Embed presentation
Download to read offline
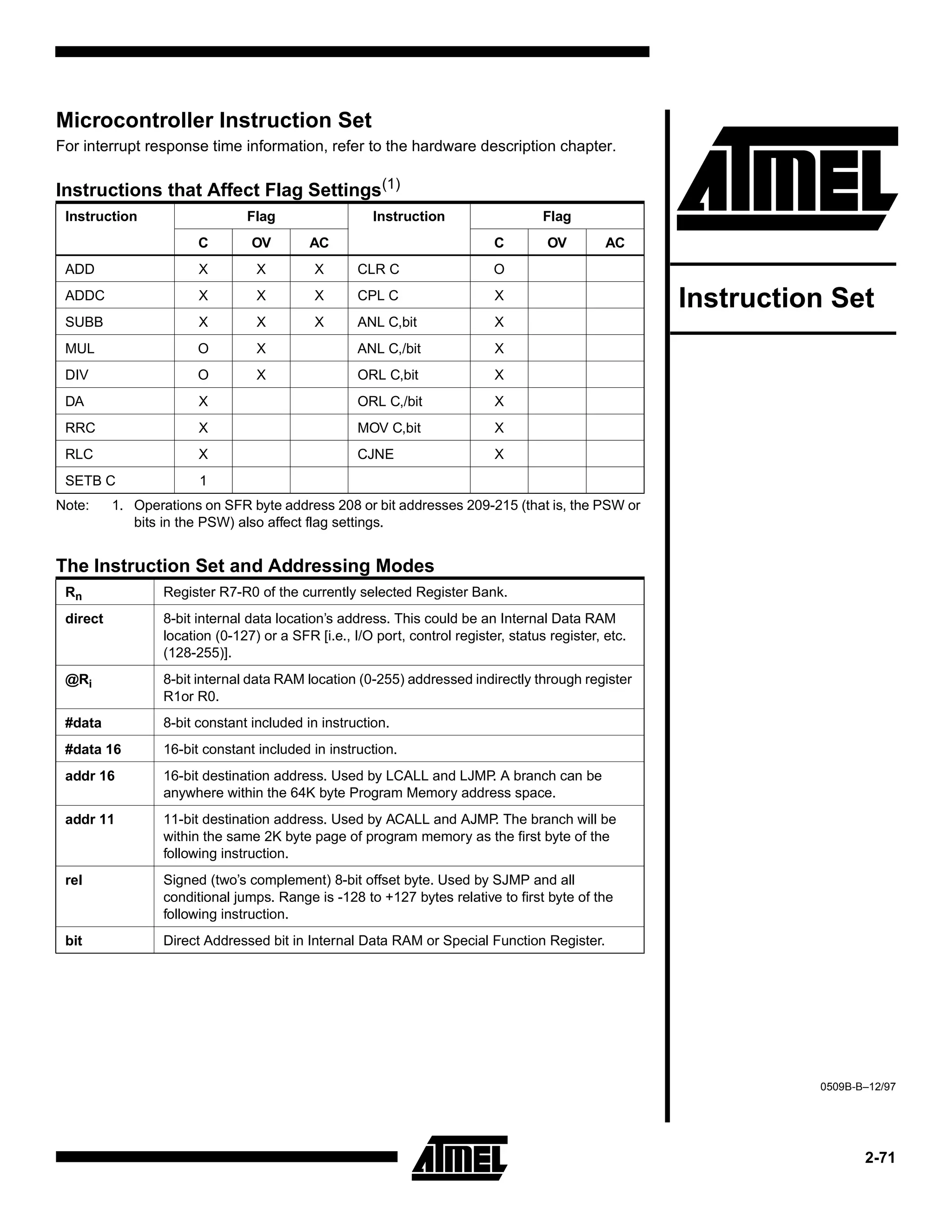
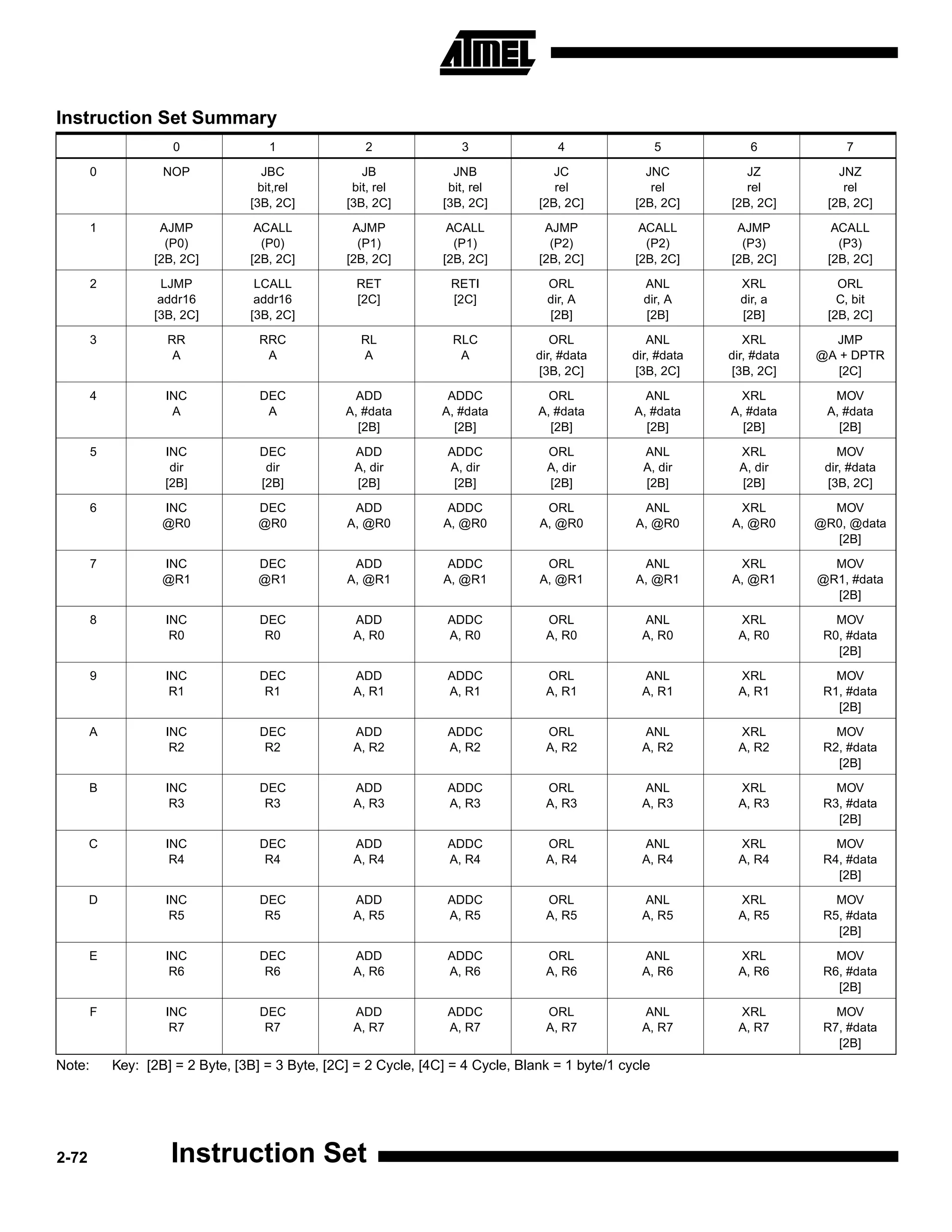
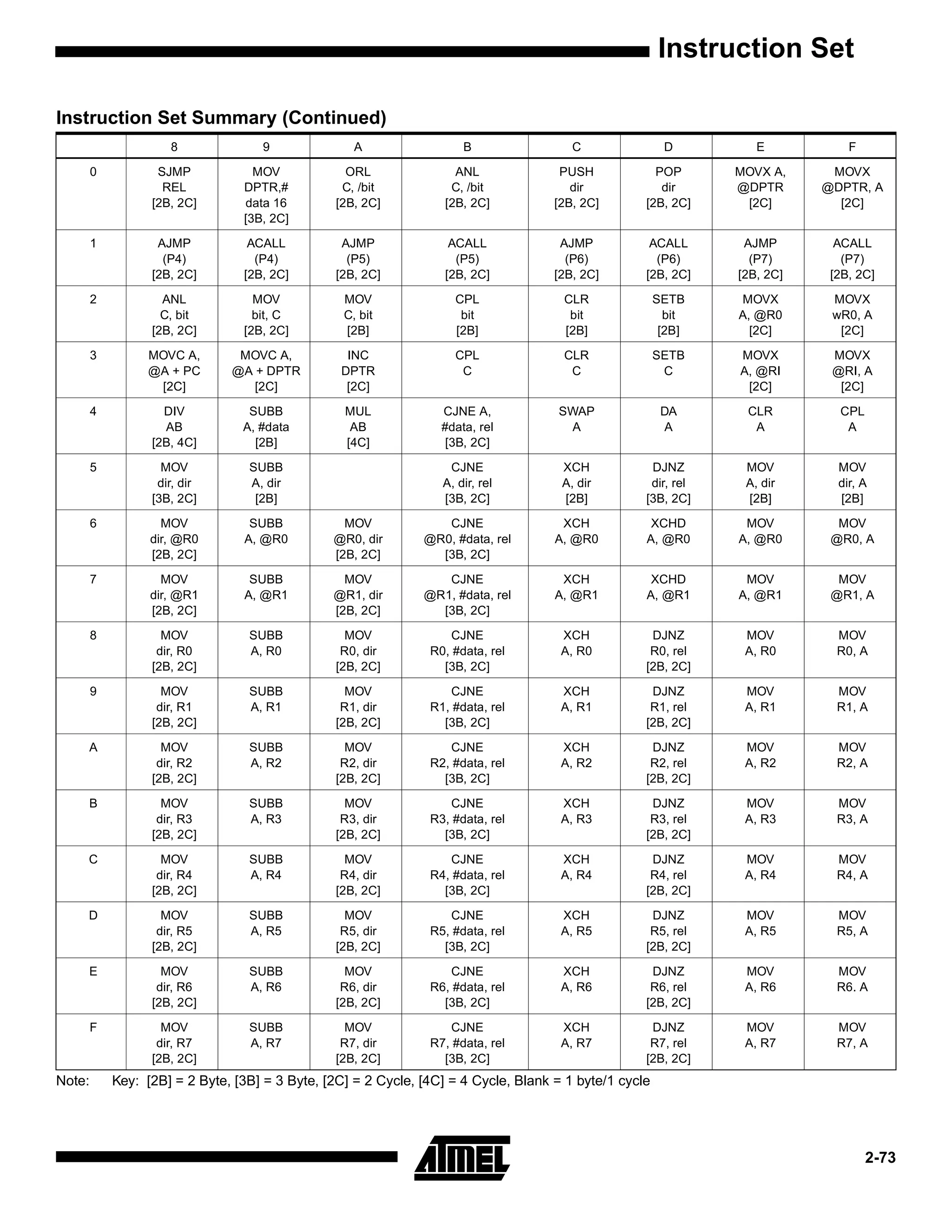
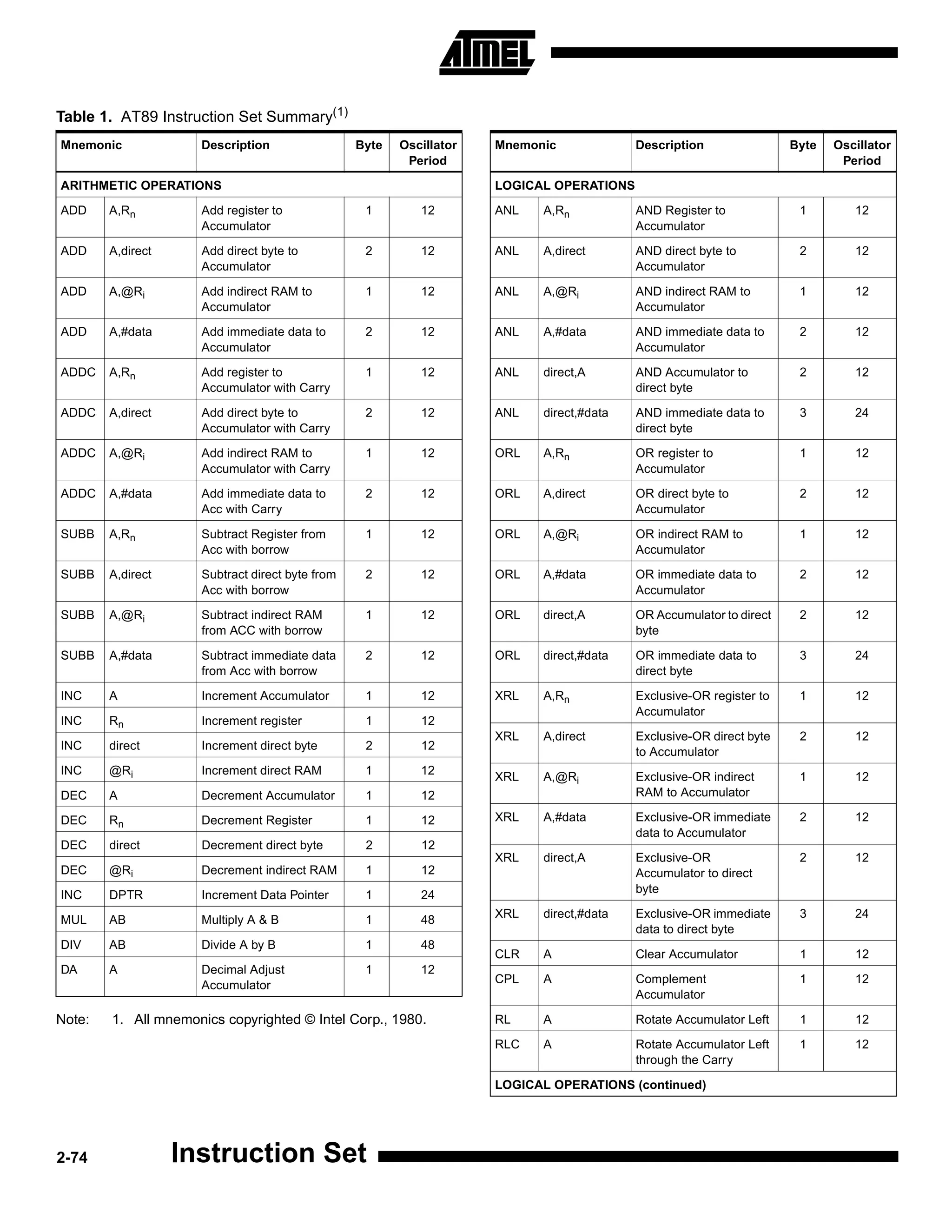
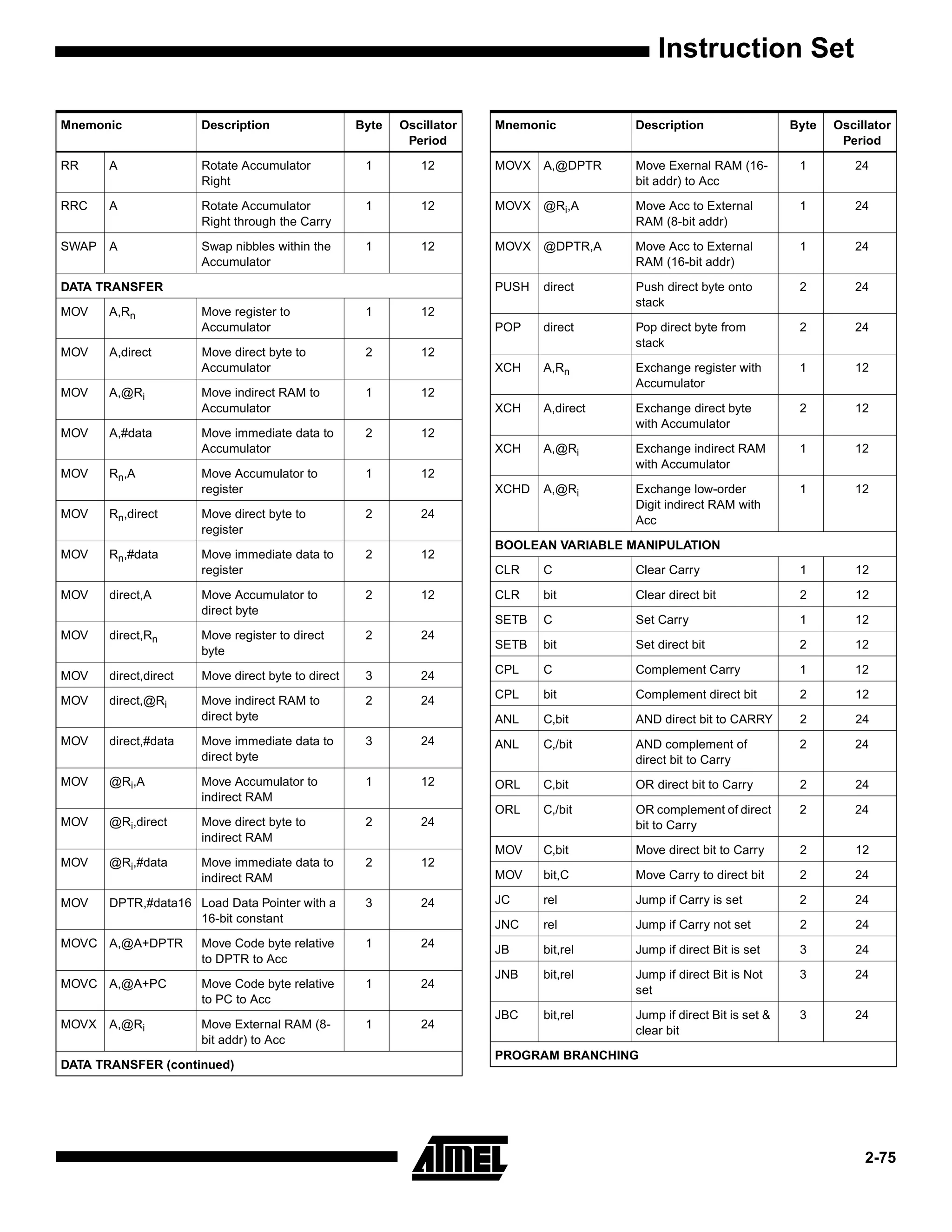
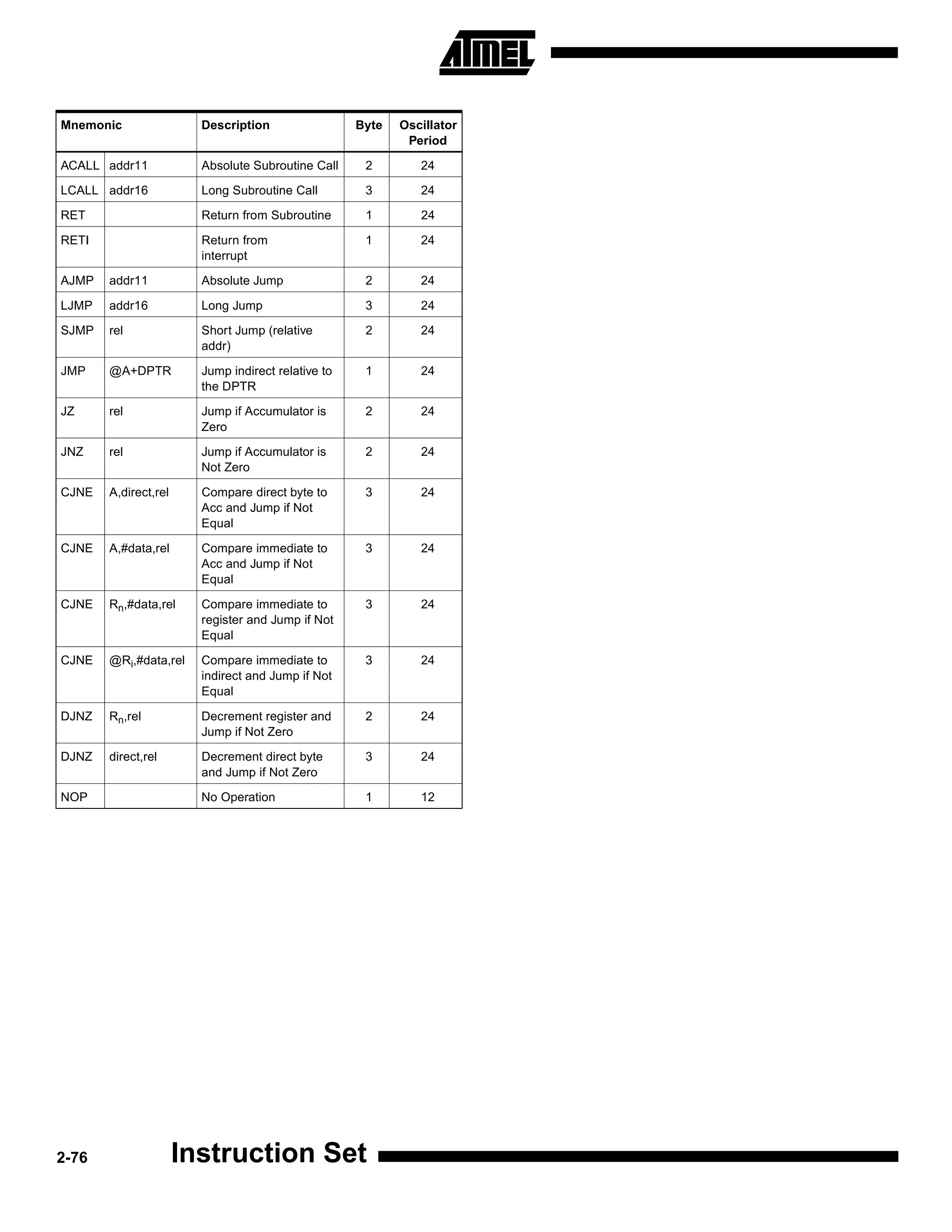
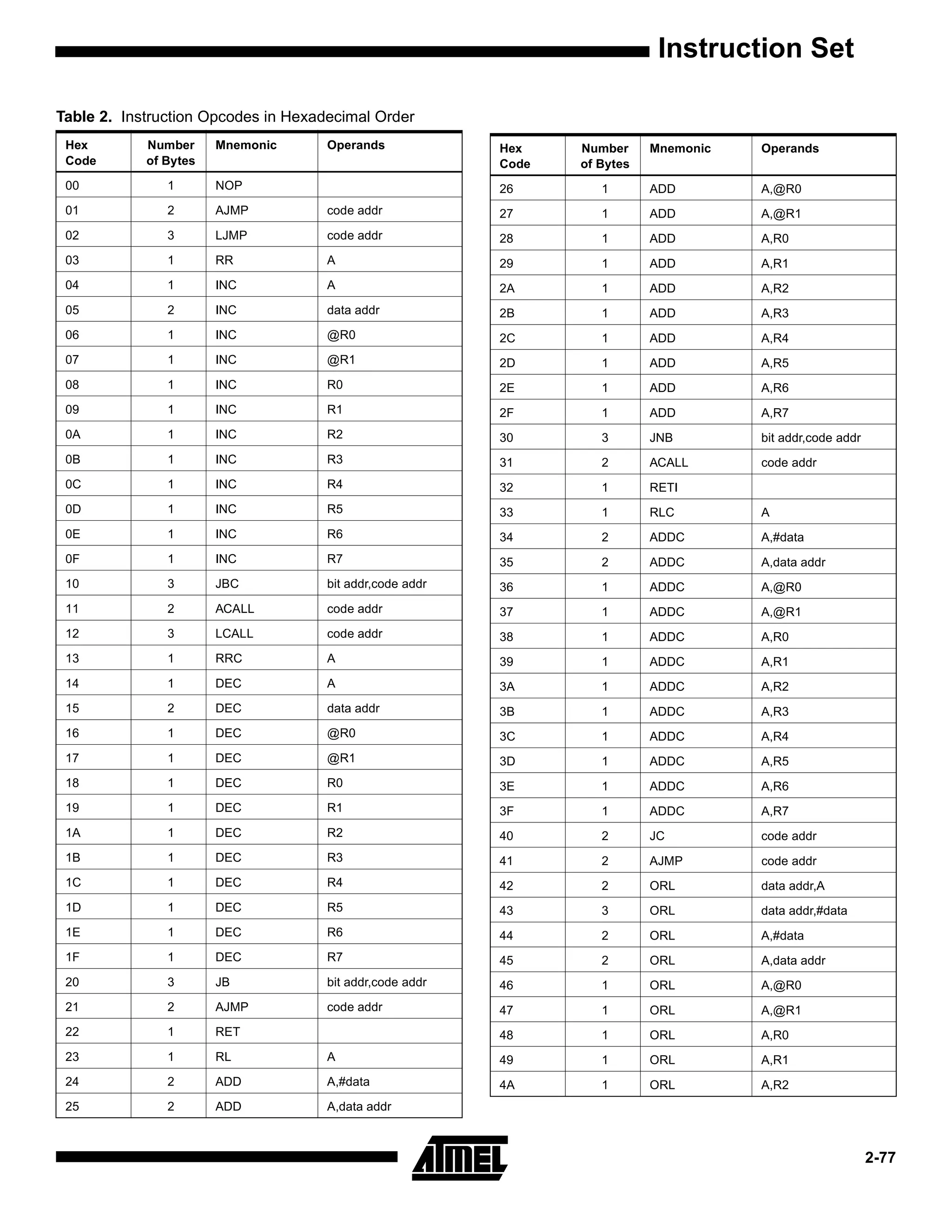
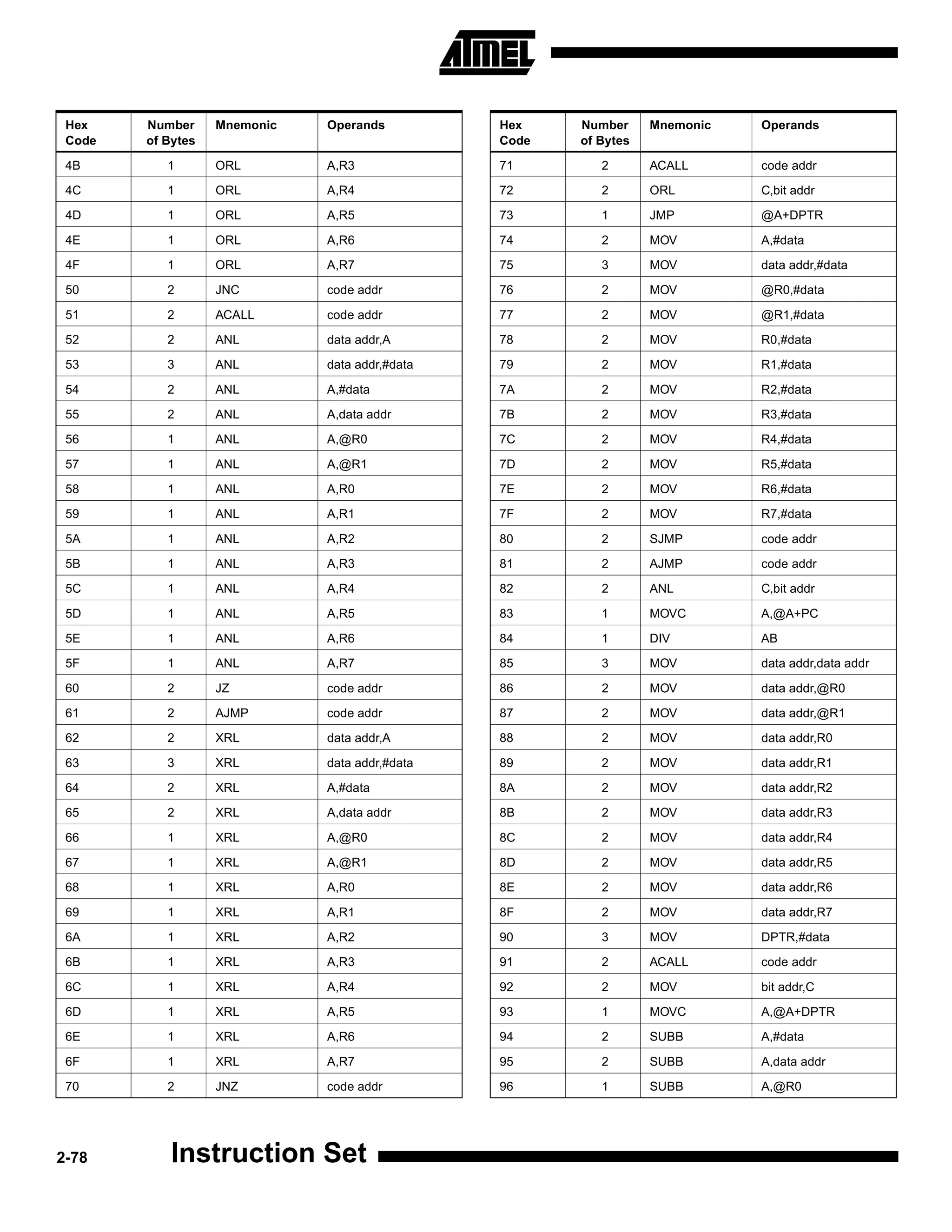
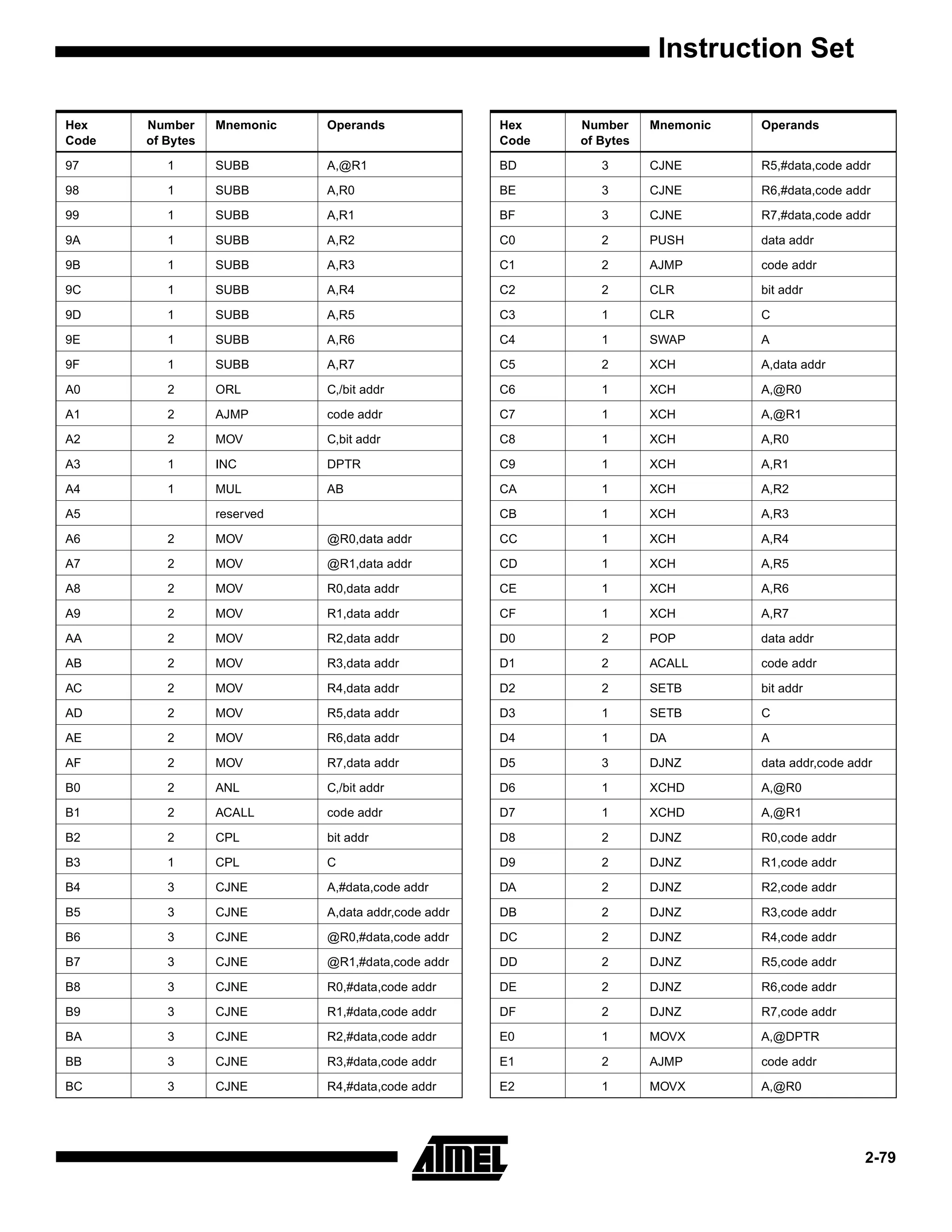
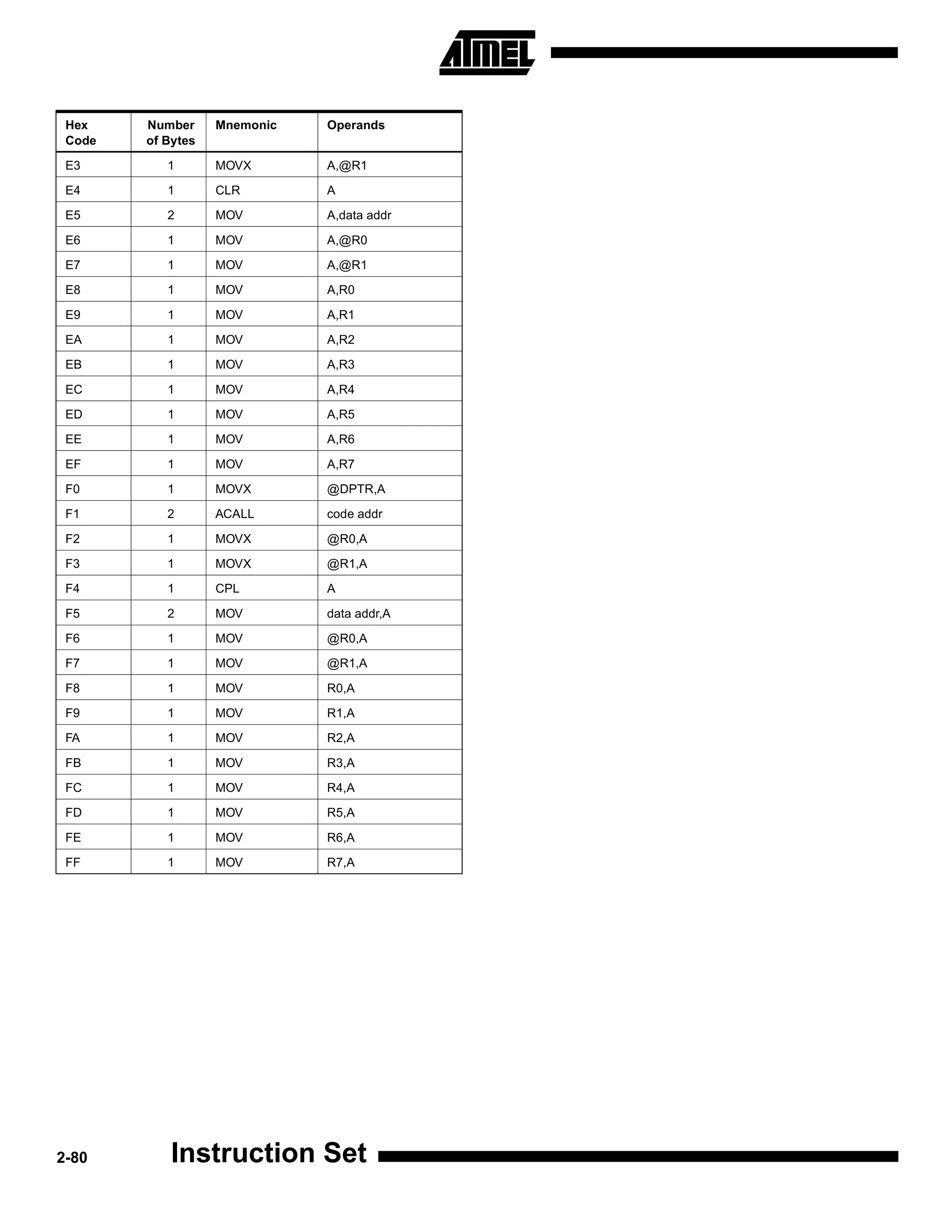
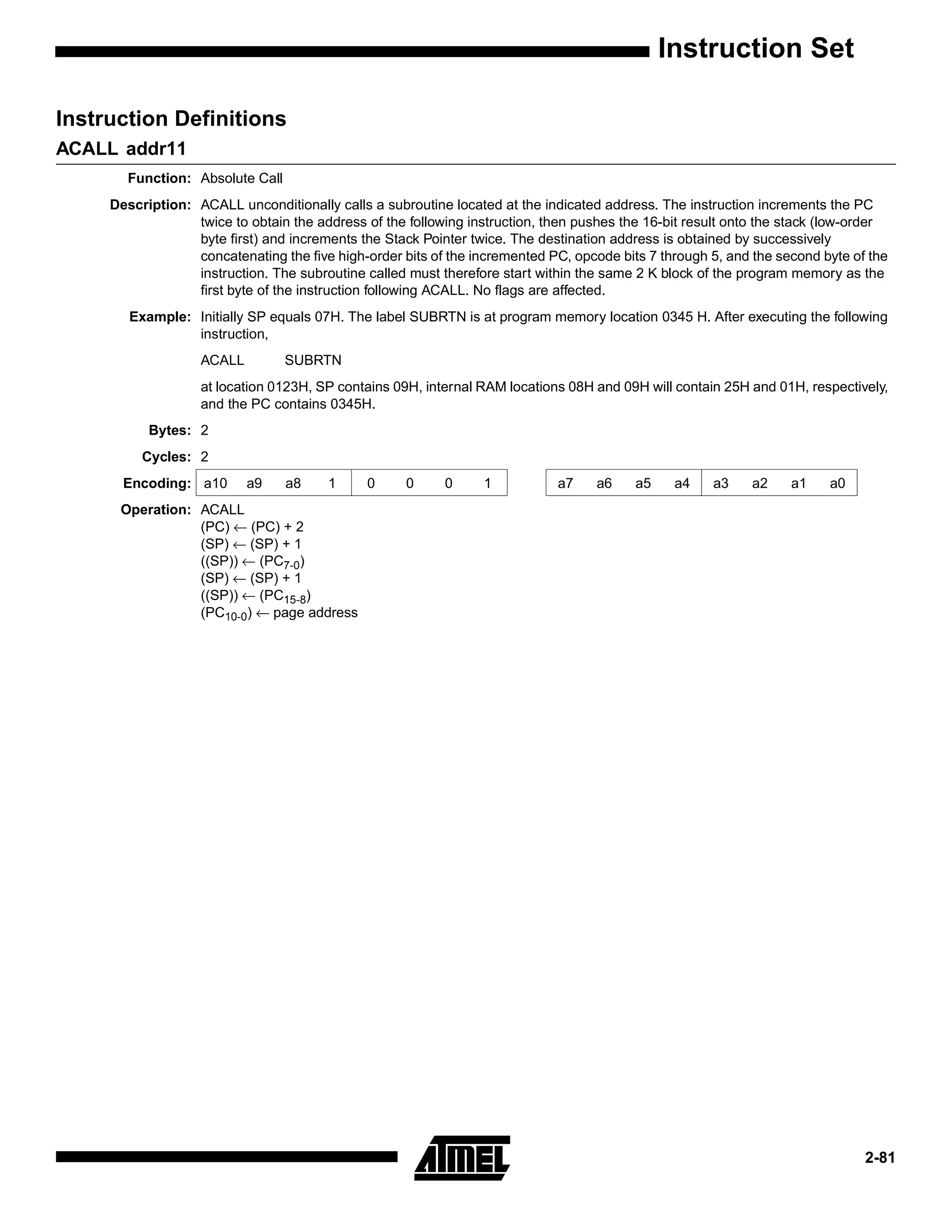
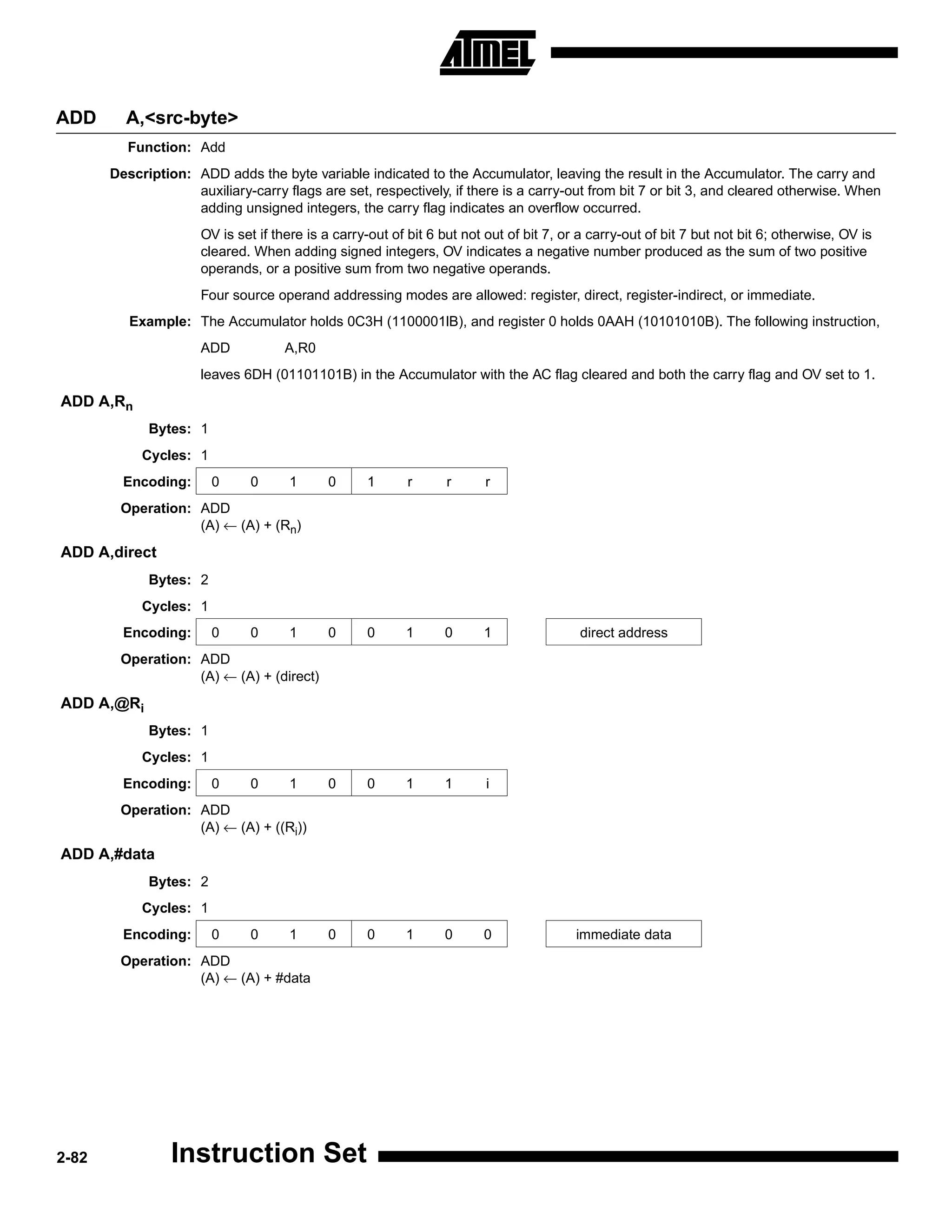
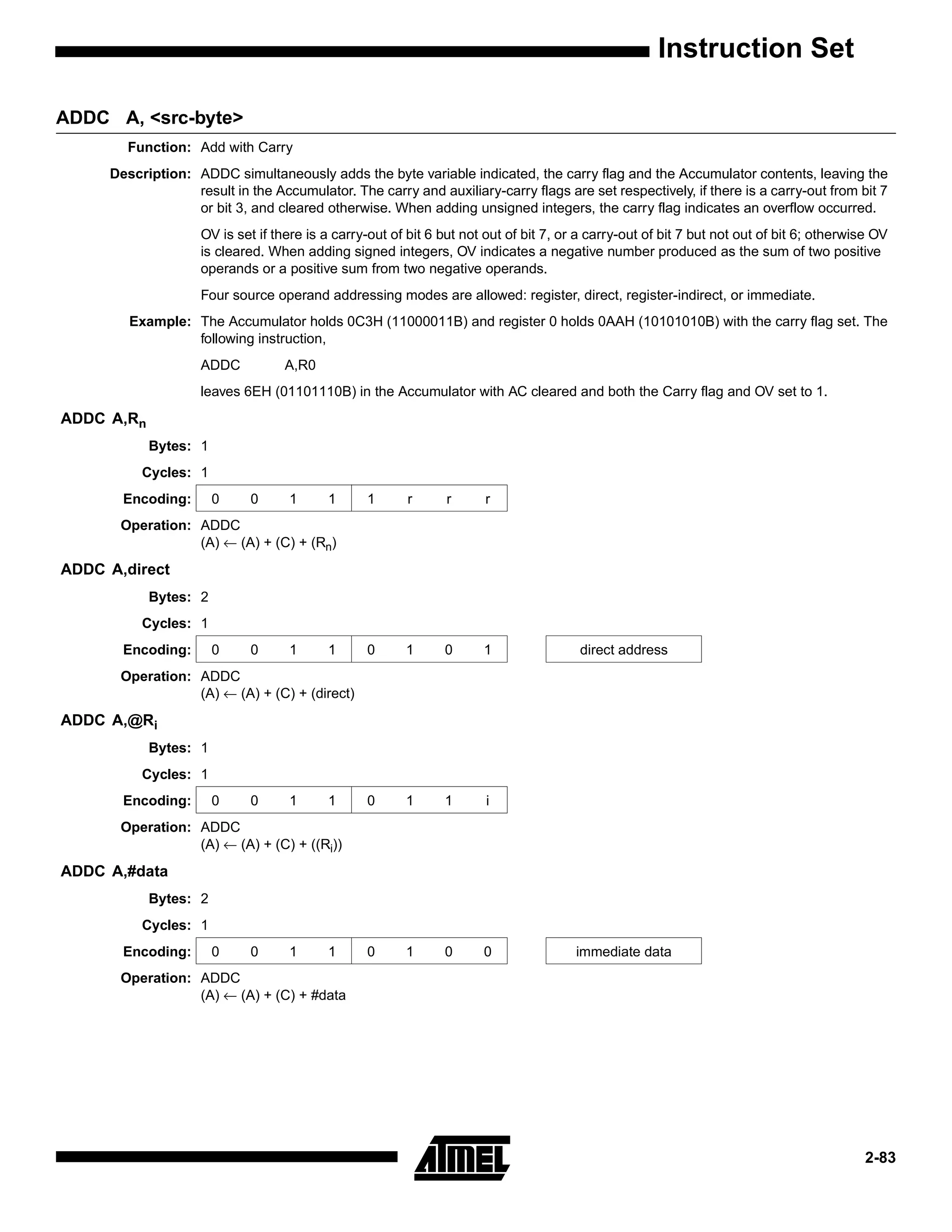
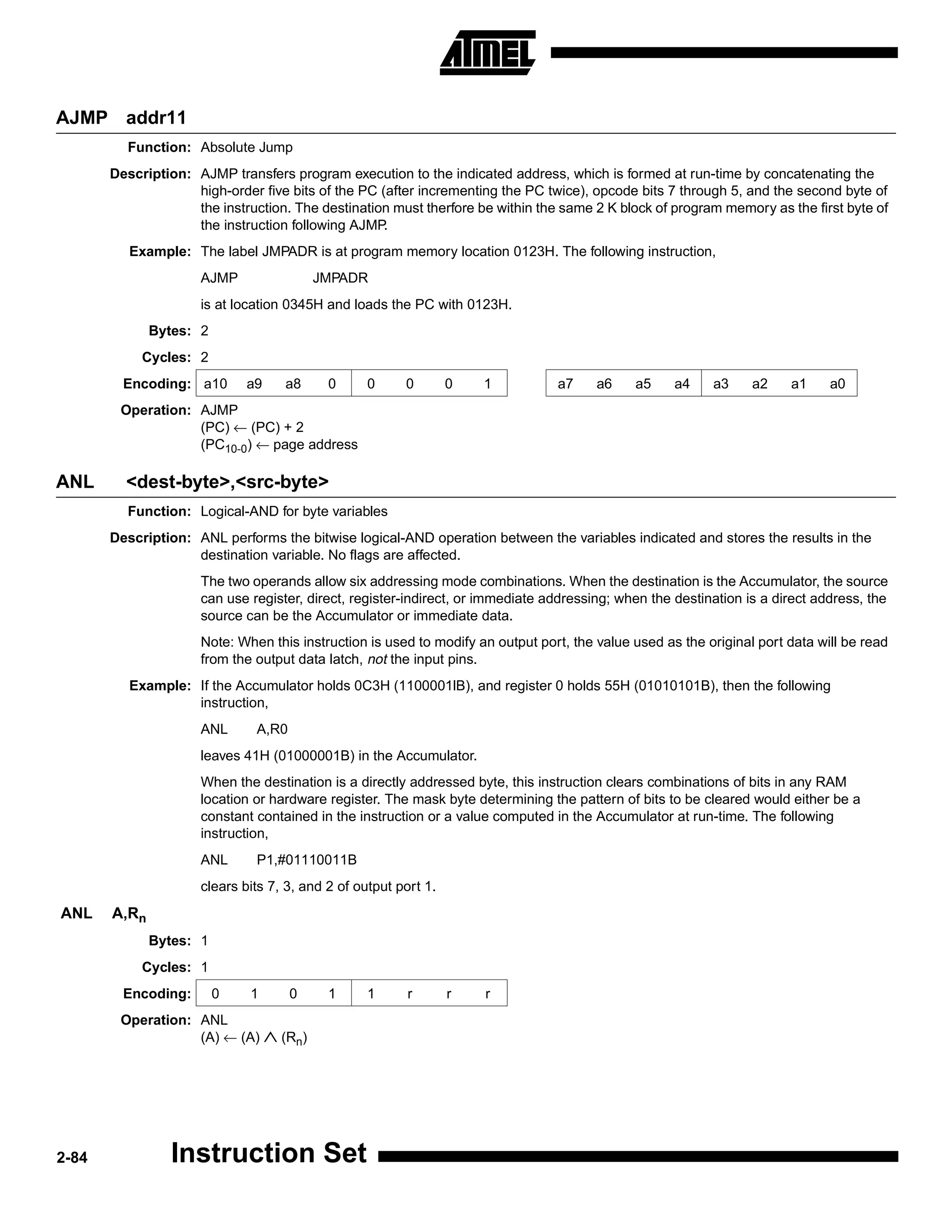
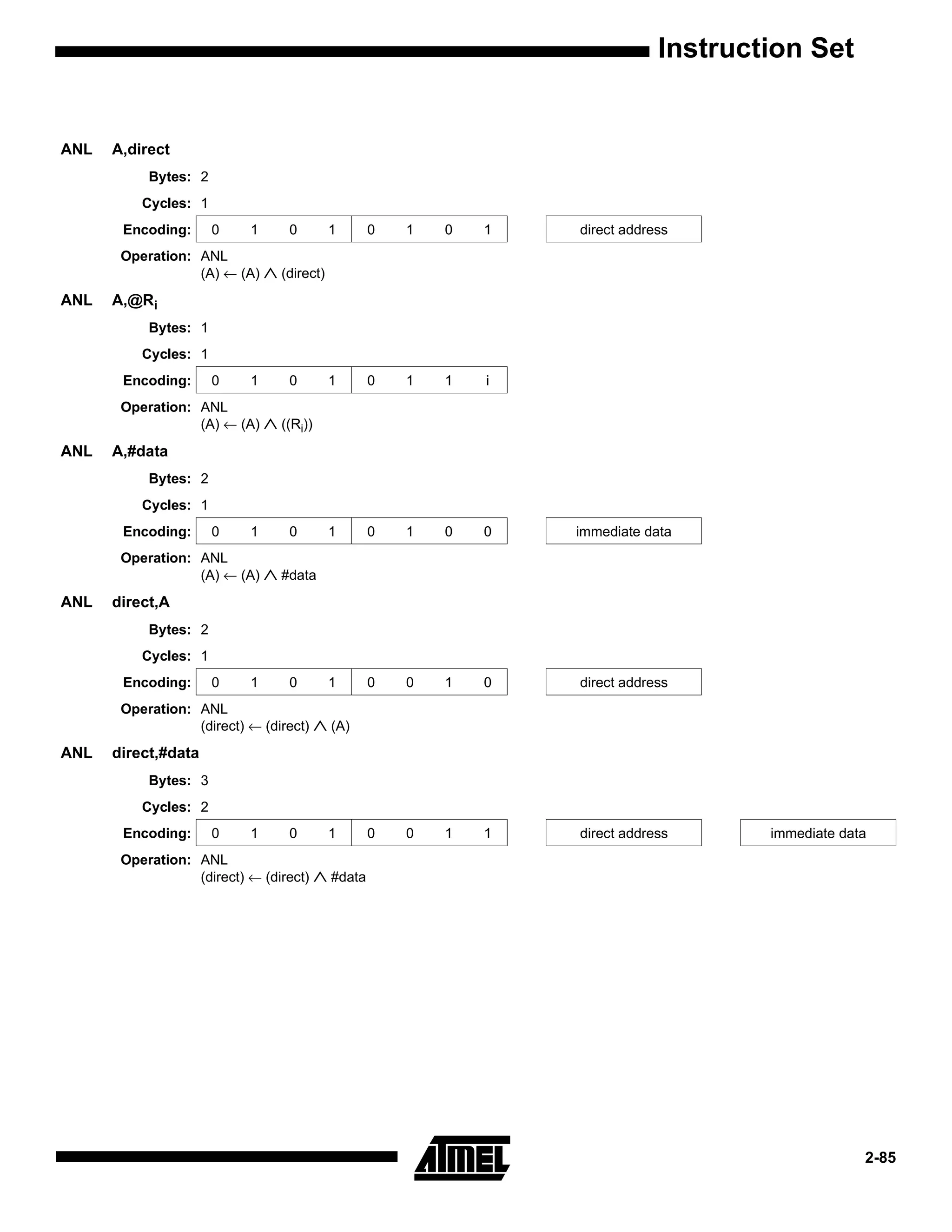
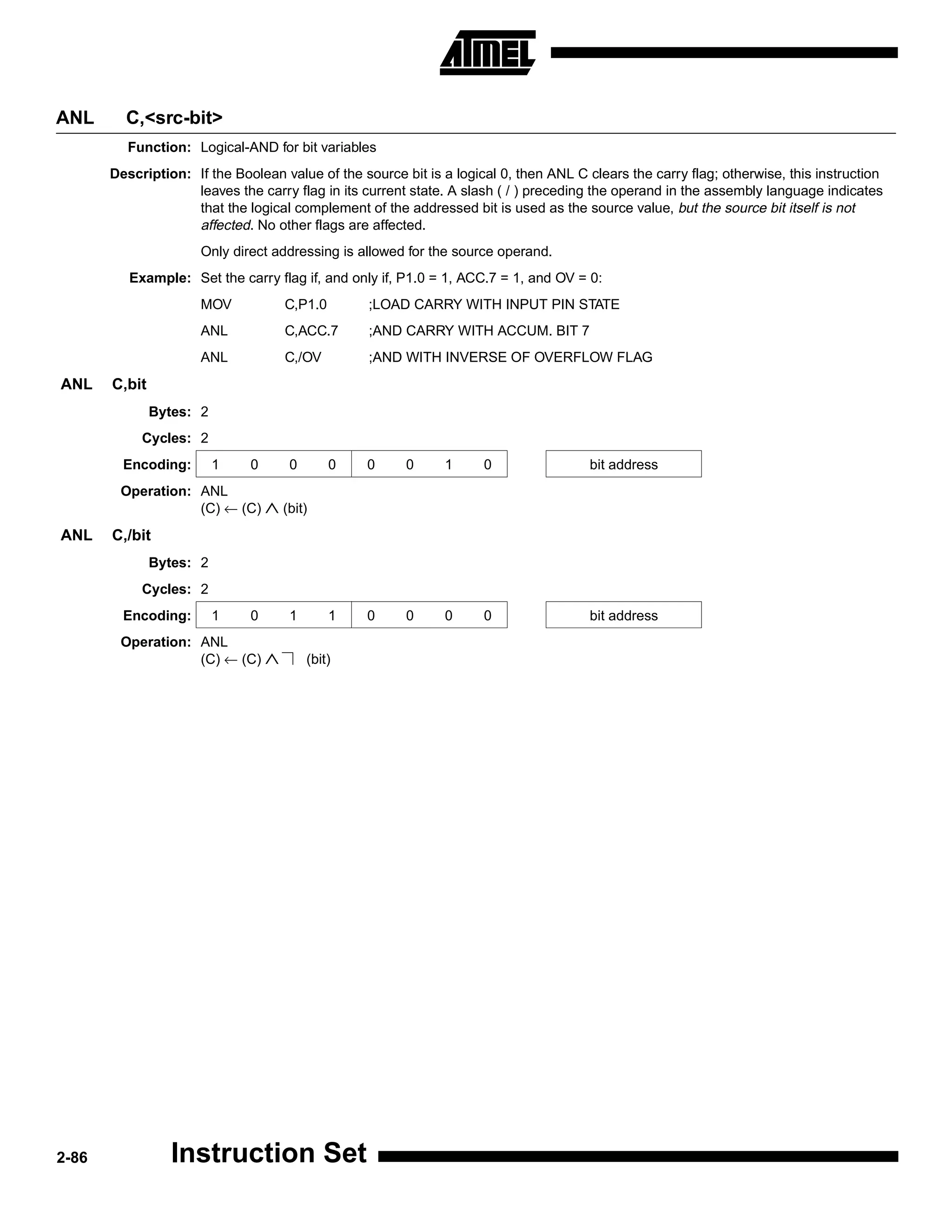
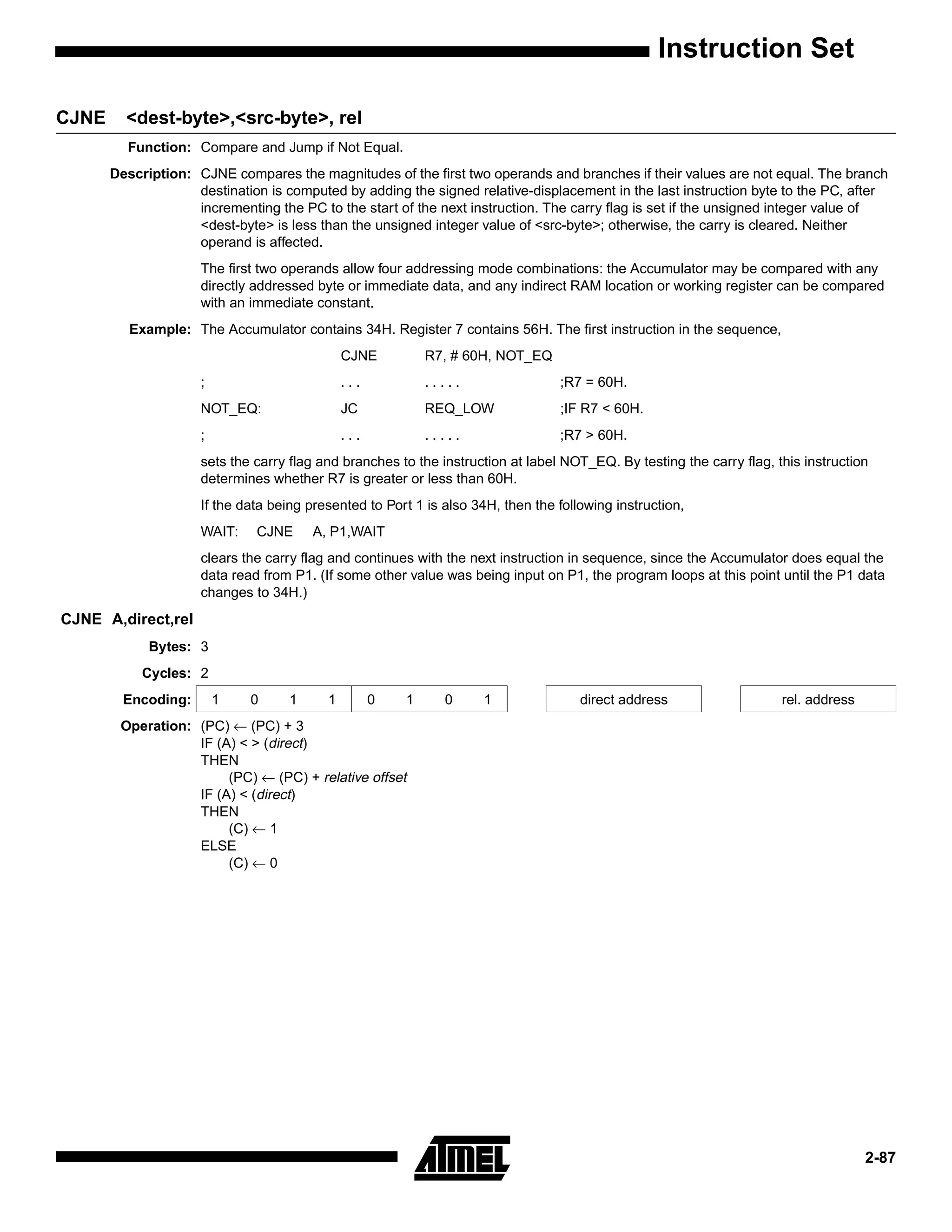
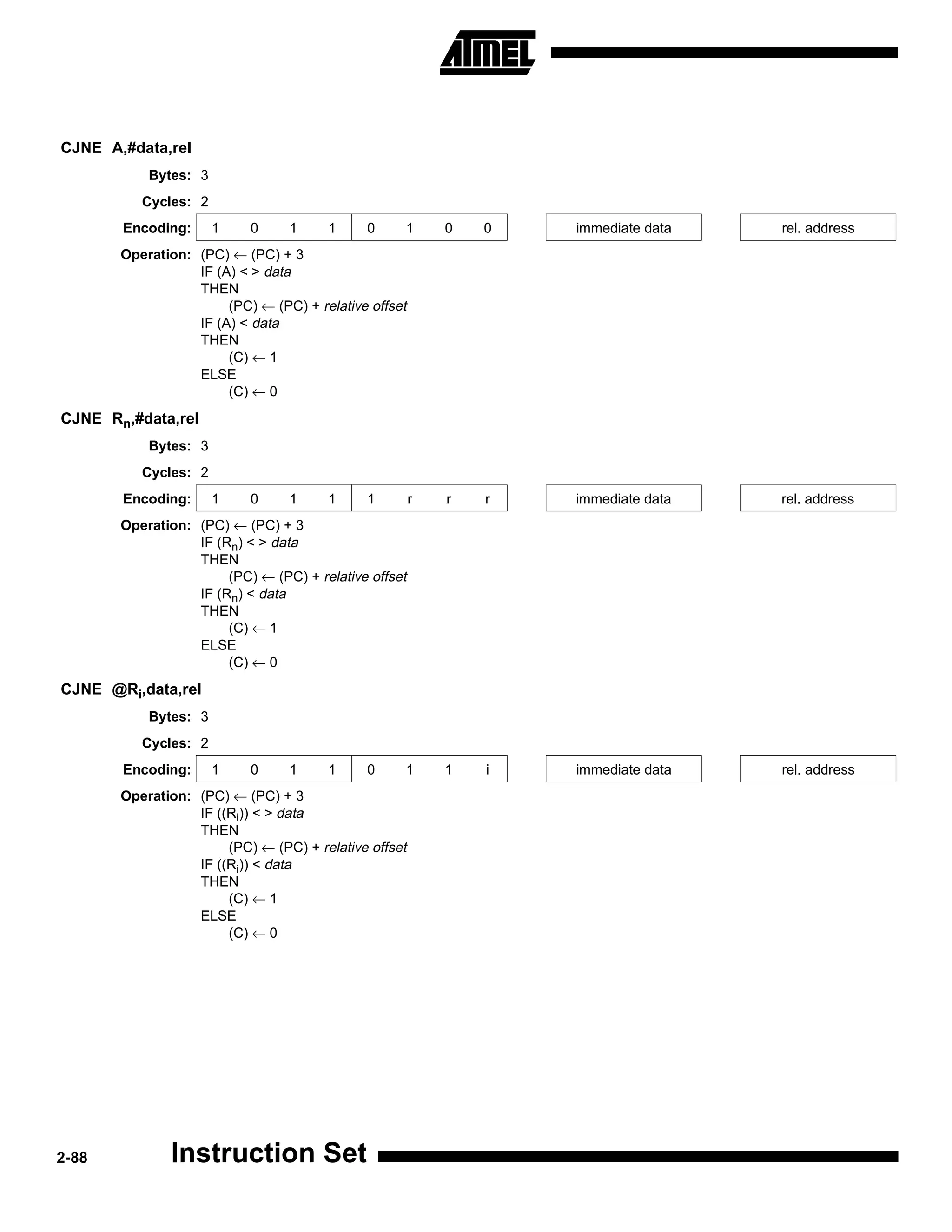
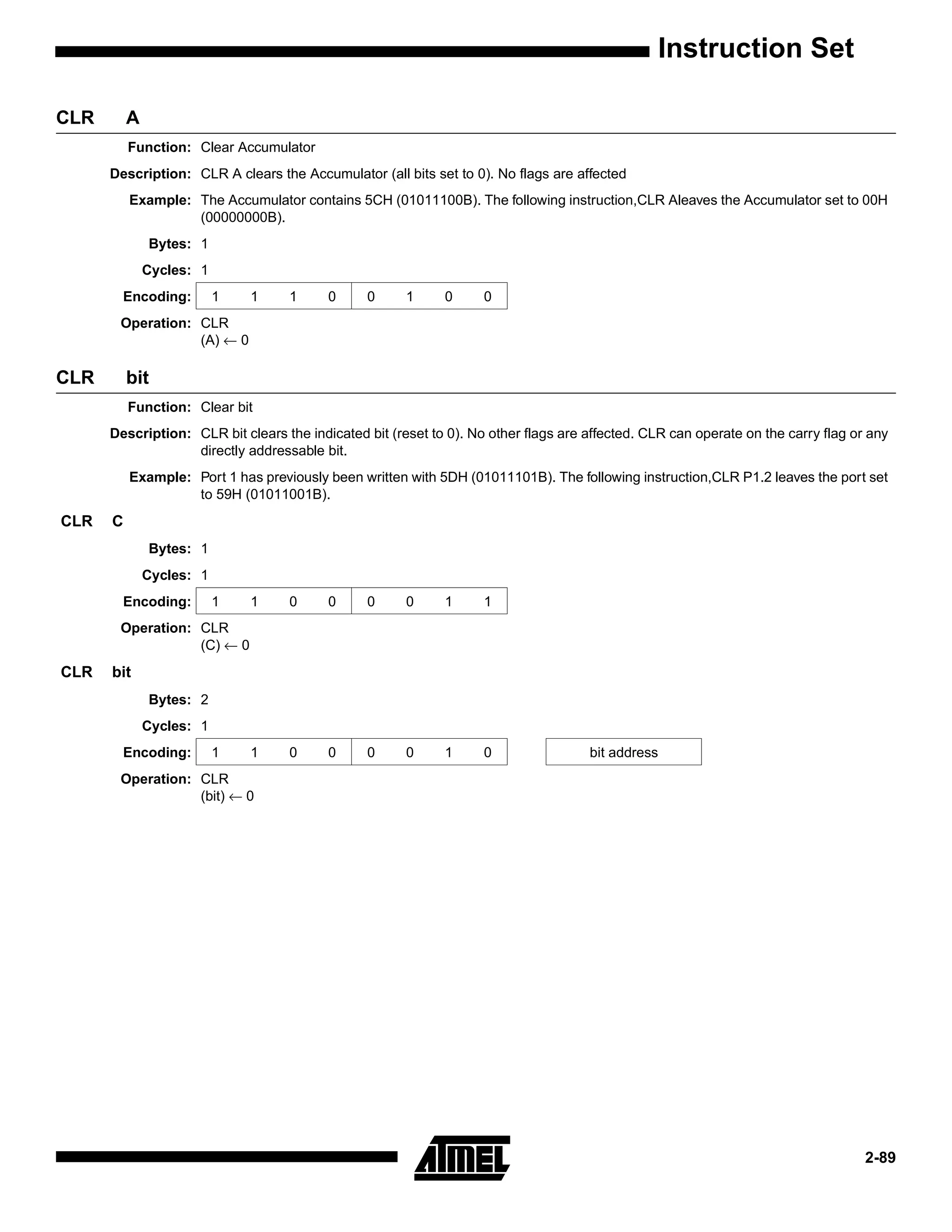
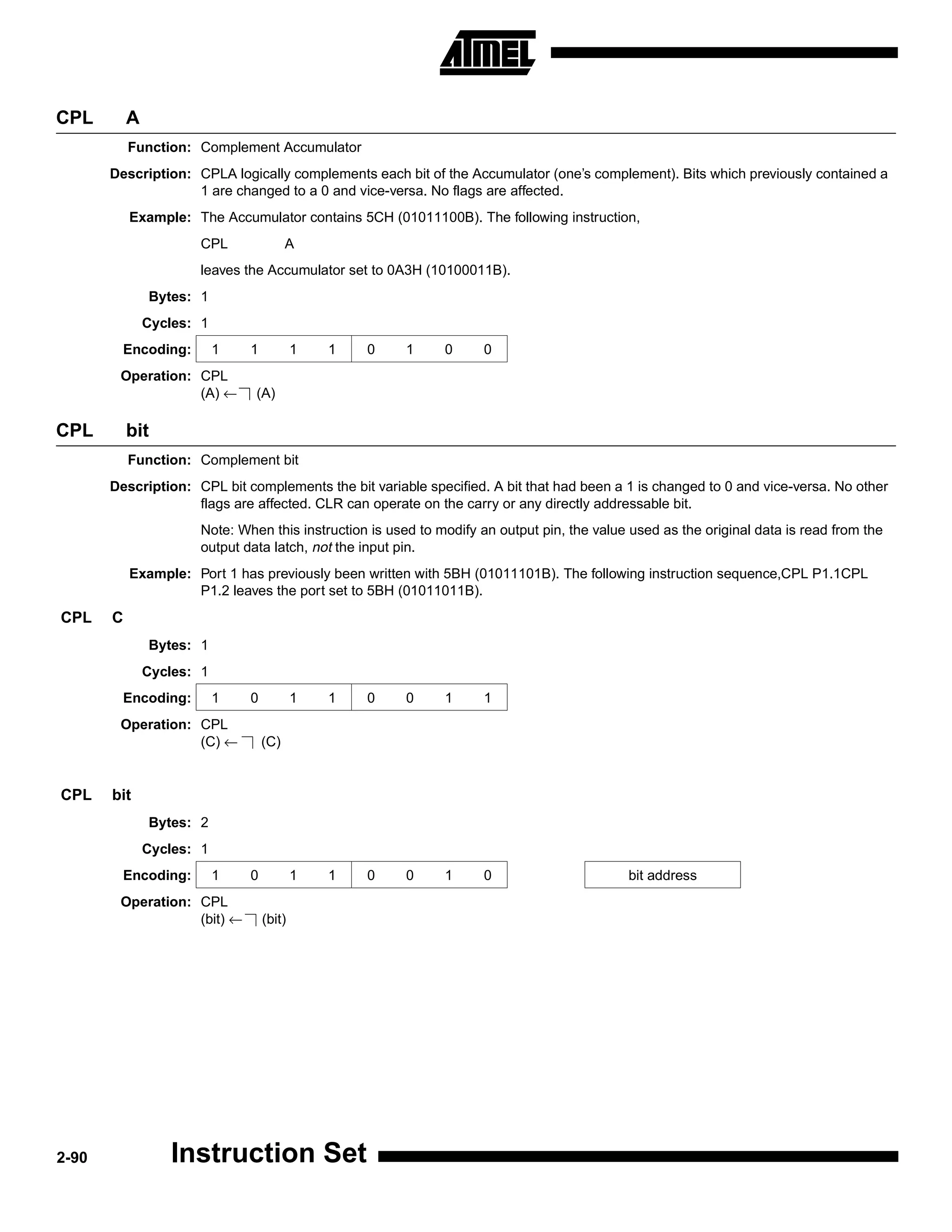
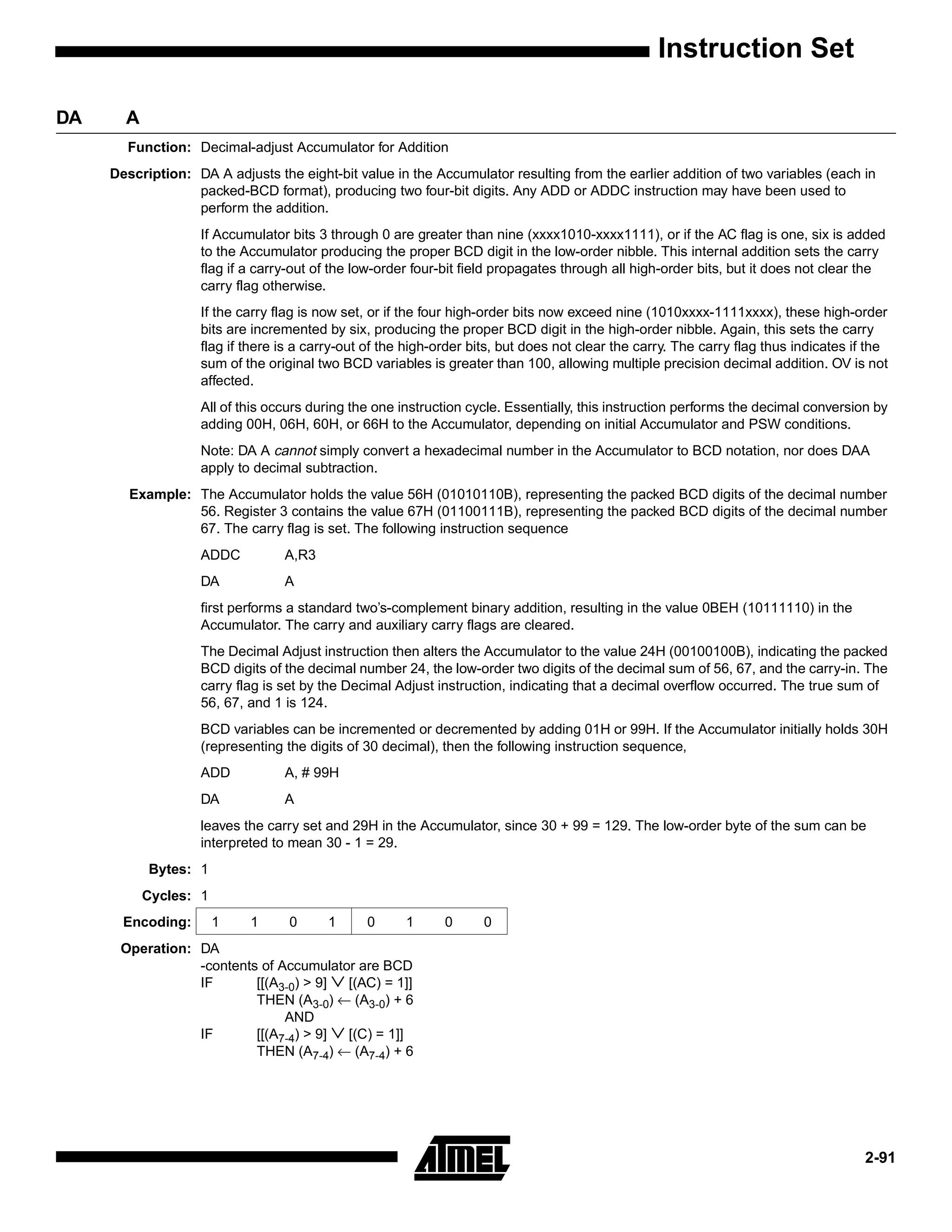
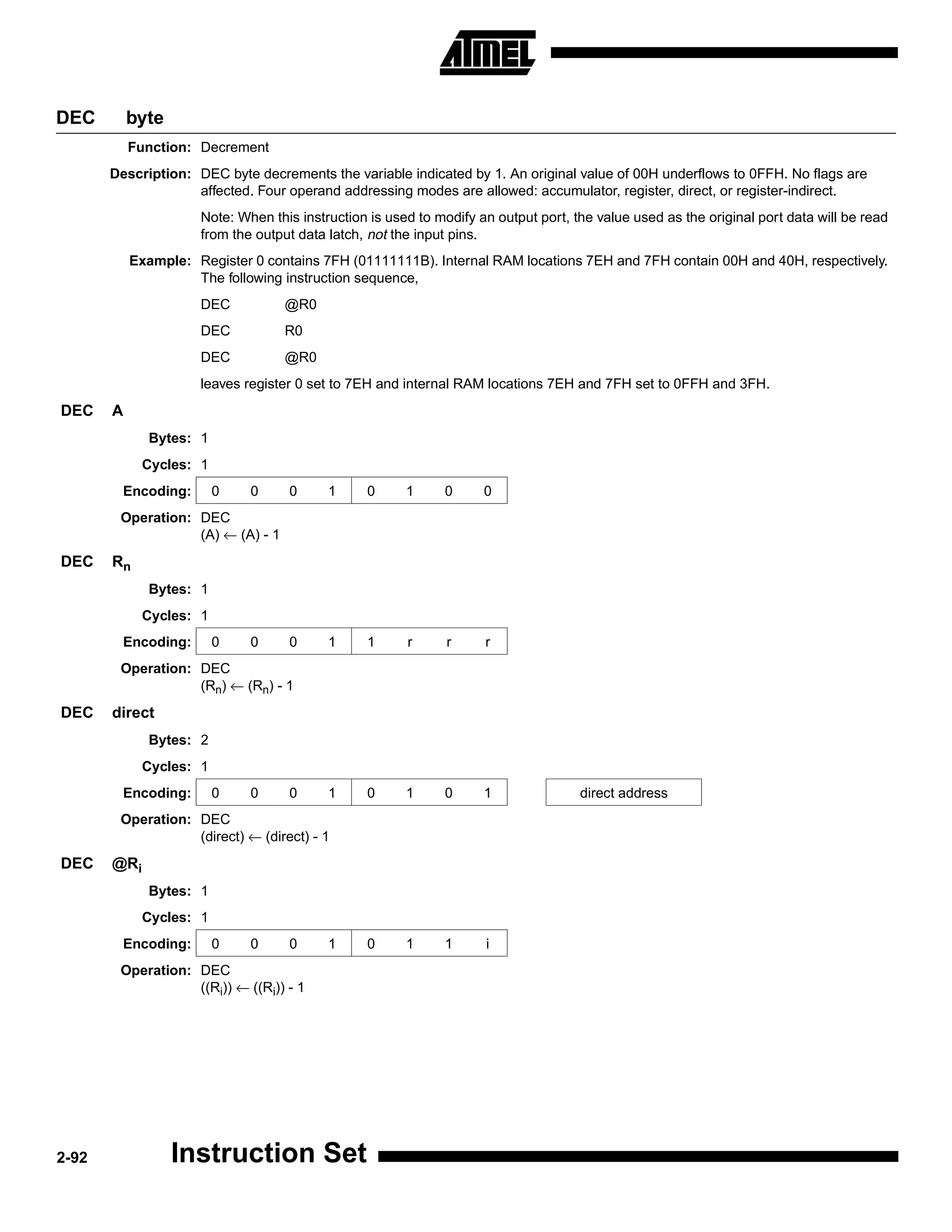
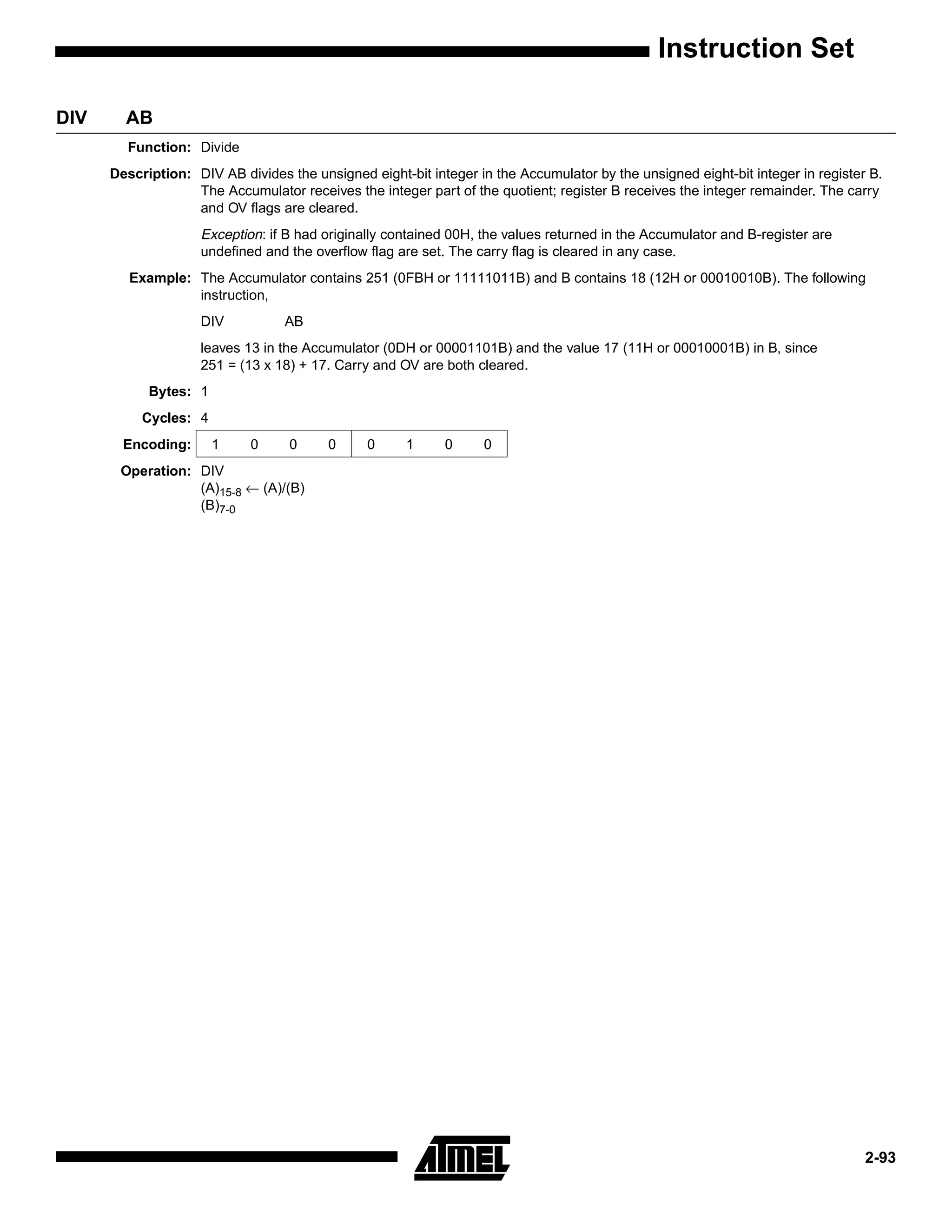
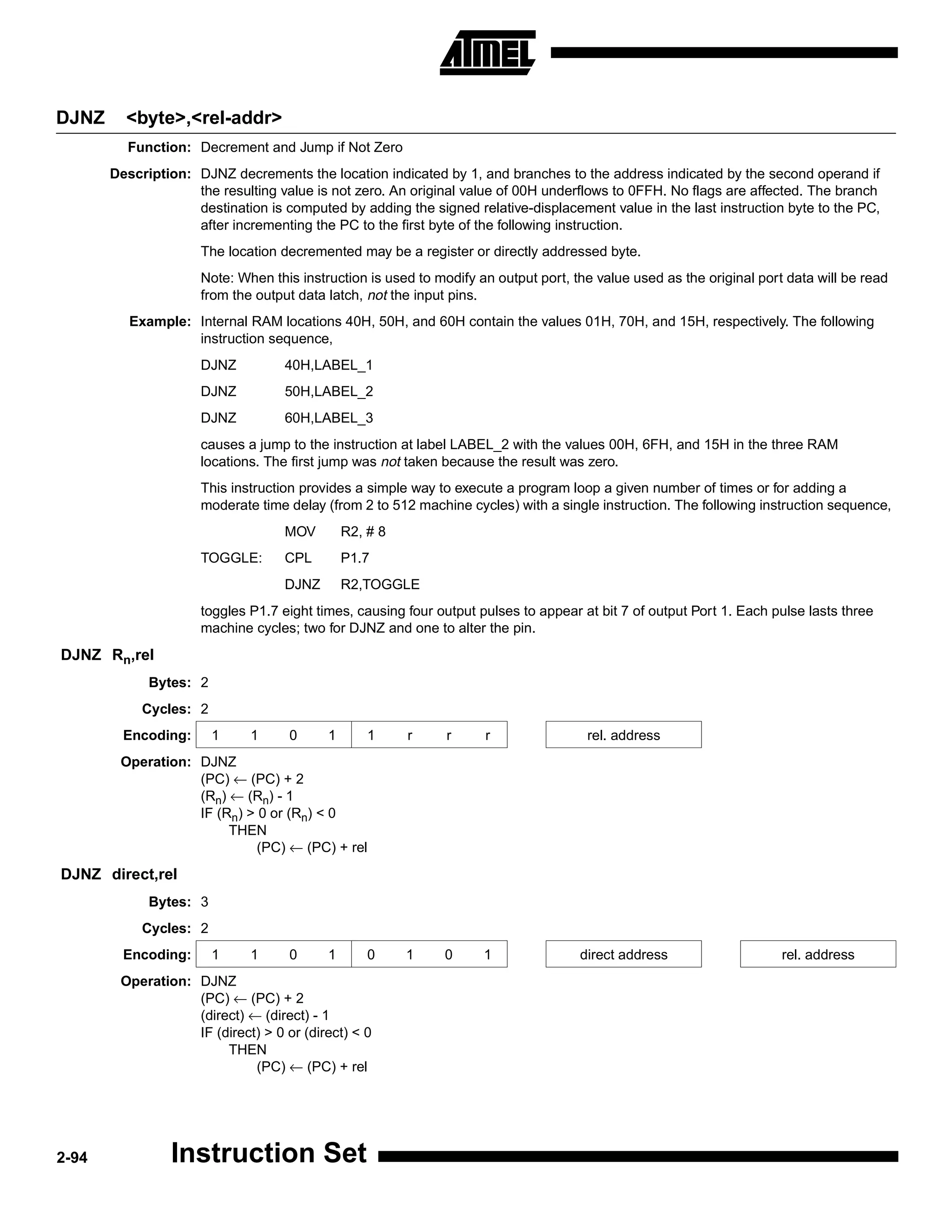
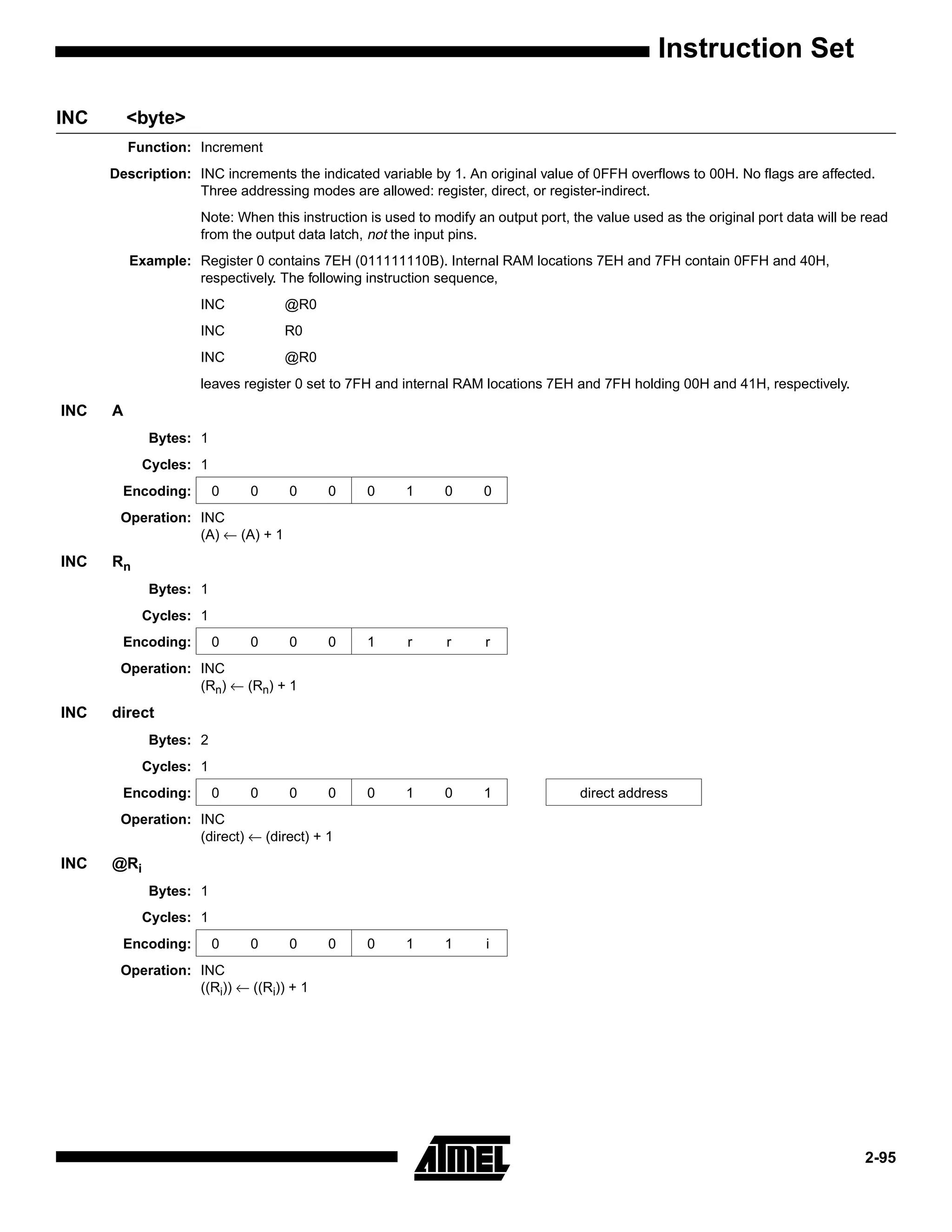
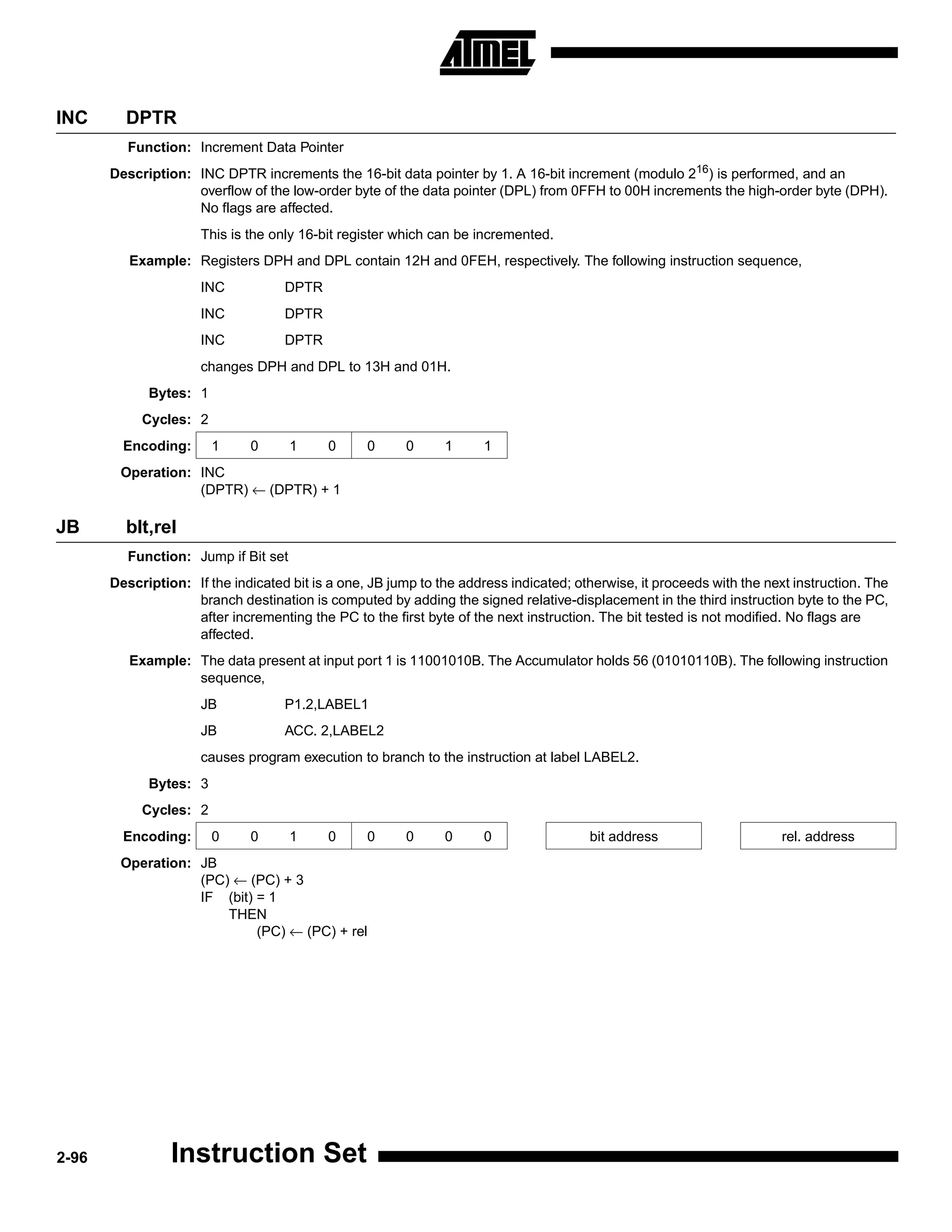
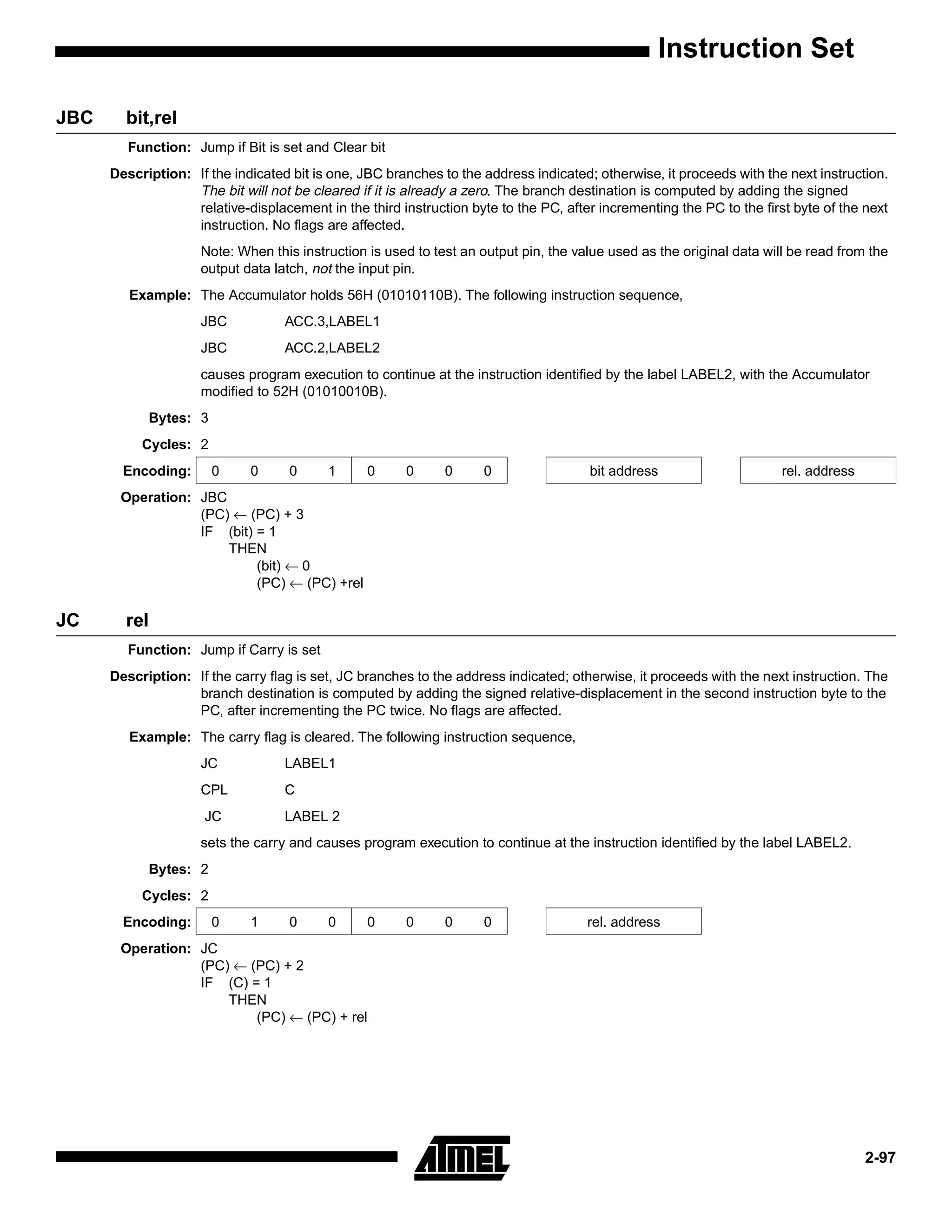
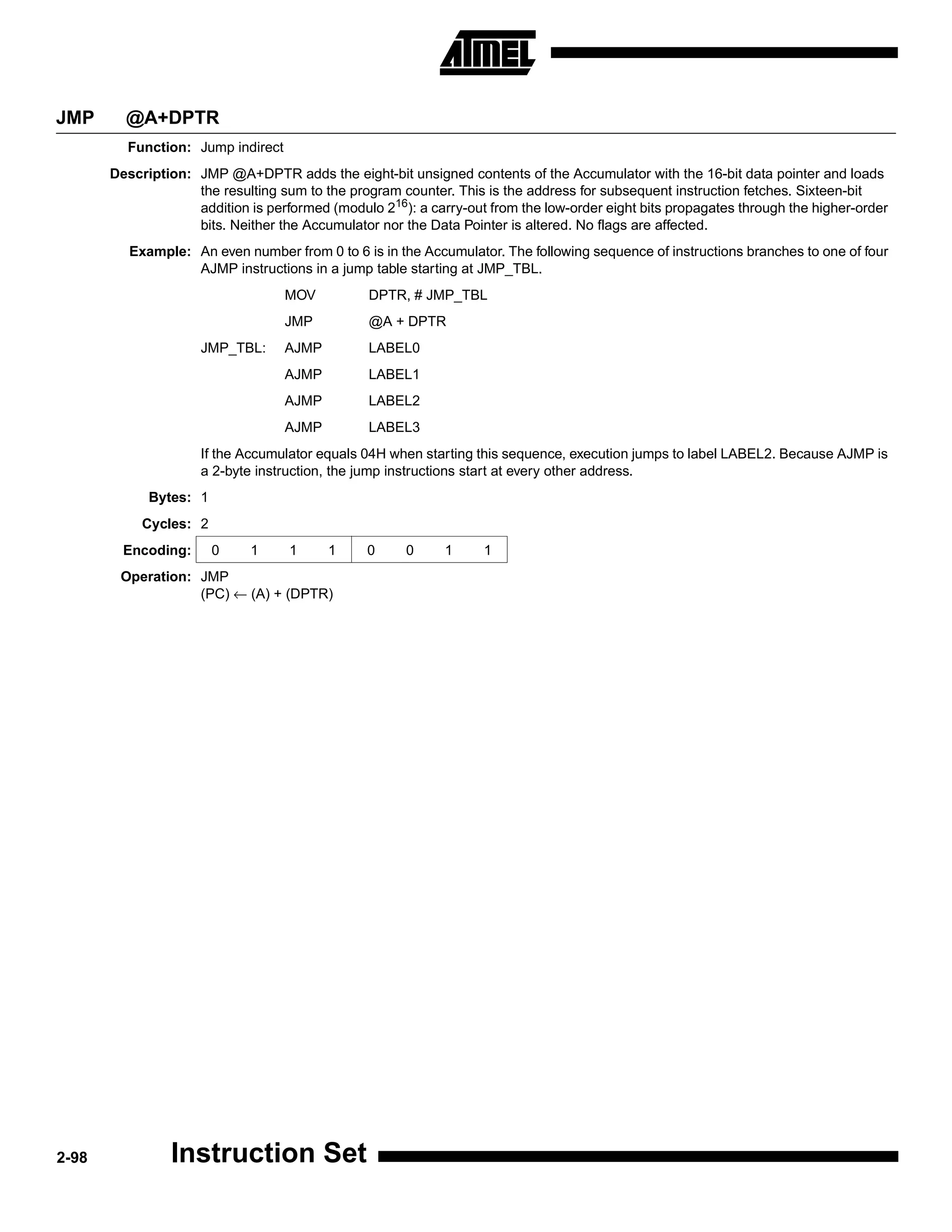

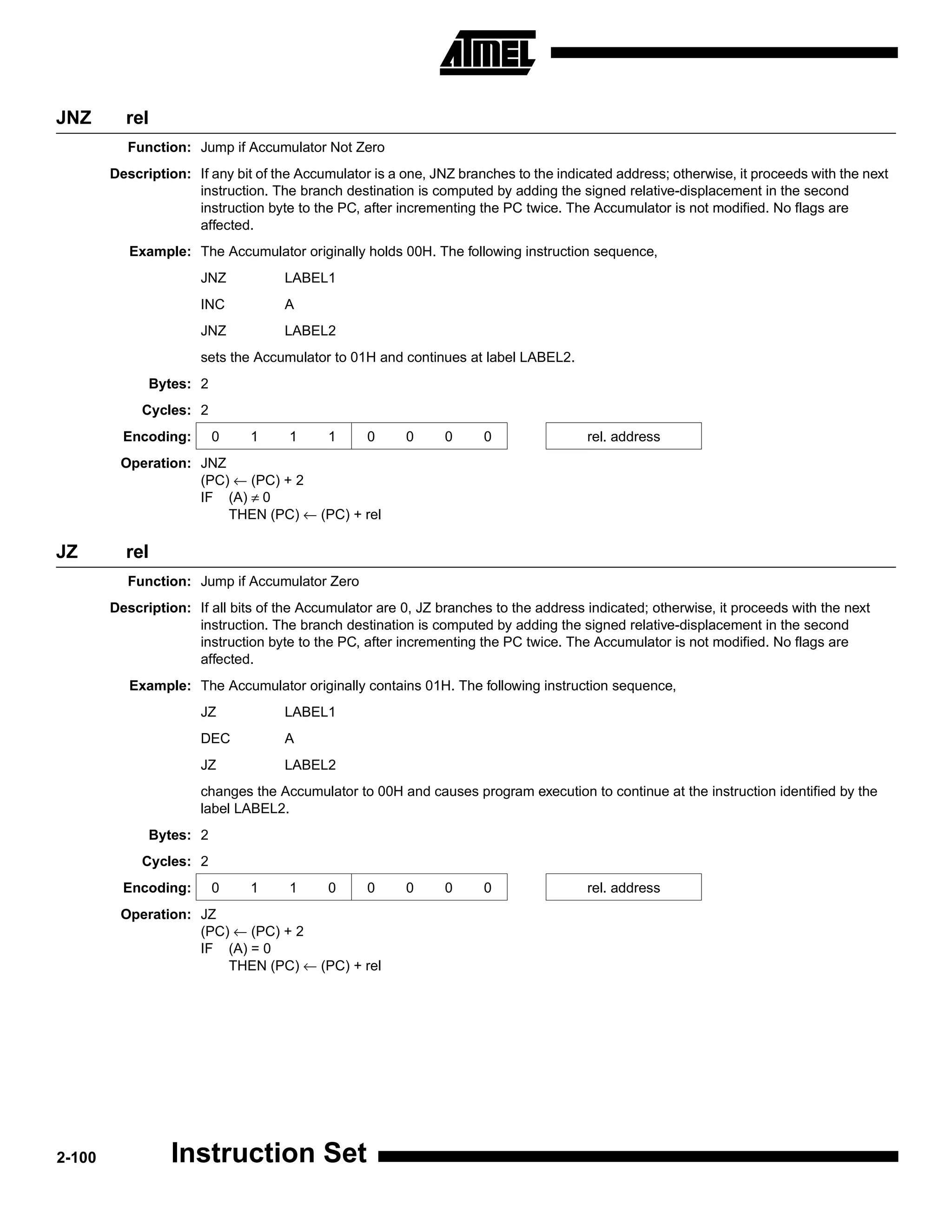
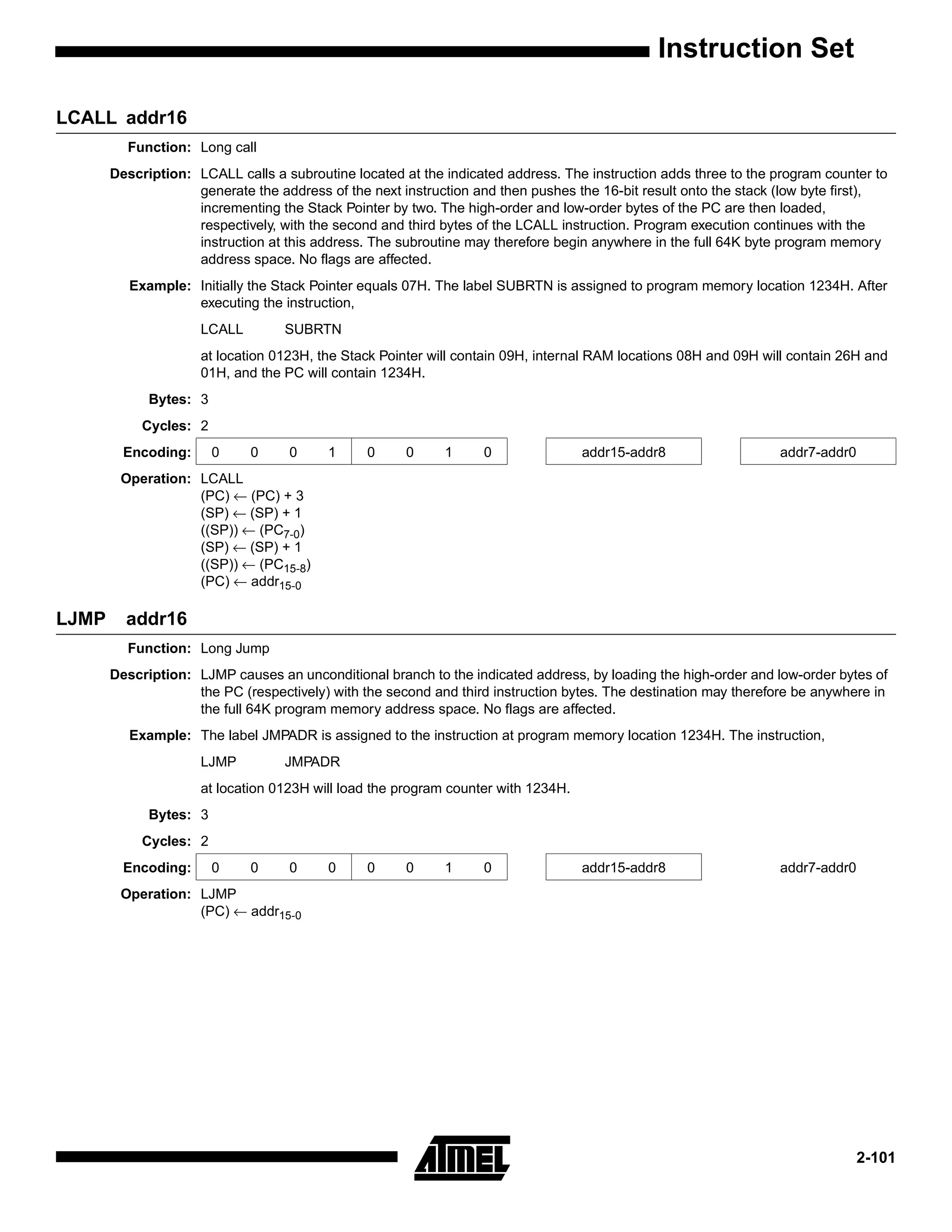
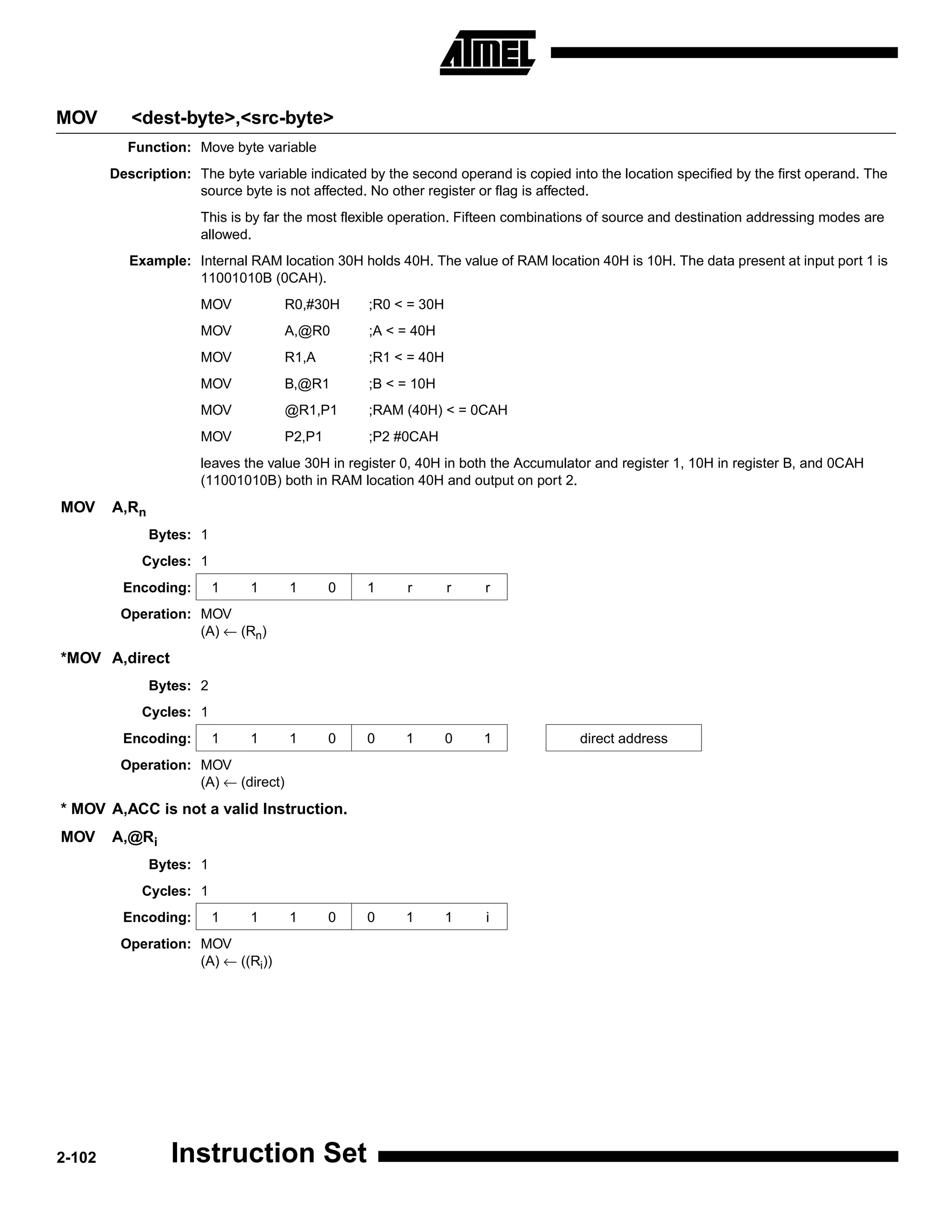
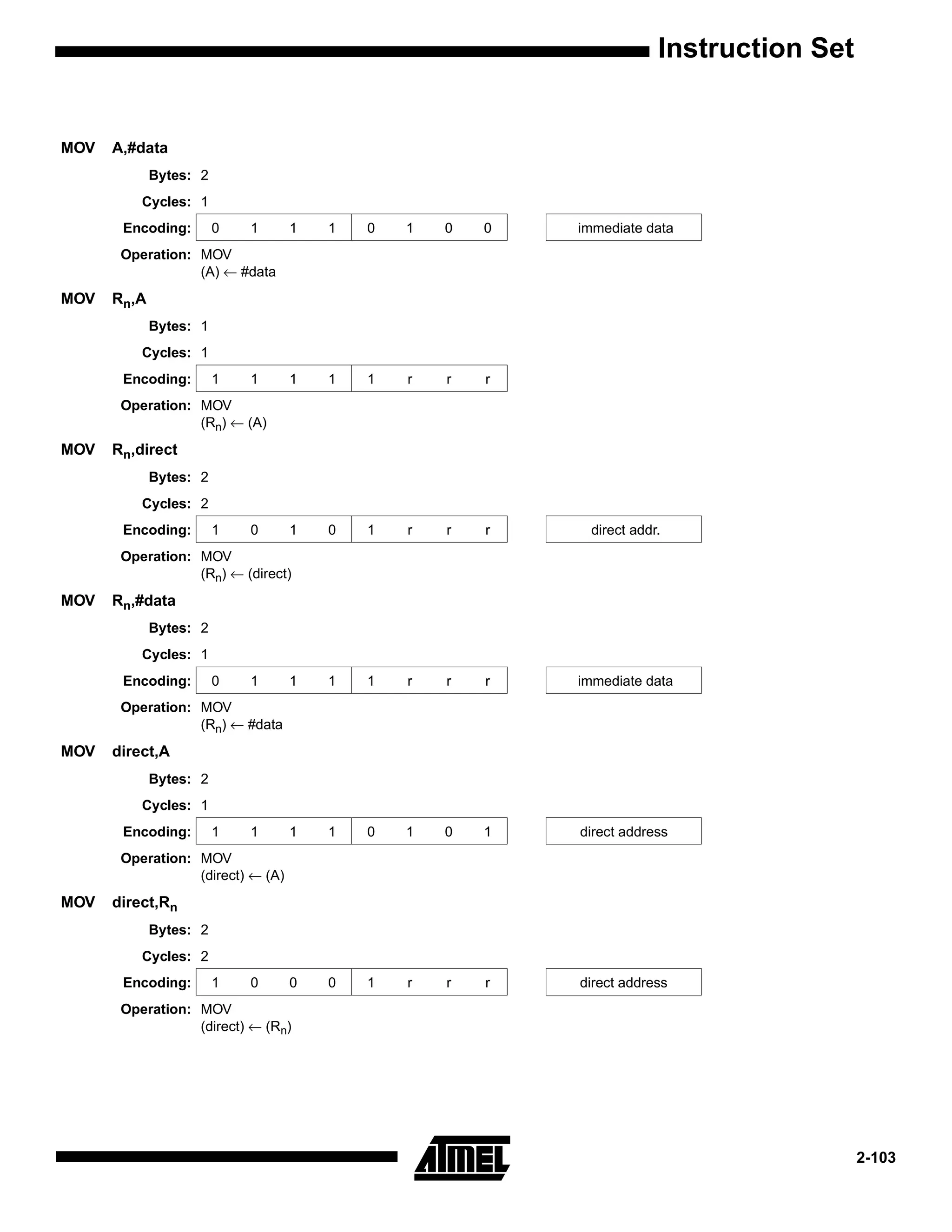
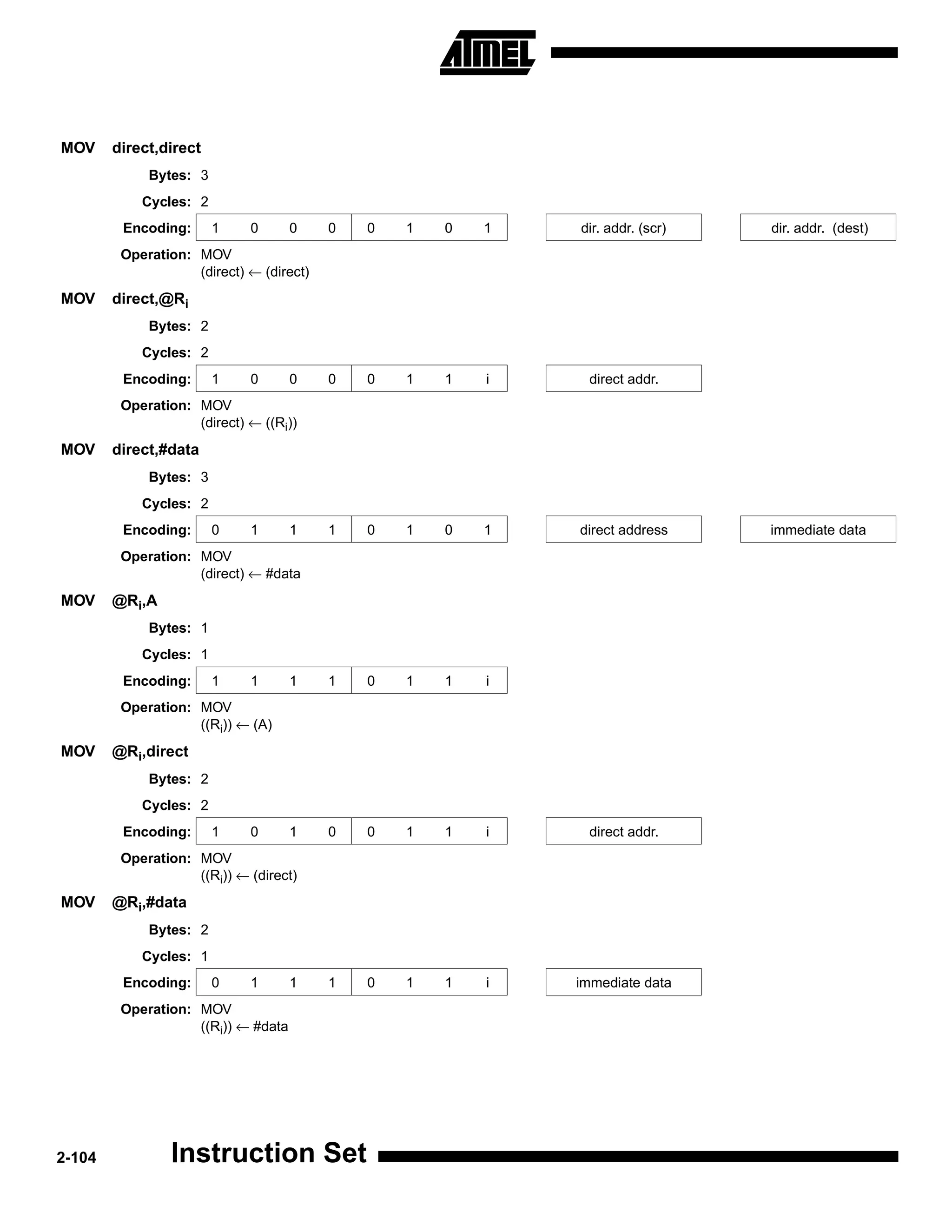
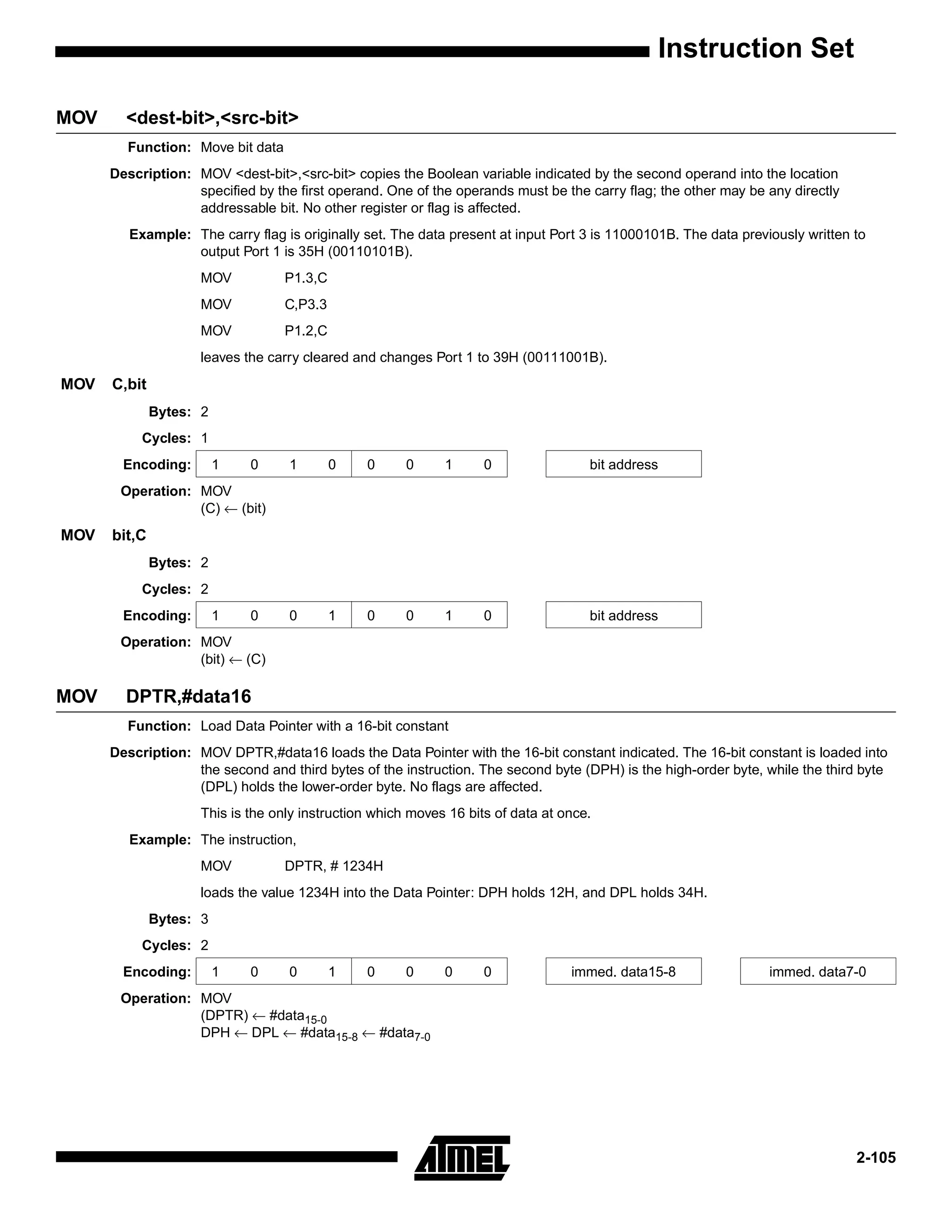
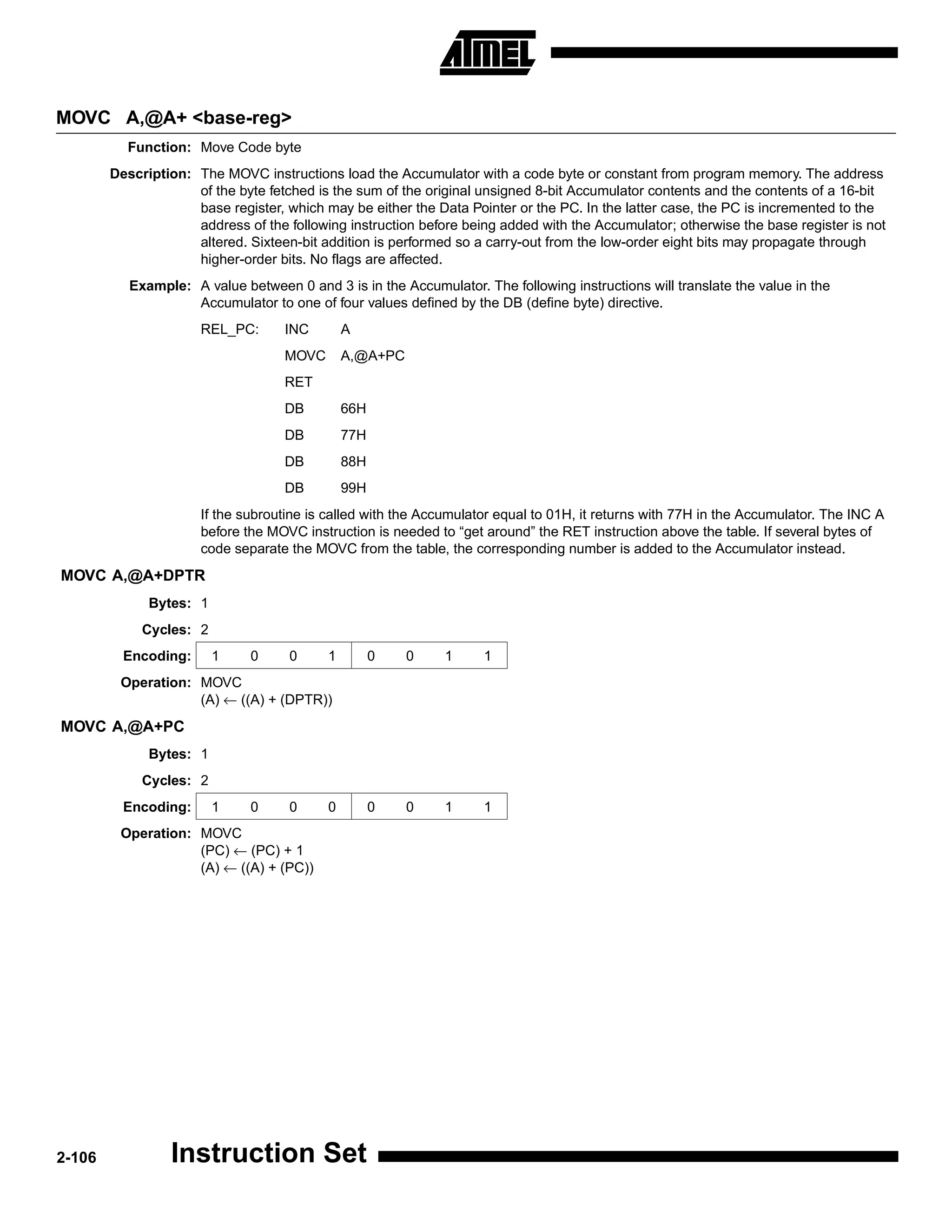
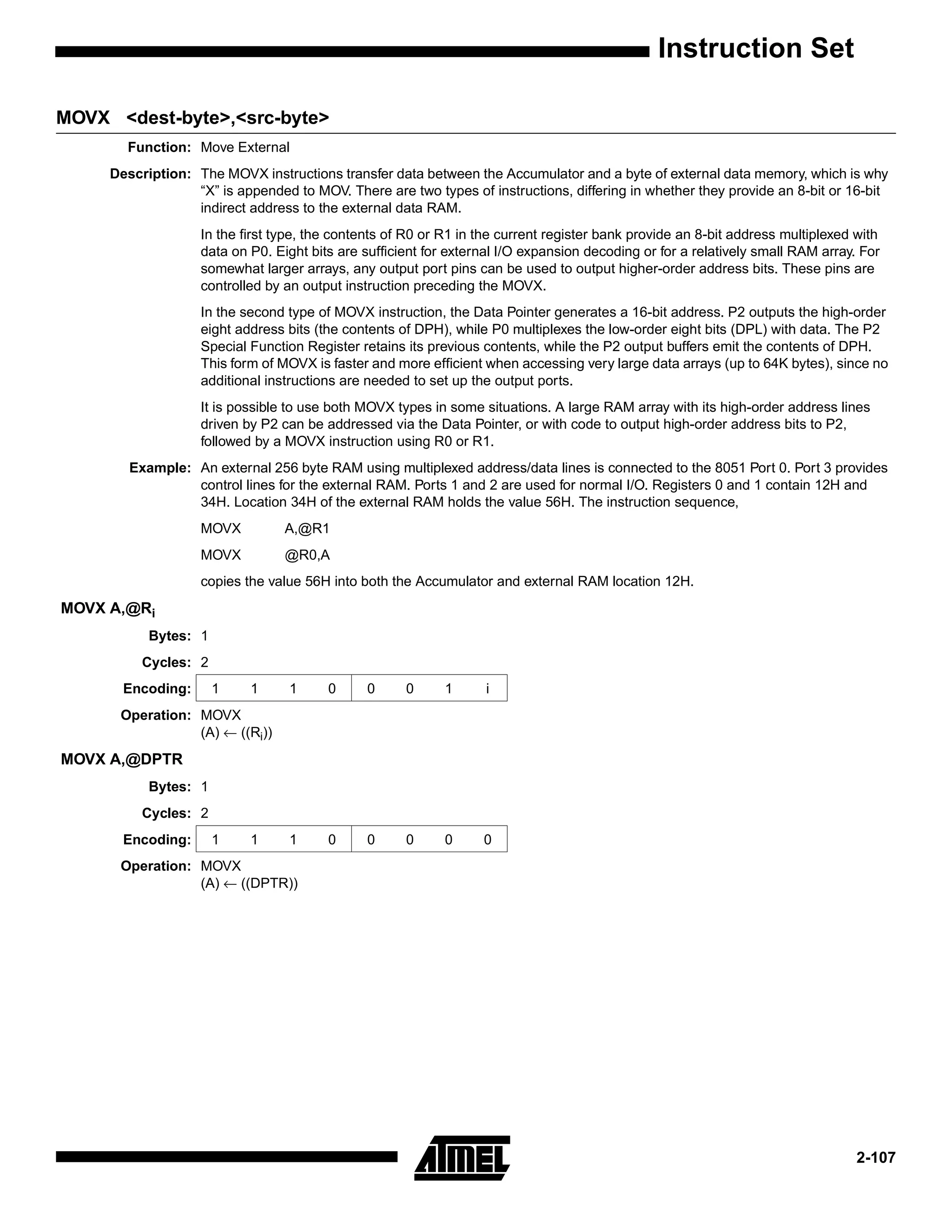
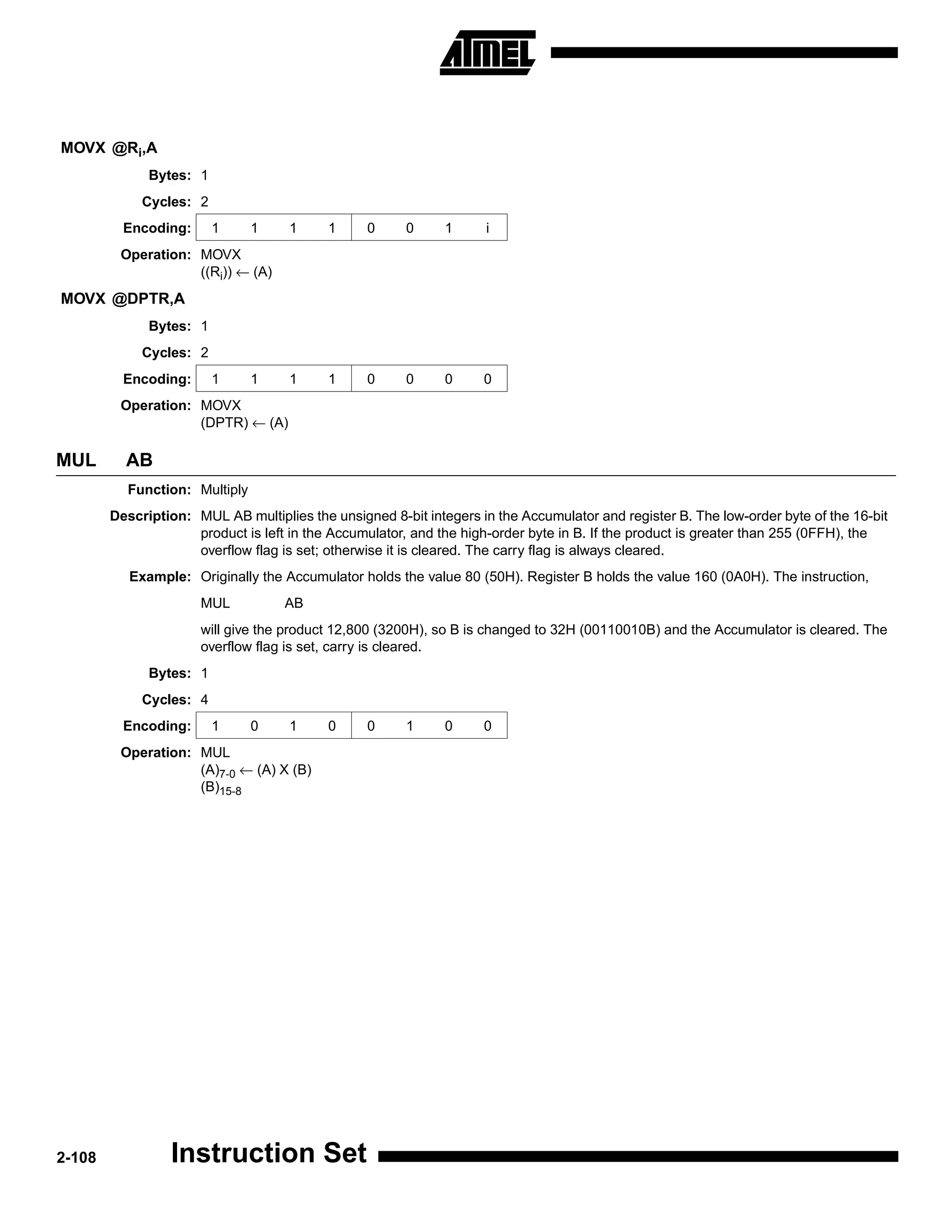
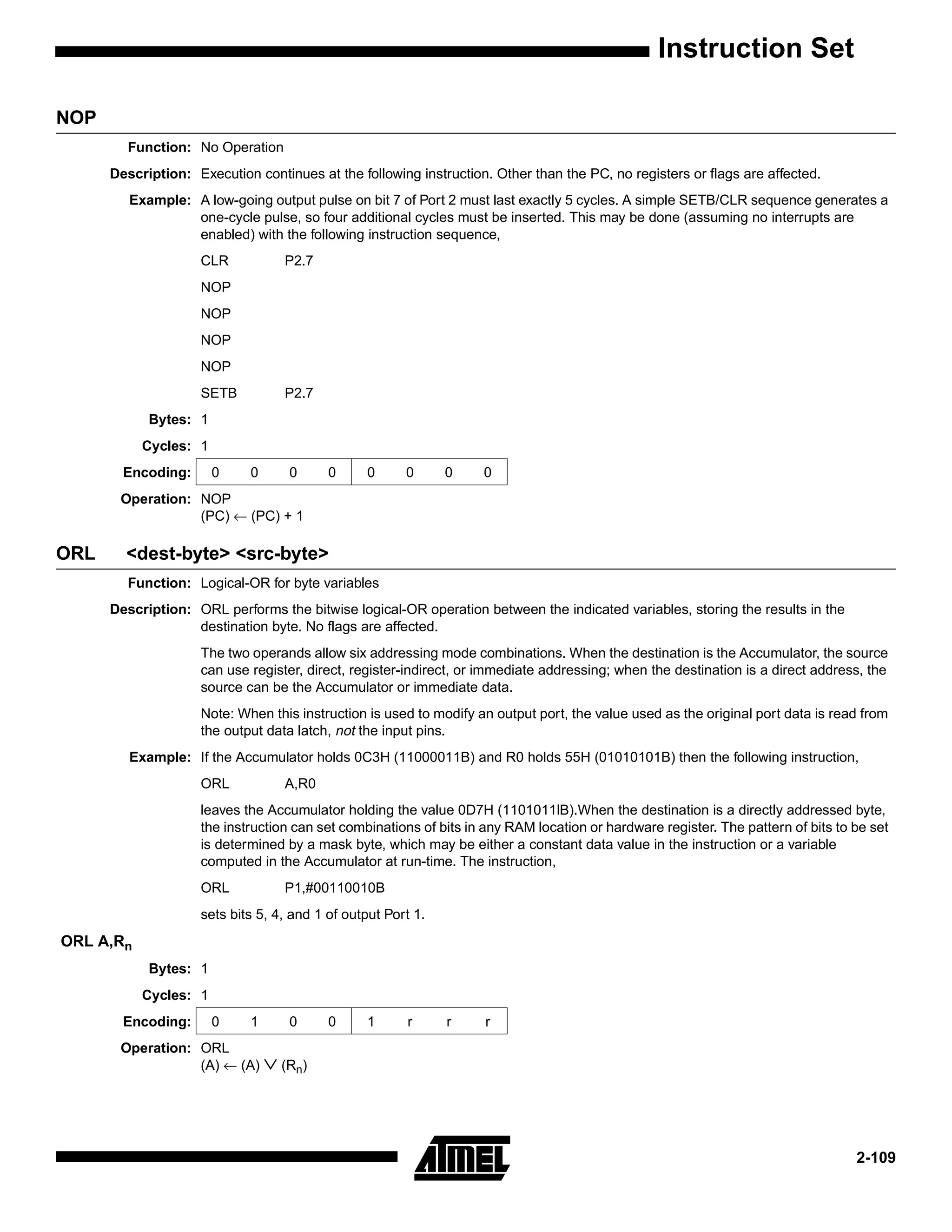
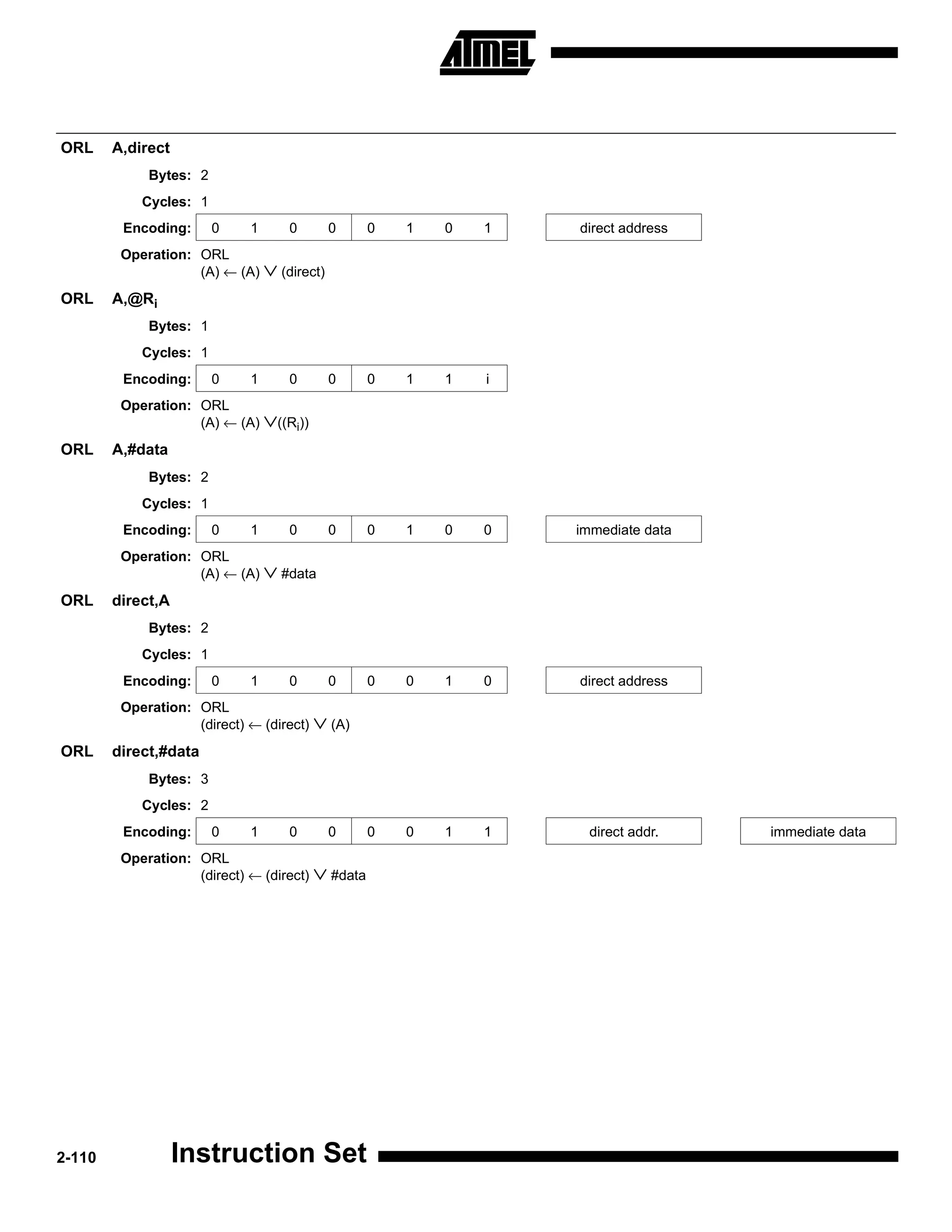
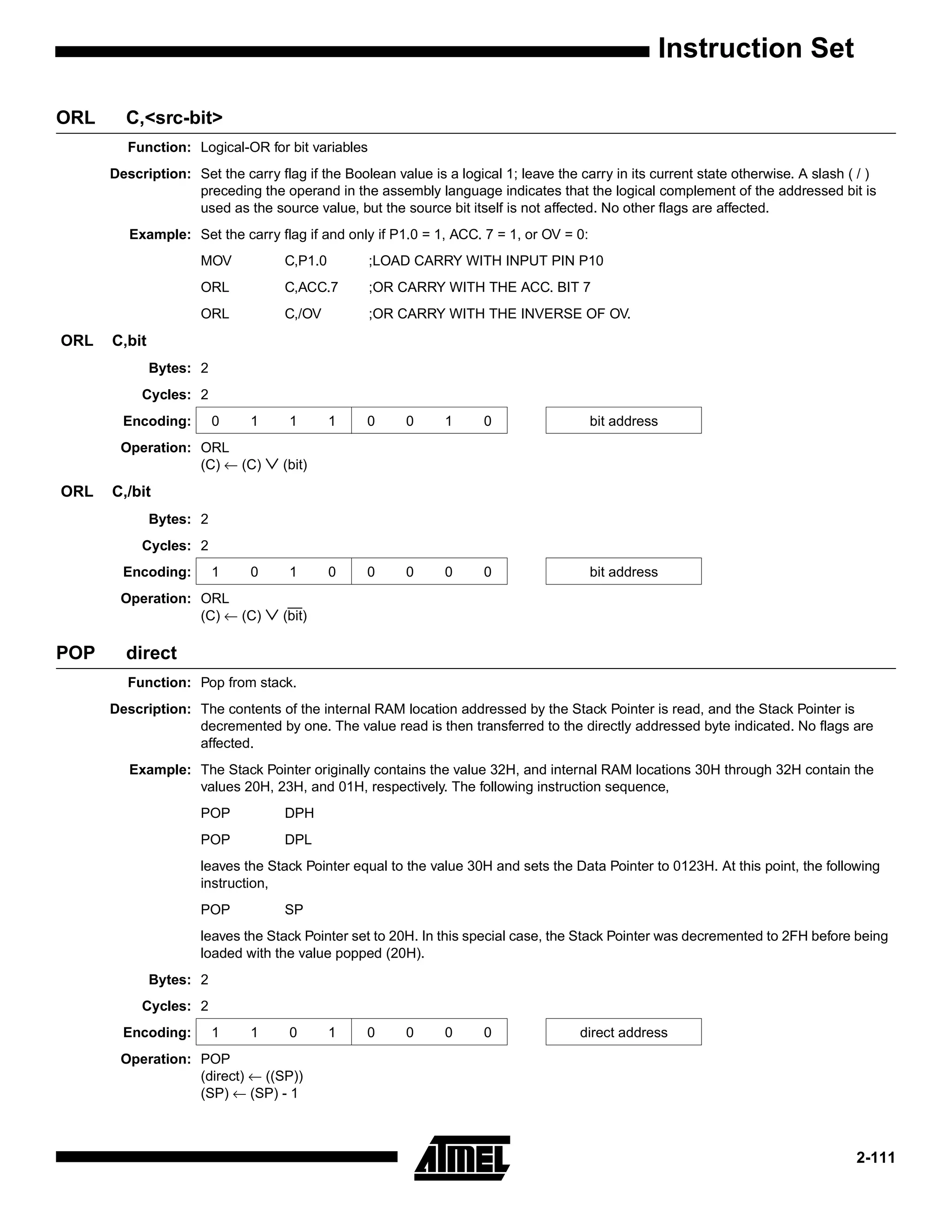
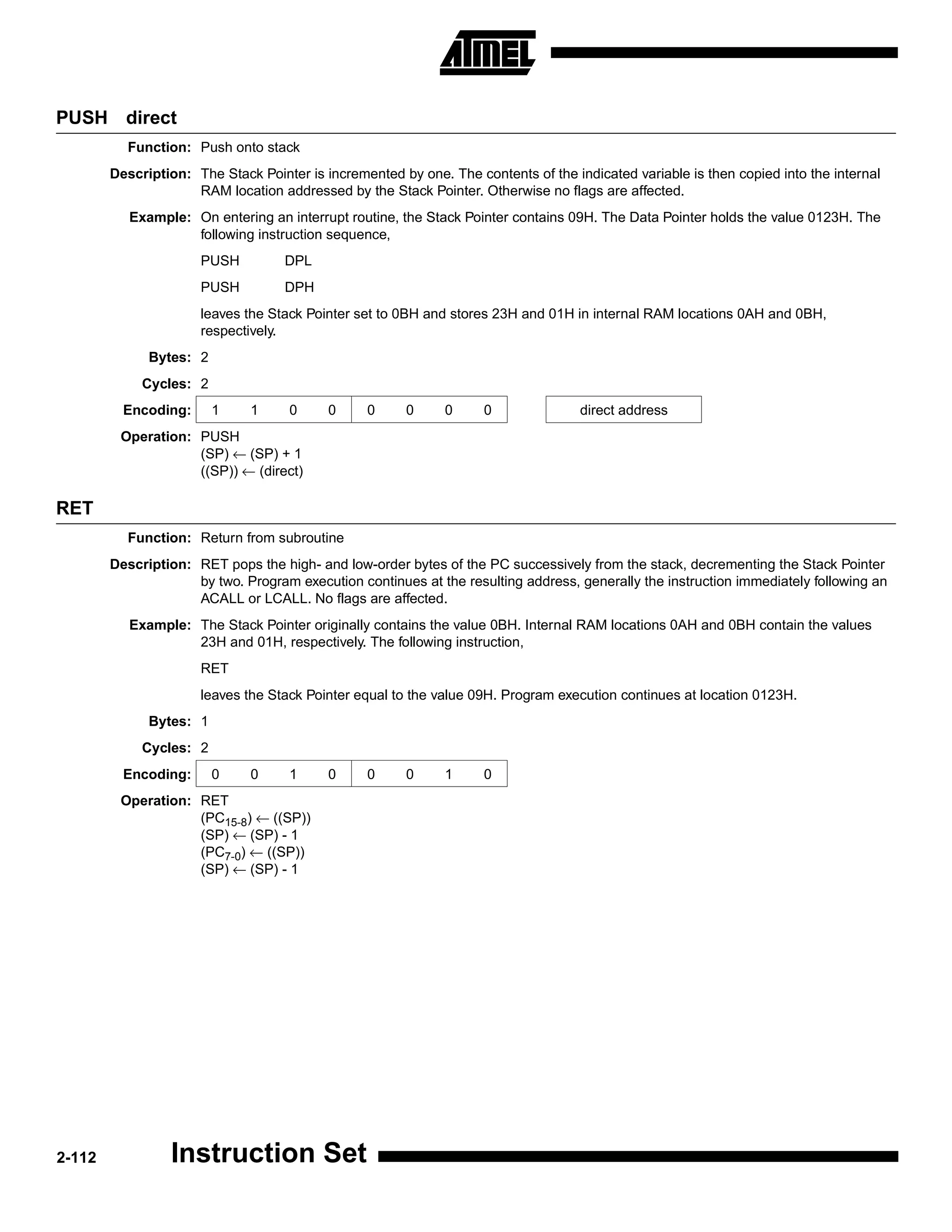
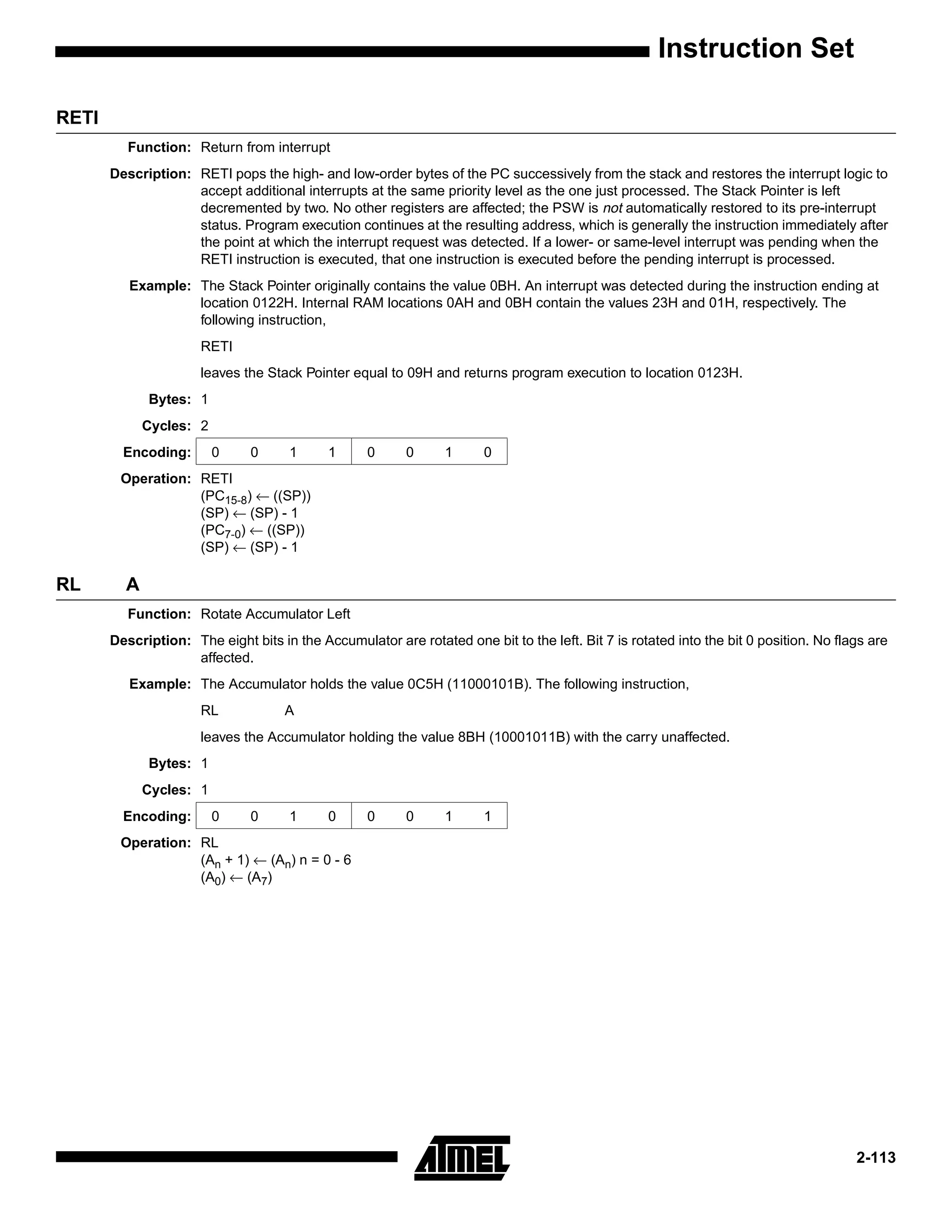
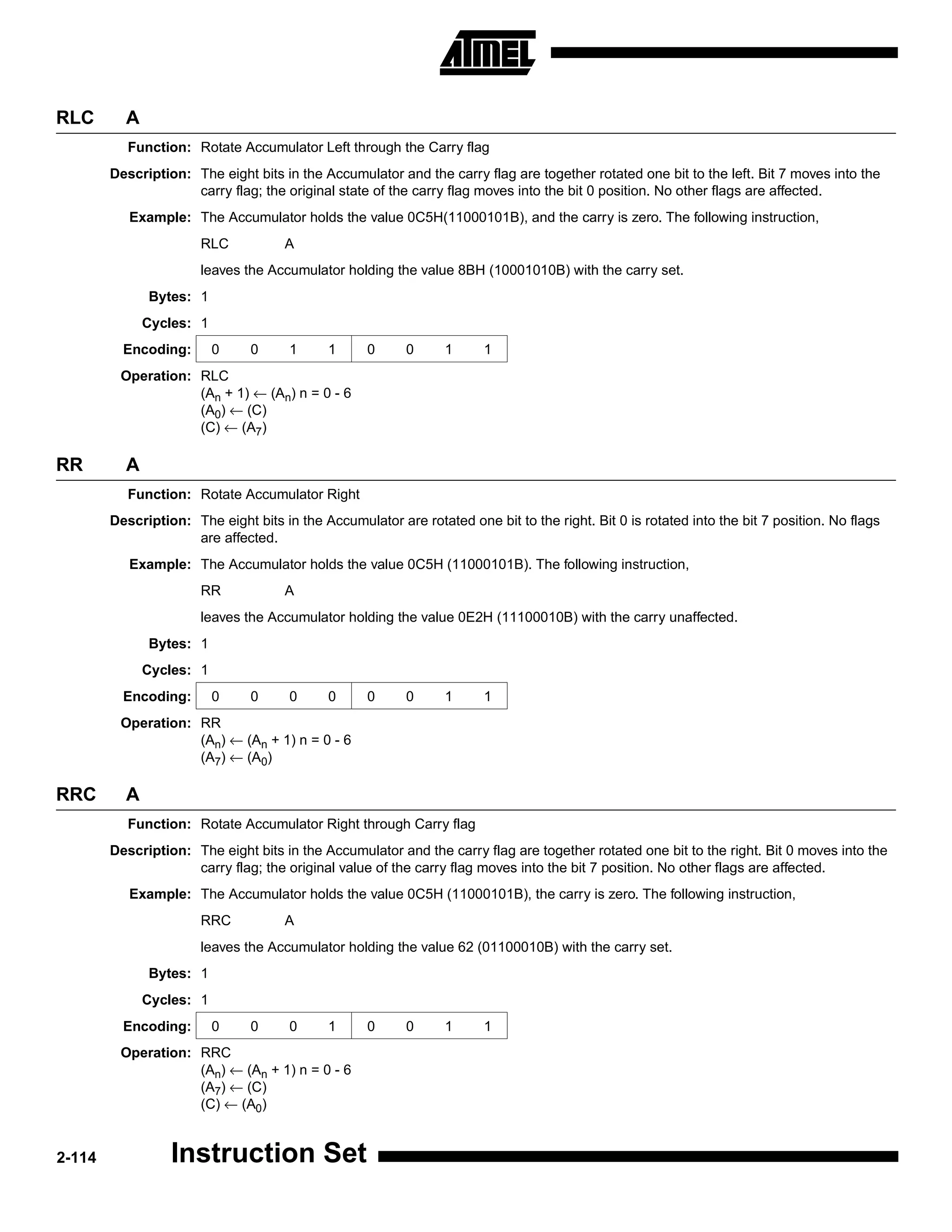
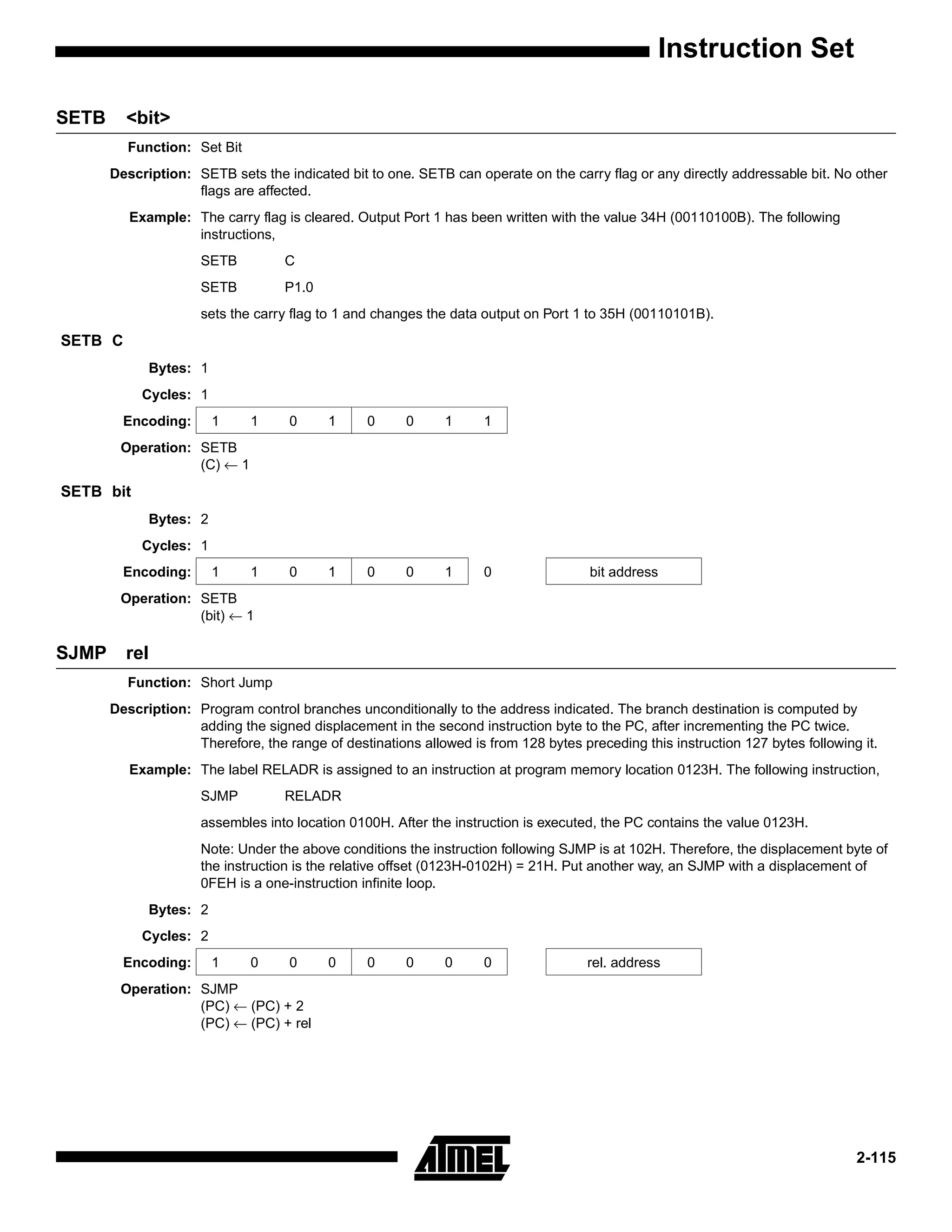

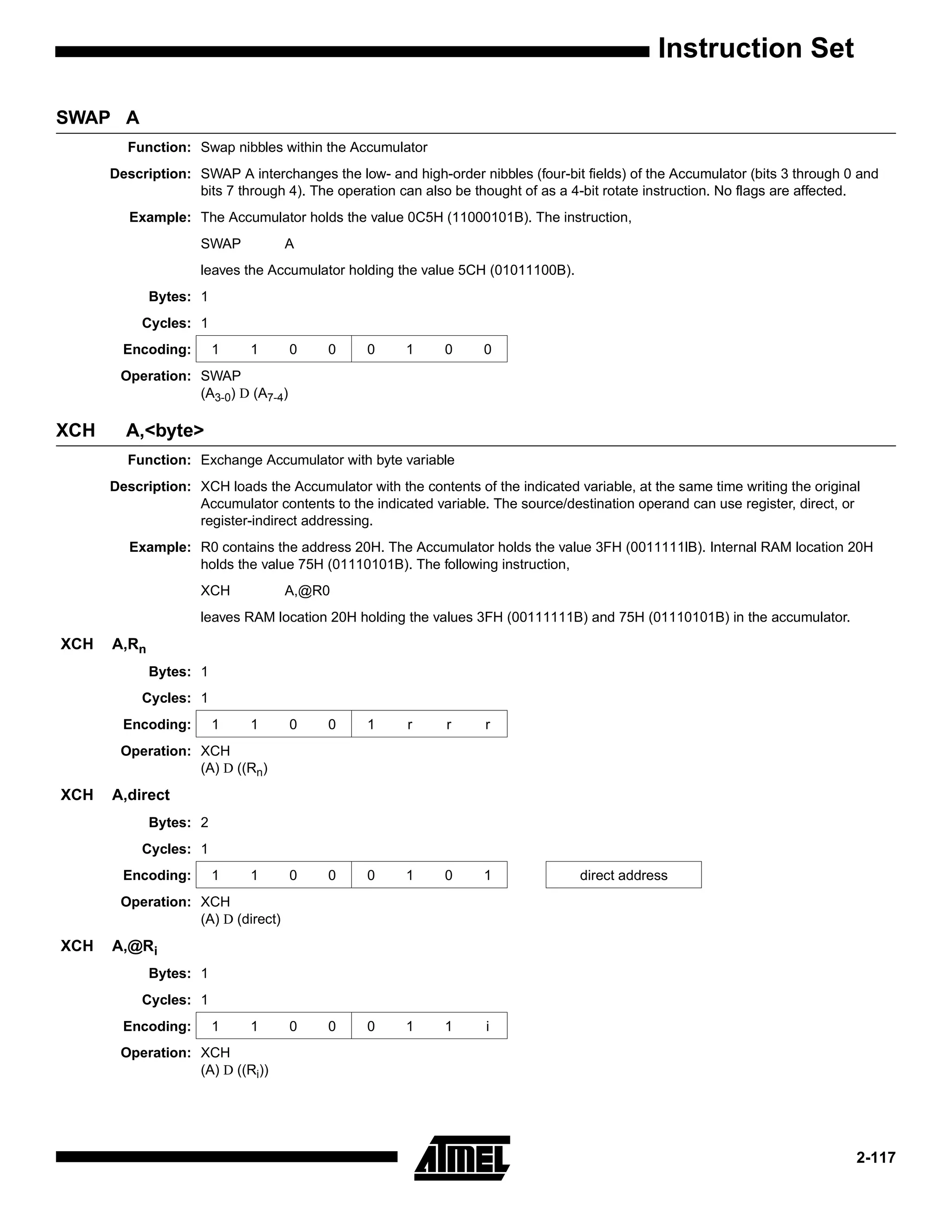
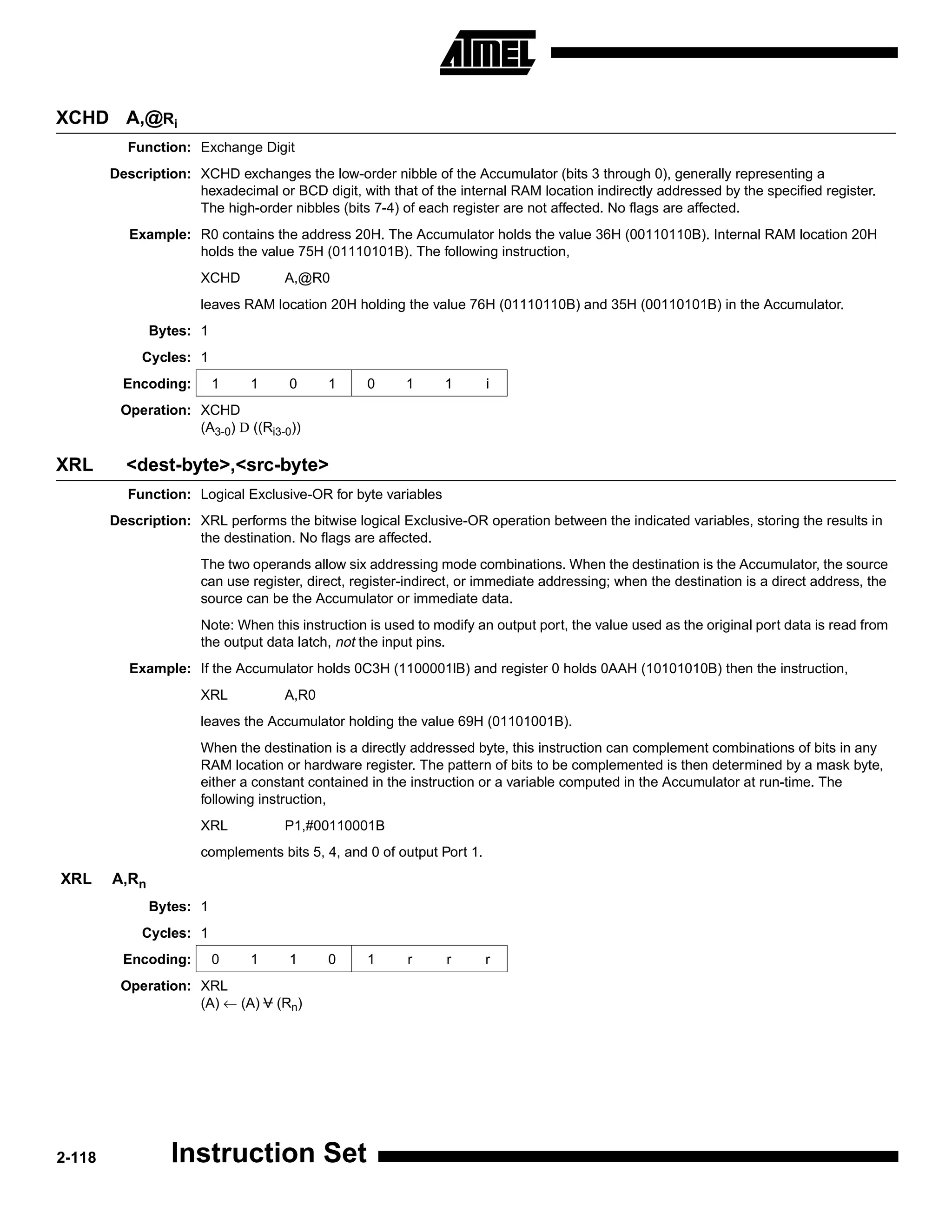
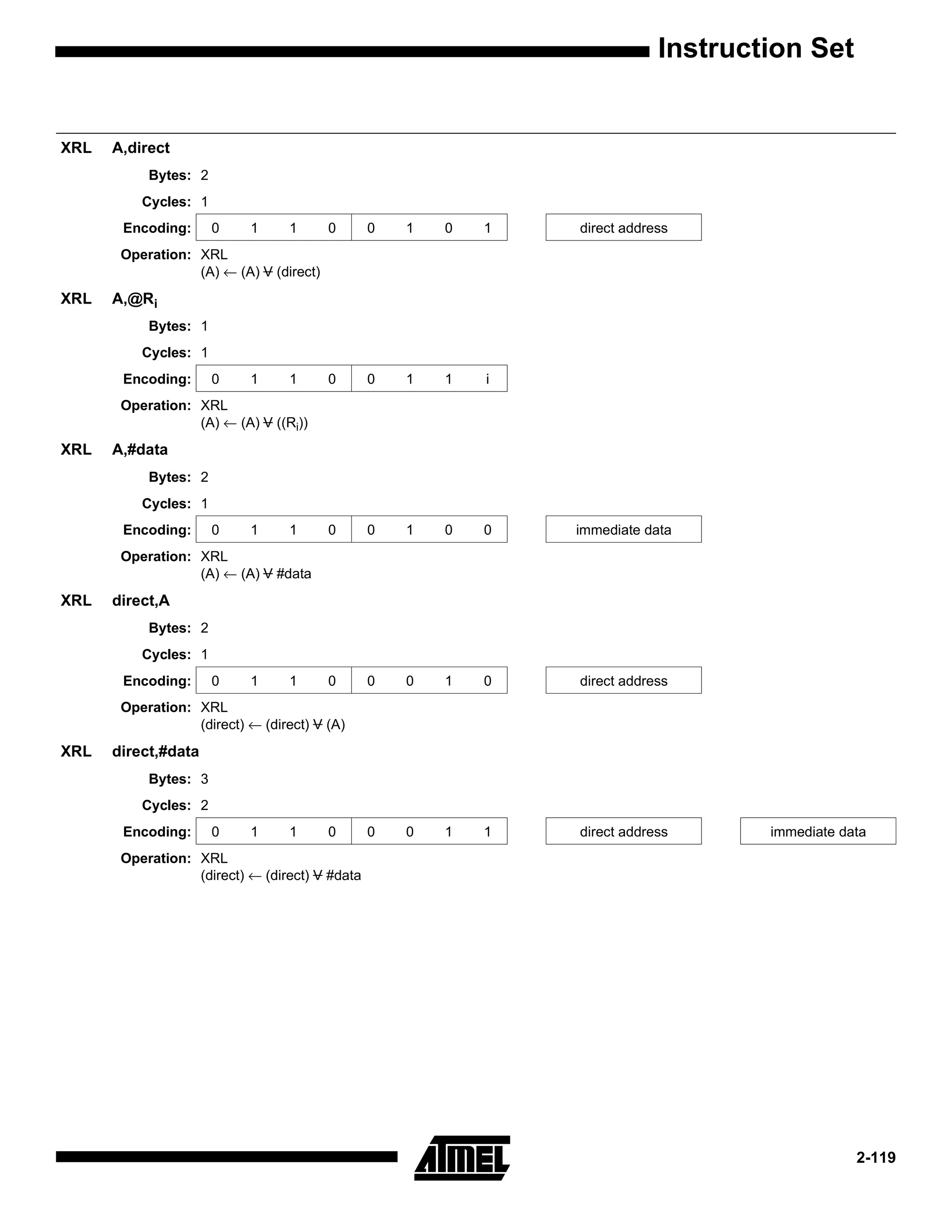
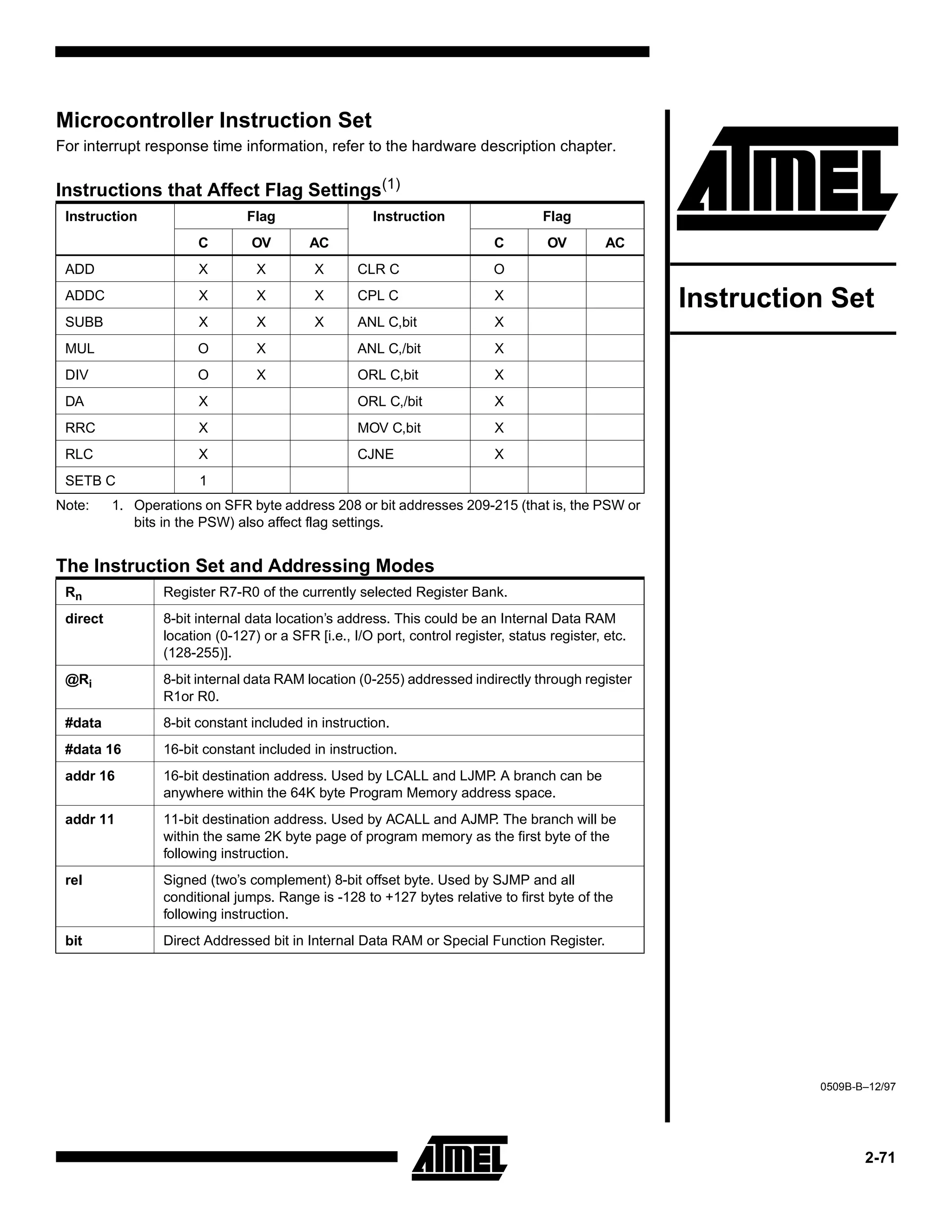
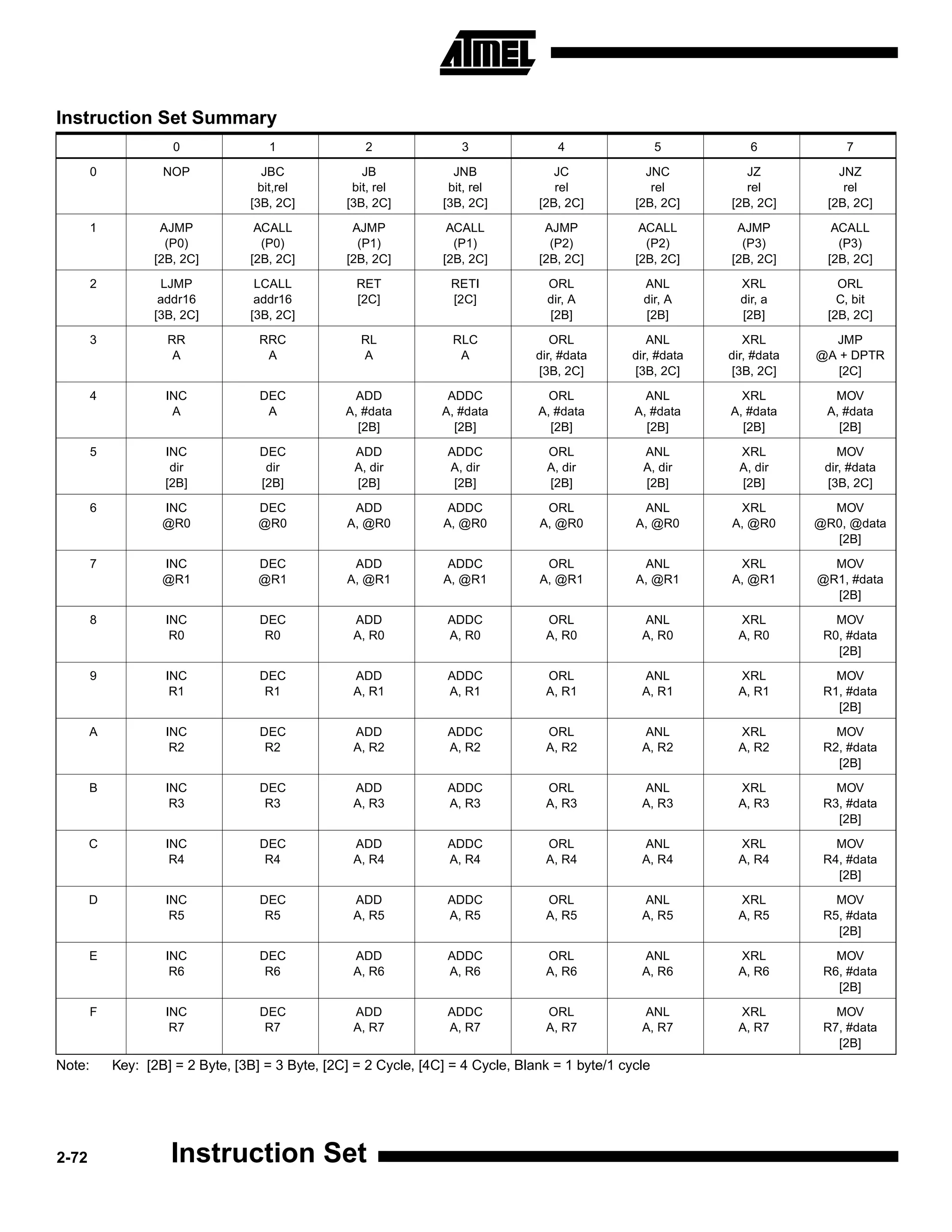
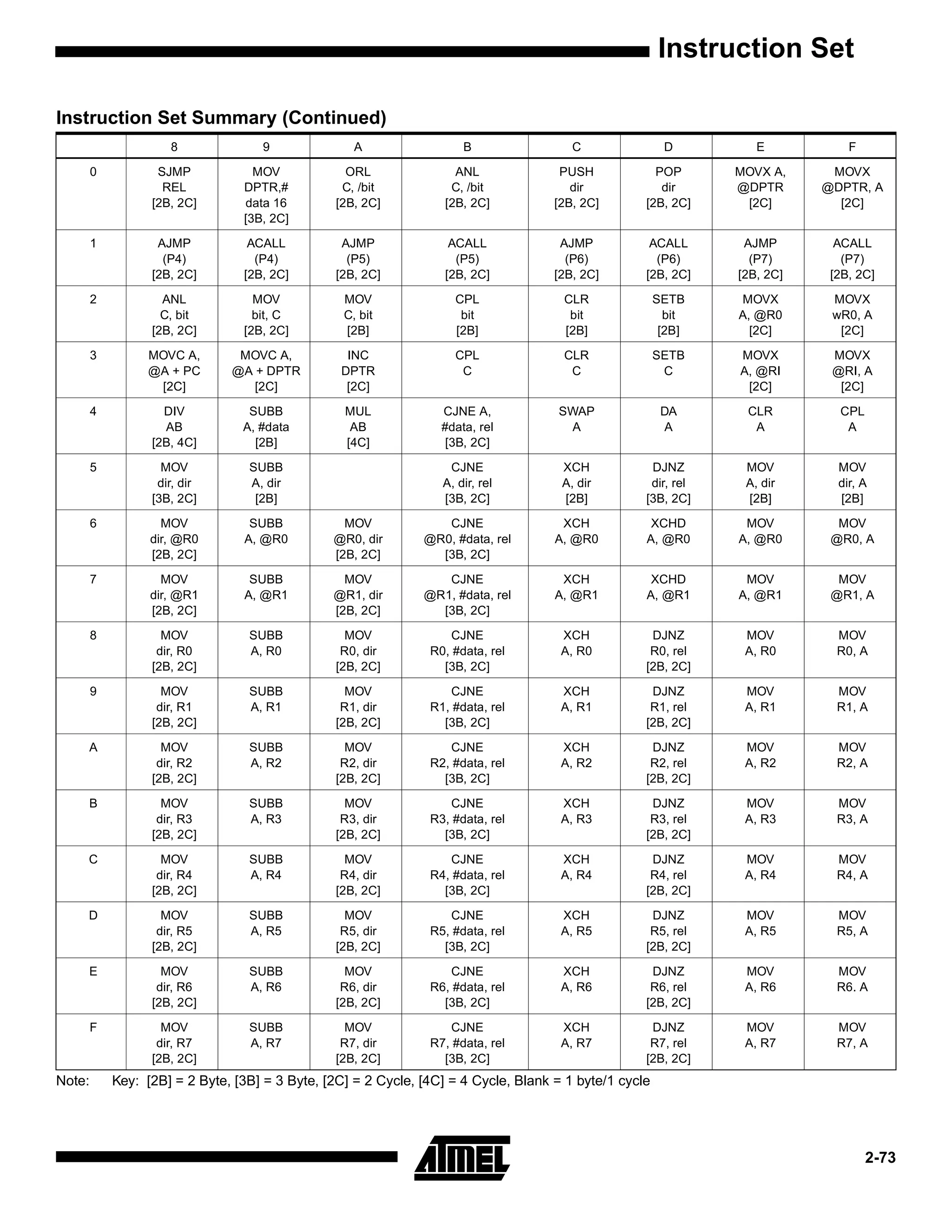
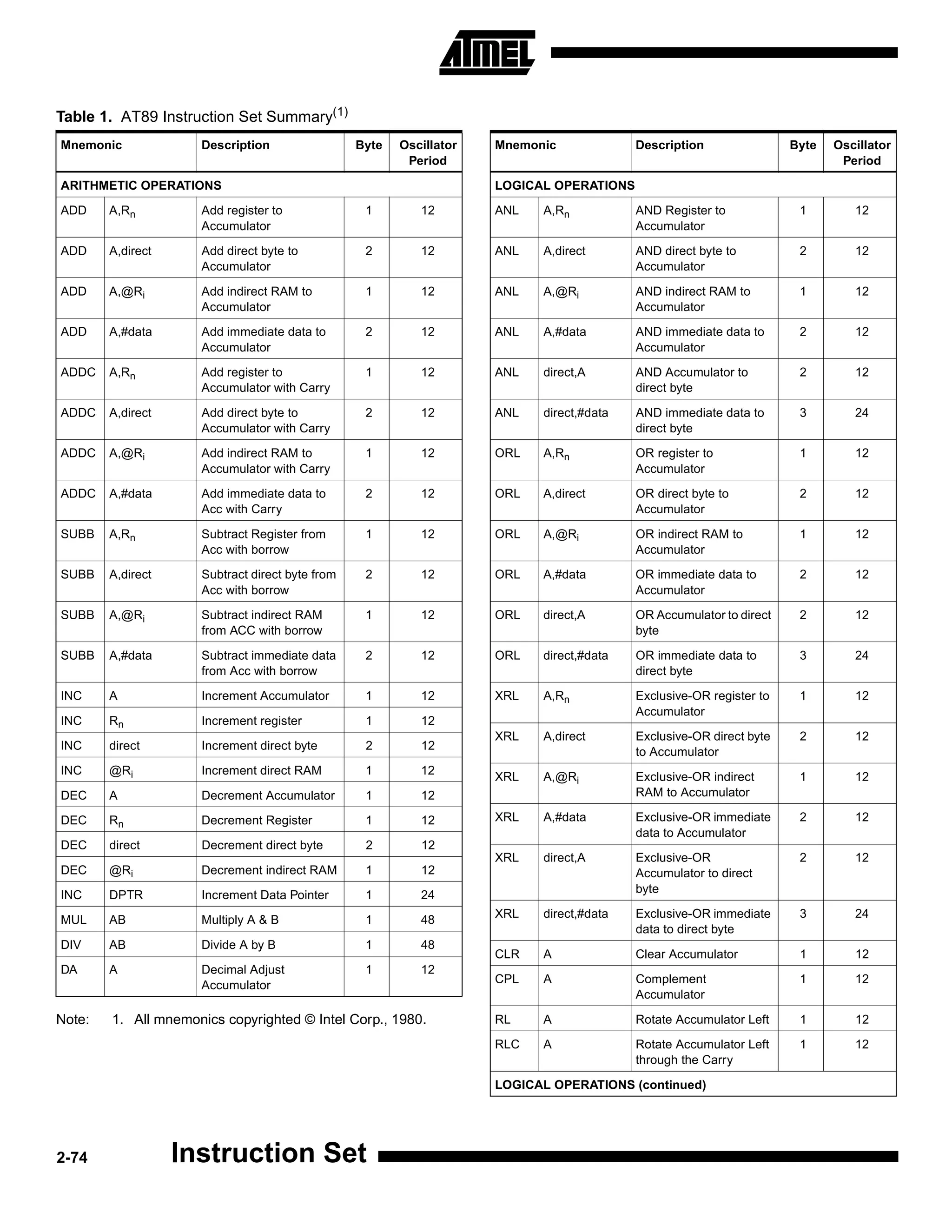
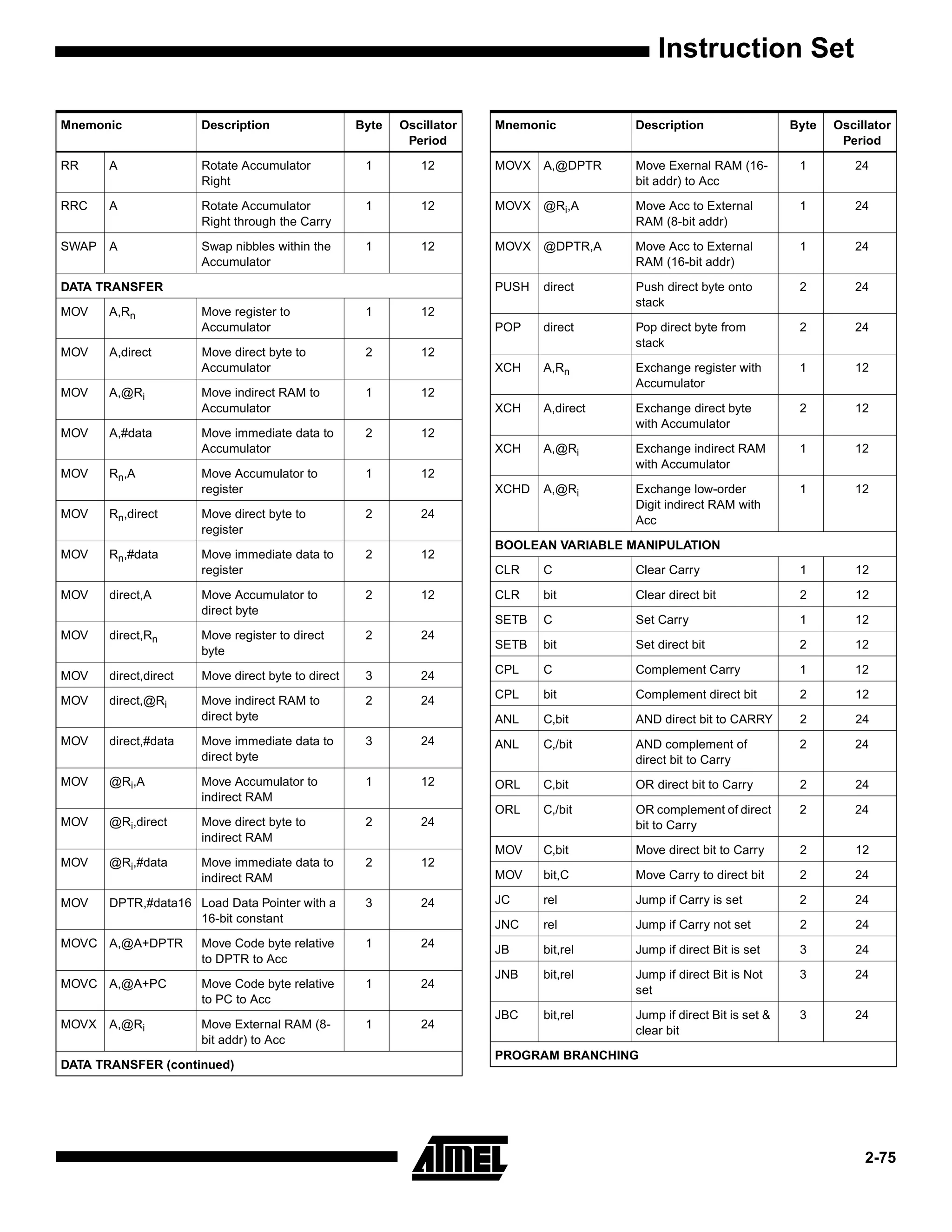
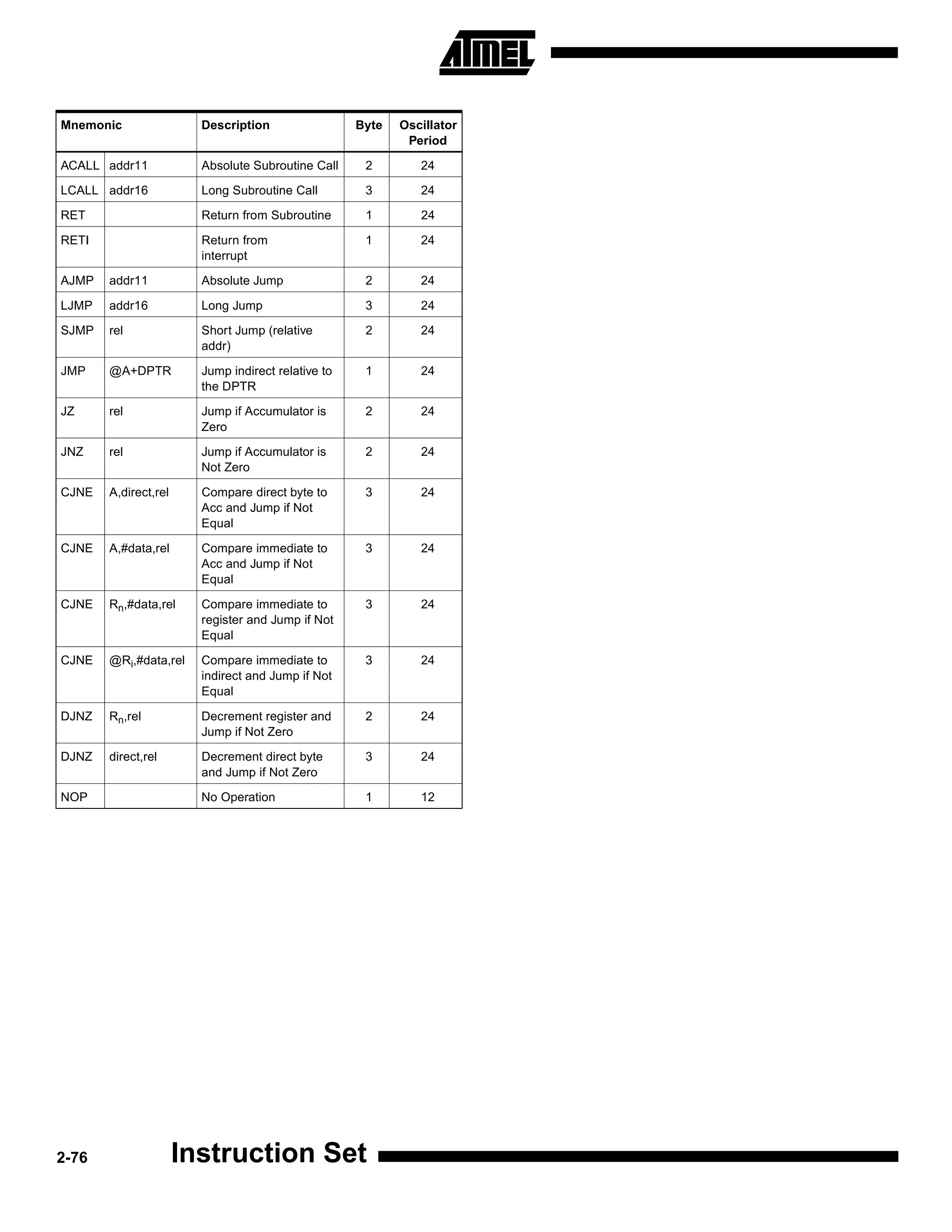
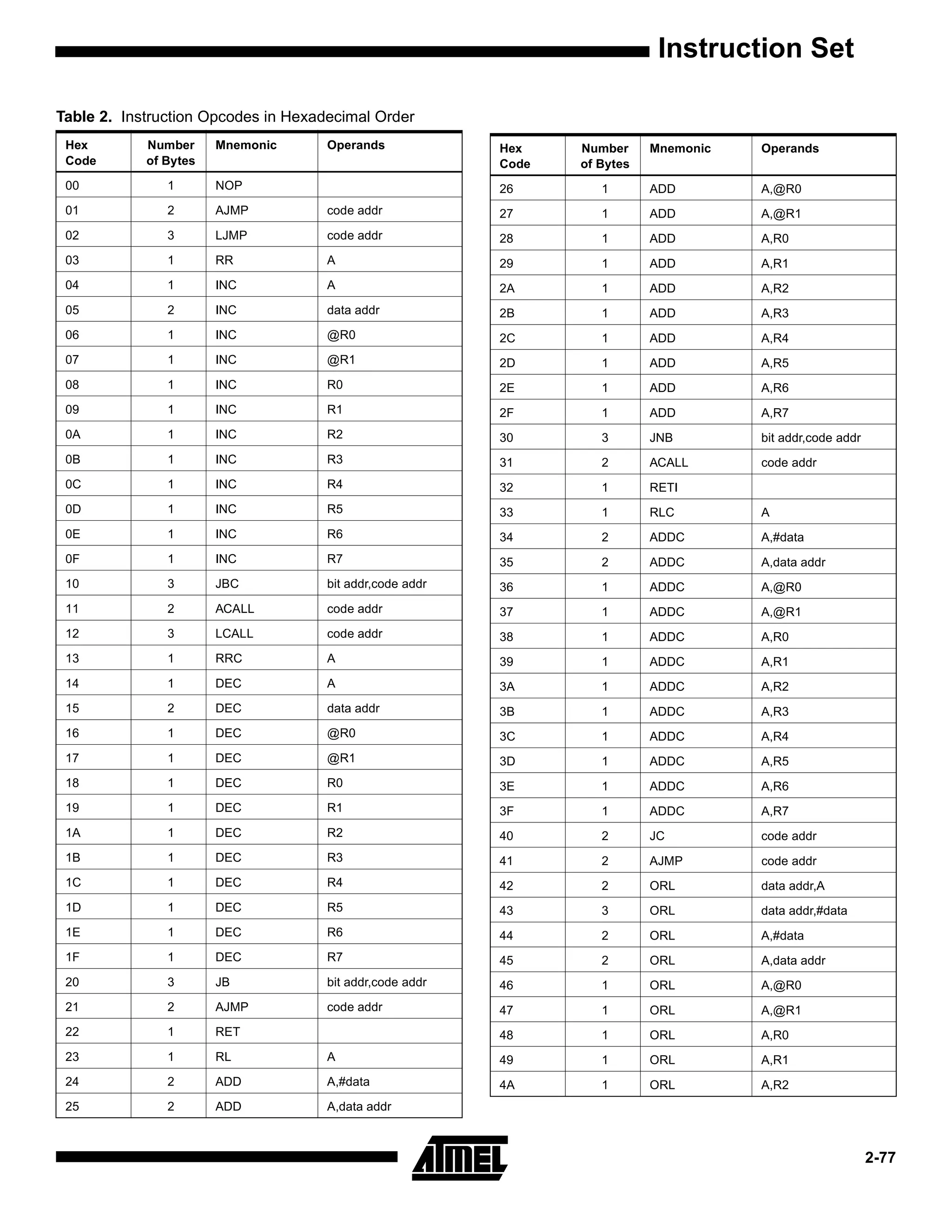
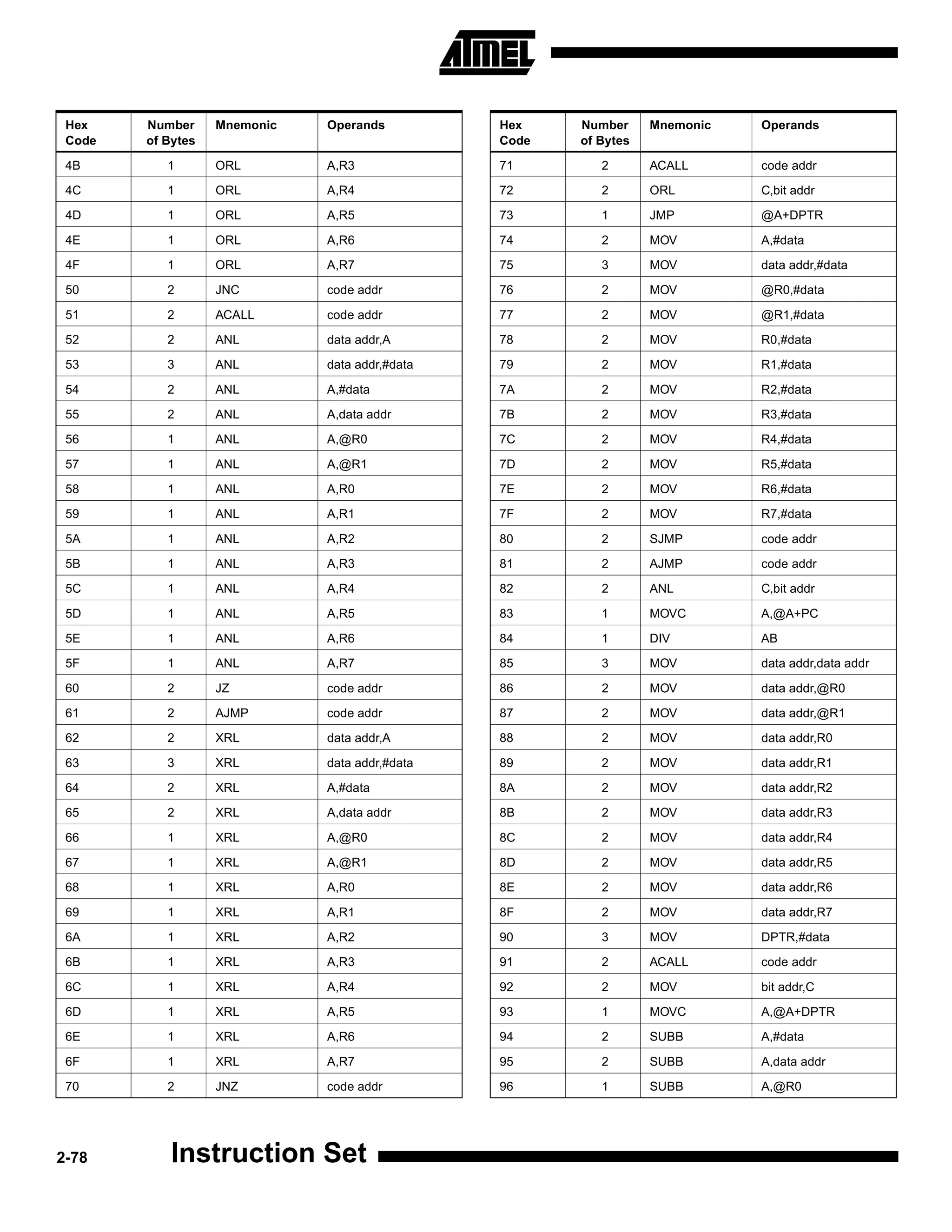
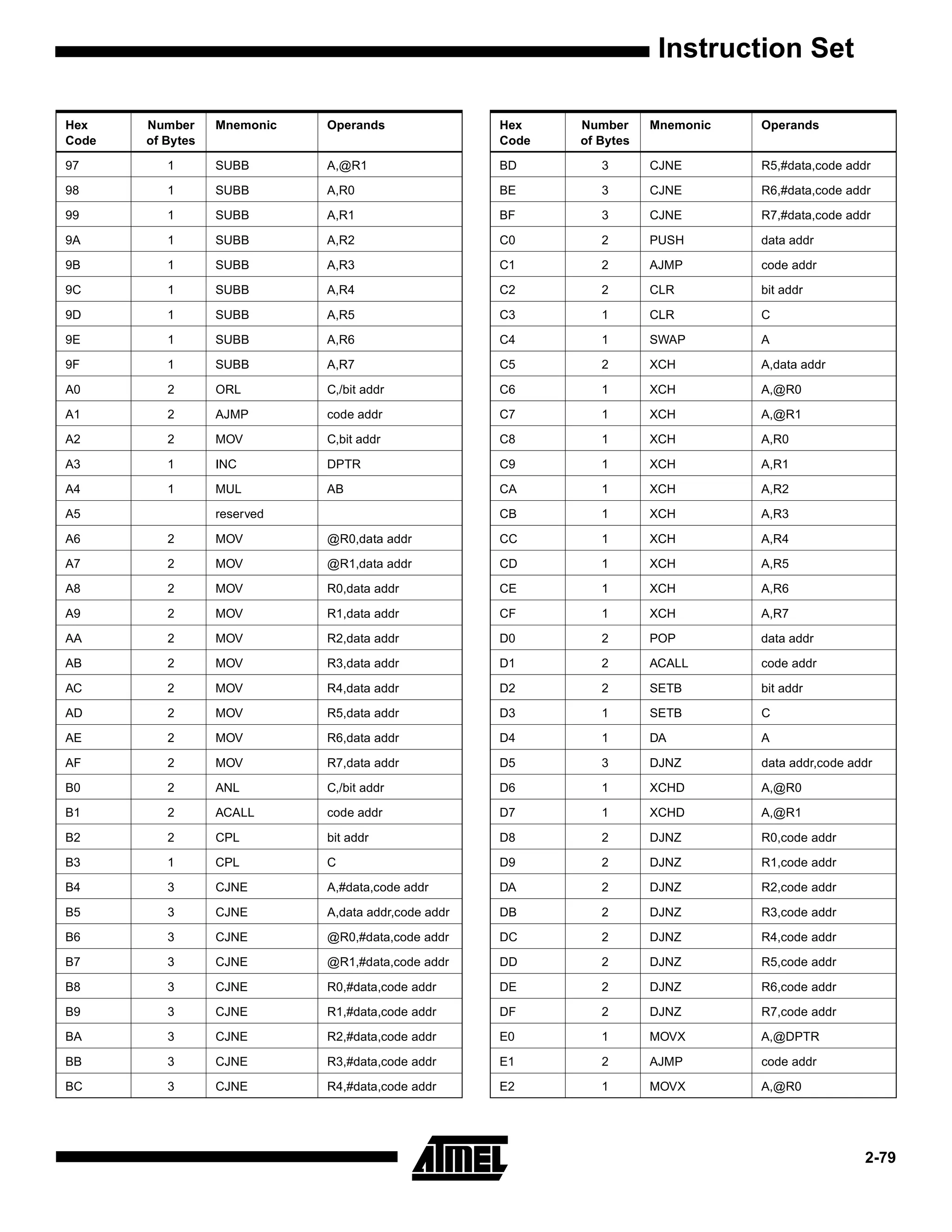
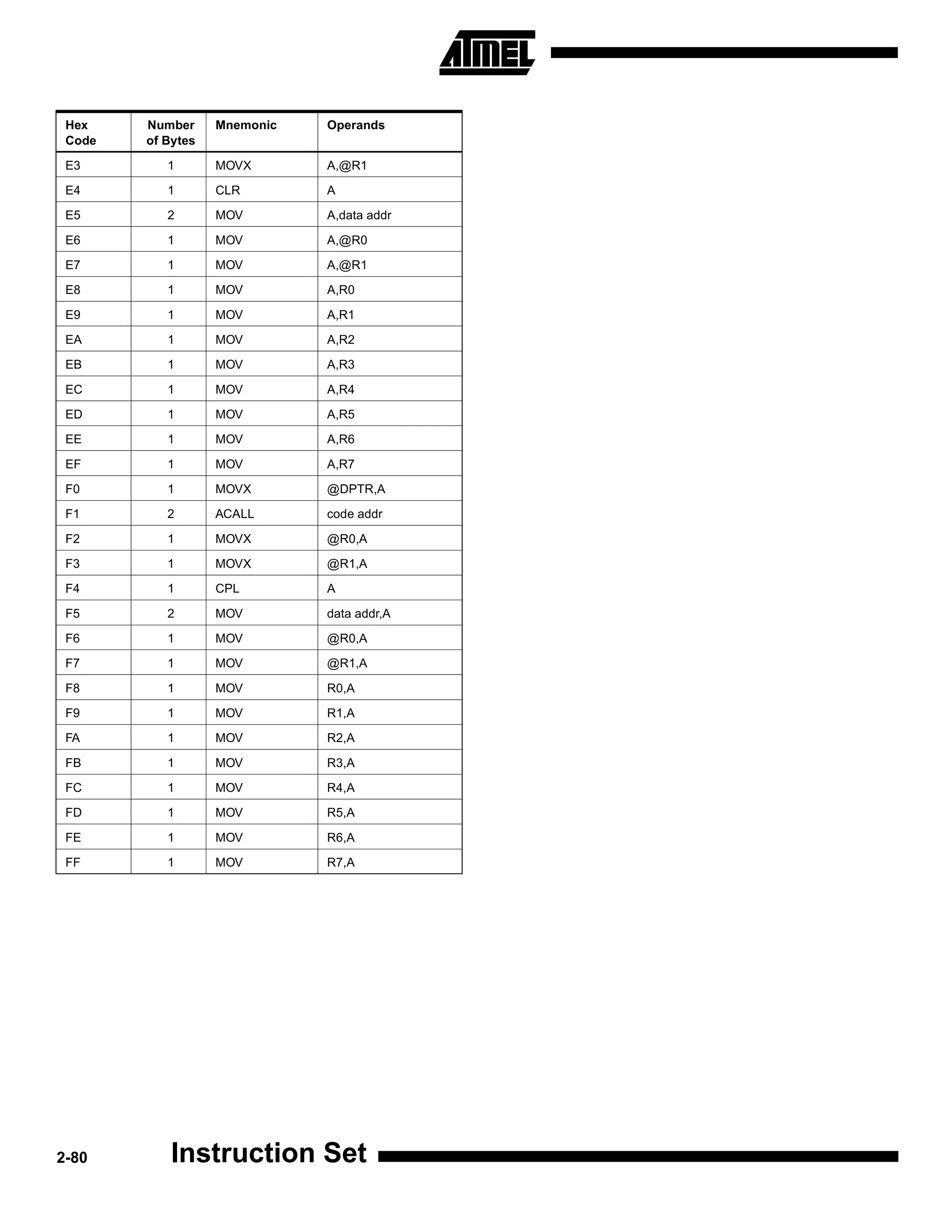
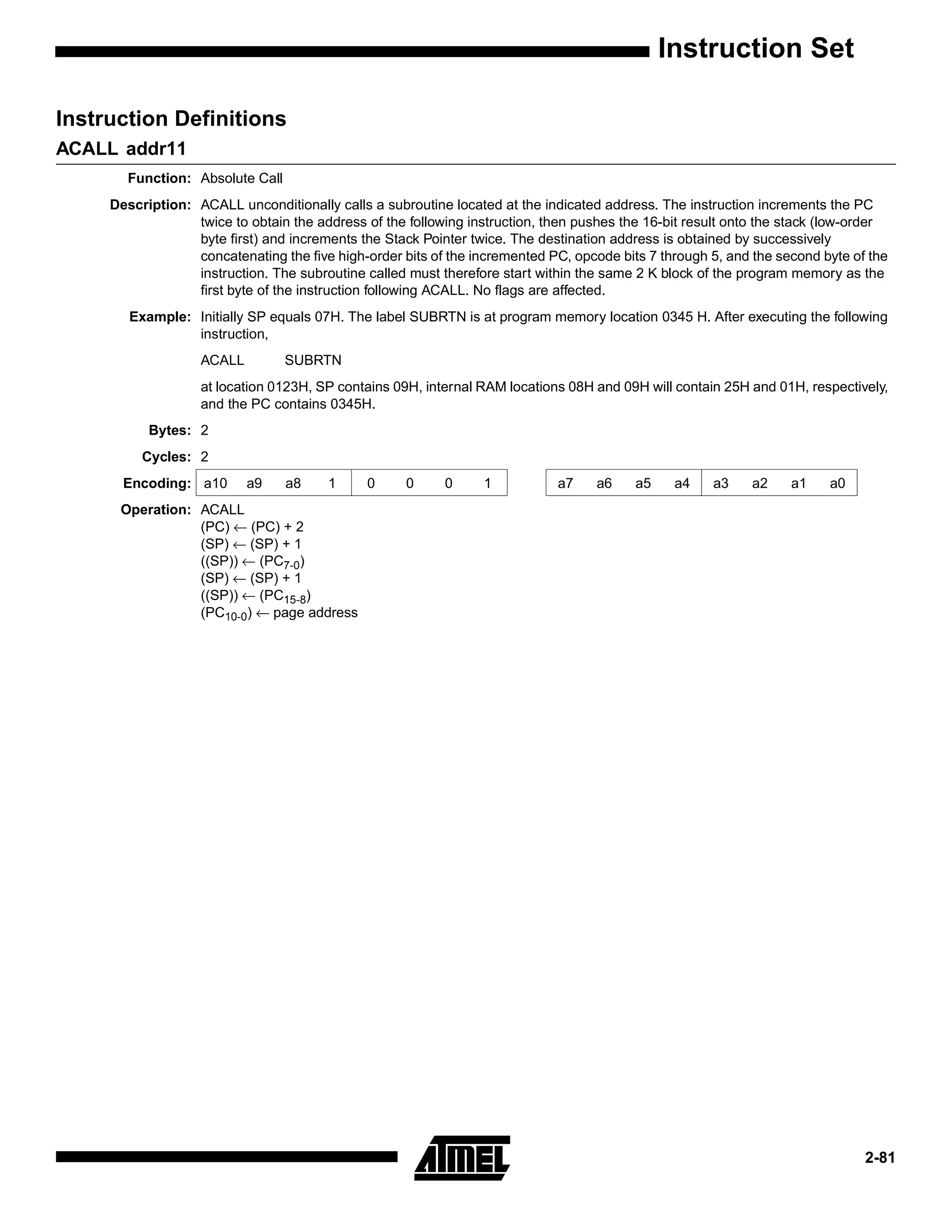
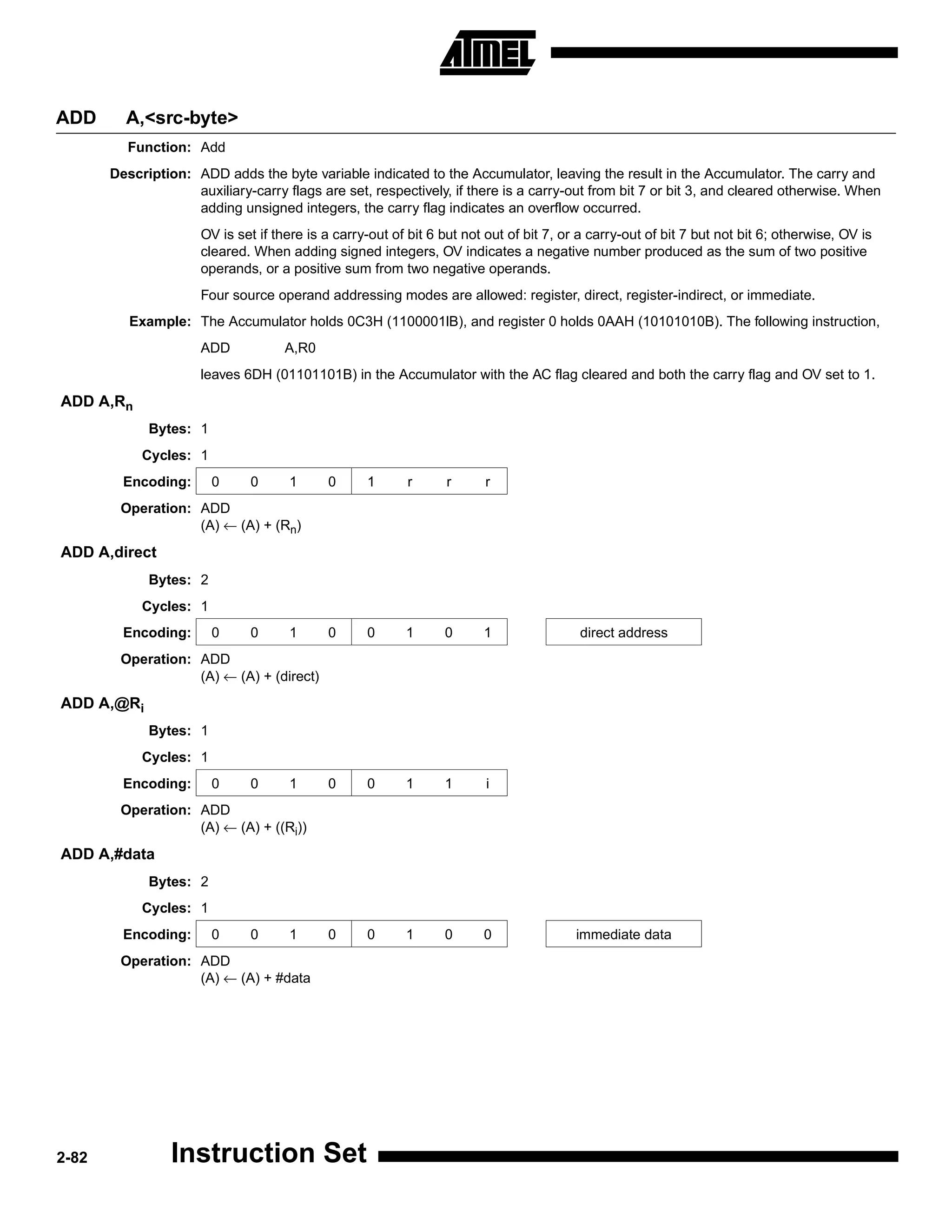
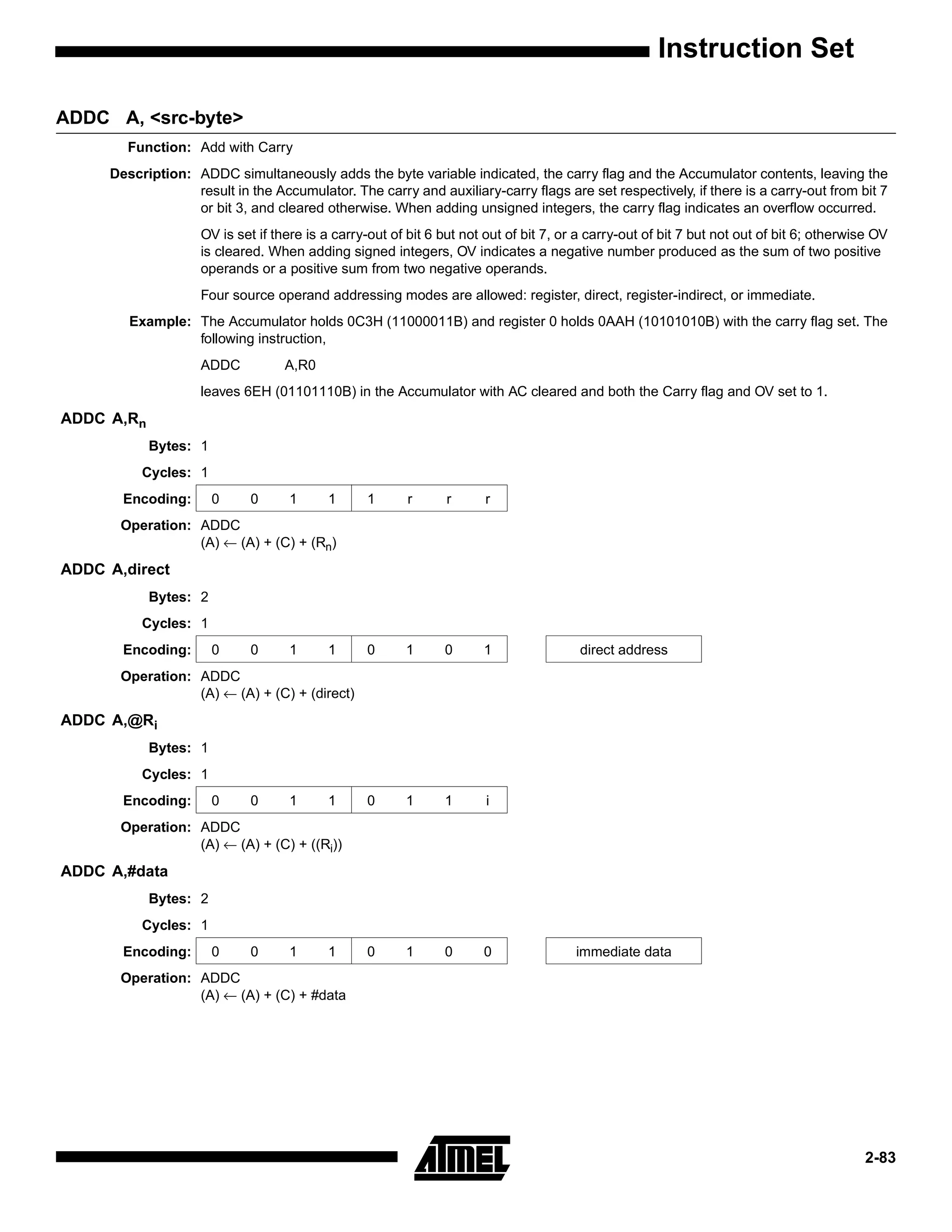
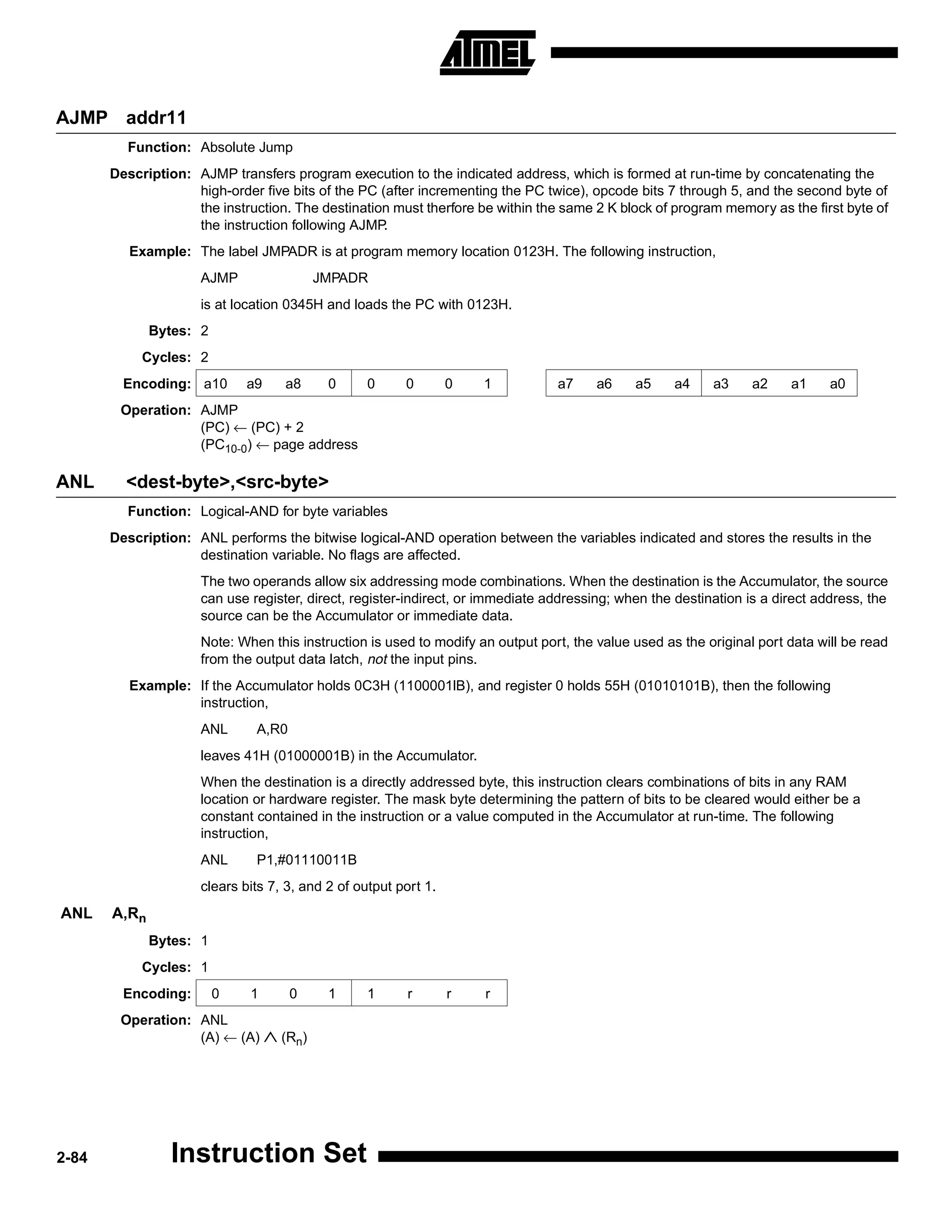
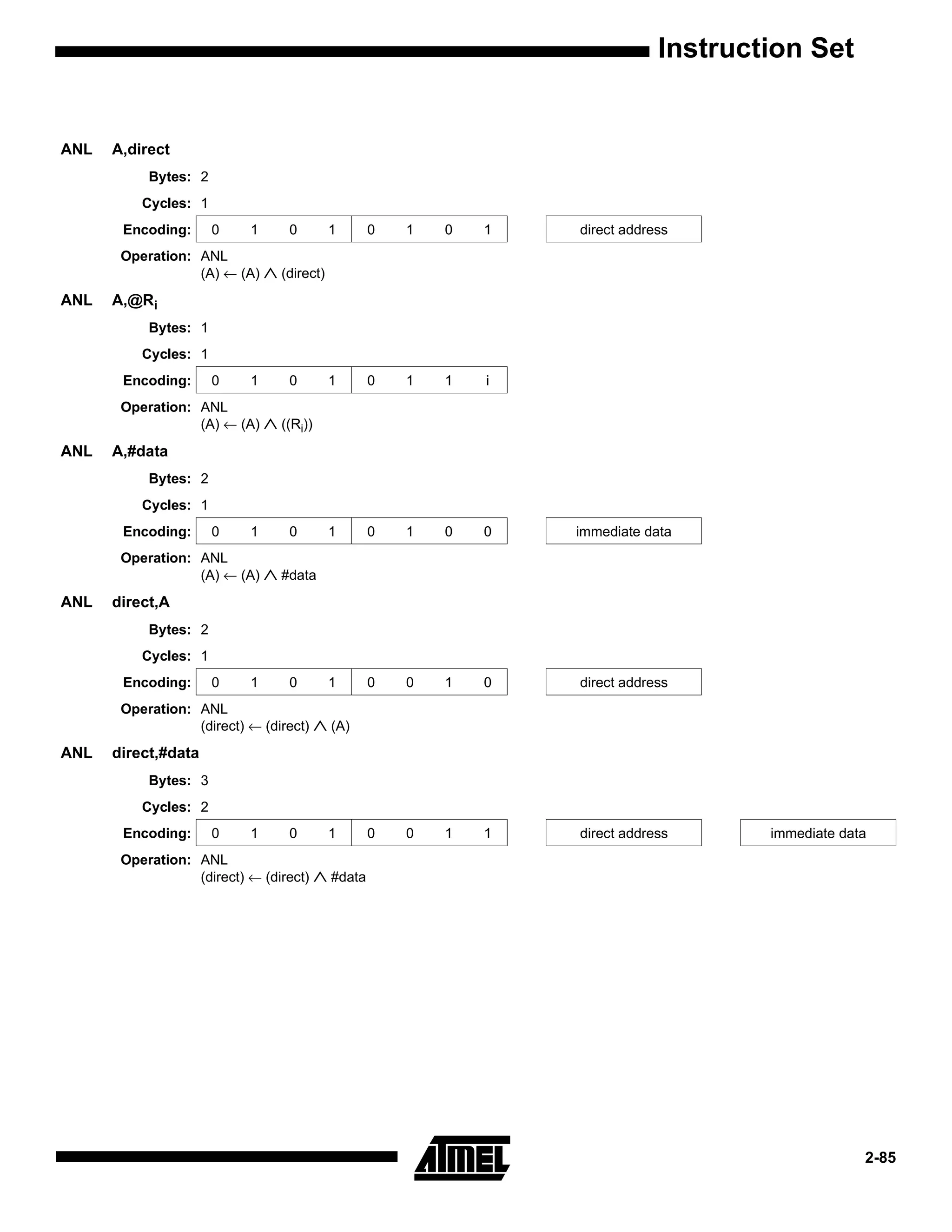
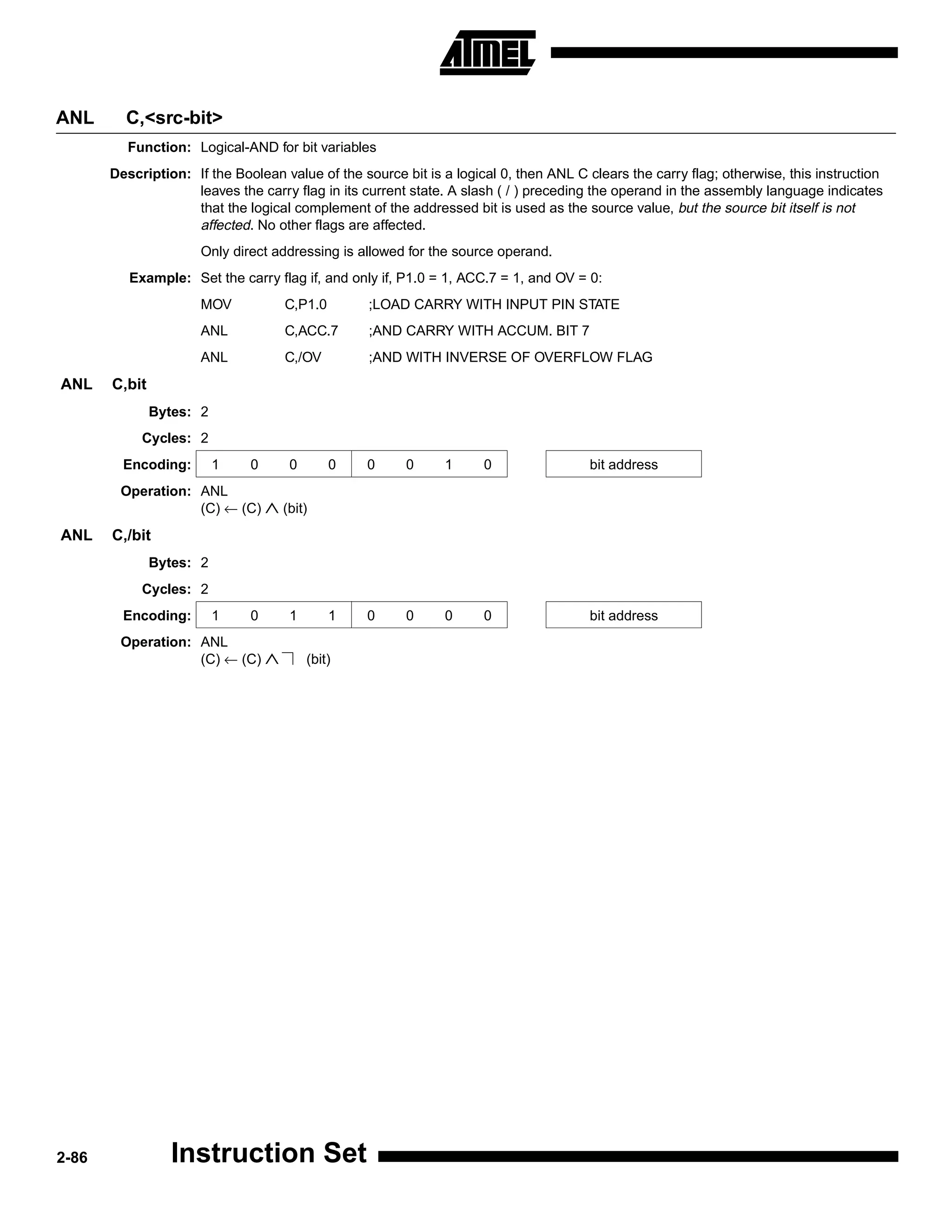
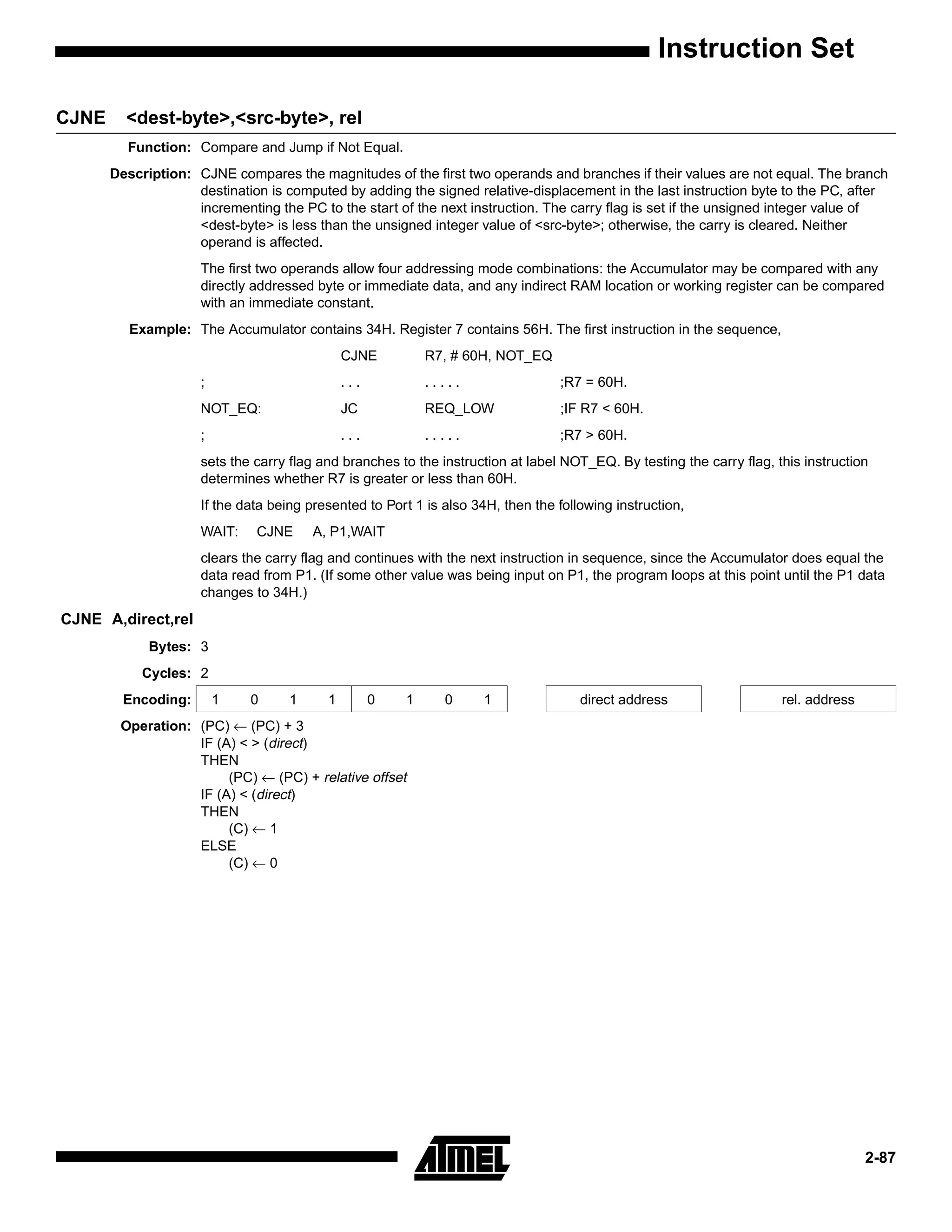
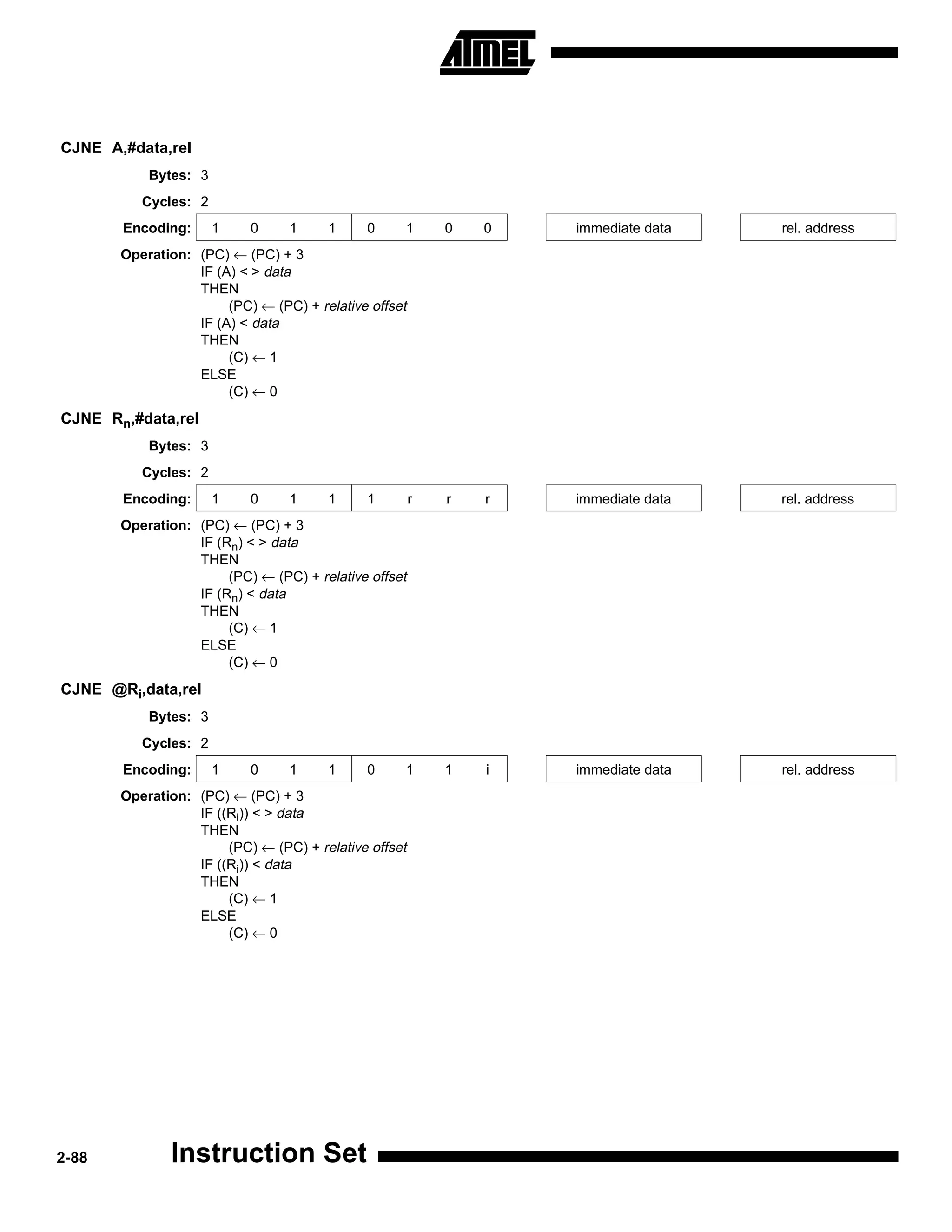
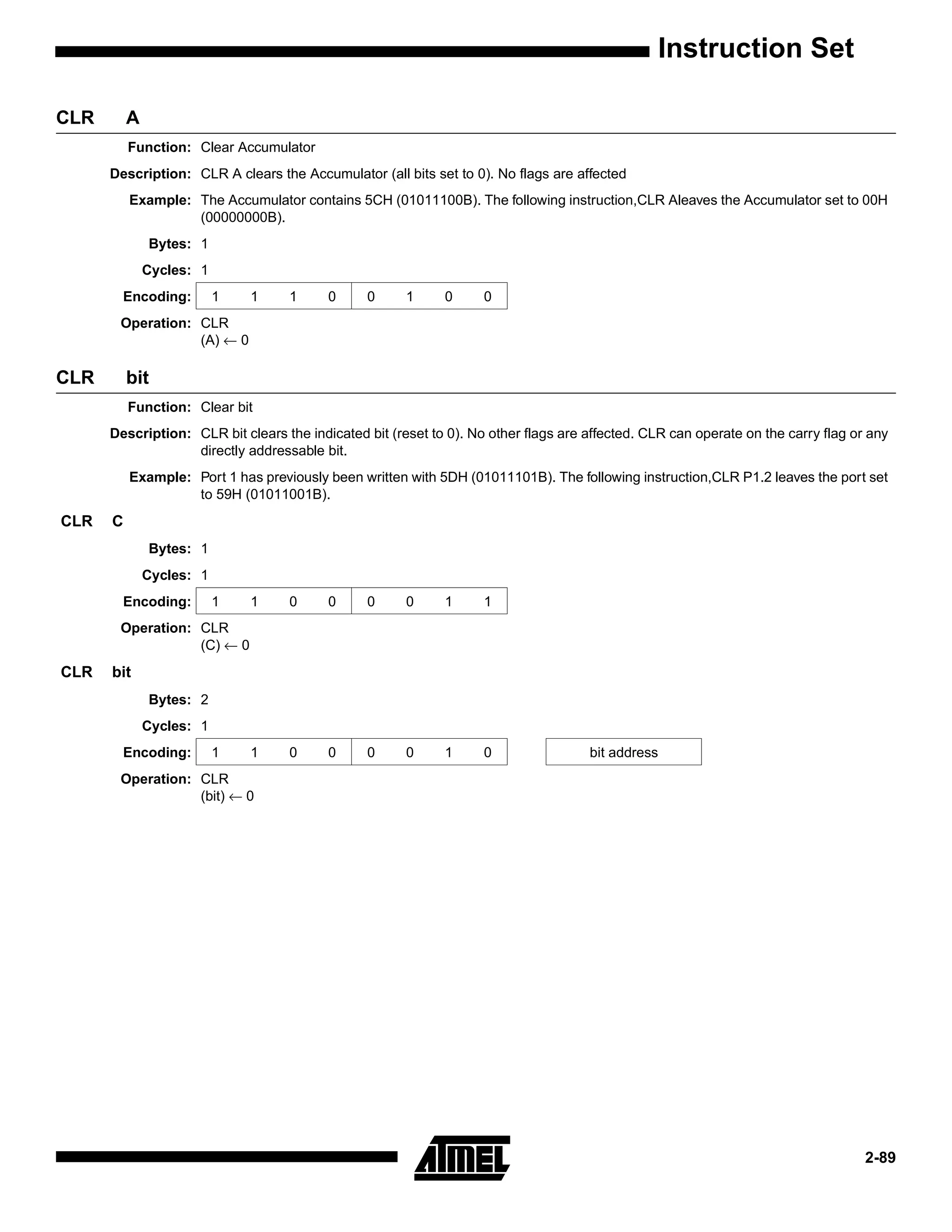
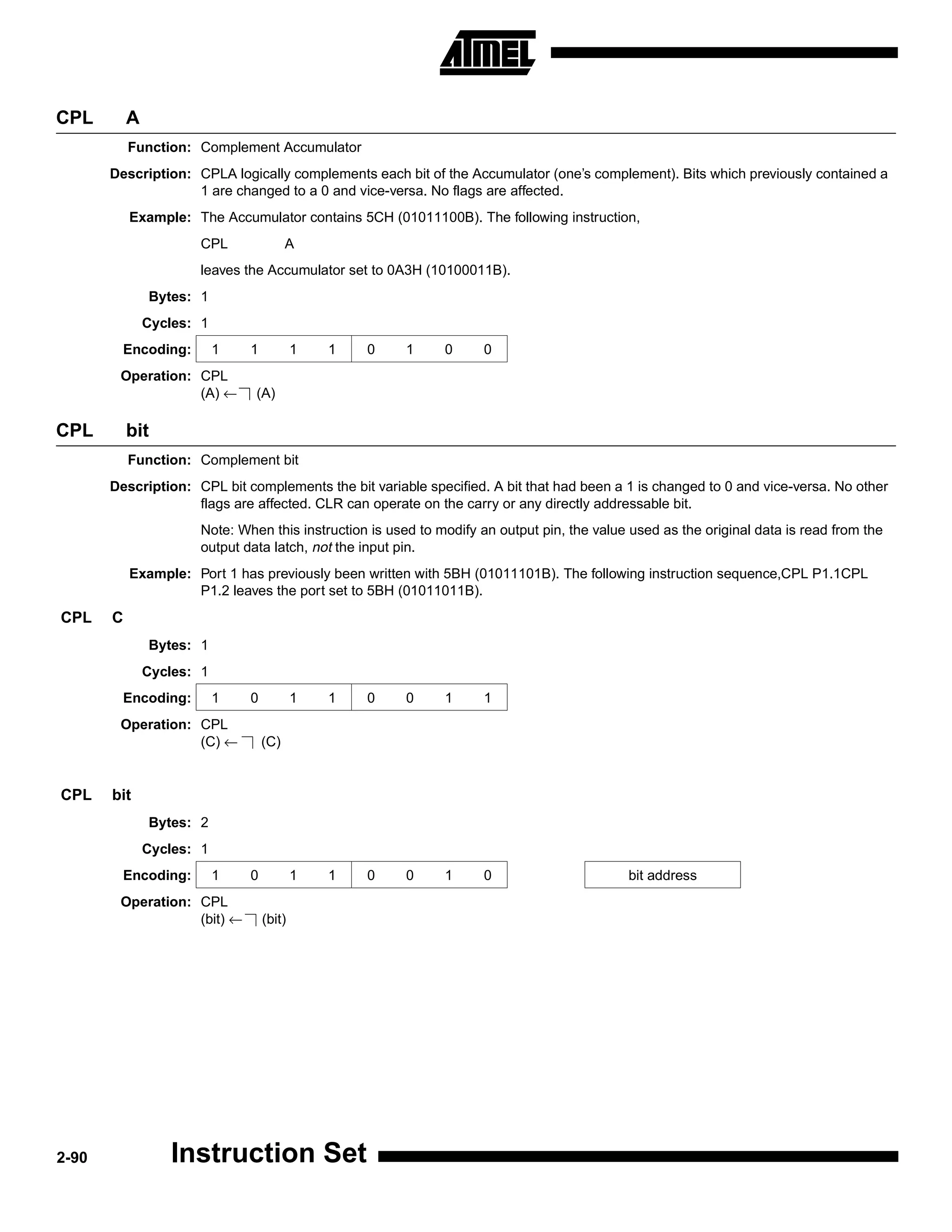
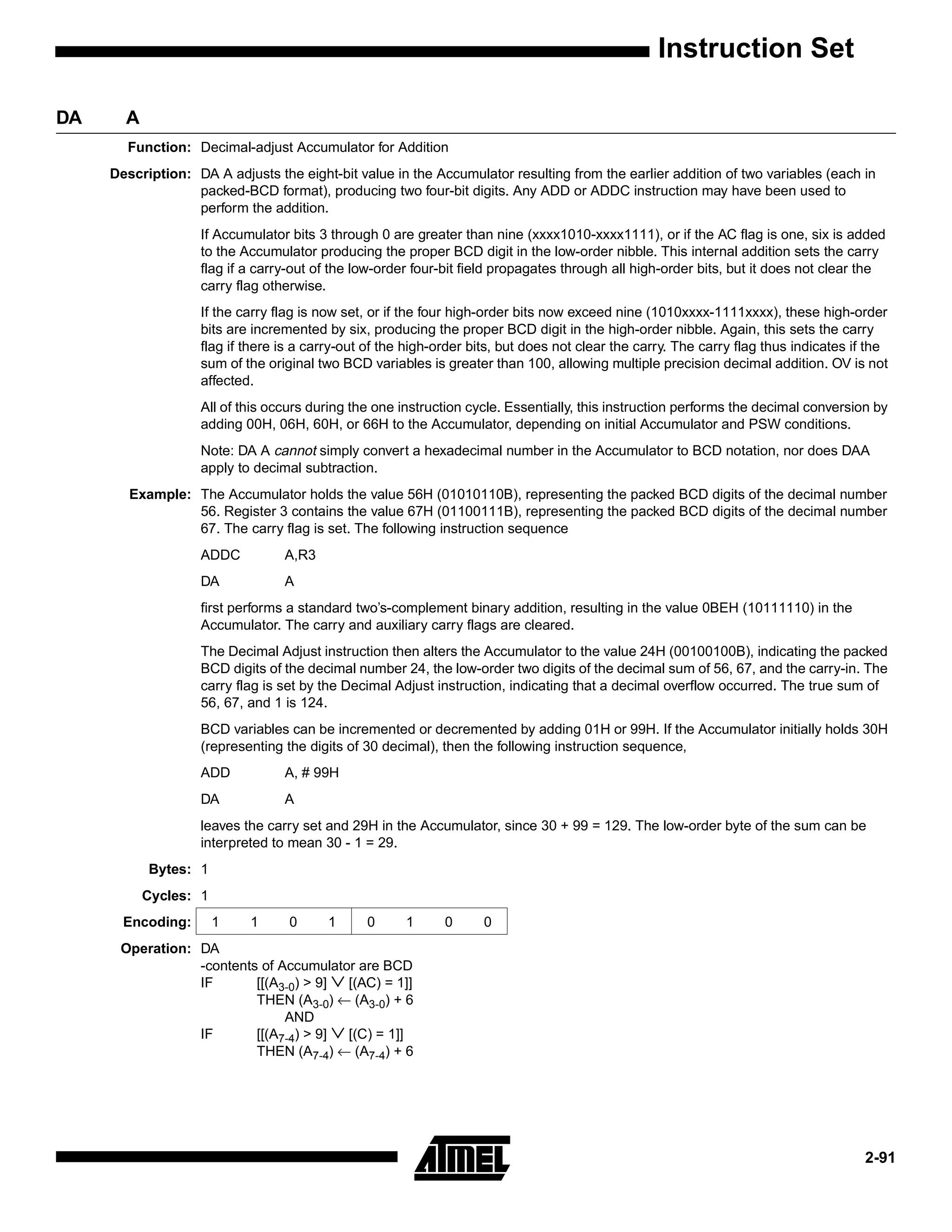
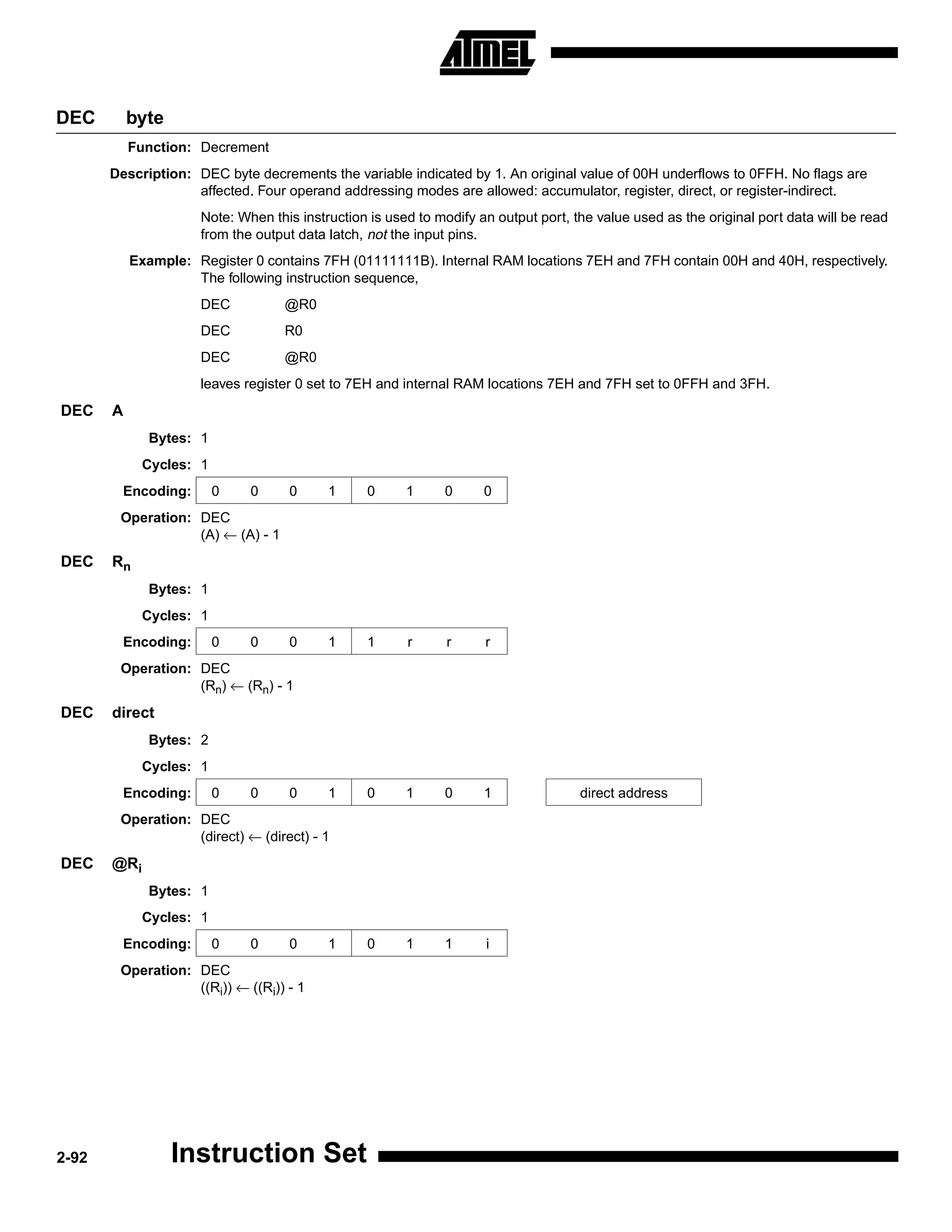
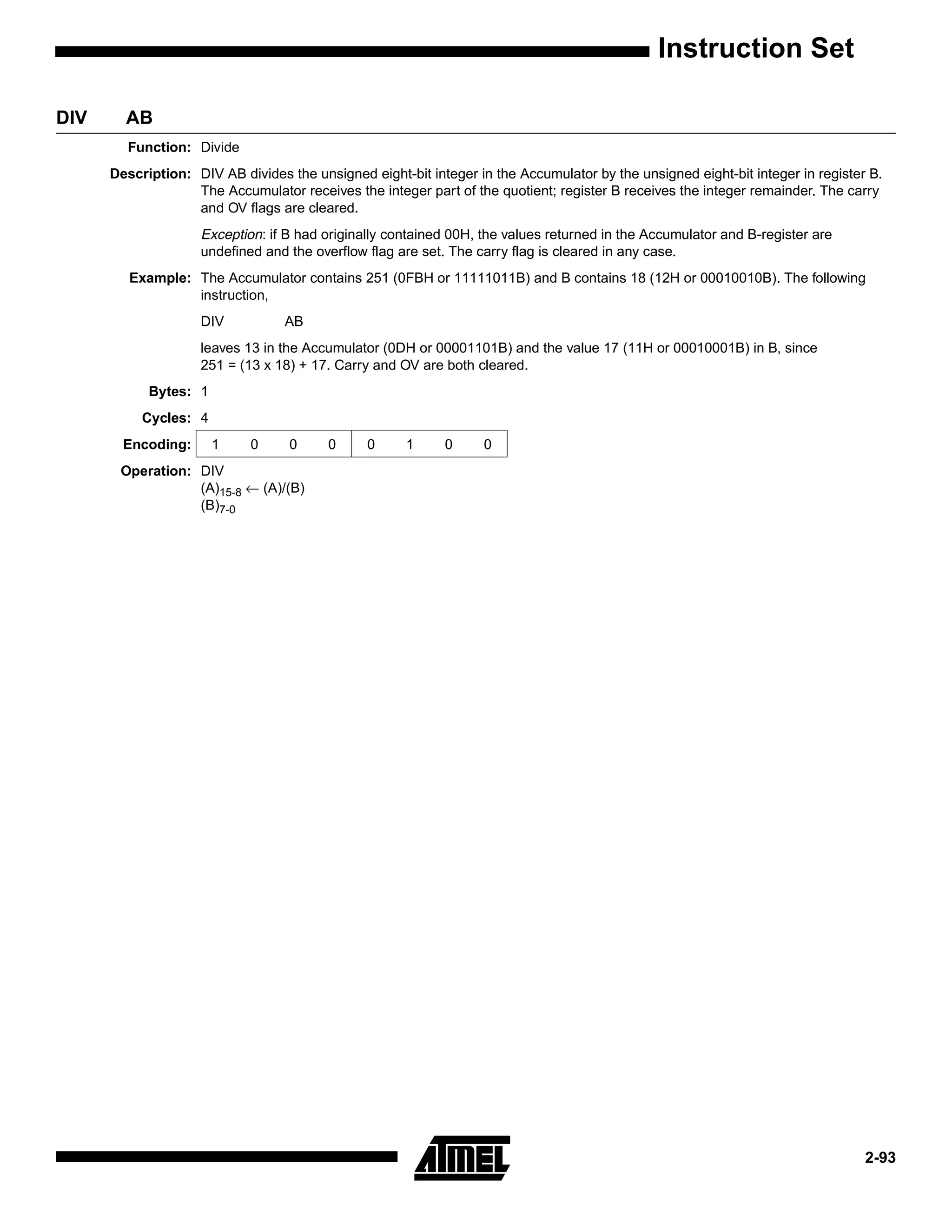
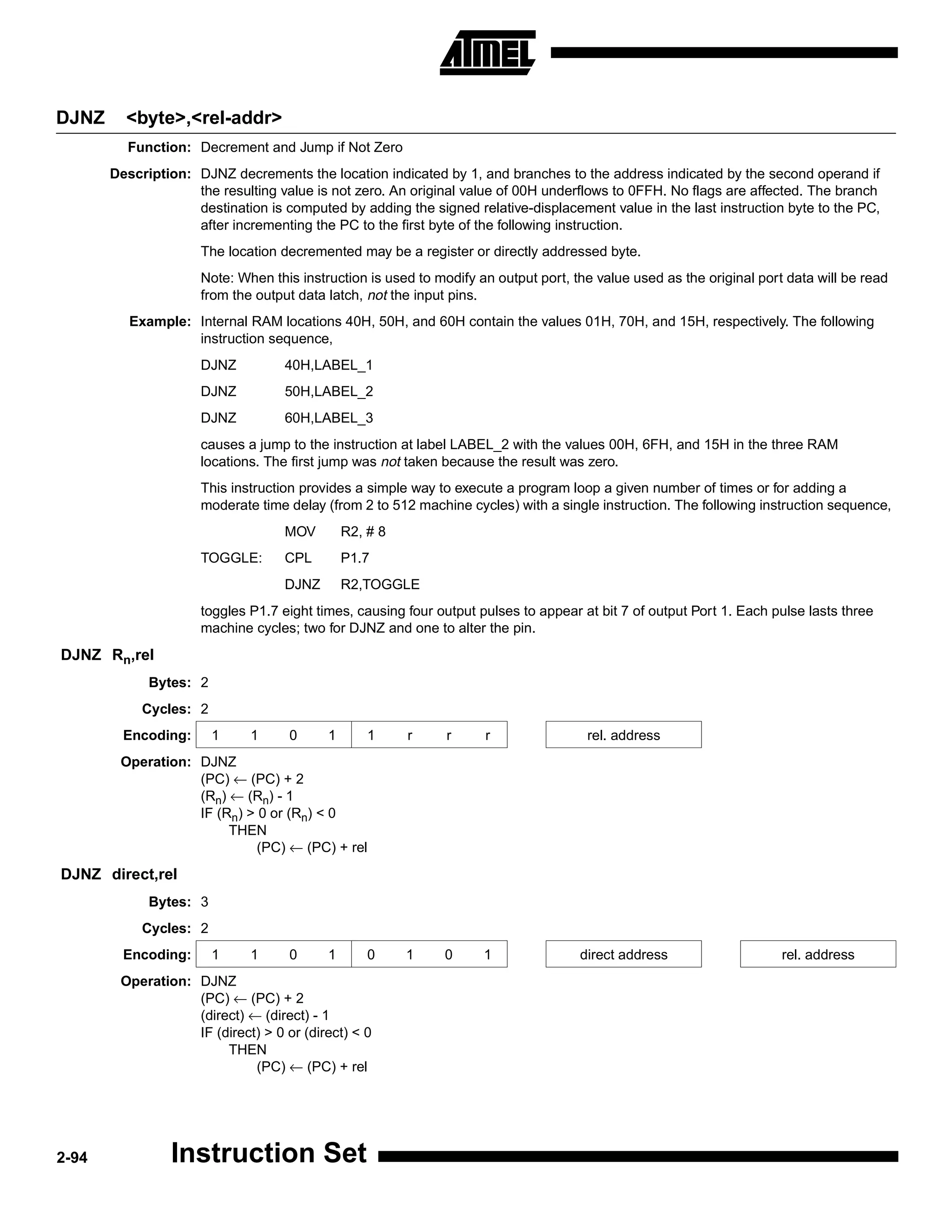
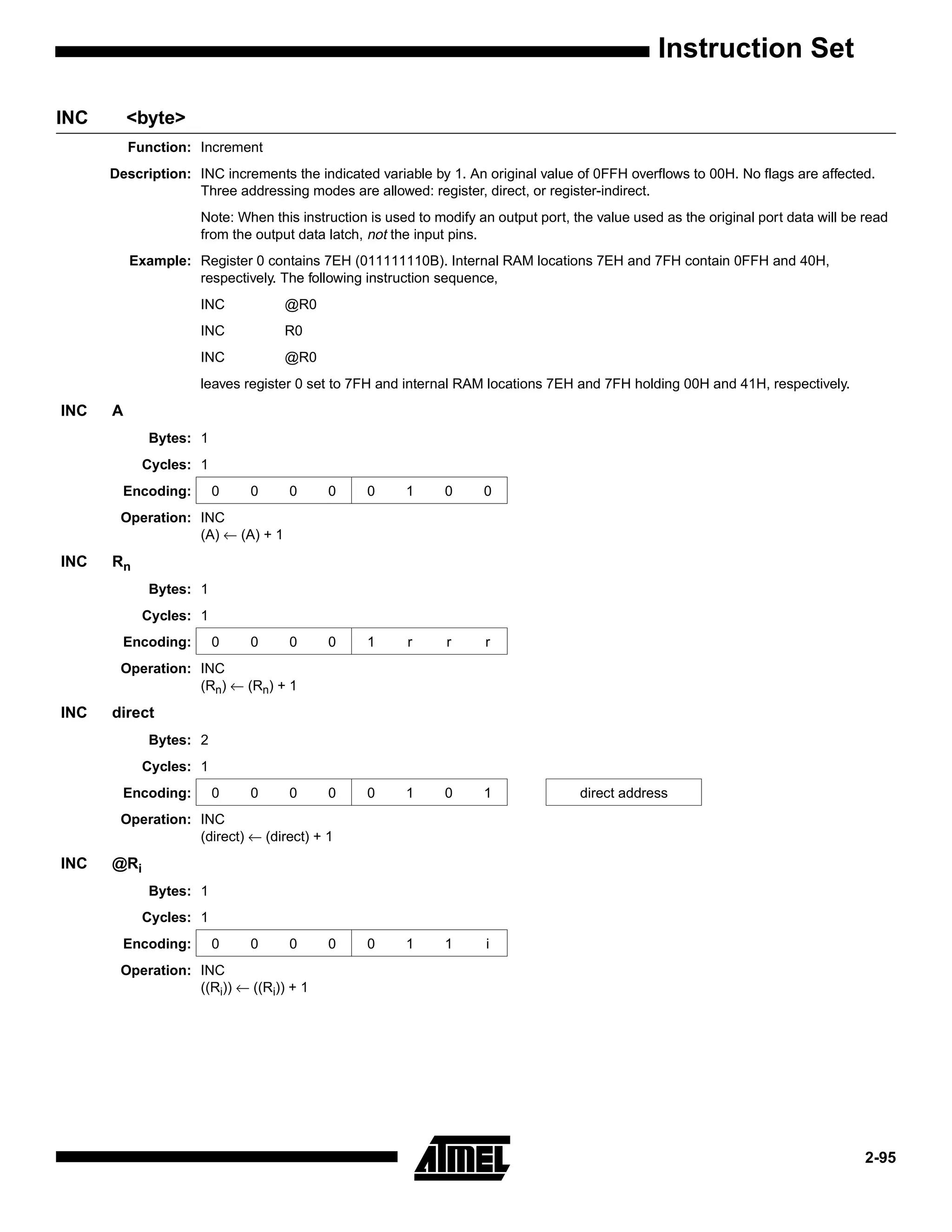
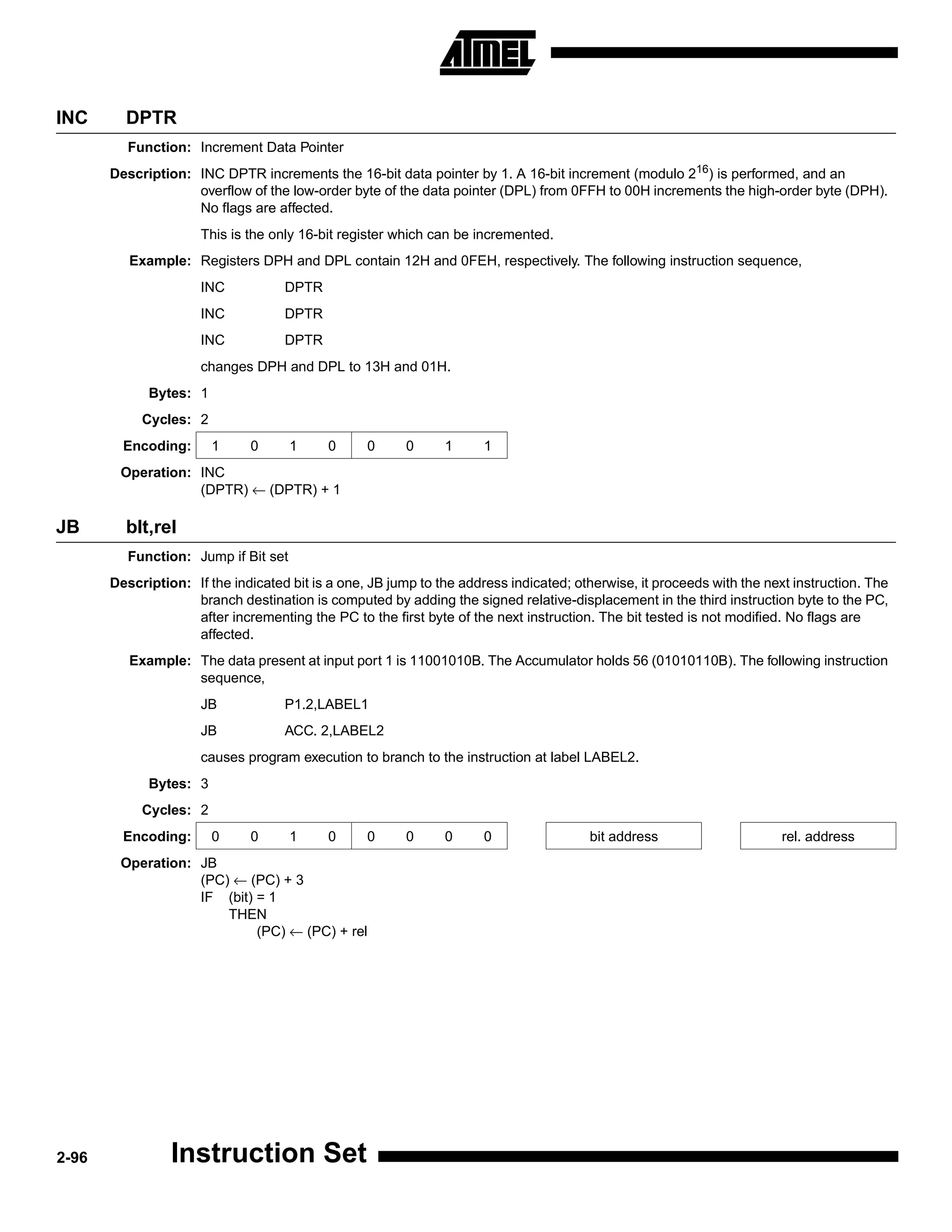
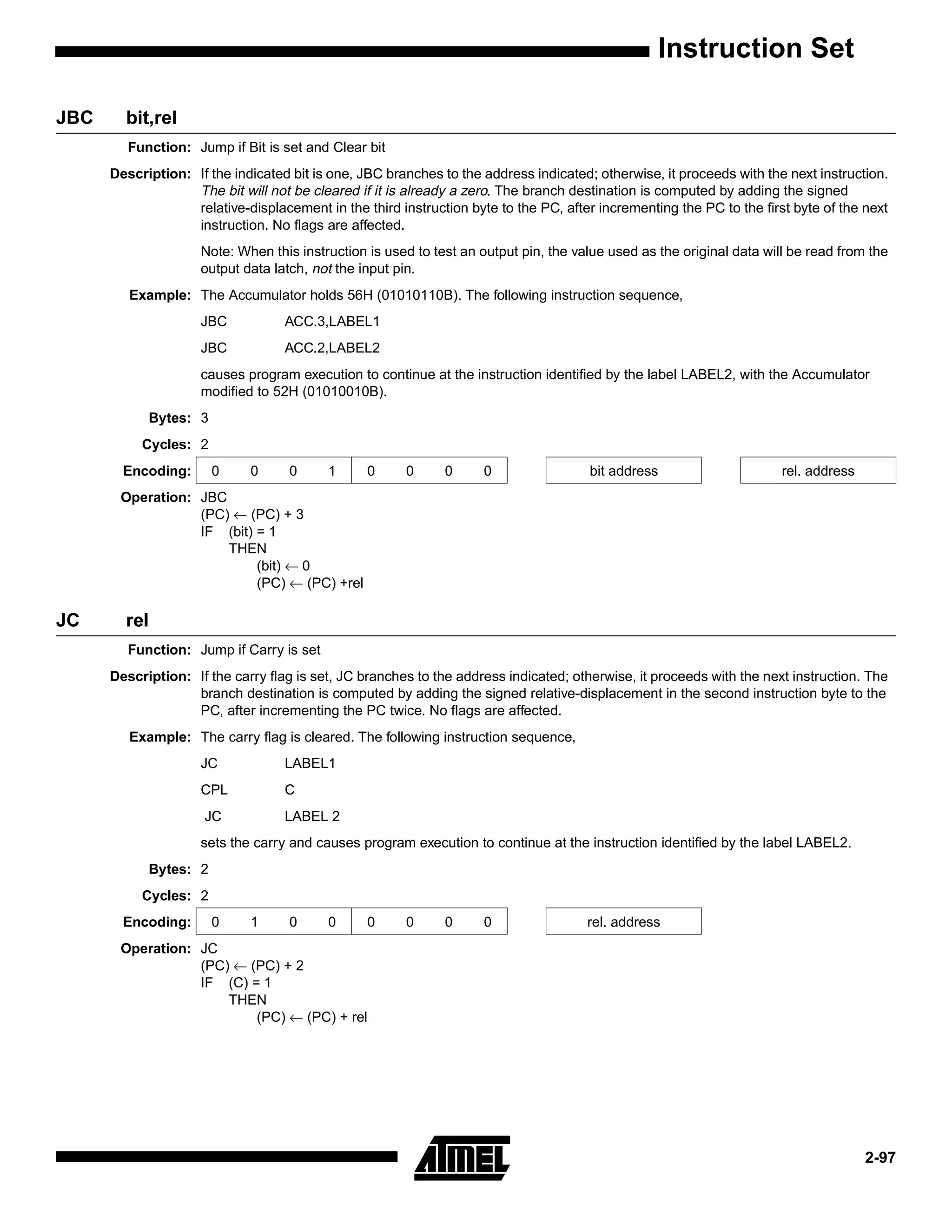
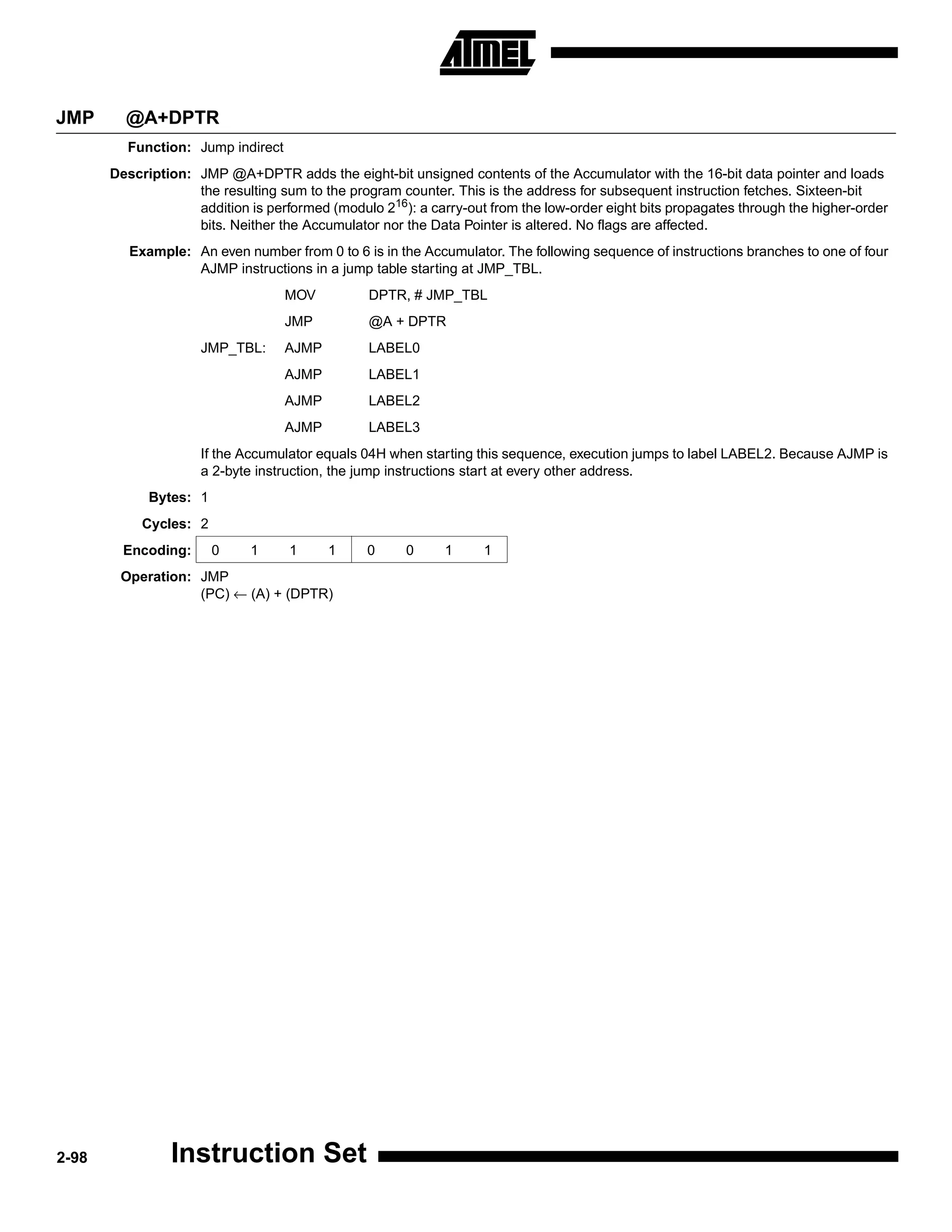
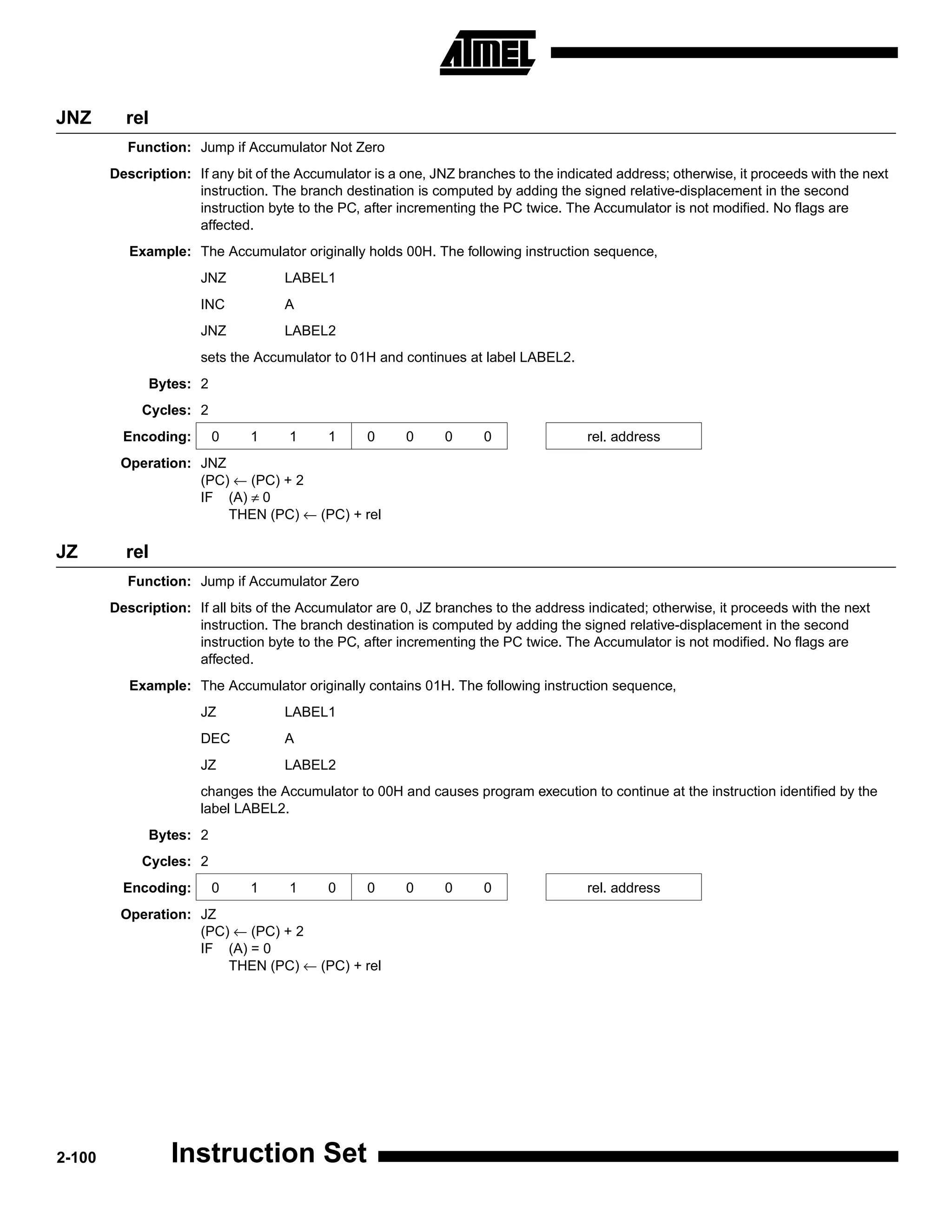
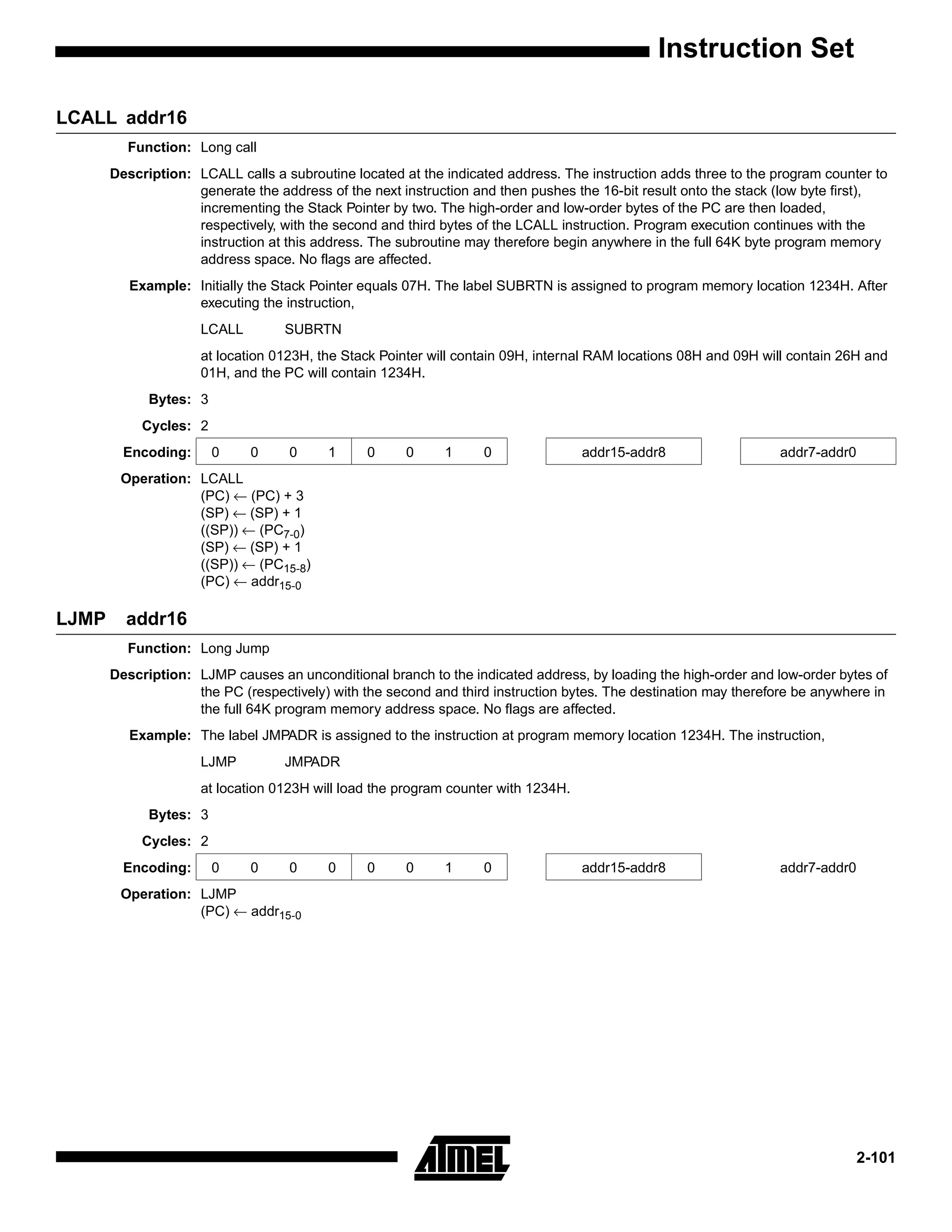
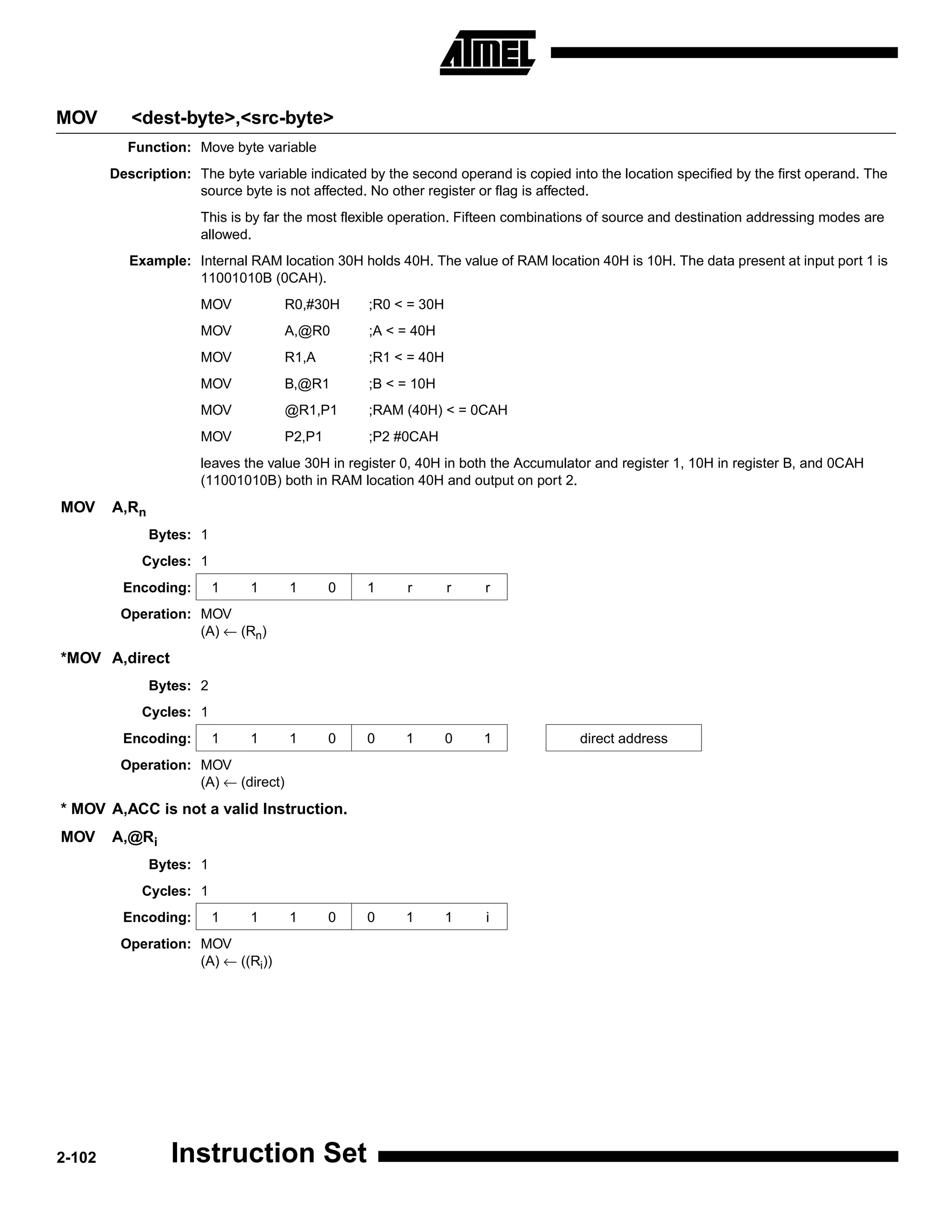
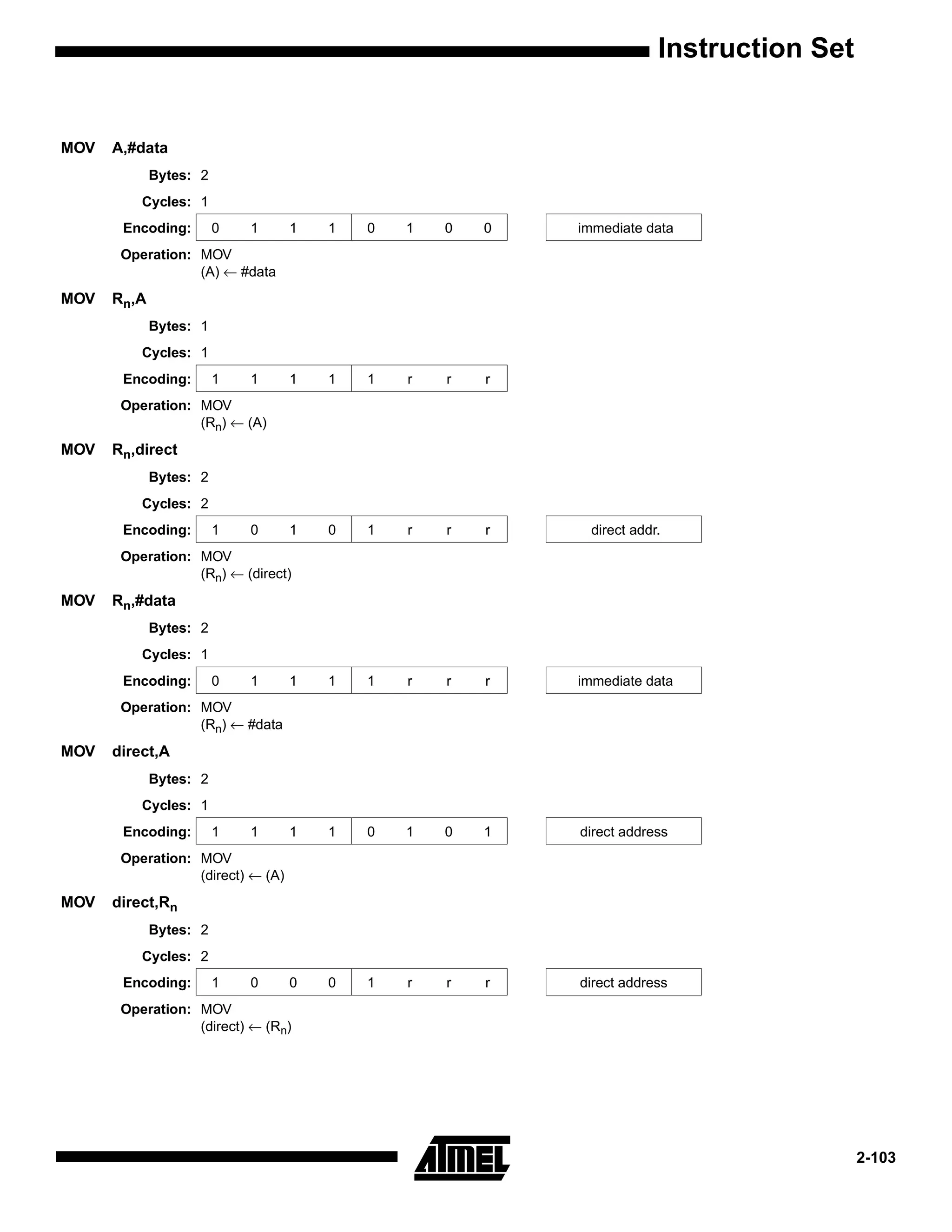
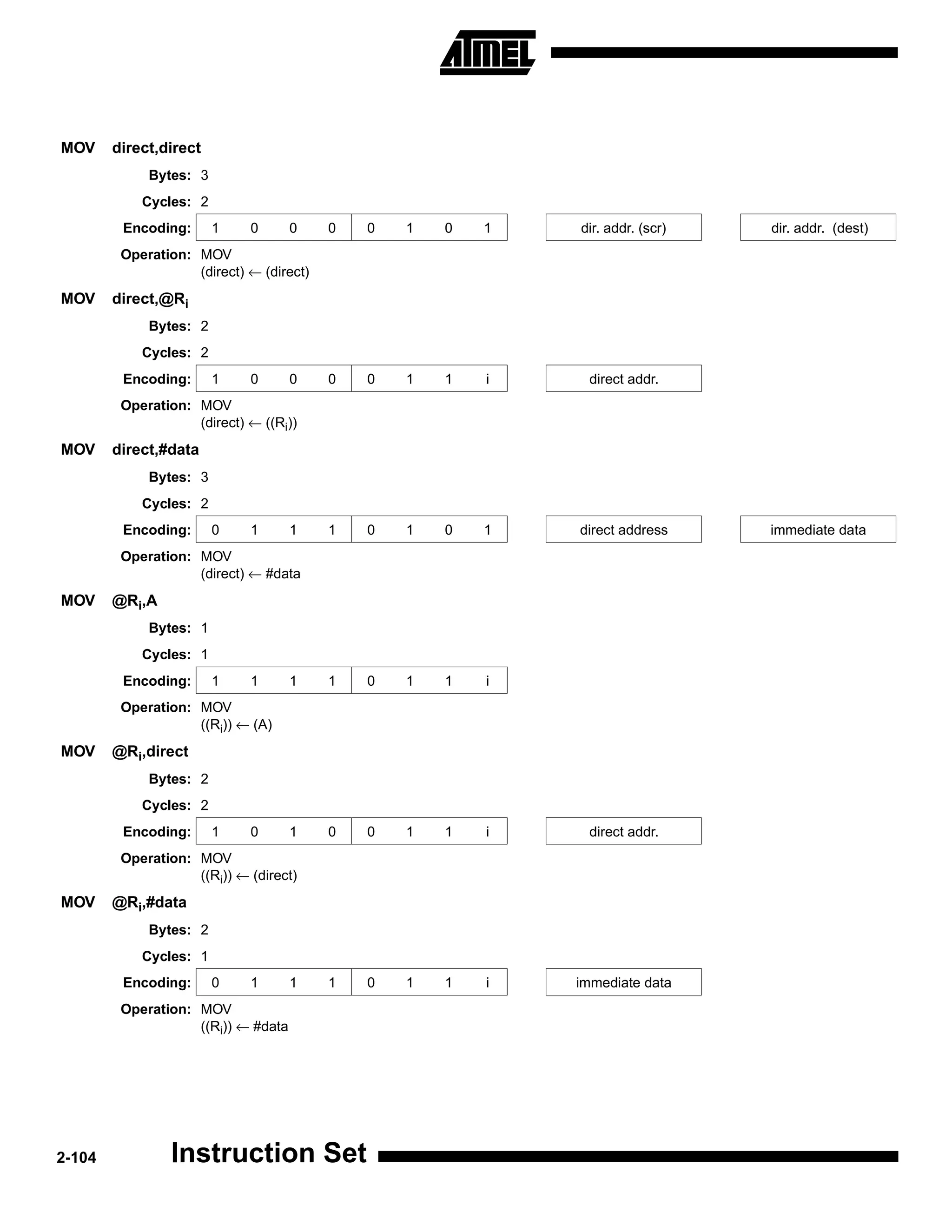
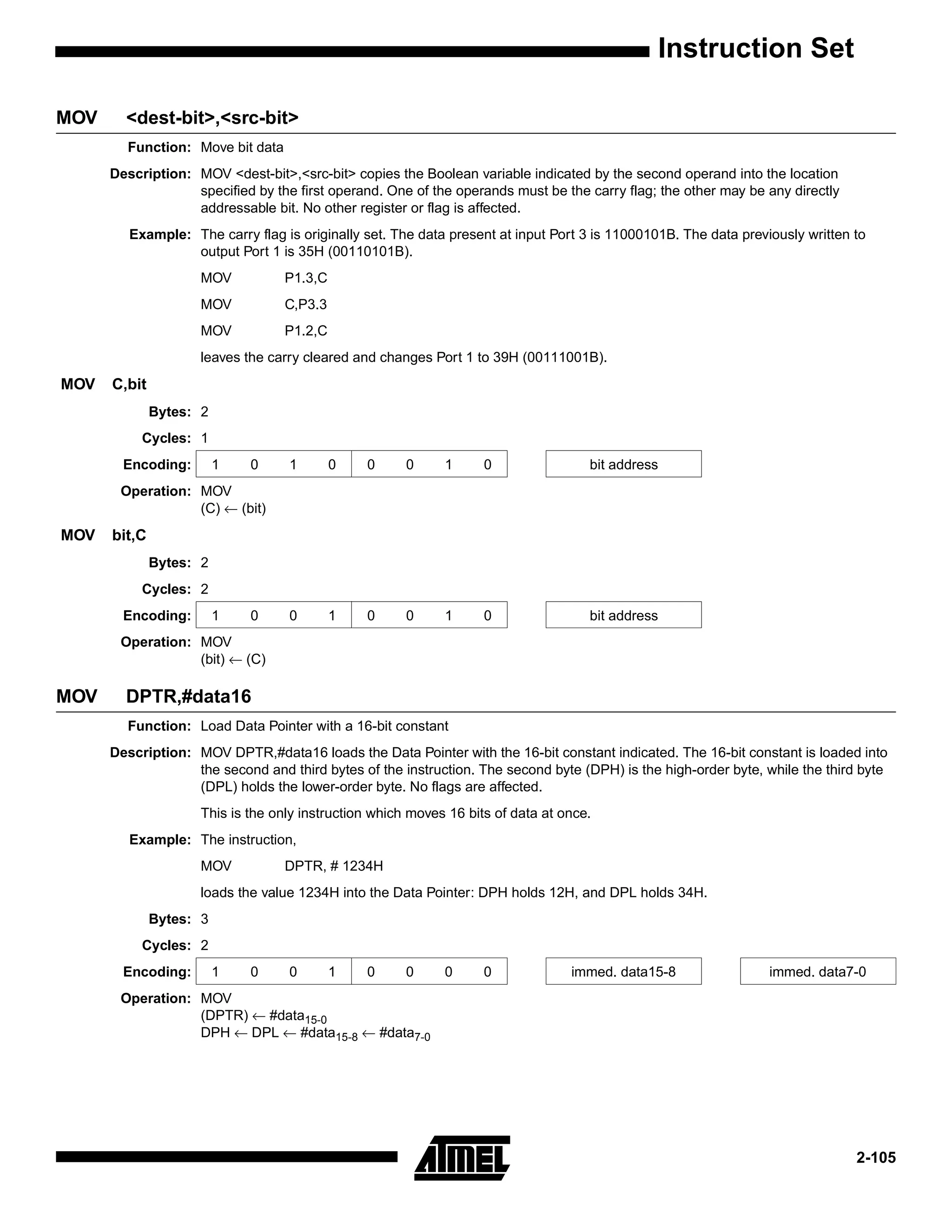
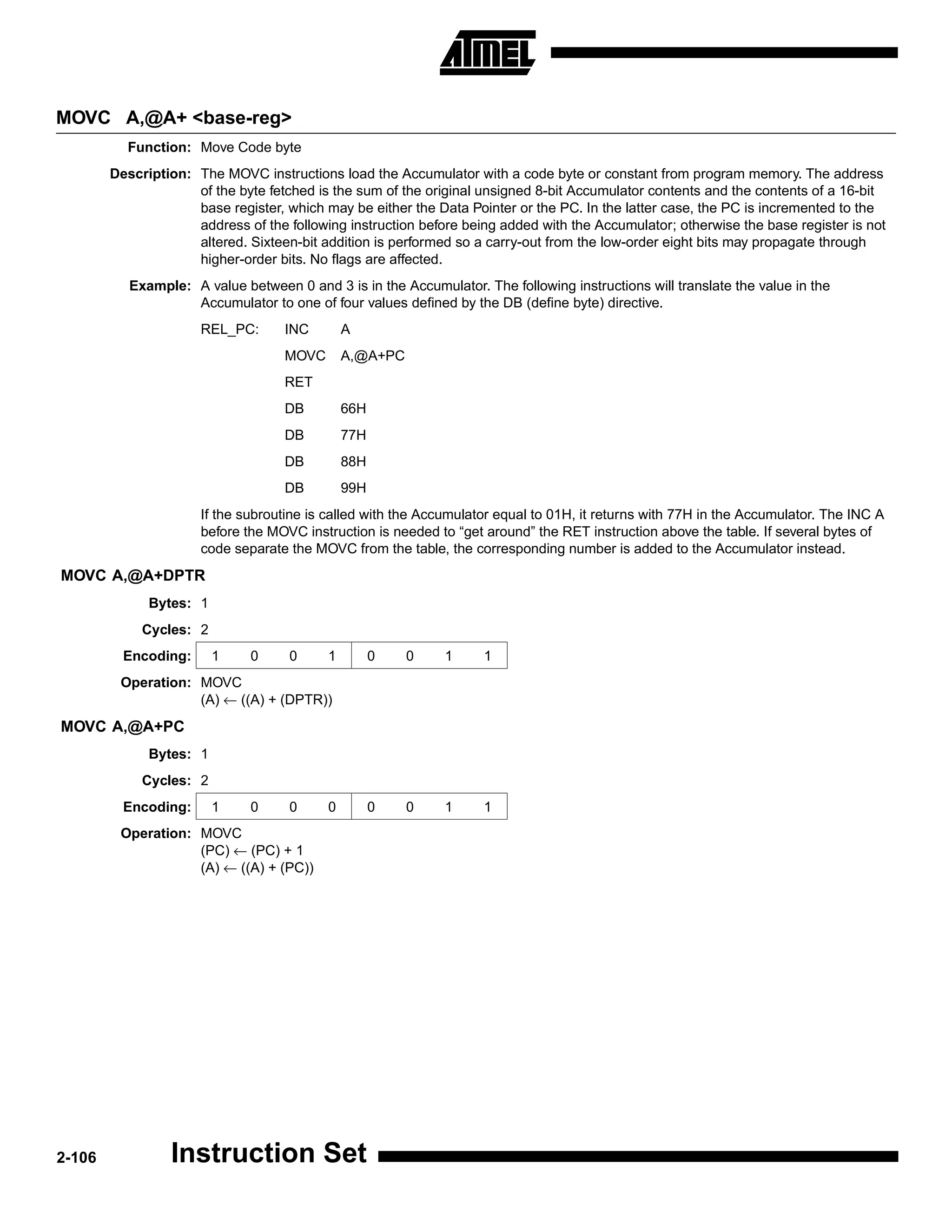
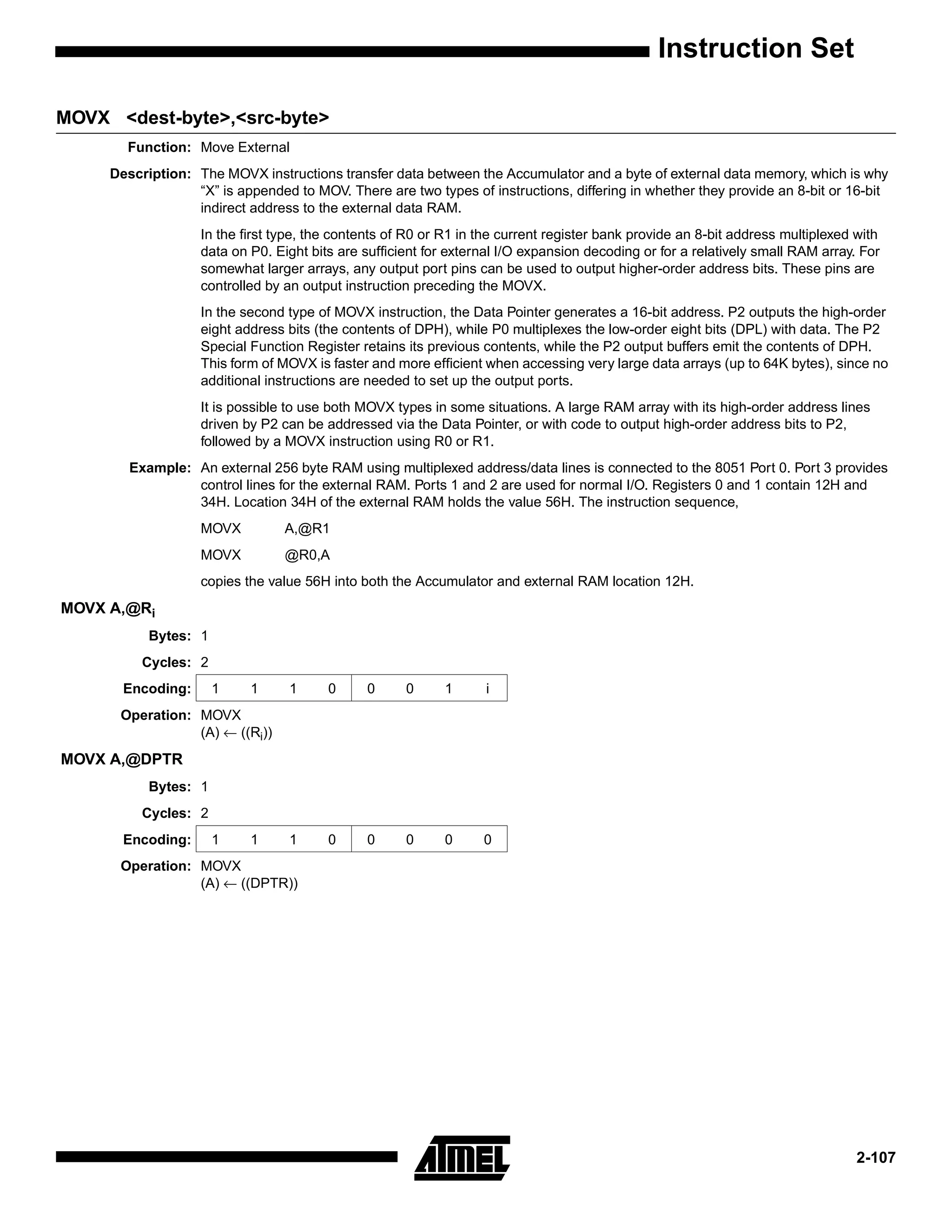
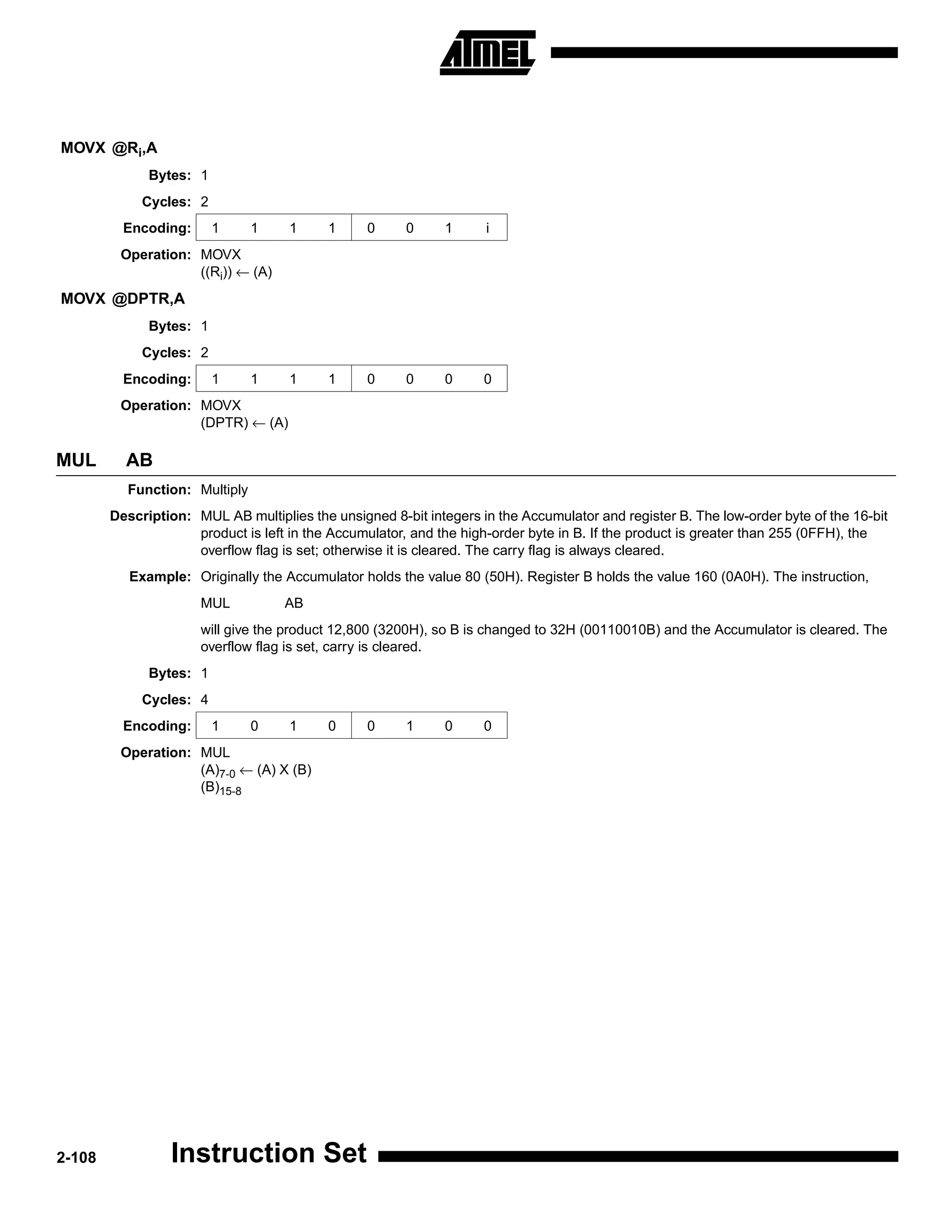
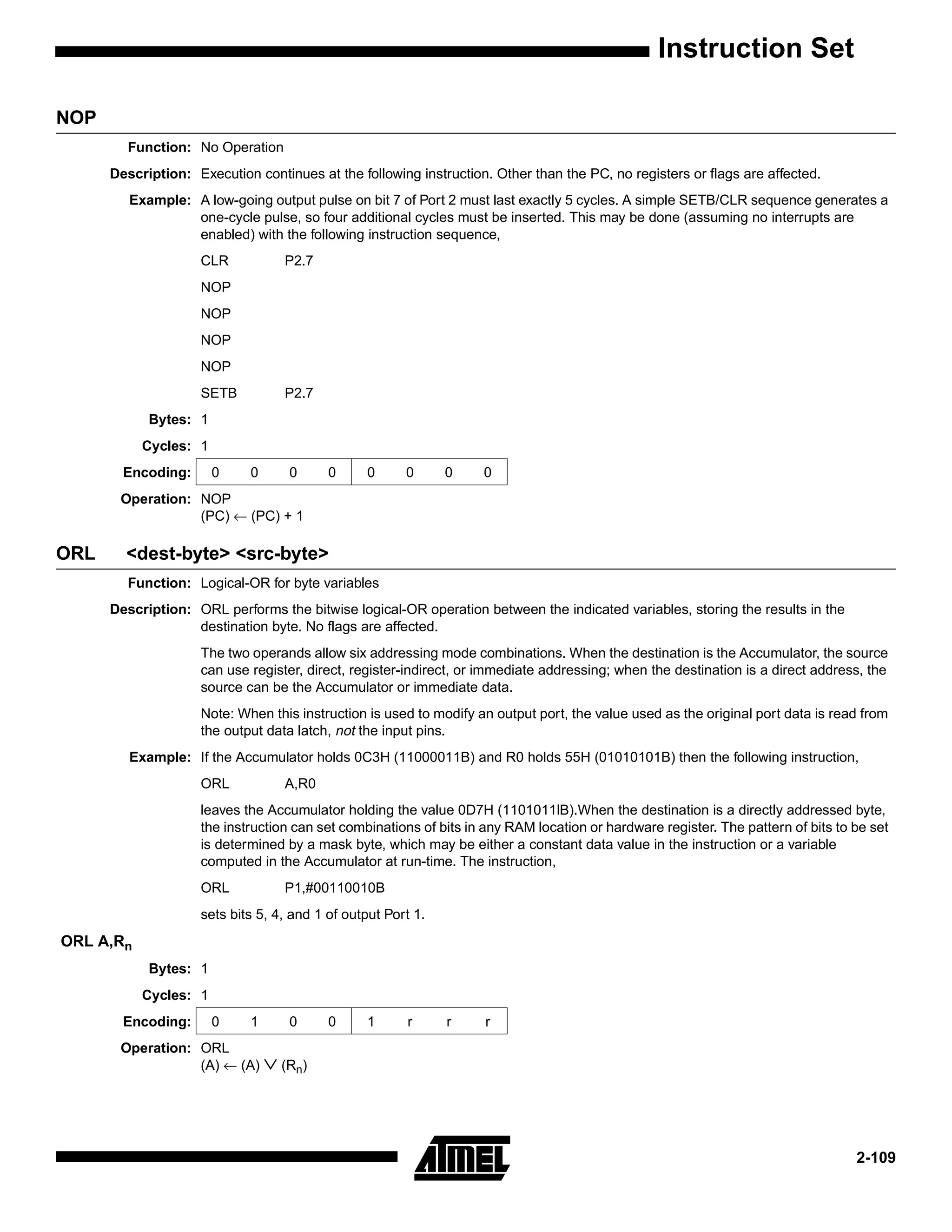
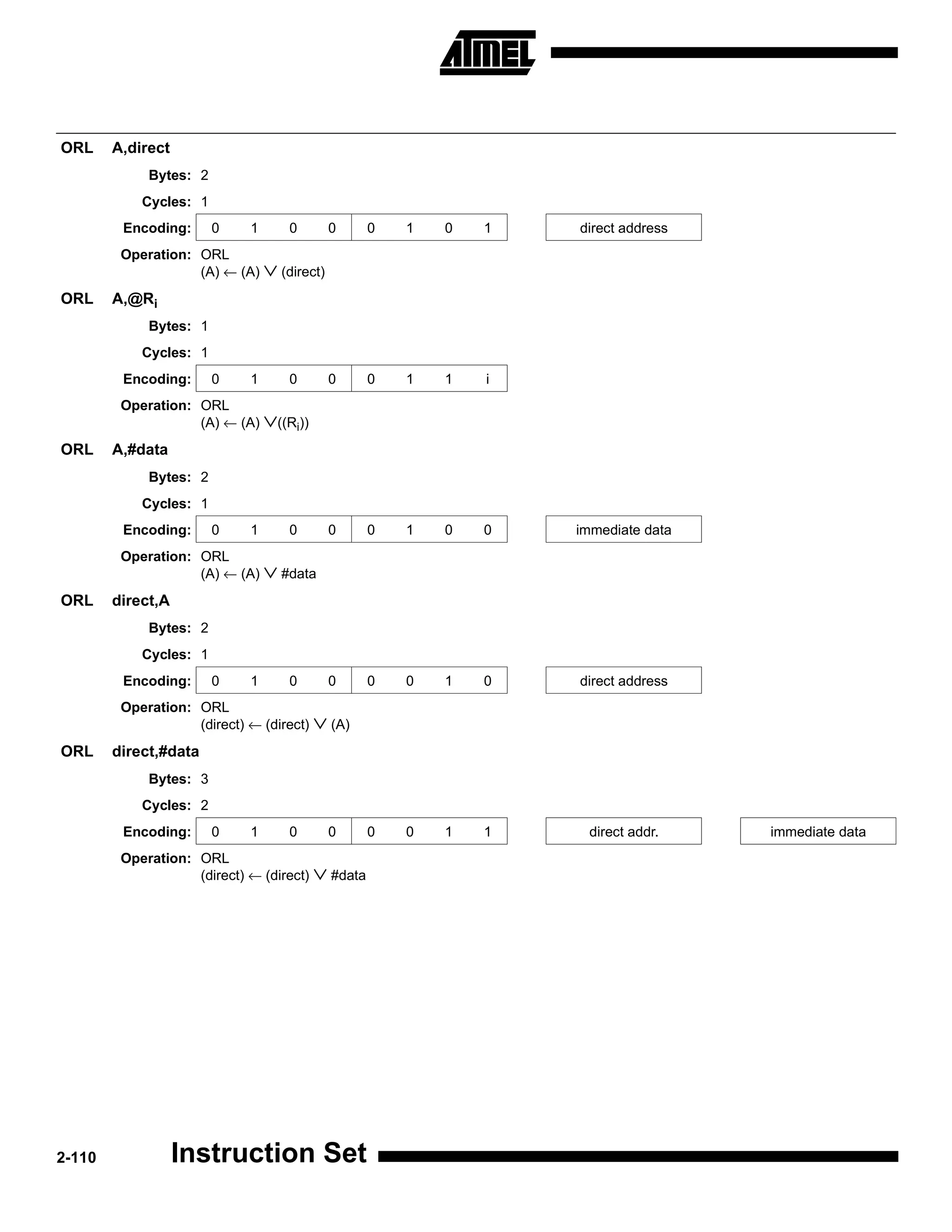
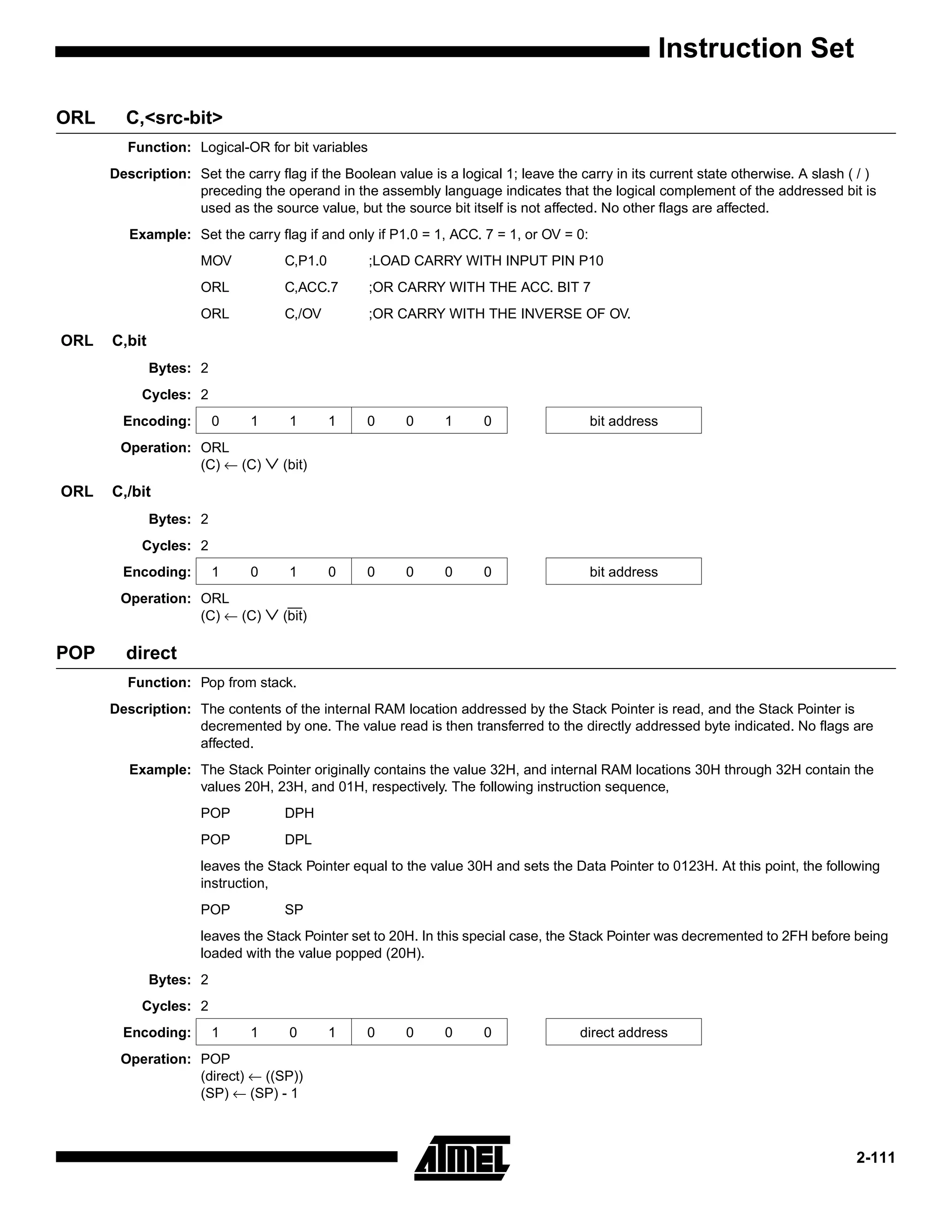
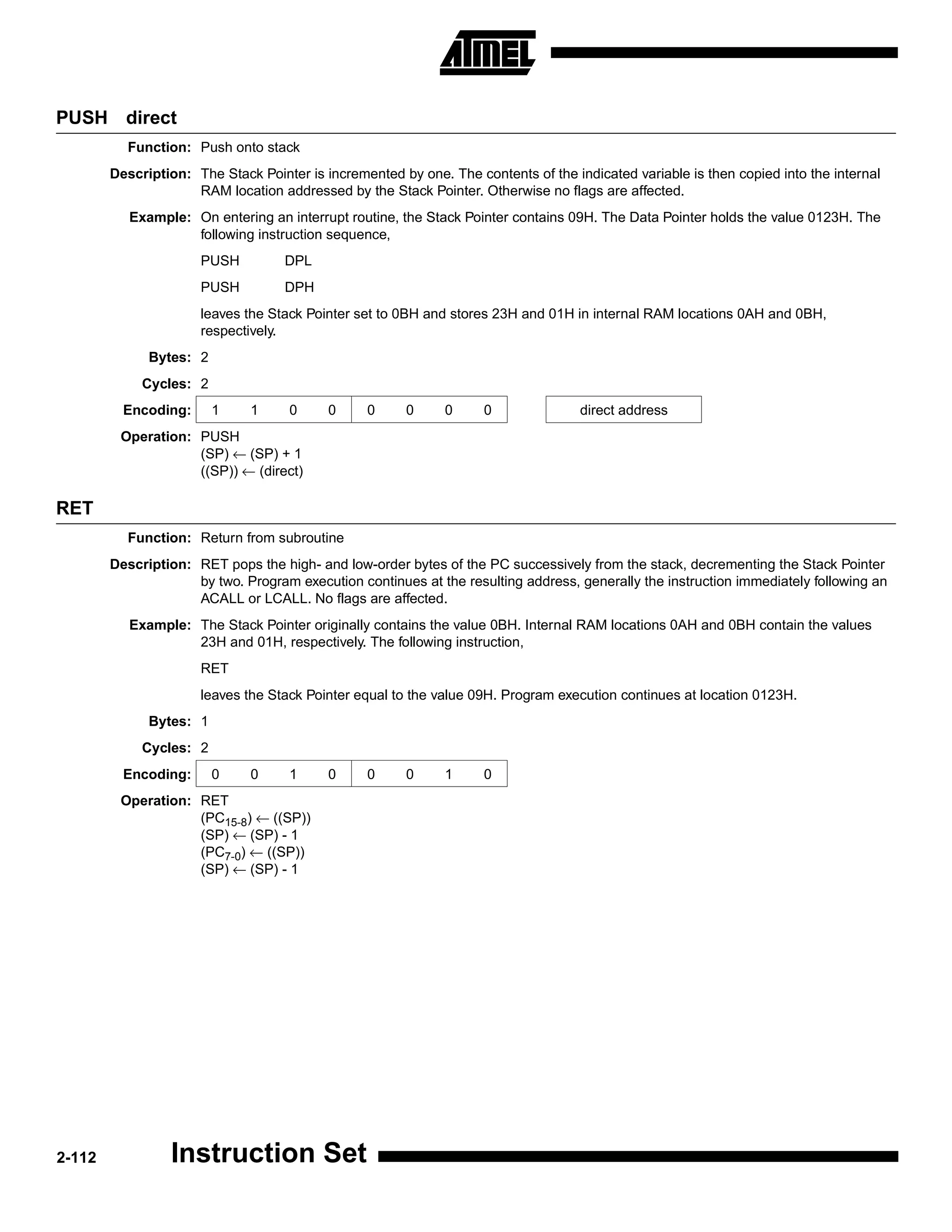
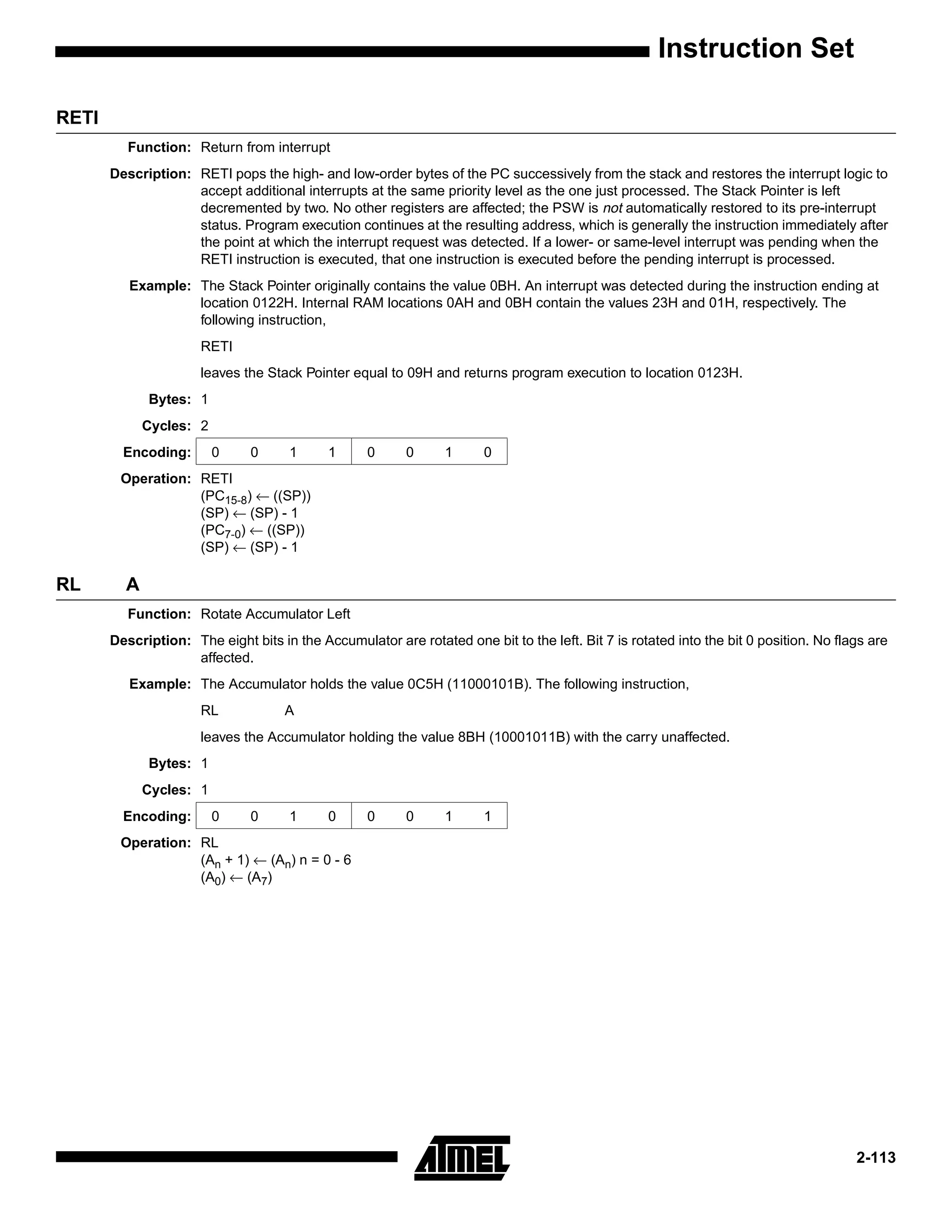
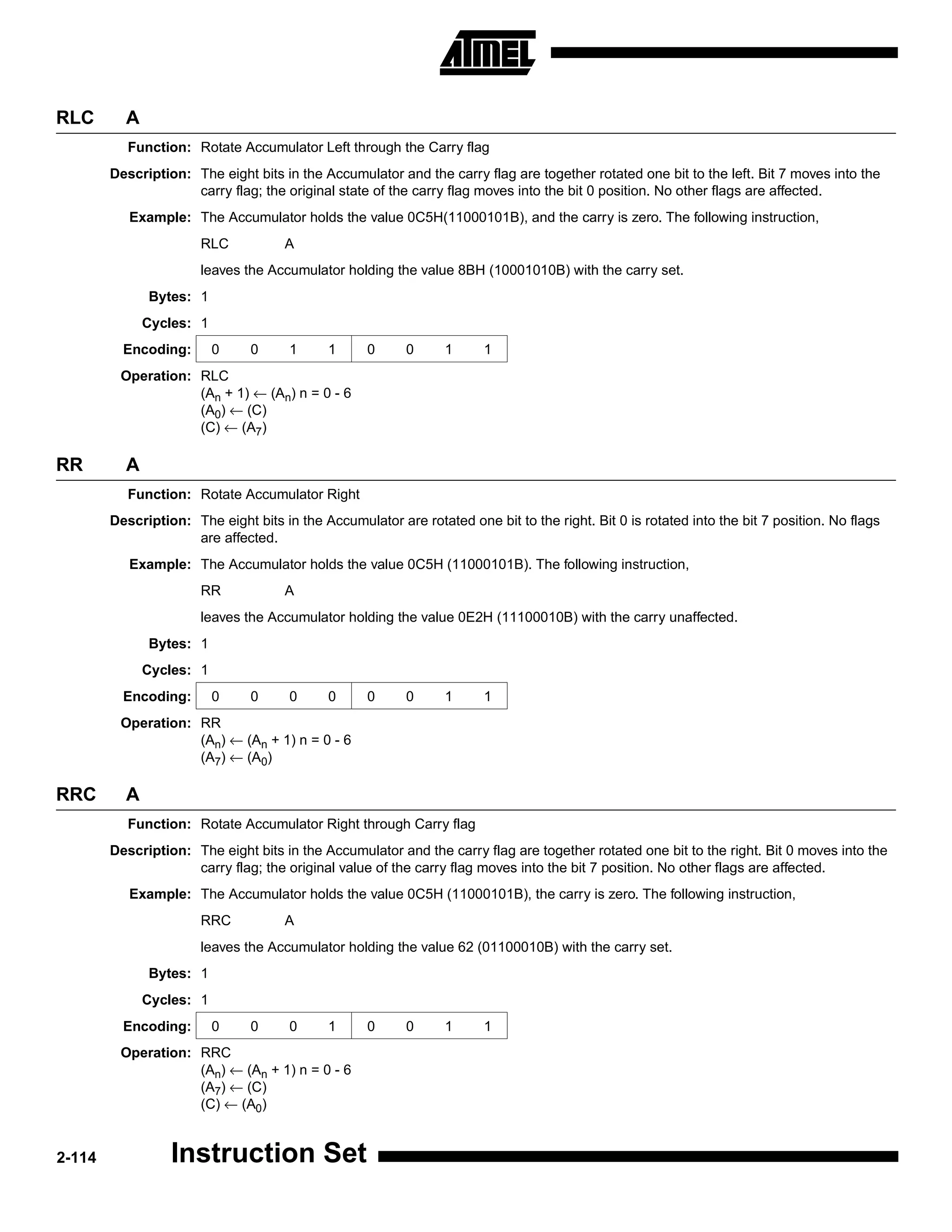
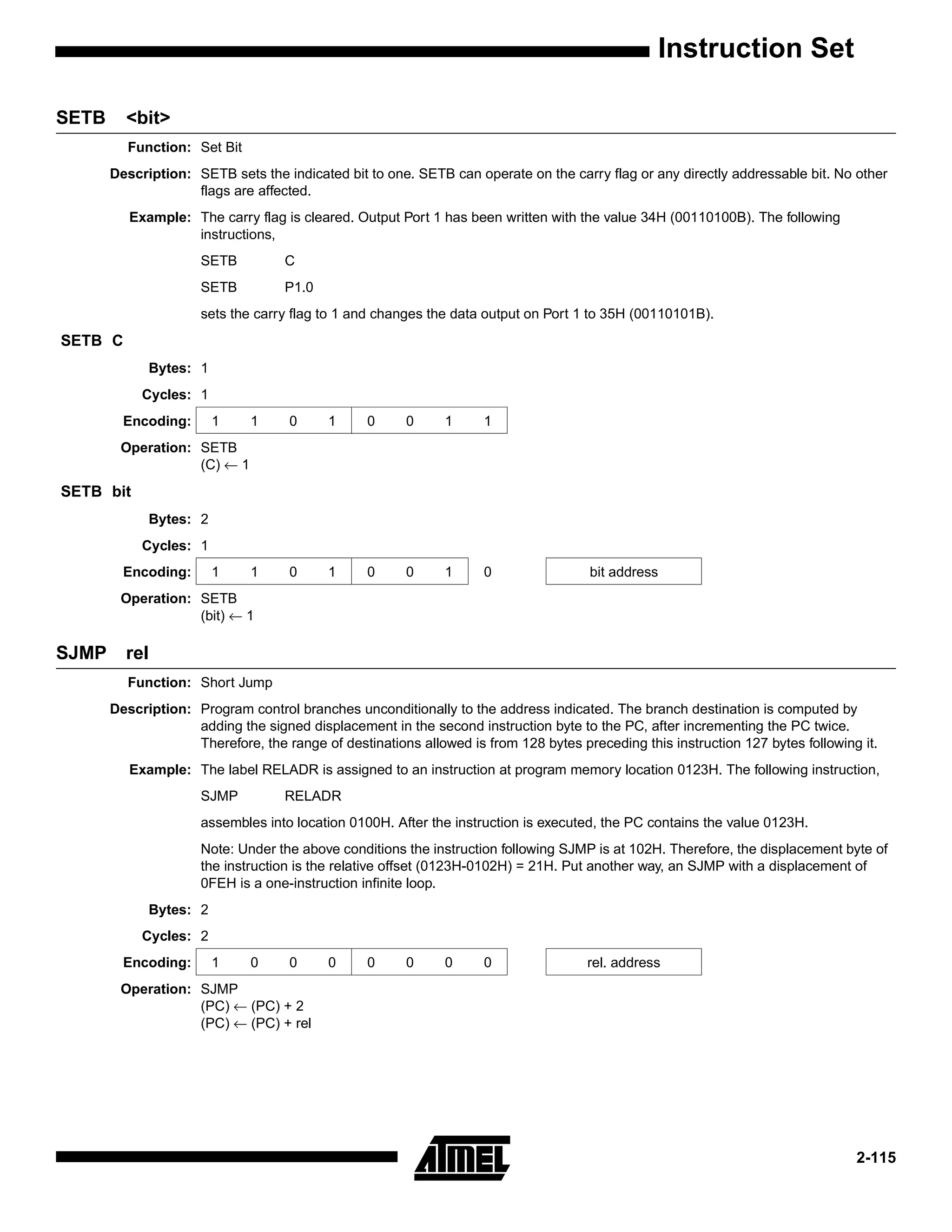
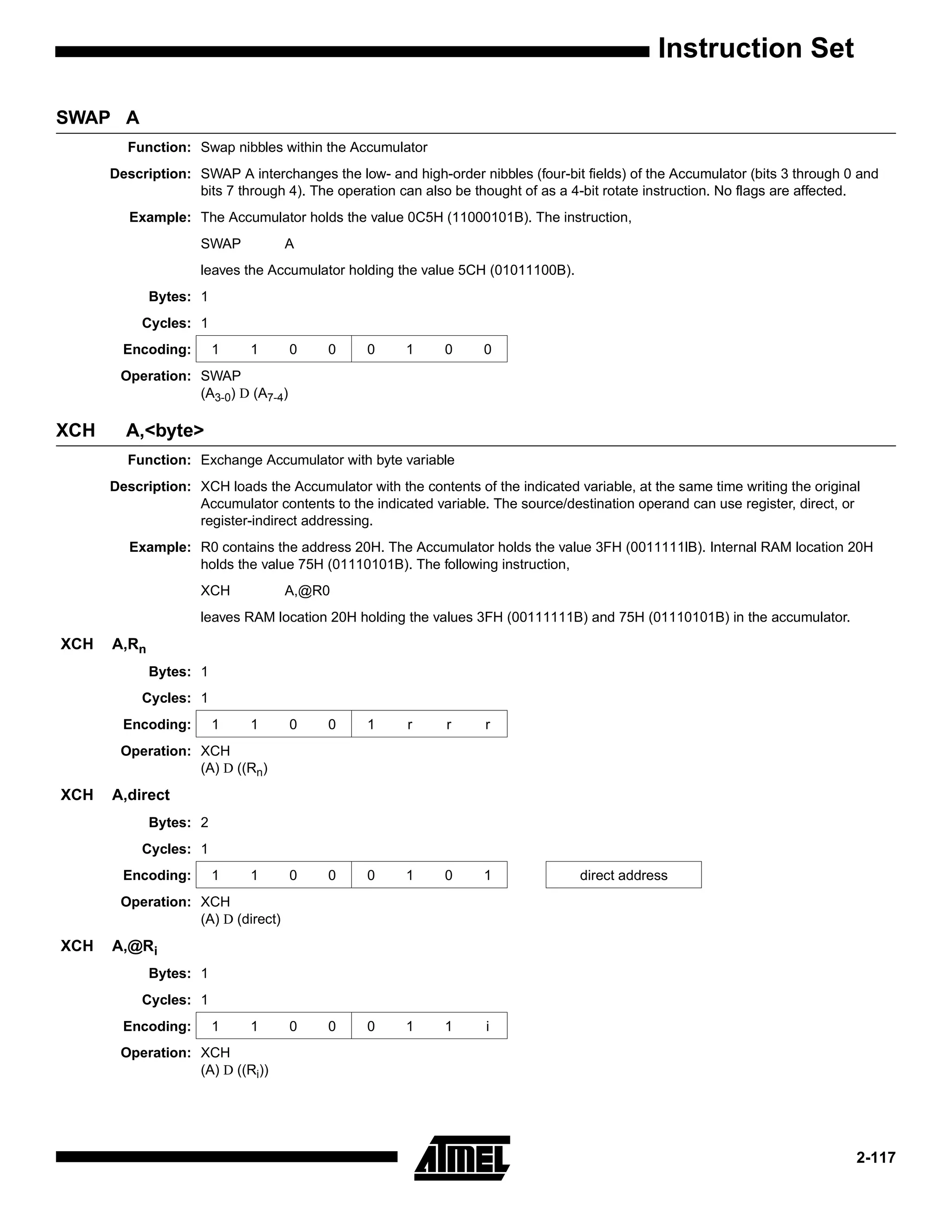
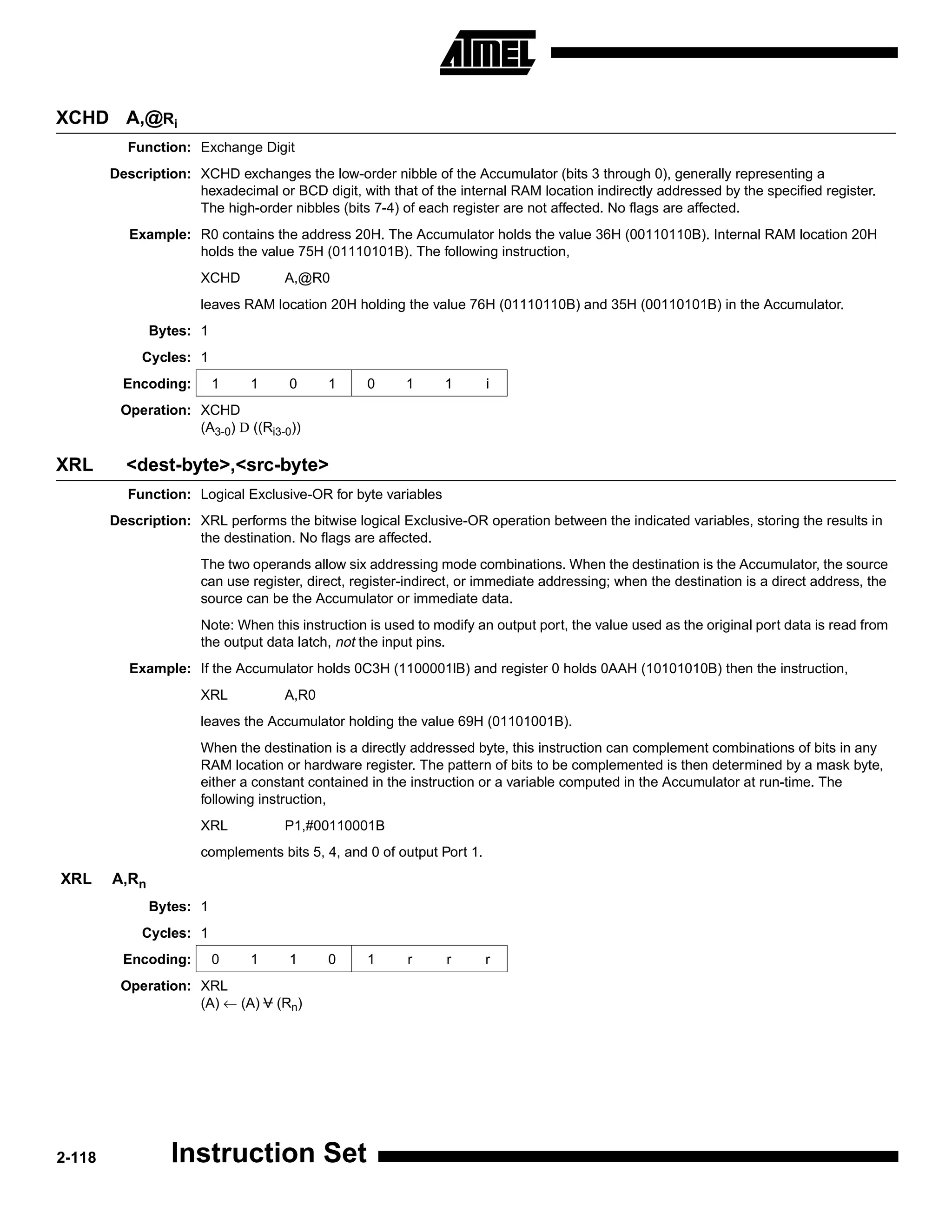
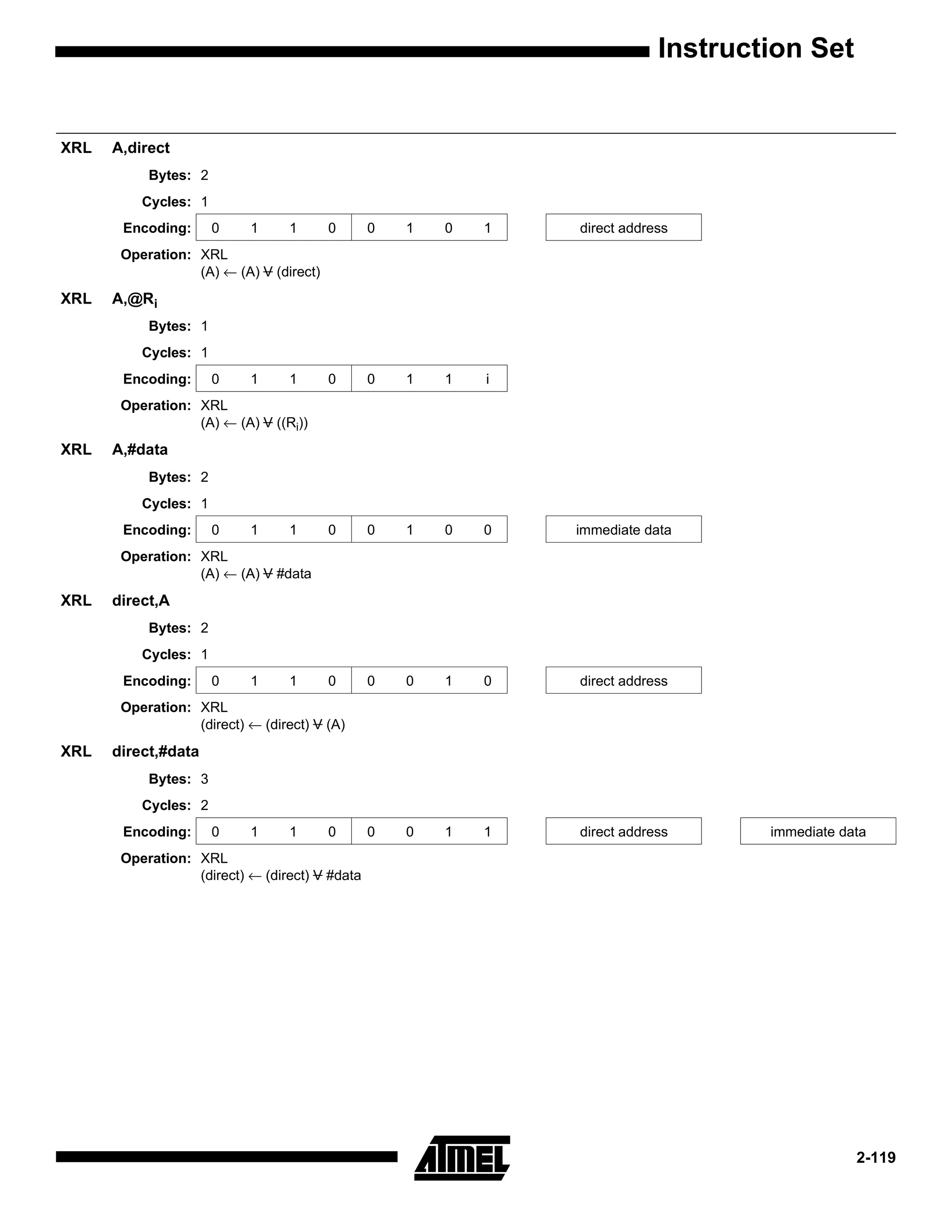
This document provides an instruction set summary for a microcontroller. It includes a table that lists each instruction, describes its function, and specifies the number of bytes in the instruction and its execution time in oscillator periods. It summarizes instructions related to arithmetic operations, logical operations, program flow control, bit manipulation, data transfer, and interrupts.