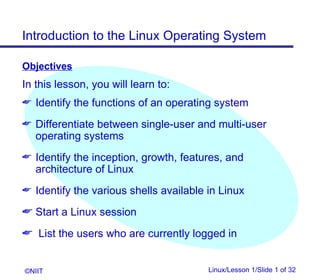
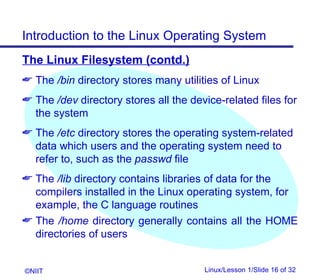
This document introduces the Linux operating system. It outlines objectives of the lesson which include identifying functions of an operating system, differentiating between single-user and multi-user systems, and learning Linux features and commands. The document describes operating system functions, types of systems, shells available in Linux, and commands for starting sessions, changing passwords, logging out, and managing files and directories.










![Introduction to the Linux Operating System
Listing the Users Currently Logged In
A list of users who are currently logged in can be
found by using the who command
who [options]
©NIIT Linux/Lesson 1/Slide 12 of 32](https://image.slidesharecdn.com/01t1s2linuxlesson1-120423130123-phpapp01/85/01-t1-s2_linux_lesson1-12-320.jpg)








![Introduction to the Linux Operating System
File Commands in Linux
The cat (concatenate) command displays the
contents of the specified file
Copying Files
The cp (copy) command duplicates the contents of
the source file into a target file
cp [options] source file/s destination
directory/file
Removing Files
The rm (remove) command is used to delete files
or directories
rm [options] file/s
©NIIT Linux/Lesson 1/Slide 23 of 32](https://image.slidesharecdn.com/01t1s2linuxlesson1-120423130123-phpapp01/85/01-t1-s2_linux_lesson1-23-320.jpg)
![Introduction to the Linux Operating System
File Commands in Linux (contd.)
Moving and Renaming Files
The mv (move) command is used to move a file or
directory from one location to another or to change
its name
mv [option] source destination
Displaying the Contents Page–Wise
The more command is used to display data one
screen-full at a time. While viewing a file using the
more command, once you have scrolled down, you
cannot move up
more [options] filename
©NIIT Linux/Lesson 1/Slide 24 of 32](https://image.slidesharecdn.com/01t1s2linuxlesson1-120423130123-phpapp01/85/01-t1-s2_linux_lesson1-24-320.jpg)
![Introduction to the Linux Operating System
File Commands in Linux (contd.)
Displaying the Contents Page–Wise (contd.)
The less command is similar to the more
command except that you can scroll upwards also
while viewing the contents of a file
less [options] filename
Wildcard Characters
The shell offers the facility to perform an operation on
a set of files by the use of certain special characters in
the command in place of the actual file names
©NIIT Linux/Lesson 1/Slide 25 of 32](https://image.slidesharecdn.com/01t1s2linuxlesson1-120423130123-phpapp01/85/01-t1-s2_linux_lesson1-25-320.jpg)
![Introduction to the Linux Operating System
File Commands in Linux (contd.)
Wildcard Characters (contd.)
The * Wildcard
The * wildcard is interpreted as a string of none,
one, or more characters
The ? Wildcard
The ? wildcard matches exactly one occurrence of
any character
The [ ] Wildcard
The [ ] wildcard can be used to restrict the
characters to be matched
©NIIT Linux/Lesson 1/Slide 26 of 32](https://image.slidesharecdn.com/01t1s2linuxlesson1-120423130123-phpapp01/85/01-t1-s2_linux_lesson1-26-320.jpg)