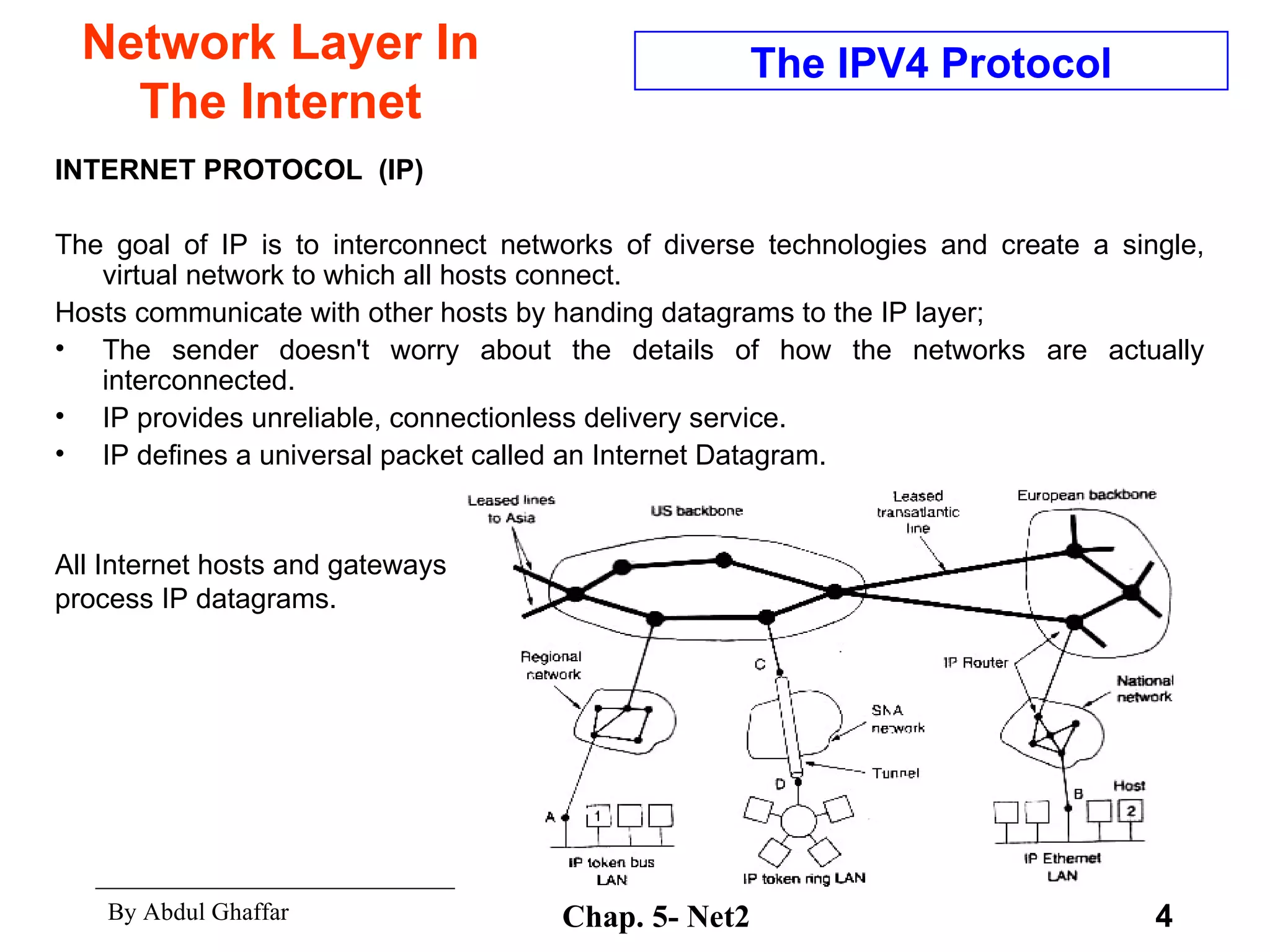
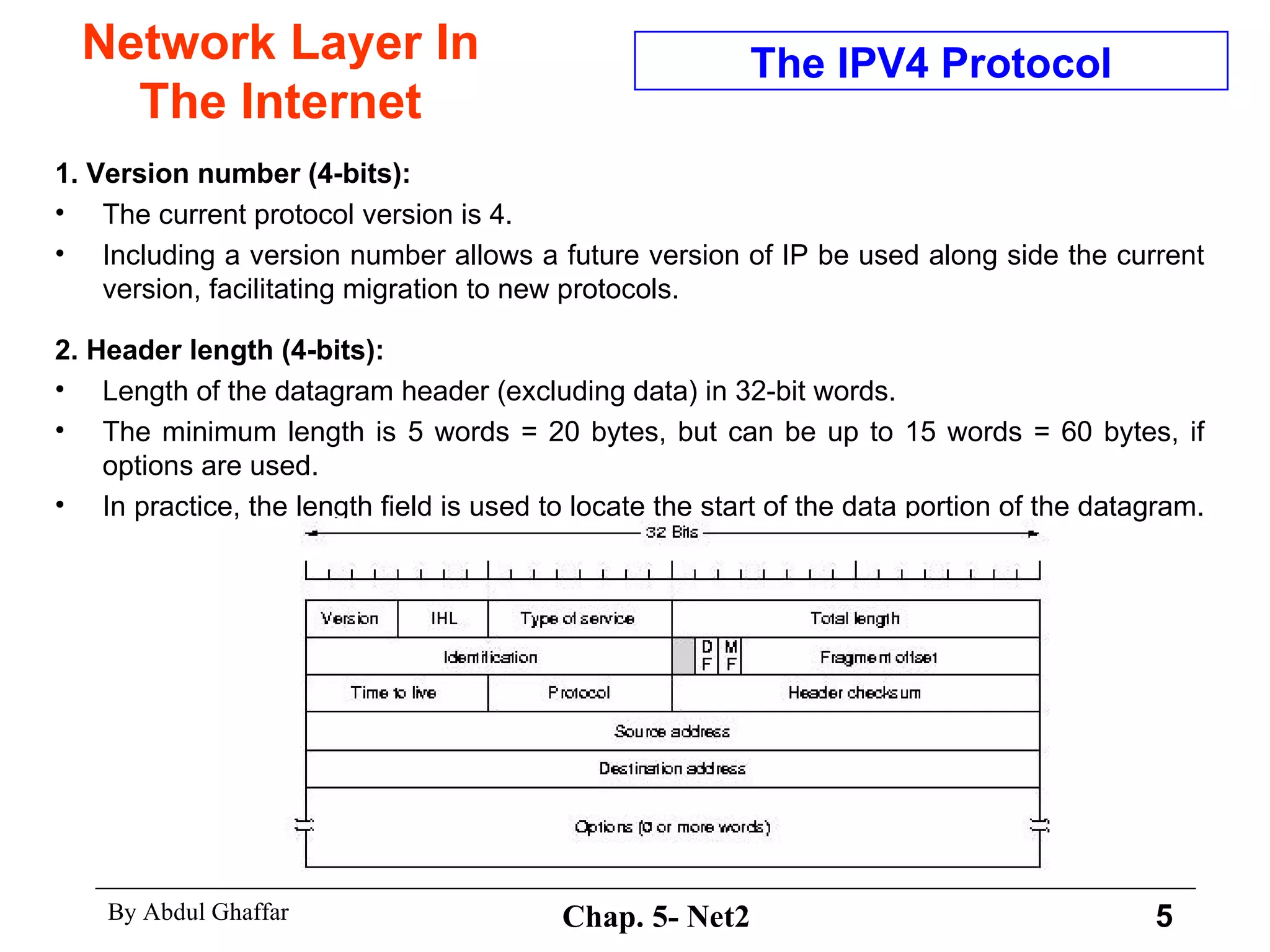
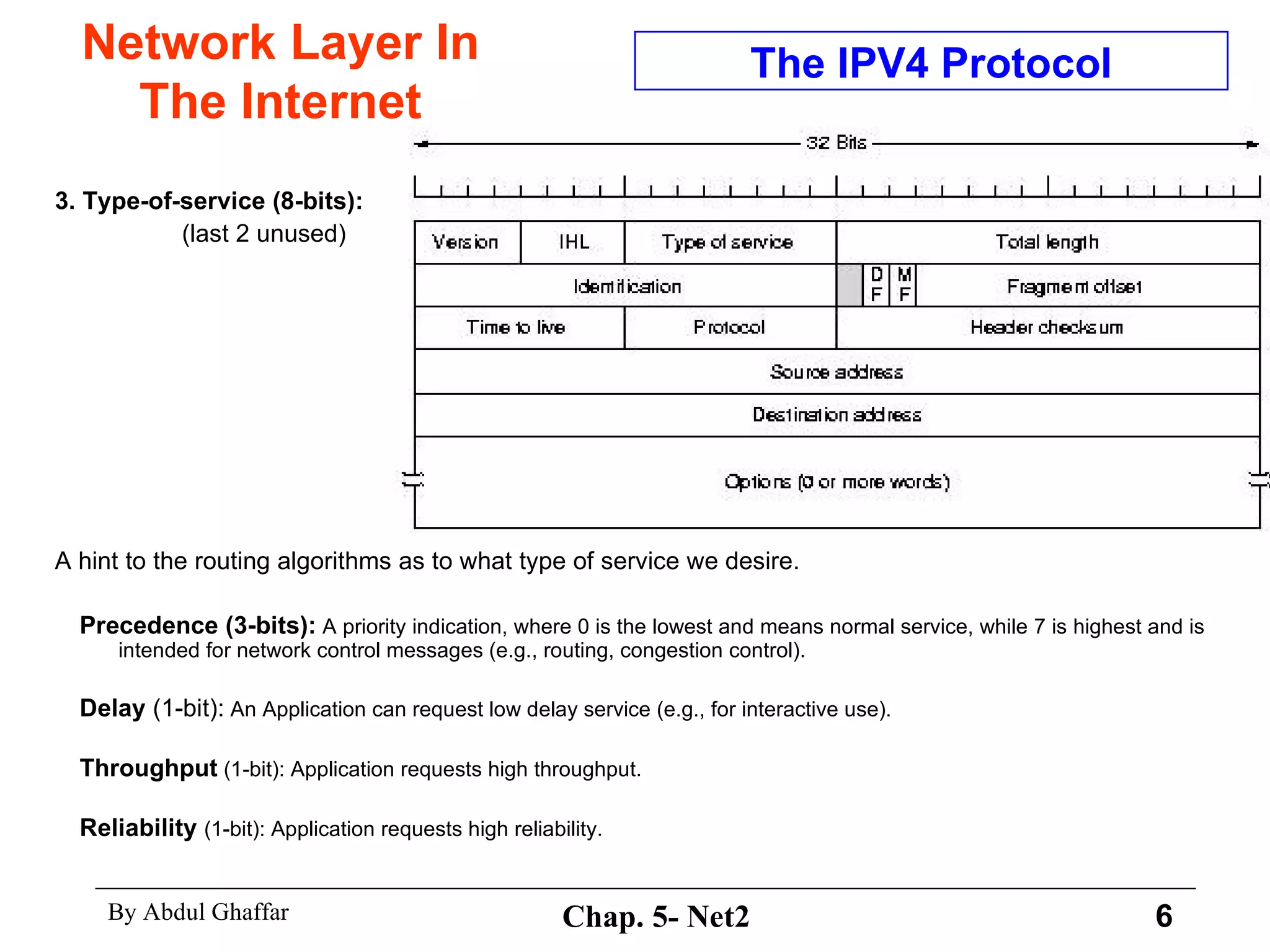
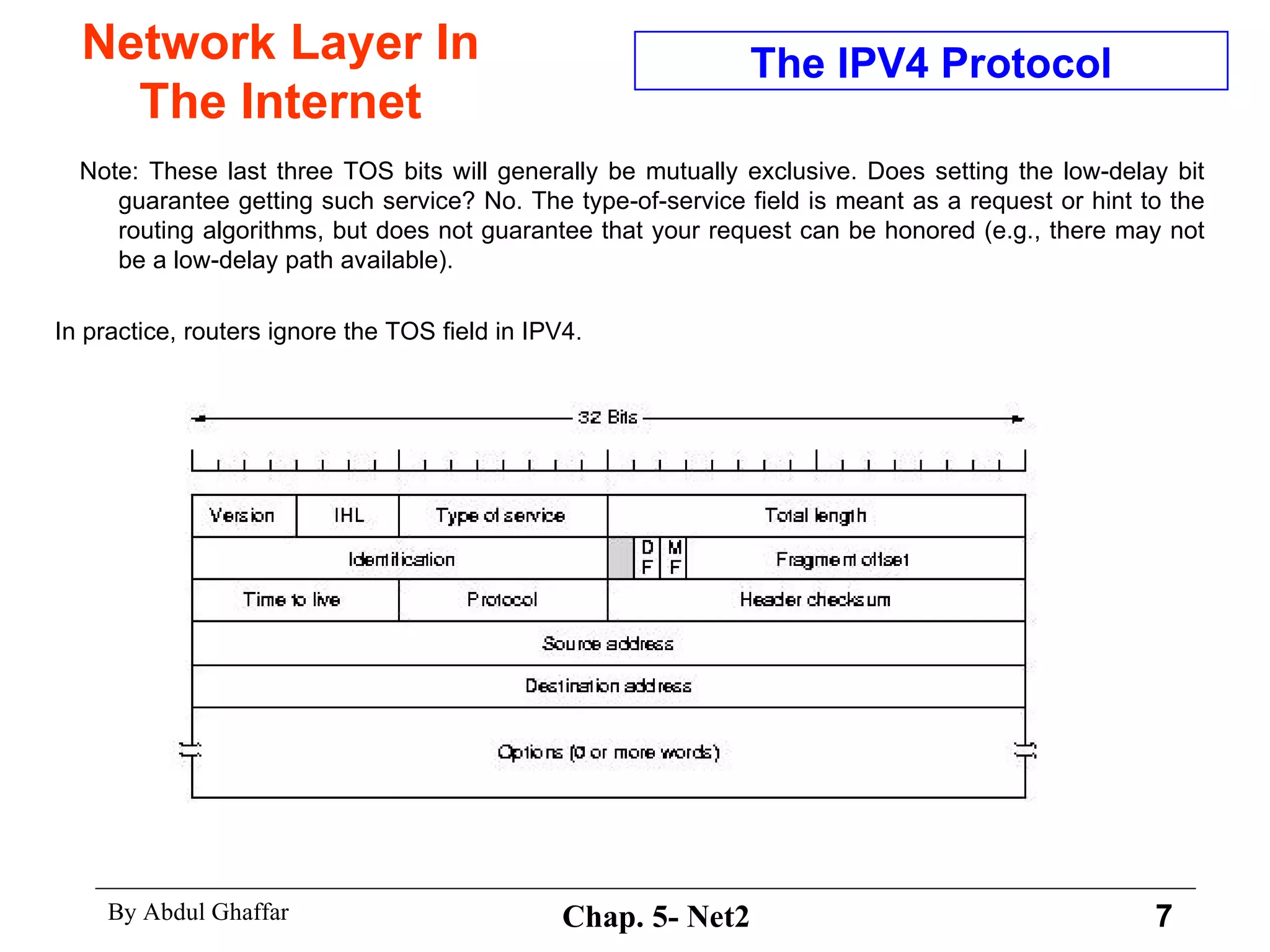
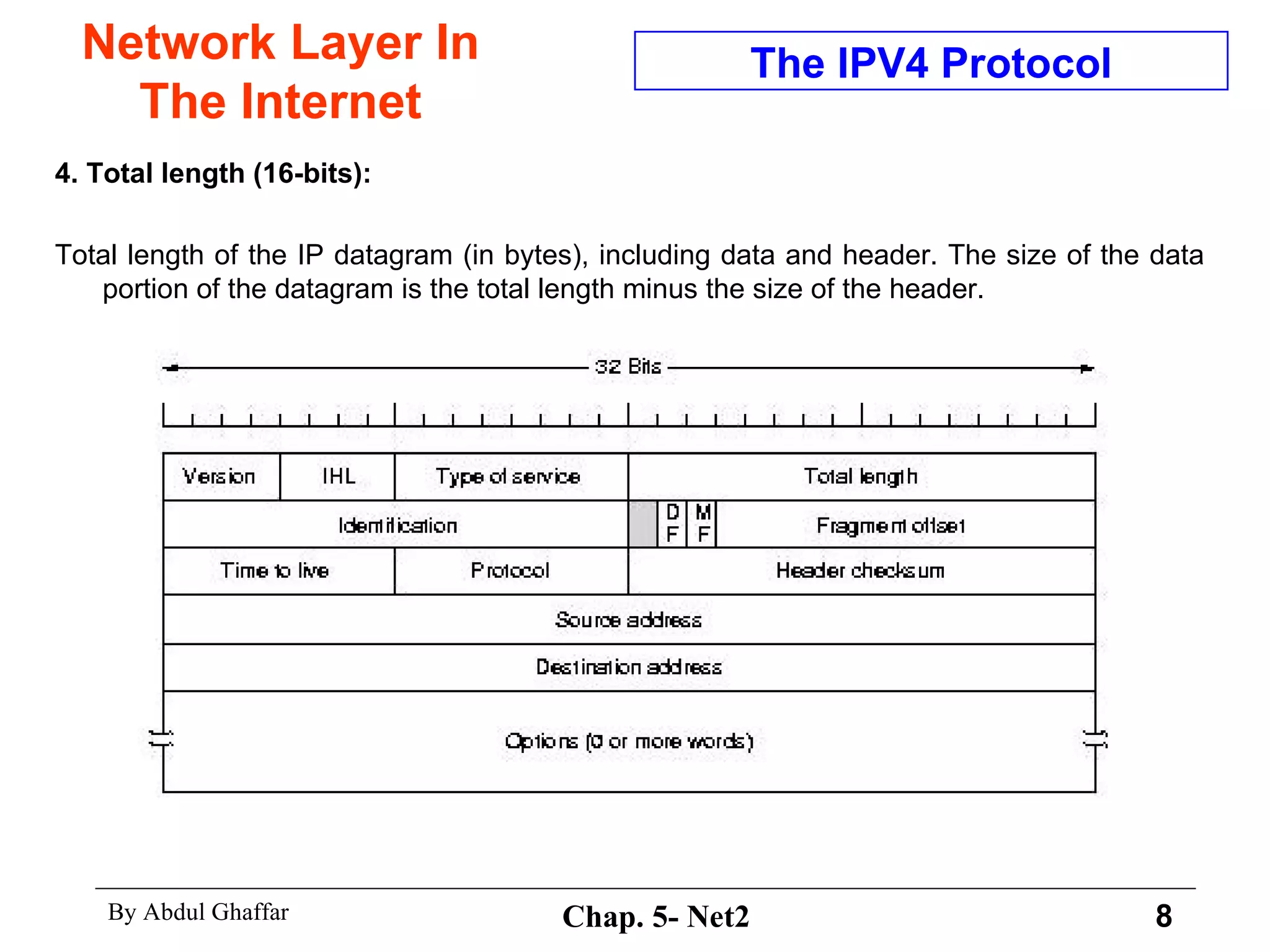
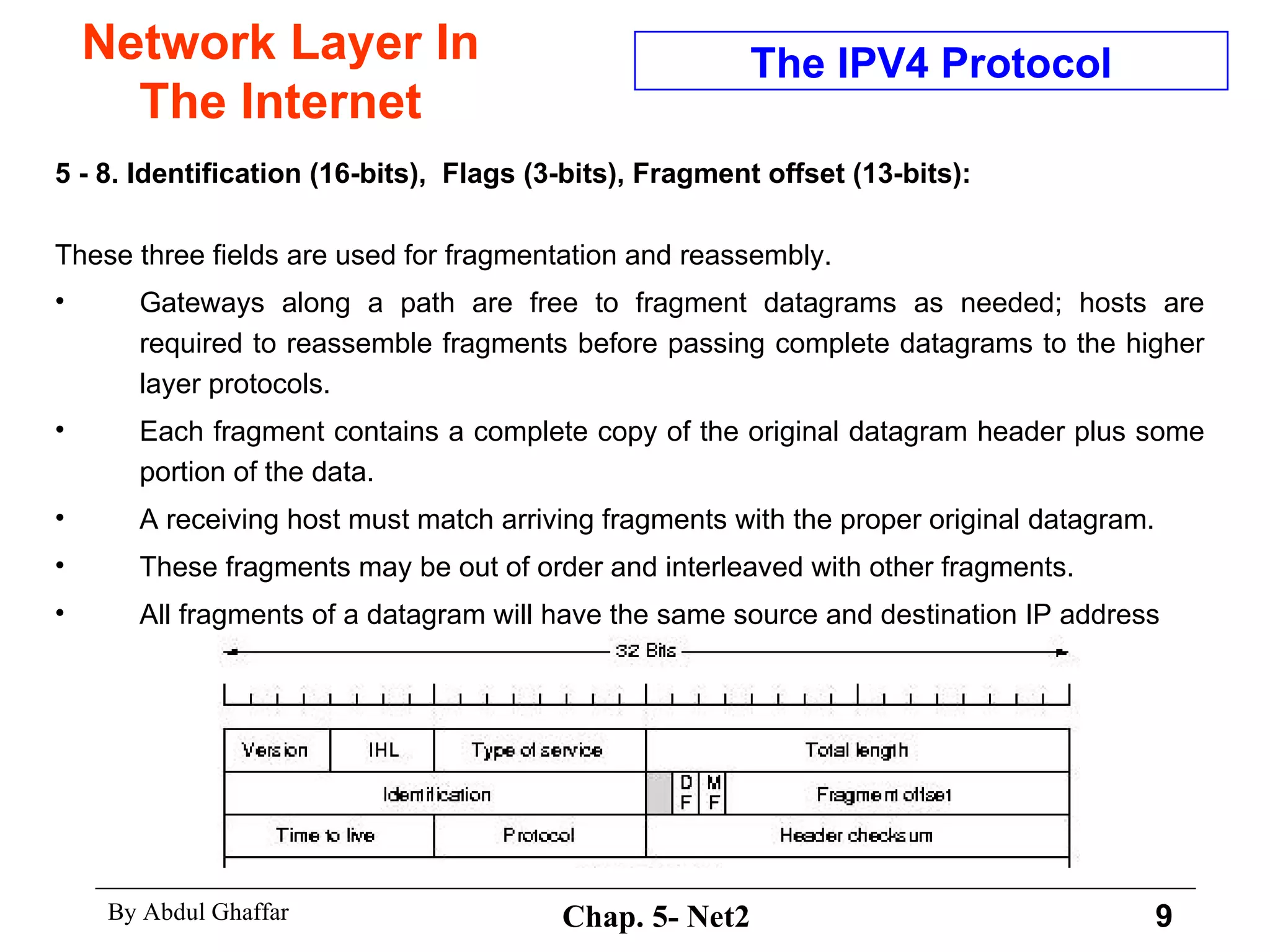
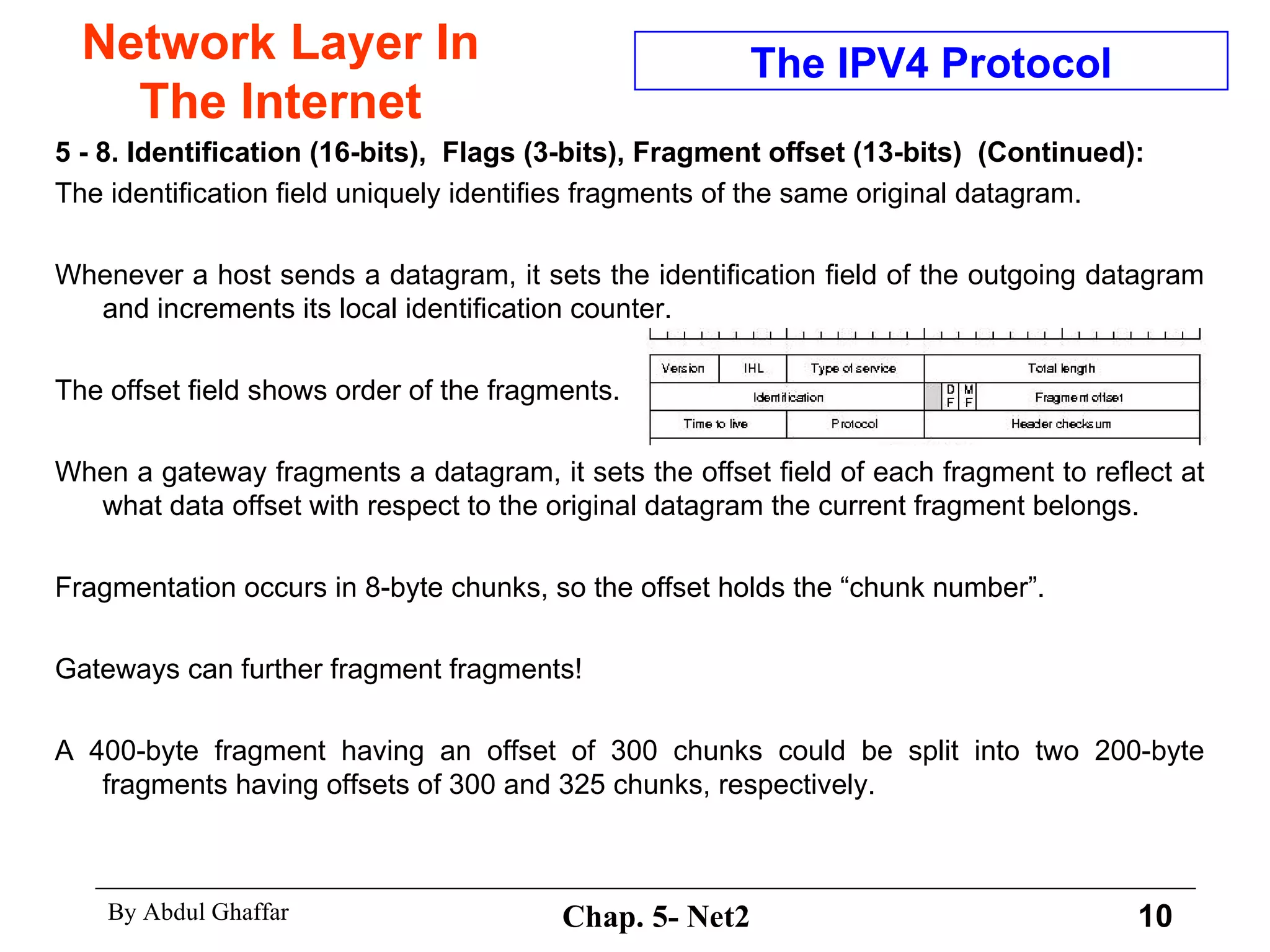
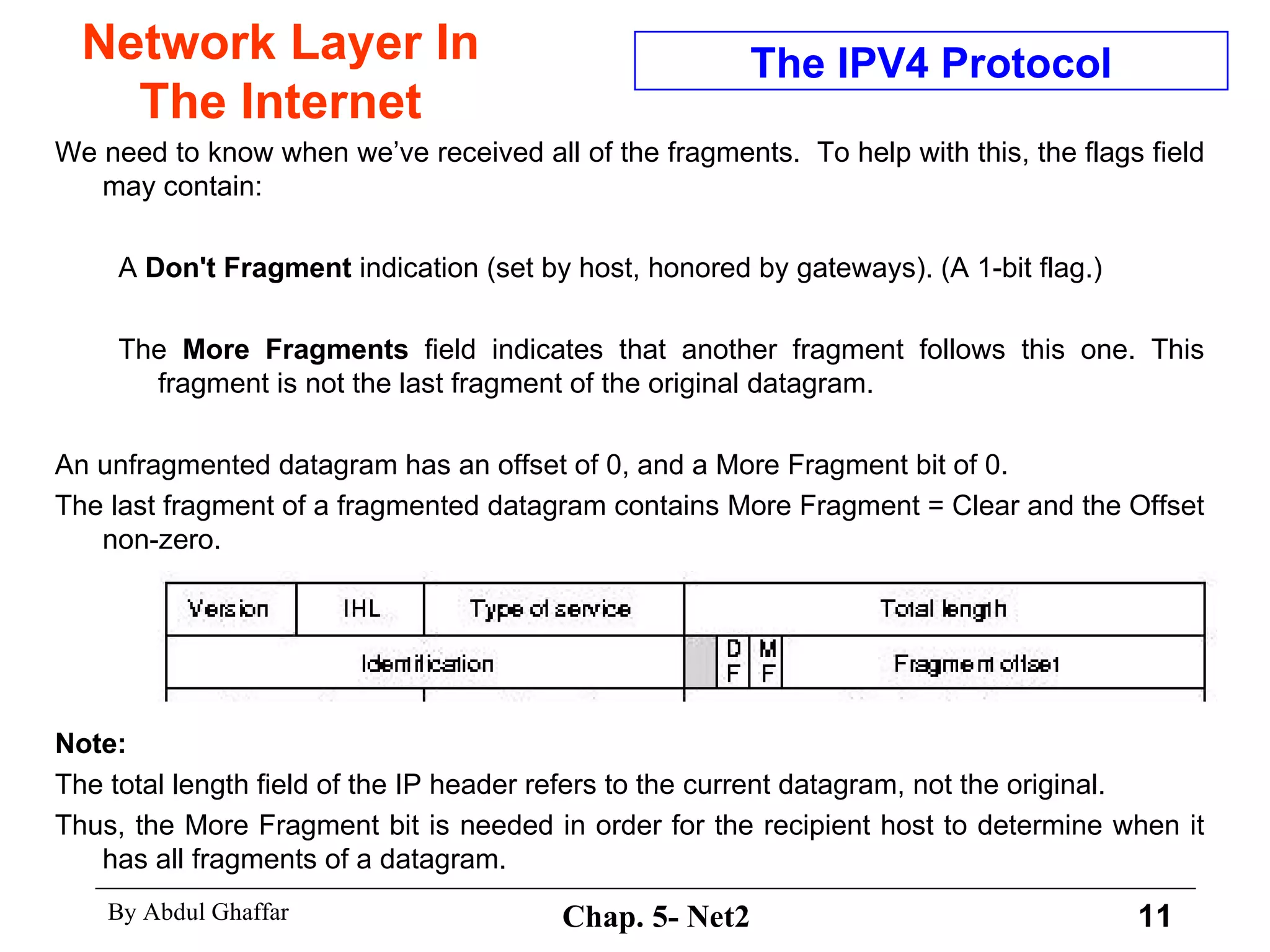
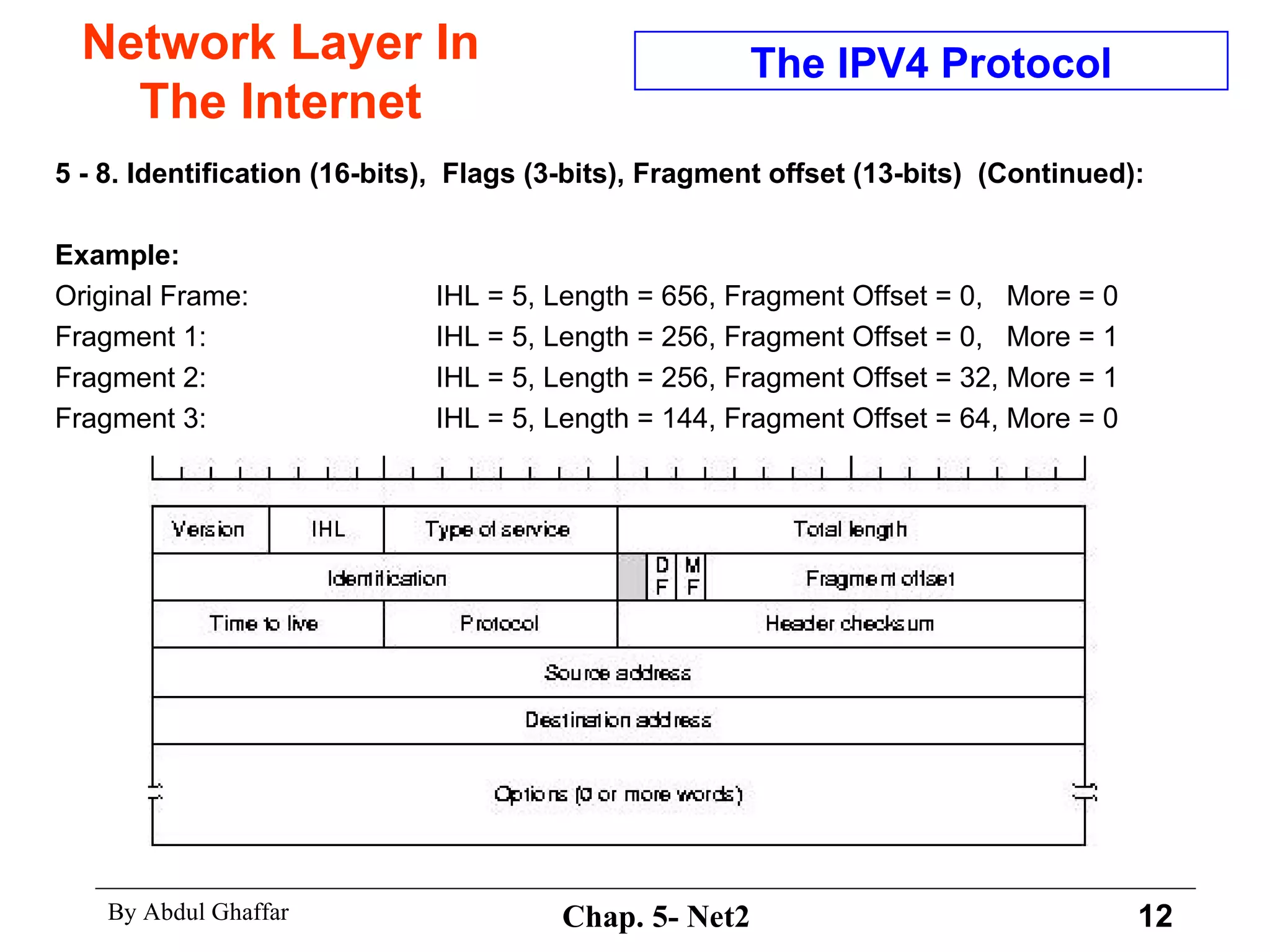
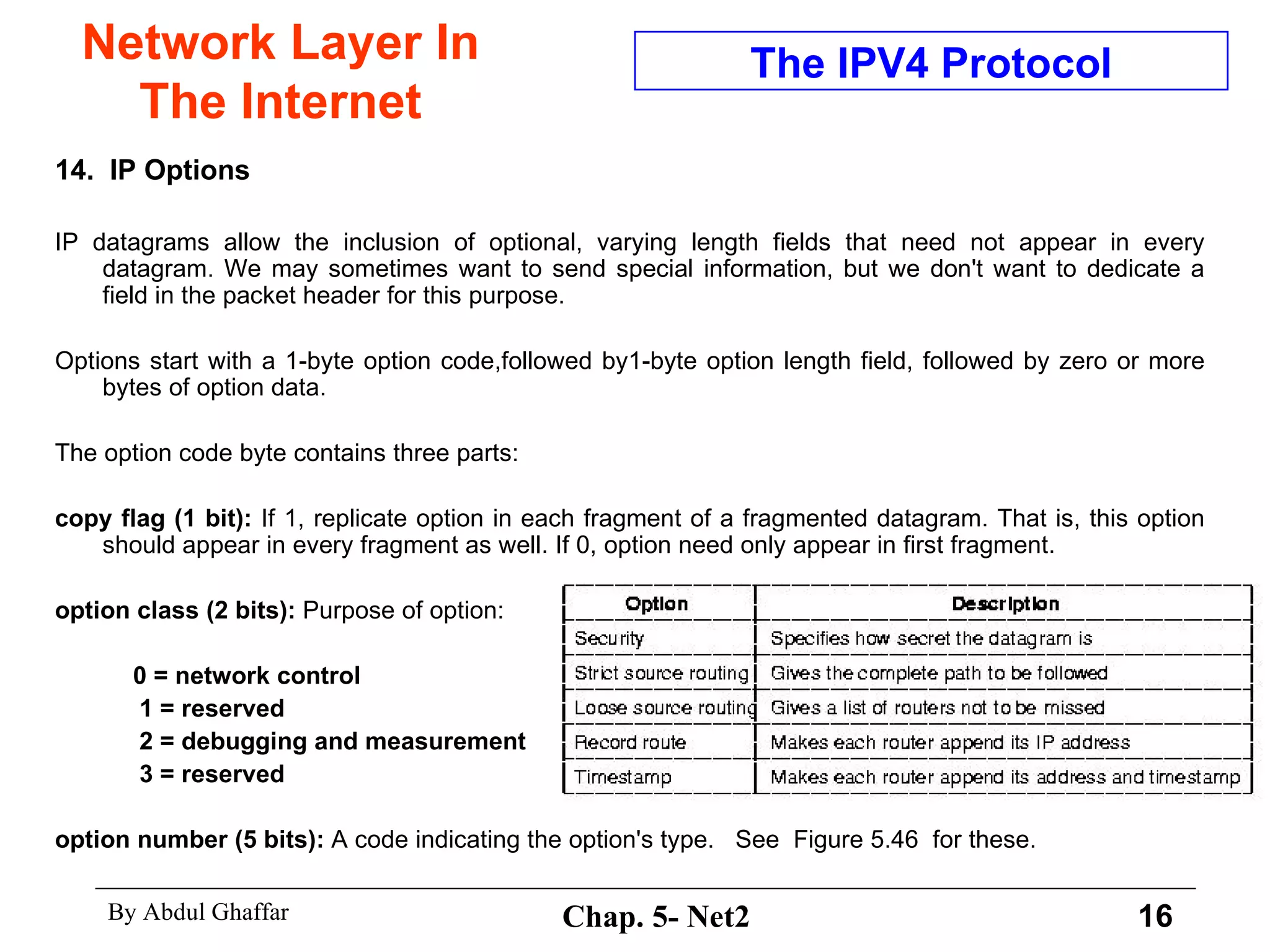
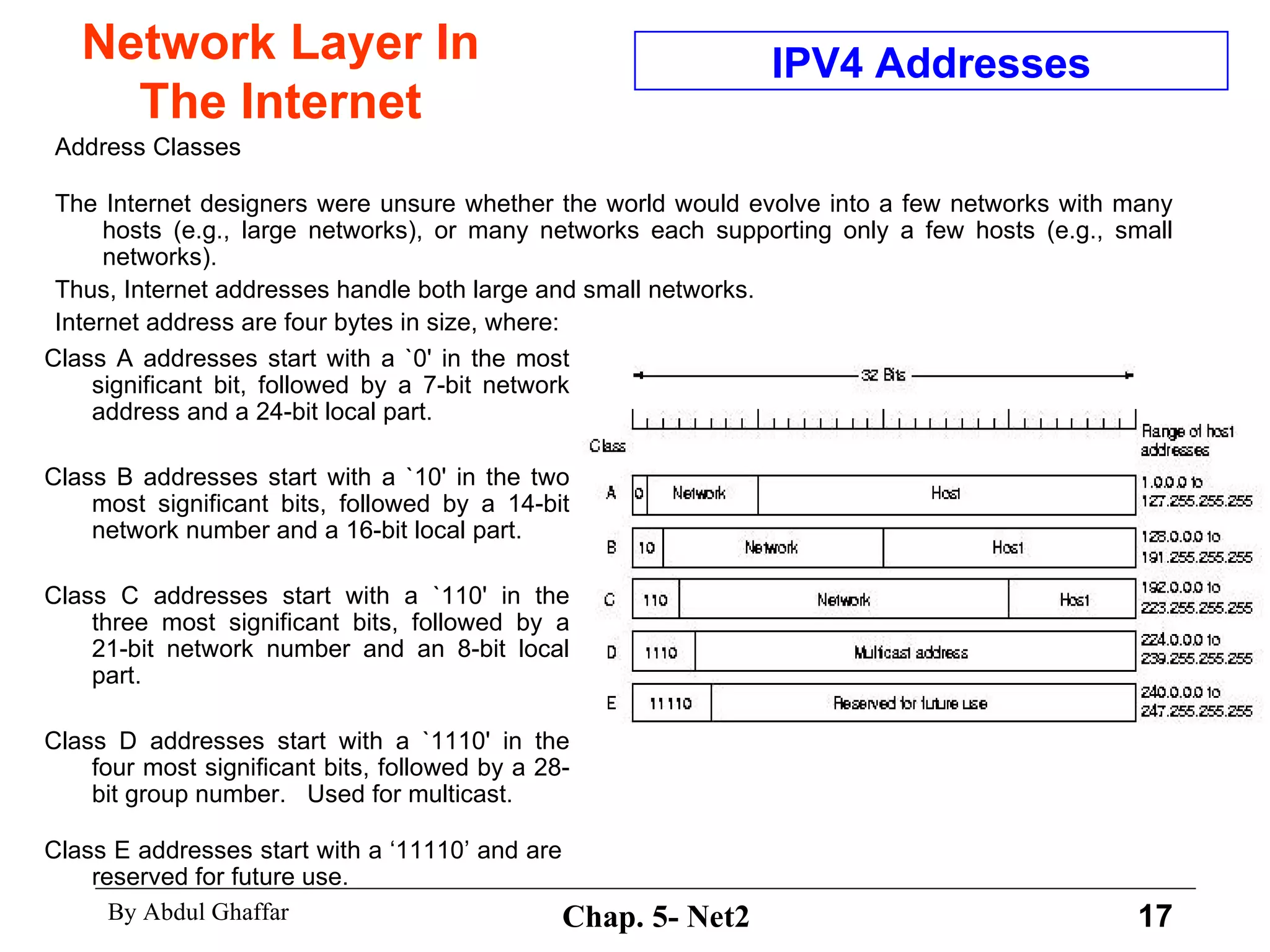
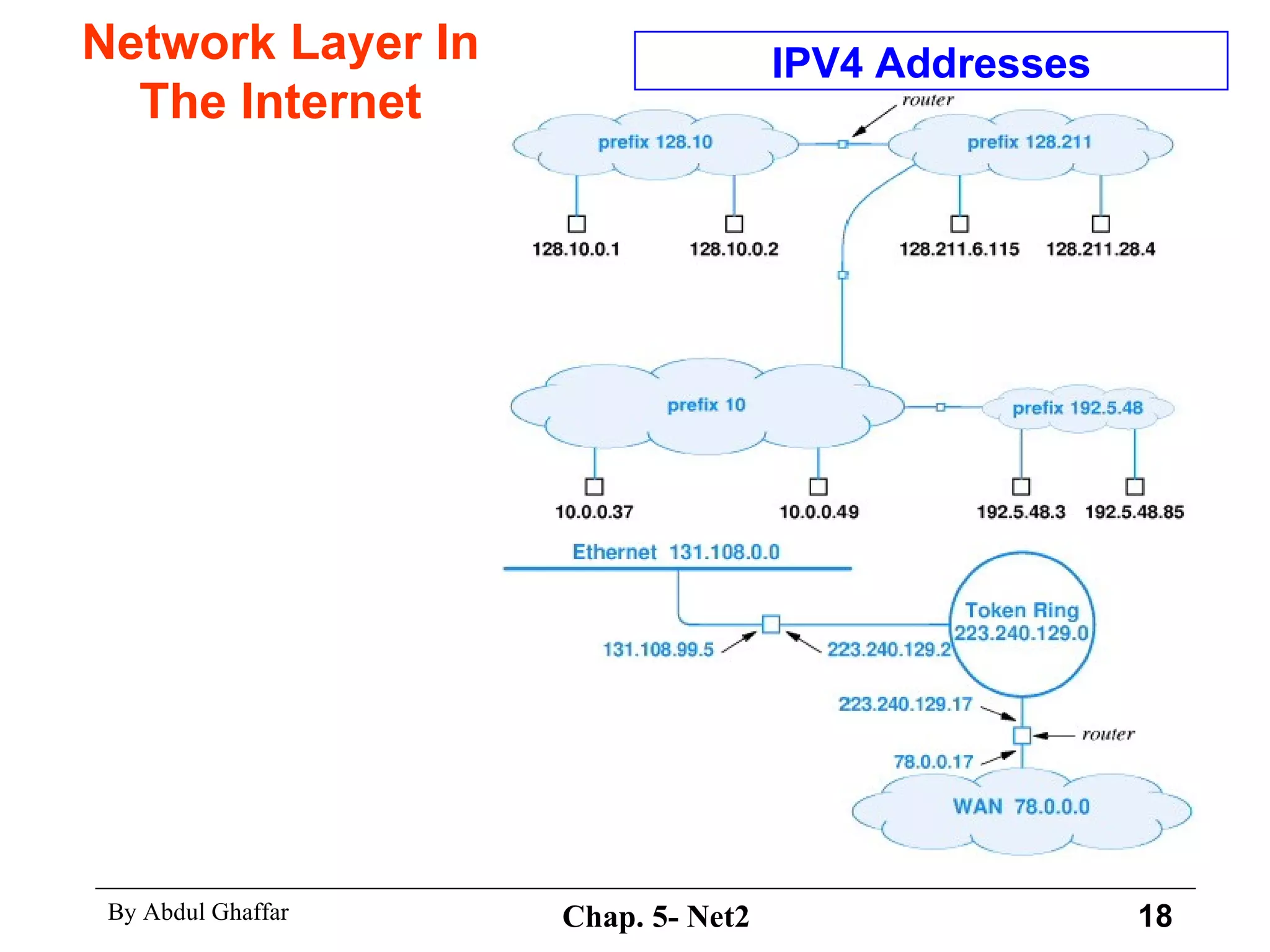
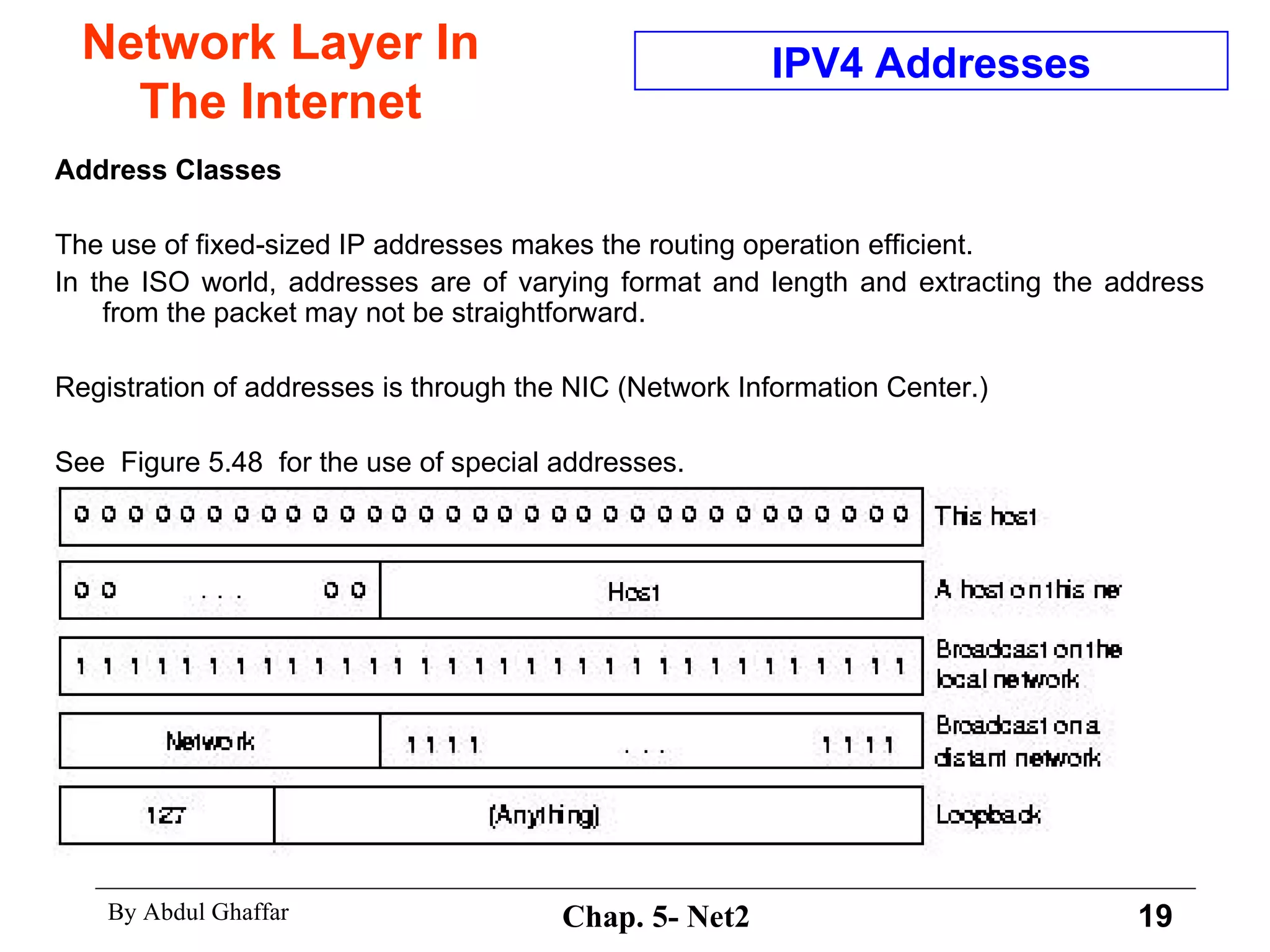
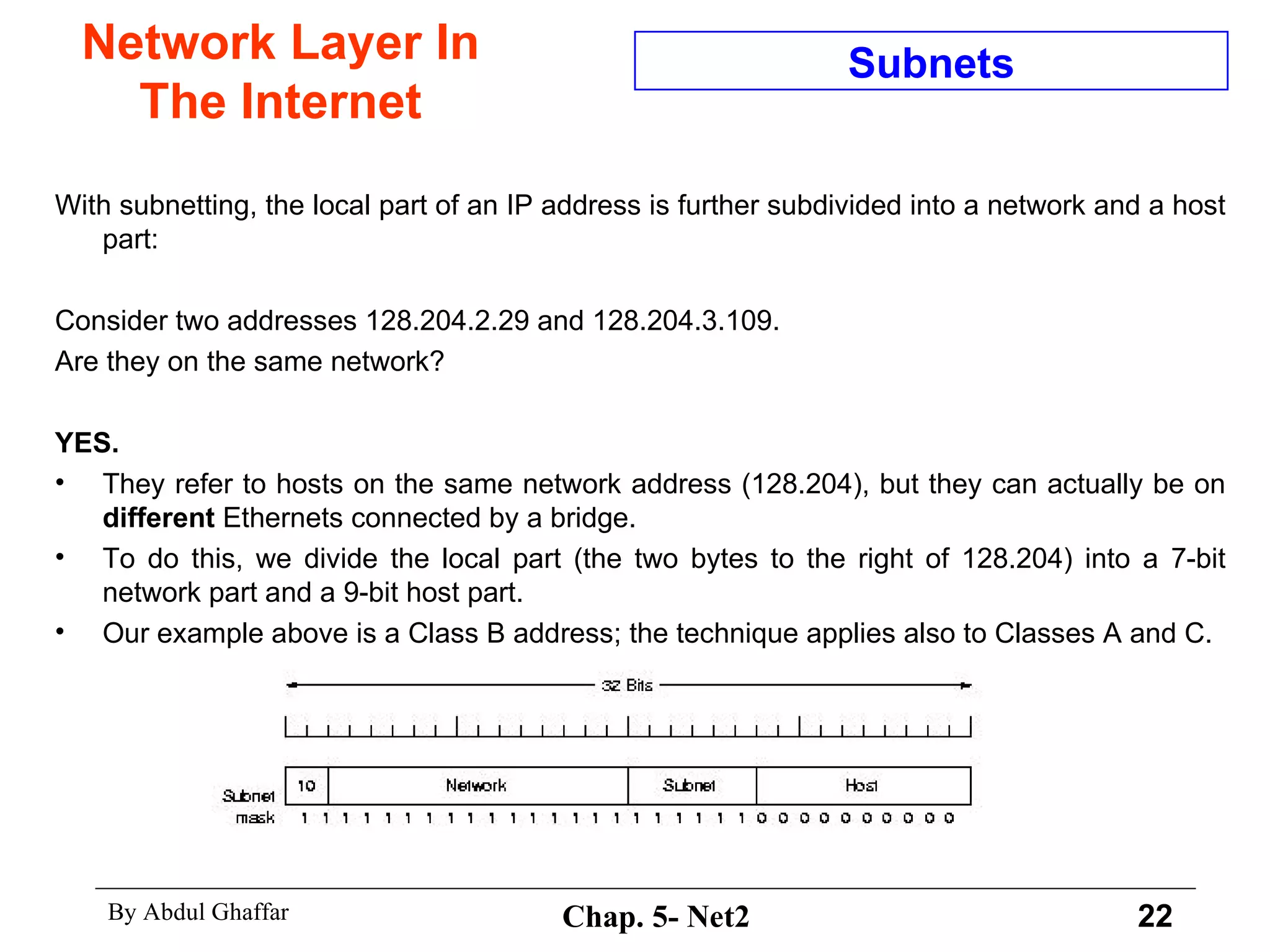
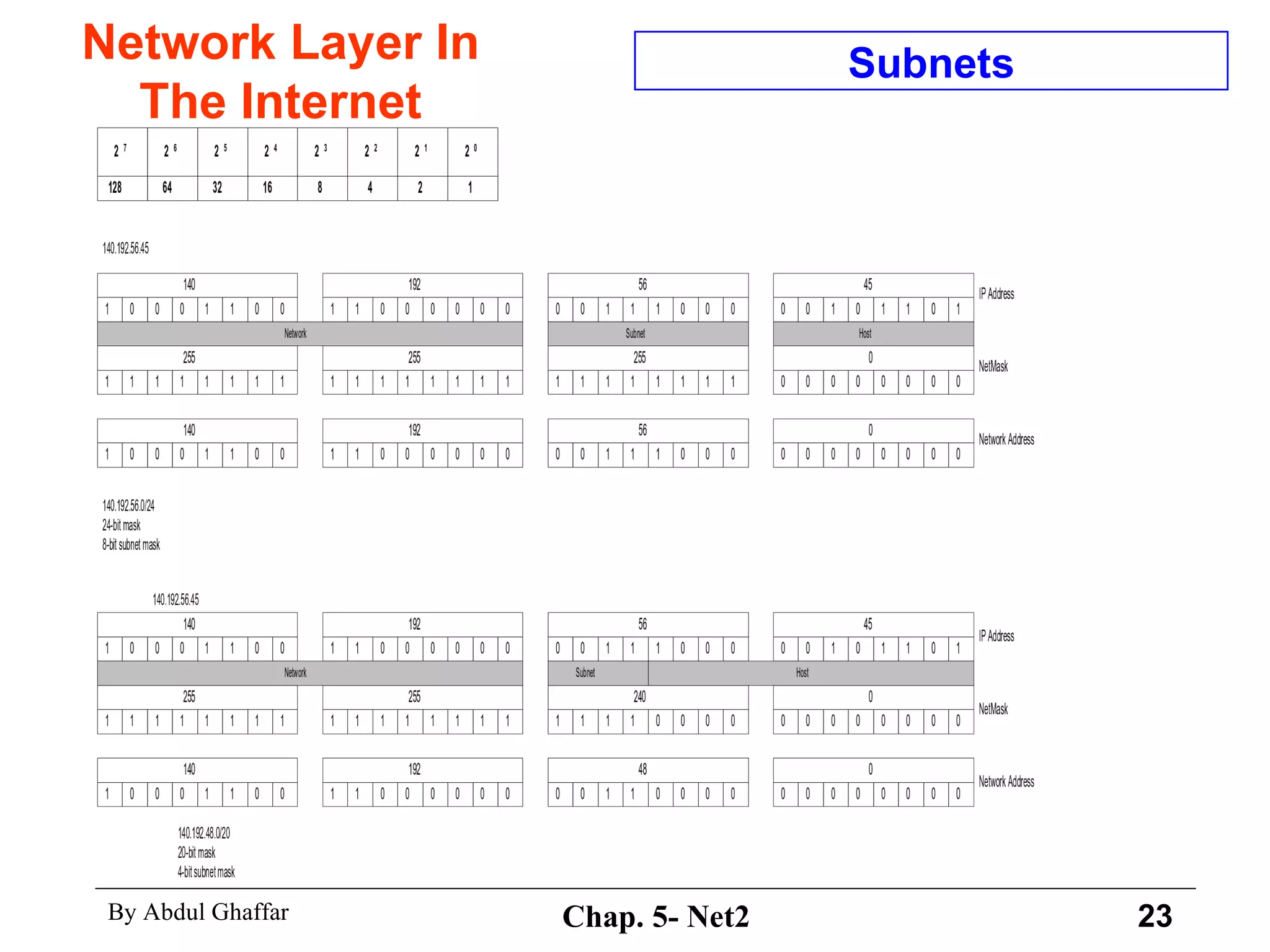
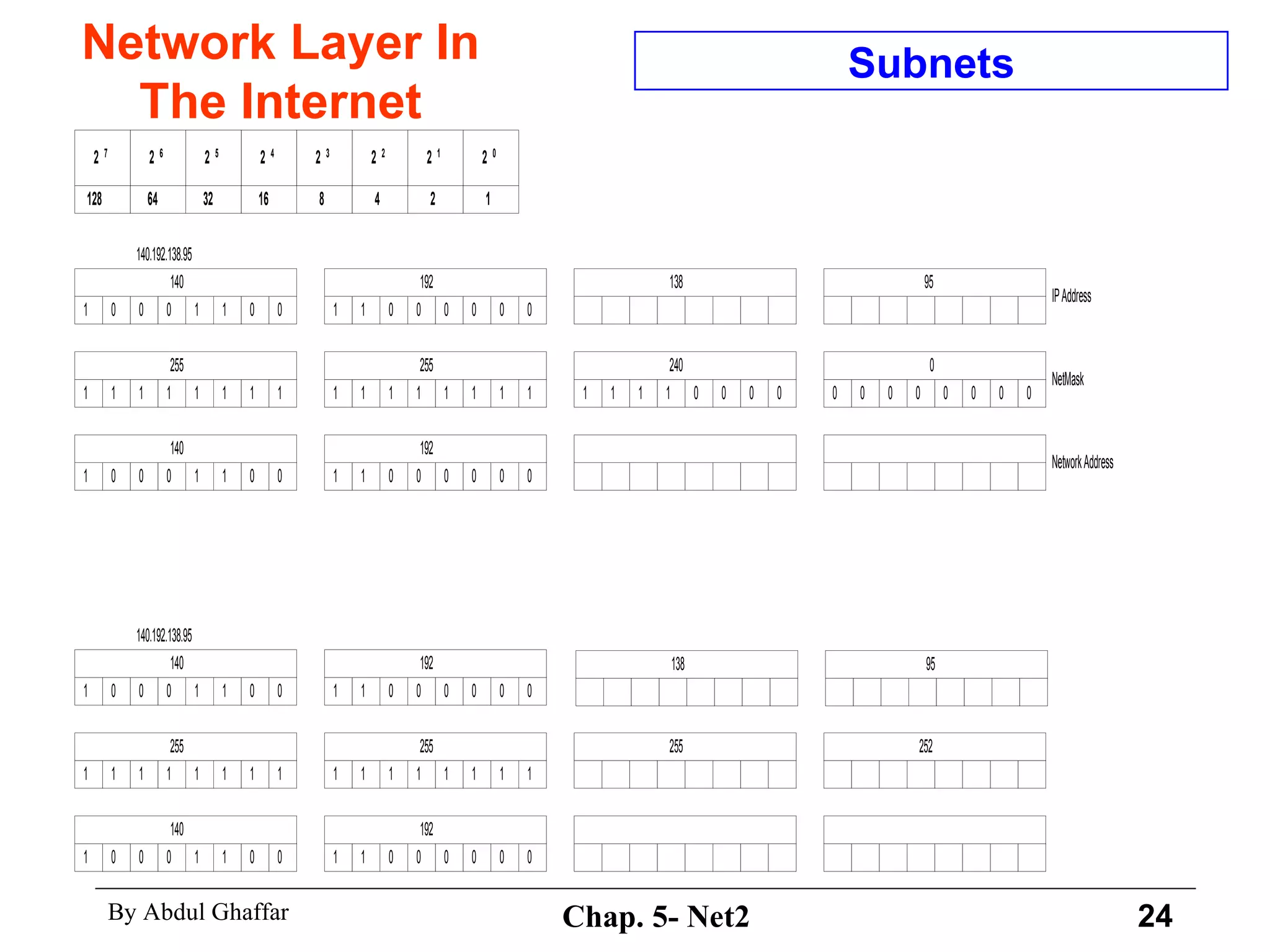
This document discusses the network layer in the internet. It covers the internet protocol (IP) which provides connectionless best-effort delivery of packets called internet datagrams. The transmission control protocol (TCP) provides reliable stream service using acknowledgments, while the user datagram protocol (UDP) provides connectionless datagram service. The document then describes the IP version 4 protocol, including the header fields, fragmentation, addressing, and subnetting techniques.