Chapter 3
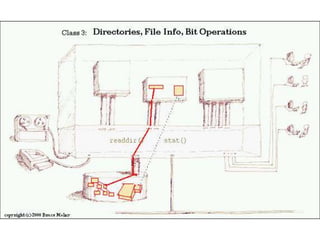
- 6. What does ls do? How does it work? What does ls do? Lists the contents of directories Displays information about files How does it work? How to list the contents of a directory? How to obtain and display properties of a file? How to determine if a name refers to a file or a directory?
- 12. direct structure structdirent { ino_td_ino; /* inode number */ off_td_off; /* offset to the next dirent */ unsigned short d_reclen; /* length of this record */ unsigned char d_type; /* type of file */ char d_name[256]; /* filename */ };
- 18. stat structure struct stat { dev_tst_dev; /* ID of device containing file */ ino_tst_ino; /* inode number */ mode_tst_mode; /* protection: type and permission */ nlink_tst_nlink; /* number of hard links */ uid_tst_uid; /* user ID of owner */ gid_tst_gid; /* group ID of owner */ dev_tst_rdev; /* device ID (if special file) */ off_tst_size; /* total size, in bytes */ blksize_tst_blksize; /* blocksize for file system I/O */ blkcnt_tst_blocks; /* number of 512B blocks allocated */ time_tst_atime; /* time of last access */ time_tst_mtime; /* time of last modification */ time_tst_ctime; /* time of last status (properties) change */ };
- 20. Converting File Mode to a String
- 25. Flag for st_mode field The following flags are defined for the st_mode field: #define S_IFMT 0170000 bit mask for the file type bit fields #define S_IFSOCK 0140000 socket #define S_IFLNK 0120000 symbolic link #define S_IFREG 0100000 regular file #define S_IFBLK 0060000 block device #define S_IFDIR 0040000 directory #define S_IFCHR 0020000 character device #define S_IFIFO 0010000 FIFO
- 26. Flag for st_mode field The following flags are defined for the st_mode field: #define S_ISUID 0004000 set UID bit #define S_ISGID 0002000 set-group-ID bit (see below) #define S_ISVTX 0001000 sticky bit (see below) #define S_IRWXU 00700 mask for file owner permissions #define S_IRUSR 00400 owner has read permission #define S_IWUSR 00200 owner has write permission #define S_IXUSR 00100 owner has execute permission #define S_IRWXG 00070 mask for group permissions #define S_IRGRP 00040 group has read permission #define S_IWGRP 00020 group has write permission #define S_IXGRP 00010 group has execute permission
- 27. Flag for st_mode field #define S_IRWXO 00007 mask for permissions for others (not in group) #define S_IROTH 00004 others have read permission #define S_IWOTH 00002 others have write permission #define S_IXOTH 00001 others have execute permission
- 28. File Type Macros The following POSIX macros are defined to check the file type using the st_mode field: S_ISREG(m) is it a regular file? S_ISDIR(m) directory? S_ISCHR(m) character device? S_ISBLK(m) block device? S_ISFIFO(m) FIFO (named pipe)? S_ISLNK(m) symbolic link? (Not in POSIX.1-1996.) S_ISSOCK(m) socket? (Not in POSIX.1-1996.)
- 30. struct passwd The passwd structure is defined in <pwd.h> as follows: structpasswd { char *pw_name; /* username */ char *pw_passwd; /* user password */ uid_tpw_uid; /* user ID */ gid_tpw_gid; /* group ID */ char *pw_gecos; /* real name */ char *pw_dir; /* home directory */ char *pw_shell; /* shell program */ };
- 31. sprintf #include <stdio.h> main() { char st[5]="test"; char outString[50]=""; sprintf(outString, "This is a %s", st); printf("%s", outString); }
- 33. Special Constant Expressions Constant values can be declared explicitly as long values, in fact, by placing the letter L after the constant. long int variable = 23L; variable = 236526598L
- 34. Advanced programmers, writing systems software, often find it convenient to work with hexadecimal or octal numbers since these number bases have a special relationship to binary. A constant in one of these types is declared by placing either 0 (zero) or 0x in front of the appropriate value.If ddd is a value, then: Octal number 0ddd Hexadecimal number 0xddd
- 35. For example: oct_value = 077; /* 77 octal */ hex_value = 0xFFEF; /* FFEF hex */
- 36. Three Special Bits Set-User-ID Bit Example, How can a regular user change his or her password since passwd file is owned by root? -rw-r--r-- 1 rootroot 2391 2009-09-01 10:59 /etc/passwd Solution: Give permission to the program, not to user. The program, /usr/bin/passwd, is owned by root and has the set-user-ID bit set. -rwsr-xr-x 1 root root 29328 2008-04-08 09:49 /usr/bin/passwd
- 37. Three Special Bits The SUID bit tells the kernel to run the program as though is were being run by the owner of the program. This bit causes the kernel to set the effective user ID to the user ID of the owner of the program. The Set-Group-ID bit: sgid If a program belongs to group g and the set group ID is set, the program runs as though it were being a member of group g.
- 38. A mask to test for the SUID Bit #define S_ISUID 0004000 0000 100 000 000 000 A mask to test for the SGID Bit #define S_ISGID0002000 0000 010 000 000 000 Indicates a octal number suid Other group User sgid Other group User Other Other
- 39. Three Special Bits The Sticky bit: The sticky bit tells the kernel to keep the program on the swap device even if no one is using it. The sway device is faster than hard disk because no fragments happen.
- 40. Understanding file permissions on Unix: a brief tutorial http://www.dartmouth.edu/~rc/help/faq/permissions.html -rw-rw---- 2 richard staff 12040 Aug 20 1996 admin/userinfo drwxr-xr-x 3 richard user 2048 May 13 09:27 public s in the place where 'x' would normally go is called the set-UID or set-groupID flag.