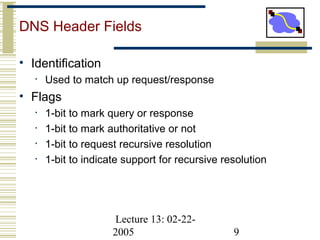
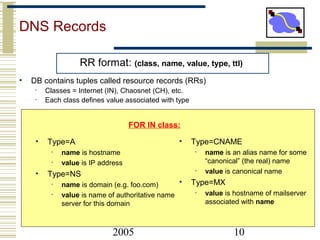
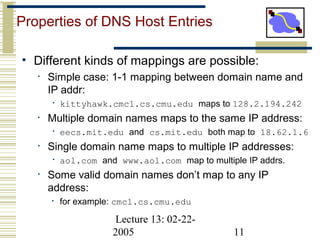
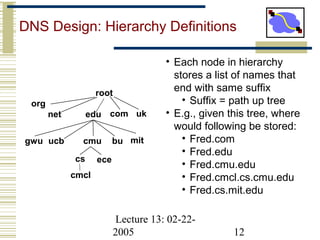
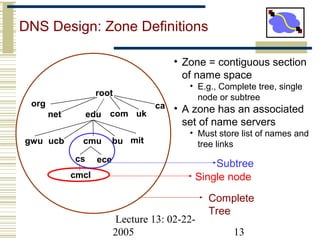
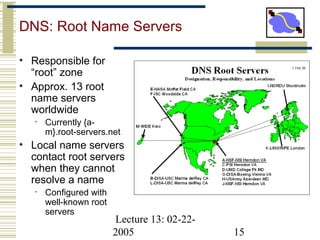
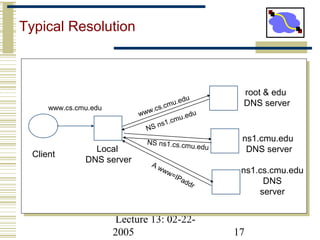
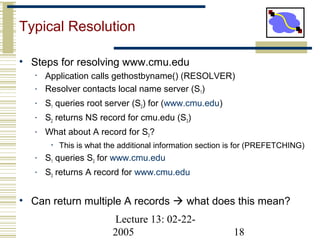
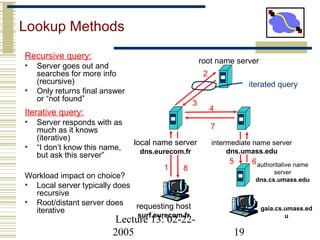
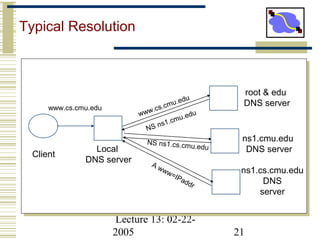
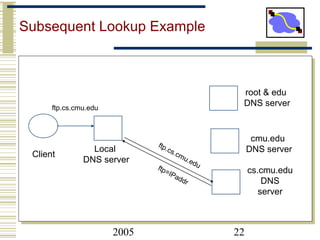
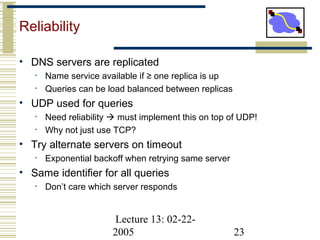
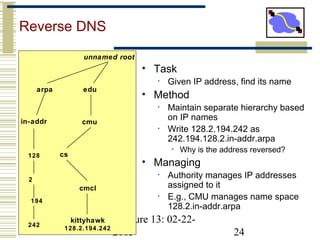
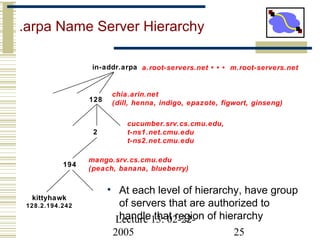
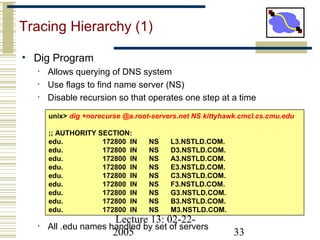
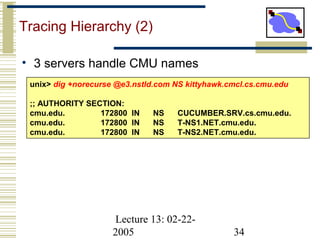
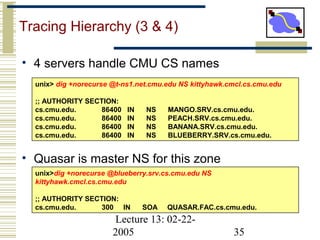
This document discusses DNS design and how it functions today. It outlines DNS hierarchy and zone definitions to allow for scalable and decentralized name resolution. It describes how typical DNS resolution works, with a client's local resolver contacting root servers and authoritative name servers in sequence to map names to IP addresses. The document also discusses reliability mechanisms, caching, and the roles of different record types like MX and reverse DNS lookups.