This document provides an overview of common network devices and initial device login procedures. It discusses switches, routers, firewalls and their basic functions. It also covers configuring interfaces, routes and login methods including console, telnet, SSH and web access. Initial device configuration includes enabling services, configuring administrators and setting the management interface. Basic system settings covered include file management, system time synchronization and logging.



![Page 23
Copyright © 2018 Huawei Technologies Co., Ltd. All rights reserved.
Introduction to Command Line
The CLI is divided into command views. All commands must be executed in
command views. You can run a command only after you enter its
command view.
<NGFW> User view
<NGFW>system-view
[NGFW] System view
[NGFW]interface GigabitEthernet 0/0/1
[NGFW–GigabitEthernet0/0/1]quit Interface view
[NGFW]ospf 1
[NGFW-ospf-1] Protocol view](https://image.slidesharecdn.com/y79yscc9remsqmdpifch-signature-60c36908fb947b8e09da270e3e3c4446c111cca17b0b57bbac85cb5b34c25b65-poli-210619133101/85/104-Common-network-devices-21-320.jpg)
![Page 26
Copyright © 2018 Huawei Technologies Co., Ltd. All rights reserved.
Command Line Help: Tab Key
If there is only one match for an incomplete keyword:
If there are multiple matches for a keyword:
[NGFW]info-
[NGFW]info-center
[NGFW]info-center l
[NGFW]info-center lo
[NGFW]info-center loghost
[NGFW]info-center local
[NGFW]info-center logbuffer
[NGFW]info-center logfile](https://image.slidesharecdn.com/y79yscc9remsqmdpifch-signature-60c36908fb947b8e09da270e3e3c4446c111cca17b0b57bbac85cb5b34c25b65-poli-210619133101/85/104-Common-network-devices-24-320.jpg)



![Page 39
Copyright © 2018 Huawei Technologies Co., Ltd. All rights reserved.
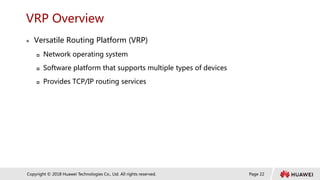
SSH Login: Configuration Management (1)
SSH provides greater security and powerful authentication functions for users to log in to the device. Configure SSH
device management on the USG interface. The administrator can enable SSH device management as required.
Configuration commands:
Enable the STelnet service.
Configure SSH management on the USG interface.
Configure a local RSA key pair.
Configure VTY user interfaces.
[NGFW]stelnet server enable
[NGFW-GigabitEthernet1/0/1]service-manage enable
[NGFW-GigabitEthernet1/0/1]service-manage ssh permit
<NGFW>system-view
[NGFW]rsa local-key-pair create
[USG]user-interface vty 0 4
[USG-ui-vty0-4]protocol inbound all
[USG-ui-vty0-4]authentication-mode aaa](https://image.slidesharecdn.com/y79yscc9remsqmdpifch-signature-60c36908fb947b8e09da270e3e3c4446c111cca17b0b57bbac85cb5b34c25b65-poli-210619133101/85/104-Common-network-devices-37-320.jpg)
![Page 40
Copyright © 2018 Huawei Technologies Co., Ltd. All rights reserved.
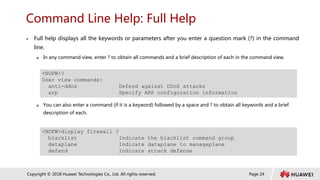
SSH Login: Configuration Management (2)
Create an SSH administrator account and set the authentication mode to Password and service mode
to STelnet.
Create an SSH user.
After the preceding configurations are completed, run the SSH client software to establish an SSH
connection.
If a Huawei device functions as an SSH client, enable the SSH login function on the client.
[NGFW]aaa
[NGFW-aaa]manager-user sshadmin
[NGFW-aaa-manager-user-sshadmin]service-type ssh
[NGFW-aaa-manager-user-sshadmin]level 3
[NGFW-aaa-manager-user-sshadmin]password cipher huawei
[NGFW]ssh user sshadmin
[NGFW]ssh user sshadmin authentication-type password
[NGFW]ssh user sshadmin service-type stelnet
[NGFW]ssh client first-time enable](https://image.slidesharecdn.com/y79yscc9remsqmdpifch-signature-60c36908fb947b8e09da270e3e3c4446c111cca17b0b57bbac85cb5b34c25b65-poli-210619133101/85/104-Common-network-devices-38-320.jpg)