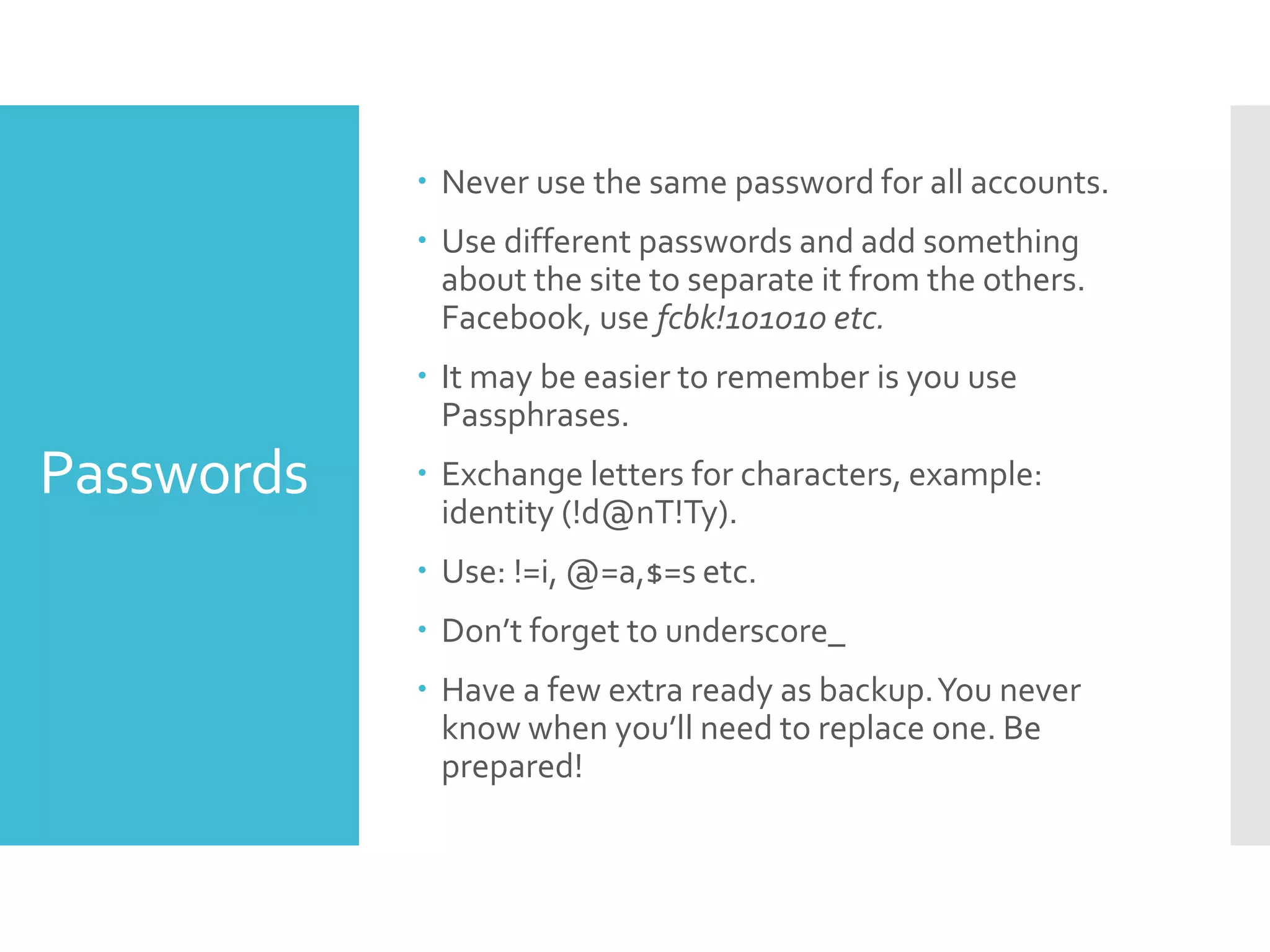
This document provides a comprehensive guide for safely surfing the internet, emphasizing the protection of personal information from data brokers and identity thieves. It includes tips on using pseudonyms, secure tools like VPNs and secure browsers, and the importance of backing up data while practicing safe online habits. The guide encourages users to limit the disclosure of their real identities and to implement strong security measures across various online platforms.