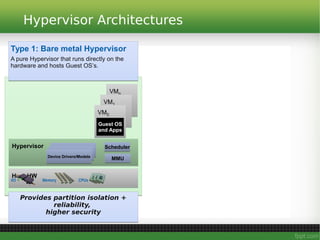
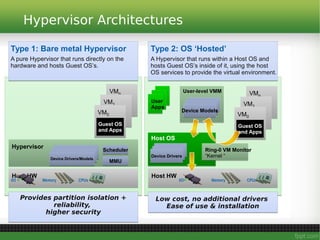
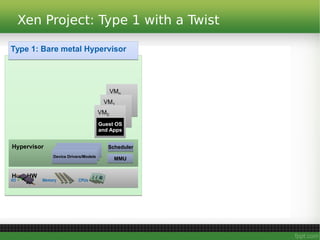
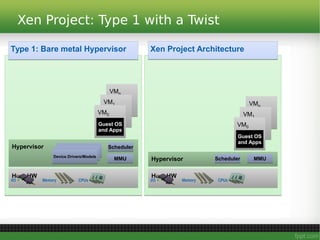
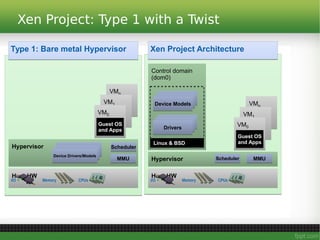
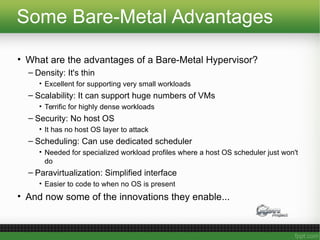
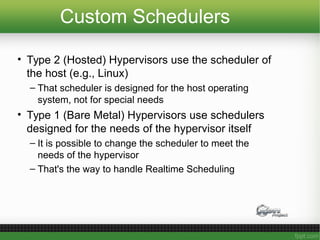
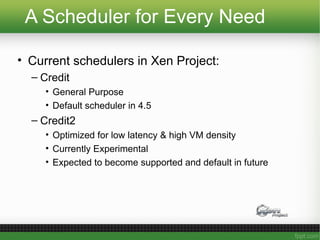
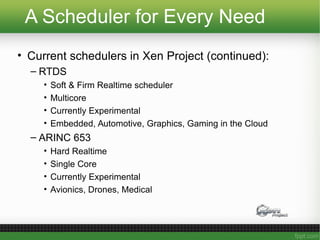
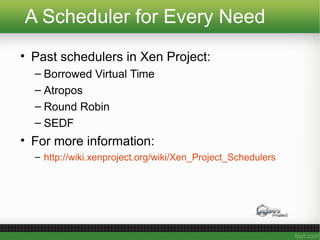
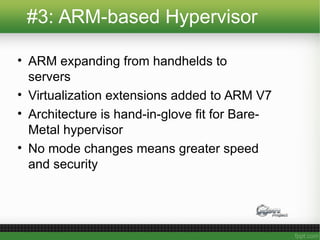
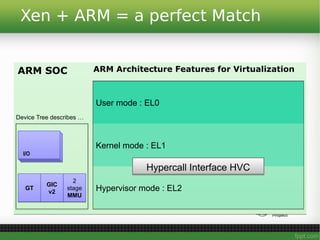
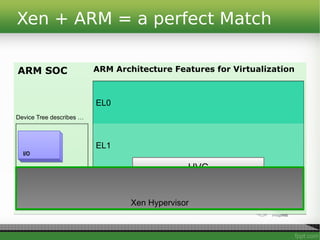
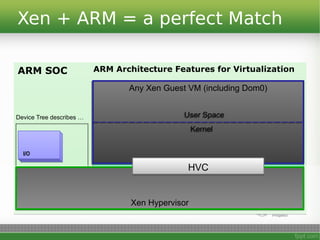
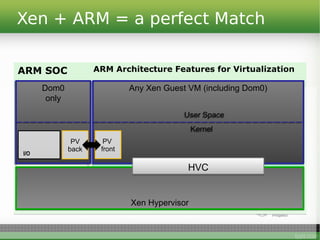
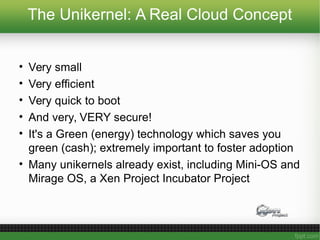
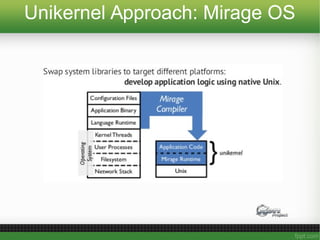
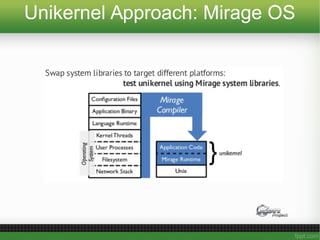
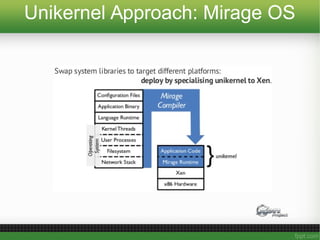
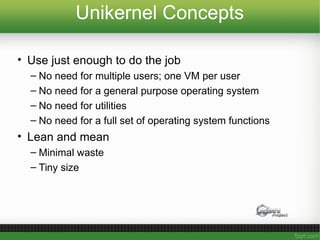
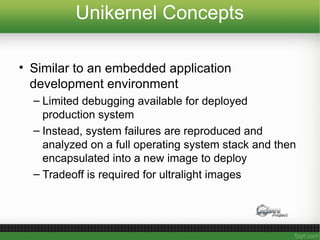
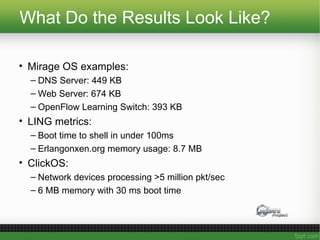
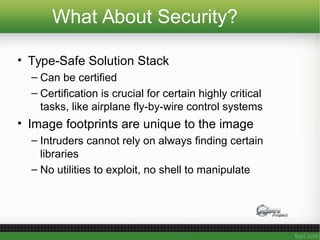
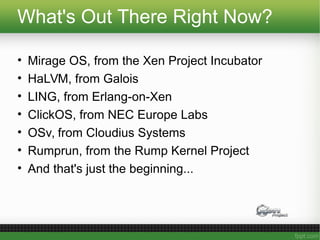
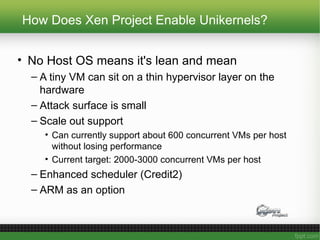
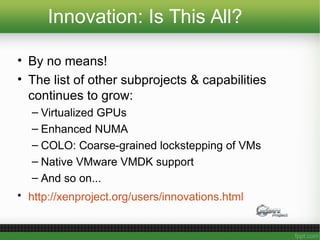
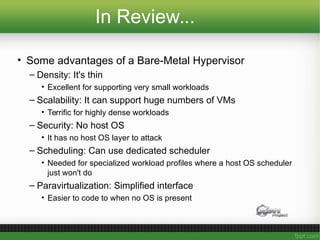
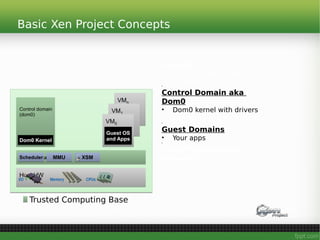
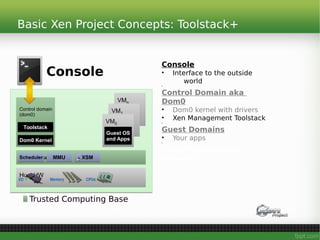
This document summarizes Russell Pavlicek's presentation on the bare-metal hypervisor as a platform for innovation. Some key innovations enabled by the bare-metal hypervisor discussed include Xen Automotive for developing embedded automotive systems, real-time virtualization support, an ARM-based hypervisor for new applications on ARM architecture, and unikernel systems that create highly secure and efficient cloud applications. A bare-metal hypervisor provides advantages like density, scalability, security and custom scheduling that facilitate these innovations.