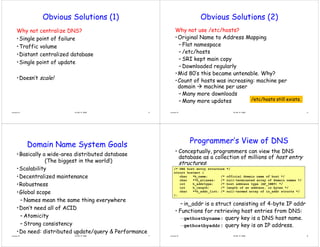
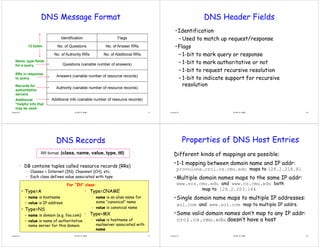
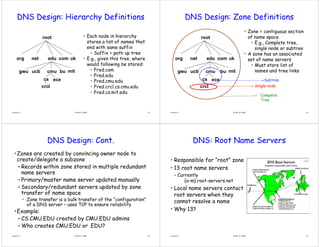
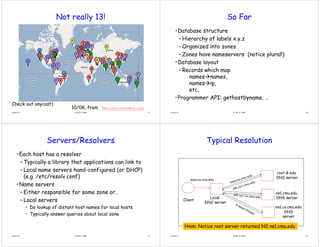
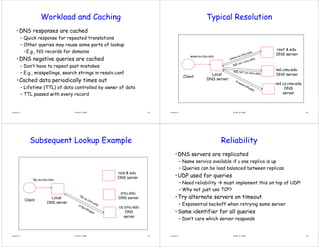
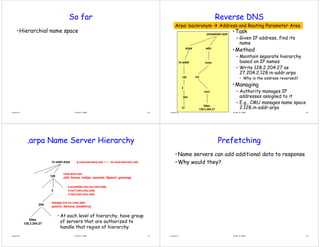
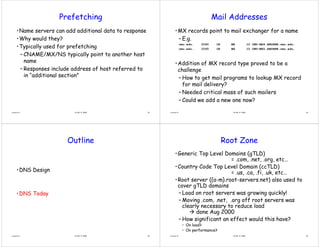
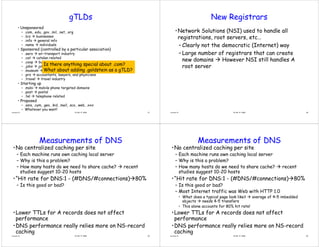
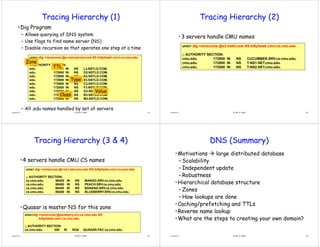
The document discusses DNS (Domain Name System) design and operation. It describes how DNS works as a distributed database to map human-readable domain names to machine-readable IP addresses. DNS has a hierarchical design where domains are divided into zones with authoritative name servers. When resolving a domain name, the local DNS server will iteratively query root servers, top-level domain servers, and authoritative name servers until it receives the IP address record. Caching is used to improve performance and distribute workload.