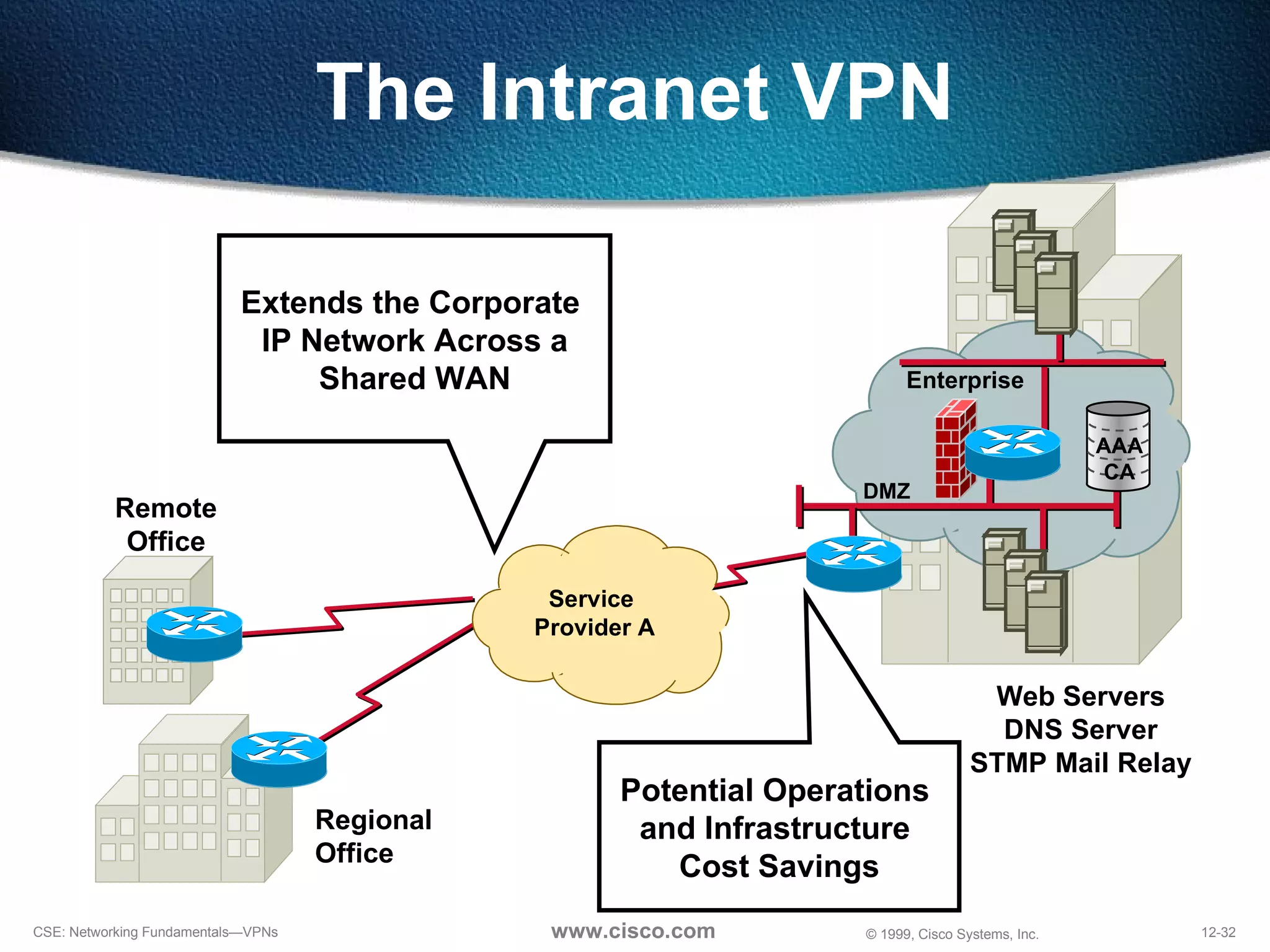
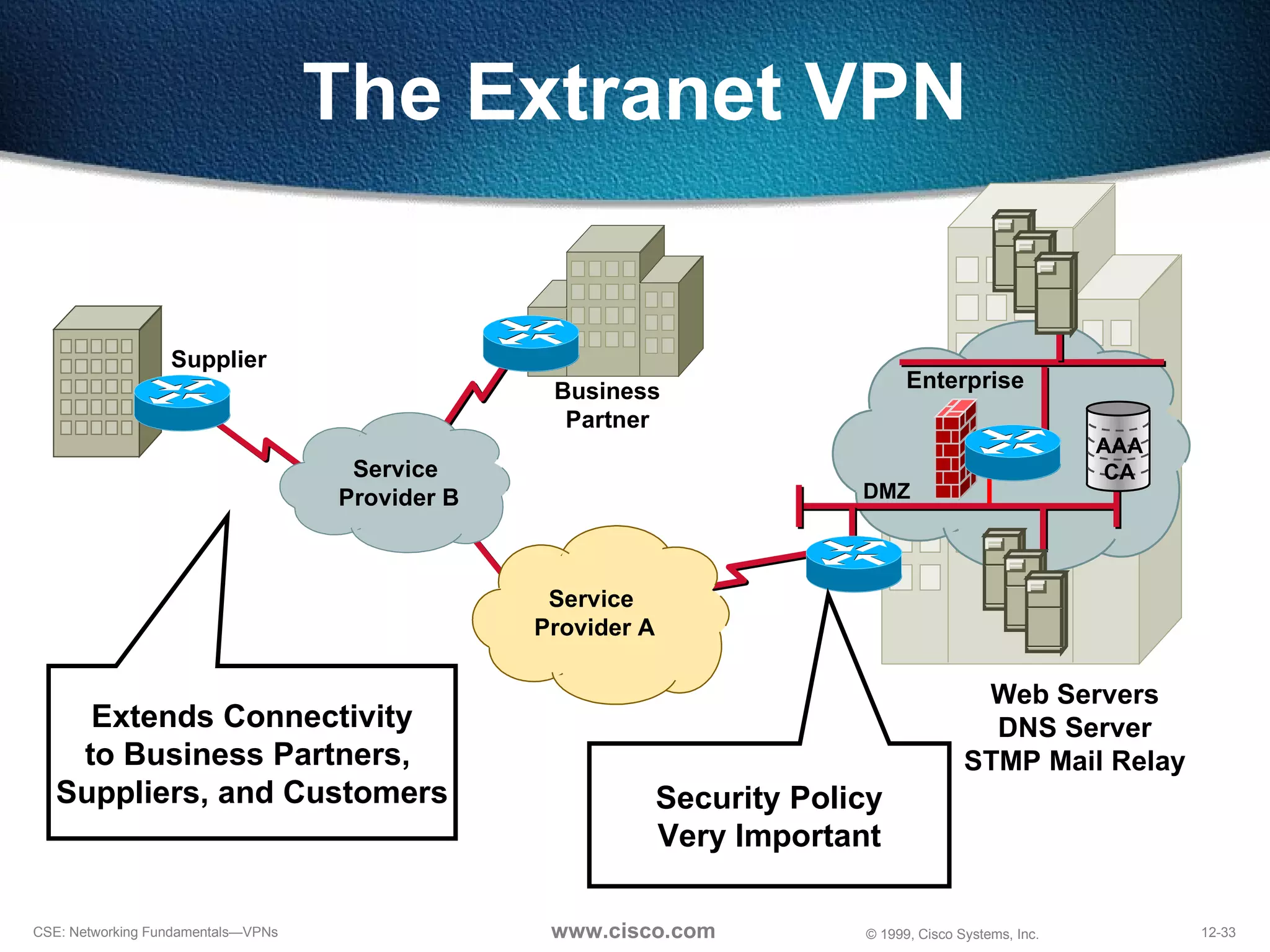
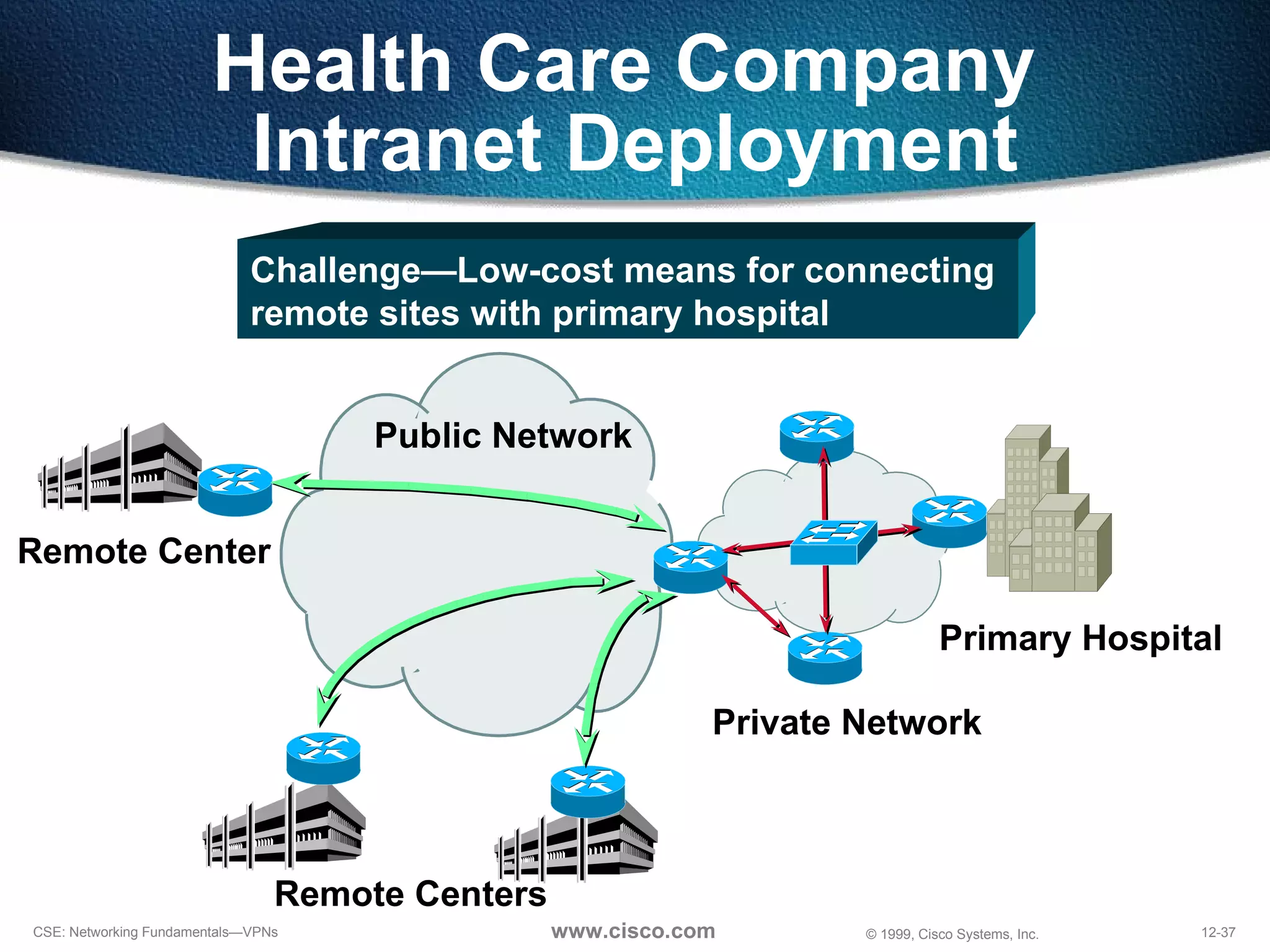
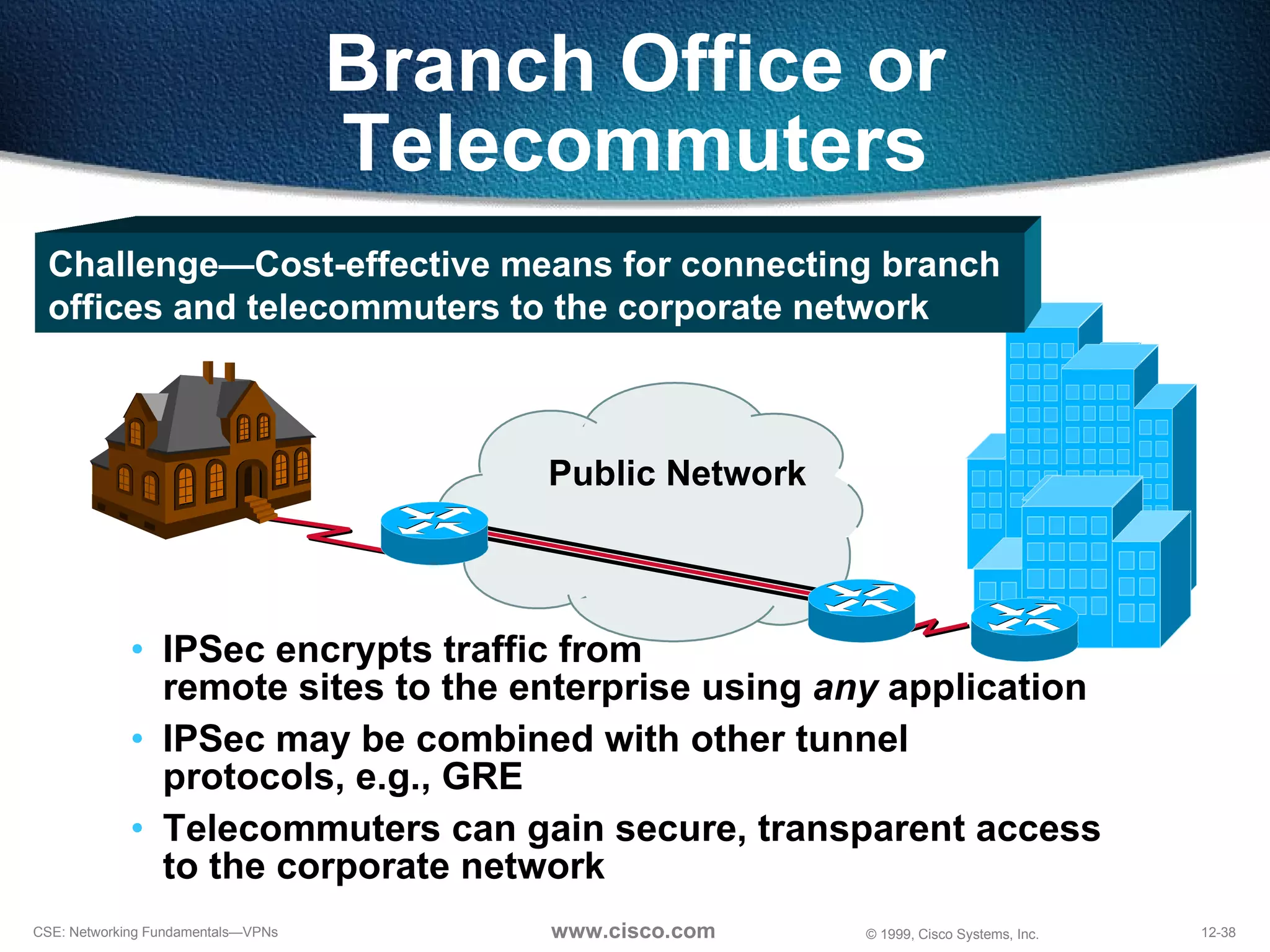
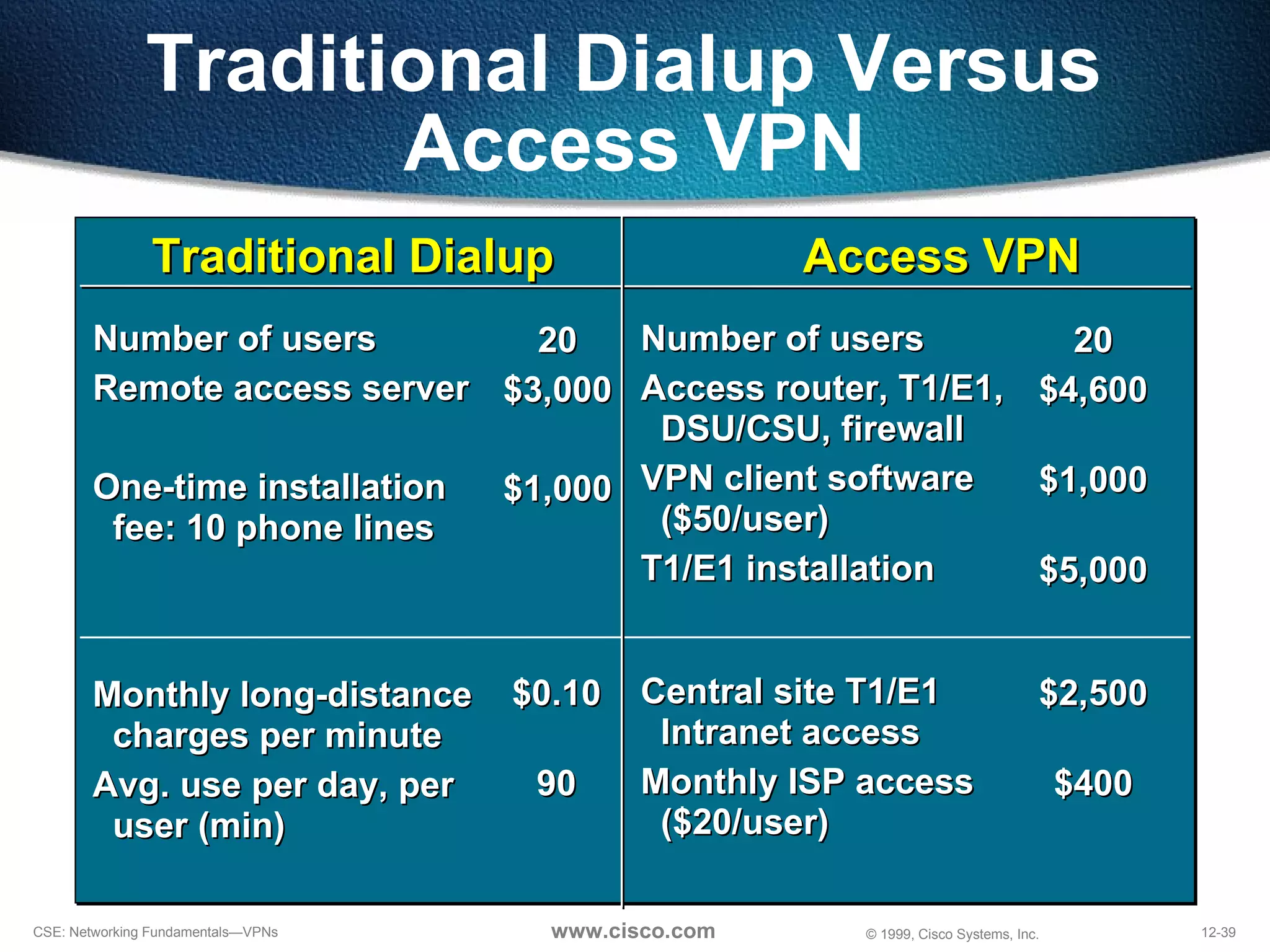
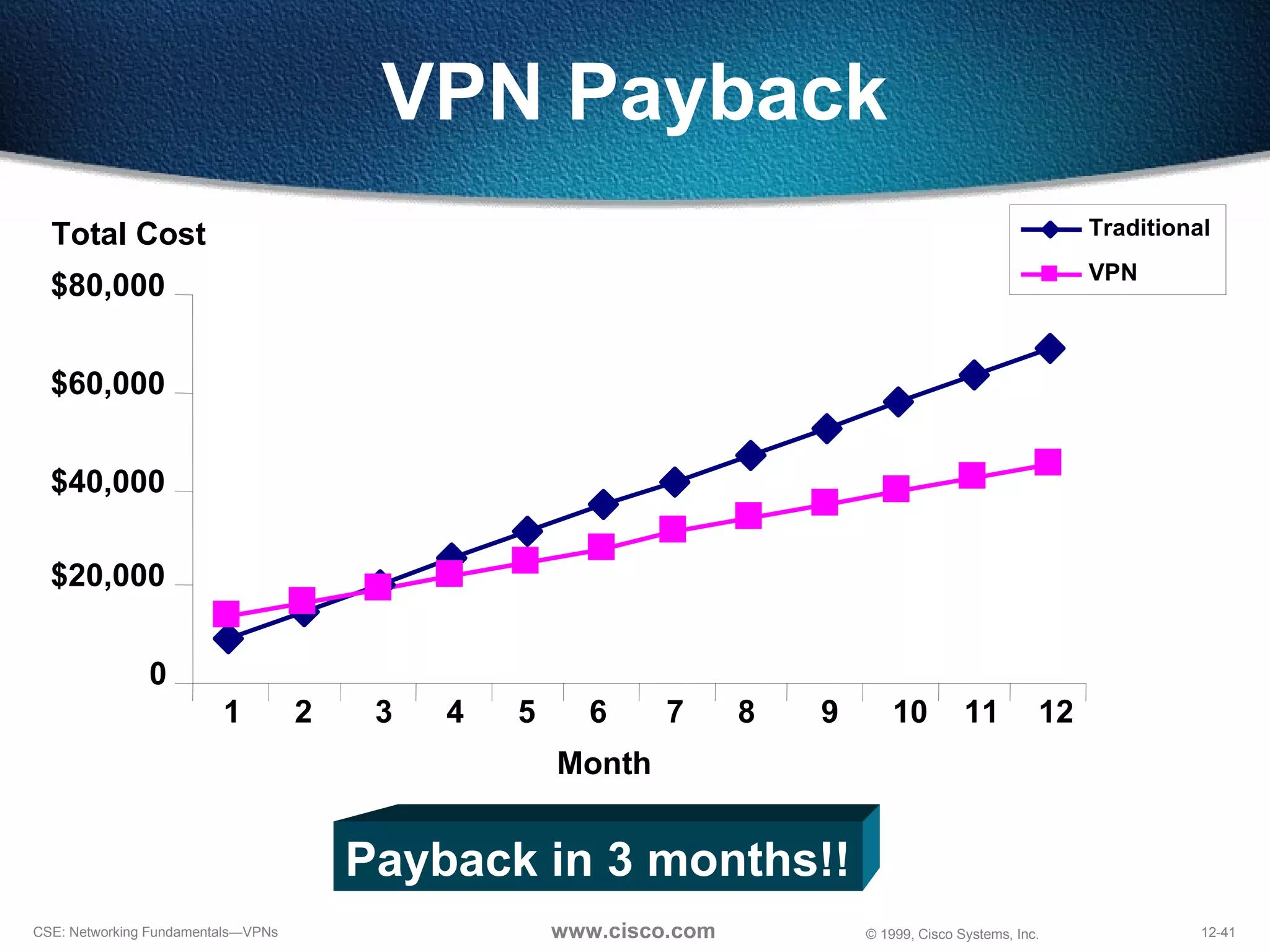
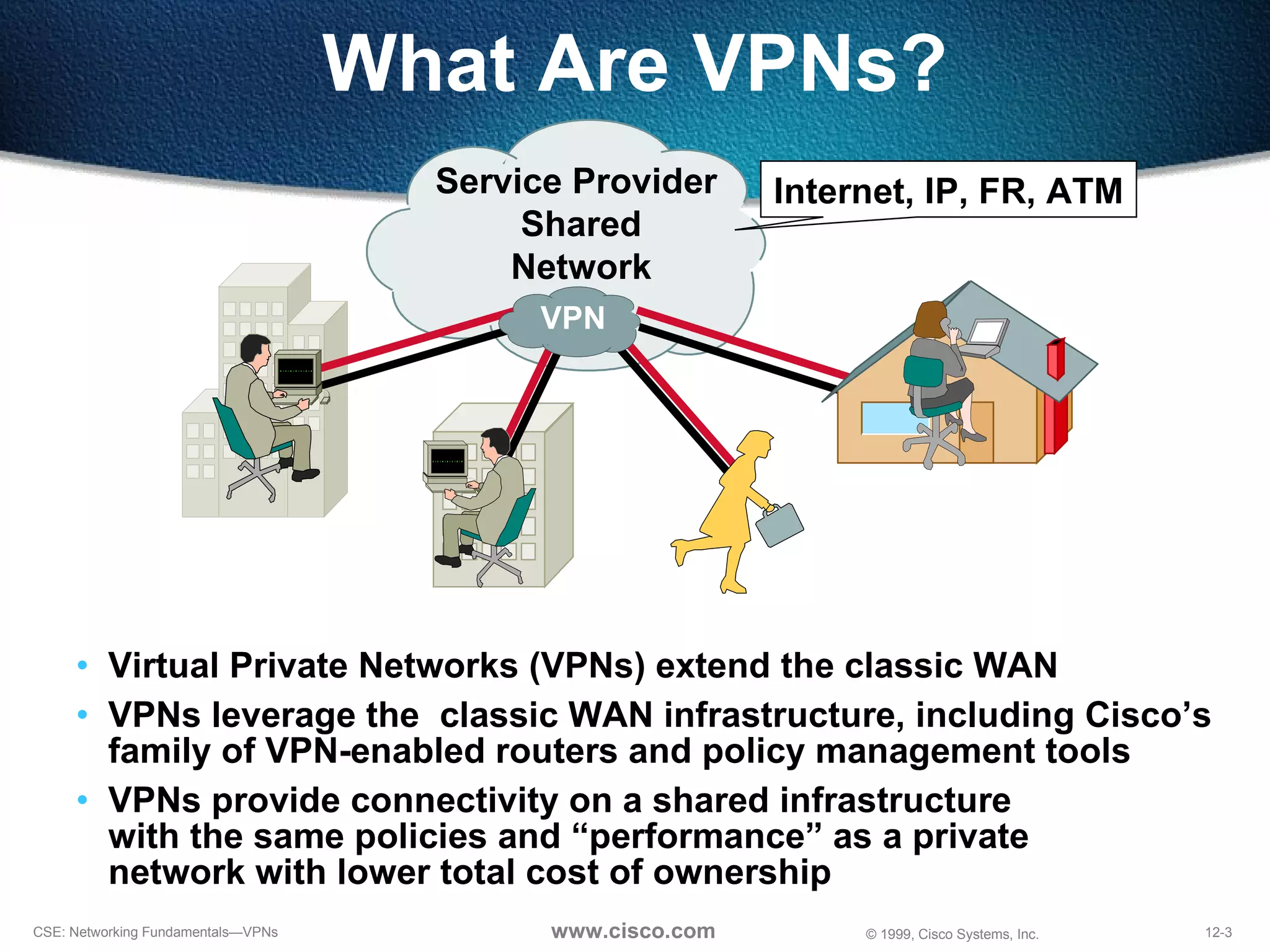
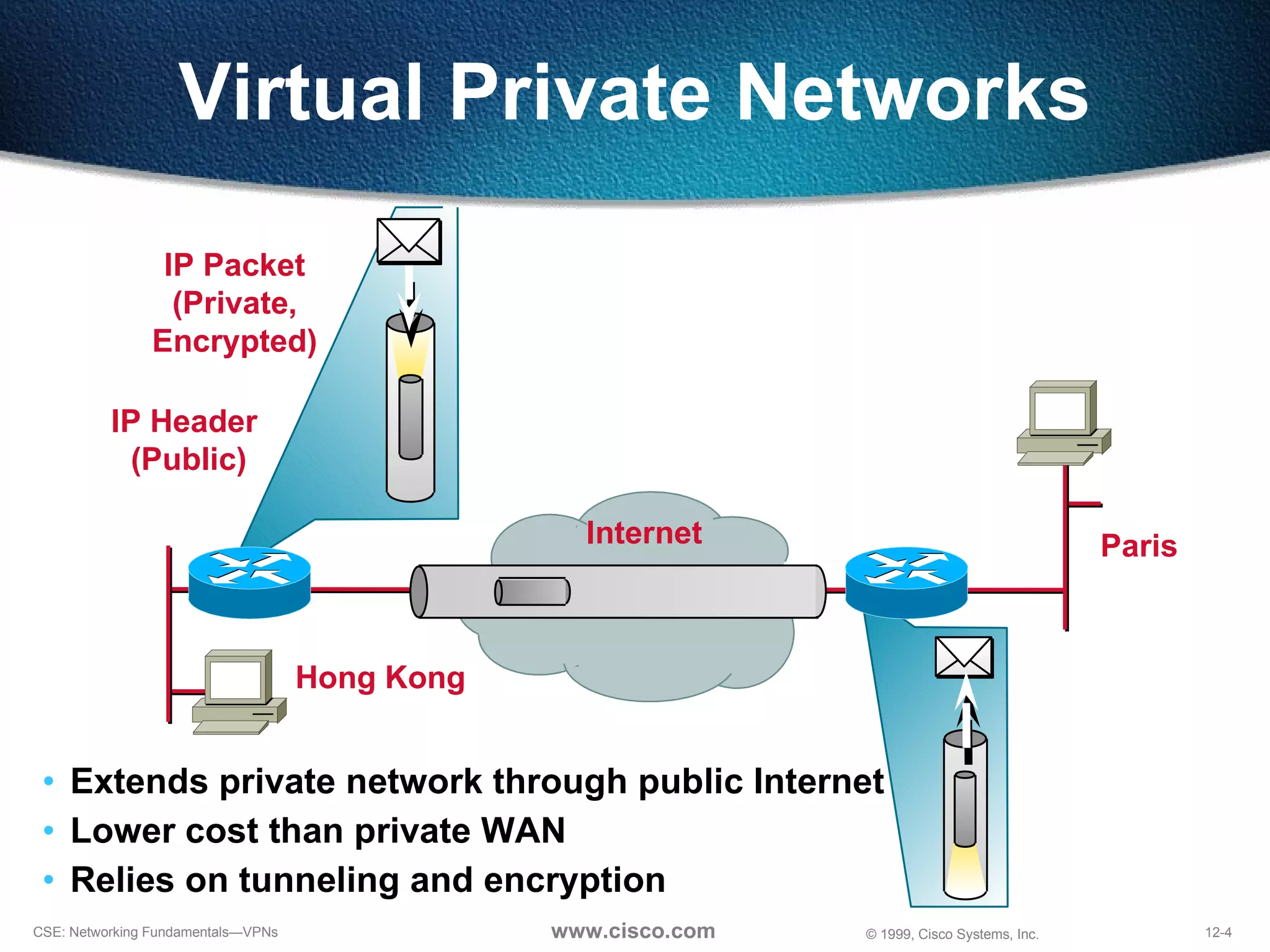
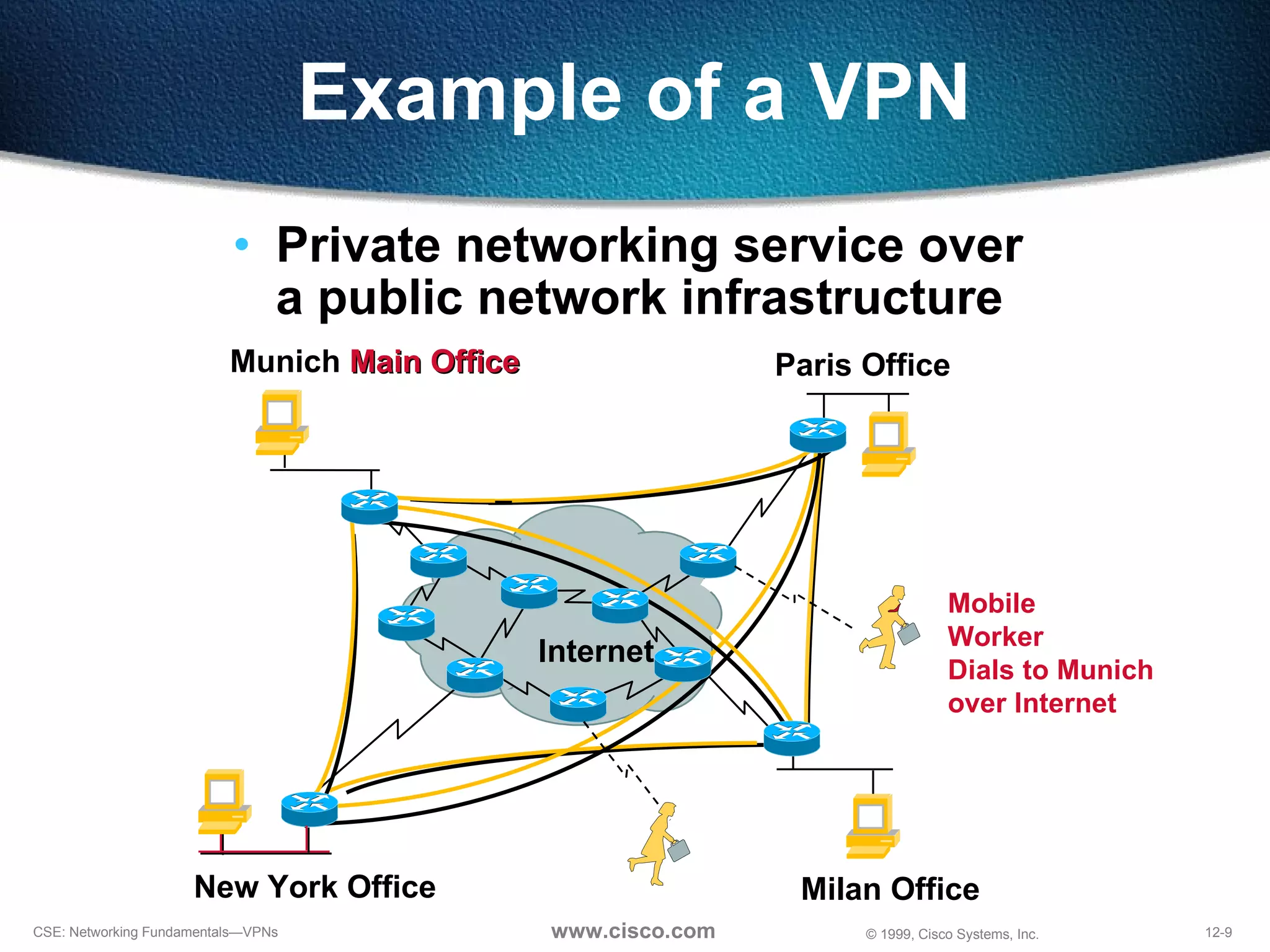
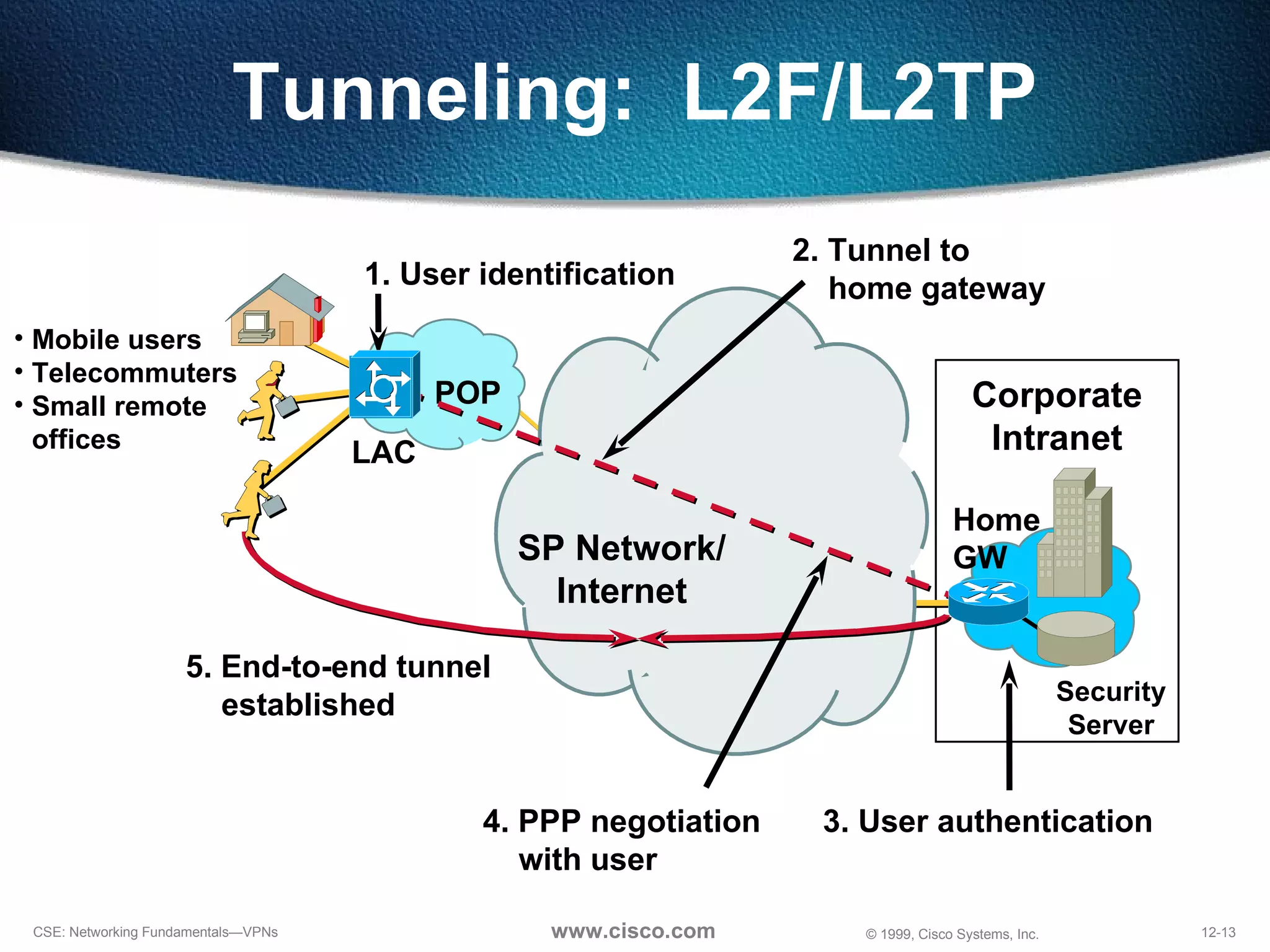
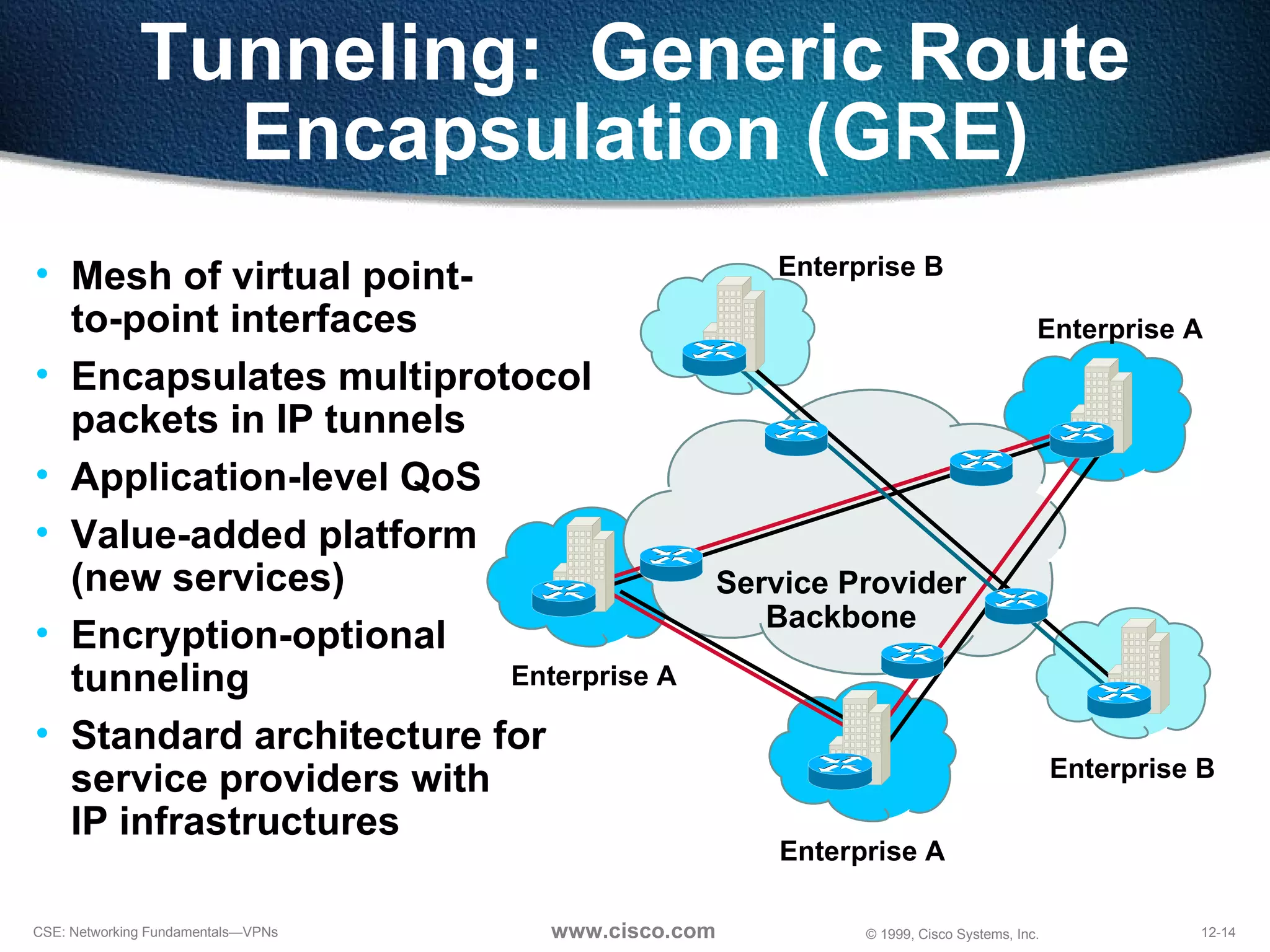
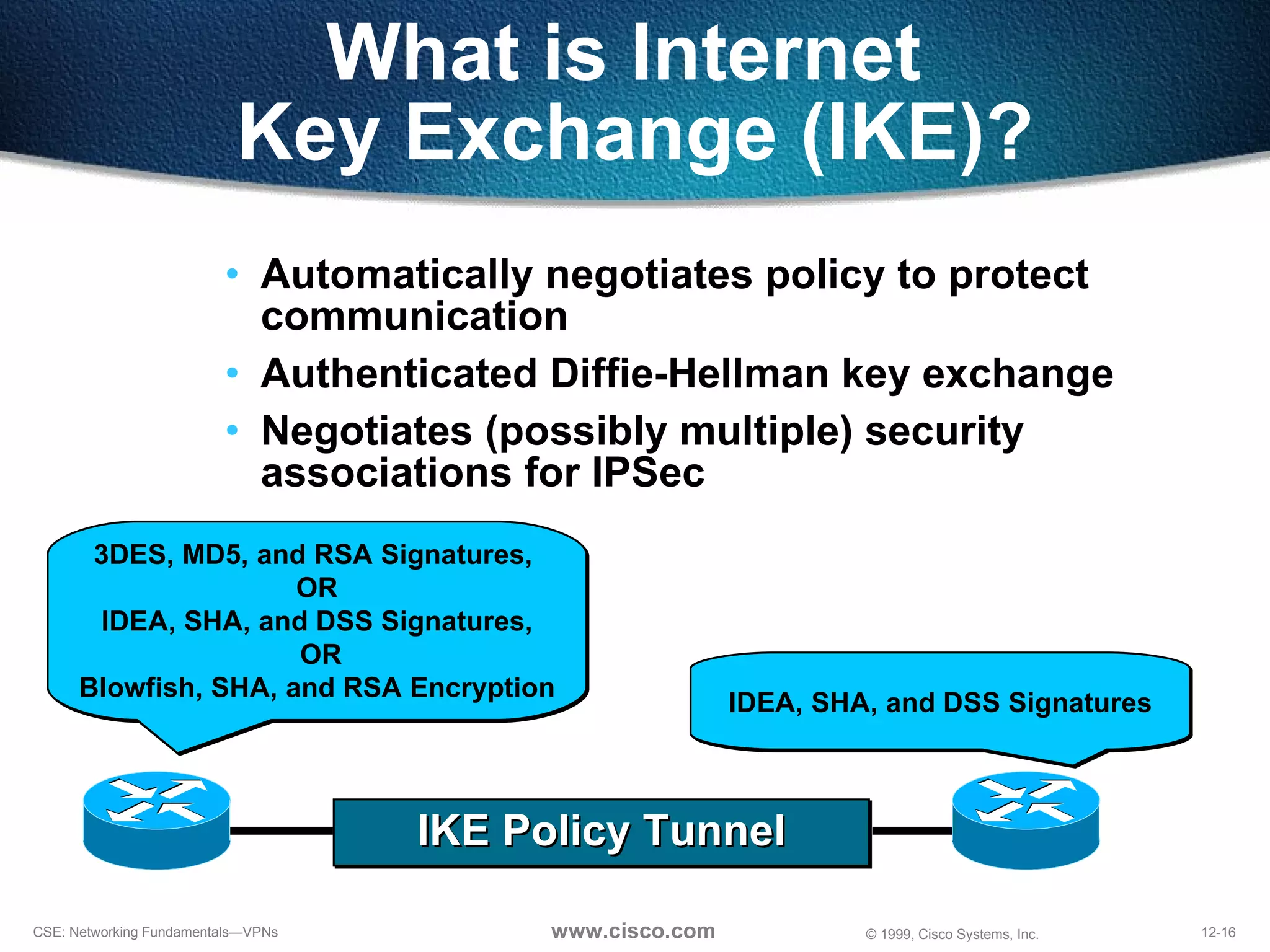
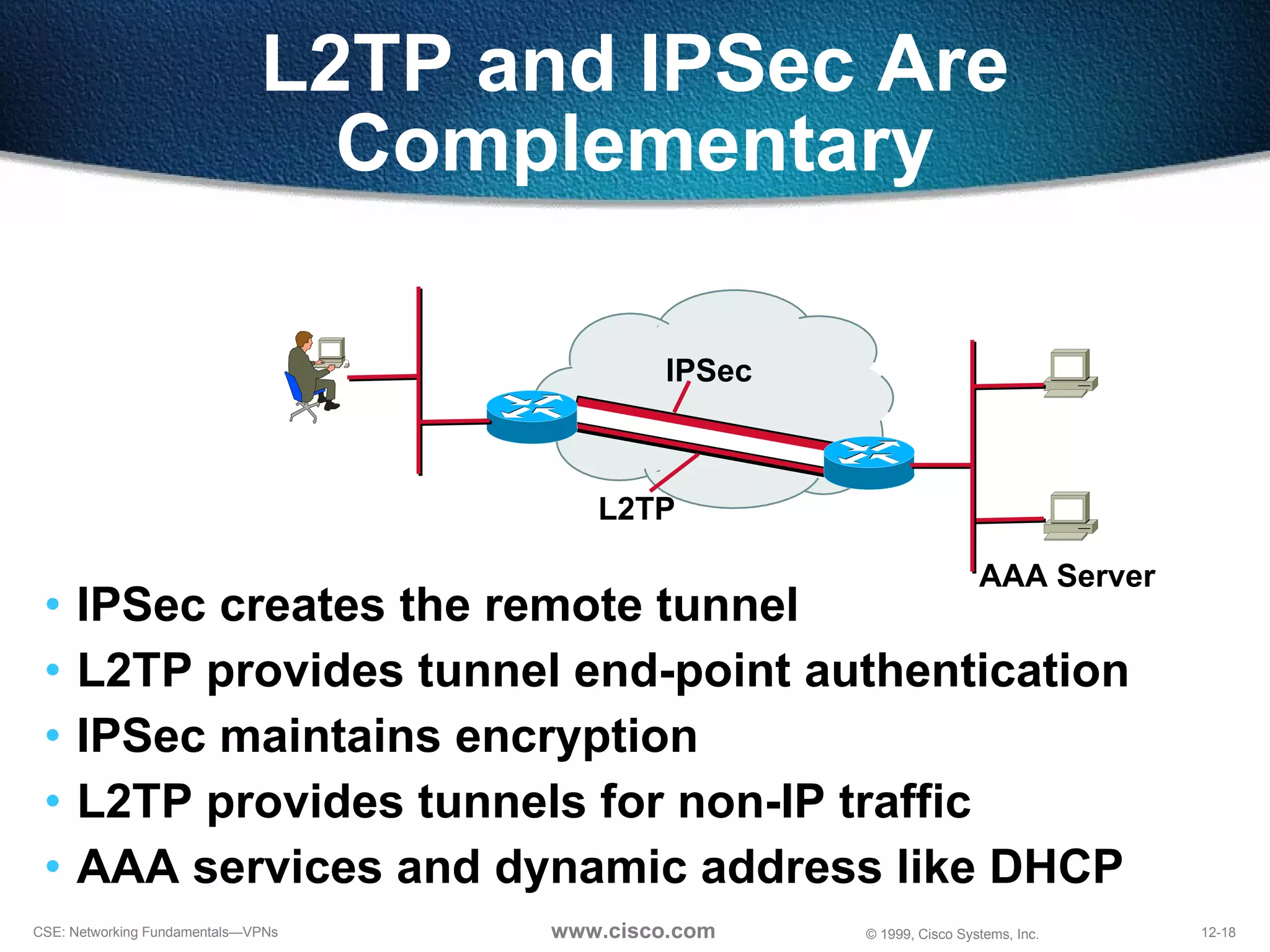
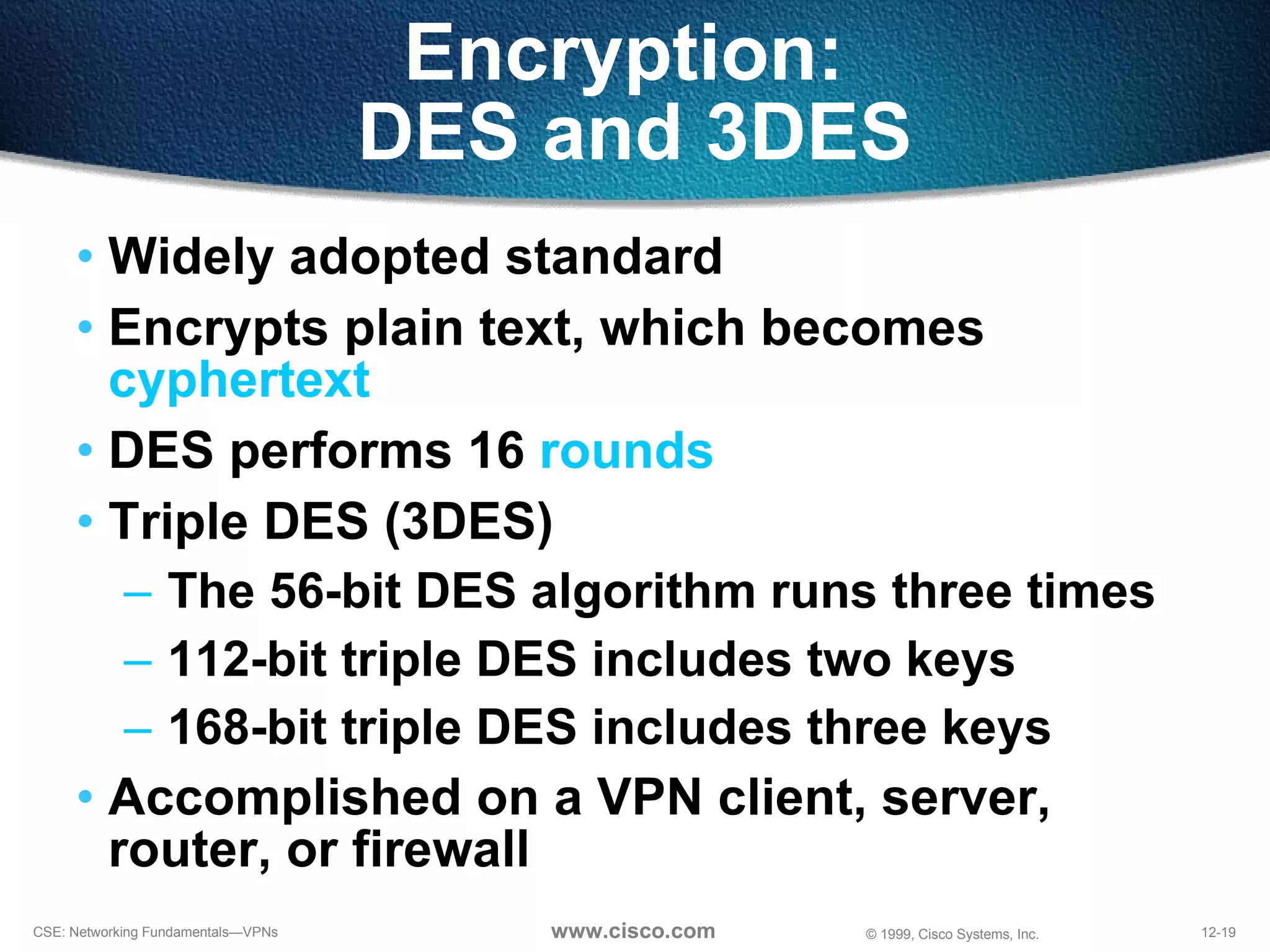
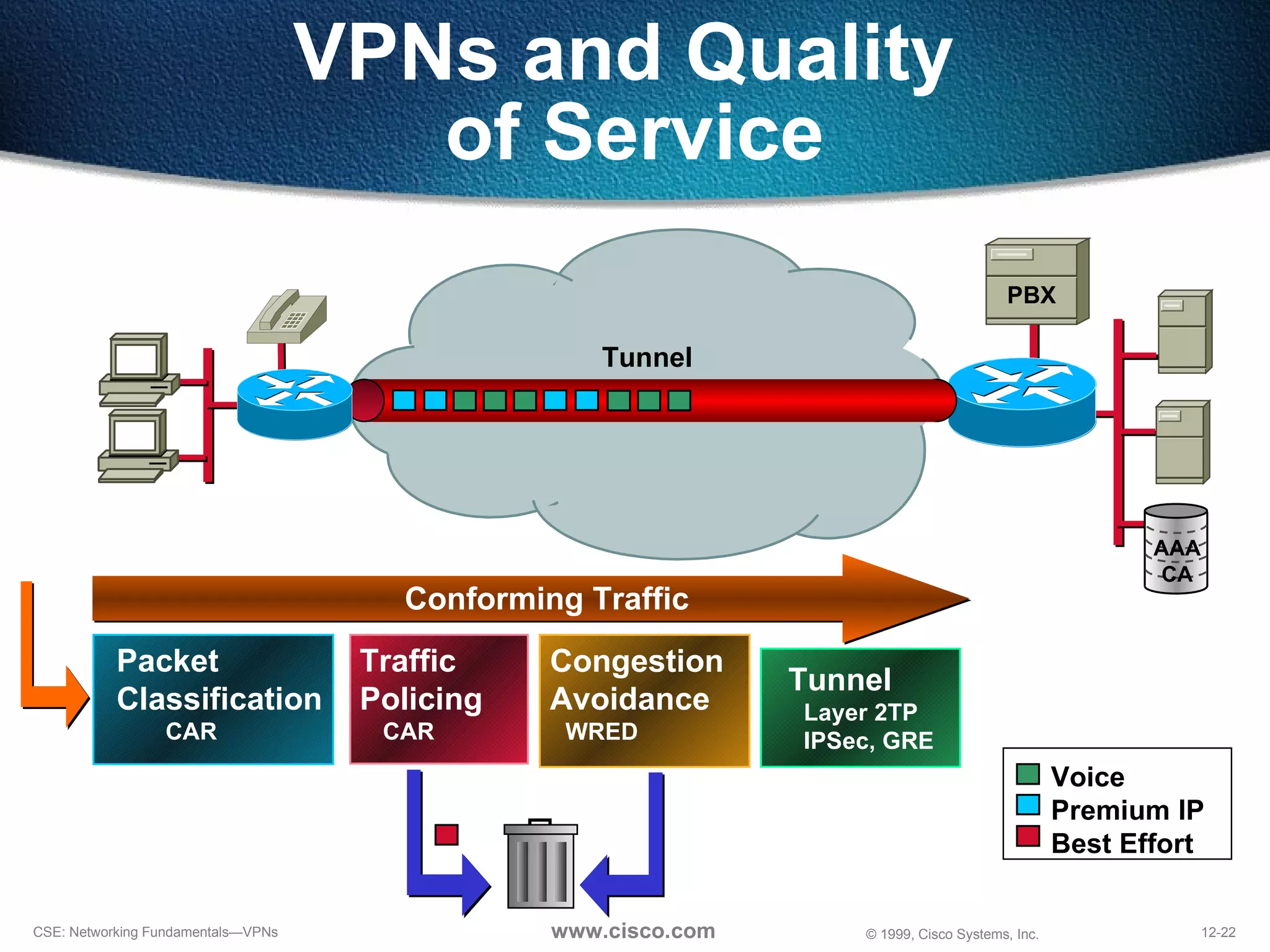
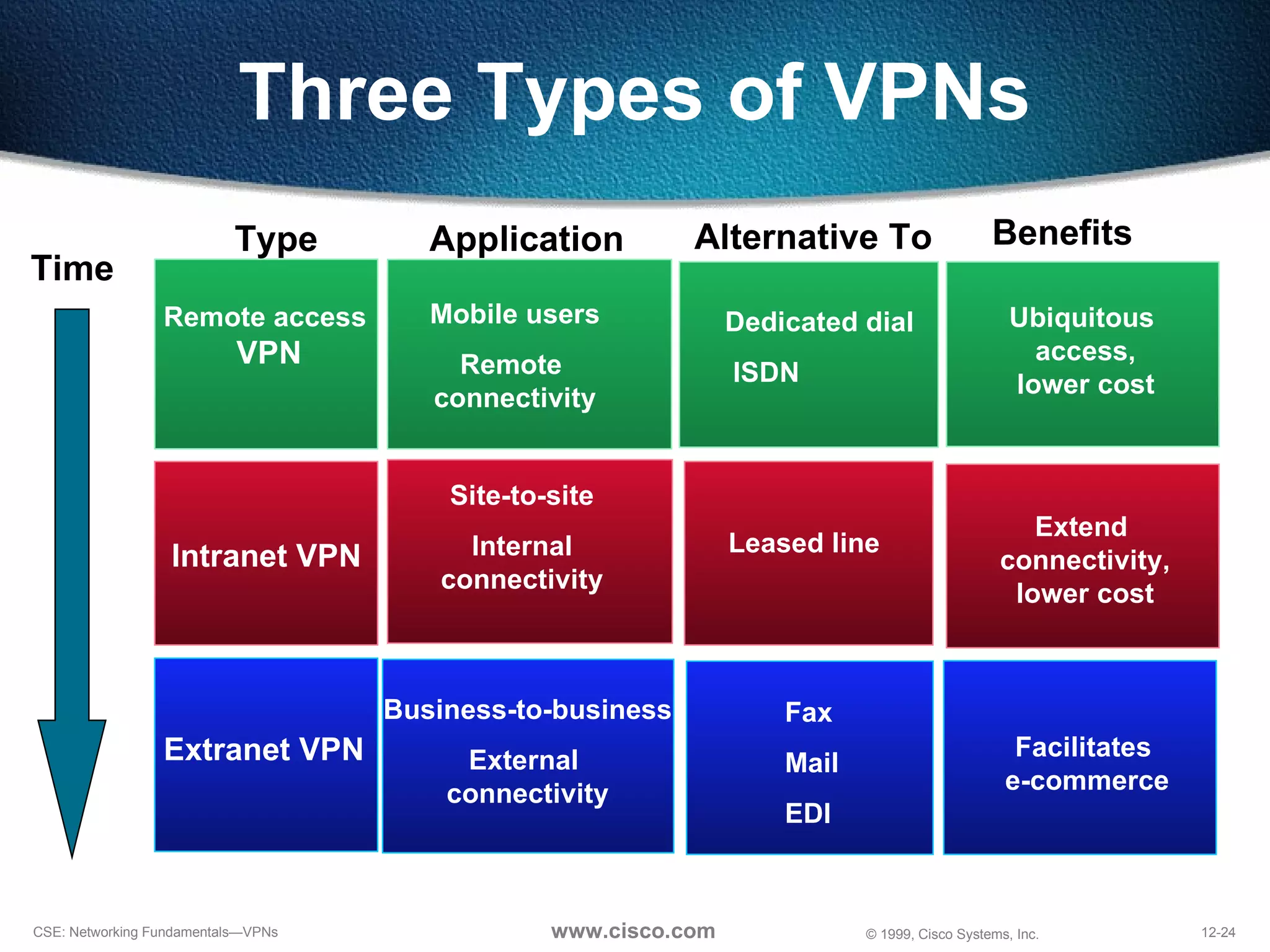
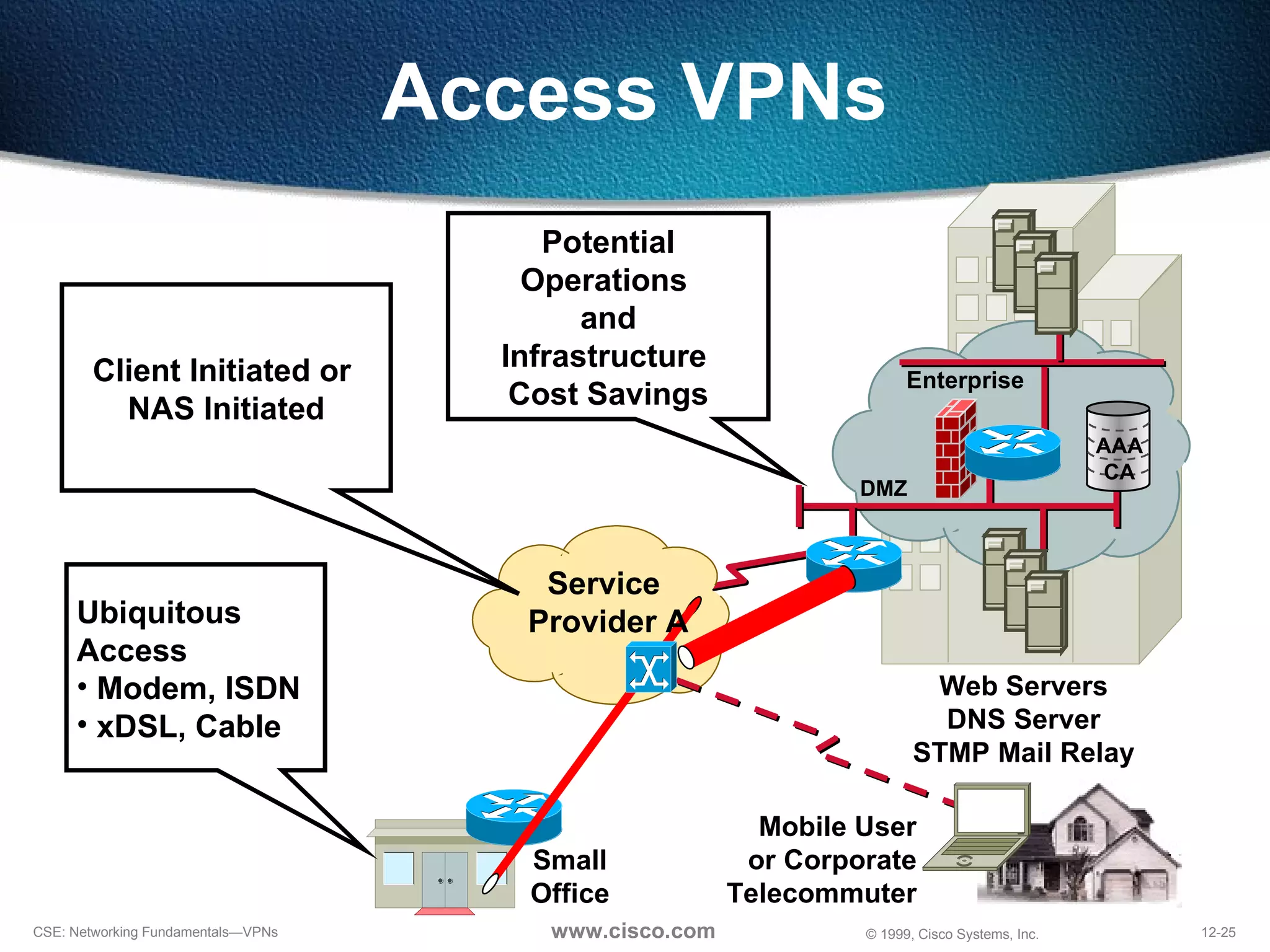
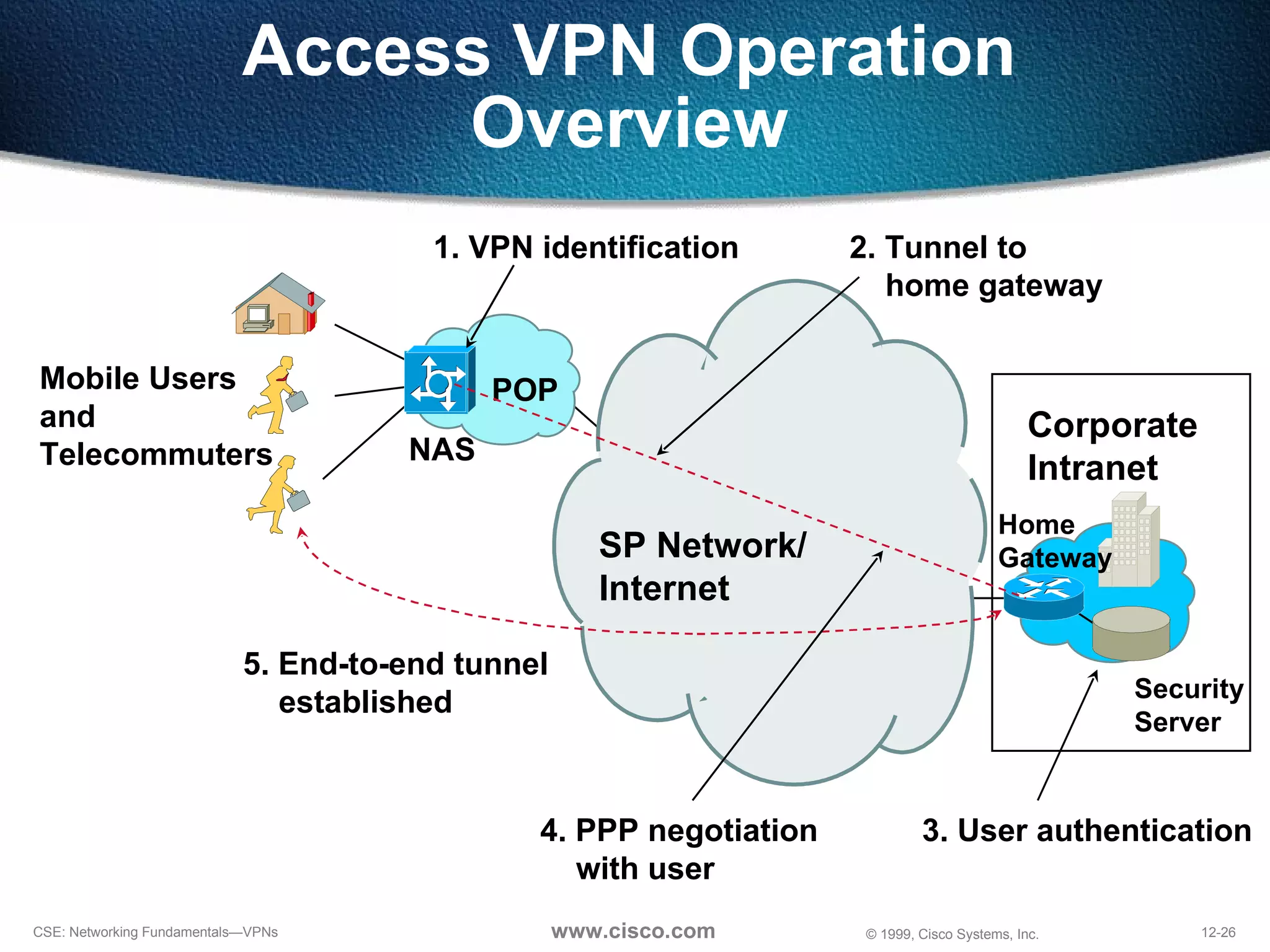
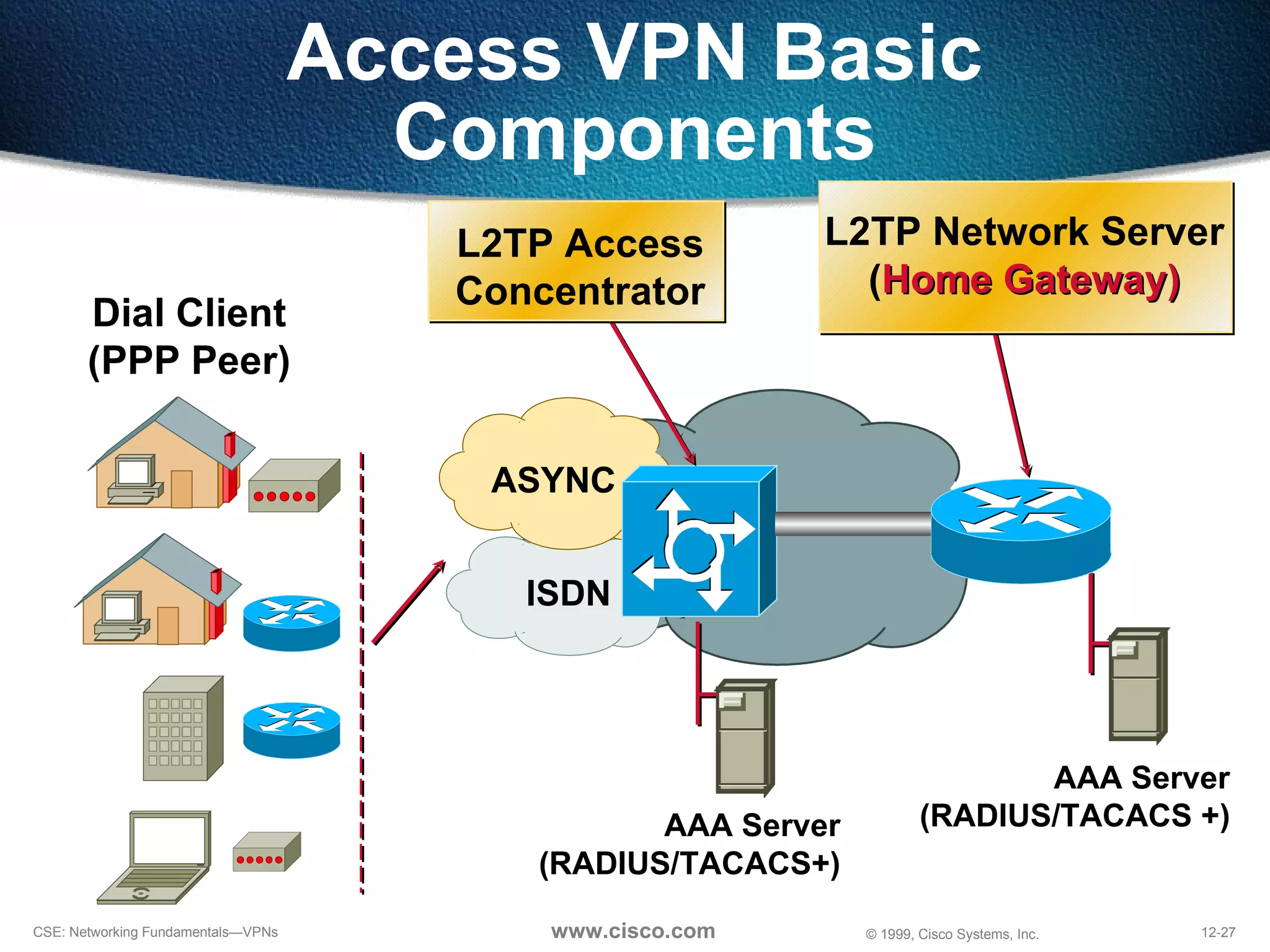
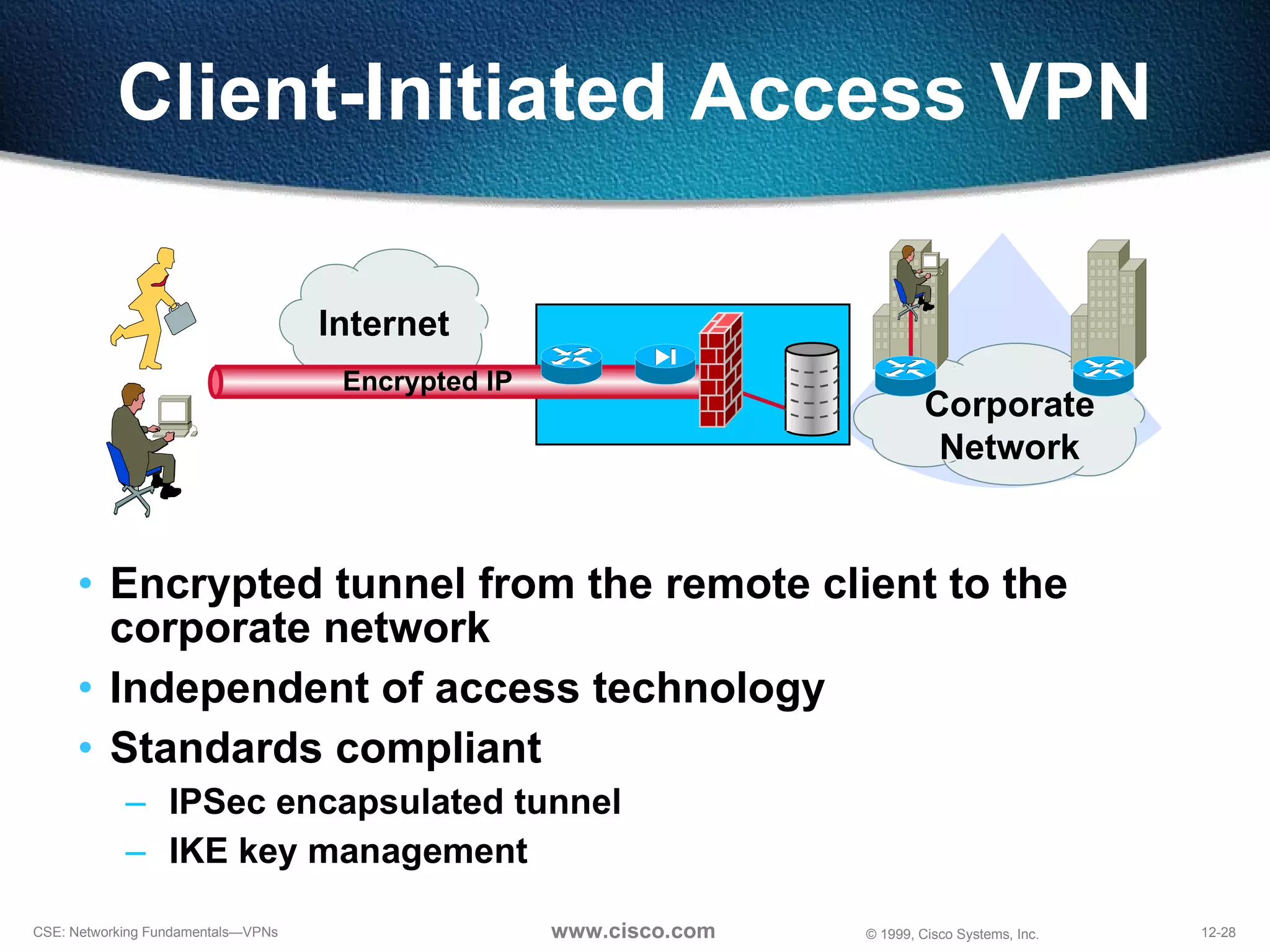
VPNs extend private networks over shared public infrastructure like the internet. They use encryption and tunneling to securely connect multiple sites including remote offices, mobile users, and business partners. Common VPN technologies include IPSec, L2TP, PPTP, and SSL which provide security while tunneling non-IP traffic. VPNs lower networking costs compared to private WANs and facilitate remote access and extranet connections with better performance than traditional dial-up.
![NAS-Initiated Access VPN NAS [email_address] Home Gateway IP Network](https://image.slidesharecdn.com/12-understanding-vpns-120201235007-phpapp01/75/Acit-Mumbai-understanding-vpns-30-2048.jpg)