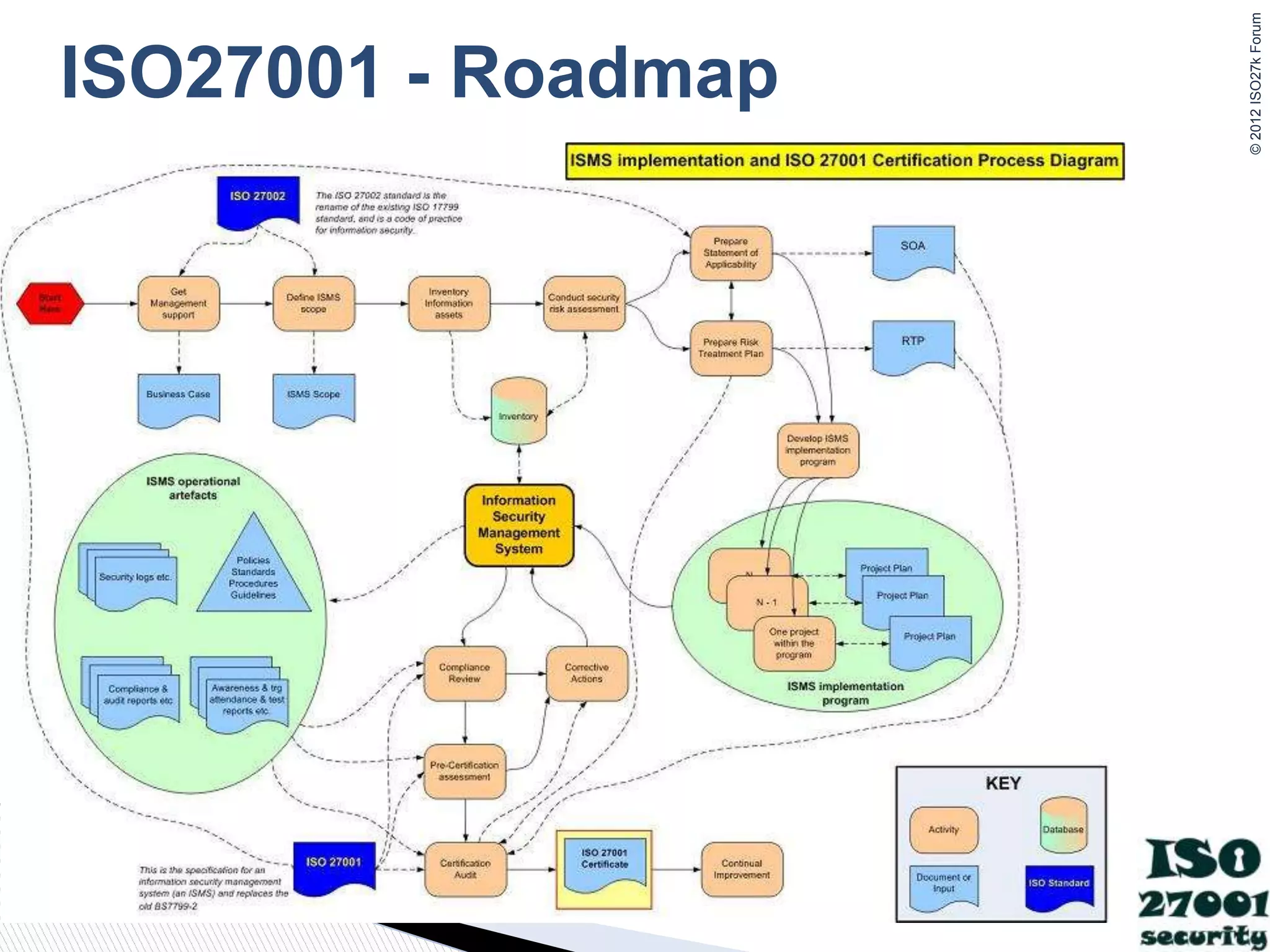
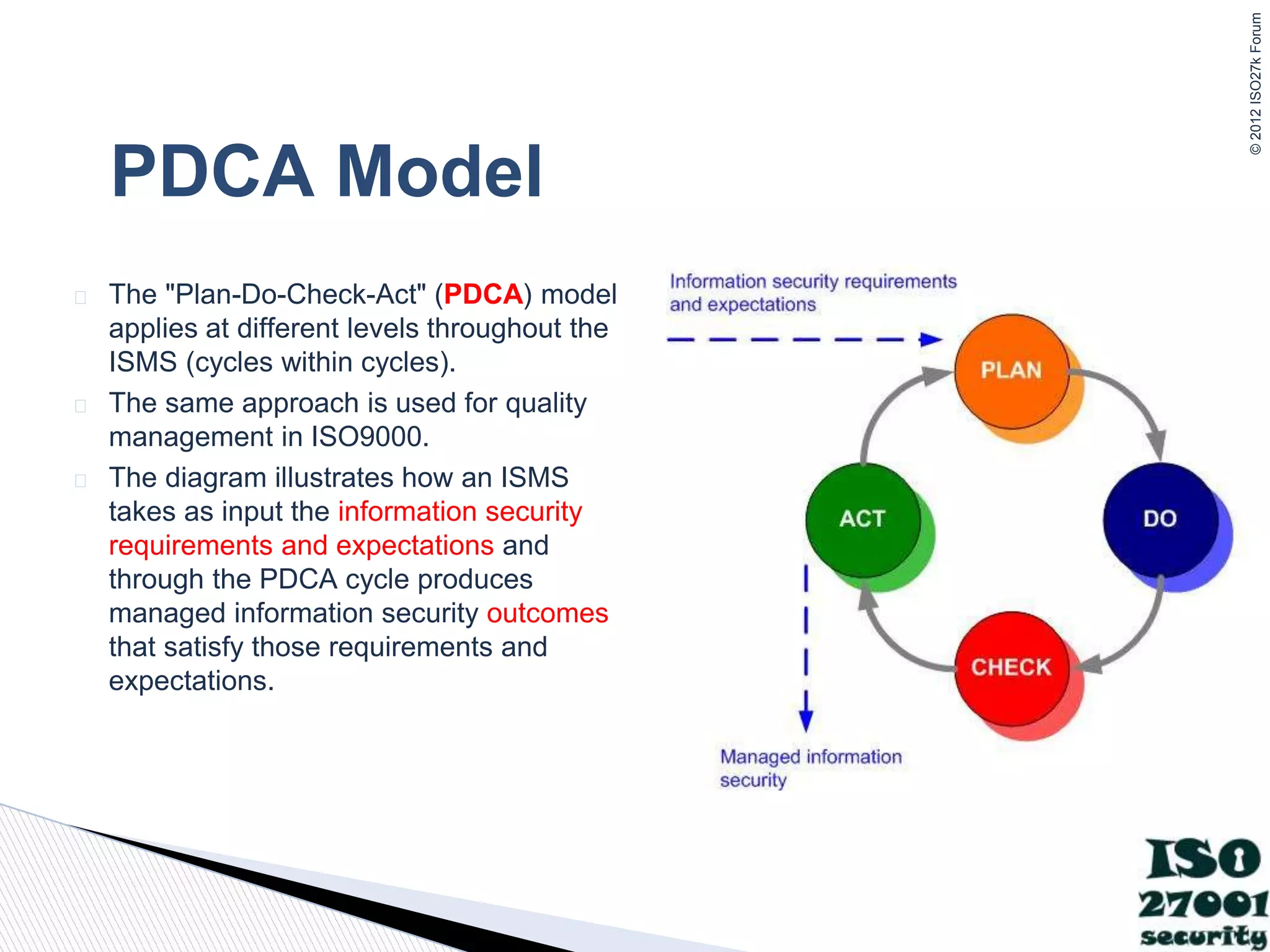
This document provides an overview of the ISO27001 Information Security Management System (ISMS) implementation and certification process. It describes establishing the ISMS scope, conducting a risk assessment, developing necessary documentation like the Statement of Applicability and Risk Treatment Plan, implementing controls, conducting internal audits and management reviews, completing a pre-certification assessment, and undergoing a certification audit to obtain ISO27001 certification. Certification verifies the organization has properly implemented an ISMS to systematically manage its information security risks.