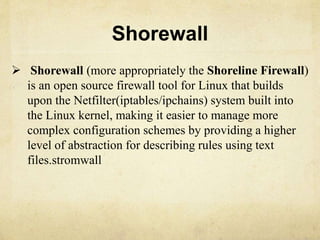
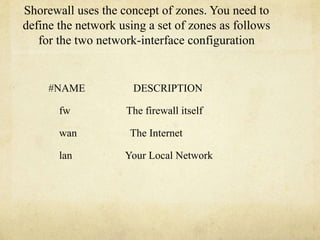
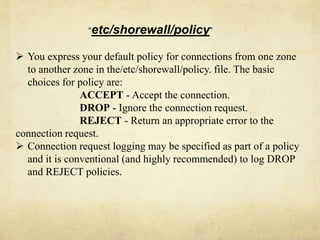
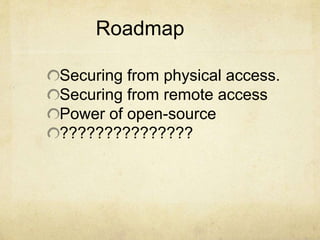
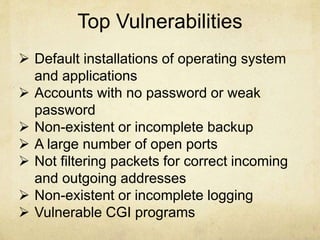
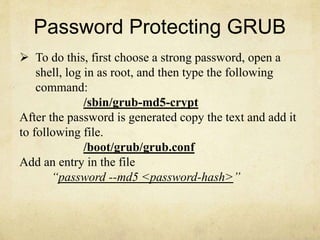
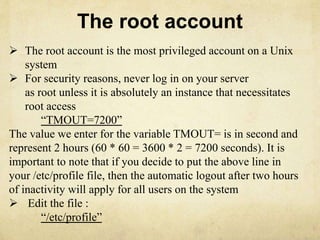
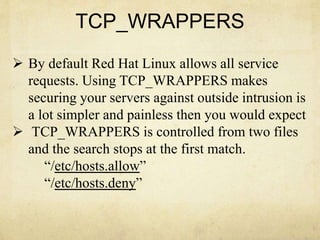
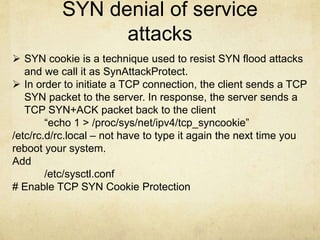
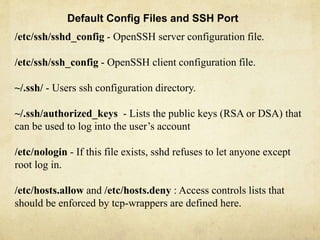
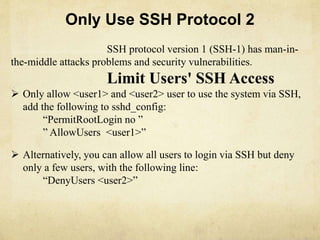
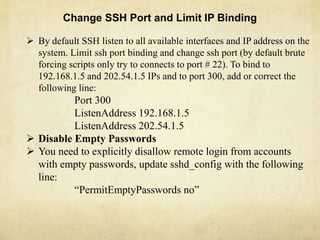
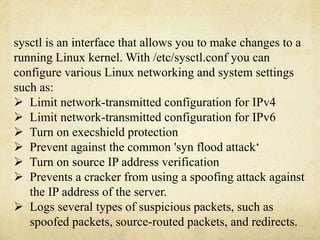
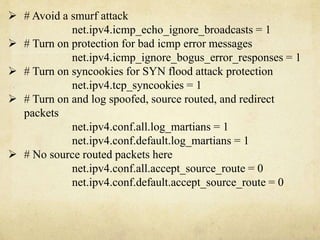
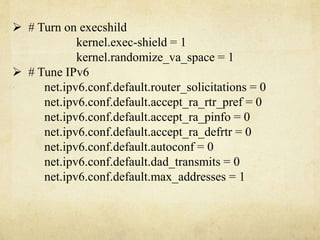
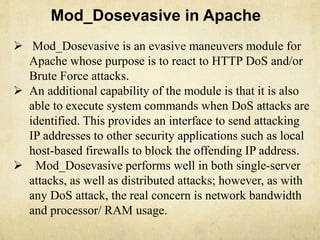
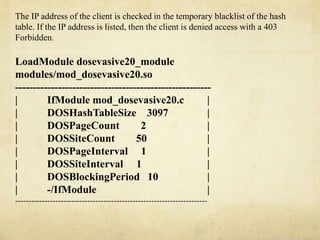
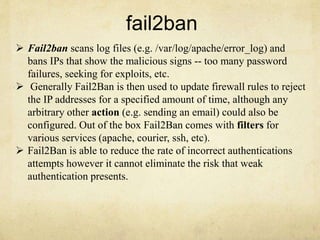
The document discusses various methods for hardening Linux security, including securing physical and remote access, addressing top vulnerabilities like weak passwords and open ports, implementing security policies, setting BIOS passwords, password protecting GRUB, choosing strong passwords, securing the root account, disabling console programs, using TCP wrappers, protecting against SYN floods, configuring SSH securely, hardening sysctl.conf settings, leveraging open source tools like Mod_Dosevasive, Fail2ban, Shorewall, and implementing security at the policy level with Shorewall.


![bantime = 3600
ignoreip = 127.0.0.1/8
maxretry = 3
# A host is banned if it has generated "maxretry" during the
last "findtime"
findtime = 600 # seconds
[ssh-iptables]
enabled = true
Filter = sshd
action = iptables[name=SSH, port=ssh, protocol=tcp]
sendmail-whois[name=SSH, dest=root,
sender=fail2ban@example.com, sendername="Fail2Ban"]
logpath = /var/log/secure
maxretry = 5](https://image.slidesharecdn.com/lyfnsq6lrgarlq1y5ba8-signature-113473783658b09a133a1f44f9ab91f23b00573ea88431292c7ebcf423658807-poli-140904042716-phpapp02/85/Server-hardening-25-320.jpg)