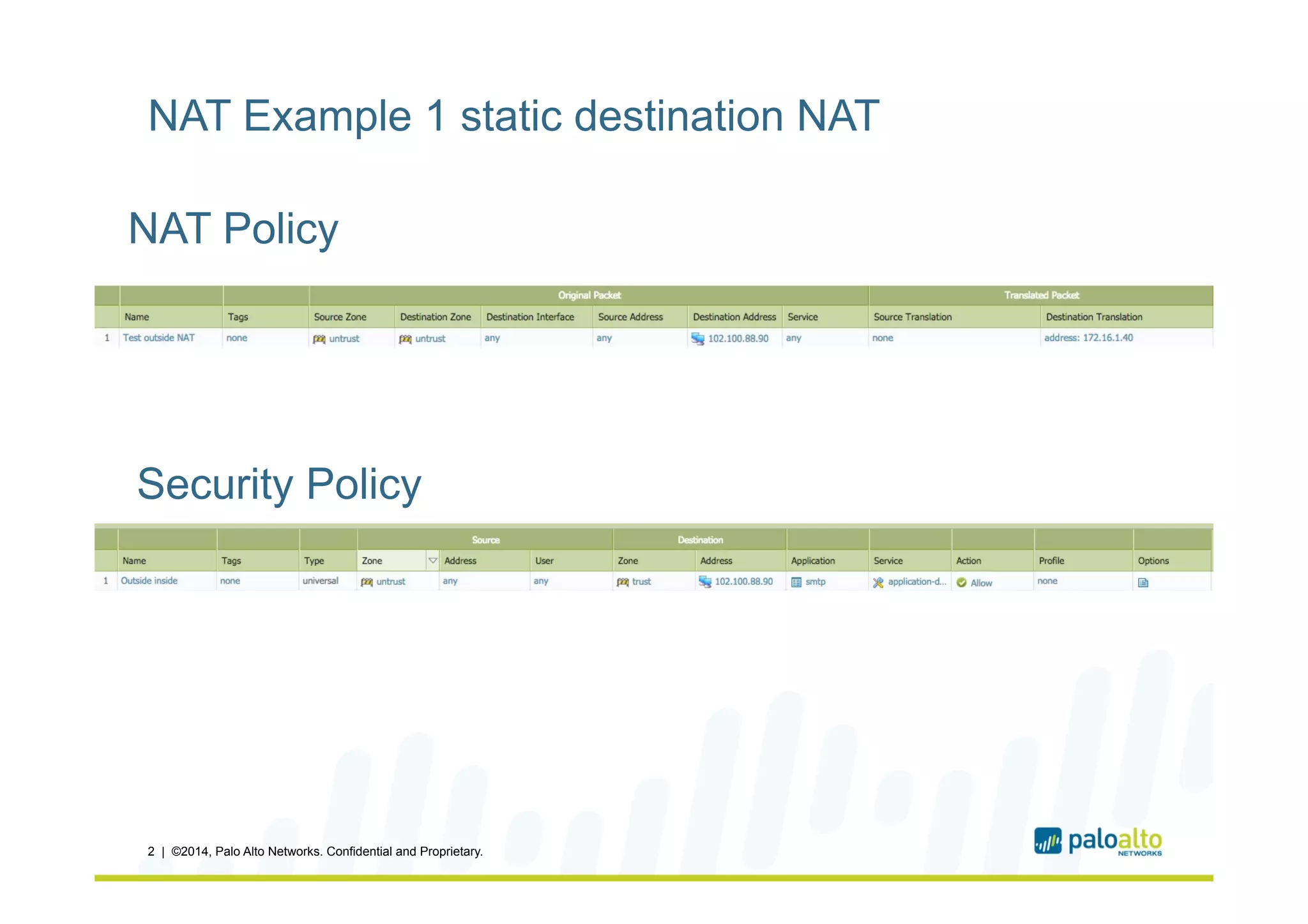
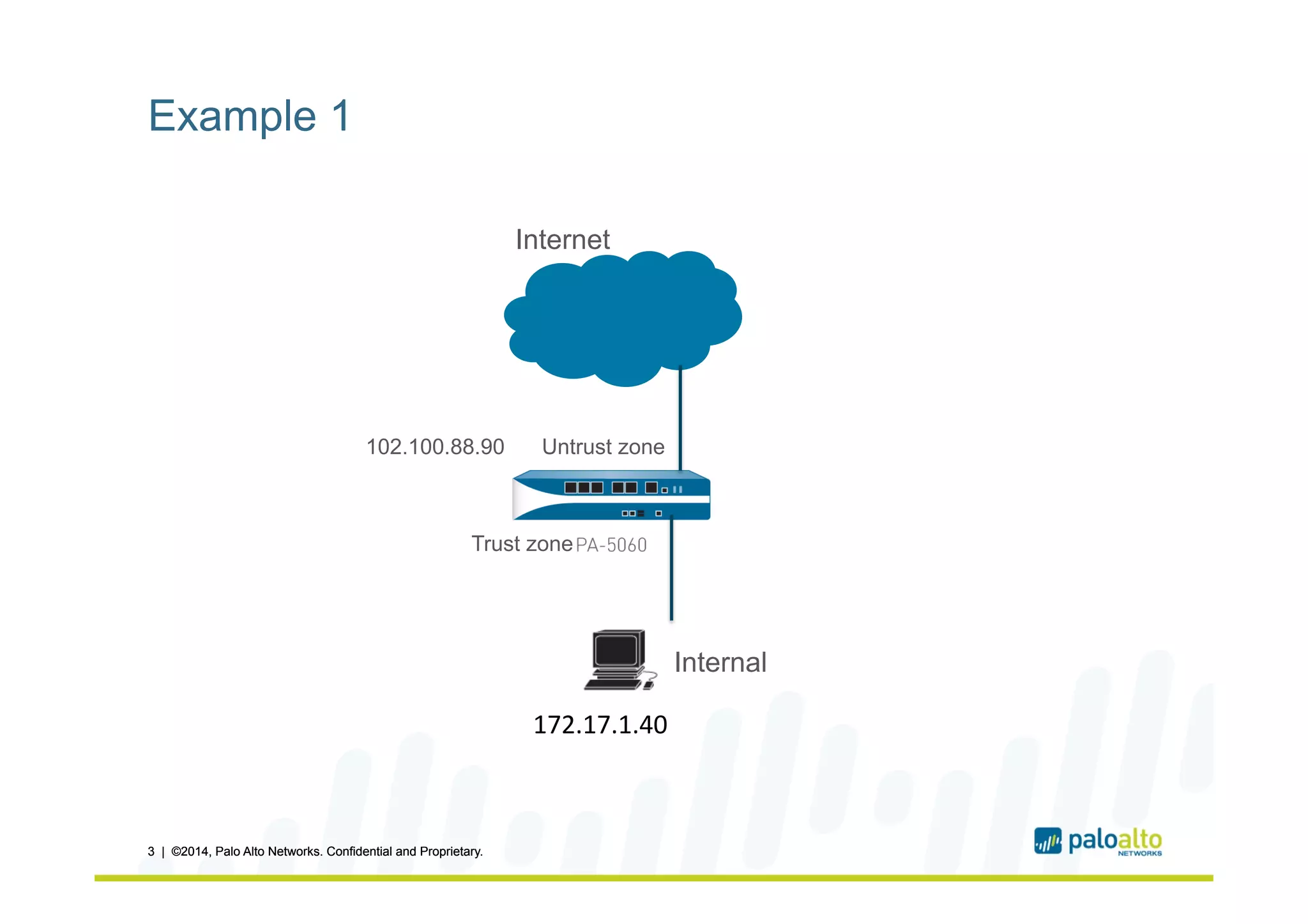
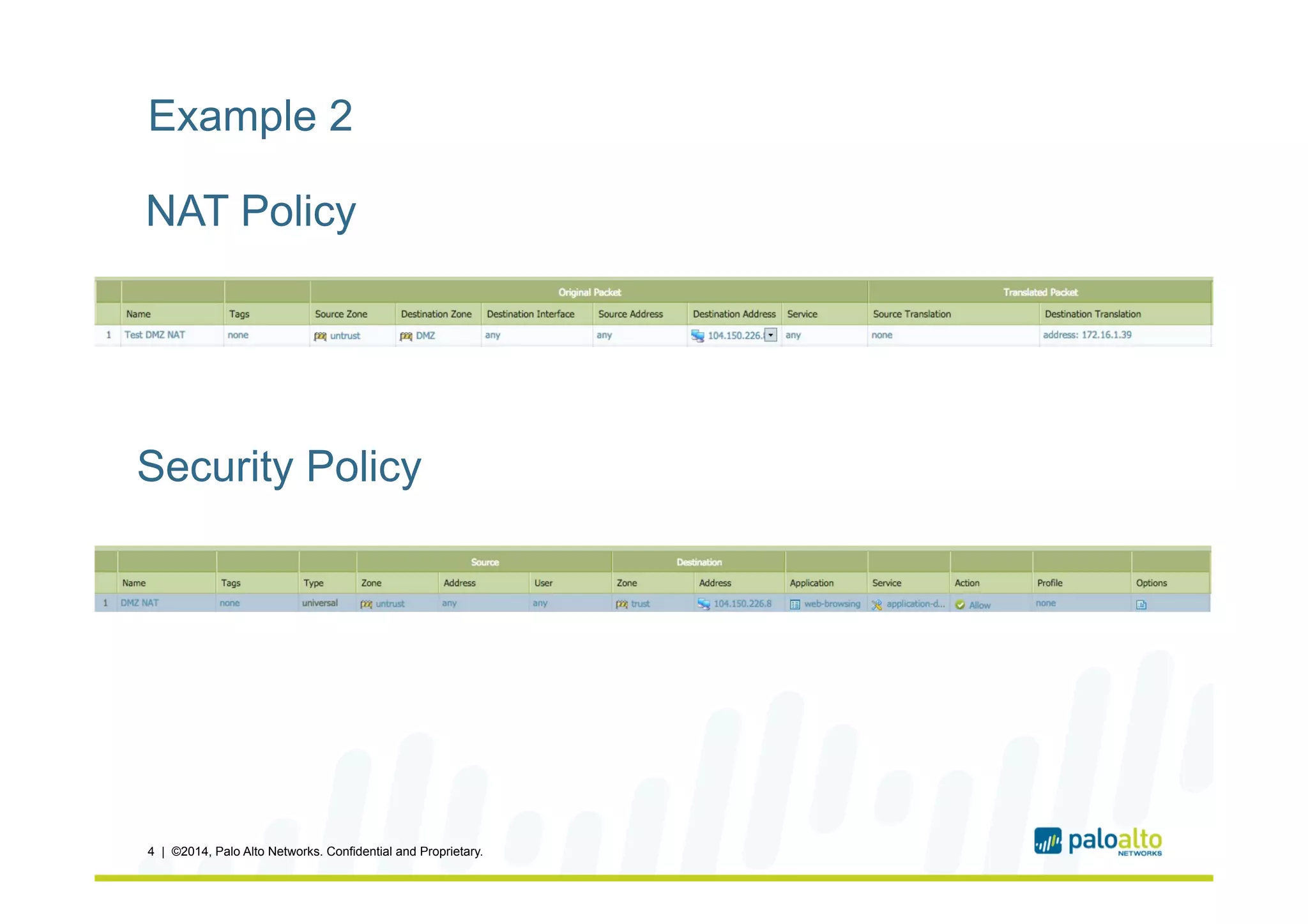
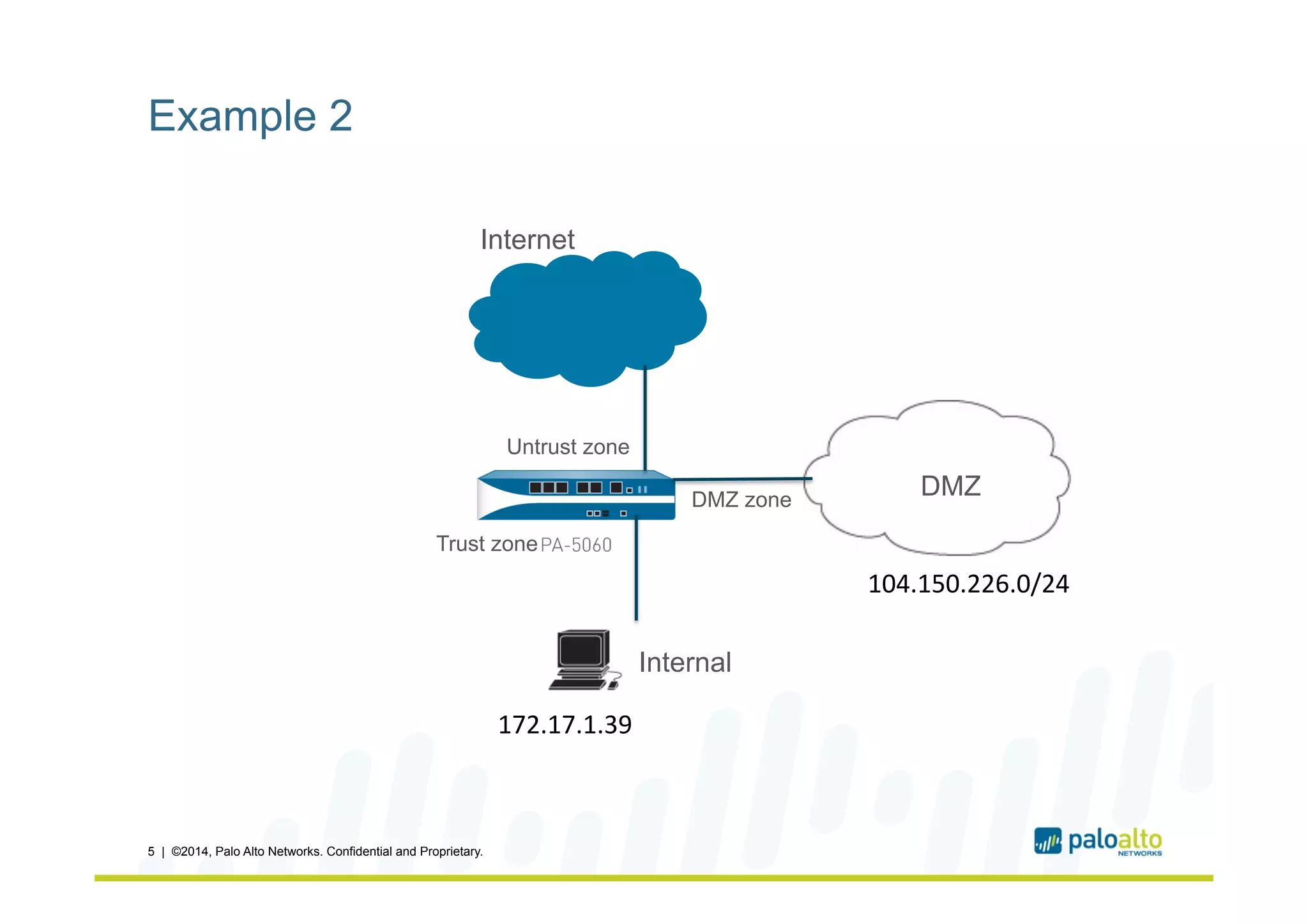
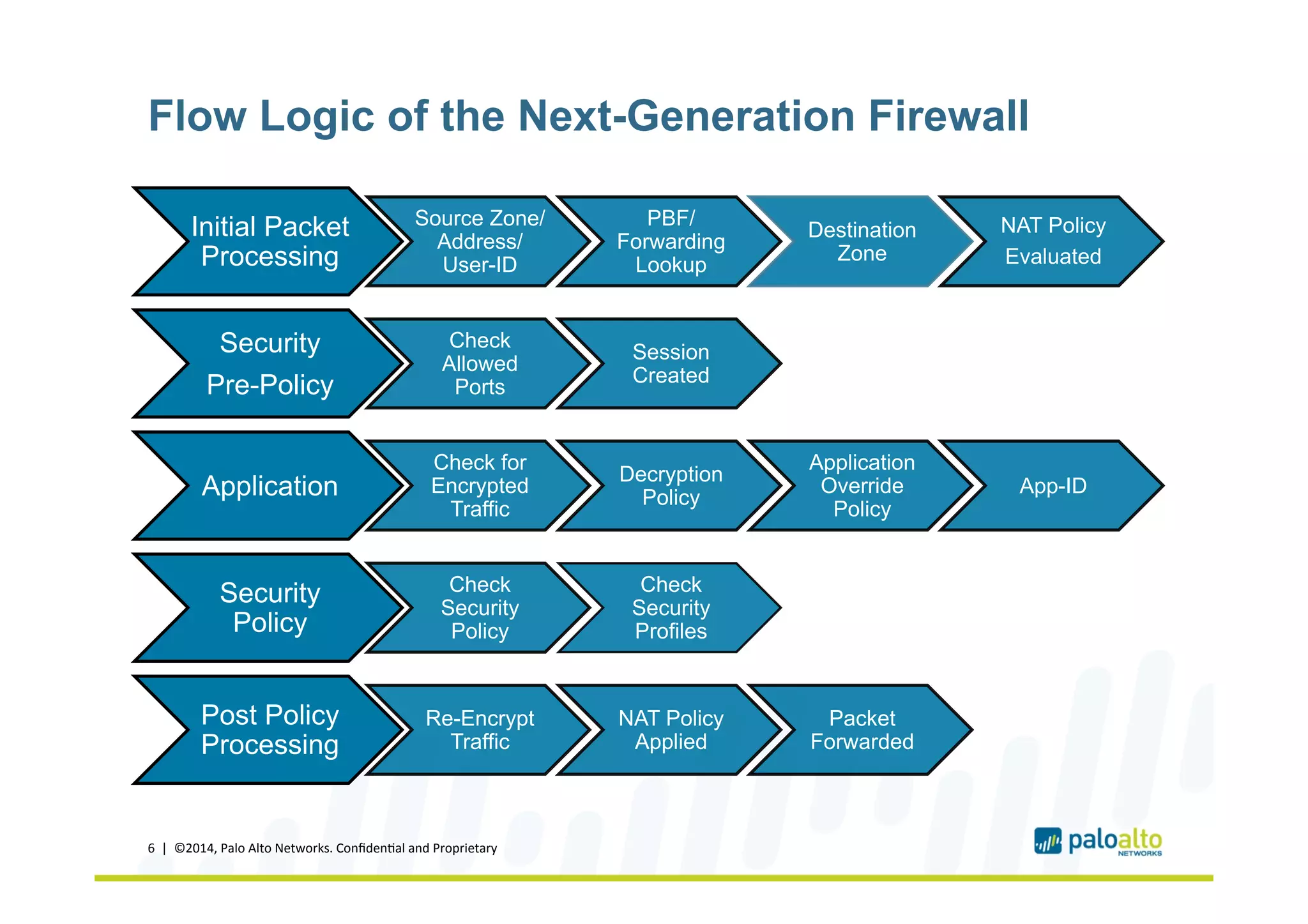
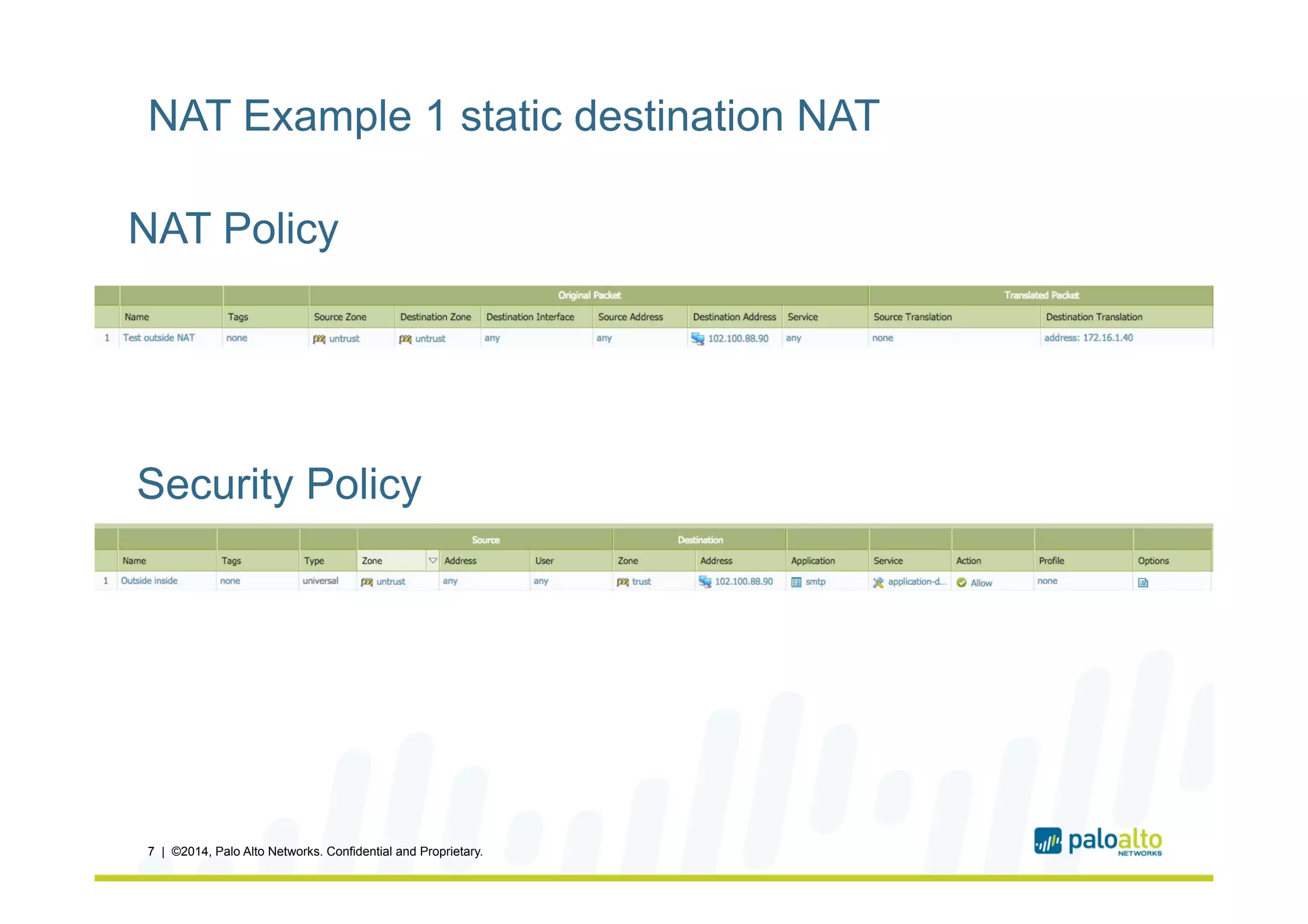
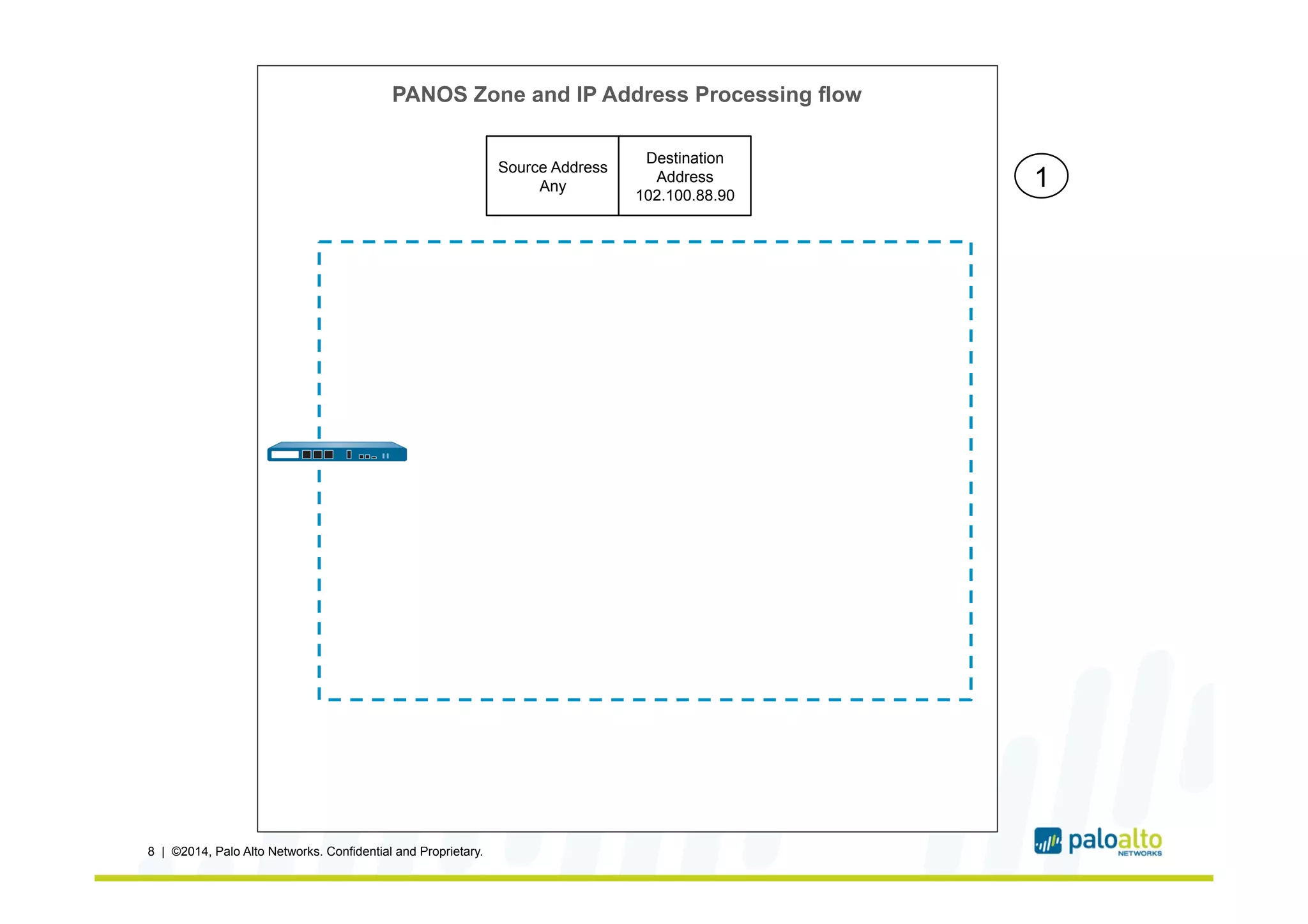
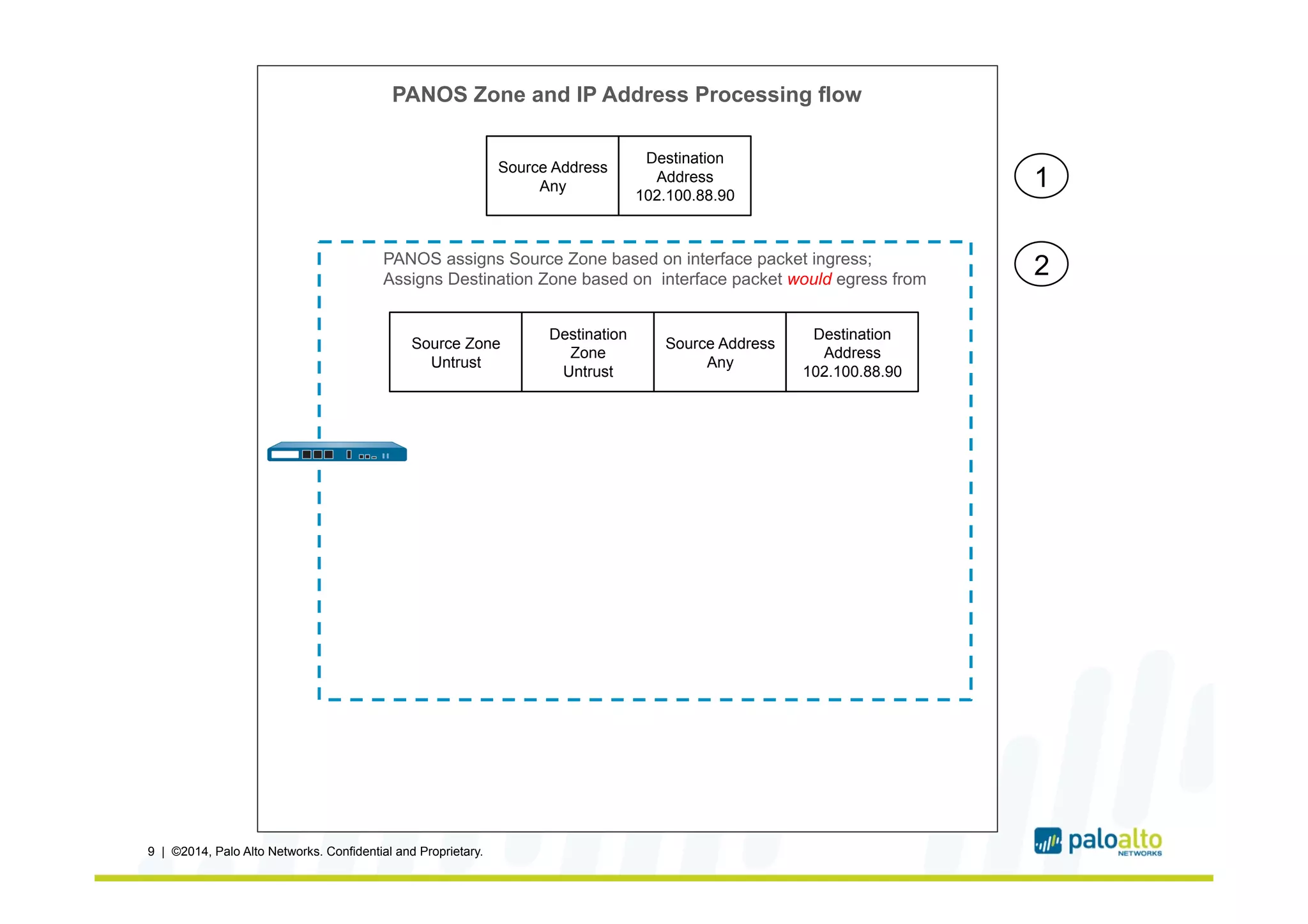
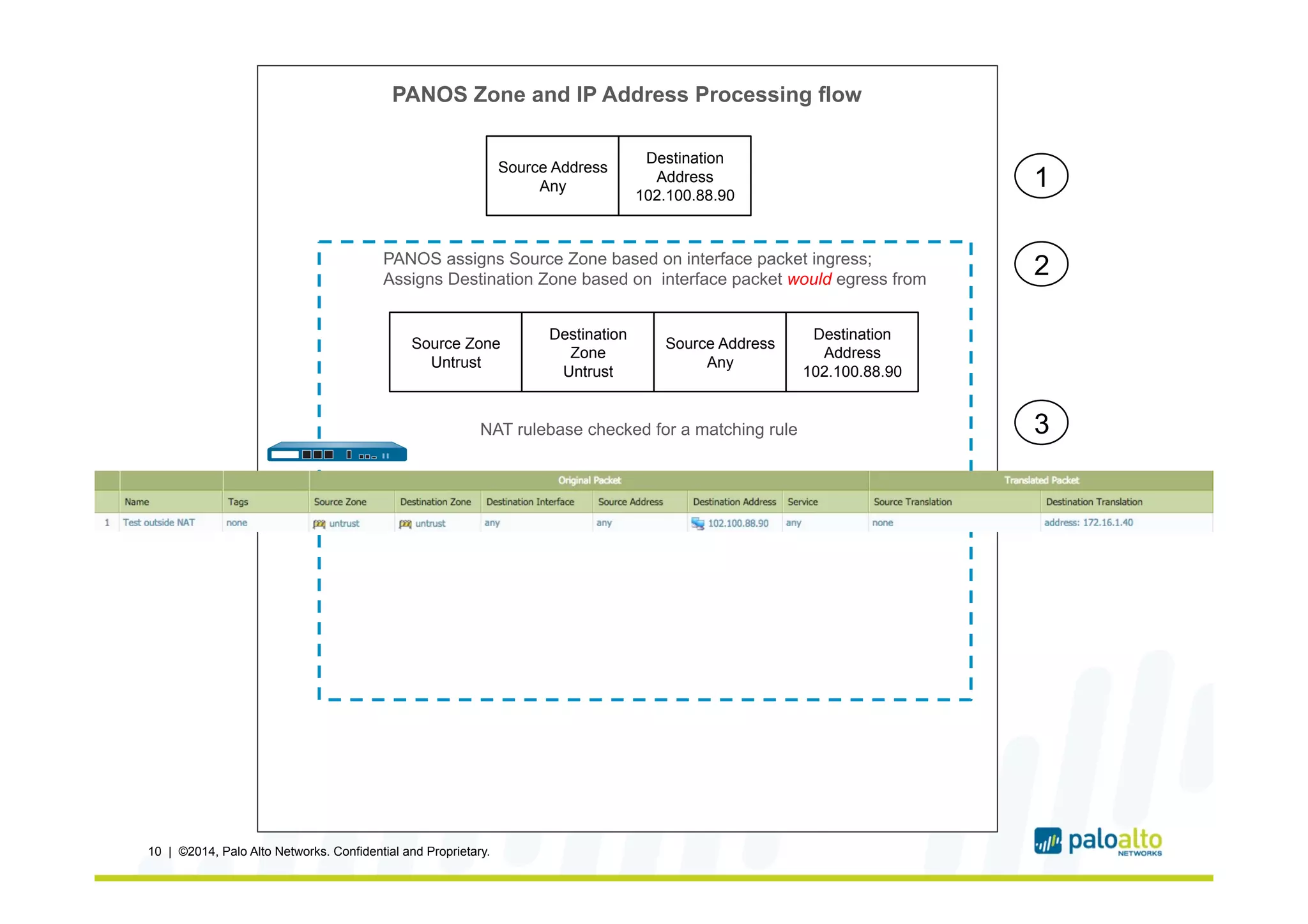
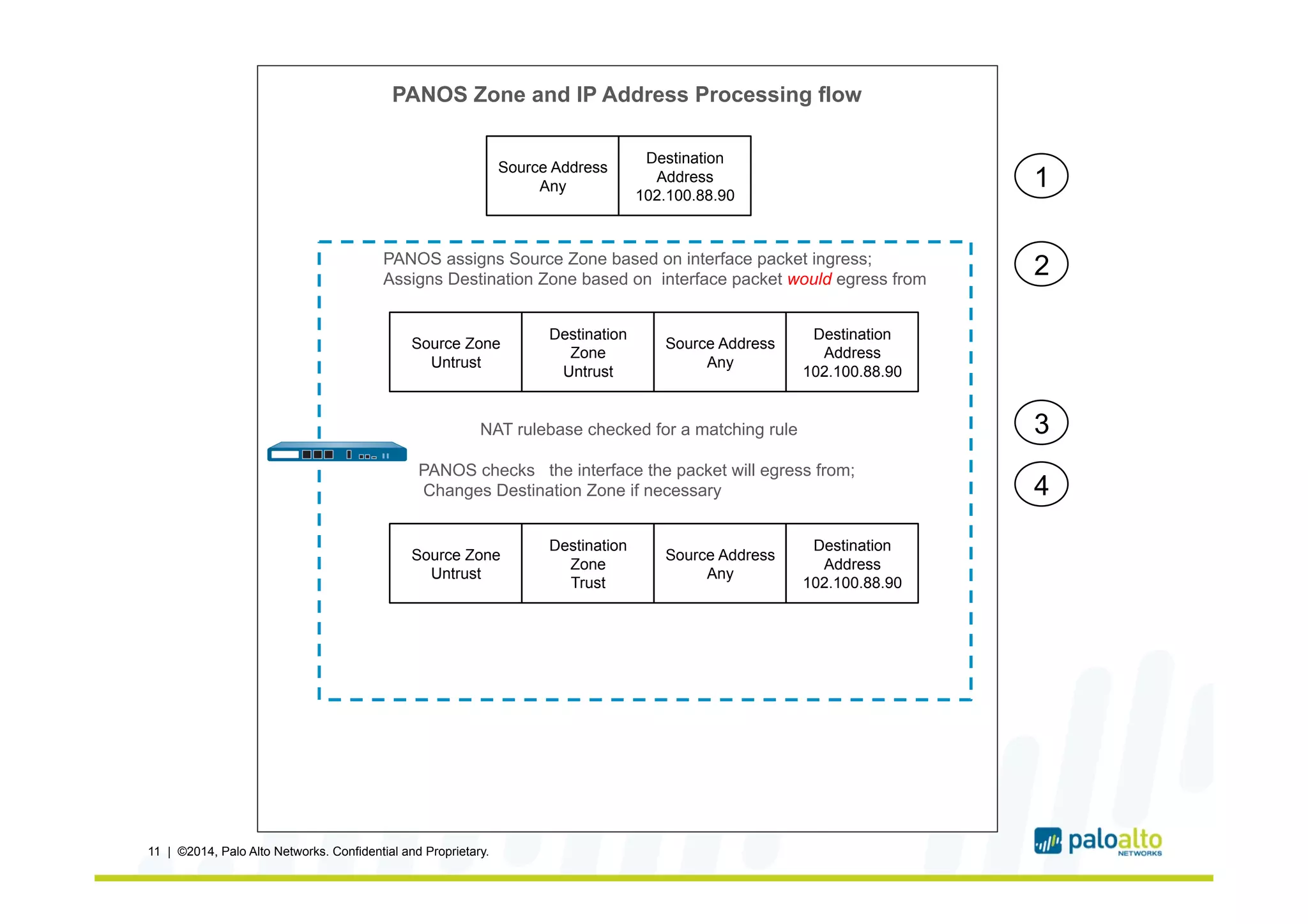
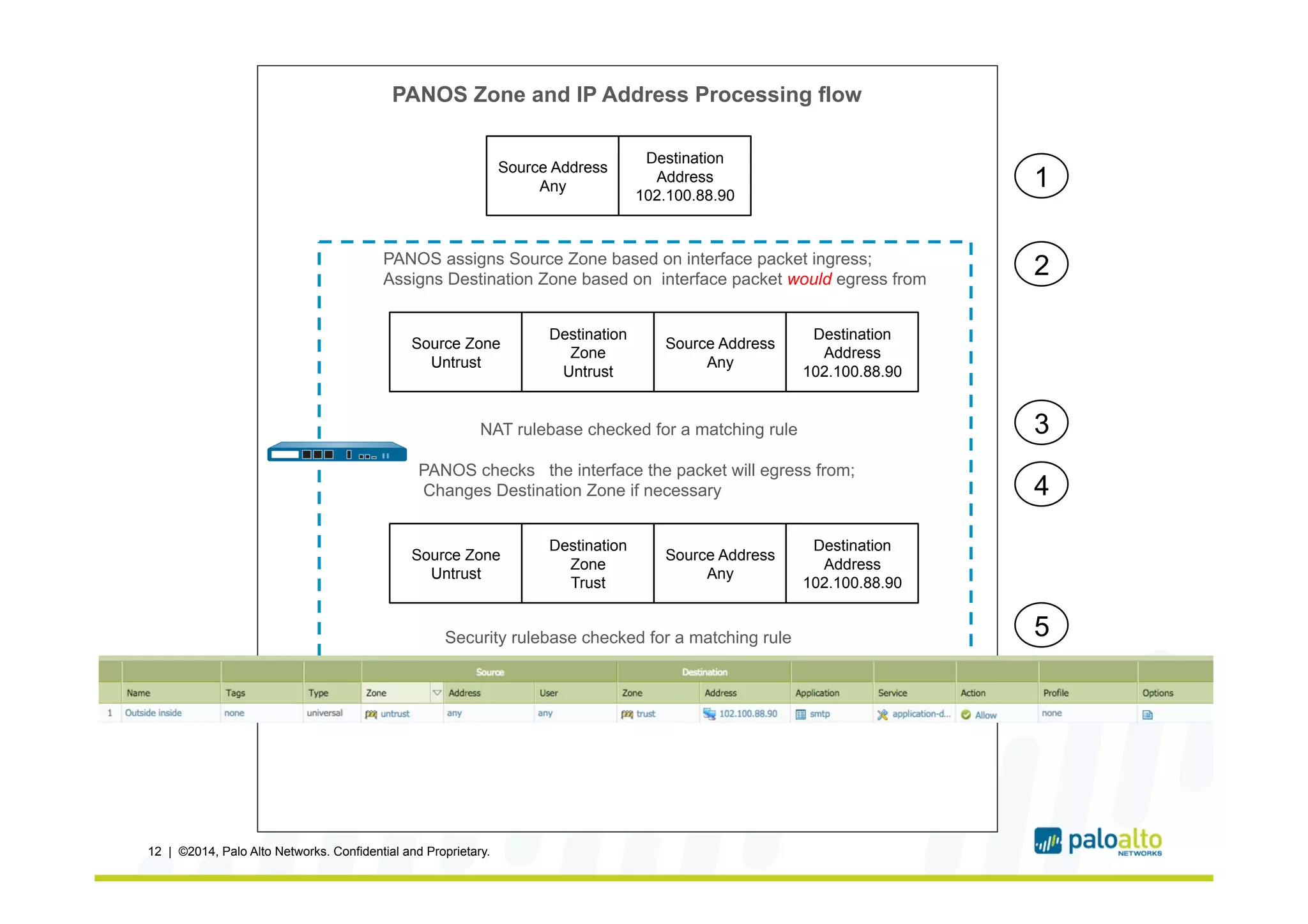
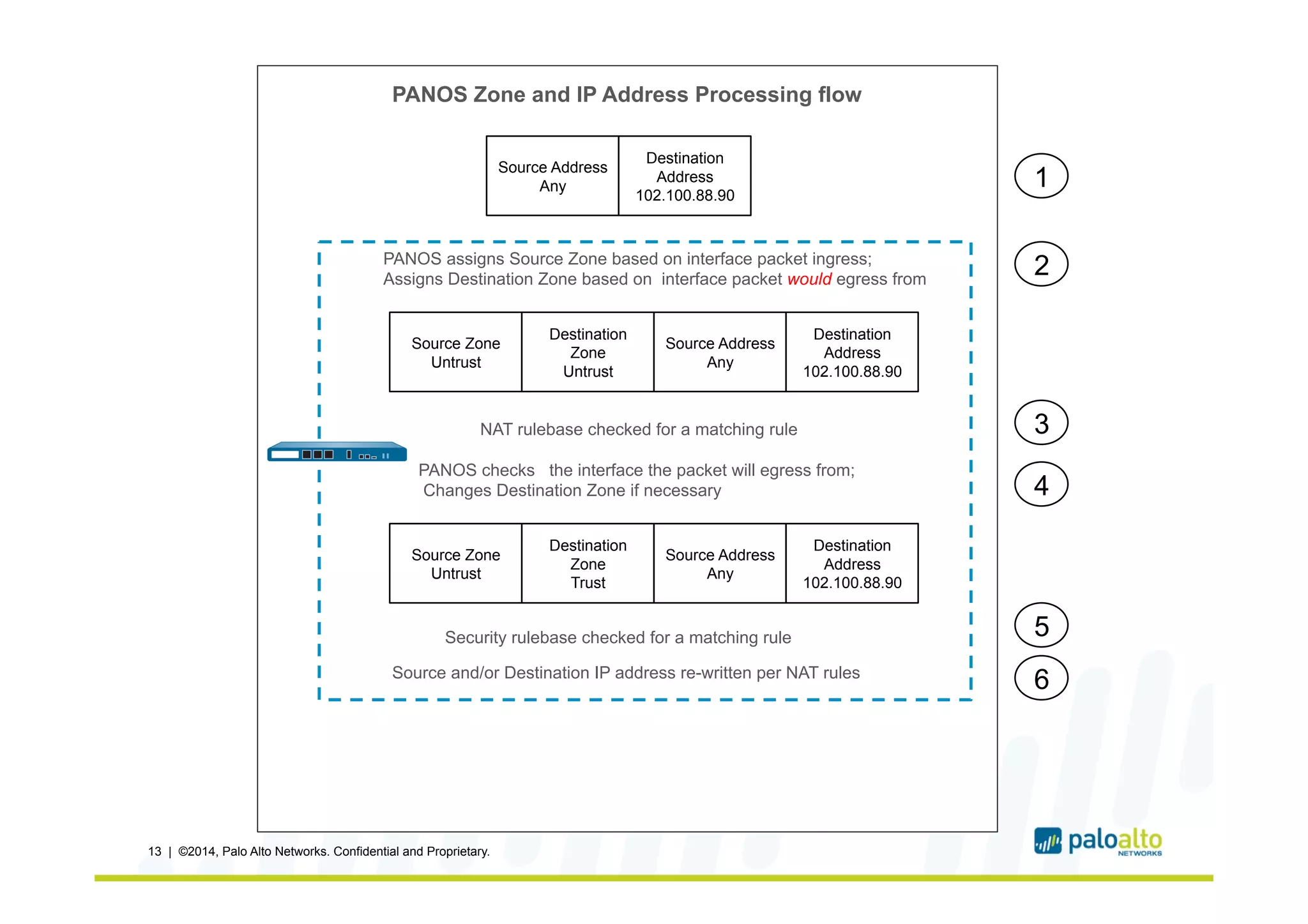
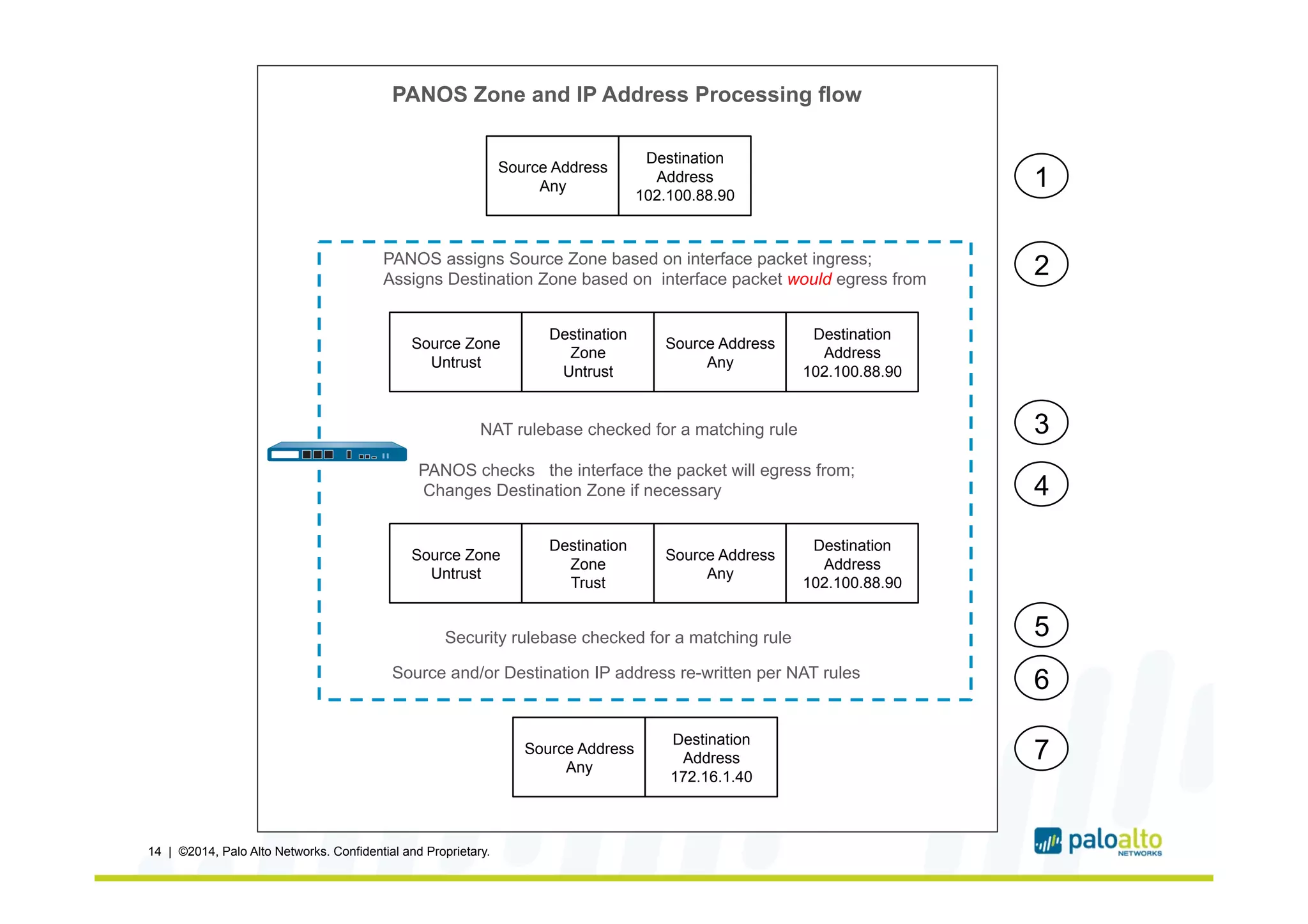
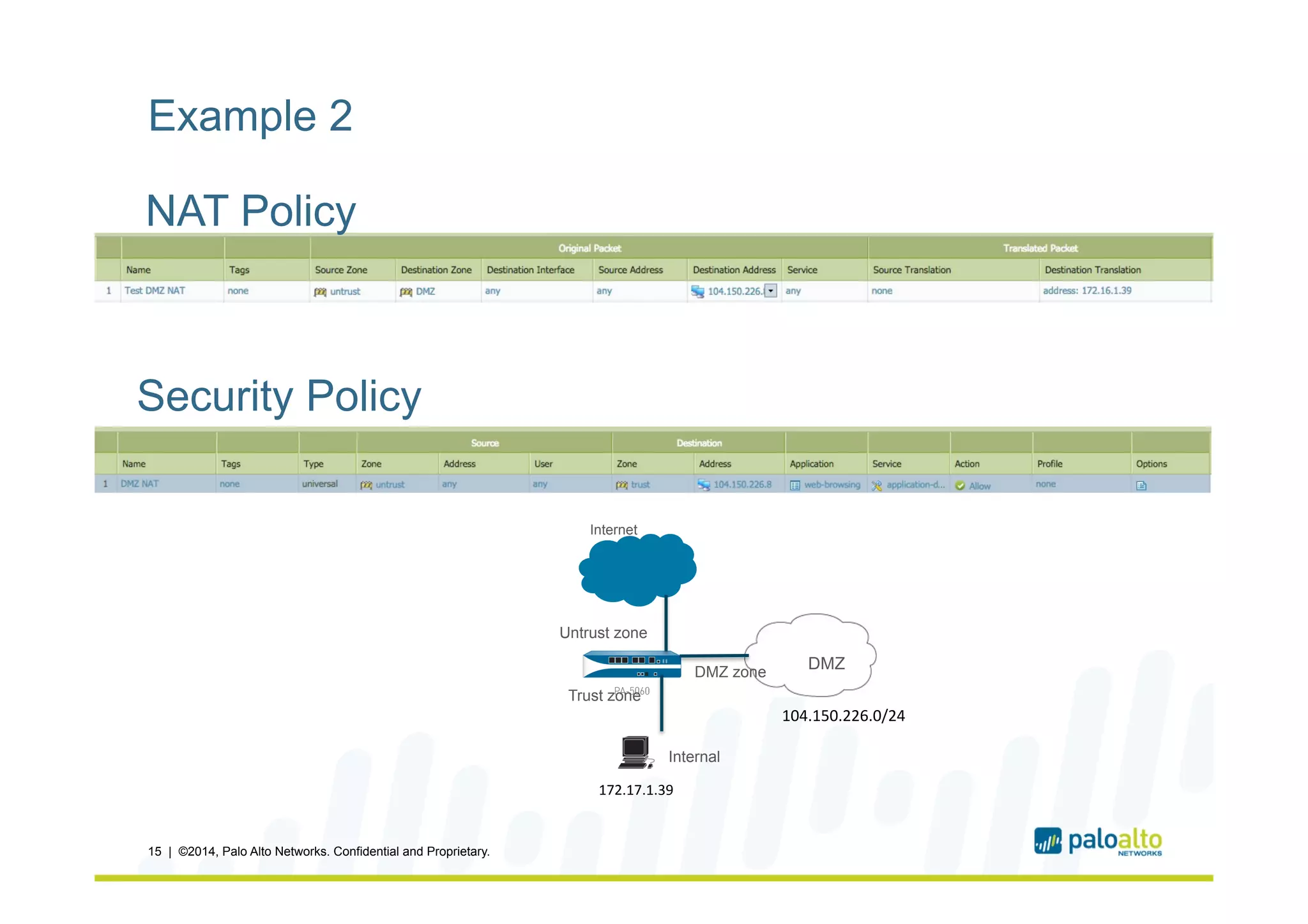
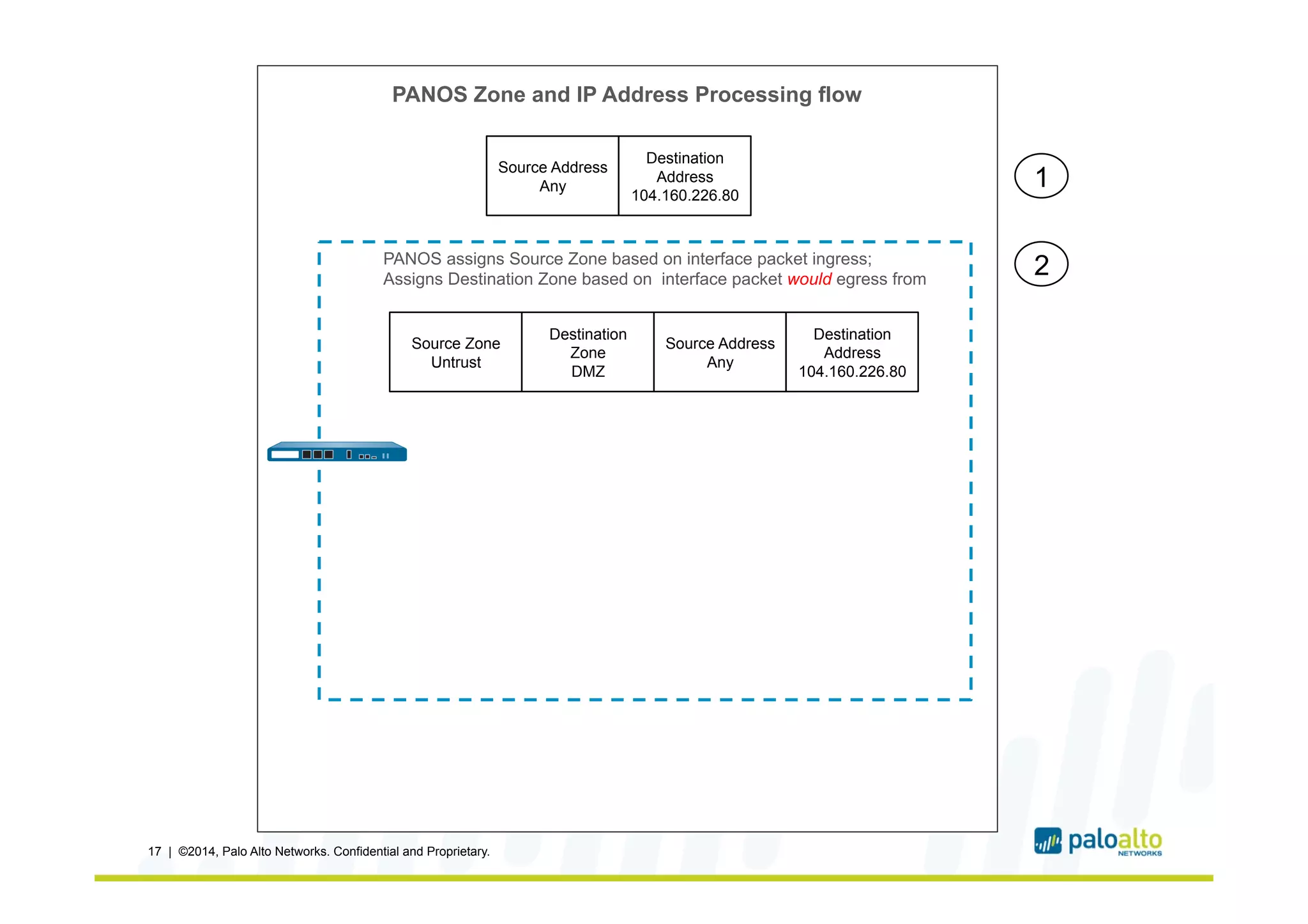
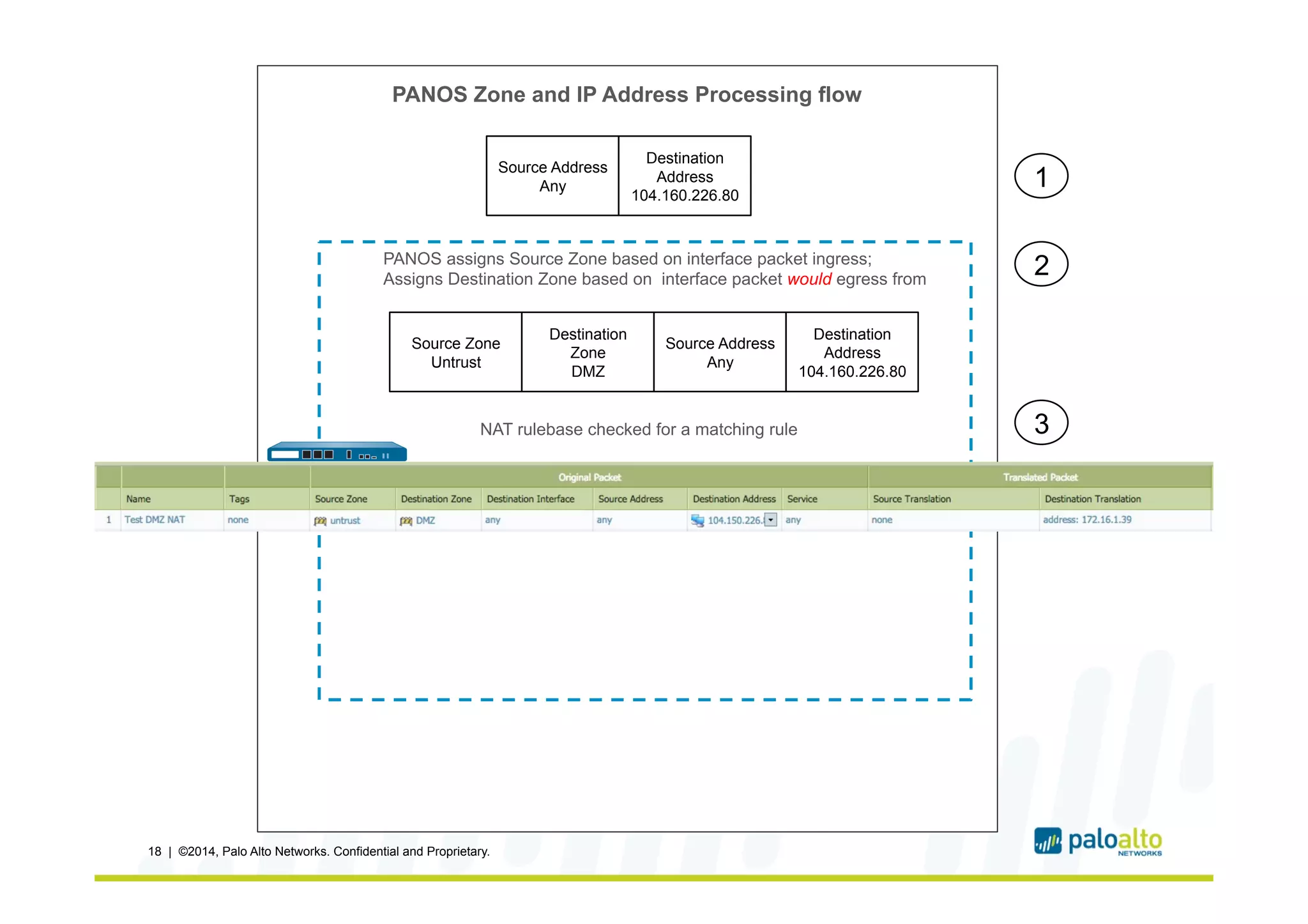
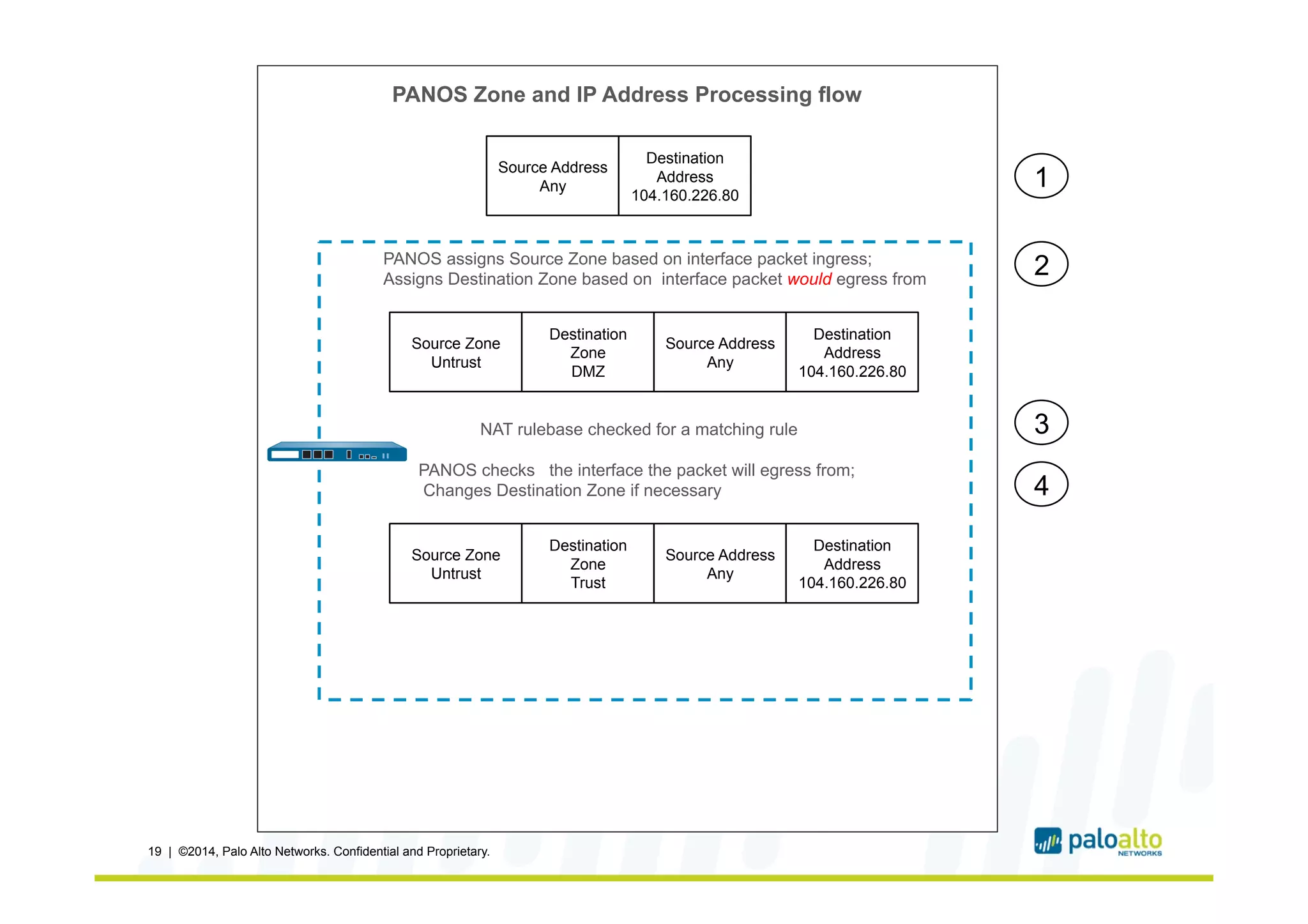
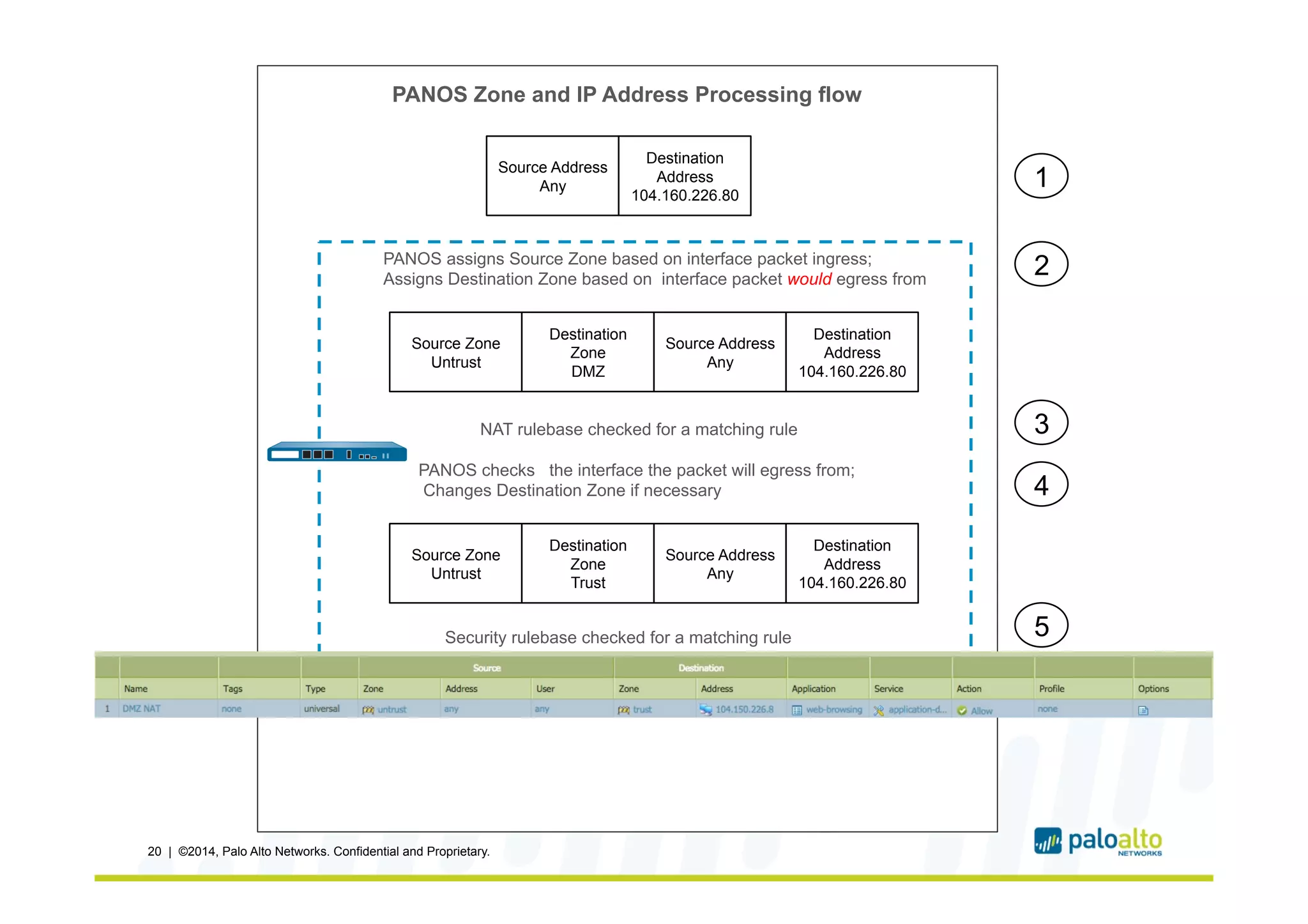
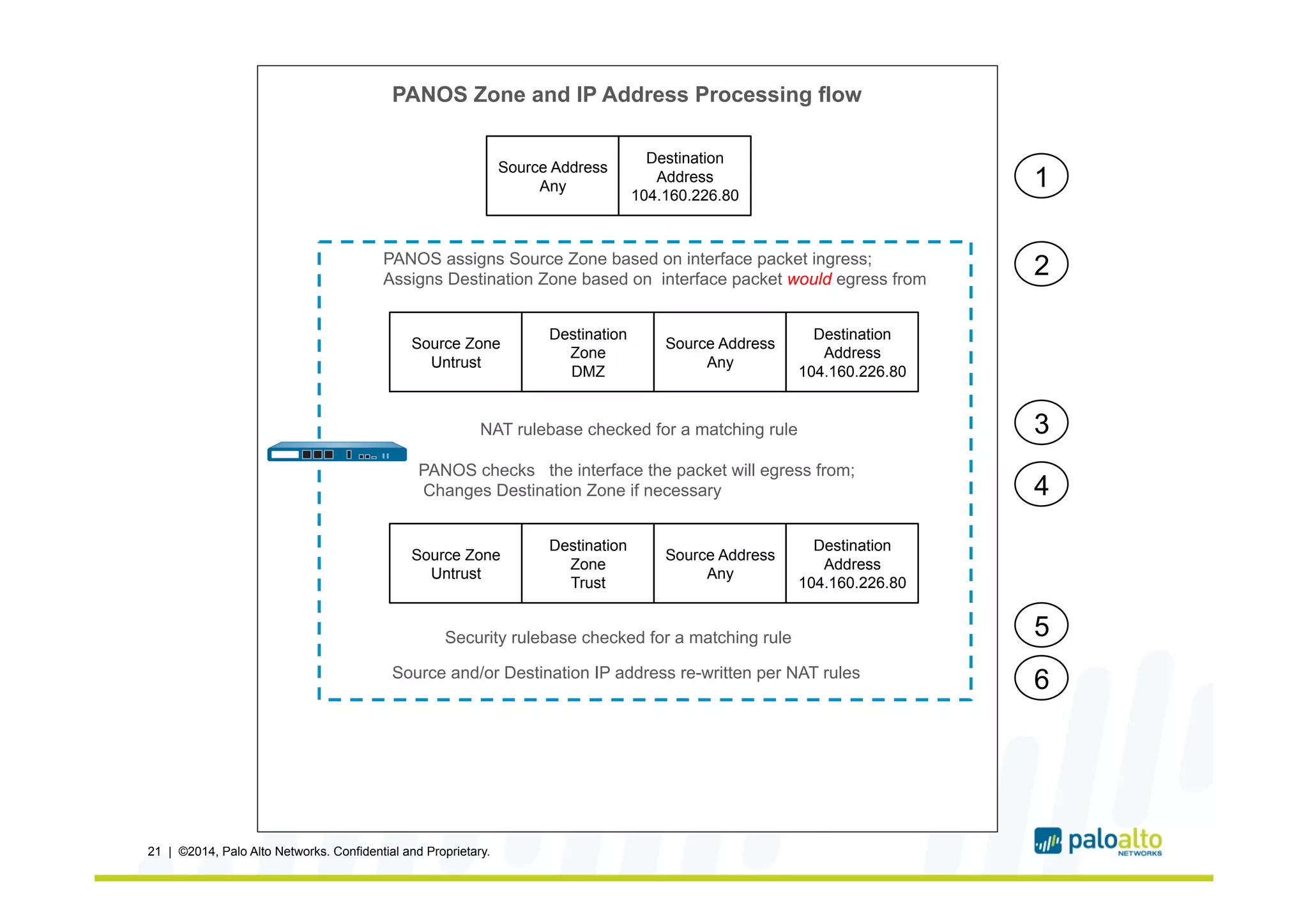
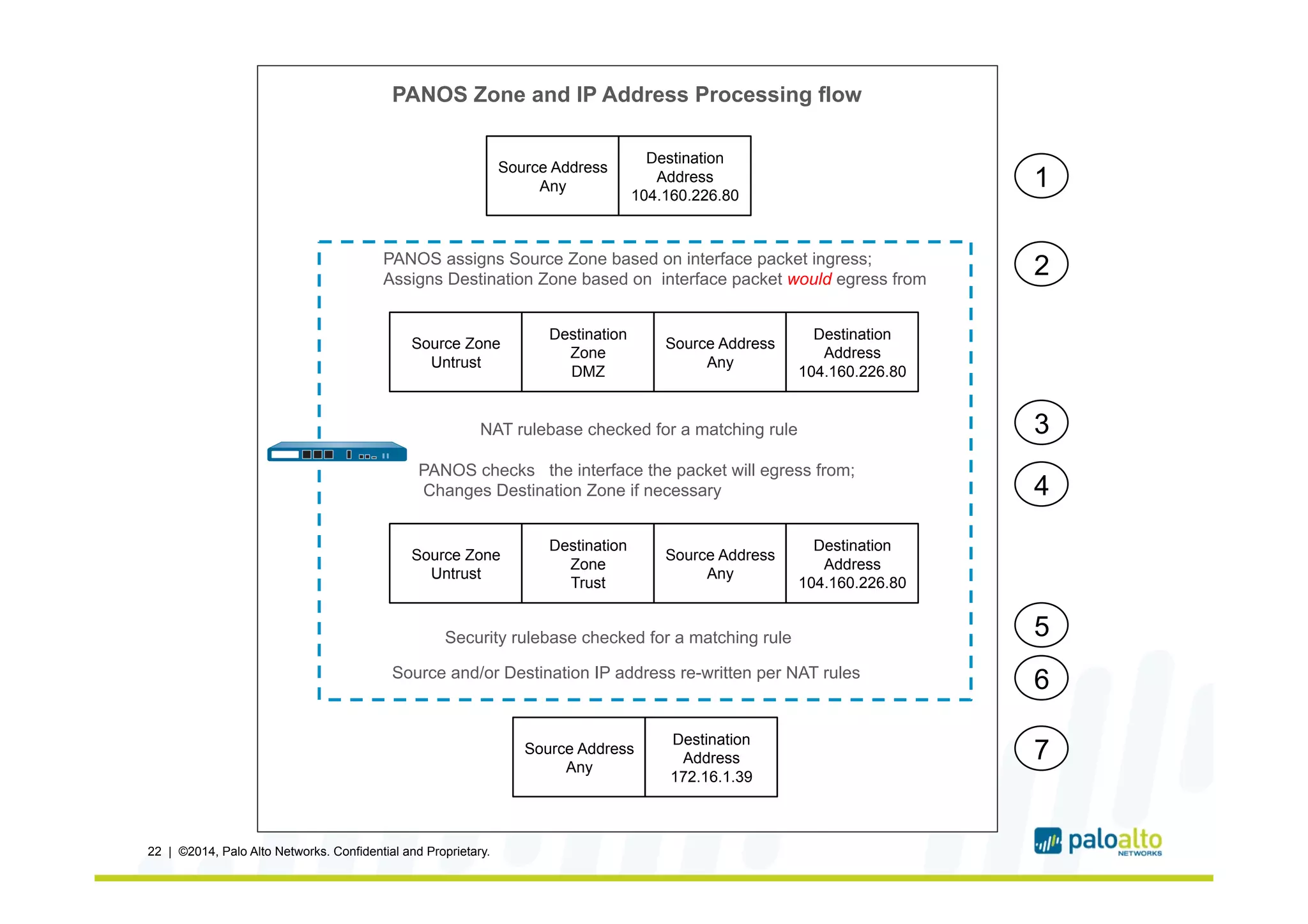
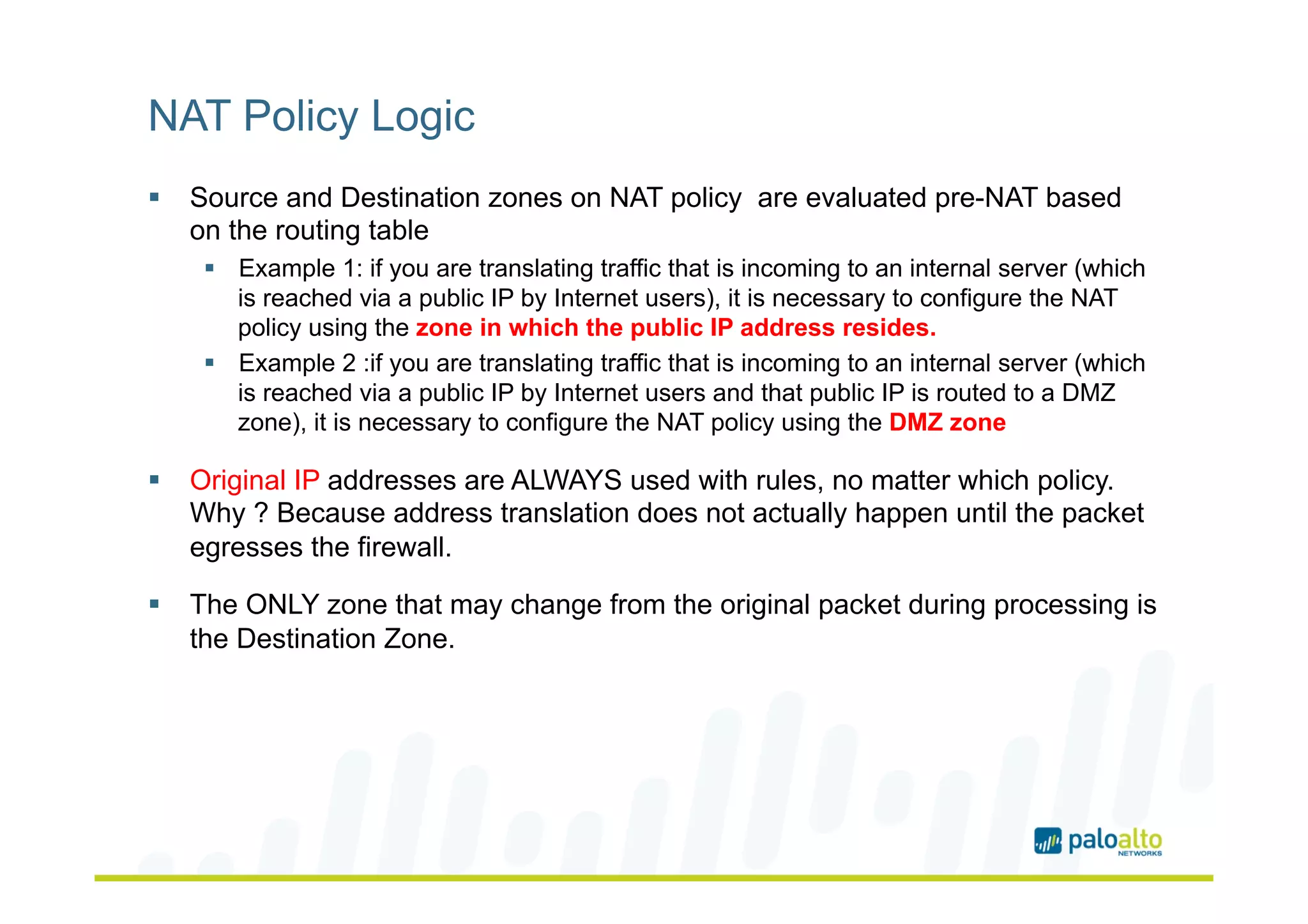
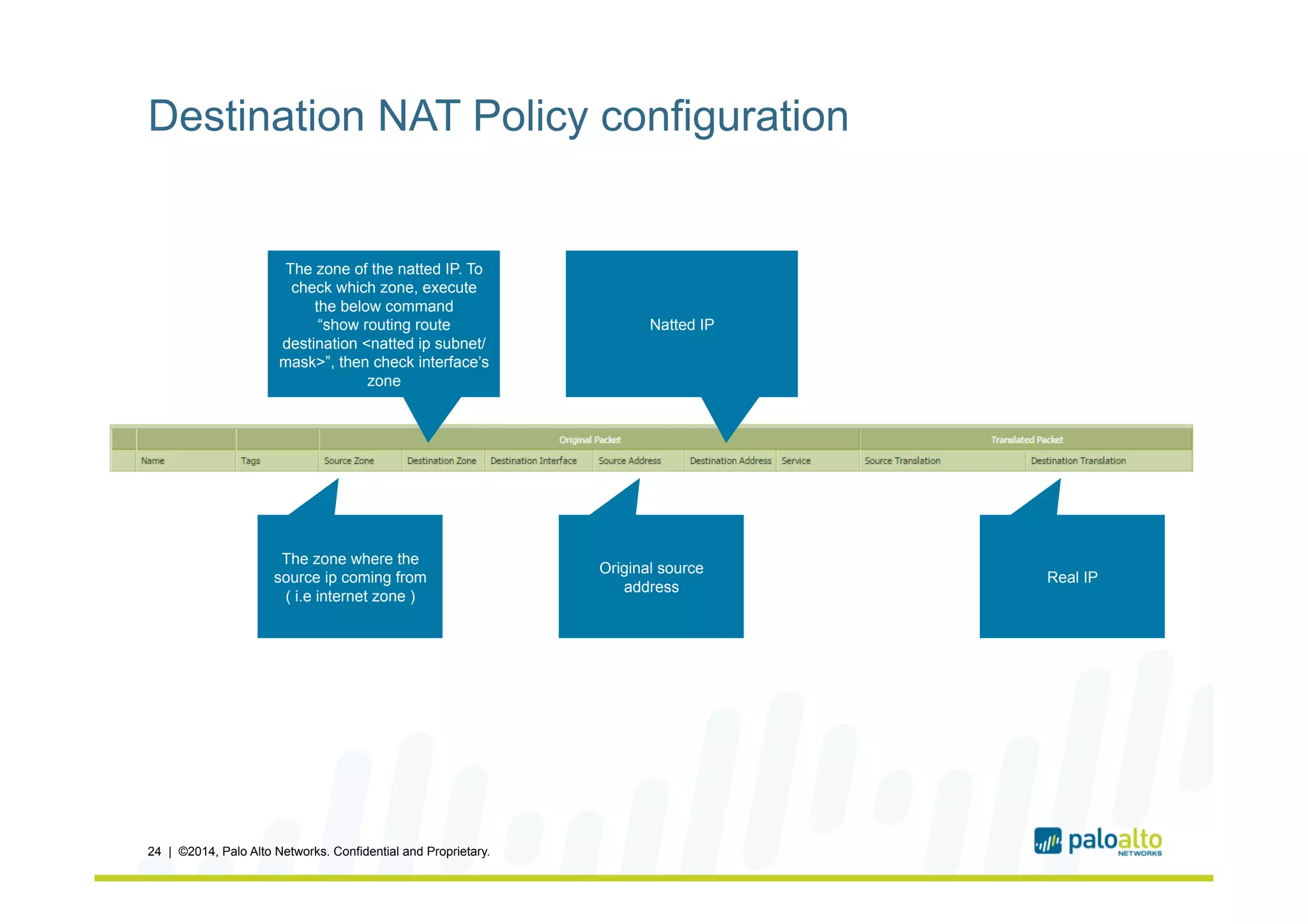
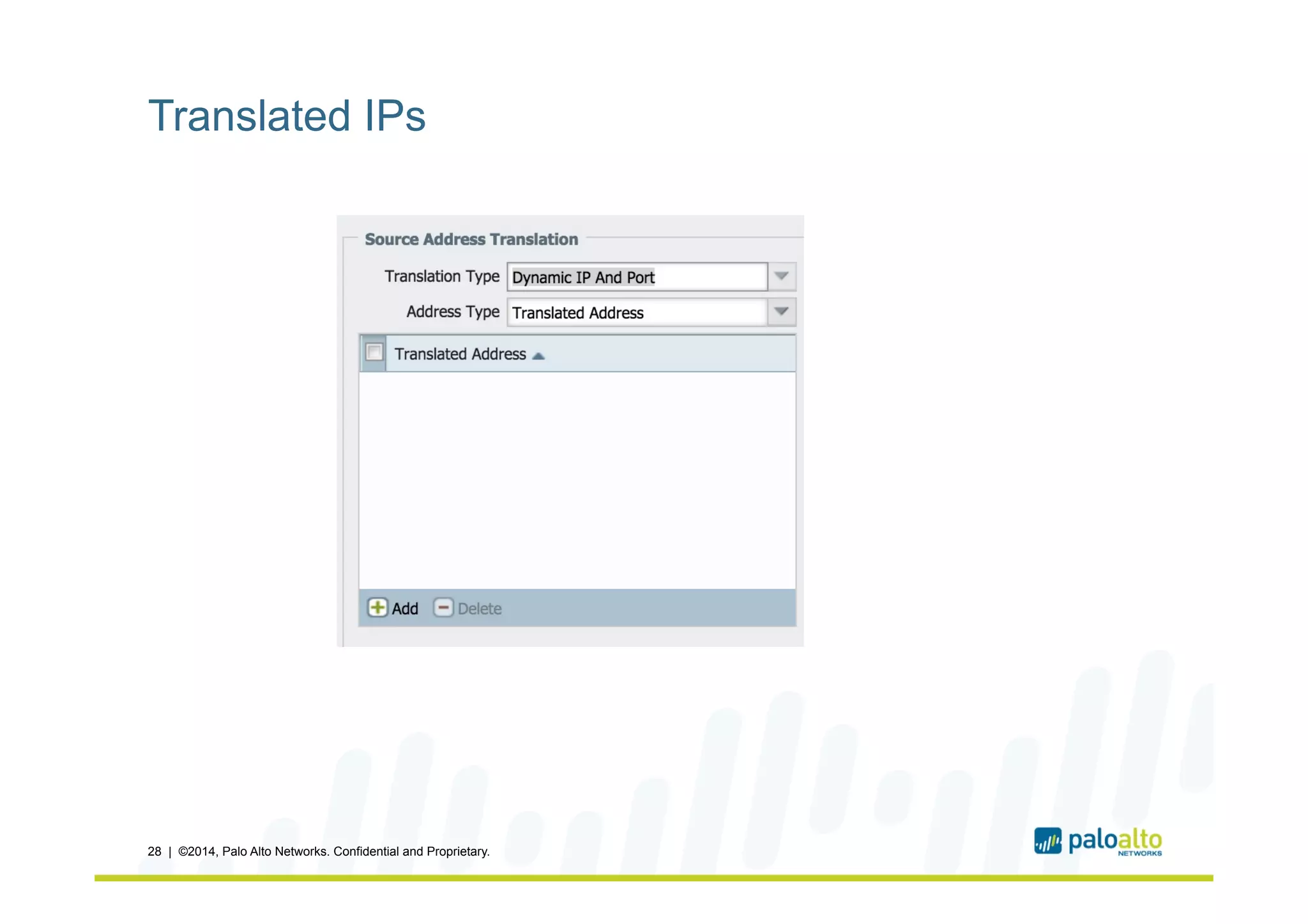
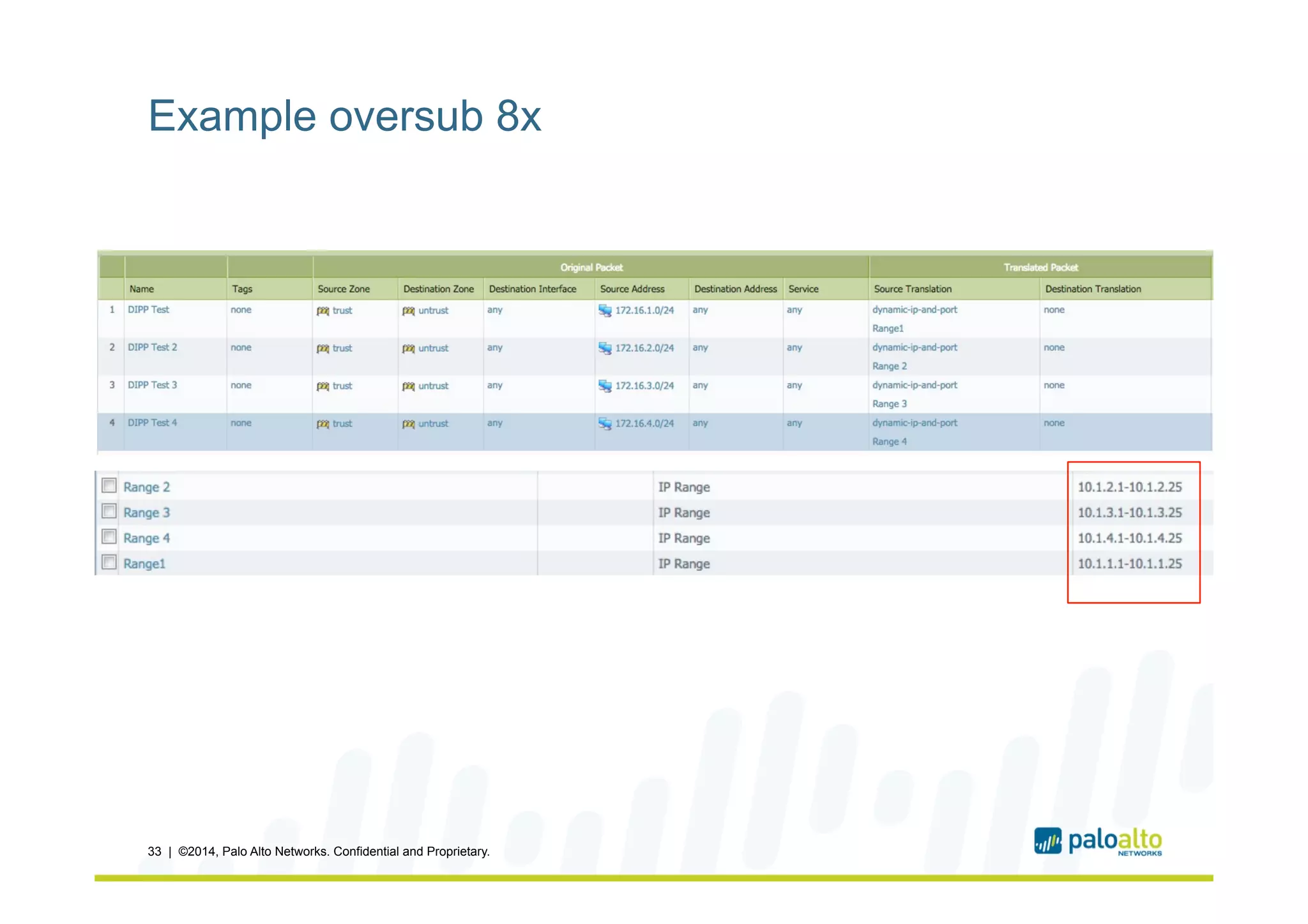
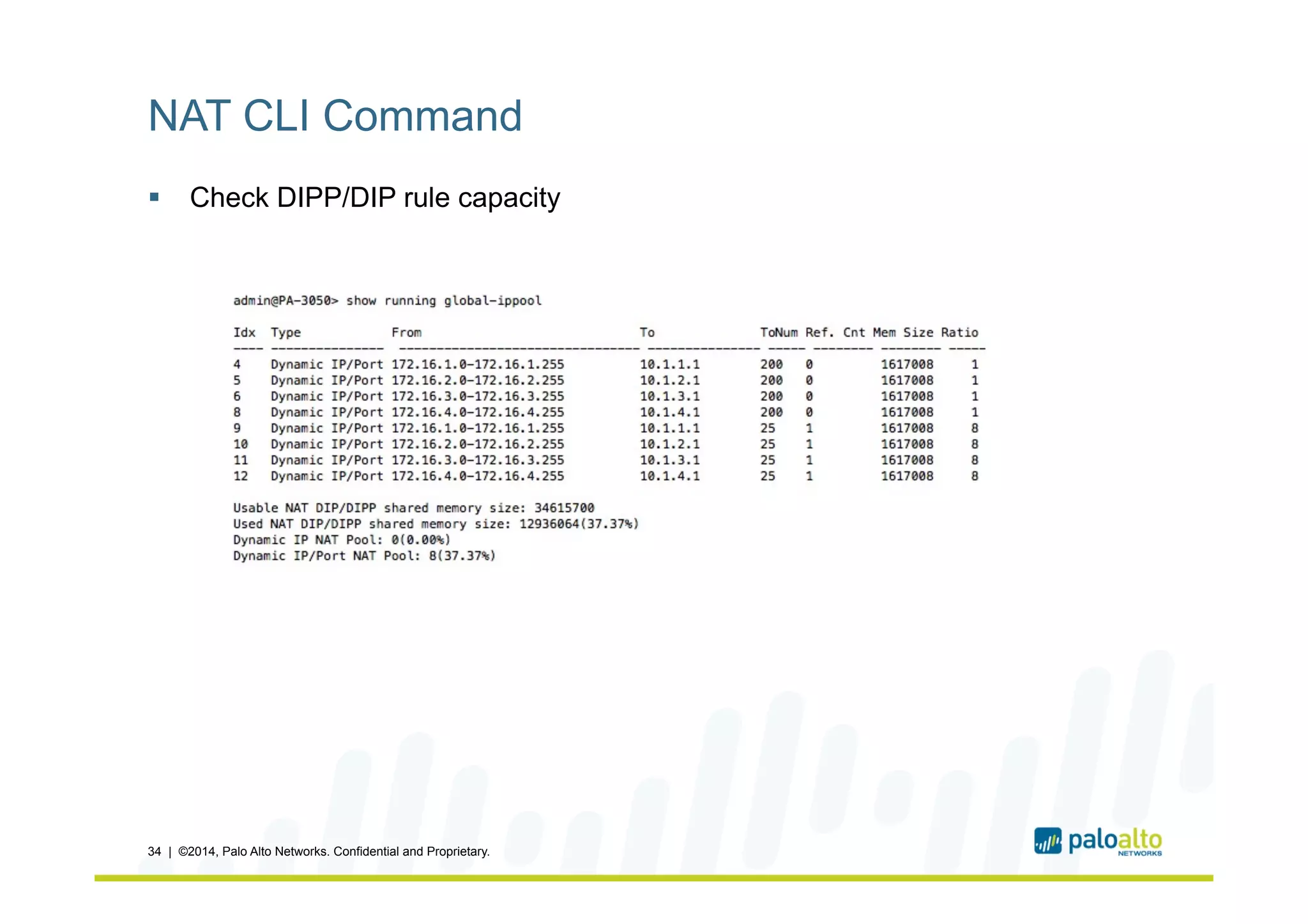
The document provides examples and explanations of network address translation (NAT) configurations on Palo Alto Networks next-generation firewalls. It shows how NAT policies work with security policies to translate source and destination IP addresses and apply firewall rules. The first example demonstrates static destination NAT to map any internal address to a single public address. The second example uses source NAT to map a DMZ subnet to an internal address. Flow charts illustrate how the firewall evaluates zones, NAT rules, security rules and applies address translations at each step.