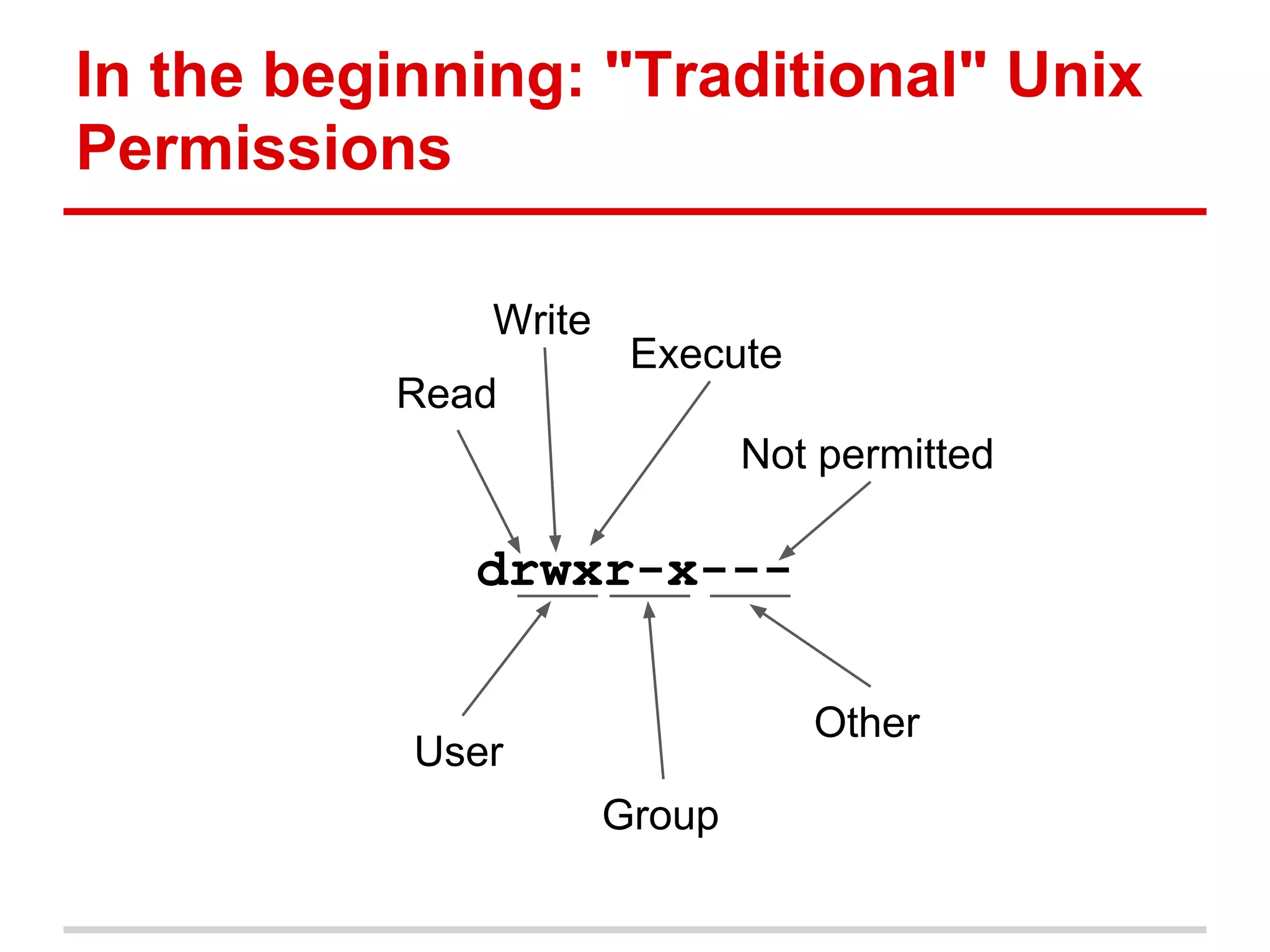
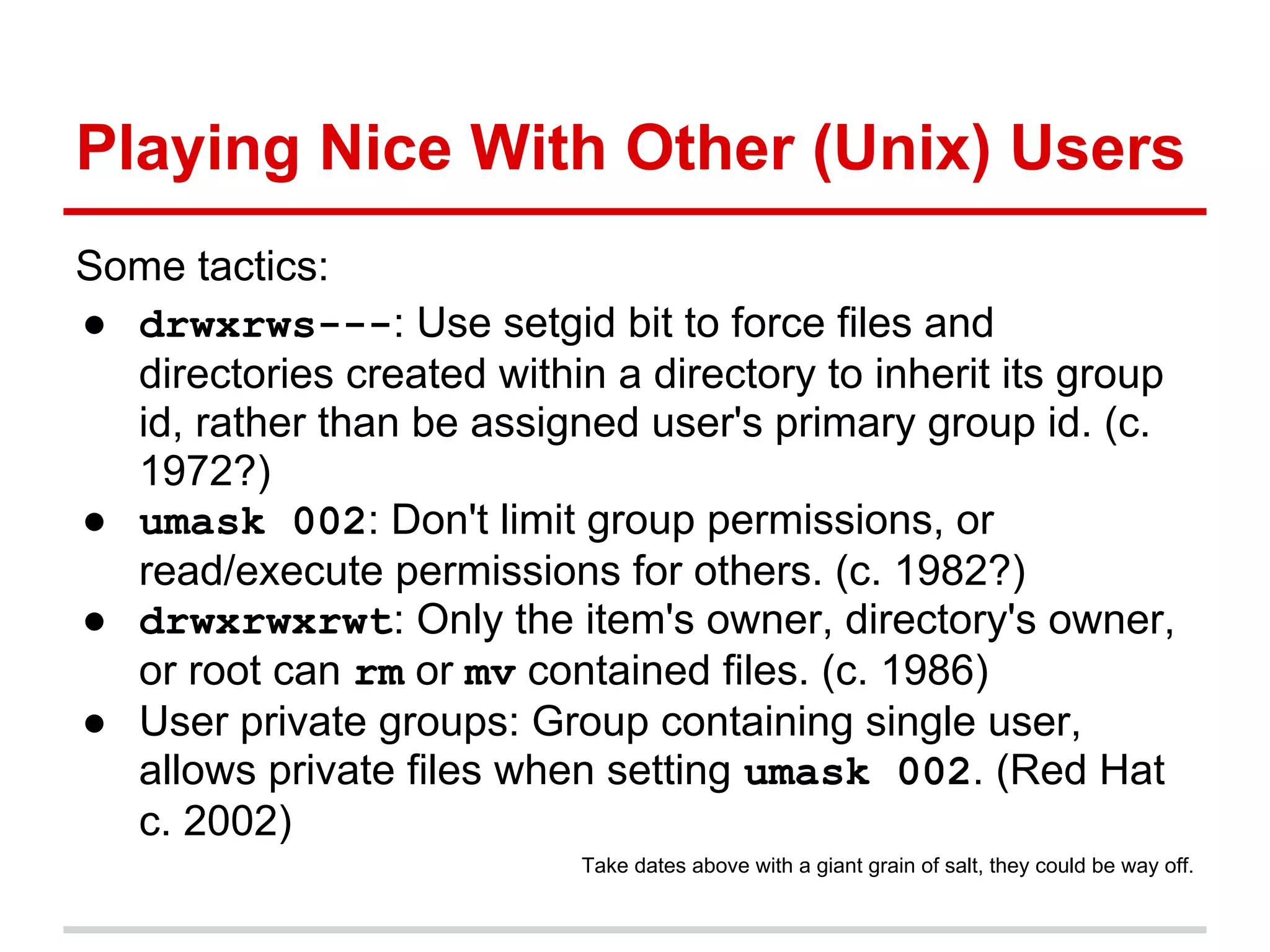
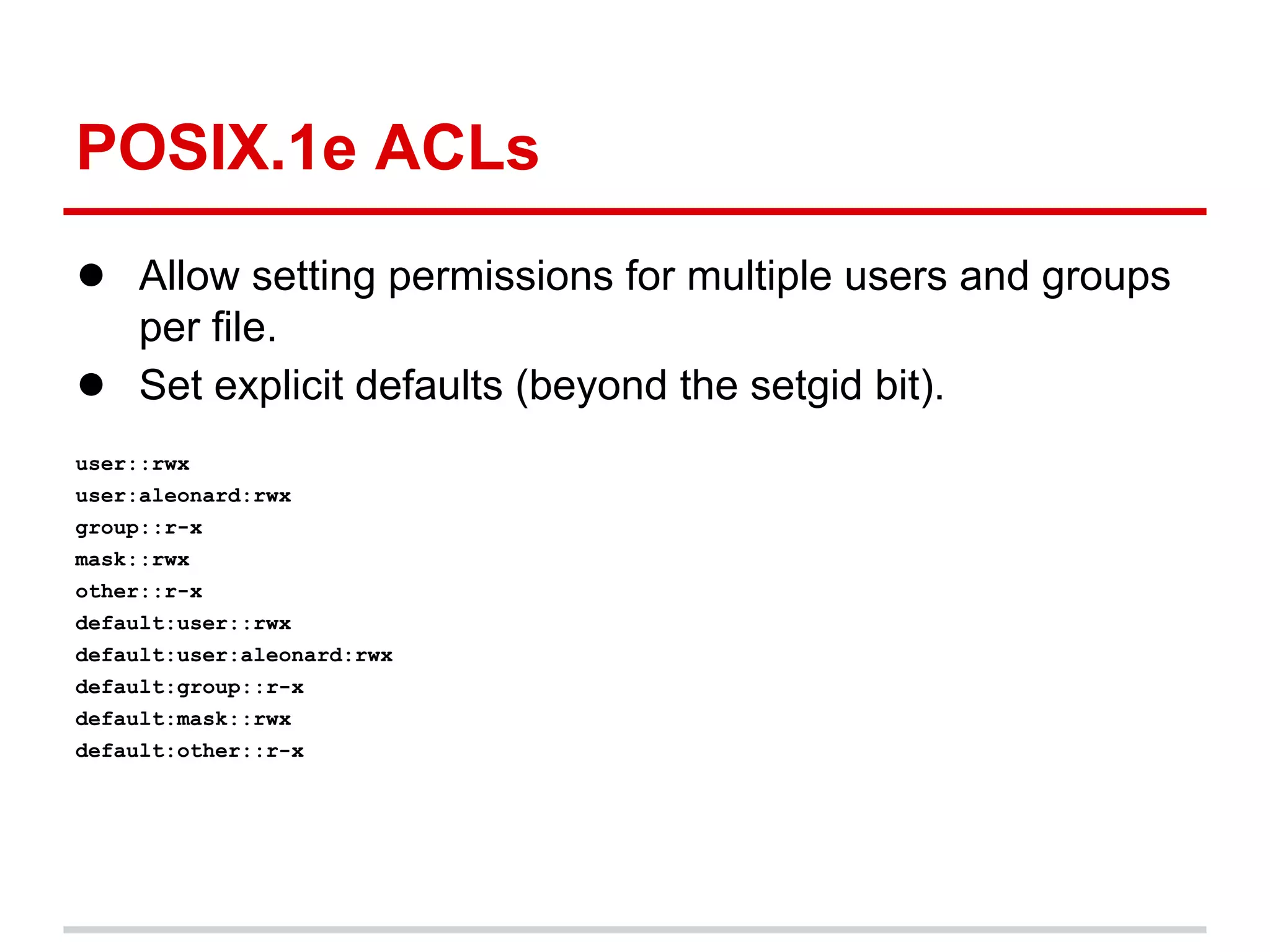
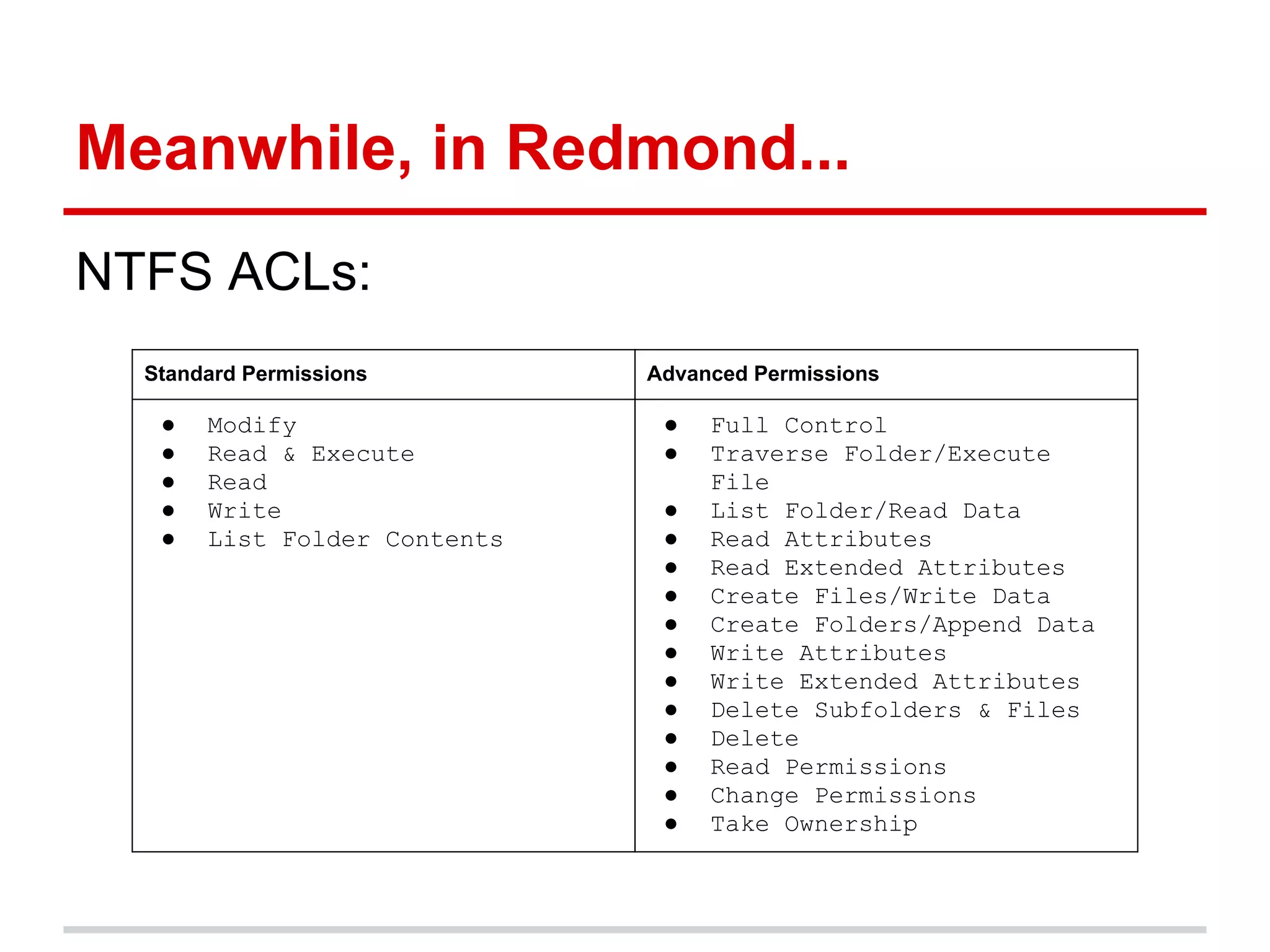
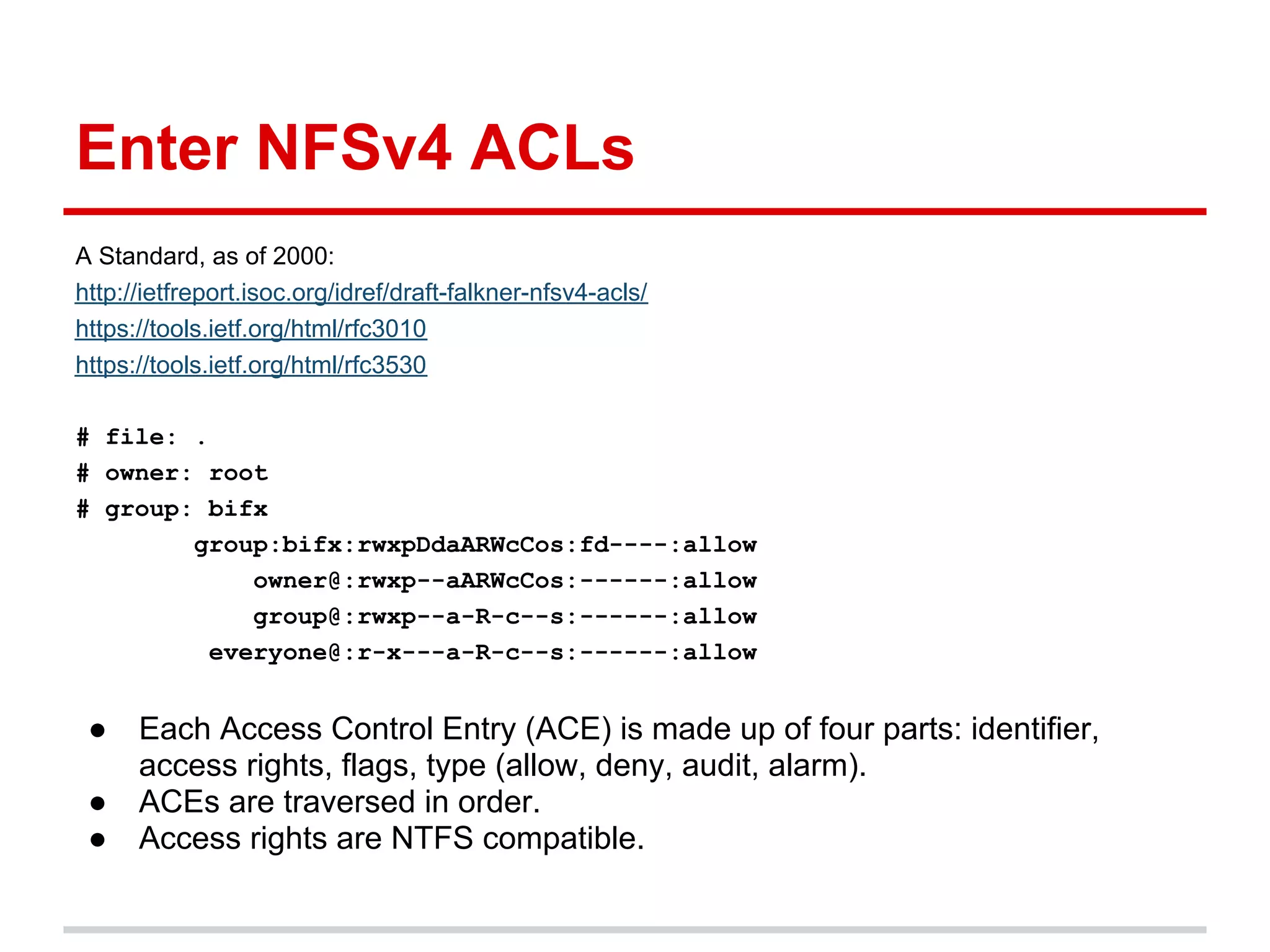
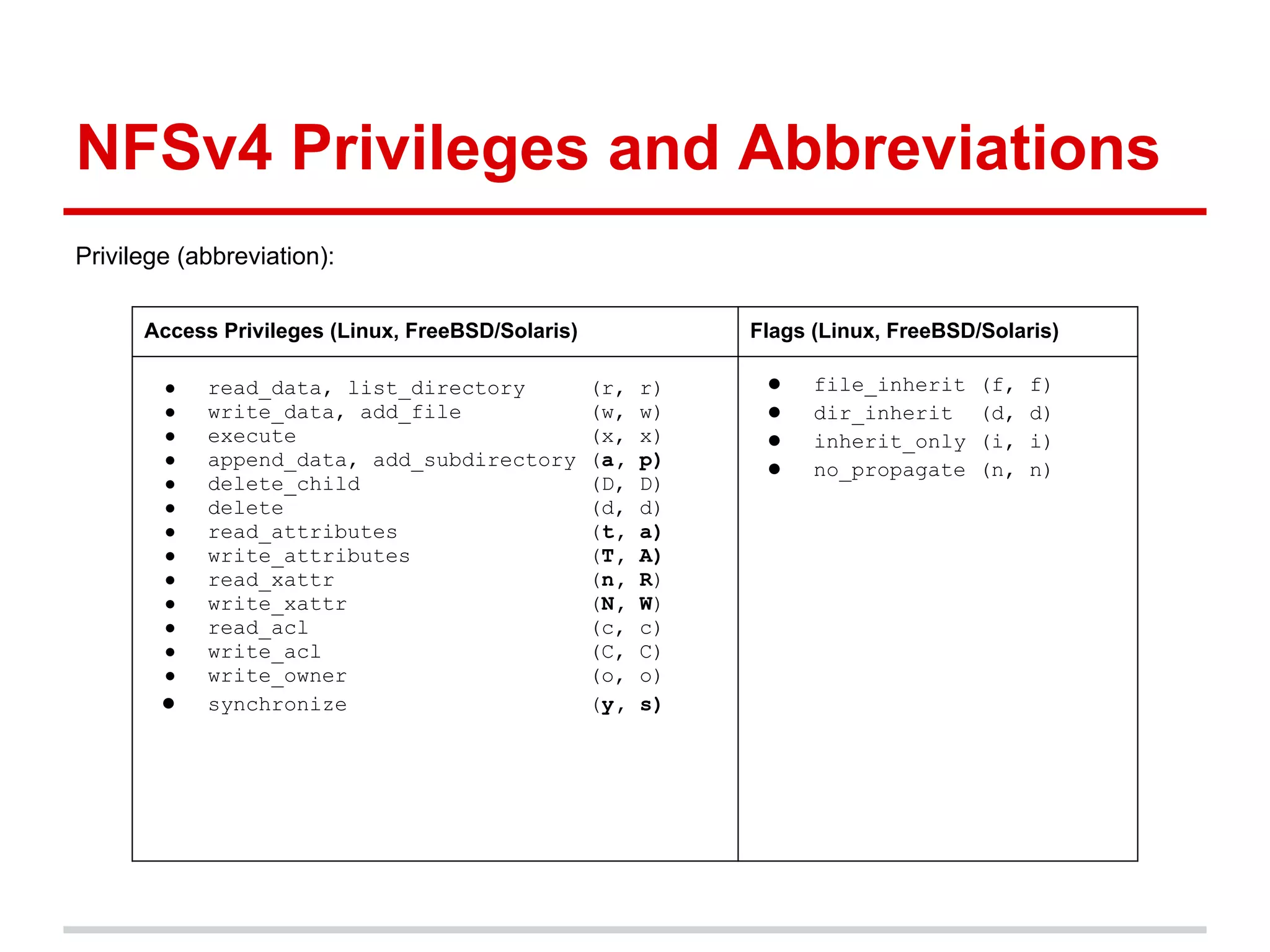
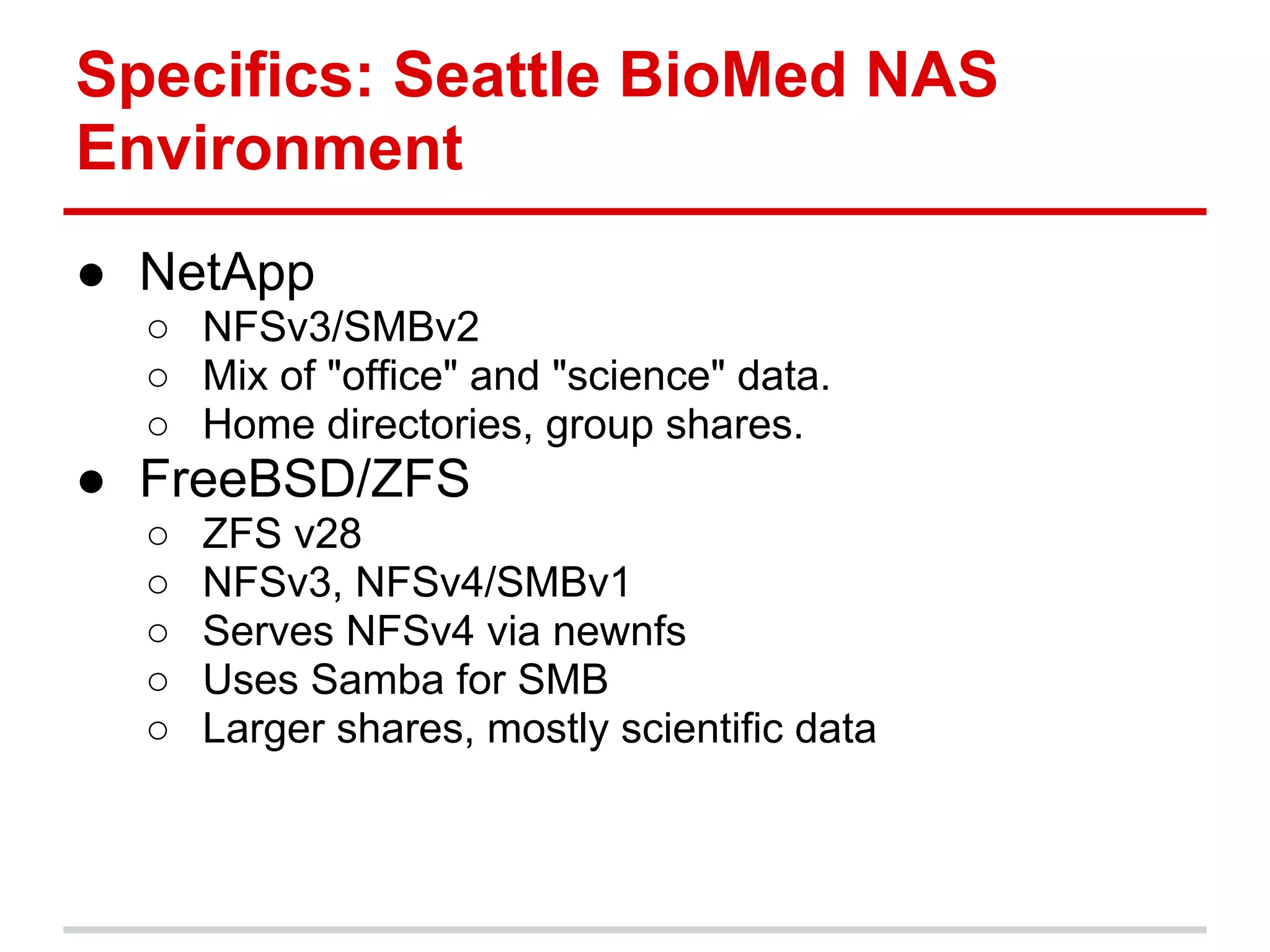
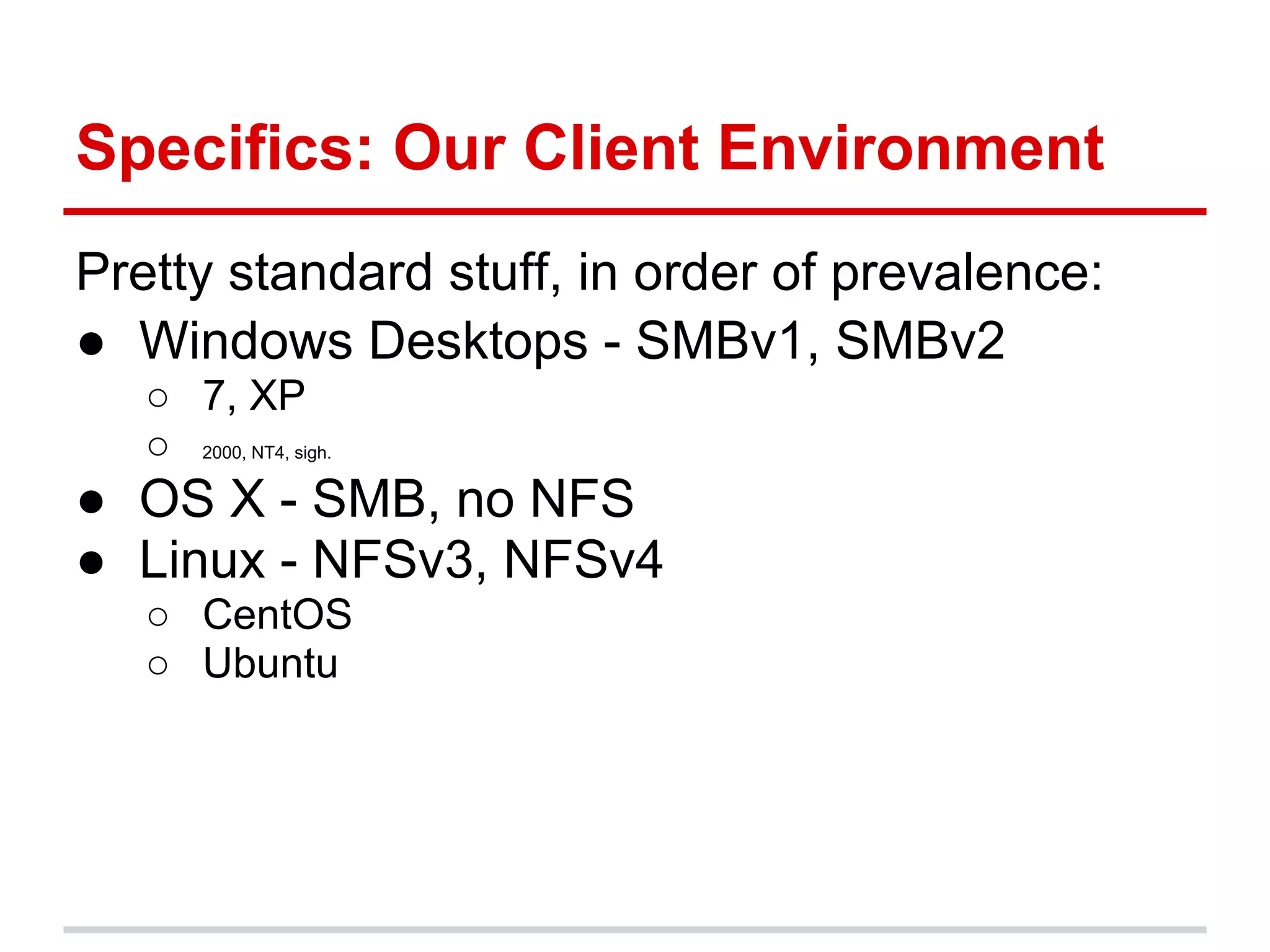
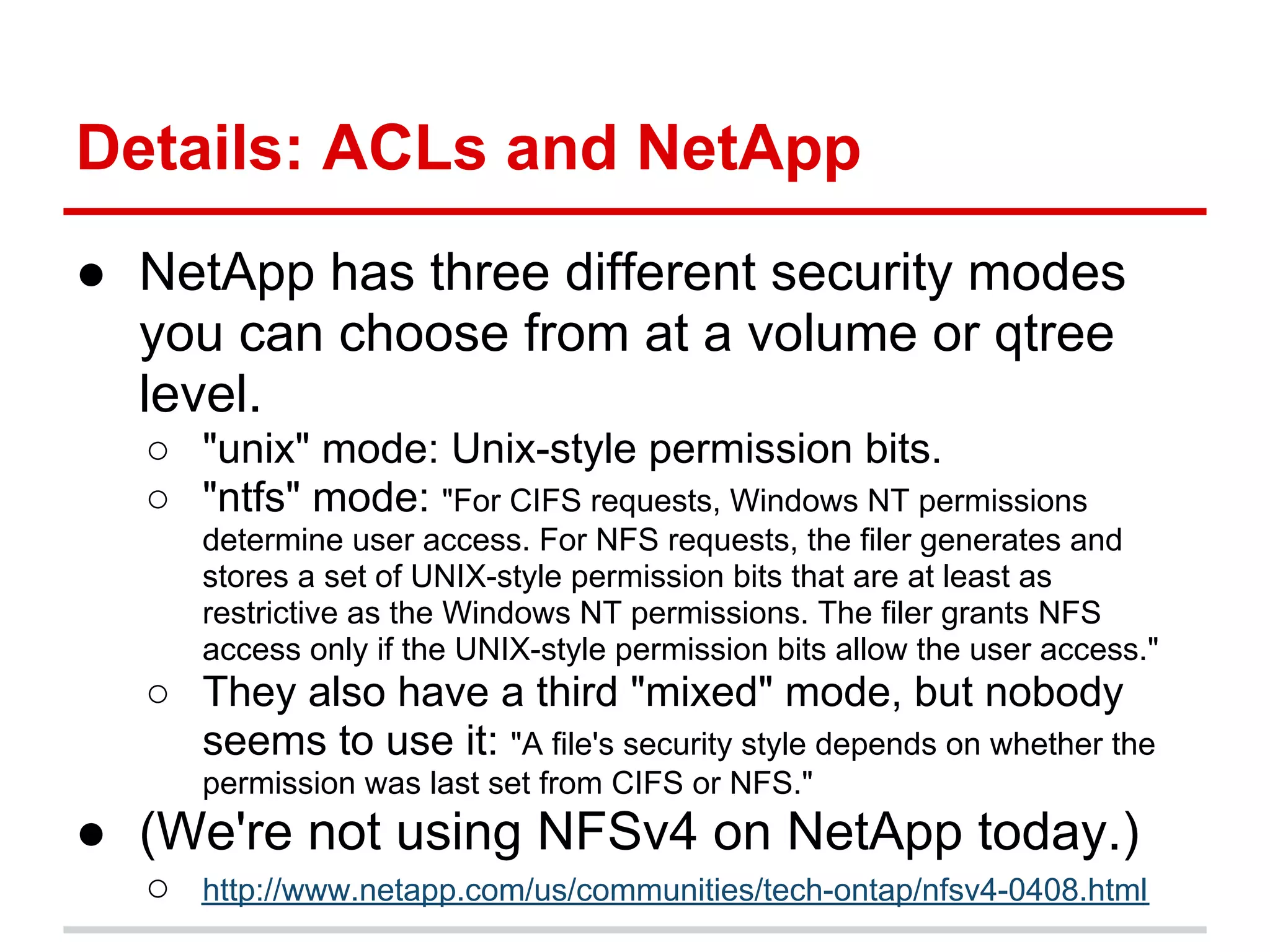
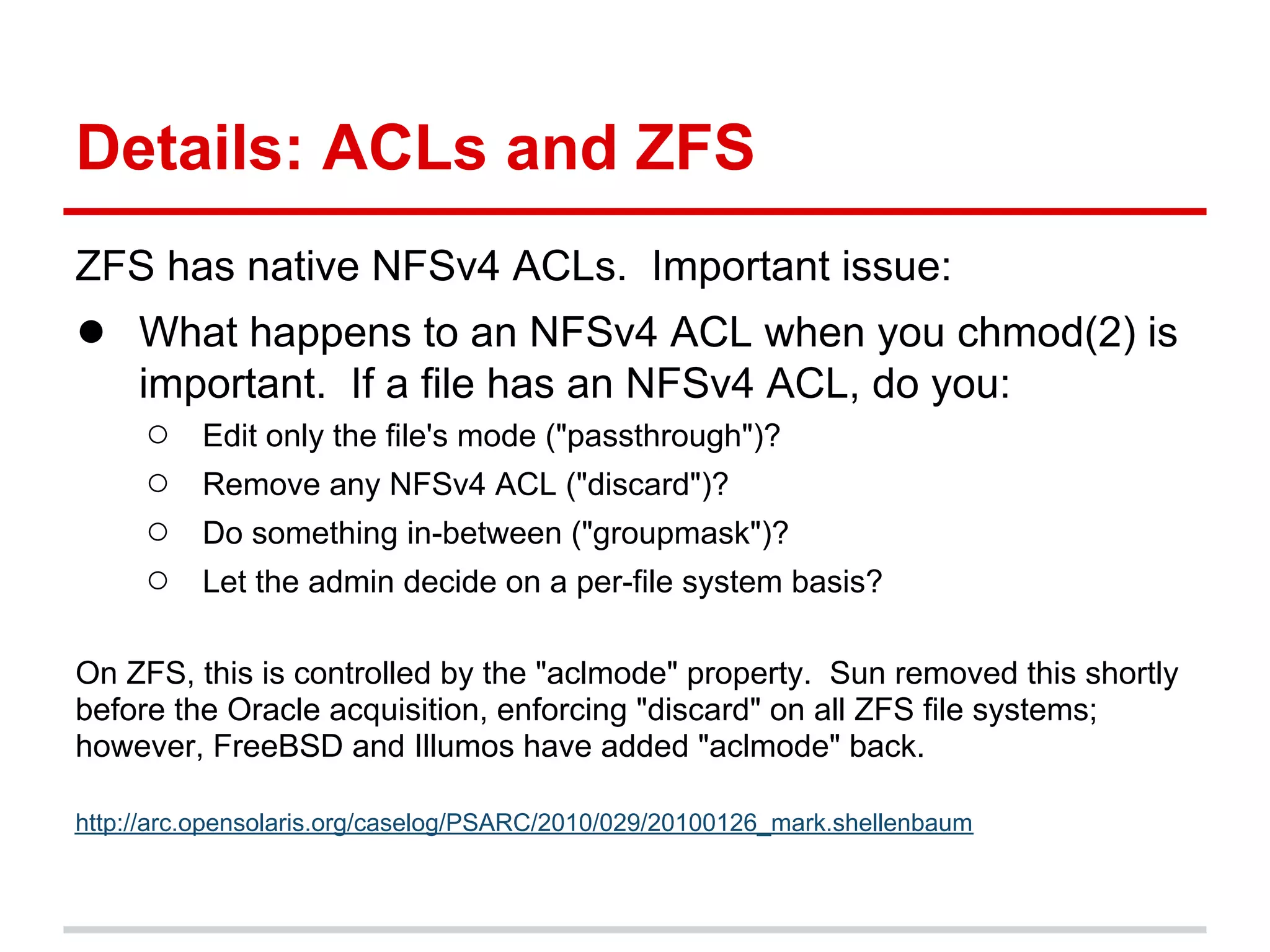
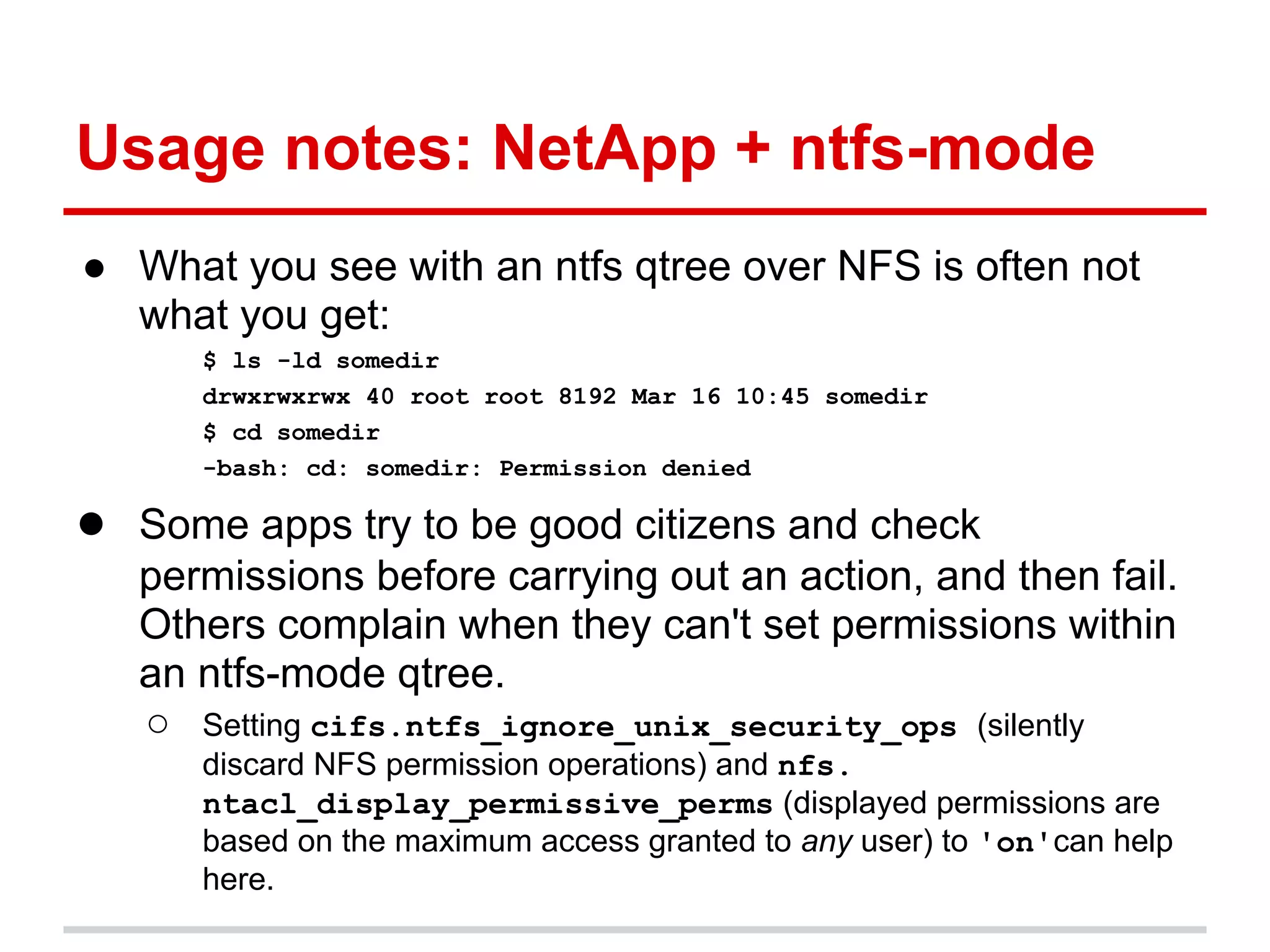
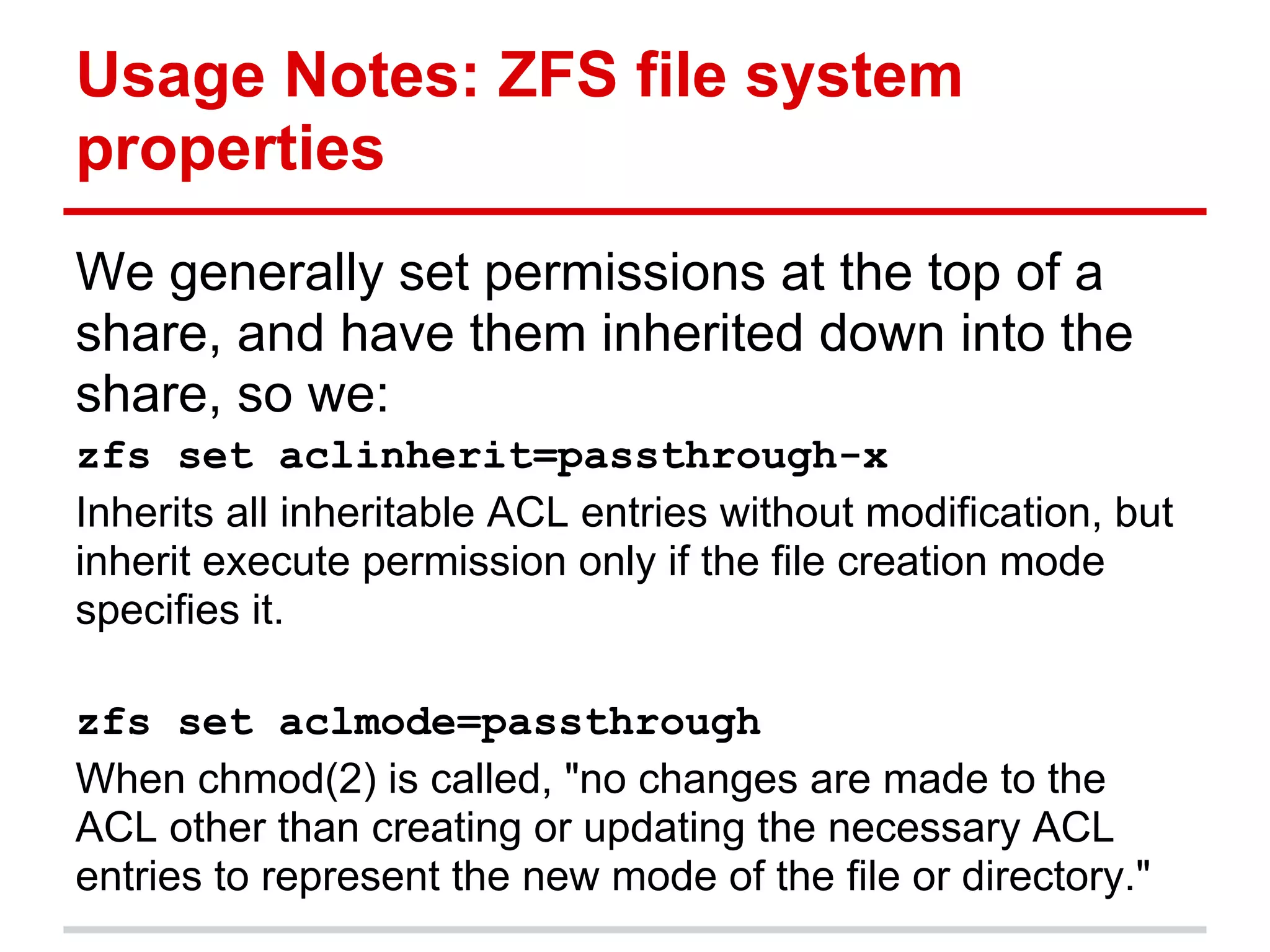
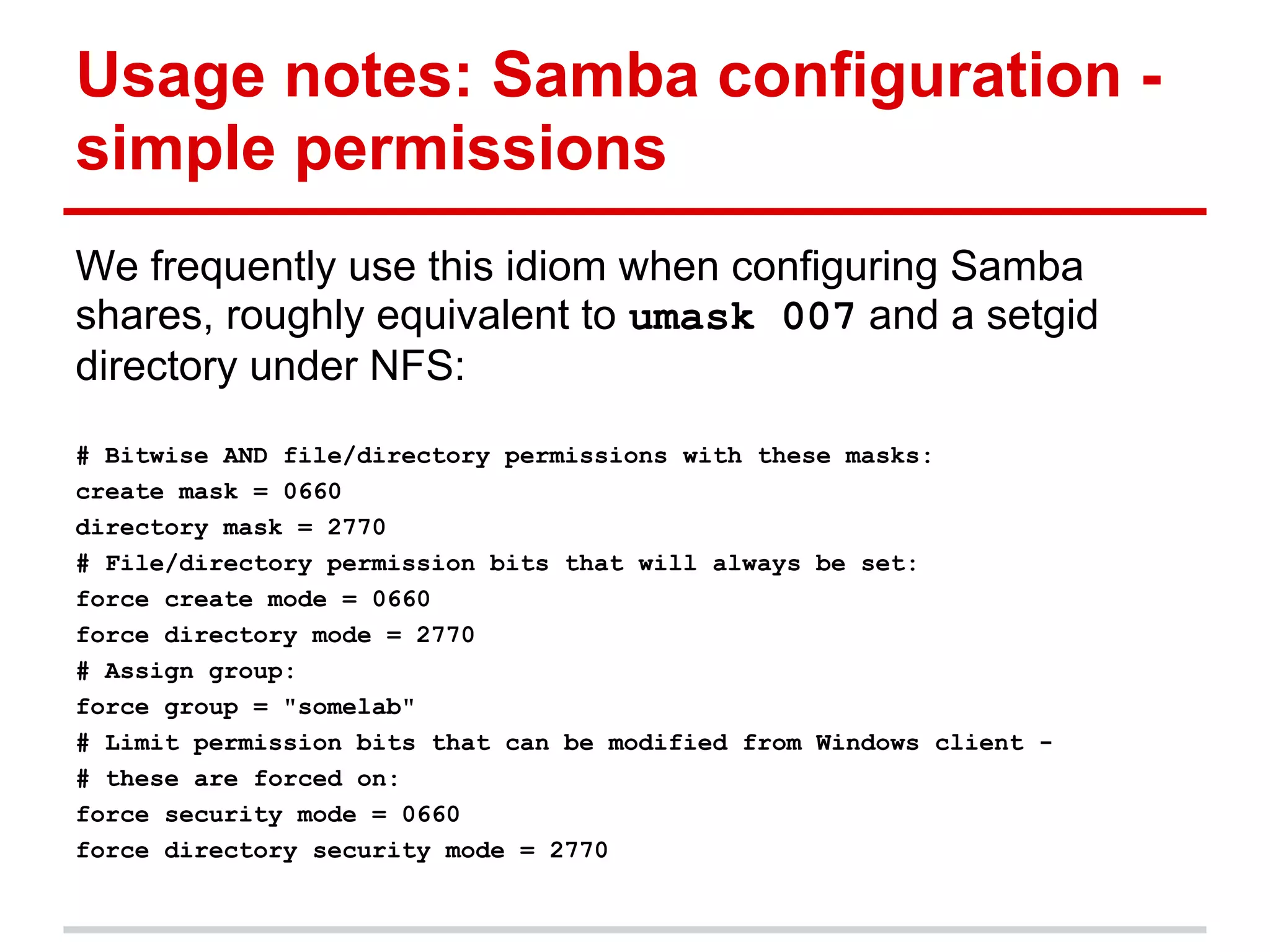
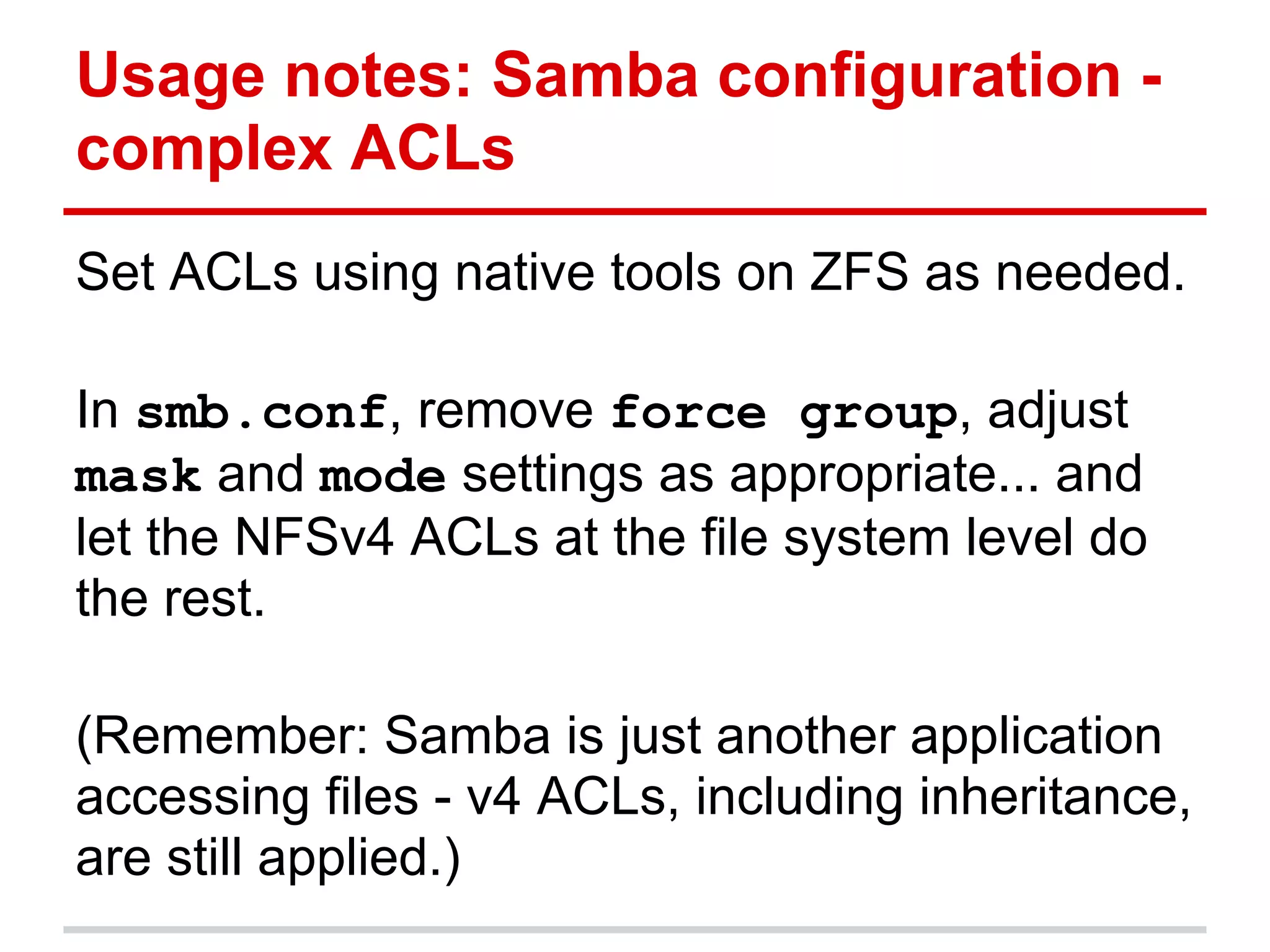
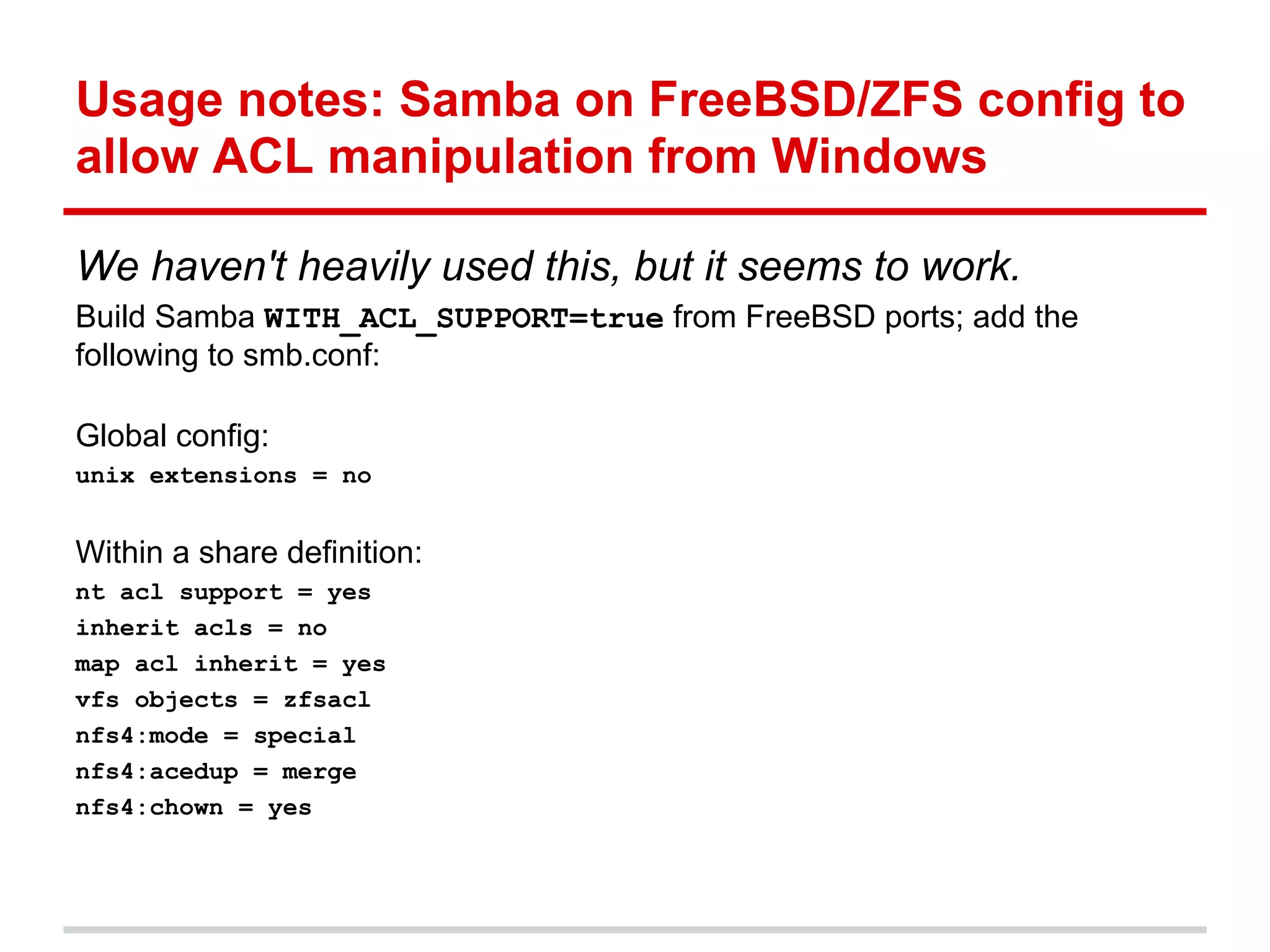
This document discusses access control lists (ACLs) and how they are implemented across different platforms and file systems. It provides a history of ACL implementations including POSIX ACLs, NTFS ACLs, and NFSv4 ACLs. It also discusses specifics of how ACLs are supported and some issues that can arise with ACLs on the author's NetApp and FreeBSD environments. Overall, the document aims to educate about ACL standards and interoperability challenges across platforms.