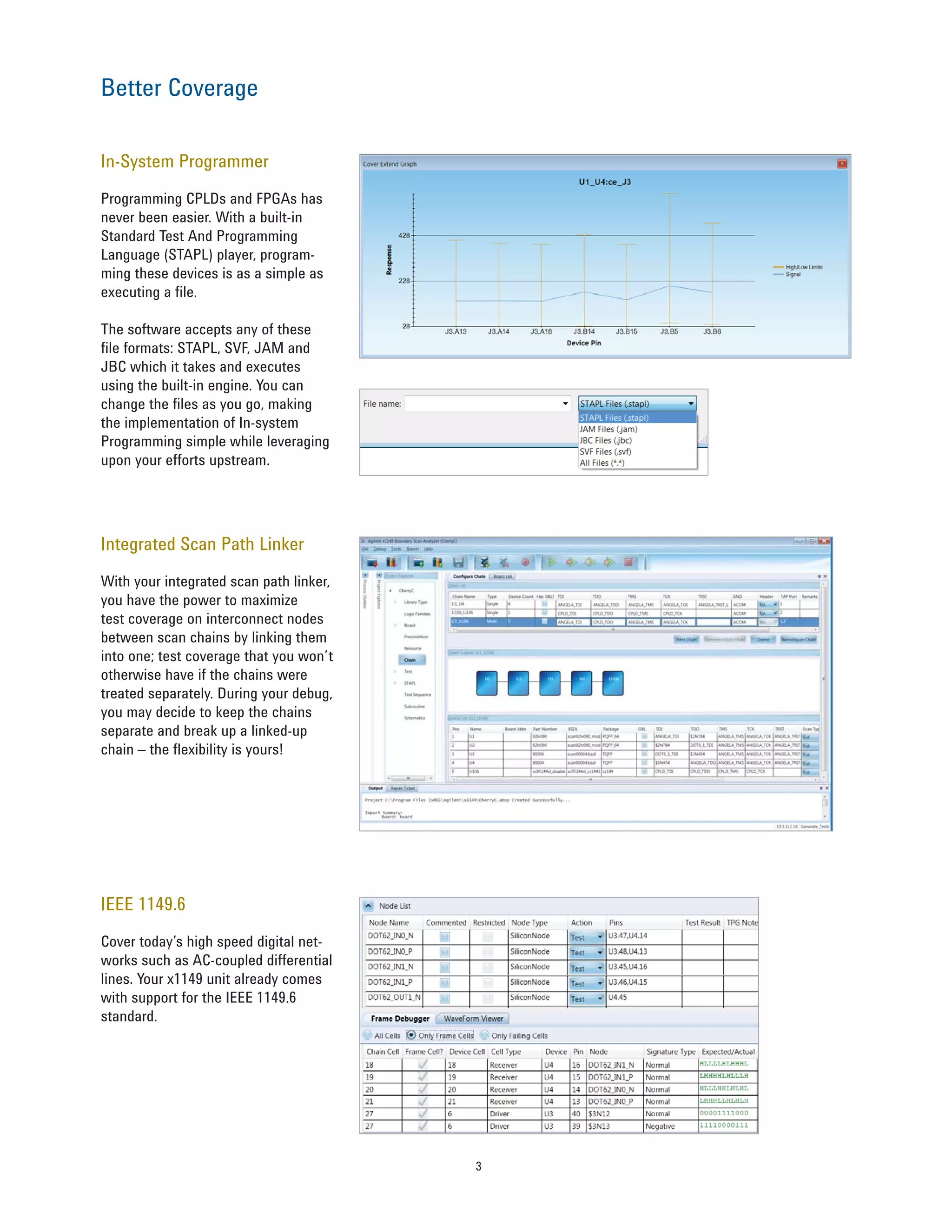
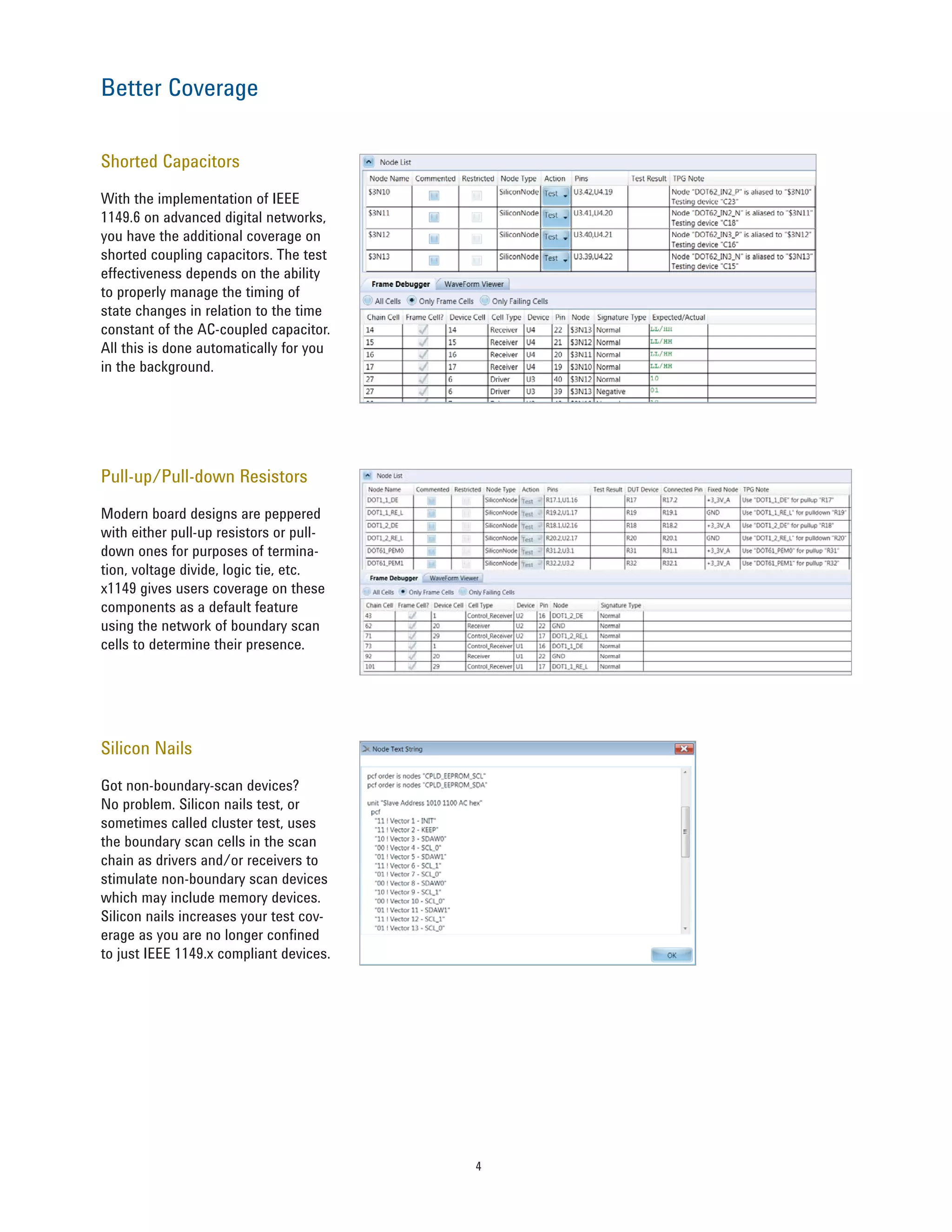
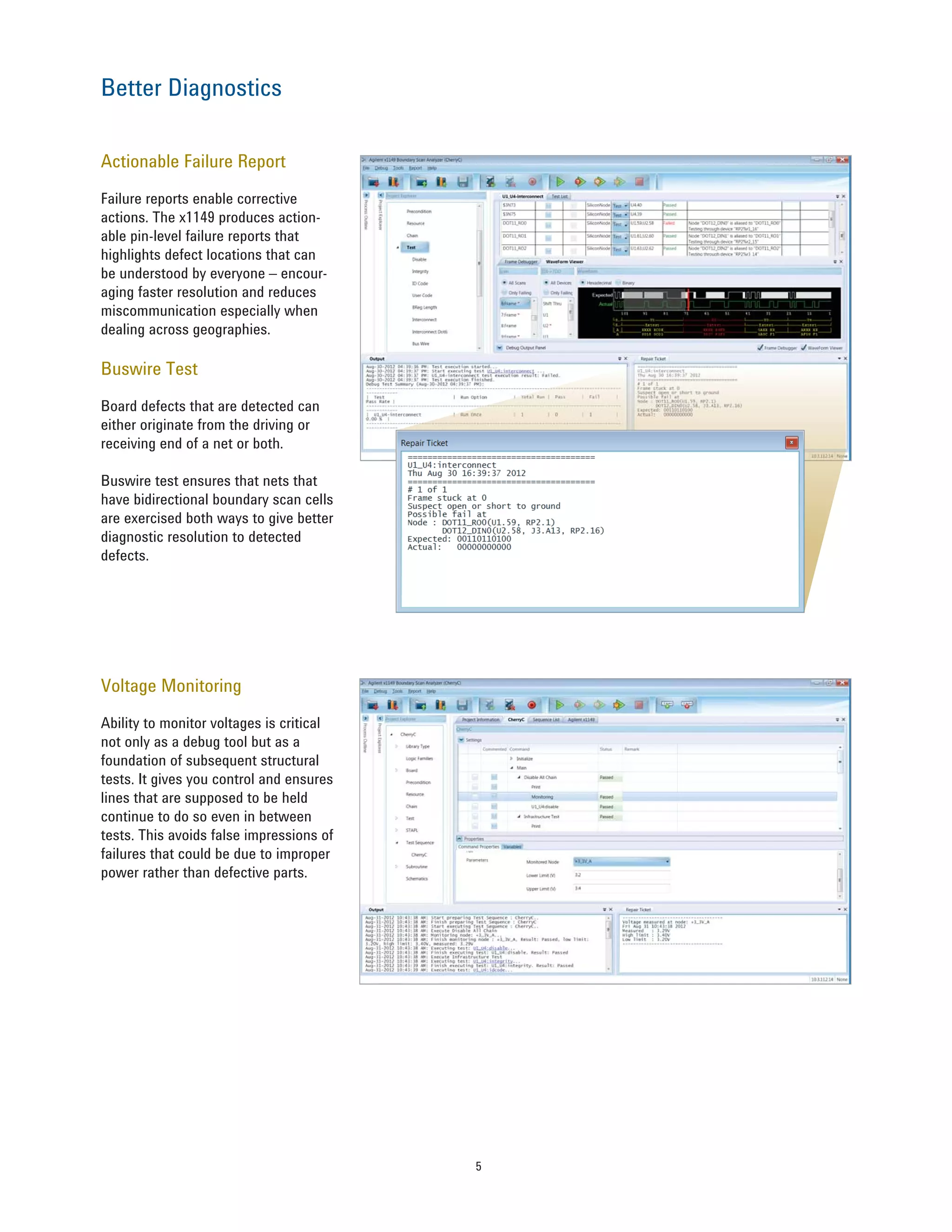
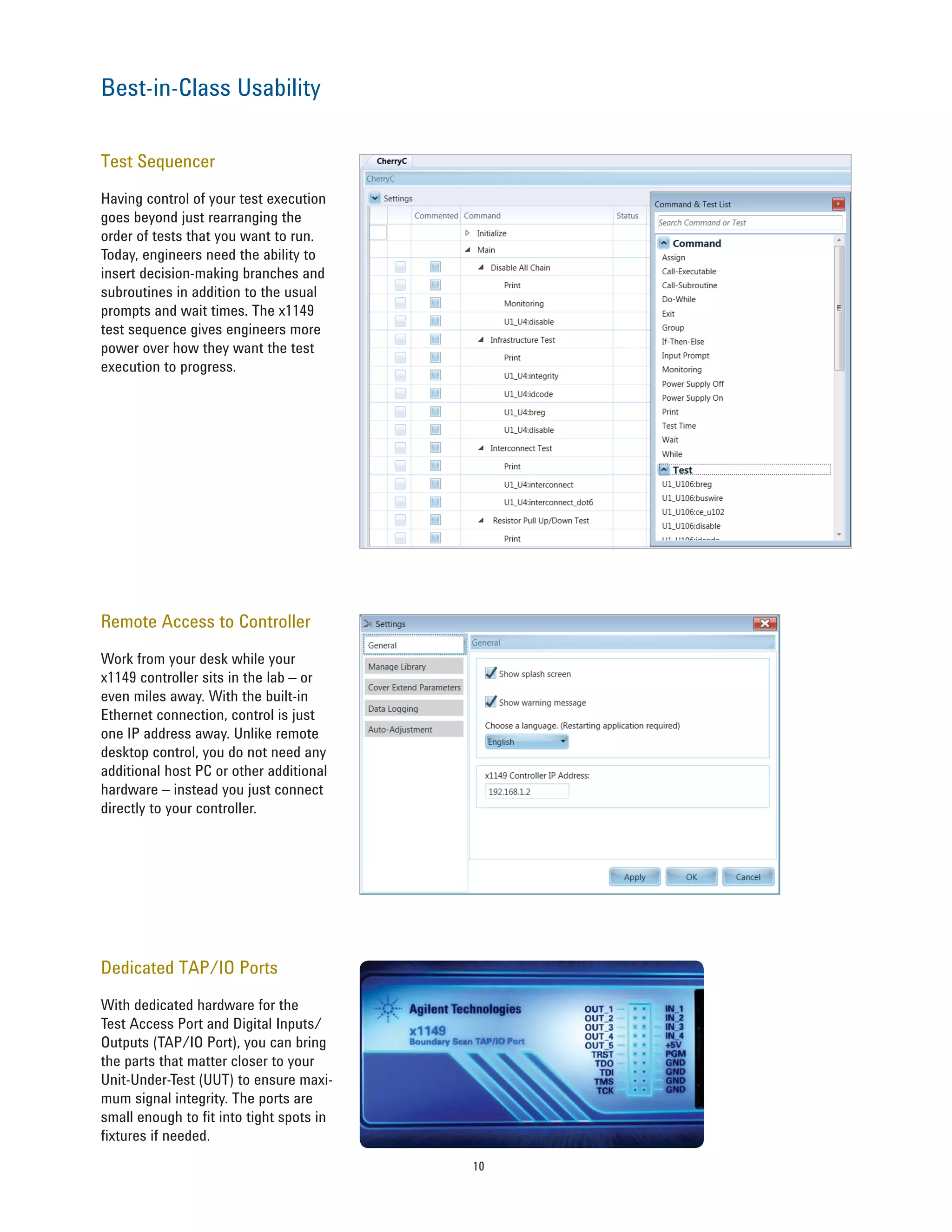
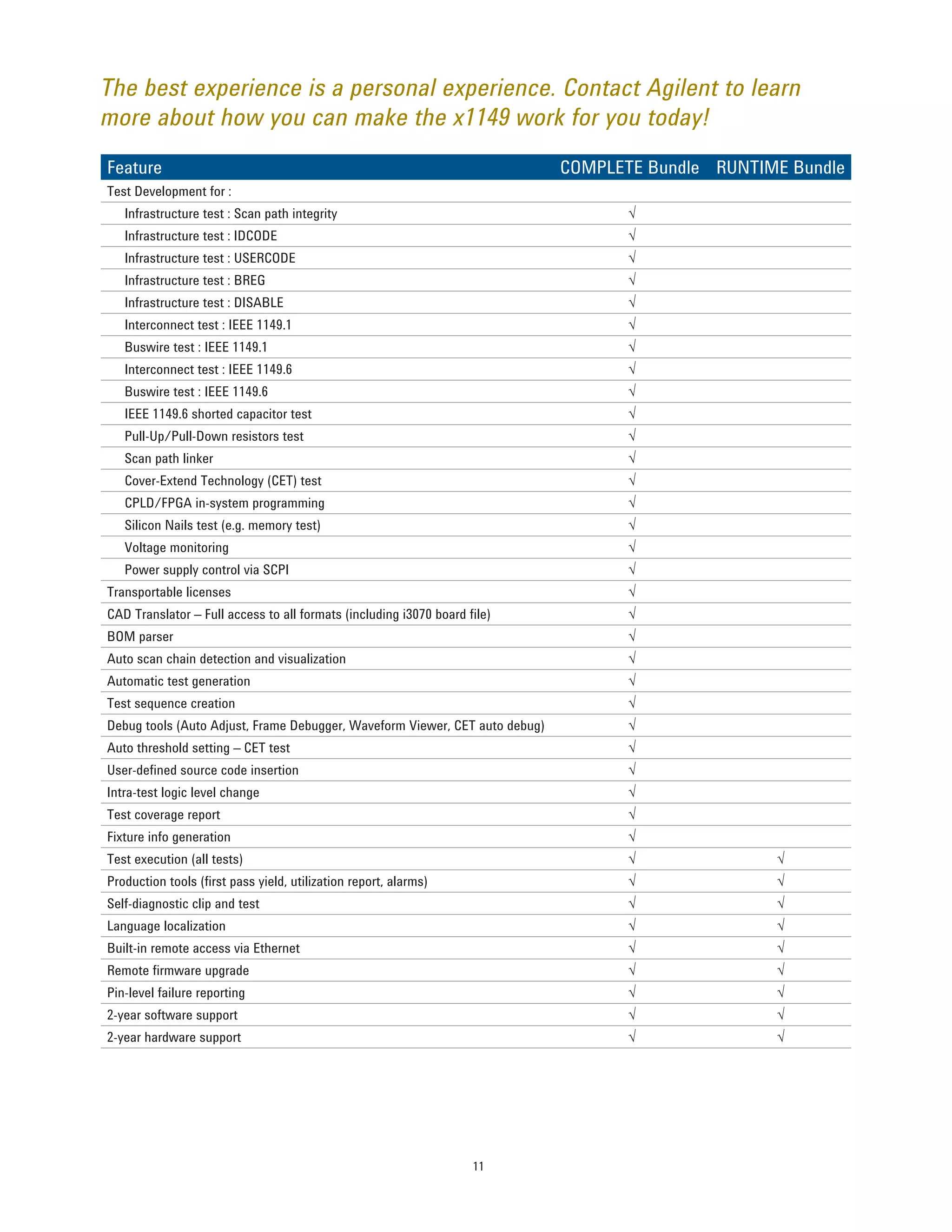
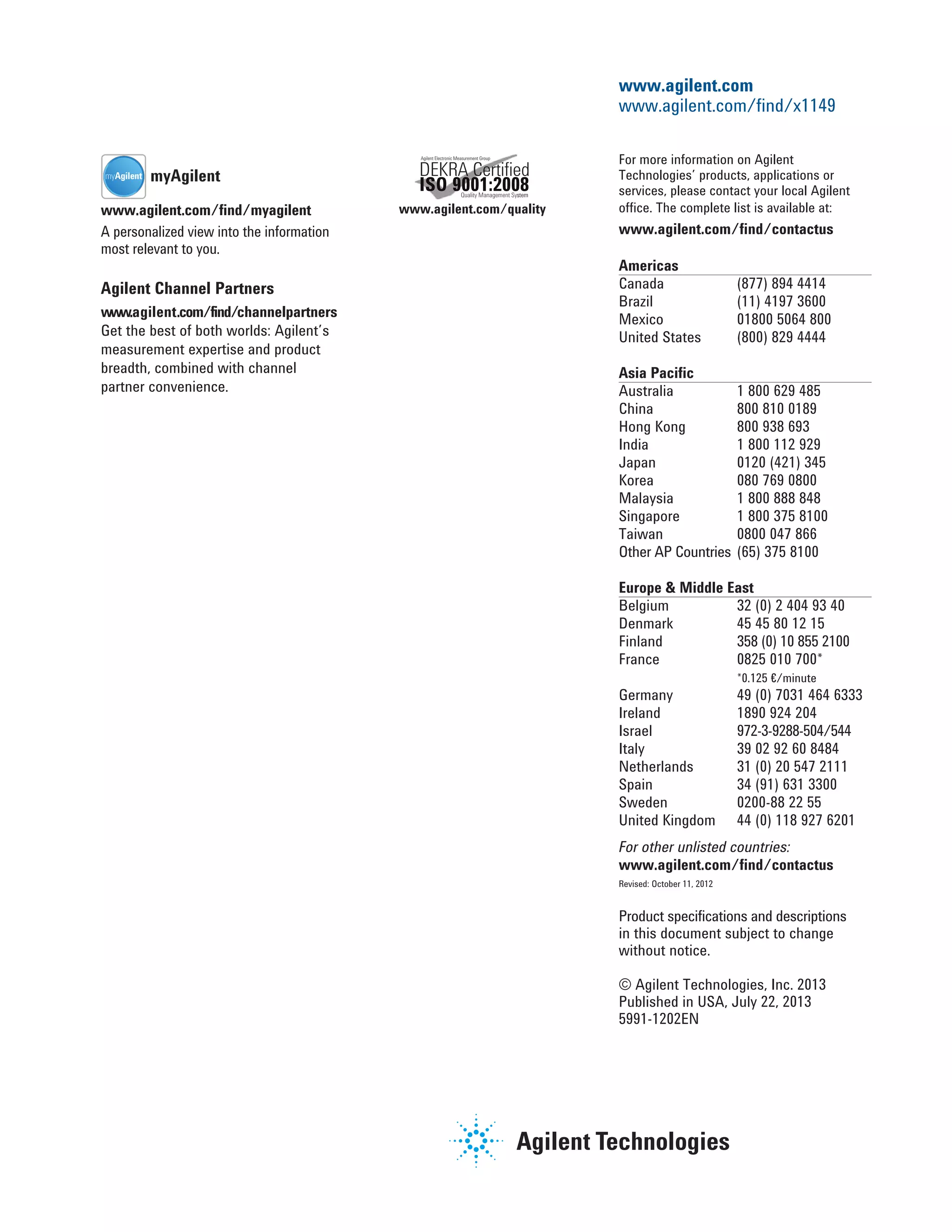
The Agilent X1149 Boundary Scan Analyzer provides a versatile solution for engineers facing testing challenges, offering quick start-up, extensive test coverage, and reusability from design validation to mass manufacturing. Key features include patented Cover-Extend Technology for non-scan components, in-system programming for CPLD/FPGA, and actionable pin-level failure reporting. Its user-friendly interface and built-in remote access enhance usability while ensuring effective diagnostics and test coverage across various applications.