The document provides guidelines for enhancing web application security, covering topics such as protecting sites against various attacks, improving code quality, and implementing critical security headers like Content Security Policy and X-Frame-Options. It emphasizes the need for proper server configuration and directives to safeguard against vulnerabilities such as clickjacking and cross-site scripting (XSS). Additionally, the document discusses session and cookie protection, and the importance of using HTTPS and other measures to secure data in transit.






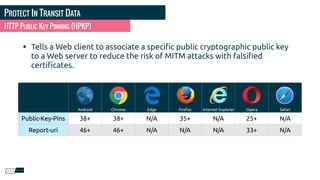
![PROTECT YOUR SITES
• content
• nosnippet
• noodp
• noydir
• notranslate
• noimageindex
• unavailable_after: [RFC-850 date/time]
META NAME=ROBOTS](https://image.slidesharecdn.com/header2017-en-170808125814/85/Browser-Serving-Your-Web-Application-Security-NorthEast-PHP-2017-9-320.jpg)

![IMPROVE YOUR CODE
• Normally, for IE8 +
• Requests IE to use the latest render engines or a particular version.
• Should use the ChromeFrame renderer (for IE6 and IE7)
• Does not validate
• Reduce the display speed of the site if it needs to change mode
• Does not work in a conditional comment ( <!--[if lt IE 7]> )
META/HEADER : X-UA-COMPATIBLE](https://image.slidesharecdn.com/header2017-en-170808125814/85/Browser-Serving-Your-Web-Application-Security-NorthEast-PHP-2017-13-320.jpg)

































![PROTECT YOUR COOKIES
PHP CODE
bool setcookie ( string $name [, string $value = "" [, int $expire = 0 [, string $path = ""
[, string $domain = "" [, bool $secure = false [, bool $httponly = false ]]]]]] )](https://image.slidesharecdn.com/header2017-en-170808125814/85/Browser-Serving-Your-Web-Application-Security-NorthEast-PHP-2017-51-320.jpg)


![HTTP STRICT TRANSPORT SECURITY
APACHE EXAMPLE
#apache
<VirtualHost *:80>
ServerAlias *
RewriteEngine On
RewriteRule ^(.*)$ https://%{HTTP_HOST}$1 [redirect=301]
</VirtualHost>
<VirtualHost *:443>
ServerAlias *
...
<IfModule mod_headers.c>
Header set Strict-Transport-Security “max-age=16070400; preload"
</IfModule>
</VirtualHost>](https://image.slidesharecdn.com/header2017-en-170808125814/85/Browser-Serving-Your-Web-Application-Security-NorthEast-PHP-2017-54-320.jpg)
![HTTP STRICT TRANSPORT SECURITY
PHP EXAMPLE
<?php
// IIS defines the HTTPS protocol to be “off” for non-SSL requests
if (isset($_SERVER['HTTPS']) && $_SERVER['HTTPS'] != 'off') {
header(’Strict-Transport-Security: max-age=16070400’);
} else {
header('Location: https://’.$_SERVER[’HTTP_HOST'] .
$_SERVER['REQUEST_URI'], true, 301);
exit;
}](https://image.slidesharecdn.com/header2017-en-170808125814/85/Browser-Serving-Your-Web-Application-Security-NorthEast-PHP-2017-55-320.jpg)