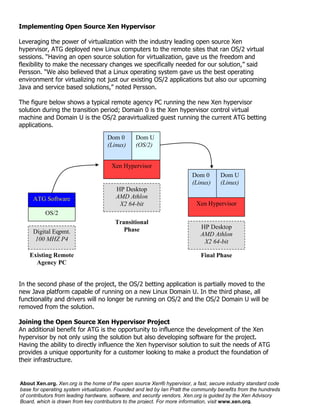
ATG needed to virtualize over 2,000 remote betting terminals to allow for hardware independence and an evolutionary transition from older OS/2 systems to newer Linux systems. They implemented the open source Xen hypervisor which allowed them to run existing OS/2 applications virtually on new Linux machines, transition applications to a new Java platform gradually, and gain more flexibility and influence over the hypervisor development. This provided a cost effective solution to modernize systems while maintaining existing functionality during the transition.