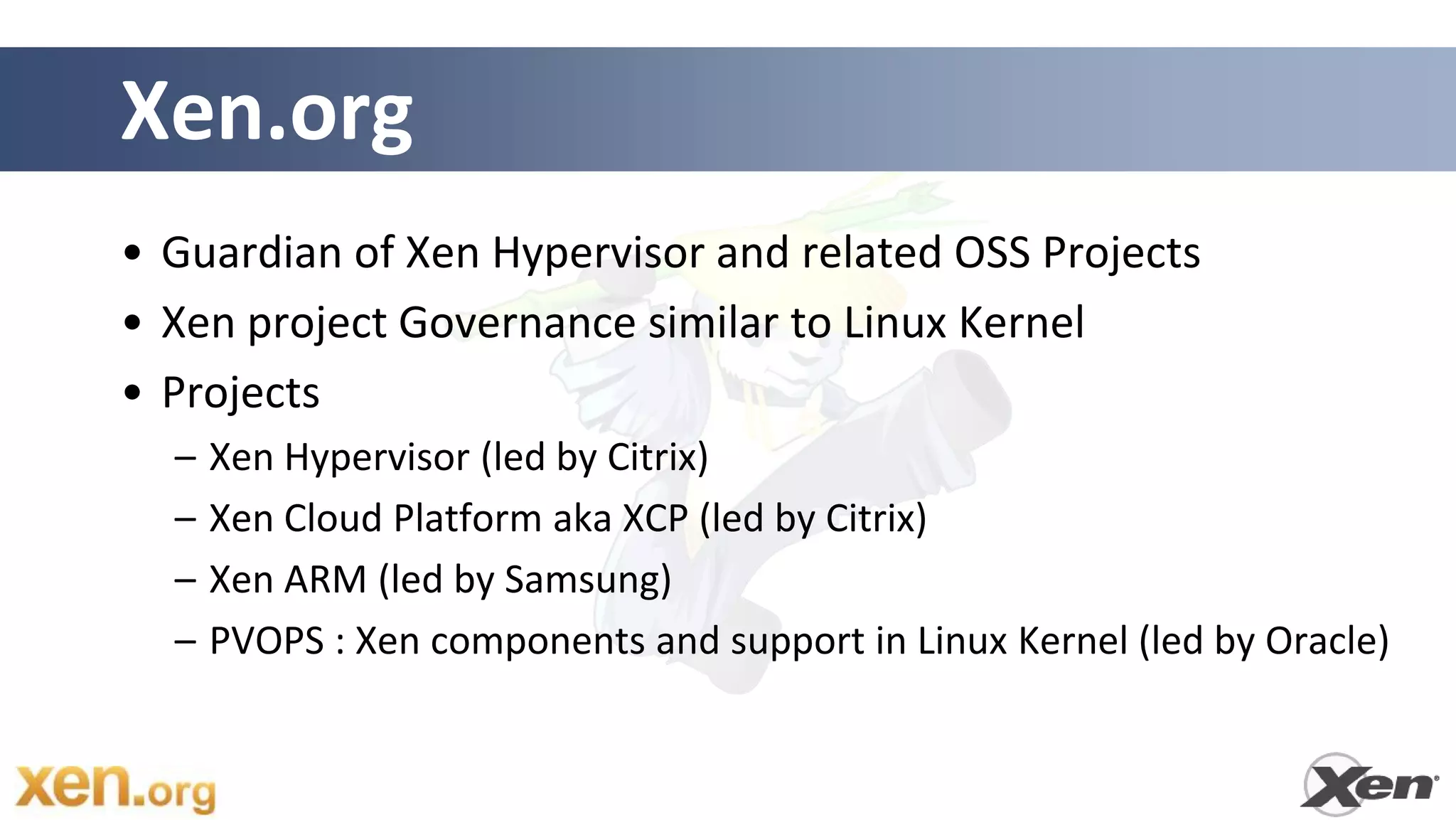
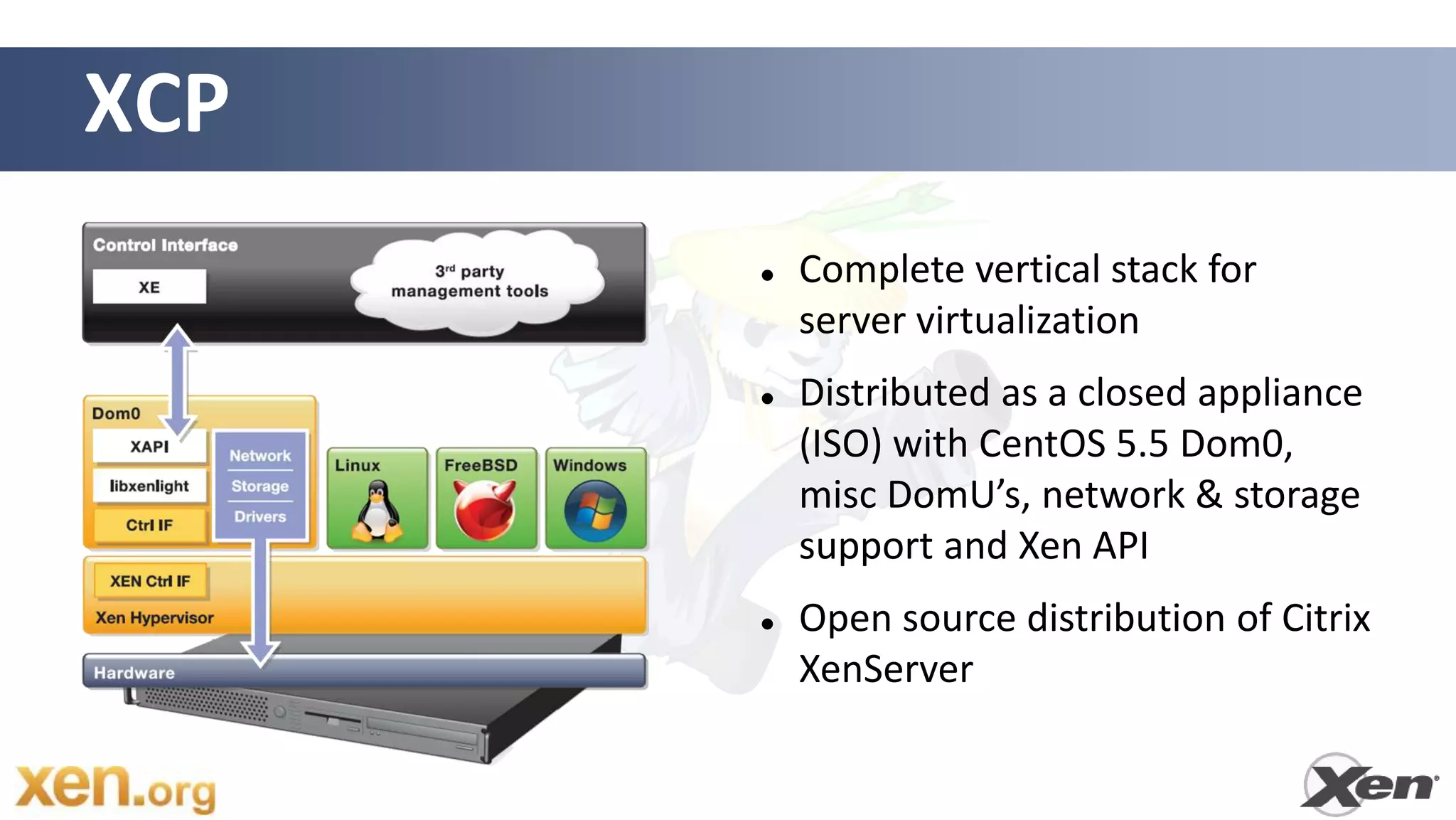
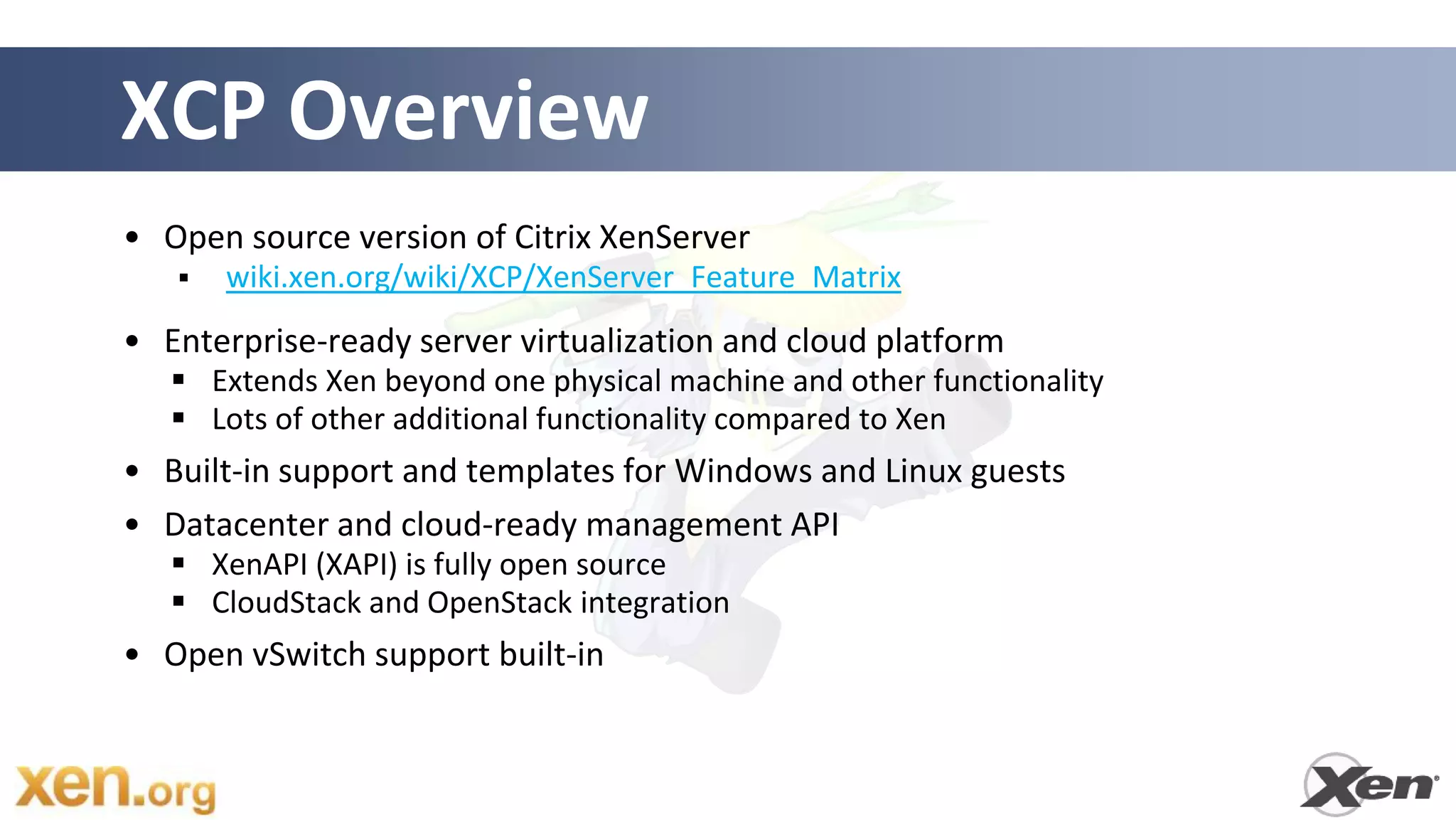
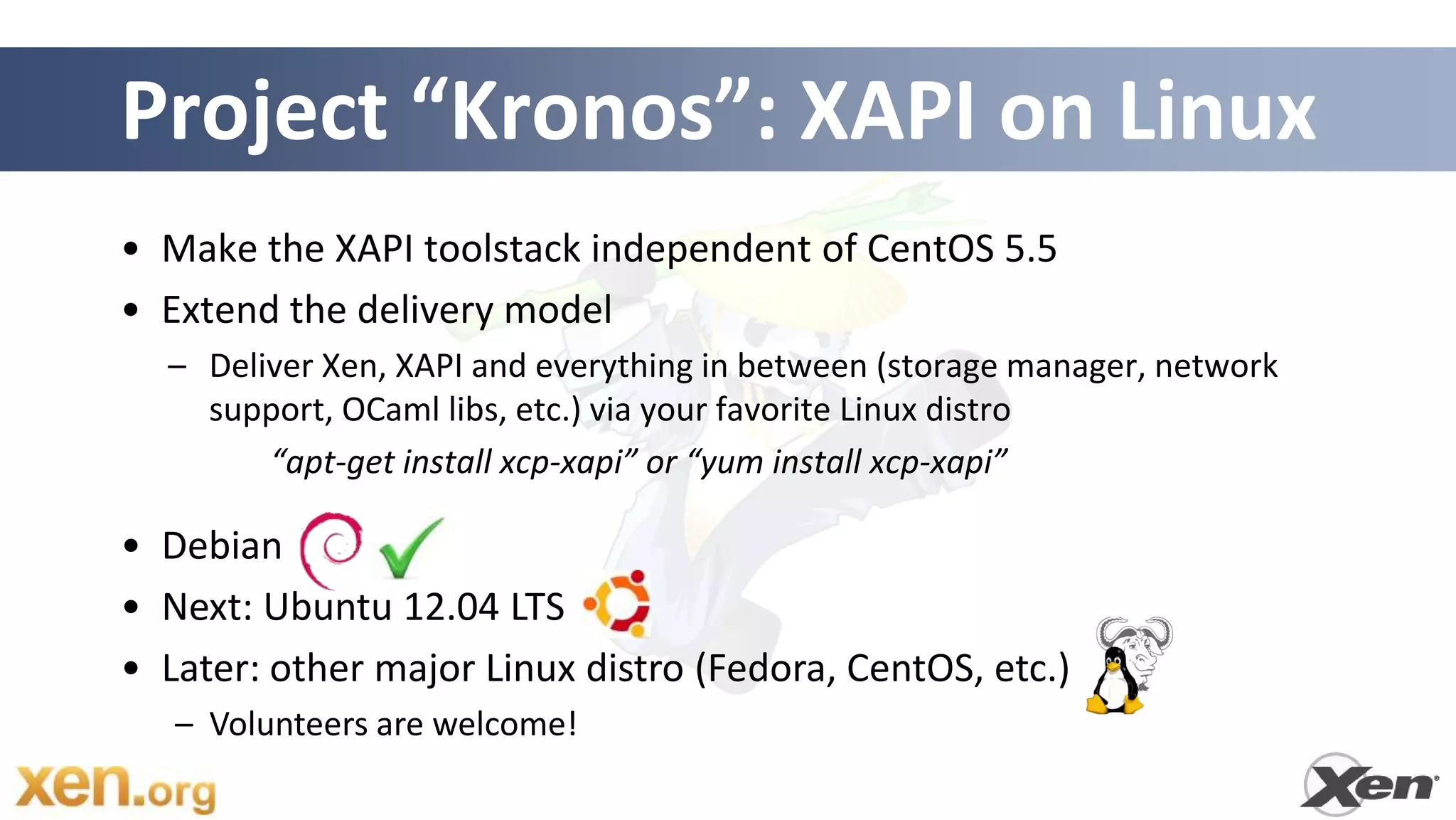
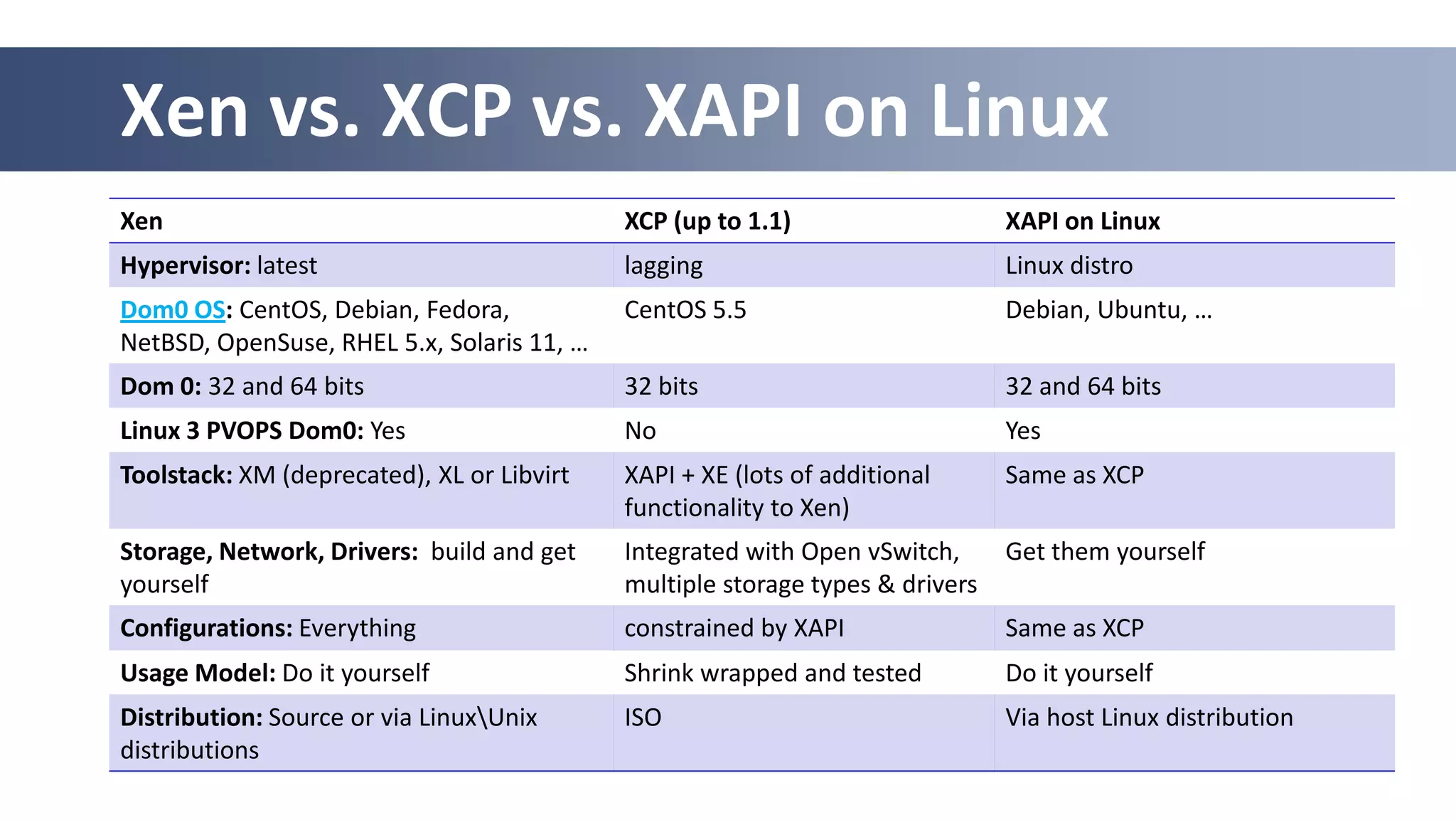
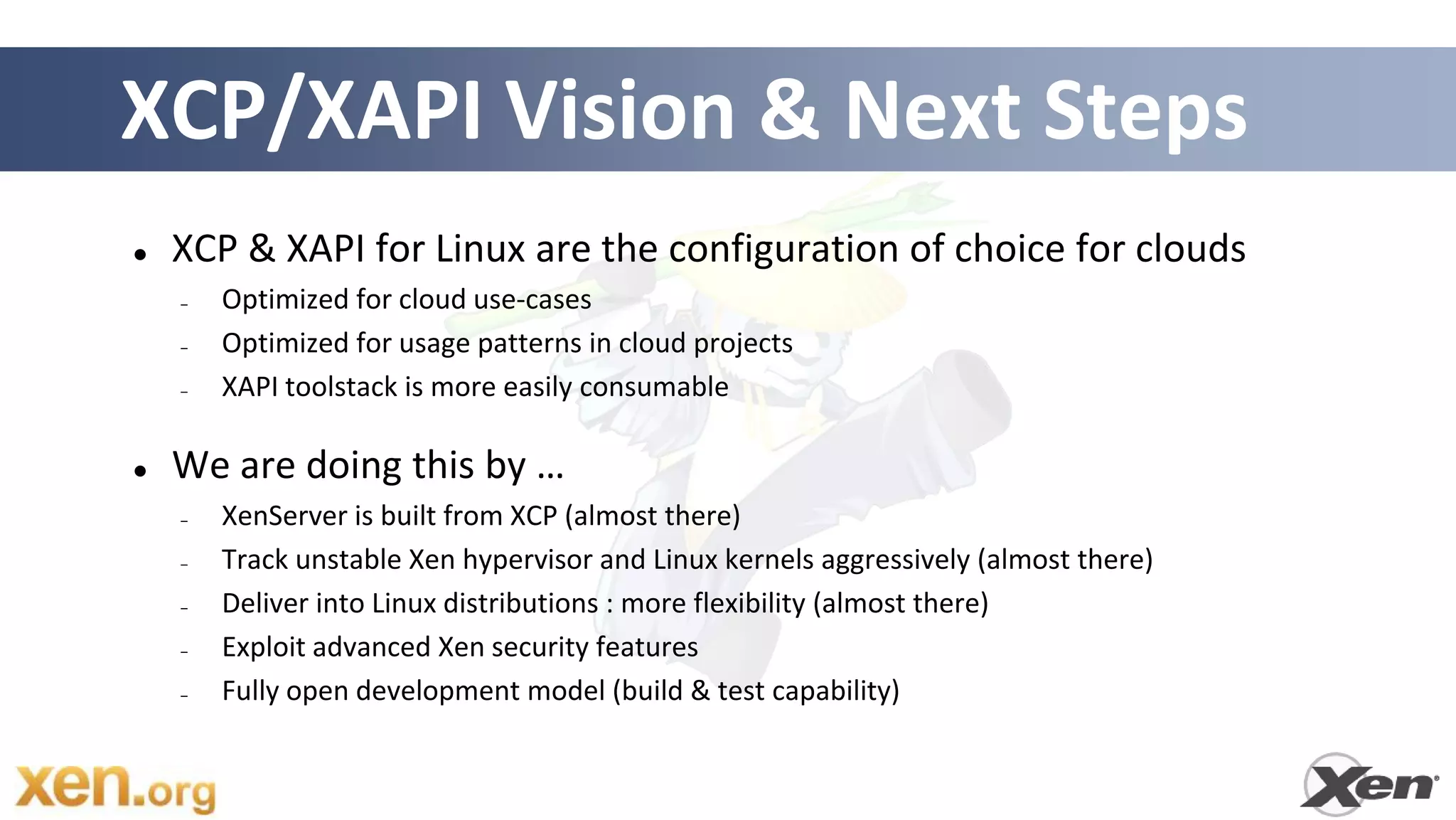
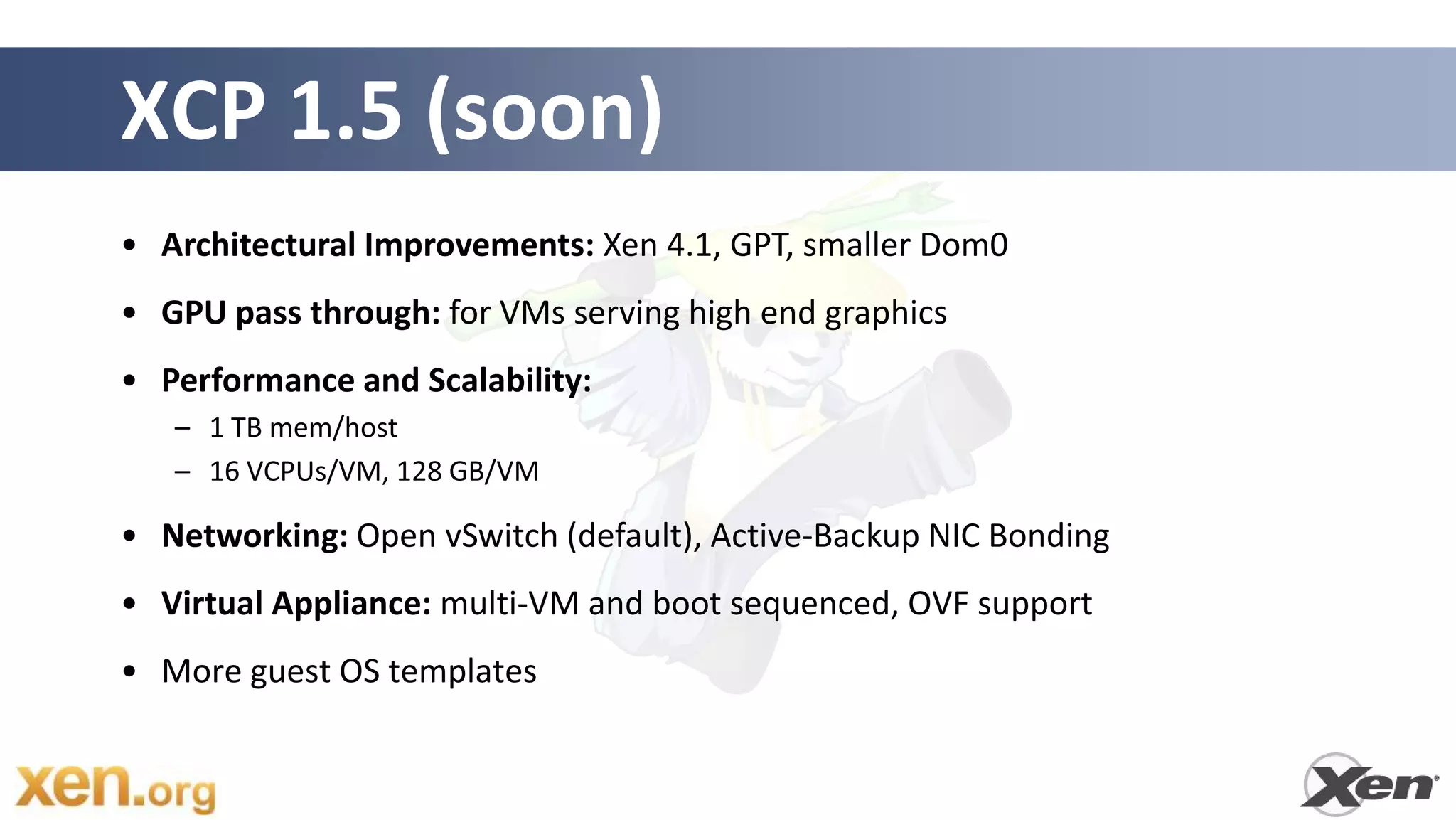
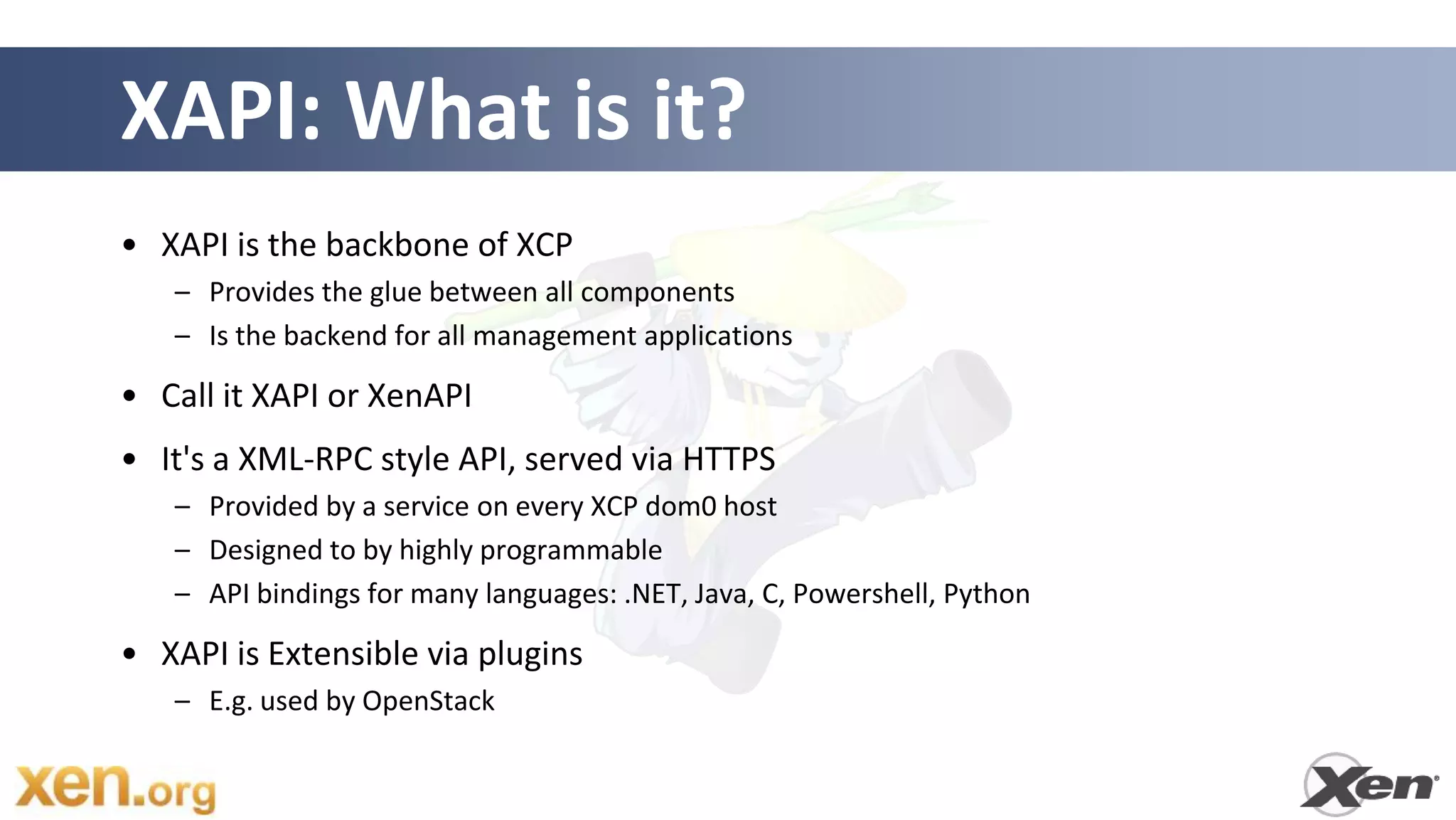
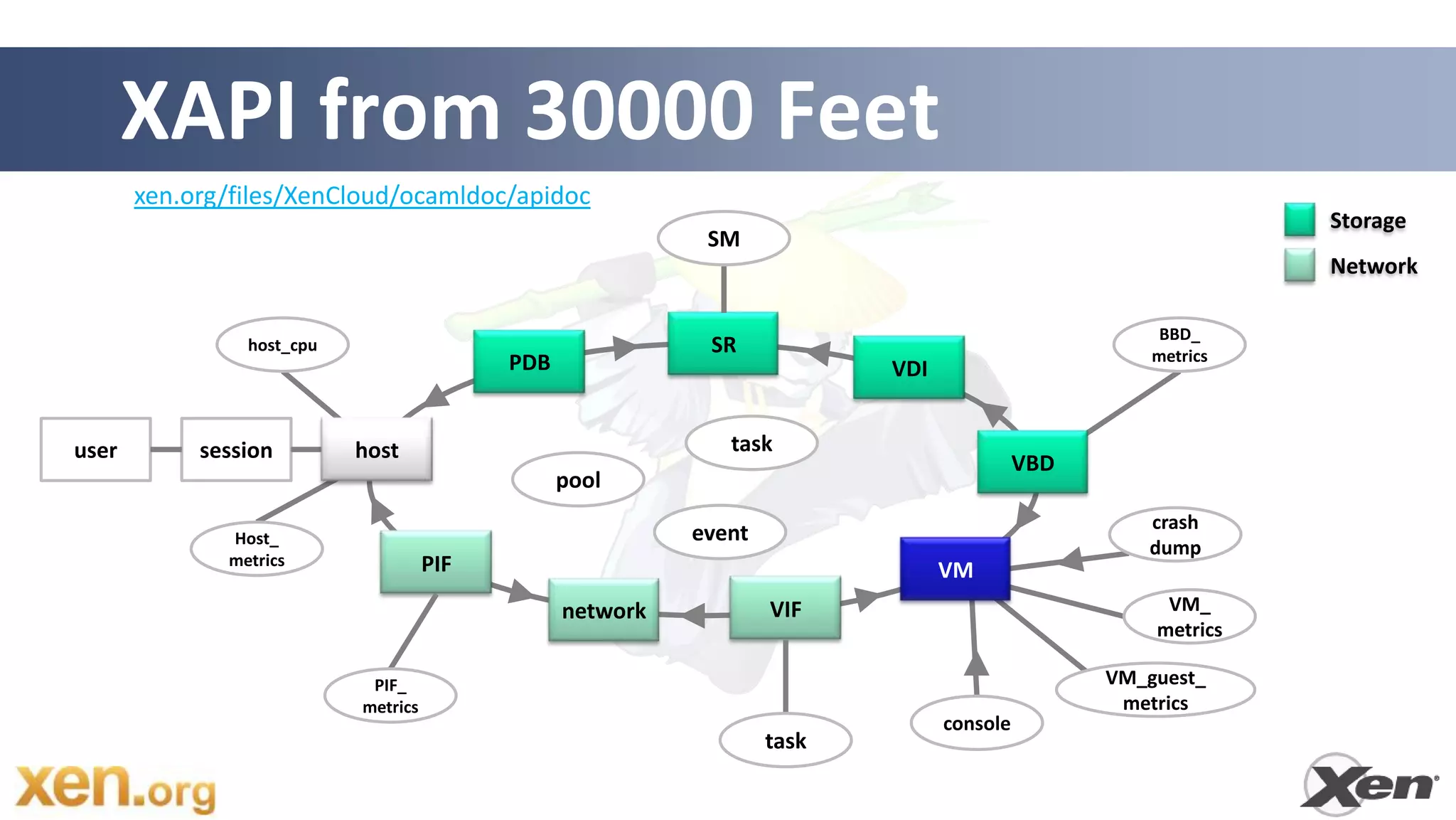
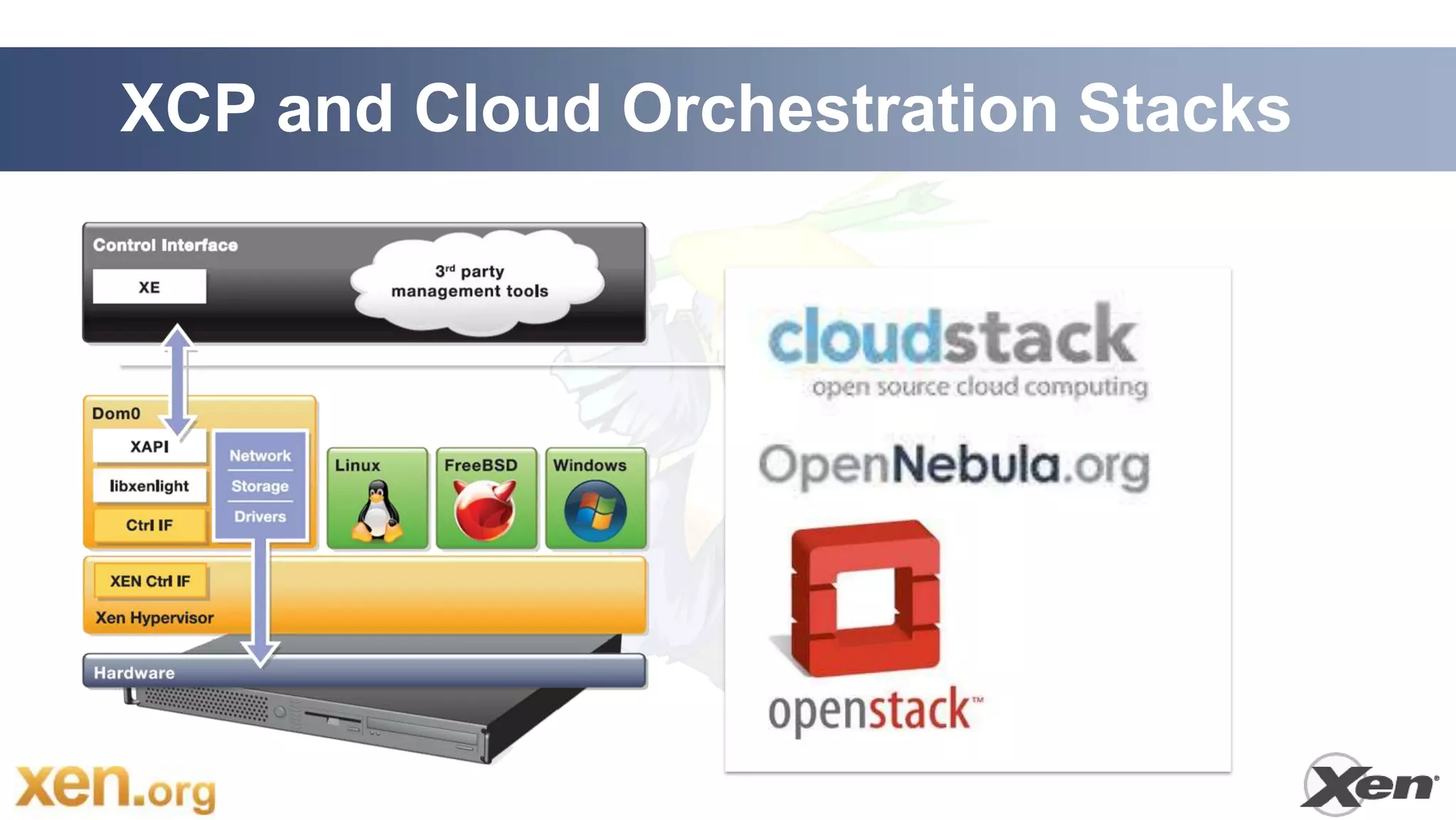
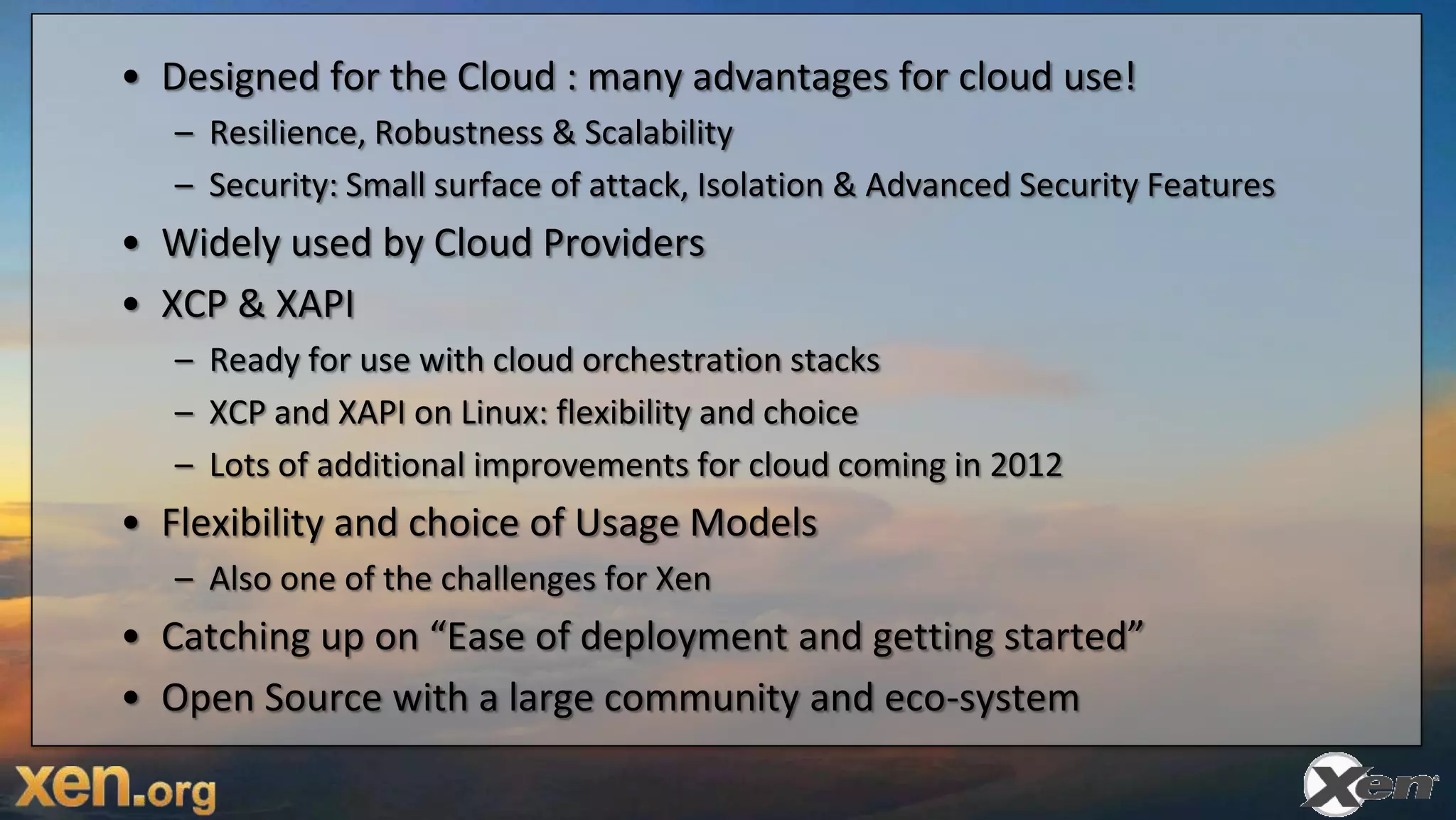
Xen Cloud Platform (XCP) provides a complete virtualization stack for server virtualization and cloud computing. It is based on the open source Xen hypervisor and extends it with features for cloud management and orchestration through the open source XenAPI toolstack. XCP delivers Xen, XenAPI, and all related components as a pre-packaged virtual appliance that can be easily deployed. This summary focuses on the history and architecture of Xen in cloud computing and how XCP builds upon Xen to deliver an enterprise-ready virtualization platform.