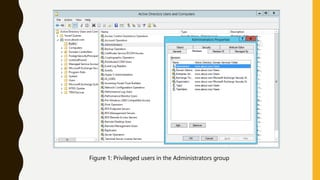
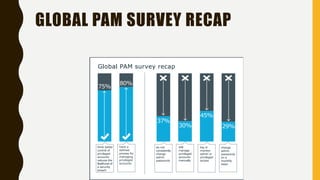
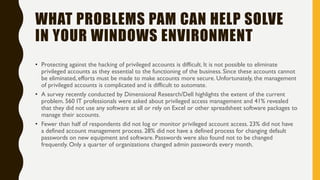
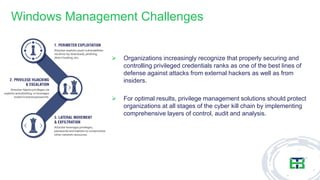
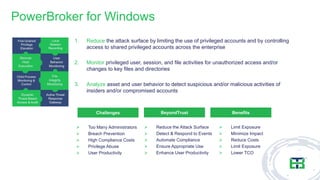
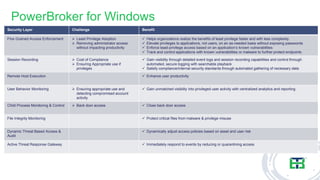
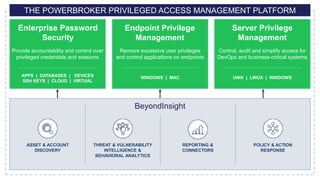
This document discusses best practices for managing Windows privileged access, focusing on the risks associated with privileged accounts and the necessity for effective access controls. It emphasizes the importance of identifying privileged users, implementing granular authorization, and auditing access to mitigate insider threats and external attacks. Additionally, it outlines ten steps for enhancing privileged access management and highlights solutions for minimizing risks while maintaining productivity.