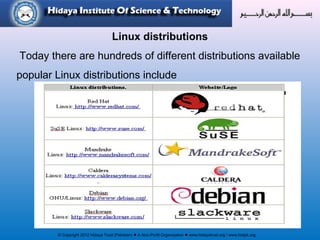
The document discusses the history and features of the Linux operating system. It notes that Linux was originally created by Linus Torvalds in 1991 as a free and open-source alternative to other operating systems. Linux is based on Unix and uses a model of free and open-source development. It describes Linux as stable, secure, and able to run on a variety of devices from servers to smartphones. The document outlines some popular Linux distributions and notes that Linux is now widely used both for basic uses and high-performance applications.