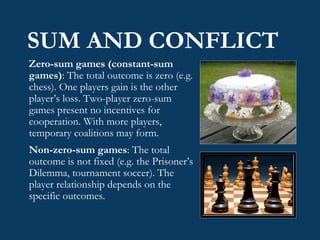
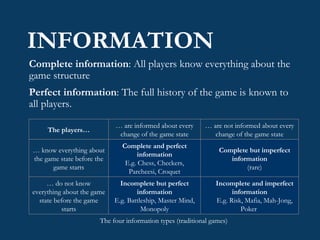
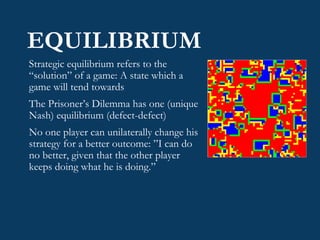
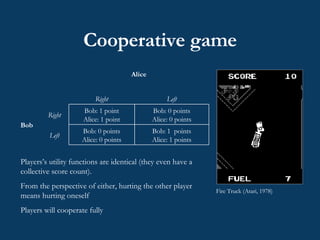
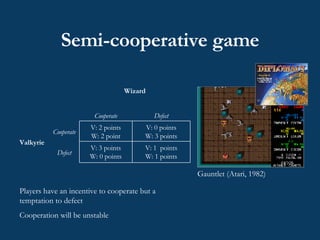
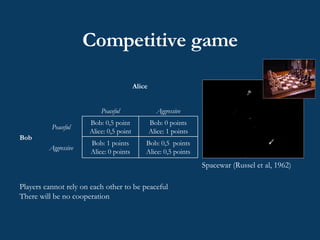
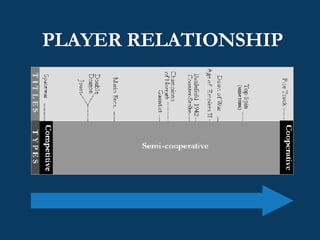
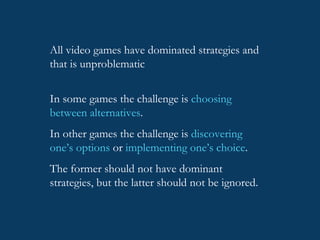
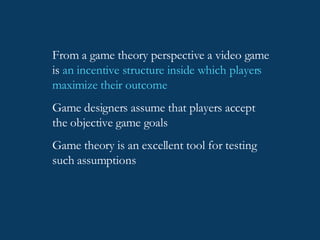
The document discusses using game theory to analyze video games. It provides background on game theory, explaining that it is the formal study of decision-making where players' choices affect each other. It outlines some key game theory concepts like the prisoner's dilemma, chicken game, and Nash equilibrium. It then discusses how different types of video games like cooperative, semi-cooperative, and competitive games can be modeled using concepts from game theory.
![GOALS, REASON, AND DANGEROUS THINGS An über-ludological approach to game analysis unabashedly rooted in economic game theory Advanced Game Theory, Sep 24 2007 JONAS HEIDE SMITH [email_address]](https://image.slidesharecdn.com/advanced-game-theory-guest-lecture4269/75/Advanced-Game-Theory-guest-lecture-1-2048.jpg)
![“ It helps […] to think of a game’s structure as akin to an economy, or an ecosystem; a complex, interacting system that does not dictate outcomes but guides behavior through the need to achieve a single goal: energy, in the case of ecosystems; money, in the case of economics; victory, in the case of a game.” Costikyan, G. (2002). I Have No Words & I Must Design: Toward a Critical Vocabulary for Games . Paper presented at the Computer Games and Digital Cultures Conference Proceedings, Tampere.](https://image.slidesharecdn.com/advanced-game-theory-guest-lecture4269/85/Advanced-Game-Theory-guest-lecture-2-320.jpg)


![STRATEGIC DOMINANCE “ A well-designed game shouldn’t contain an option that is never worth using […] A dominated option is worthless. You wasted your time putting it in your game. A dominant option is worse. It means that all the other options are worthless.” (Rollings & Morris, 2004: p62-63)](https://image.slidesharecdn.com/advanced-game-theory-guest-lecture4269/85/Advanced-Game-Theory-guest-lecture-31-320.jpg)


![Thanks for your attention jonassmith.dk [email_address]](https://image.slidesharecdn.com/advanced-game-theory-guest-lecture4269/85/Advanced-Game-Theory-guest-lecture-37-320.jpg)