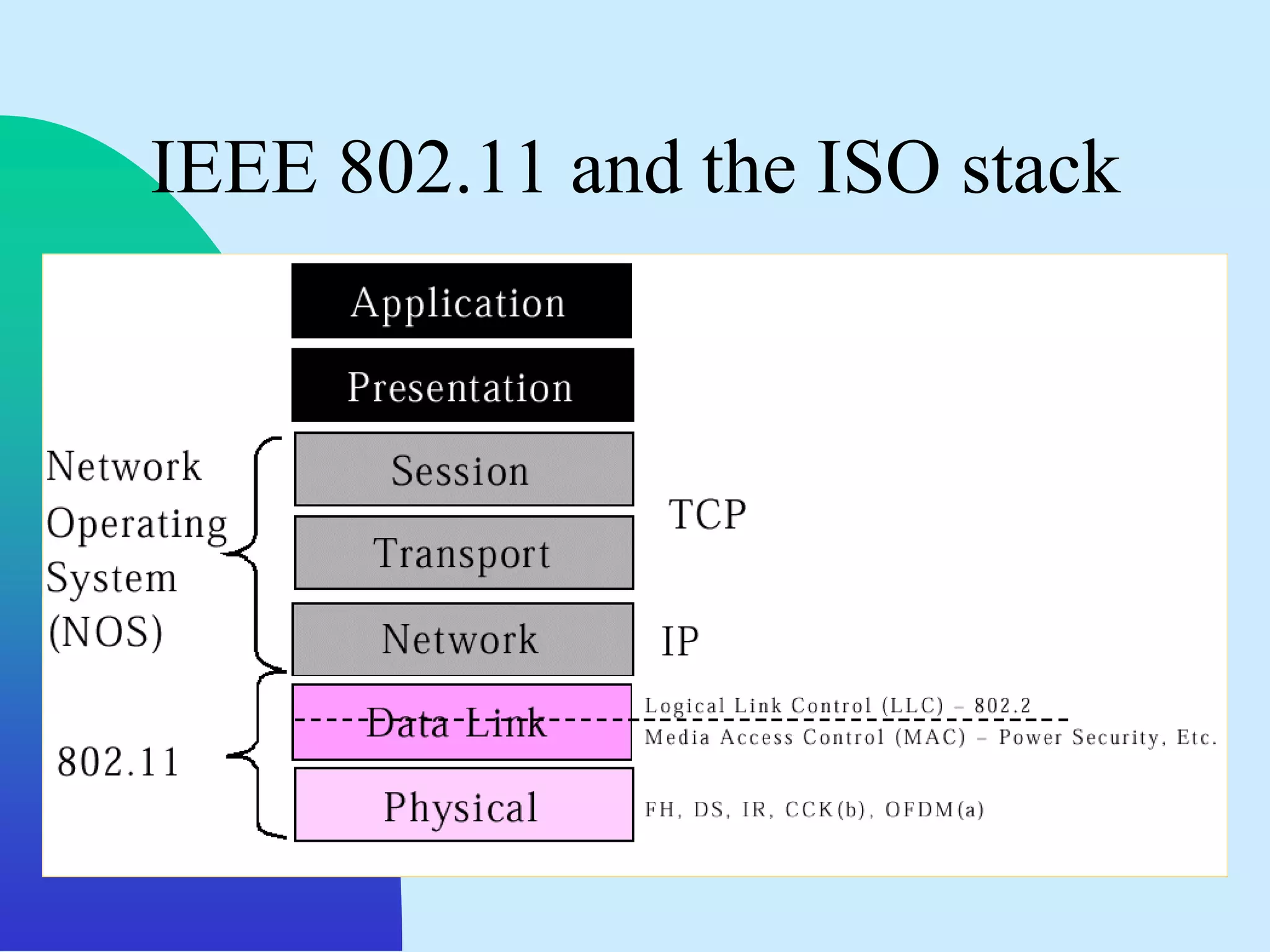
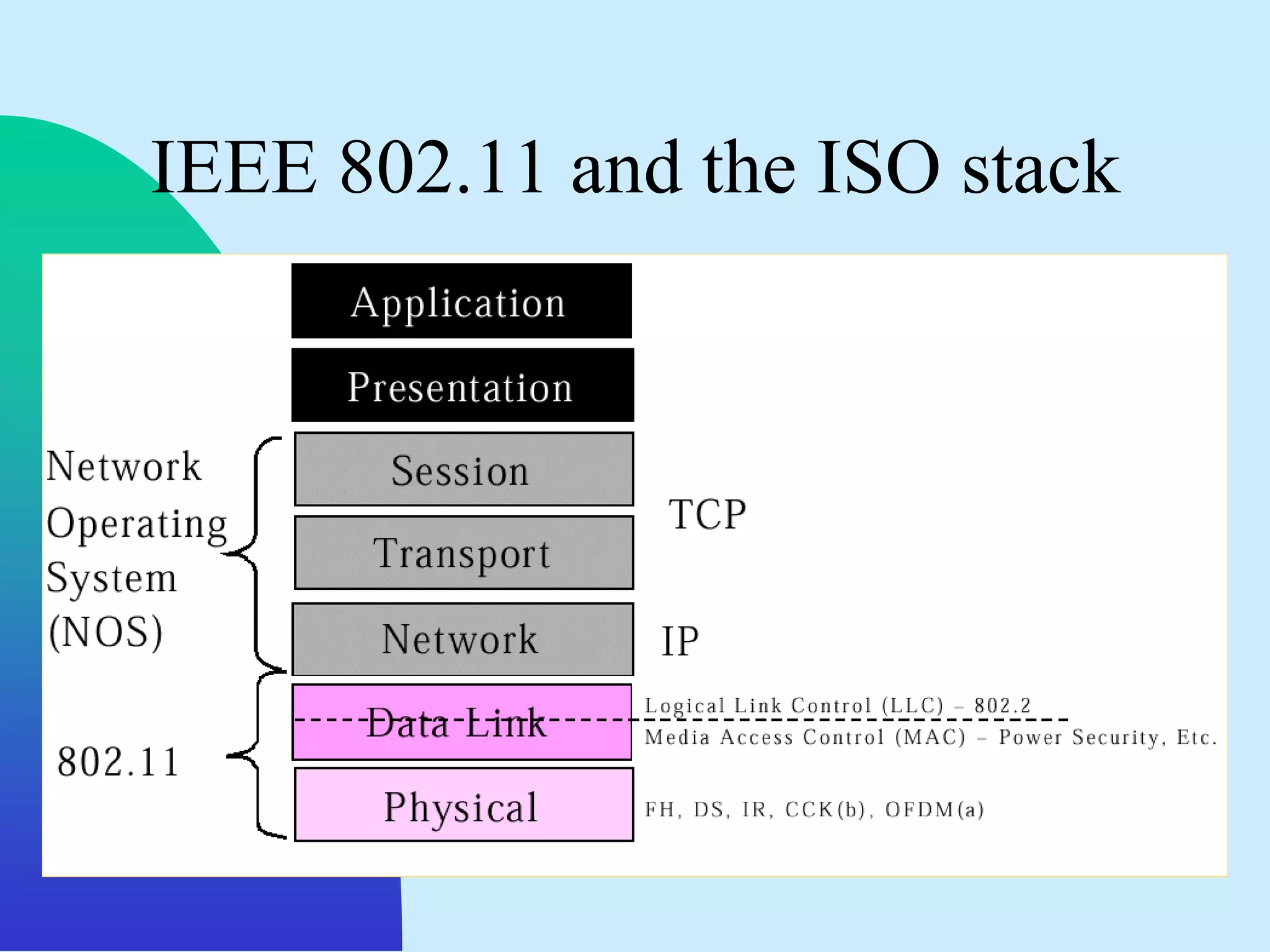
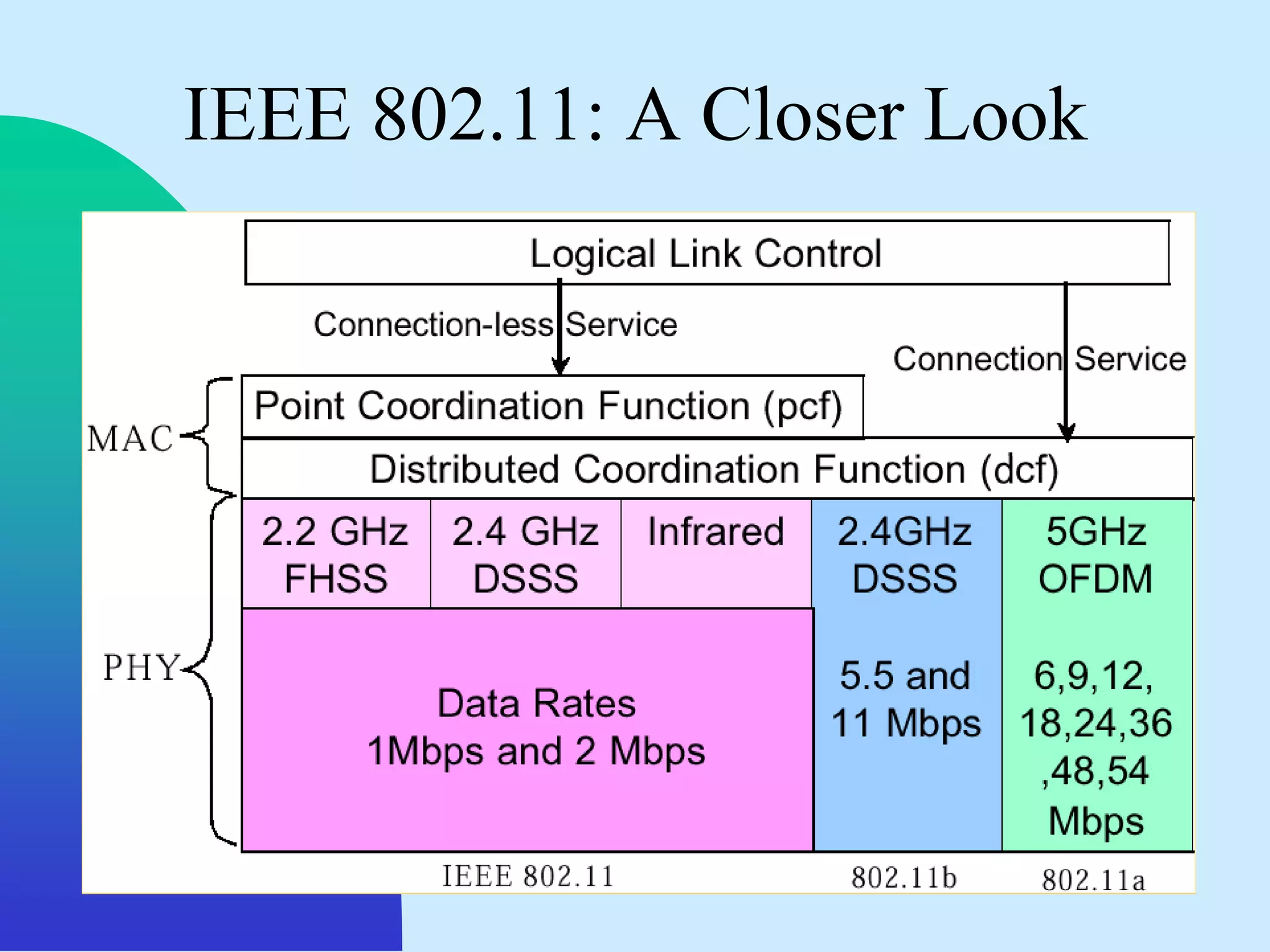
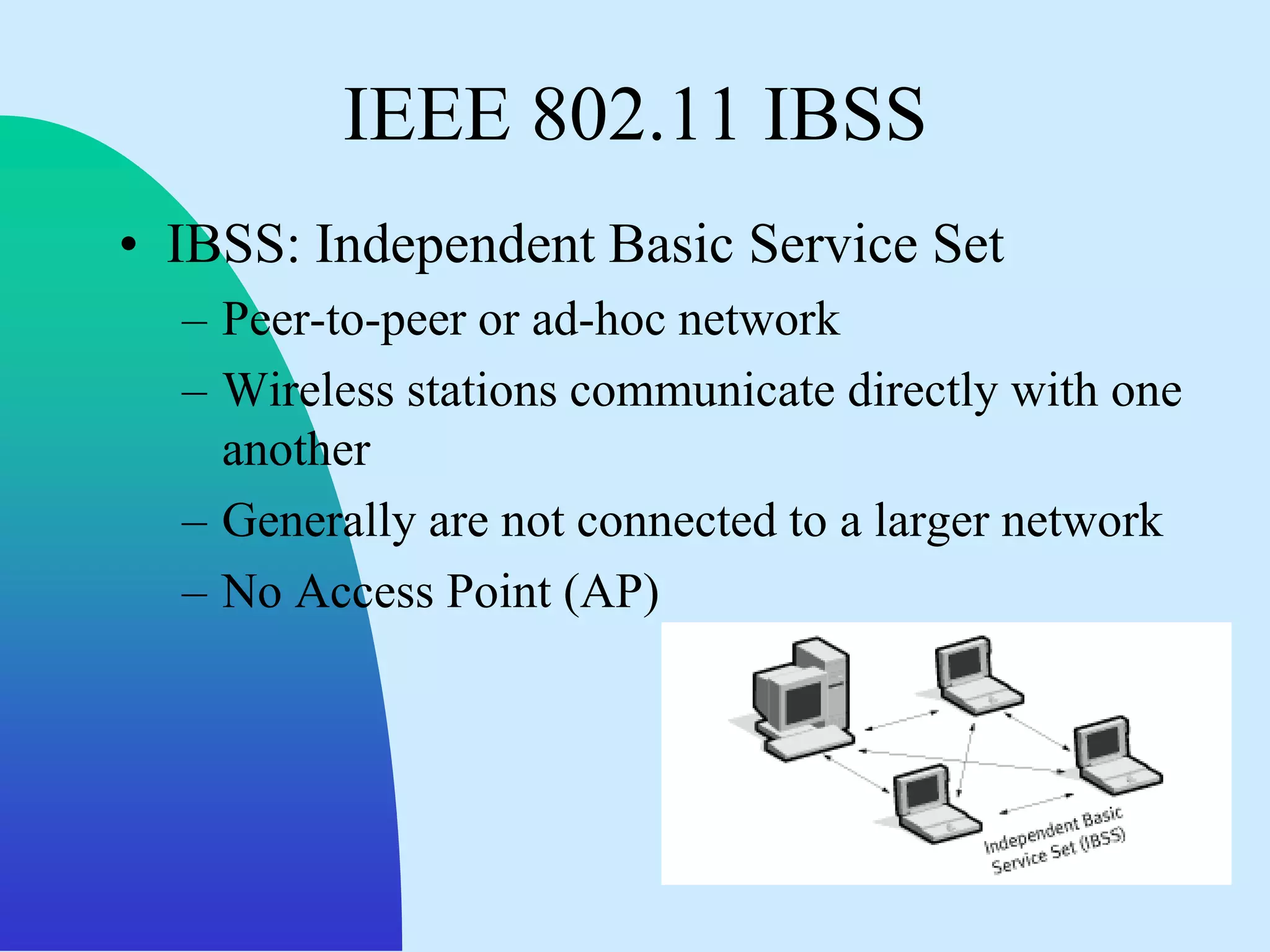
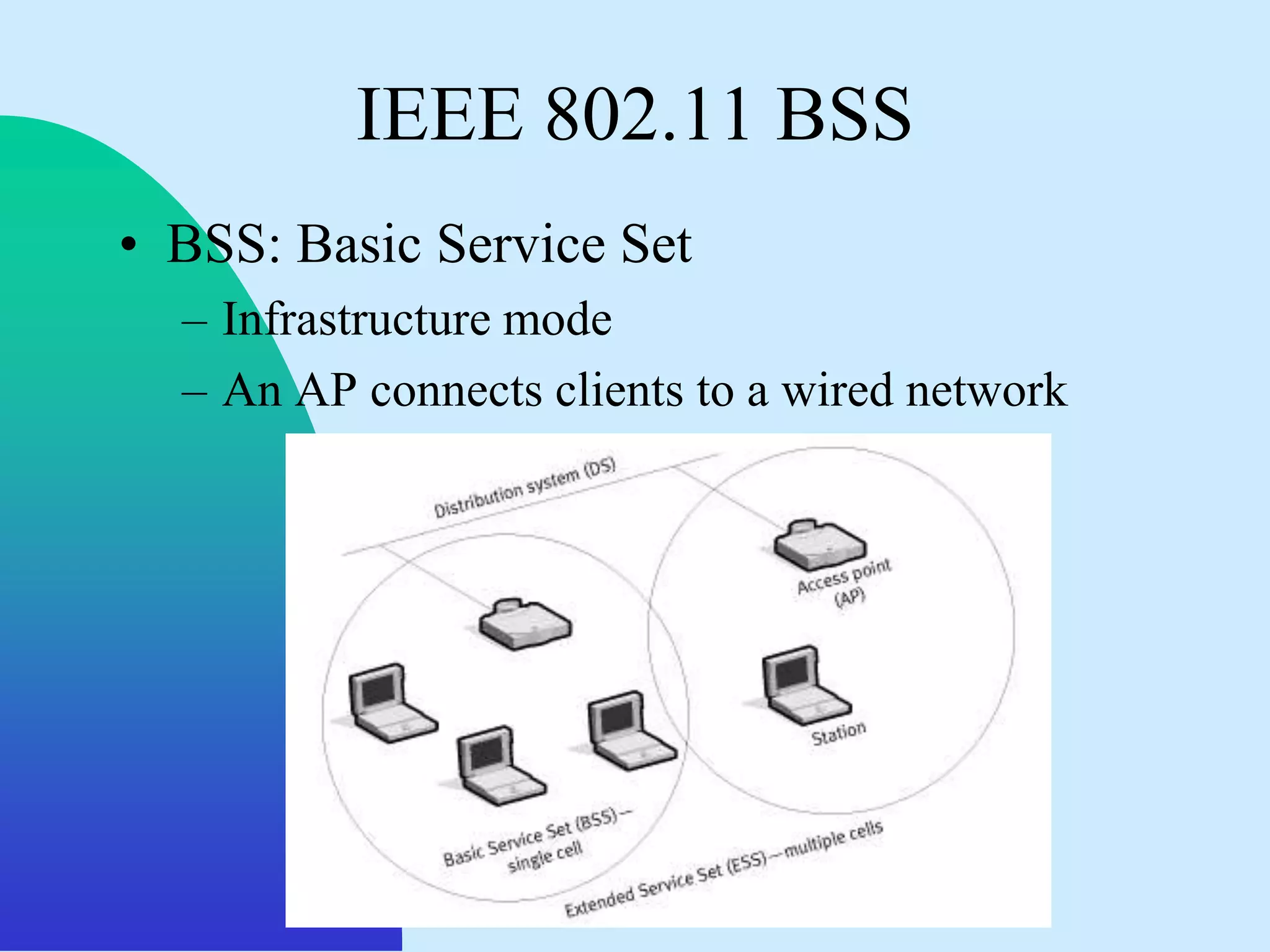
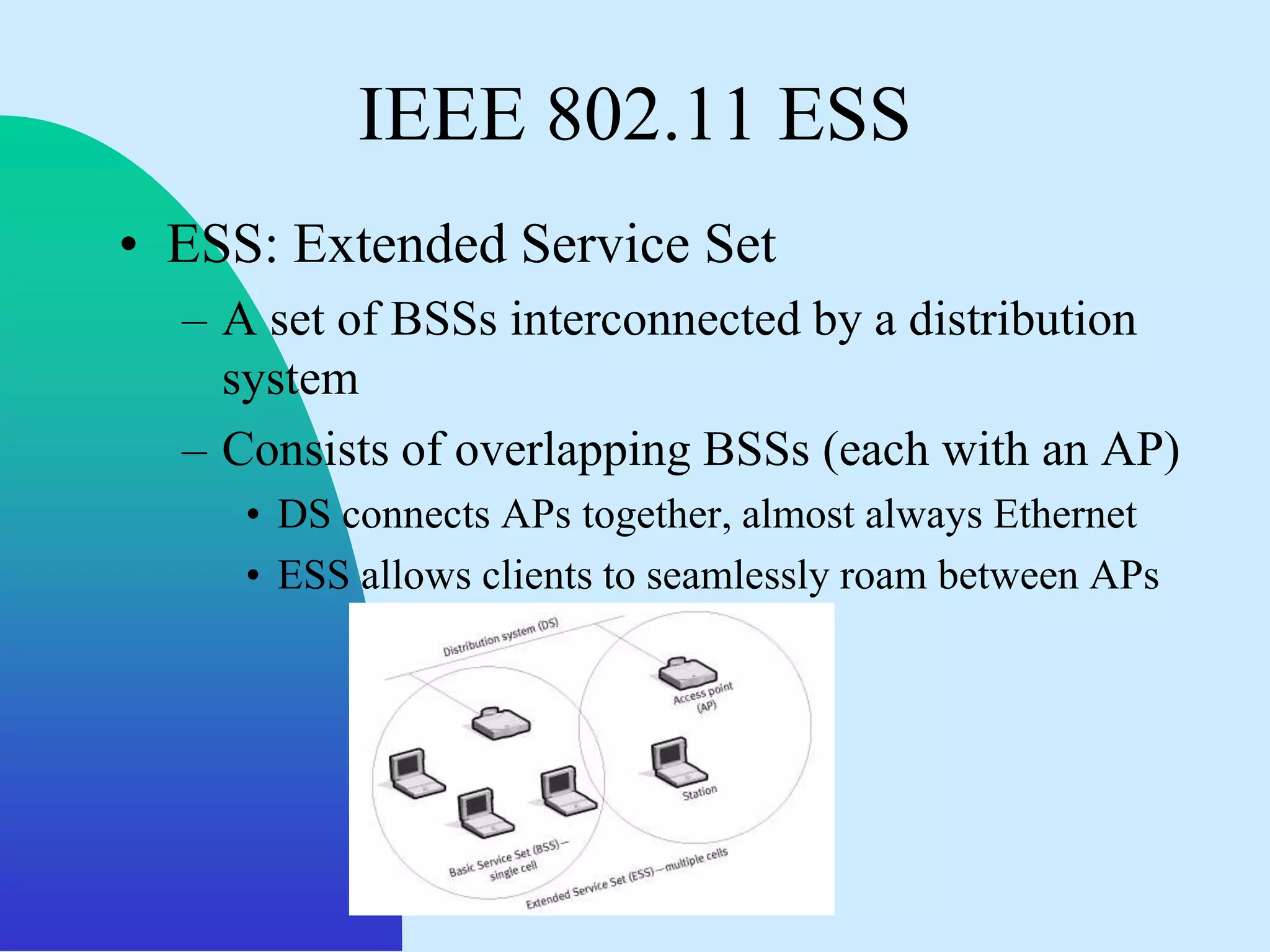
The document discusses wireless local area networks (WLANs) and the IEEE 802.11 standards. It describes some of the challenges of wireless transmissions and provides an overview of the IEEE 802.11 standards including 802.11, 802.11a, 802.11b, 802.11e, and 802.11g. It also summarizes the IEEE 802.11 network architecture including the physical layer, data link layer, and different network topologies like IBSS, BSS, and ESS.