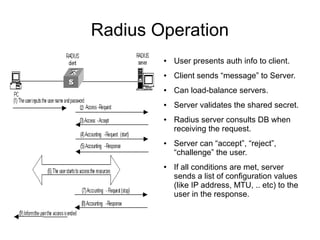
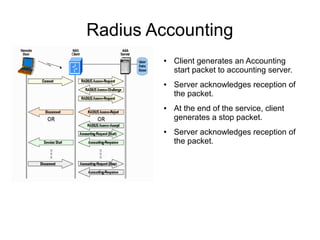
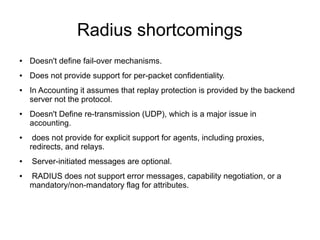
This document discusses RADIUS, a protocol for authentication, authorization, and accounting. It describes key RADIUS features like its client/server model and extensibility. It explains how RADIUS operates, including how clients authenticate users and how servers can accept, reject, or challenge requests. The document also covers RADIUS accounting, shortcomings like lack of failover support, and how Diameter evolved from RADIUS to address some of these issues. It introduces SBR as a Juniper RADIUS product and describes its modular design and features like centralized management, proxy support, and 3GPP integration.
![Diameter
●
It evolved from and replaces RADIUS protocol.
●
Ability to exchange messages and deliver AVPs.
●
Capabilities negotiation.
●
Error notification.
●
●
Extensibility, required in [RFC2989], through addition
of new applications, commands, and AVPs
Basic services necessary for applications, such as the
handling of user sessions or accounting](https://image.slidesharecdn.com/aaainanutshell-131022170019-phpapp02/85/AAA-in-a-nutshell-16-320.jpg)