Mi0034 database management system
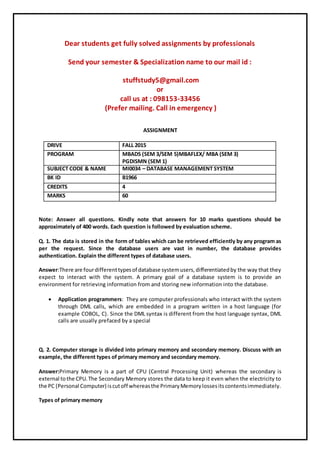
- 1. Dear students get fully solved assignments by professionals Send your semester & Specialization name to our mail id : stuffstudy5@gmail.com or call us at : 098153-33456 (Prefer mailing. Call in emergency ) ASSIGNMENT DRIVE FALL 2015 PROGRAM MBADS (SEM 3/SEM 5)MBAFLEX/ MBA (SEM 3) PGDISMN (SEM 1) SUBJECT CODE & NAME MI0034 – DATABASE MANAGEMENT SYSTEM BK ID B1966 CREDITS 4 MARKS 60 Note: Answer all questions. Kindly note that answers for 10 marks questions should be approximately of 400 words. Each question is followed by evaluation scheme. Q. 1. The data is stored in the form of tables which can be retrieved efficiently by any program as per the request. Since the database users are vast in number, the database provides authentication. Explain the different types of database users. Answer:There are fourdifferenttypesof database systemusers,differentiatedby the way that they expect to interact with the system. A primary goal of a database system is to provide an environment for retrieving information from and storing new information into the database. Application programmers: They are computer professionals who interact with the system through DML calls, which are embedded in a program written in a host language (for example COBOL, C). Since the DML syntax is different from the host language syntax, DML calls are usually prefaced by a special Q. 2. Computer storage is divided into primary memory and secondary memory. Discuss with an example, the different types of primary memory and secondary memory. Answer:Primary Memory is a part of CPU (Central Processing Unit) whereas the secondary is external tothe CPU.The Secondary Memory stores the data to keep it even when the electricity to the PC (Personal Computer) iscutoff whereasthe PrimaryMemorylossesitscontentsimmediately. Types of primary memory
- 2. (a) Analog Memory: This type of Memory was used in the computers built during 1960's. The basic storage device in this type of memory consists of a small ring shaped piece of magnetic material called a magnetic core. Each magnetic core in a Q. 3. Considerany one example ofa relational database and show how the different operations of relational algebra can be performed on the table showing the output. Answer:A querylanguage isa language inwhichuserrequestsinformationfromthe database. it can be categorized as either procedural or nonprocedural. In a procedural language the user instructs the system to do a sequence of operations on database to compute the desired result. In nonprocedural language the user describes the desired information without giving a specific procedure for obtaining that information. The relational algebraisaprocedural querylanguage.Itconsistsof a set of operations that take one or two relations as input and produces a new relation as output. Fundamental Operations Q. 4. Describe the different normal forms with one example throughout. Answer:Firstnormal form (1NF or Minimal Form) is a normal form used in database normalization. A relational database tablethatadheresto 1NF is one that meets a certain minimum set of criteria. These criteria are basically concerned with ensuring that the table is a faithful representation of a relation and that it is free of repeating groups. The concept of a "repeating group" is, however, understood in different ways by different theorists. As a consequence, there is no universal agreement as to which features would disqualify a table from being in 1NF. Q. 5. Write Short Notes on a. Transaction Commit:Marks the endof a successful implicit or explicit transaction. If TRANCOUNT is 1, COMMIT TRANSACTION makes all data modifications performed since the start of the transaction a permanent b. Atomicity:Indatabase systems,atomicity(oratomicness;fromGreeka-tomos,undividable) isone of the ACIDtransaction properties. In an atomic transaction, a series of database operations either all occur, or nothingoccurs.The seriesof operationscannotbe divided apart and executed partially from c. Deferred update:With deferred update, the macro could run an order of magnitude faster. The more insidiousof the twowayshigher-levelcommands come about is through the efforts of a good
- 3. designer. The primitive operations of the editor are treated as building blocks for more complex editor operations. This produces the usual increase in productivity during editor development -- a good thing. d. Security:Security is the degree of resistance to, or protection from, harm. It applies to any vulnerable and valuable asset, such as a person, dwelling, community, nation, or organization. As noted e. System log:The system log file contains events that are logged by the operating system components Q. 6. With an example explain the working of ODBMS. Explaining with an example Answer:When you use an ODBMS, the way you use your data is the way you store it. The first benefitcanbe foundindevelopment.Whenyouuse anODBMS, you will write less code than if you were writing to an RDBMS. The reason for the smaller amount of code is simple -- when you are using Java or C++ -- you won't Dear students get fully solved assignments by professionals Send your semester & Specialization name to our mail id : stuffstudy5@gmail.com or call us at : 098153-33456 (Prefer mailing. Call in emergency )
