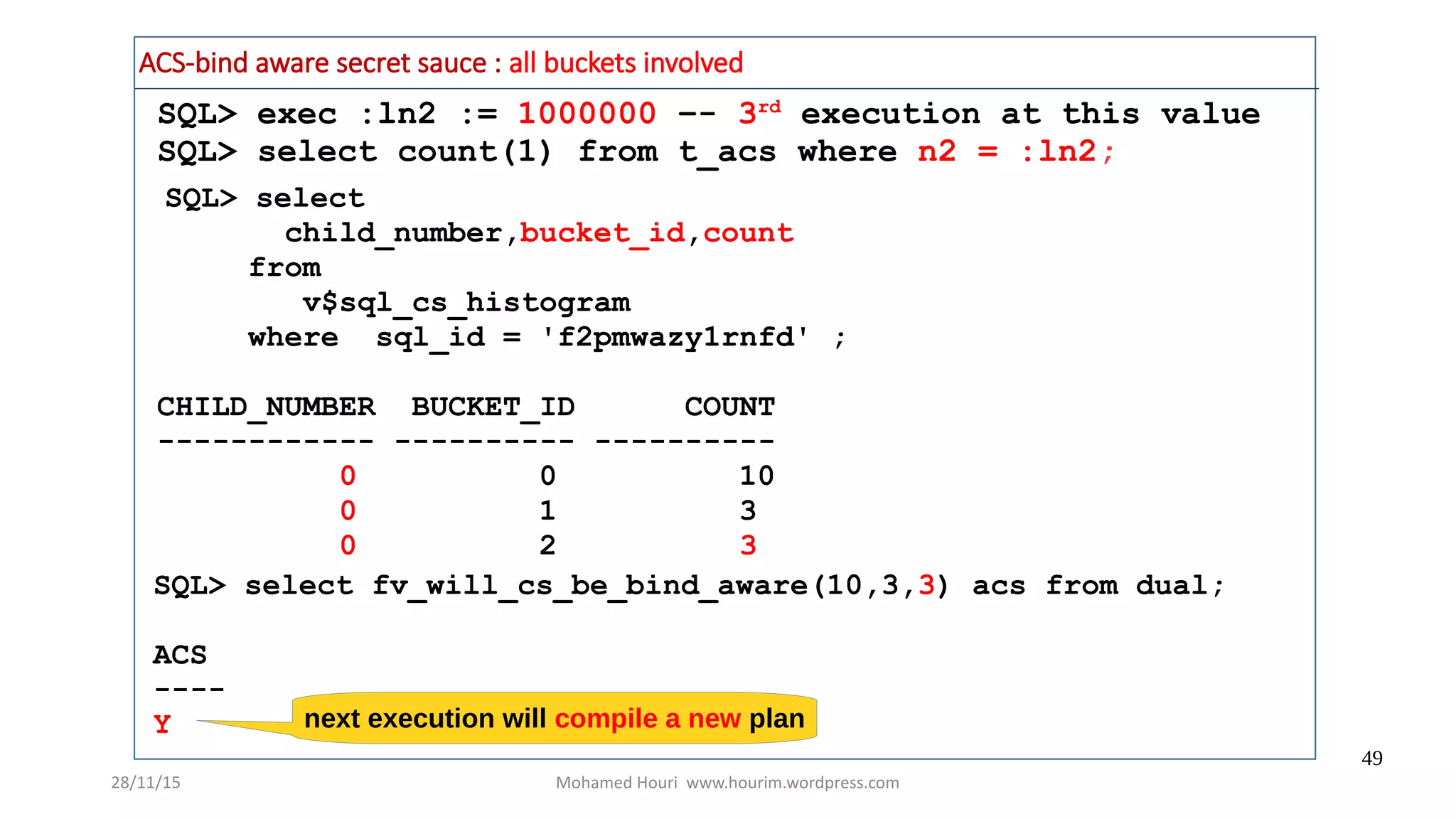
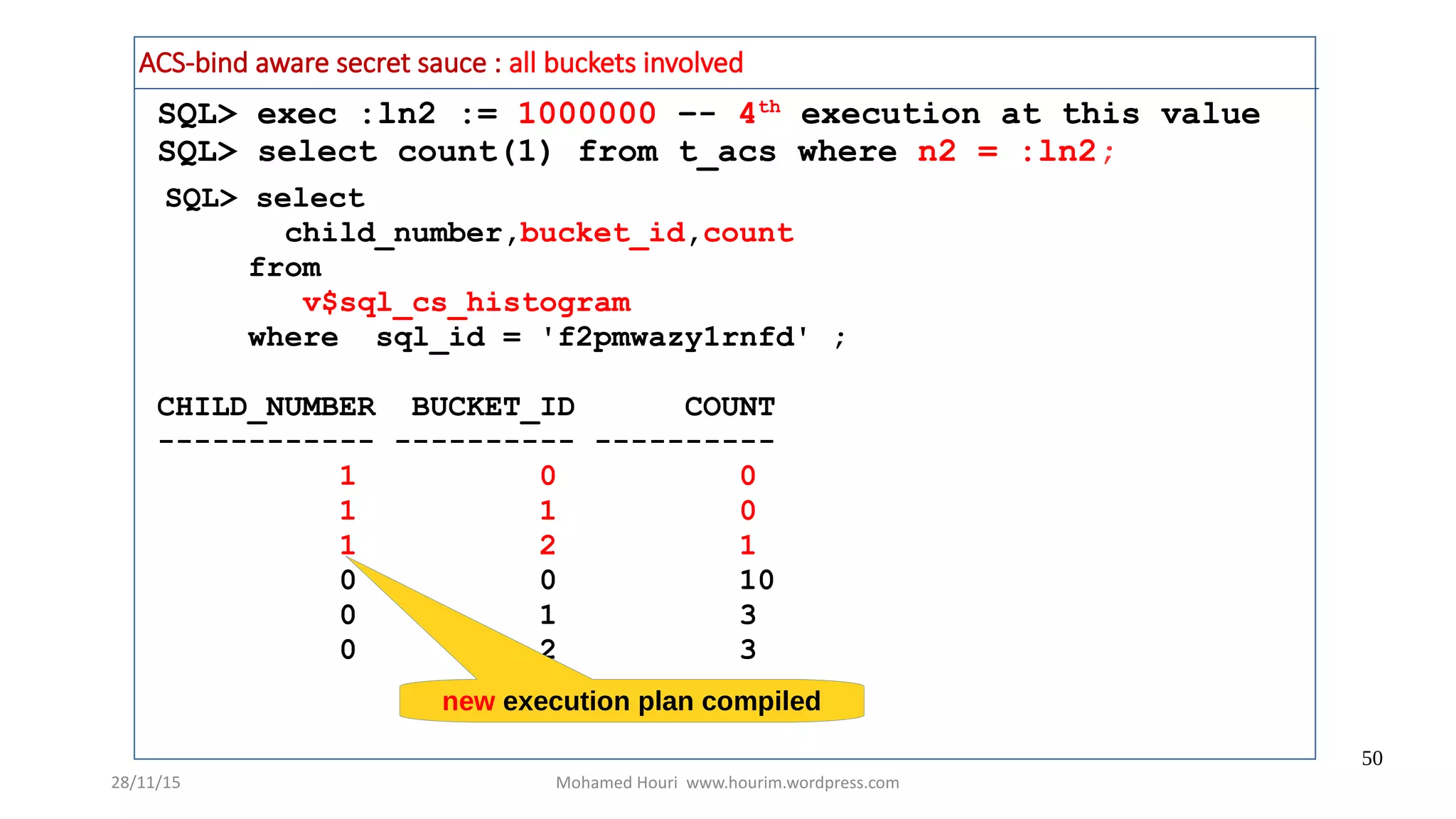
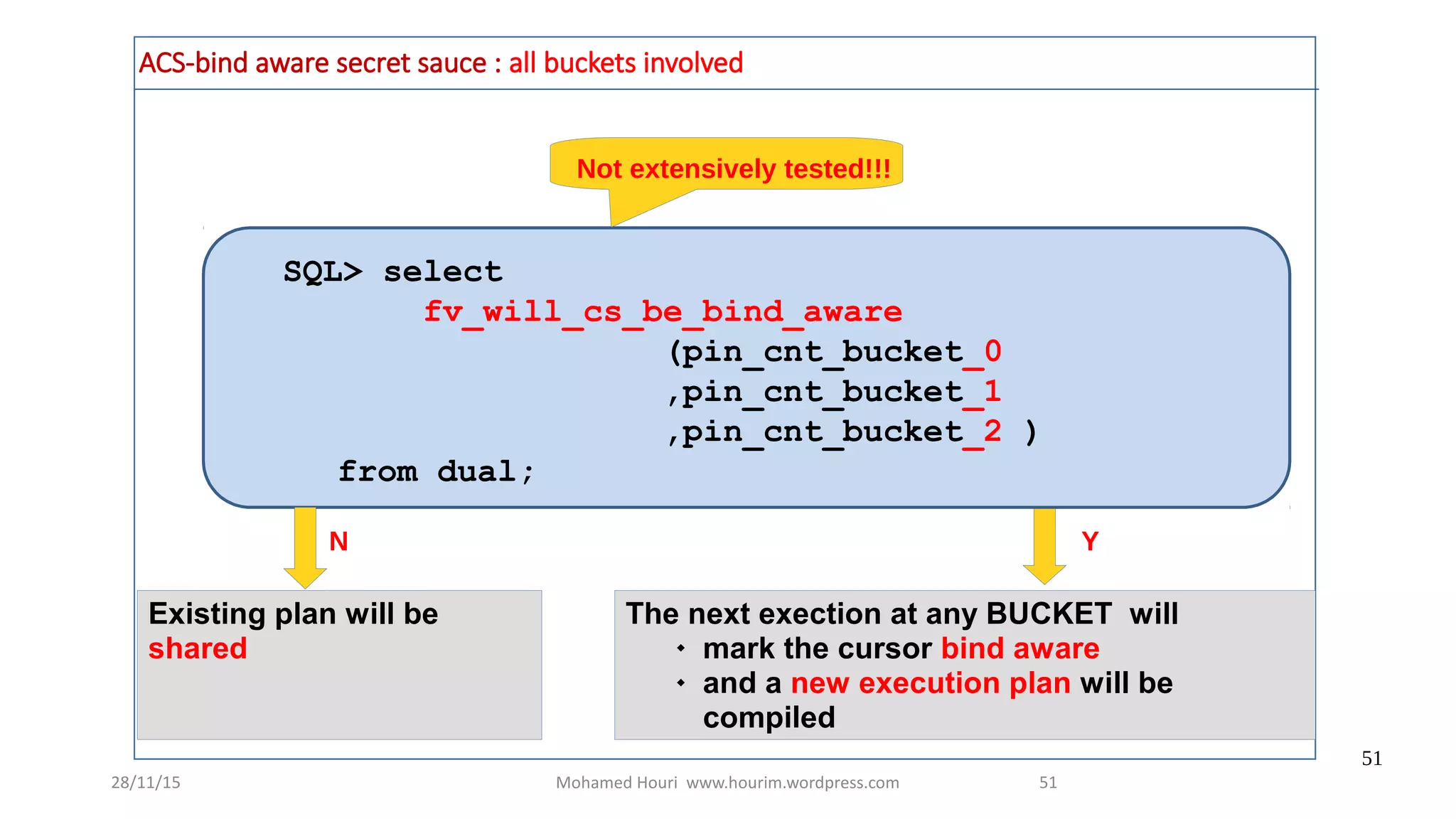
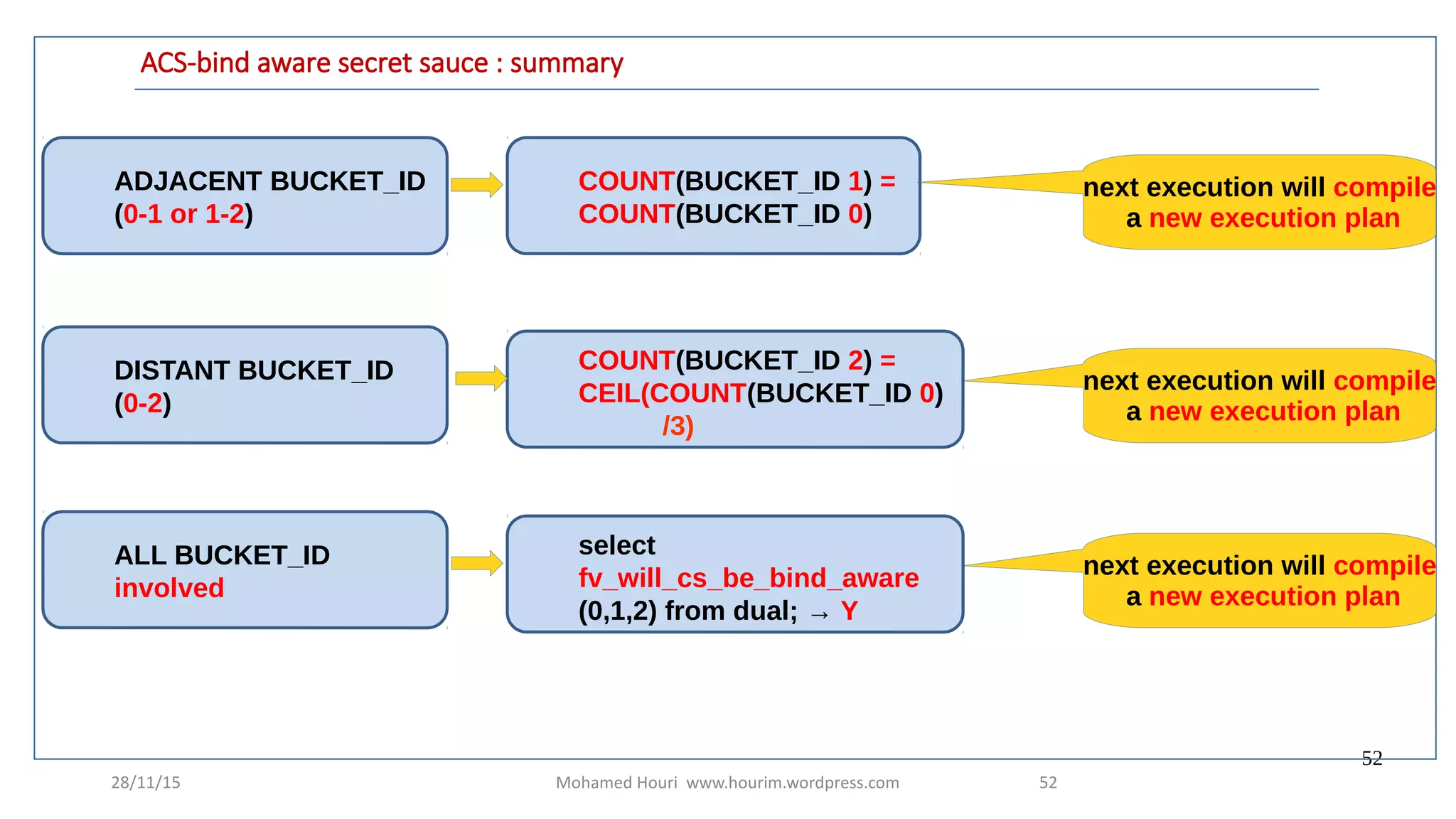
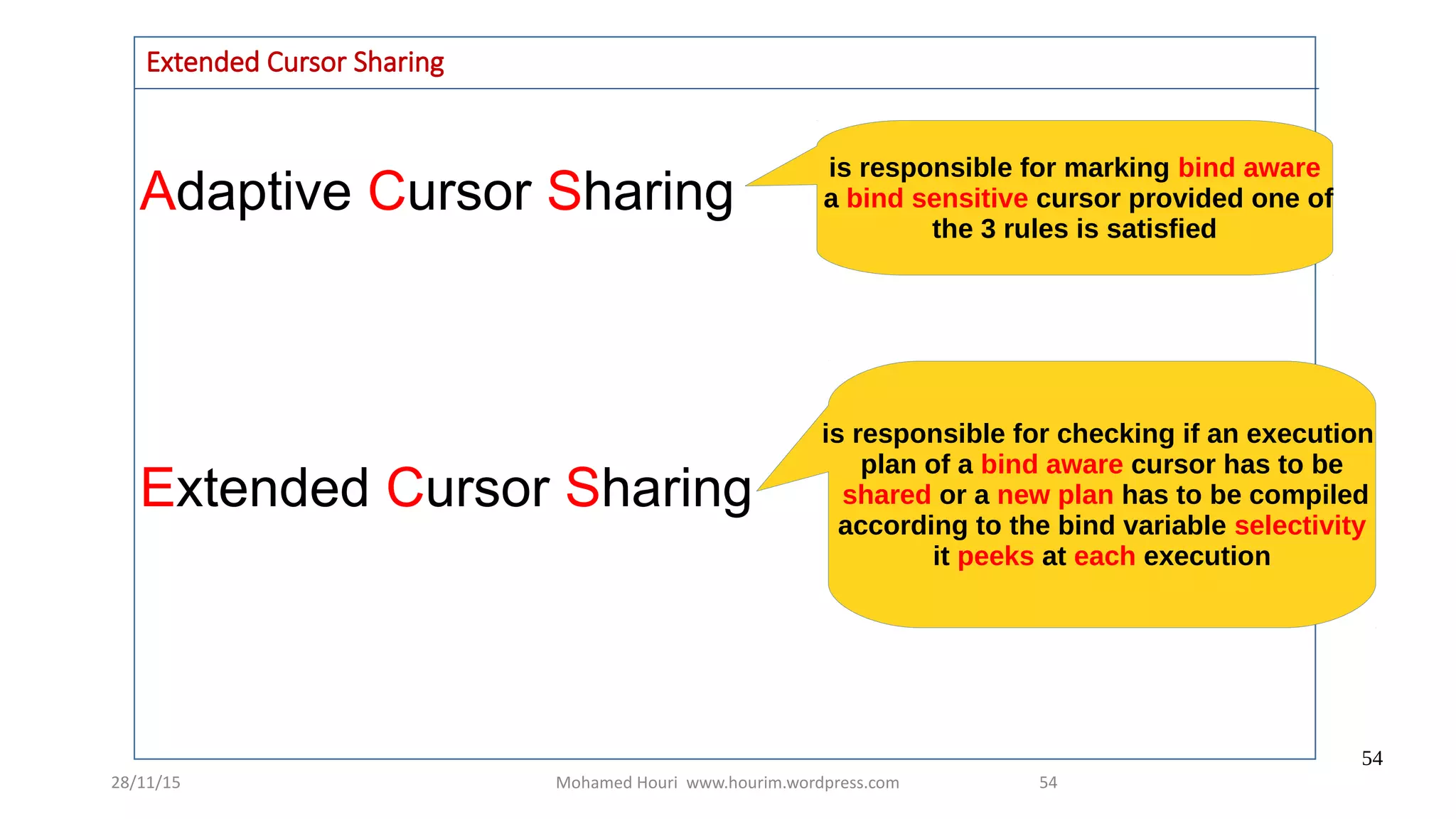
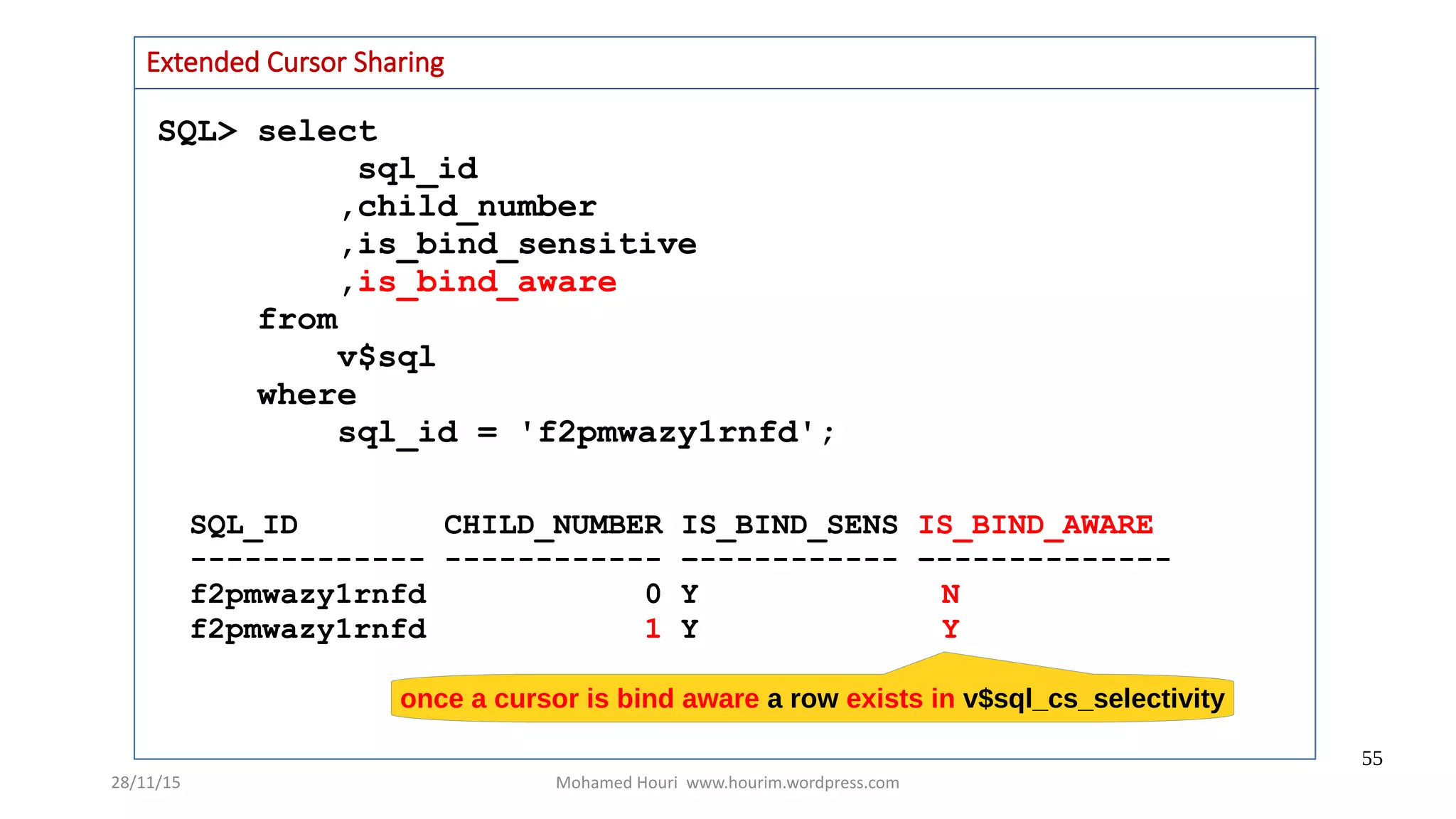
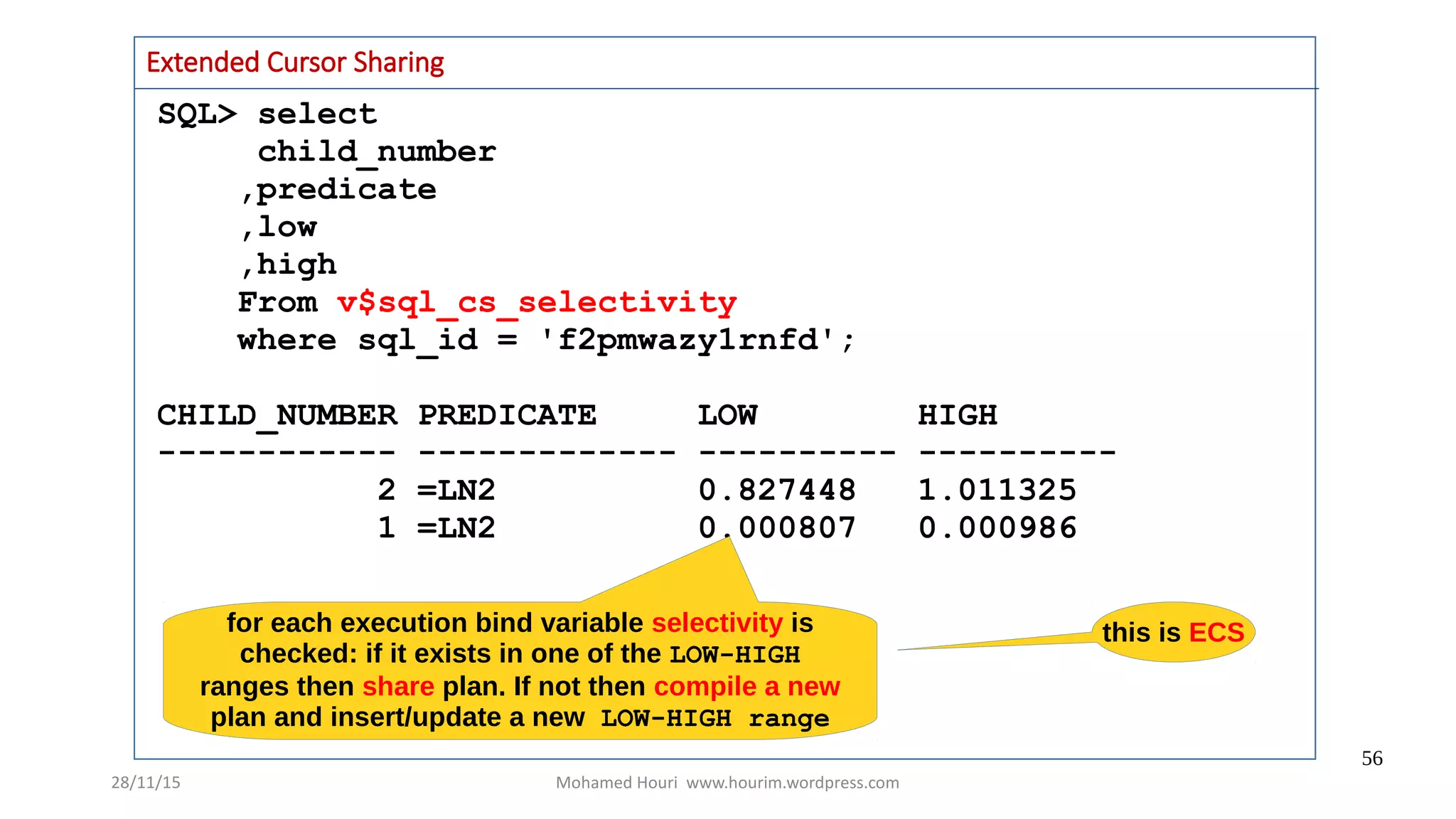
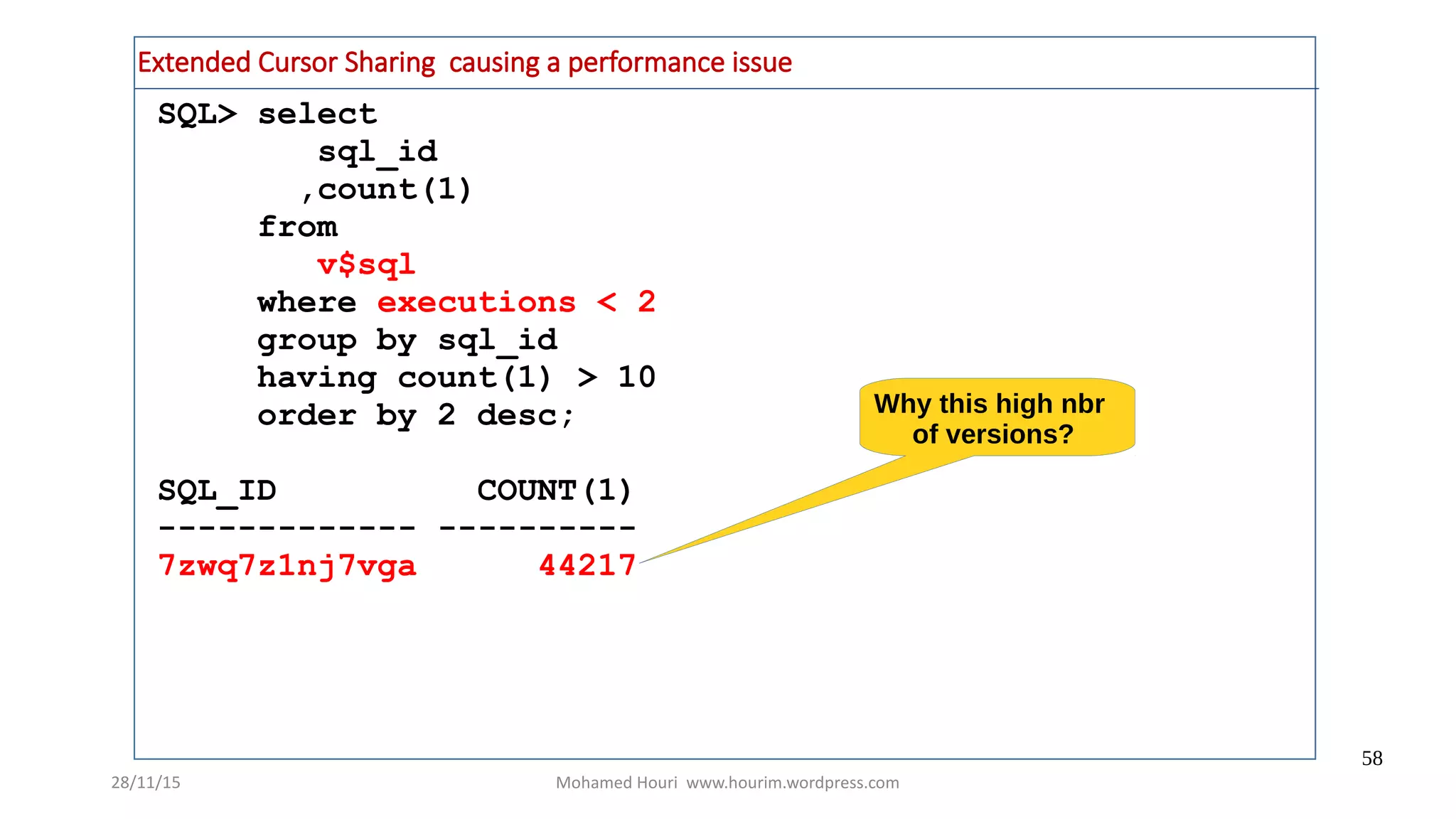
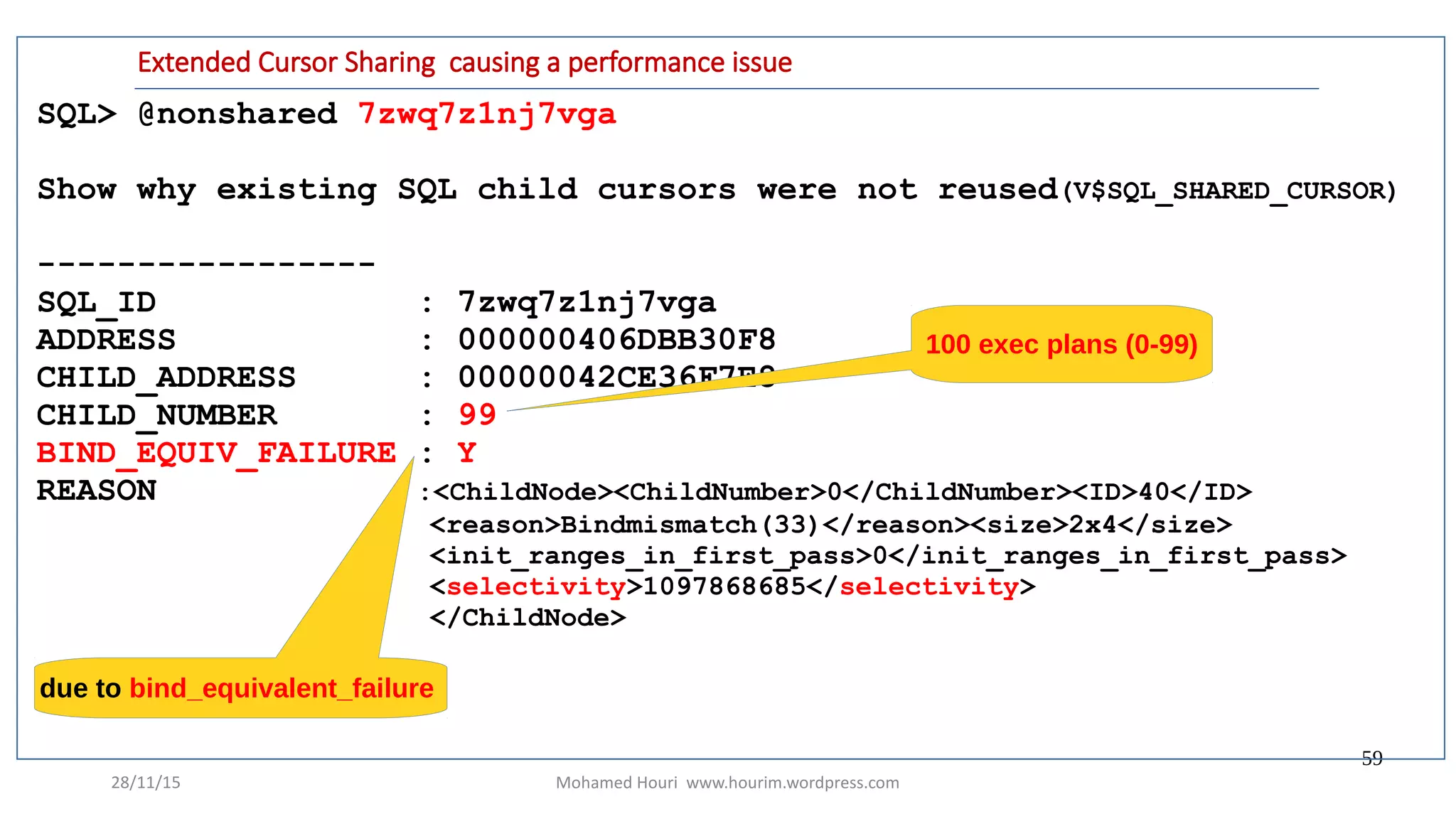
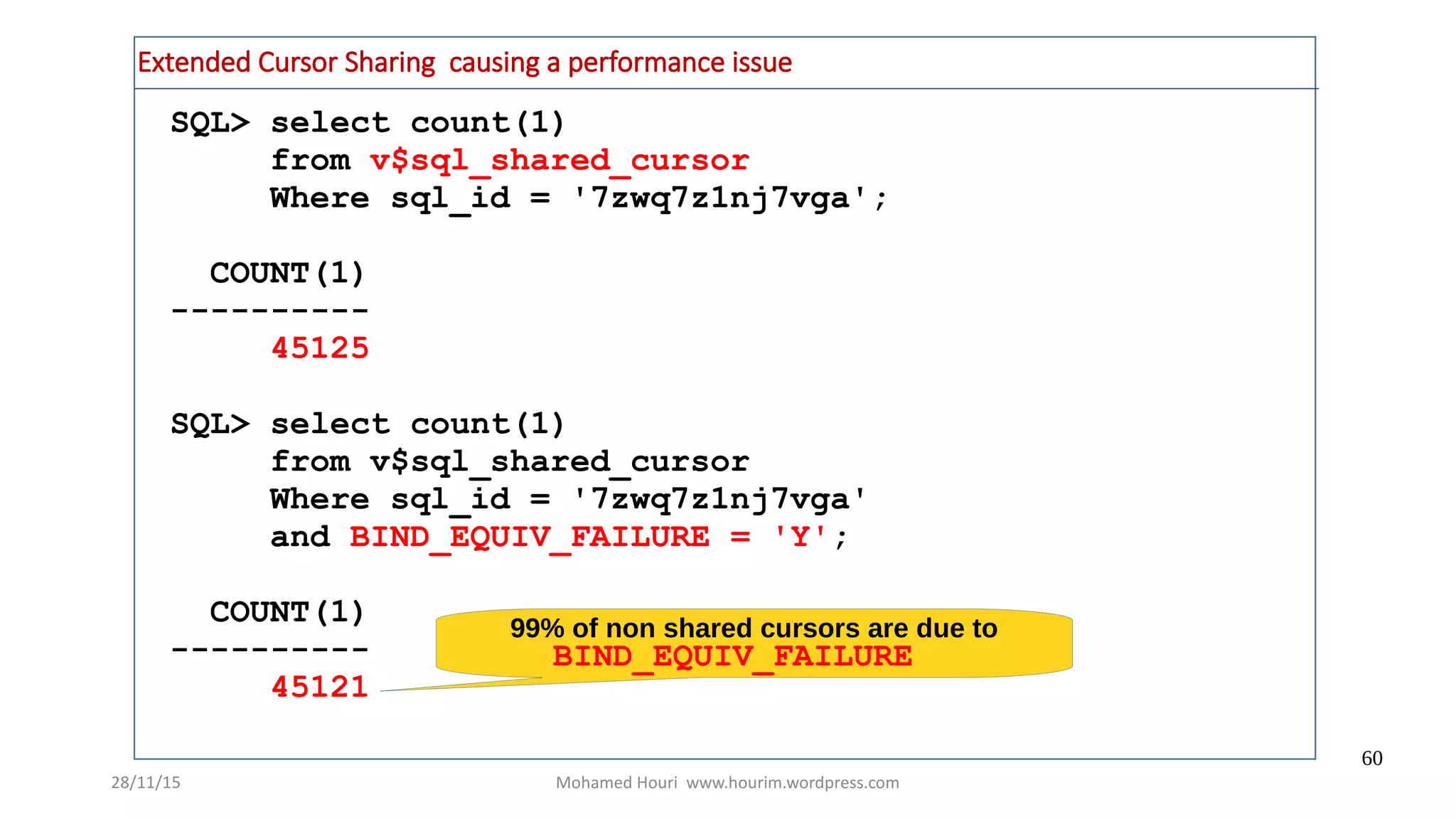
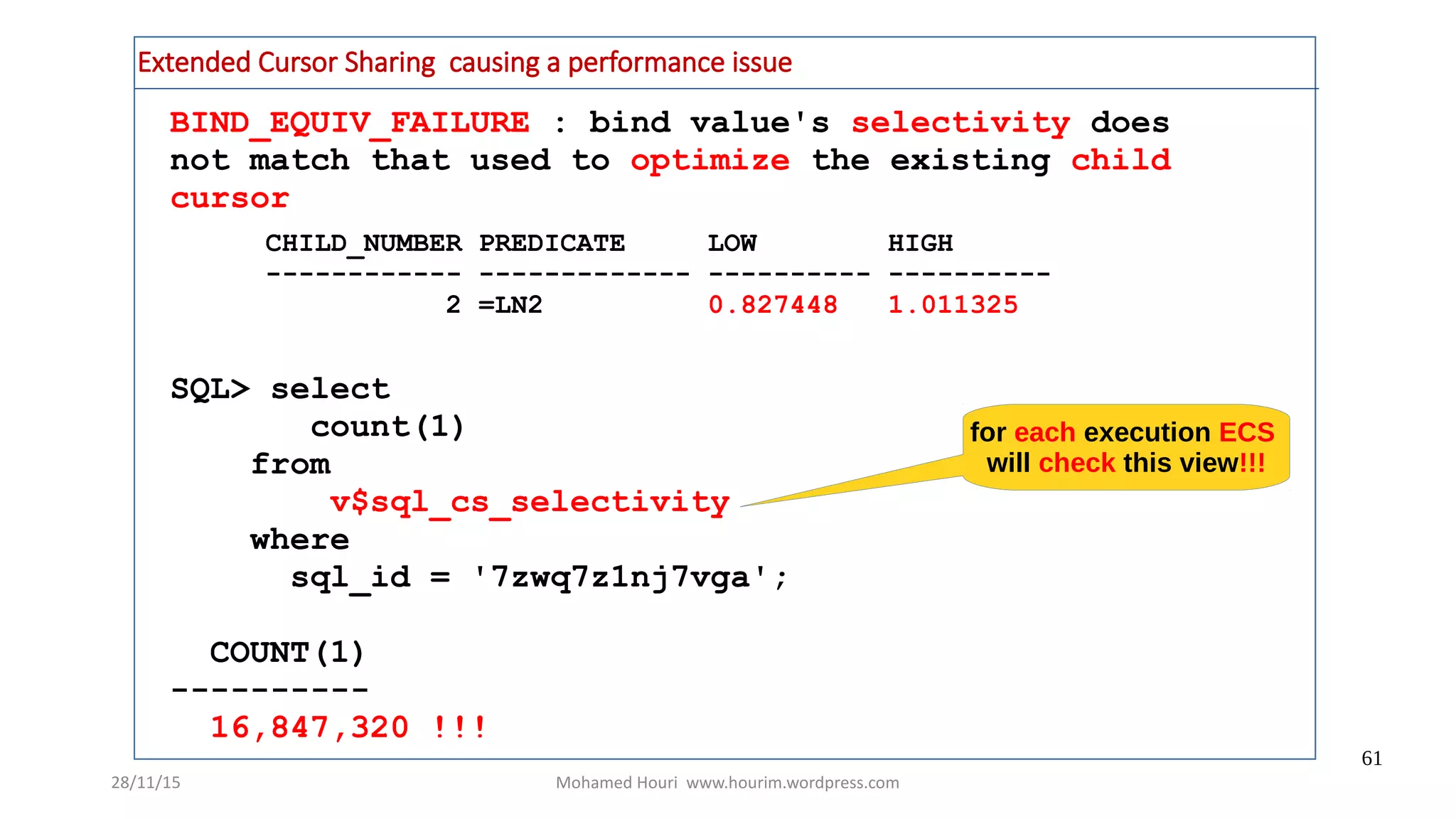
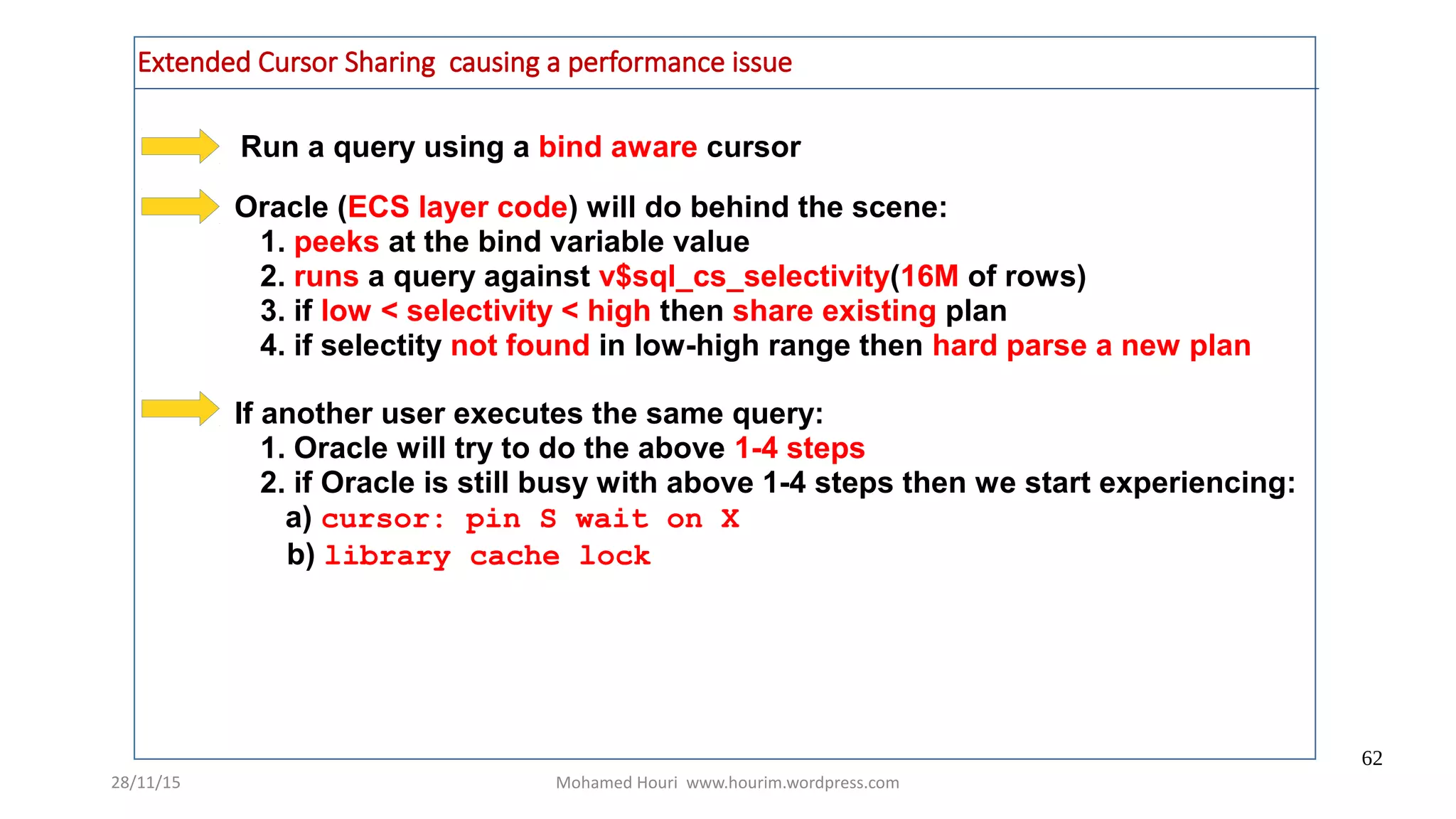
The document discusses adaptive cursor sharing (ACS) in SQL optimization, highlighting performance issues caused by traditional cursor sharing methods and how ACS can lead to optimal execution plans by being bind sensitive and aware. It provides practical examples, explores monitoring through v$sql views, and illustrates how ACS can address performance bottlenecks by triggering new execution plans based on variable bindings. The conclusion emphasizes the importance of understanding the dynamic behavior of cursor execution to leverage ACS effectively.