MIPS Instruction Formats
•Download as PPTX, PDF•
0 likes•191 views
Audio version available in www.youtube.com/Aksharam subscribe the channal Computer Architecture and Organization V semester Anna University By Babu M, Assistant Professor Department of ECE RMK College of Engineering and Technology Chennai
Report
Share
Report
Share
Recommended
Pipeline hazards | Structural Hazard, Data Hazard & Control Hazard

Audio Version available in YouTube Link : https://www.youtube.com/AKSHARAM?sub_confirmation=1
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
4.4.1.3 packet tracer configuring a zone-based policy firewall (zpf) instru...

This document describes how to configure a zone-based policy firewall (ZPF) on router R3 to allow internal hosts to access external resources while blocking external hosts from accessing internal resources. It involves verifying basic network connectivity, creating firewall zones, defining traffic classes and access lists, specifying firewall policies, applying policies to zone pairs, and testing functionality from the internal and external zones.
Mp lab manual

This document provides a list of experiments to be conducted using microprocessors and microcontrollers for two cycles. The first cycle involves programs written for the 8086 assembler using TASM software. The second cycle involves programs written for the 8051 assembler using TOP VIEW SIMULATOR software for interfacing experiments. A total of minimum 10 programs must be conducted between the two cycles.
ARM Fundamentals

The document provides an overview of the ARM instruction set, including data processing, branch, load-store, and program status register instructions. It describes common instruction mnemonics and addressing modes. Key points covered include conditional execution, different instruction types for arithmetic, logical, comparison and multiply operations, and single and multiple register transfer instructions for moving data between registers and memory.
Booth’s algorithm.(a014& a015)

This document provides an overview of Booth's algorithm for multiplying signed and unsigned integers. It begins with an introduction and history, noting that the algorithm was invented by Andrew Donald Booth in 1950. It then explains the key points of Booth's algorithm through a flow chart and examples. For unsigned integers, it uses fewer additions/subtractions than other methods by conditionally adding or subtracting the multiplicand. For signed integers, it first converts them to unsigned using 2's complement before applying the same process.
Build reliable, traceable, distributed systems with ZeroMQ

ZeroMQ is used to build a distributed system with reliable and traceable communication. It allows exposing code over RPC with minimal modification. Exceptions are properly propagated across services. The system is language agnostic and brokerless. Introspection allows viewing methods and signatures without opening code. Streaming APIs allow continuous updates without timeouts. Tracing helps profile nested calls and identify performance bottlenecks. Security is not implemented but could use SSL or authentication layers.
8085 branching instruction

The document summarizes the branch group instructions of the 8085 microprocessor. It describes jump instructions like JMP, conditional jump instructions, and the PCHL instruction. It also covers CALL and return instructions like CALL, RET, and conditional call and return instructions. Finally, it discusses restart instructions like RST that can be used as software interrupts to transfer program execution to specific restart locations.
Ibm db2 case study

DB2 Express-C is a free version of the DB2 database server from IBM. It has no usage or deployment limits and can run on Windows, Linux, Mac OS X, and Solaris operating systems. Minimum requirements are 256MB of RAM but it is recommended to have at least 1GB. DB2 Express-C provides basic database functionality and sits below the paid DB2 Workgroup and Enterprise editions in terms of features. It uses concurrency controls like locking and transactions to allow for multi-user access to the database.
Recommended
Pipeline hazards | Structural Hazard, Data Hazard & Control Hazard

Audio Version available in YouTube Link : https://www.youtube.com/AKSHARAM?sub_confirmation=1
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
4.4.1.3 packet tracer configuring a zone-based policy firewall (zpf) instru...

This document describes how to configure a zone-based policy firewall (ZPF) on router R3 to allow internal hosts to access external resources while blocking external hosts from accessing internal resources. It involves verifying basic network connectivity, creating firewall zones, defining traffic classes and access lists, specifying firewall policies, applying policies to zone pairs, and testing functionality from the internal and external zones.
Mp lab manual

This document provides a list of experiments to be conducted using microprocessors and microcontrollers for two cycles. The first cycle involves programs written for the 8086 assembler using TASM software. The second cycle involves programs written for the 8051 assembler using TOP VIEW SIMULATOR software for interfacing experiments. A total of minimum 10 programs must be conducted between the two cycles.
ARM Fundamentals

The document provides an overview of the ARM instruction set, including data processing, branch, load-store, and program status register instructions. It describes common instruction mnemonics and addressing modes. Key points covered include conditional execution, different instruction types for arithmetic, logical, comparison and multiply operations, and single and multiple register transfer instructions for moving data between registers and memory.
Booth’s algorithm.(a014& a015)

This document provides an overview of Booth's algorithm for multiplying signed and unsigned integers. It begins with an introduction and history, noting that the algorithm was invented by Andrew Donald Booth in 1950. It then explains the key points of Booth's algorithm through a flow chart and examples. For unsigned integers, it uses fewer additions/subtractions than other methods by conditionally adding or subtracting the multiplicand. For signed integers, it first converts them to unsigned using 2's complement before applying the same process.
Build reliable, traceable, distributed systems with ZeroMQ

ZeroMQ is used to build a distributed system with reliable and traceable communication. It allows exposing code over RPC with minimal modification. Exceptions are properly propagated across services. The system is language agnostic and brokerless. Introspection allows viewing methods and signatures without opening code. Streaming APIs allow continuous updates without timeouts. Tracing helps profile nested calls and identify performance bottlenecks. Security is not implemented but could use SSL or authentication layers.
8085 branching instruction

The document summarizes the branch group instructions of the 8085 microprocessor. It describes jump instructions like JMP, conditional jump instructions, and the PCHL instruction. It also covers CALL and return instructions like CALL, RET, and conditional call and return instructions. Finally, it discusses restart instructions like RST that can be used as software interrupts to transfer program execution to specific restart locations.
Ibm db2 case study

DB2 Express-C is a free version of the DB2 database server from IBM. It has no usage or deployment limits and can run on Windows, Linux, Mac OS X, and Solaris operating systems. Minimum requirements are 256MB of RAM but it is recommended to have at least 1GB. DB2 Express-C provides basic database functionality and sits below the paid DB2 Workgroup and Enterprise editions in terms of features. It uses concurrency controls like locking and transactions to allow for multi-user access to the database.
4 bit uni shift reg

This document describes the design and implementation of a universal shift register (USR) in Verilog. It includes:
1) A block diagram and description of a USR that can perform shift left, shift right, and parallel load operations using D flip-flops and 4-to-1 multiplexers.
2) The Verilog code for the USR module using D flip-flop and 4-to-1 multiplexer submodules.
3) The test bench and simulation results verifying the USR functionality.
Cisco CCNA- How to Configure Multi-Layer Switch

Cisco CCNA Training/Exam Tips that are helpful for your Certification Exam!
To be Cisco Certified please Check out:
http://asmed.com/information-technology-it/
Modified booth's algorithm Part 2

The document describes the Modified Booth's Algorithm for binary multiplication of negative numbers. It uses bit pair recoding of the multiplier and defines a recoding table. As an example, it shows the step-by-step binary multiplication of -13 x -7 using bit pair recoding of the multiplier, multiplication according to the recoding table, and addition of partial products to get the final result of 91.
Uart

The document describes a Universal Asynchronous Receiver Transmitter (UART) circuit. A UART allows a computer to communicate with external devices by transmitting serial data. It contains a receiver that takes in serial data and a transmitter that sends out serial data. A baud rate generator is used to synchronize the transmission and reception of bits. The document provides details on the UART components, data encoding, and includes VHDL code for a UART design.
Huawei cisco command conversion

This document provides command equivalents for common commands between Cisco IOS and Huawei routers. It lists the Cisco command, the equivalent Huawei command, and a brief description of each command. Some Cisco commands like "mtu" and "hwtacacs scheme" do not have direct equivalents on Huawei routers. The document is intended to help users transition between the two platforms by showing similar functions and settings that can be configured.
Synchronous Loadable Up and Down Counter 

Synchronous loadable up and down counter is a very important block in any complex digital system design. It is not just used for counting, it is also used for phase signal generation, clock division and for initiation of a process.
Hotspot on Mikrotik Router

Ean Sarath is a technical support specialist at MaxBIT ISP who is certified in MikroTik. The presentation discusses hotspots and how to configure them using MikroTik. It covers benefits of hotspots like providing secure login pages and bandwidth limiting. The document then explains how to set up a hotspot interface, IP pool, and DHCP server. It also discusses bypassing hotspots through IP binding, walled gardens, and limiting user bandwidth profiles. Shared user profiles are explained as well to allow multiple logins under one account.
Cisco vs. huawei CLI Commands

This document provides a comparison of commands between Cisco and Huawei routers. It lists Cisco commands along with their equivalent Huawei commands. For example, the Cisco command "configure terminal" is equivalent to the Huawei command "system". It also provides examples of basic Huawei configuration commands like setting the device name, viewing the configuration, and configuring an interface.
Microprocessor Based Systems.ppt

This document provides an introduction to microprocessors and microcontrollers. It begins with a brief history of computers and their classification including mainframes, personal computers, and supercomputers. Embedded controllers are introduced as dedicated systems that perform specific functions. The evolution of integrated circuits and transistors is discussed leading to the development of microprocessors. Key components of microprocessor-based systems including the CPU, memory, I/O ports, and buses are described. Microcontrollers are then introduced as integrated systems that combine a microprocessor with memory and peripherals on a single chip for embedded applications. Several examples of microprocessor and microcontroller-based systems are provided.
LF_DPDK17_Flexible and Extensible support for new protocol processing with DP...

This document discusses dynamic device personalization (DDP) using Intel Ethernet 700 Series network cards. DDP allows run-time updating and configuration of the parse graph to expand or modify protocol support. This enables identification and processing of new protocols like MPLSoGRE, GTP-U/GTP-C, and QUIC without requiring a reboot. DPDK APIs allow downloading DDP profiles to enable parsing of additional protocols and configuring traffic steering based on tunnel IDs. With DDP, encapsulated frame fields can be extracted and used for functions like RSS, whereas without DDP those protocols would not be recognized.
101 CCNA LABS.pdf

This document outlines 107 labs for networking fundamentals, including configuration, verification, and troubleshooting of topics like IP addressing, routing protocols, switching, VLANs, ACLs, NAT, DHCP, SNMP, device security, wireless access points, and more. Each lab has a section for configuration and verification. The document provides a table of contents to help navigate the various sections and labs.
CCNA PPT

This document discusses Cisco Certified Network Associate (CCNA) certification and networking concepts. It includes:
- An overview of the CCNA certification and what skills it demonstrates in networking areas like LANs, WANs, routing protocols, and network access.
- Explanations of common networking devices, topologies, protocols like IP addressing and routing, and models like the OSI model.
- Descriptions of static and dynamic routing, protocols like RIP, OSPF, EIGRP, and commands used to configure routers.
Hardware Multi-Threading

Hardware multithreading allows multiple threads to share the functional units of a single processor by switching between threads when one thread is stalled. There are three main types of hardware multithreading: coarse-grained multithreading switches threads on long latency events like L2 cache misses; fine-grained multithreading switches threads every clock cycle in a round-robin fashion for high throughput but poor single-thread performance; simultaneous multithreading combines fine-grained multithreading with superscalar processing to further improve throughput by hiding memory latency but increases conflicts for shared resources.
database application using SQL DML statements: all types of Join, Sub-Query ...

Design at least 10 SQL queries for suitable database
application using SQL DML statements:
all types of Join, Sub-Query and View.
4 bit add sub

This document describes the implementation of a 4-bit adder-subtractor circuit. It first covers the implementation of a half-adder, including its truth table, circuit diagram, and module. It then covers the implementation of a full-adder, including its truth table, circuit diagram, module, and RTL schematic. Finally, it discusses the implementation of the 4-bit adder-subtractor, including its block diagram, flow chart, module, testbench, waveform, and RTL schematic. The 4-bit adder-subtractor can perform addition or subtraction depending on the carry-in bit value.
Computer architecture instruction formats

Computer architecture instruction formats seminar
Mustansiriya University
Department of Education
Computer Science
Hardware I/O organization 

Hardware refers to the physical components of computers that can be touched and seen. This includes input devices like keyboards and mice and output devices like monitors and printers. The document then provides details about computer buses that connect hardware components and allow communication, different types of computer memory architectures, input/output techniques like port I/O and memory-mapped I/O, and direct memory access which allows hardware devices to access memory directly without using the CPU.
8086 alp

This document describes 16 assembly language programs for the 8086 microprocessor. It includes programs that increment/decrement 8-bit and 16-bit numbers, take the 1's and 2's complement of numbers, add/subtract/multiply/divide 8-bit and 16-bit numbers, and manipulate strings. It also discusses the use of procedures, stacks, and macros in 8086 assembly language programming. Examples are provided to illustrate how to define and call procedures, use push/pop on the stack, and define macros with parameters.
Stable OSPF: choosing network type.pdf

in this webinar, we will discuss one way to setup a stable OSPF network. that is how to select properly network type: default (broadcast), NBMA (non broadcast multiple access), PTP (point to point). we also discuss how OSPF works, how link state differs from distance vector, and discuss the benefit and drawback on each type. ospf drawback and ospf benefit
Introduction to Advance Computer Architecture

Audio Version available in YouTube Link : https://www.youtube.com/AKSHARAM?sub_confirmation=1
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
Clusters and Wharehouse Scale Computers

Audio Version available in YouTube Link : https://www.youtube.com/AKSHARAM?sub_confirmation=1
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
More Related Content
What's hot
4 bit uni shift reg

This document describes the design and implementation of a universal shift register (USR) in Verilog. It includes:
1) A block diagram and description of a USR that can perform shift left, shift right, and parallel load operations using D flip-flops and 4-to-1 multiplexers.
2) The Verilog code for the USR module using D flip-flop and 4-to-1 multiplexer submodules.
3) The test bench and simulation results verifying the USR functionality.
Cisco CCNA- How to Configure Multi-Layer Switch

Cisco CCNA Training/Exam Tips that are helpful for your Certification Exam!
To be Cisco Certified please Check out:
http://asmed.com/information-technology-it/
Modified booth's algorithm Part 2

The document describes the Modified Booth's Algorithm for binary multiplication of negative numbers. It uses bit pair recoding of the multiplier and defines a recoding table. As an example, it shows the step-by-step binary multiplication of -13 x -7 using bit pair recoding of the multiplier, multiplication according to the recoding table, and addition of partial products to get the final result of 91.
Uart

The document describes a Universal Asynchronous Receiver Transmitter (UART) circuit. A UART allows a computer to communicate with external devices by transmitting serial data. It contains a receiver that takes in serial data and a transmitter that sends out serial data. A baud rate generator is used to synchronize the transmission and reception of bits. The document provides details on the UART components, data encoding, and includes VHDL code for a UART design.
Huawei cisco command conversion

This document provides command equivalents for common commands between Cisco IOS and Huawei routers. It lists the Cisco command, the equivalent Huawei command, and a brief description of each command. Some Cisco commands like "mtu" and "hwtacacs scheme" do not have direct equivalents on Huawei routers. The document is intended to help users transition between the two platforms by showing similar functions and settings that can be configured.
Synchronous Loadable Up and Down Counter 

Synchronous loadable up and down counter is a very important block in any complex digital system design. It is not just used for counting, it is also used for phase signal generation, clock division and for initiation of a process.
Hotspot on Mikrotik Router

Ean Sarath is a technical support specialist at MaxBIT ISP who is certified in MikroTik. The presentation discusses hotspots and how to configure them using MikroTik. It covers benefits of hotspots like providing secure login pages and bandwidth limiting. The document then explains how to set up a hotspot interface, IP pool, and DHCP server. It also discusses bypassing hotspots through IP binding, walled gardens, and limiting user bandwidth profiles. Shared user profiles are explained as well to allow multiple logins under one account.
Cisco vs. huawei CLI Commands

This document provides a comparison of commands between Cisco and Huawei routers. It lists Cisco commands along with their equivalent Huawei commands. For example, the Cisco command "configure terminal" is equivalent to the Huawei command "system". It also provides examples of basic Huawei configuration commands like setting the device name, viewing the configuration, and configuring an interface.
Microprocessor Based Systems.ppt

This document provides an introduction to microprocessors and microcontrollers. It begins with a brief history of computers and their classification including mainframes, personal computers, and supercomputers. Embedded controllers are introduced as dedicated systems that perform specific functions. The evolution of integrated circuits and transistors is discussed leading to the development of microprocessors. Key components of microprocessor-based systems including the CPU, memory, I/O ports, and buses are described. Microcontrollers are then introduced as integrated systems that combine a microprocessor with memory and peripherals on a single chip for embedded applications. Several examples of microprocessor and microcontroller-based systems are provided.
LF_DPDK17_Flexible and Extensible support for new protocol processing with DP...

This document discusses dynamic device personalization (DDP) using Intel Ethernet 700 Series network cards. DDP allows run-time updating and configuration of the parse graph to expand or modify protocol support. This enables identification and processing of new protocols like MPLSoGRE, GTP-U/GTP-C, and QUIC without requiring a reboot. DPDK APIs allow downloading DDP profiles to enable parsing of additional protocols and configuring traffic steering based on tunnel IDs. With DDP, encapsulated frame fields can be extracted and used for functions like RSS, whereas without DDP those protocols would not be recognized.
101 CCNA LABS.pdf

This document outlines 107 labs for networking fundamentals, including configuration, verification, and troubleshooting of topics like IP addressing, routing protocols, switching, VLANs, ACLs, NAT, DHCP, SNMP, device security, wireless access points, and more. Each lab has a section for configuration and verification. The document provides a table of contents to help navigate the various sections and labs.
CCNA PPT

This document discusses Cisco Certified Network Associate (CCNA) certification and networking concepts. It includes:
- An overview of the CCNA certification and what skills it demonstrates in networking areas like LANs, WANs, routing protocols, and network access.
- Explanations of common networking devices, topologies, protocols like IP addressing and routing, and models like the OSI model.
- Descriptions of static and dynamic routing, protocols like RIP, OSPF, EIGRP, and commands used to configure routers.
Hardware Multi-Threading

Hardware multithreading allows multiple threads to share the functional units of a single processor by switching between threads when one thread is stalled. There are three main types of hardware multithreading: coarse-grained multithreading switches threads on long latency events like L2 cache misses; fine-grained multithreading switches threads every clock cycle in a round-robin fashion for high throughput but poor single-thread performance; simultaneous multithreading combines fine-grained multithreading with superscalar processing to further improve throughput by hiding memory latency but increases conflicts for shared resources.
database application using SQL DML statements: all types of Join, Sub-Query ...

Design at least 10 SQL queries for suitable database
application using SQL DML statements:
all types of Join, Sub-Query and View.
4 bit add sub

This document describes the implementation of a 4-bit adder-subtractor circuit. It first covers the implementation of a half-adder, including its truth table, circuit diagram, and module. It then covers the implementation of a full-adder, including its truth table, circuit diagram, module, and RTL schematic. Finally, it discusses the implementation of the 4-bit adder-subtractor, including its block diagram, flow chart, module, testbench, waveform, and RTL schematic. The 4-bit adder-subtractor can perform addition or subtraction depending on the carry-in bit value.
Computer architecture instruction formats

Computer architecture instruction formats seminar
Mustansiriya University
Department of Education
Computer Science
Hardware I/O organization 

Hardware refers to the physical components of computers that can be touched and seen. This includes input devices like keyboards and mice and output devices like monitors and printers. The document then provides details about computer buses that connect hardware components and allow communication, different types of computer memory architectures, input/output techniques like port I/O and memory-mapped I/O, and direct memory access which allows hardware devices to access memory directly without using the CPU.
8086 alp

This document describes 16 assembly language programs for the 8086 microprocessor. It includes programs that increment/decrement 8-bit and 16-bit numbers, take the 1's and 2's complement of numbers, add/subtract/multiply/divide 8-bit and 16-bit numbers, and manipulate strings. It also discusses the use of procedures, stacks, and macros in 8086 assembly language programming. Examples are provided to illustrate how to define and call procedures, use push/pop on the stack, and define macros with parameters.
Stable OSPF: choosing network type.pdf

in this webinar, we will discuss one way to setup a stable OSPF network. that is how to select properly network type: default (broadcast), NBMA (non broadcast multiple access), PTP (point to point). we also discuss how OSPF works, how link state differs from distance vector, and discuss the benefit and drawback on each type. ospf drawback and ospf benefit
What's hot (20)
LF_DPDK17_Flexible and Extensible support for new protocol processing with DP...

LF_DPDK17_Flexible and Extensible support for new protocol processing with DP...
database application using SQL DML statements: all types of Join, Sub-Query ...

database application using SQL DML statements: all types of Join, Sub-Query ...
More from babuece
Introduction to Advance Computer Architecture

Audio Version available in YouTube Link : https://www.youtube.com/AKSHARAM?sub_confirmation=1
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
Clusters and Wharehouse Scale Computers

Audio Version available in YouTube Link : https://www.youtube.com/AKSHARAM?sub_confirmation=1
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
Introduction to GPU

Audio Version available in YouTube Link : https://www.youtube.com/AKSHARAM?sub_confirmation=1
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
Shared Memory Multi Processor

Audio Version available in YouTube Link : https://www.youtube.com/AKSHARAM?sub_confirmation=1
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
Instruction Level Parallelism | Static Multiple Issue & Dynamic Multiple Issu...

Audio Version available in YouTube Link : https://www.youtube.com/AKSHARAM?sub_confirmation=1
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
Exception | How Exceptions are Handled in MIPS architecture

Audio Version available in YouTube Link : https://www.youtube.com/AKSHARAM?sub_confirmation=1
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
Introduction to Embedded Laboratory EC 8711 

The document discusses ARM processors and provides information about why they are widely used, their history and design. It notes that ARM is one of the most licensed processor cores in the world and is used in many portable devices due to its low power consumption and reasonable performance. It provides brief descriptions of some ARM cores and their features. Finally, it lists some example equipment that incorporates ARM cores.
Implementation of pipelining in datapath

Audio Version available in YouTube Link : https://www.youtube.com/AKSHARAM?sub_confirmation=1
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
Datapath design with control unit

Audio Version available in YouTube Link : www.youtube.com/Aksharam
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
Introduction to datapath design

Audio Version available in YouTube Link : www.youtube.com/Aksharam
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
Floating point Binary Represenataion

Audio Version available in YouTube Link : www.youtube.com/Aksharam
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
Introduction to floating point Arithmetic

Audio Version available in YouTube Link : www.youtube.com/Aksharam
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
Improved version of division

Audio Version available in YouTube Link : www.youtube.com/Aksharam
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
Booth's algorithm part 3

Audio Version available in YouTube Link : www.youtube.com/Aksharam
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
Booth's algorithm part 1

The document describes Booth's algorithm for multiplying two binary numbers in two's complement notation. It was invented by Andrew Booth in 1950 to increase the speed of calculations on desk calculators that were faster at shifting than adding. The algorithm handles both positive and negative multipliers uniformly. It then provides an example of multiplying two positive binary numbers (+13 x +7) using Booth's algorithm in four steps: 1) representing the numbers in binary, 2) recoding the multiplier, 3) performing the multiplication, and 4) verifying the result.
Modified booths algorithm part 1

Audio Version available in YouTube Link : www.youtube.com/Aksharam
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
Booth's algorithm part 2

Booth's algorithm allows for the binary multiplication of a positive multiplicand and negative multiplier. It involves 3 steps:
1) Representing the multiplicand and multiplier in binary, with the negative multiplier represented in 2's complement form.
2) Recoding the bits of the multiplier according to Booth's recoding table to translate it into a signed-digit form.
3) Multiplying the multiplicand by the recoded multiplier through successive additions or subtractions of the multiplicand according to the recoded bits. The result is the binary product of the positive and negative values.
Booth's algorithm part 4

Audio Version available in YouTube Link : www.youtube.com/Aksharam
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
Sequential Version / Version 1 Unsigned Multiplication Algorithm

Audio Version available in YouTube Link : www.youtube.com/Aksharam
subscribe the channel
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
Binary addition and subtraction

Audio Version available in YouTube Link : www.youtube.com/Aksharam
subscribe the channal
Computer Architecture and Organization
V semester
Anna University
By
Babu M, Assistant Professor
Department of ECE
RMK College of Engineering and Technology
Chennai
More from babuece (20)
Instruction Level Parallelism | Static Multiple Issue & Dynamic Multiple Issu...

Instruction Level Parallelism | Static Multiple Issue & Dynamic Multiple Issu...
Exception | How Exceptions are Handled in MIPS architecture

Exception | How Exceptions are Handled in MIPS architecture
Sequential Version / Version 1 Unsigned Multiplication Algorithm

Sequential Version / Version 1 Unsigned Multiplication Algorithm
MIPS Instruction Formats
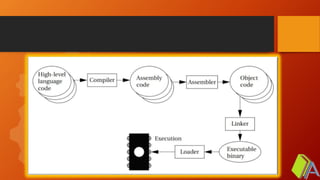
- 3. Von Neumann Vs Harvard Architecture
- 4. MIPS INSTRUCTION FORMAT – Type – Type - Type
- 5. R – TYPE INSTRUCTION FORMAT Eg:1. add $s1,$s2,$s3 Eg:2. sll $s1,$s2,10 000000
- 6. EXAMPLE add $s1,$s2,$s3 6 5 5 5 5 6 op rs rt rd Shift amt fn 000000 10010 10011 10001 00000 100000 6 5 5 5 5 6 op rs rt rd Shift amt fn 000000 00000 10010 10001 01010 000000 sll $s1,$s2,10
- 7. I – TYPE INSTRUCTION FORMAT Eg:1. lw $s1,4($s2) Eg:2. beq $s1,$s2,10 Eg:3. ori $t0,$t1,8
- 8. EXAMPLE lw $s1,4($s2) 6 5 5 16 op rs rt address 100011 10010 10001 0000000000000100 beq $s0,$s3,10 6 5 5 16 op rs rt address 000100 10011 10000 0000000000001010
- 9. EXAMPLE ori $t0,$t1,8 6 5 5 16 op rs rt address 001011 01001 01000 0000000000001000
- 10. J – TYPE INSTRUCTION FORMAT Eg J 500 6 26 op address 6 26 op address 000010 500
- 11. EXAMPLE f = (g + h) – (i + j) lw $t0,20($s4) lw $t1,24($s4) lw $t2,28($s4) lw $t3,32($s4) add $s1,$t0,$t1 add $s2,$t2,$t3 sub $s0,$s1,$s2 sw $s0, 16($s4) 35 20 8 20 35 20 9 24 35 20 10 28 35 20 11 32 0 8 9 17 0 32 0 10 11 18 0 32 0 17 18 16 0 34 43 20 16 16
- 13. 0000 0000 0001 0000 0101 0001 0000 0000 0000 0000 0001 0000 0101 0001 0000 000000000000000100000101000100000000 000000 00000100000101000100000000 R - Type 000000 00000100000101000100 000000 sll 000000 00000 10000 01010 00100 000000 sll $t2, op rs rt rd Shift amt fn $s0, 4
Editor's Notes
- Notes to presenter: Description of what you learned in your own words on one side. Include information about the topic Details about the topic will also be helpful here. Tell the story of your learning experience. Just like a story there should always be a beginning, middle and an end. On the other side, you can add a graphic that provides evidence of what you learned. Feel free to use more than one slide to reflect upon your process. It also helps to add some video of your process.
- Notes to presenter: Description of what you learned in your own words on one side. Include information about the topic Details about the topic will also be helpful here. Tell the story of your learning experience. Just like a story there should always be a beginning, middle and an end. On the other side, you can add a graphic that provides evidence of what you learned. Feel free to use more than one slide to reflect upon your process. It also helps to add some video of your process.
- Notes to presenter: Description of what you learned in your own words on one side. Include information about the topic Details about the topic will also be helpful here. Tell the story of your learning experience. Just like a story there should always be a beginning, middle and an end. On the other side, you can add a graphic that provides evidence of what you learned. Feel free to use more than one slide to reflect upon your process. It also helps to add some video of your process.