The document describes an AI-driven Occupational Skills Generator (AIOSG) that aims to automate the process of creating occupational skills reference documents. The AIOSG utilizes an intelligent web crawler, natural language processing, neural networks, and a blockchain to gather data on occupational skills from various sources, analyze the data, and generate standardized skills reference documents. It is meant to make the document creation process more efficient, data-driven, and able to incorporate rapidly changing skills demands compared to the traditional manual process. The system architecture and key components of data collection, analysis, skills ontology construction, and reference document generation are outlined.











![E-PROCEEDING OF THE 8TH INTERNATIONAL
CONFERENCE ON SOCIAL SCIENCES RESEARCH 2019
E-PROCEEDING OF THE 8TH INTERNATIONAL CONFERENCE ON SOCIAL SCIENCES RESEARCH (ICSSR 2019).
(e-ISBN 978-967-0792-36-1). 18-19 November 2019, Imperial Heritage Hotel, Melaka, Malaysia.
Organised by https://worldconferences.net Page 42
The processed skills and competencies data will be sent to blockchain API. This will then perform a
transaction proposal submission to the peers in the blockchain network. The peers will then endorse the
transaction proposal and return the simulated transactions and endorsing the peers’ signatures. The
application waits until it receives enough endorsed transaction proposals and will send the endorsed
transaction to the Ordering Peer Service to create a new block and update the ledger.
A smart contract or chaincode is required by the blockchain to store data inside. The following
chaincode shows how the occupation is added into the blockchain.
func (m *AIOSGChaincode) addOccupation(stub shim.ChaincodeStubInterface, args
[]string) pb.Response {
if len(args) != 7 {
return shim.Error("Incorrect number of arguements. Expecting 7 args")
}
// Input sanitation
fmt.Println("- Start Submit Occupation -")
if len(args[0]) <= 0 {// User
return shim.Error("User Required !")
}
if len(args[1]) <= 0 { // Project Name
return shim.Error("Occupation Required!")
}
user := args[0]
occp := args[1]
for tsid := 1; tsid >= 1; tsid++ {
tid := strconv.Itoa(tsid)
idAsBytes, err := stub.GetState(tid)
if err != nil {
return shim.Error("Failed to get state for " + tid)
}
if len(idAsBytes) == 0 {
fmt.Printf("No record found for " + tid + " ! Safe to add !")
occupation := &Occupation{OccID: tid, OccName: occp}
tsJSONasBytes, err := json.Marshal(occupation)
if err != nil {
return shim.Error(err.Error())
}
//Putstate
err = stub.PutState(user, tsJSONasBytes)
if err != nil {
return shim.Error(err.Error())
}
// indexed and saved](https://image.slidesharecdn.com/ai-drivenoccupationalskillsgenerator-211220085841/85/Ai-driven-occupational-skills-generator-14-320.jpg)
![E-PROCEEDING OF THE 8TH INTERNATIONAL
CONFERENCE ON SOCIAL SCIENCES RESEARCH 2019
E-PROCEEDING OF THE 8TH INTERNATIONAL CONFERENCE ON SOCIAL SCIENCES RESEARCH (ICSSR 2019).
(e-ISBN 978-967-0792-36-1). 18-19 November 2019, Imperial Heritage Hotel, Melaka, Malaysia.
Organised by https://worldconferences.net Page 43
tsKey, err := getTSKey(stub, occupation.OccID, occupation.OccName)
if err != nil {
return shim.Error("Error getting Occupation key" + err.Error()
)
}
fmt.Println(tsKey)
value := []byte{0x00}
stub.PutState(tsKey, value)
fmt.Println("--- end submit Occupation successfully ---")
} else {
tsid = tsid + 1
}
}
return shim.Success(nil)
}
Figure 15: Smart contract to add occupation
The data is added into a struct. A struct is a structure of how the data captured is stored. Figure 16
shows how the structure of data is stored in blockchain.
type Occupation struct {
OccID string `json:"occID"`
OccName string `json:"occupation"`
Keywords []string `json:"keywords"`
Skillset []string `json:"skillset"`
}
Figure 16: Data structure stored in blockchain
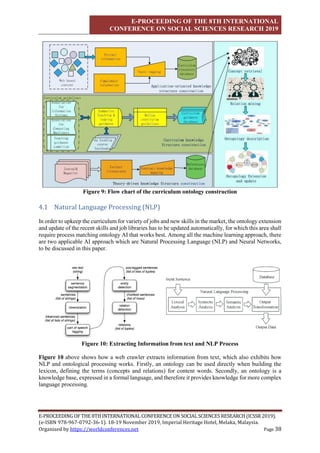
5.2 Digital Footprint Using Blockchain
The processed skills and competencies data that is stored in the blockchain is immutable. This ensures
any illegal updates performed will be disregarded as it cross references with other nodes to check if the
data is the same or not. This is because, if the data is changed, the data has will change too. This will
disconnect from the original chain of blocks itself. This ensures the integrity of the data.
A digital footprint is established using blockchain. Blockchain traces records from the beginning to the
end (Blockchain Network, 2019). This is enabled using the block hash which are chained together.
Using this feature, any data created or updated in the blockchain leaves a trace of who has invoked the
call as it stores the identity of user too. Not only does the blockchain trace the state of the data, it also
traces the person who invokes it.](https://image.slidesharecdn.com/ai-drivenoccupationalskillsgenerator-211220085841/85/Ai-driven-occupational-skills-generator-15-320.jpg)
![E-PROCEEDING OF THE 8TH INTERNATIONAL
CONFERENCE ON SOCIAL SCIENCES RESEARCH 2019
E-PROCEEDING OF THE 8TH INTERNATIONAL CONFERENCE ON SOCIAL SCIENCES RESEARCH (ICSSR 2019).
(e-ISBN 978-967-0792-36-1). 18-19 November 2019, Imperial Heritage Hotel, Melaka, Malaysia.
Organised by https://worldconferences.net Page 45
func (m *AIOSGChaincode) searchKeyword(stub shim.ChaincodeStubInterface, args
[]string) pb.Response {
queryString := "{"Keywords":"+"args[0] "+"}"
queryResults, err := getQueryResultForQueryString(stub, queryString)
if err != nil {
return shim.Error(err.Error())
}
return shim.Success(queryResults)
}
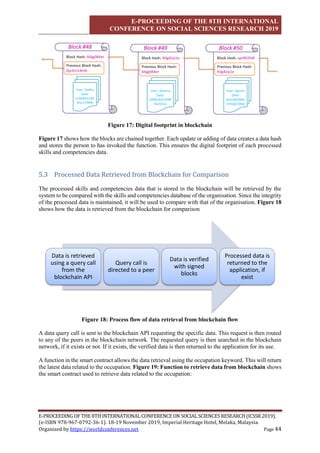
Figure 19: Function to retrieve data from blockchain
6 Generated Occupational Skills Reference
A sample table of related knowledge and skills generated by the AIOSG system for a particular OSR is
given below. It shall include occupational structure, occupational area, competency levels, competency
profile, competency based curriculum, and guidelines for assessment and training. With more sources
of information from the Internet in the form of unstructured data and Government and private sector
databases in the form of structured data as well as verification and subject matter knowledge from
industry experts and lead bodies, the final output will be generated quickly and more accurately reflect
the actual real-world knowledge and skills.
OSR TITLE Cybersecurity Penetration Tester
REQUIRED
ACTIVITY
RELATED KNOWLEDGE RELATED SKILLS
Manage IP
Network
1.1 Network documentation and change
management
1.2 IP protocol stack layers including:
Role of a layered protocol stack
Key functions of each layer of
the IP stack
1.3 Ethernet operation and addressing
structure including:
Ethernet operating principles
Ethernet frame structure &
frame fields
MAC address structure
1.4 Transport layer protocols including:
TCP and UDP
TCP flow control
1.5 Network devices including:
Router
Switch
Networking Interface
1.6 IP network management tools and
software
Protocol analyser
Command line
1.1 Configuring and operating between
layers of the IP protocol stack
1.2 Interpret Ethernet features and
operations, configuration and
troubleshooting
1.3 Interpret key transport layer protocol
operations and act on them
1.4 Identifying key network devices and
their attributes
1.5 Connecting to key network devices
1.6 Utilisation of suitable tools and
software for managing IP networks](https://image.slidesharecdn.com/ai-drivenoccupationalskillsgenerator-211220085841/85/Ai-driven-occupational-skills-generator-17-320.jpg)
![E-PROCEEDING OF THE 8TH INTERNATIONAL
CONFERENCE ON SOCIAL SCIENCES RESEARCH 2019
E-PROCEEDING OF THE 8TH INTERNATIONAL CONFERENCE ON SOCIAL SCIENCES RESEARCH (ICSSR 2019).
(e-ISBN 978-967-0792-36-1). 18-19 November 2019, Imperial Heritage Hotel, Melaka, Malaysia.
Organised by https://worldconferences.net Page 46
7 Conclusion
This paper presents a system to address the gaps in generating occupational skills reference (OSR)
documents for the workforce. The system crawls for data from the Internet and other relevant databases
in addition to taking account of inputs from industry experts. This is to form a complete picture in terms
of inputs toward a particular job sector. The inputs are then processed in terms of the relative nature of
the skills to a particular job by way of Artificial Intelligence. The processed data is then verified by the
industry expert and lead bodies’ panel to generate the final output. The final OSR is stored in the
blockchain network to ensure traceability in terms of updates of such records and be put up for review
by a panel of experts for decision-making, publishing and future workforce planning. Malicious parties
cannot easily tamper the records of the documents and associated materials, due to the immutable nature
of blockchain. Through the enablement of such a system, relevant and applicable occupational skills
can be utilised by various industries.
8 References
1. Noah, S.A., Amruddin, A.Y., & Omar, N. (2007). Semantic Similarity Measures for Malay
Sentences. [Ebrary version]. Retrieved from
http://books.google.com.my/books?id=8pxUkfwqt_0C&pg=PA117&dq=amru+semantic+mal
ay&source=gbs_toc_r&cad=4
2. Li, Y., Mclean, D., Bandar, Z.A., O'Shea, J.D., & Crockett, K. (2006). Sentence similarity
based on semantic nets and corpus statistics. [Ebrary version]. Retrieved from
http://ants.iis.sinica.edu.tw/3BkMJ9lTeWXTSrrvNoKNFDxRm3zFwRR/55/Sentence%20Si
milarity%20Based%20on%20Semantic%20Nets%20and%20corpus%20statistics.pdf
3. Strickland, J. (2014). Predictive Analytics Using R. Colorado Springs, Simulation Educators.
4. Zhu, Y, C., Zhang, W., He, Y., Wen, J. B., & Li, M. Y. (2018). Design and implementation of
curriculum knowledge Ontology – Driven SPOC Flipped Classroom Teaching Model.
Educational Sciences: Theory & Practice, 18(5), 1351-1374.
5. Hyperledger (2019). Introduction to Hyperledger Fabric. Retrieved from https://hyperledger-
fabric.readthedocs.io/en/release-1.4/blockchain.html
6. Blockchain Network (2019). Retrieved November 2019, from https://hyperledger-
fabric.readthedocs.io/en/release-1.4/network/network.html.](https://image.slidesharecdn.com/ai-drivenoccupationalskillsgenerator-211220085841/85/Ai-driven-occupational-skills-generator-18-320.jpg)