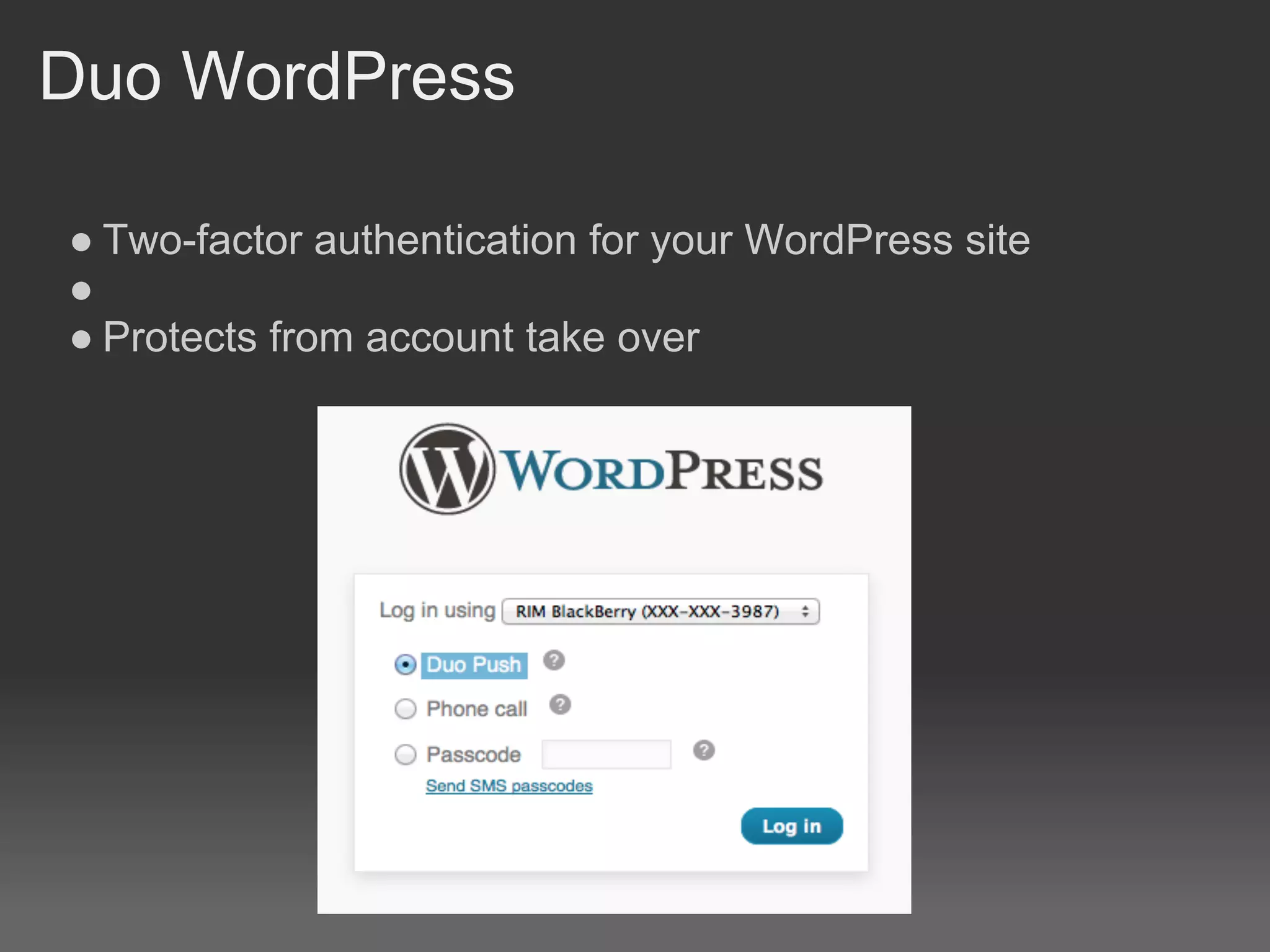
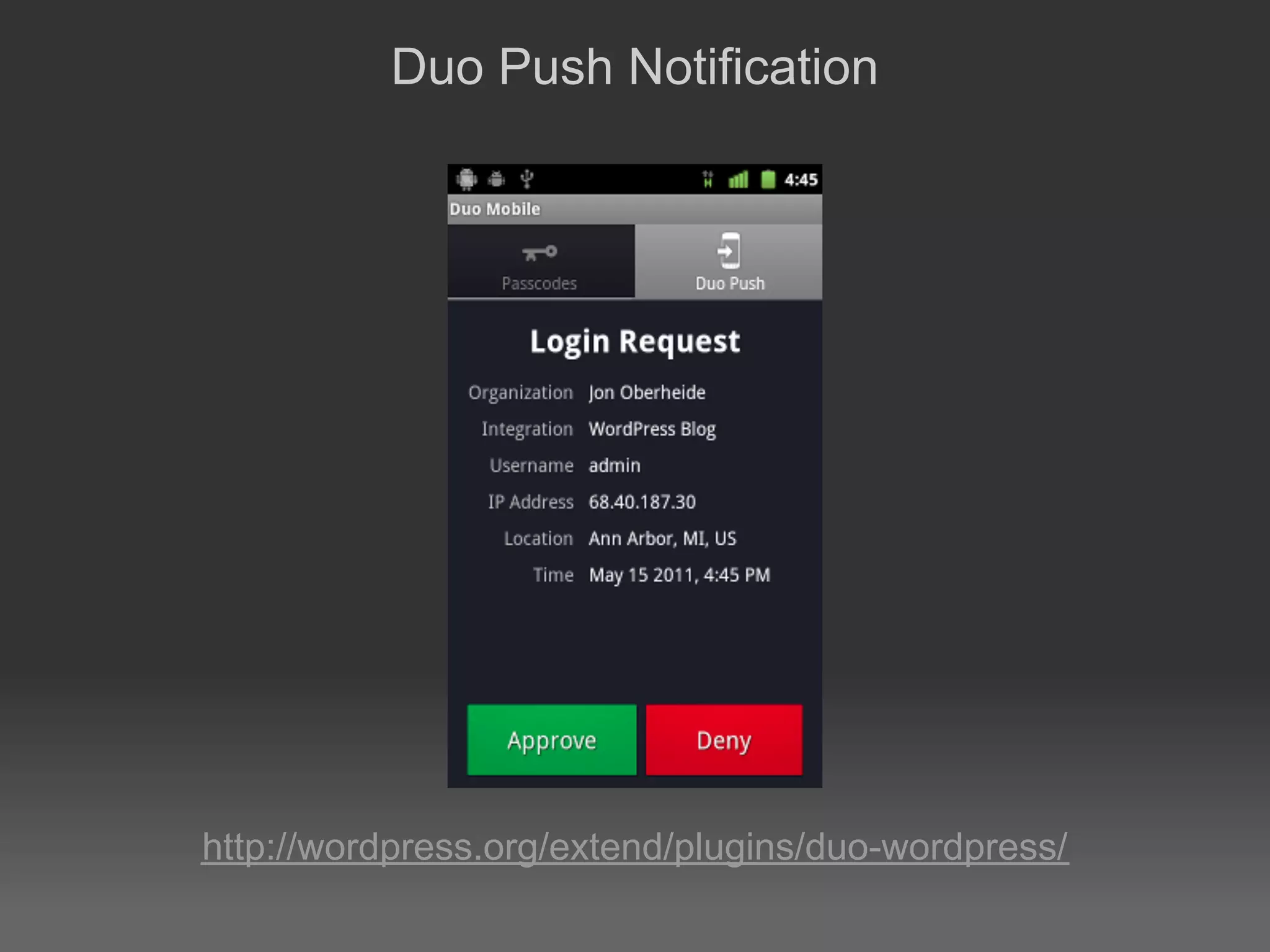
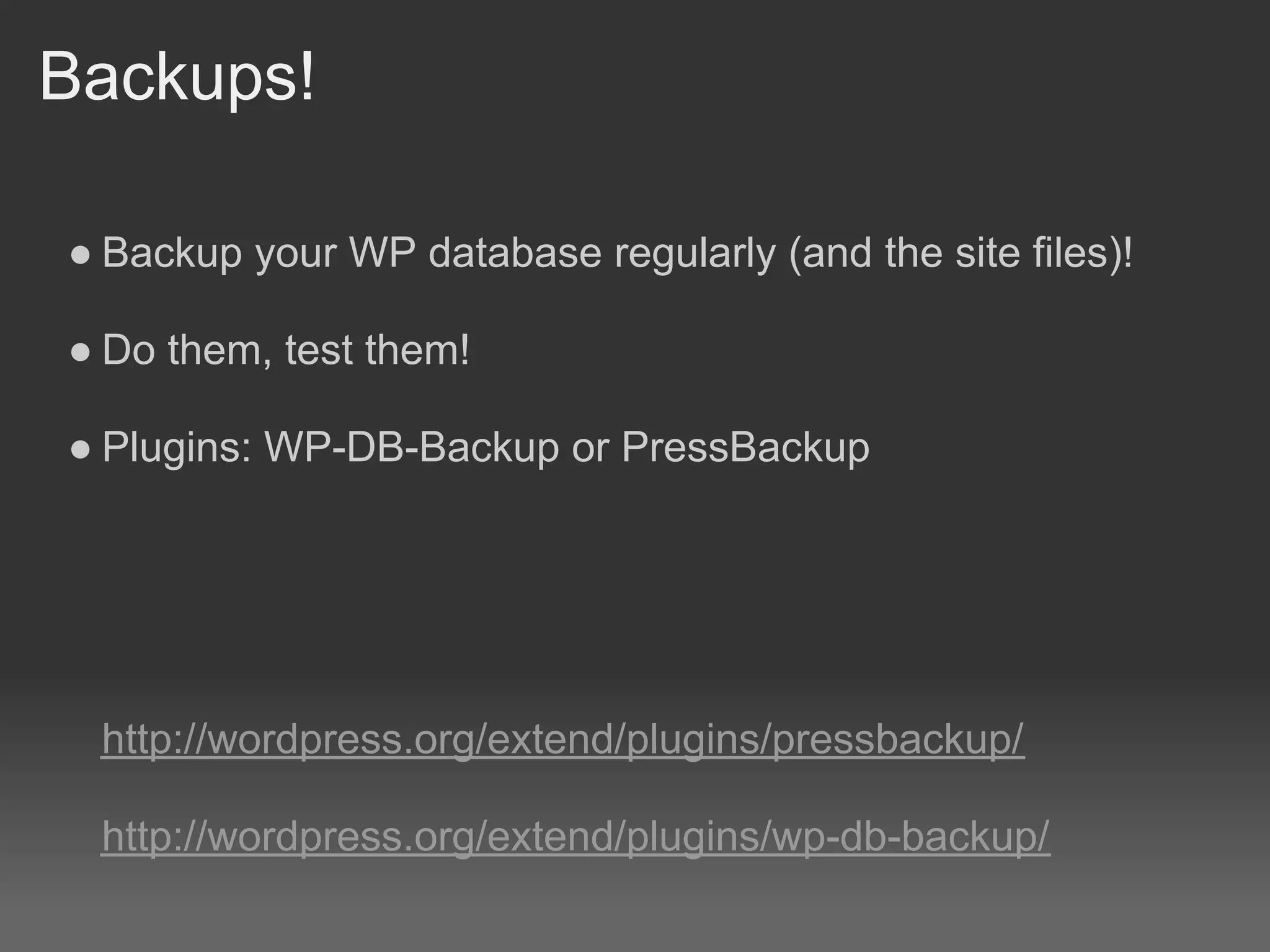
The document is an introduction to WordPress security presented at WordCamp Detroit on November 12-13, 2011. It discusses raising the security bar of WordPress sites by changing database prefixes, deleting the default admin user, using SSL for wp-admin, setting proper file permissions, and limiting login attempts. It also stresses the importance of regular backups and having disaster recovery plans, including restoring from backups if the site becomes compromised. Various security plugins are presented that can help harden WordPress sites, and paid services like VaultPress are introduced that can make security management easier. The overall message is that sites can be better protected with minimal effort, especially regular backups.