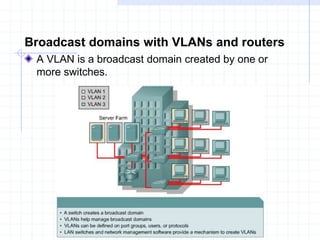
VLANs logically segment networks based on organizational functions rather than physical connections. This allows workstations and servers used by the same workgroup to communicate regardless of location. VLANs restrict communication between different VLAN groups and function by logically segmenting the network into broadcast domains so packets are only switched between ports in the same VLAN. Routers provide security, broadcast filtering, and traffic management between VLANs. VLANs address issues like scalability, security, and network management.