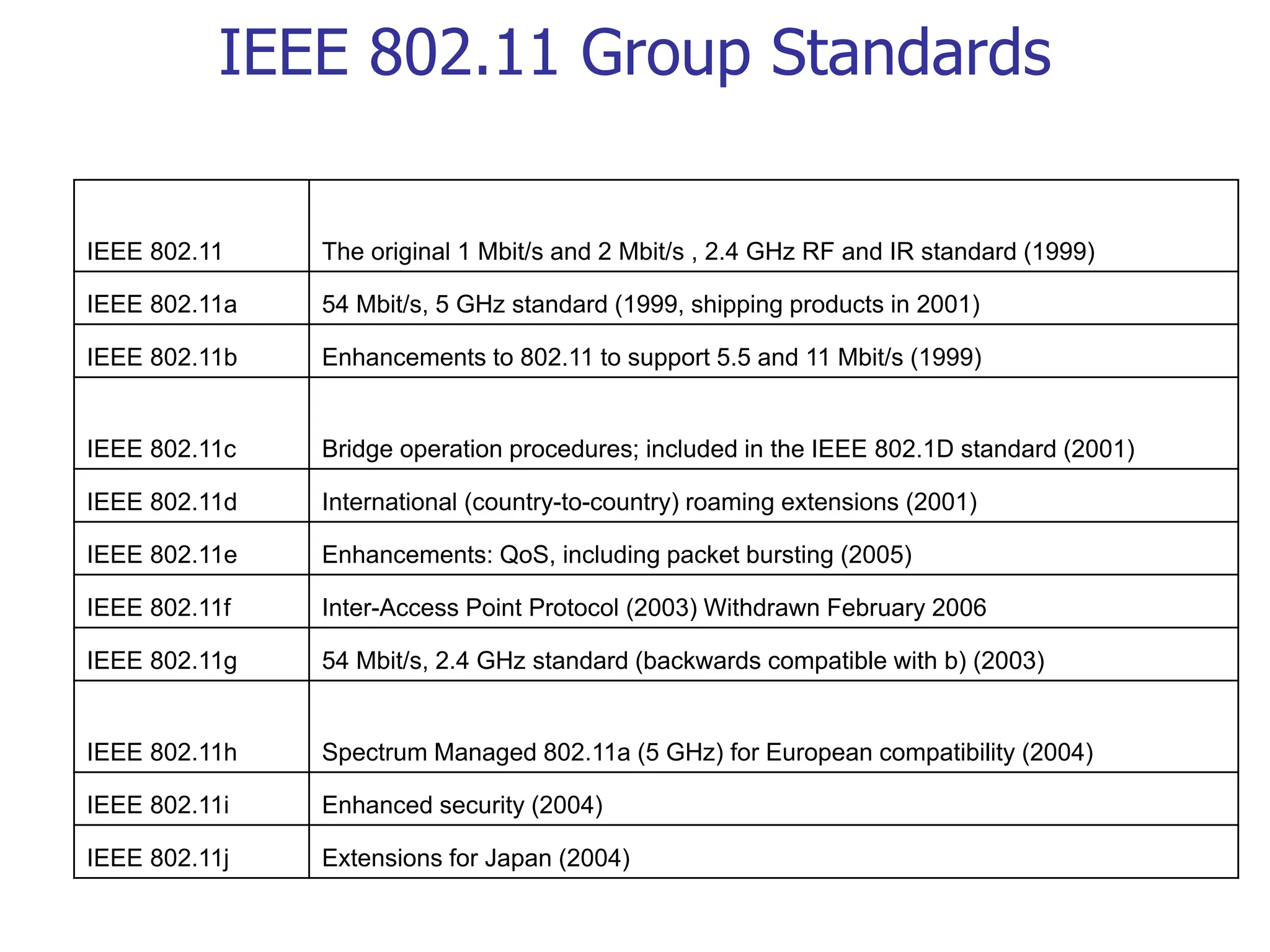
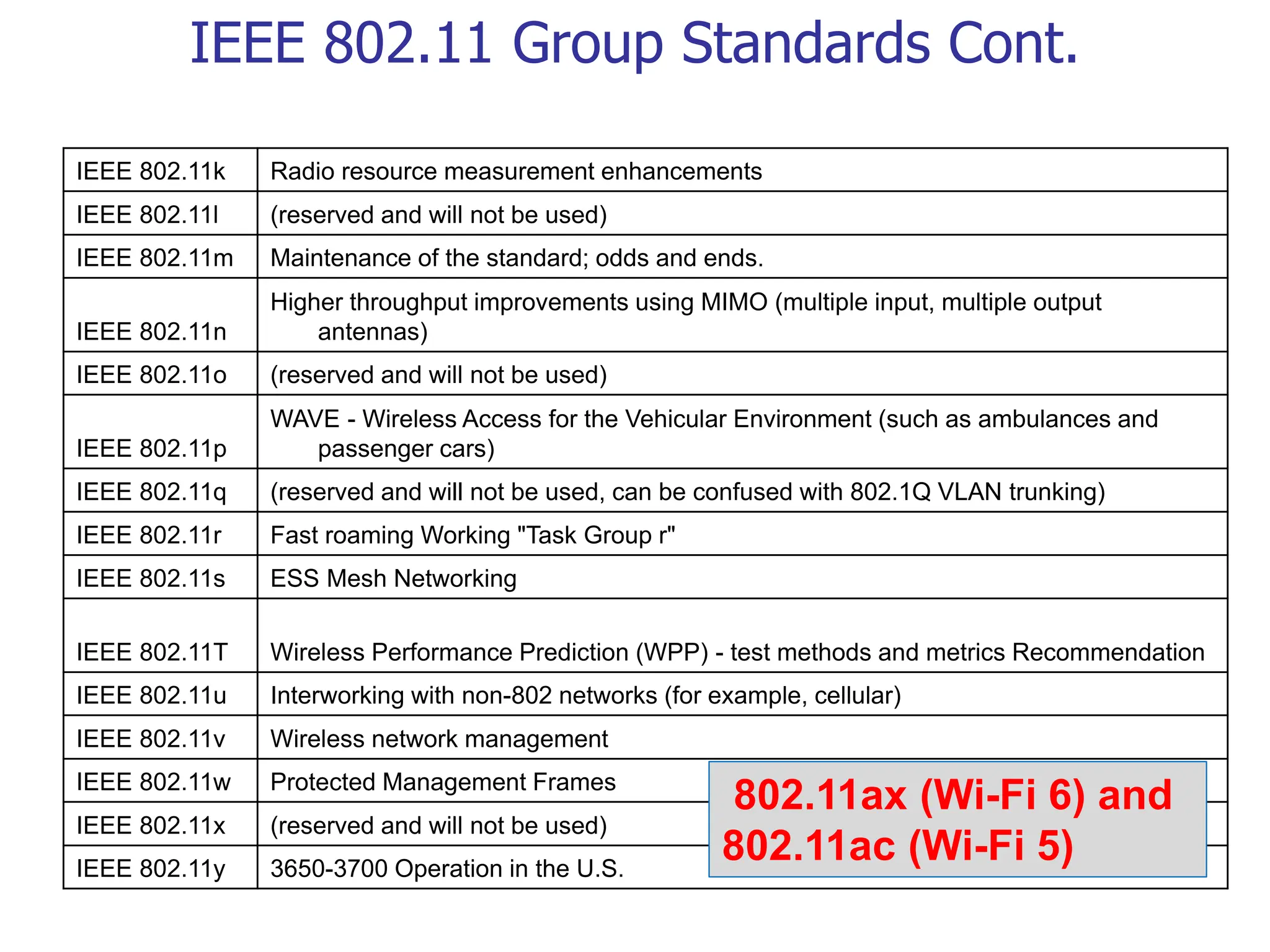
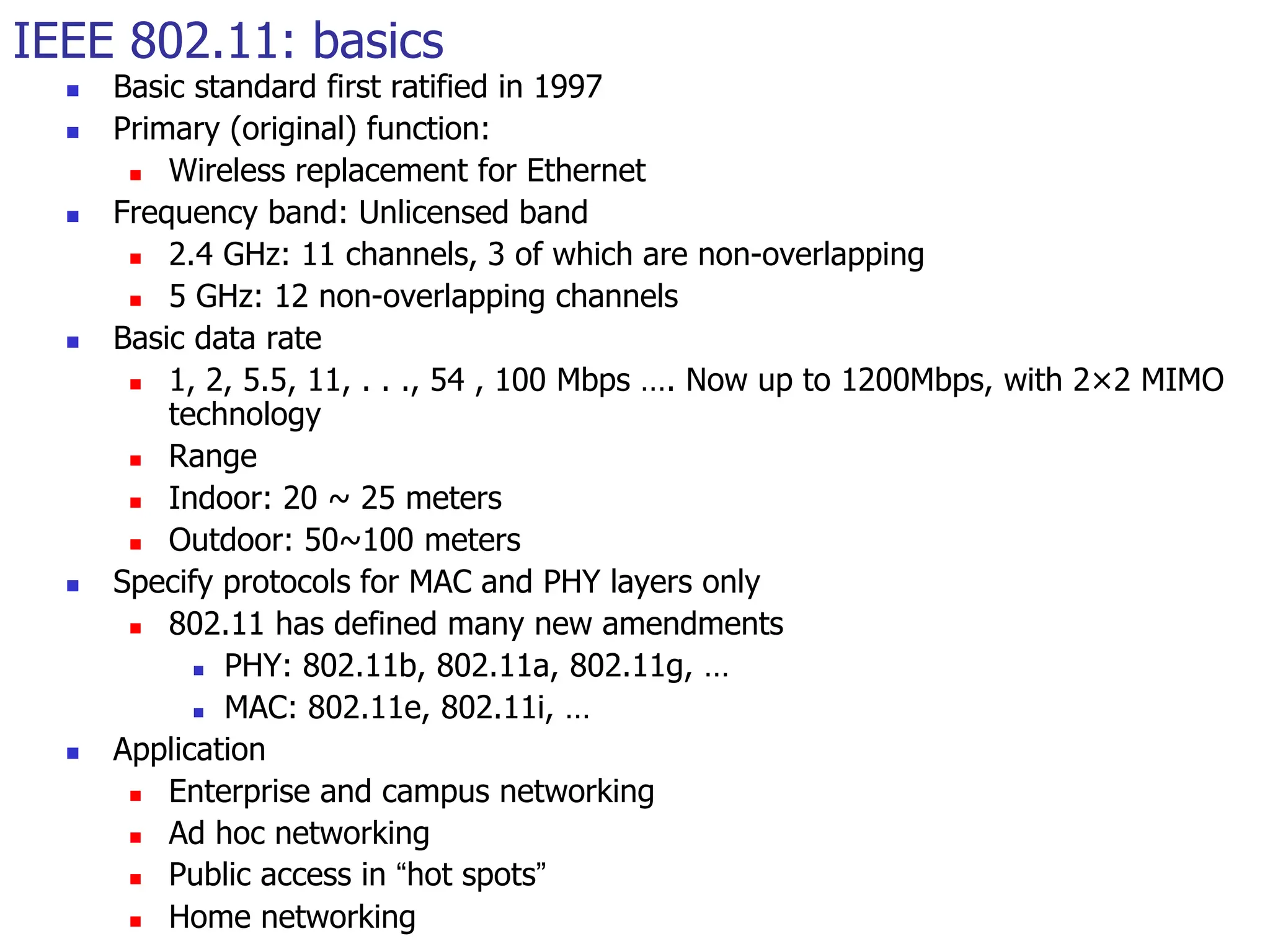
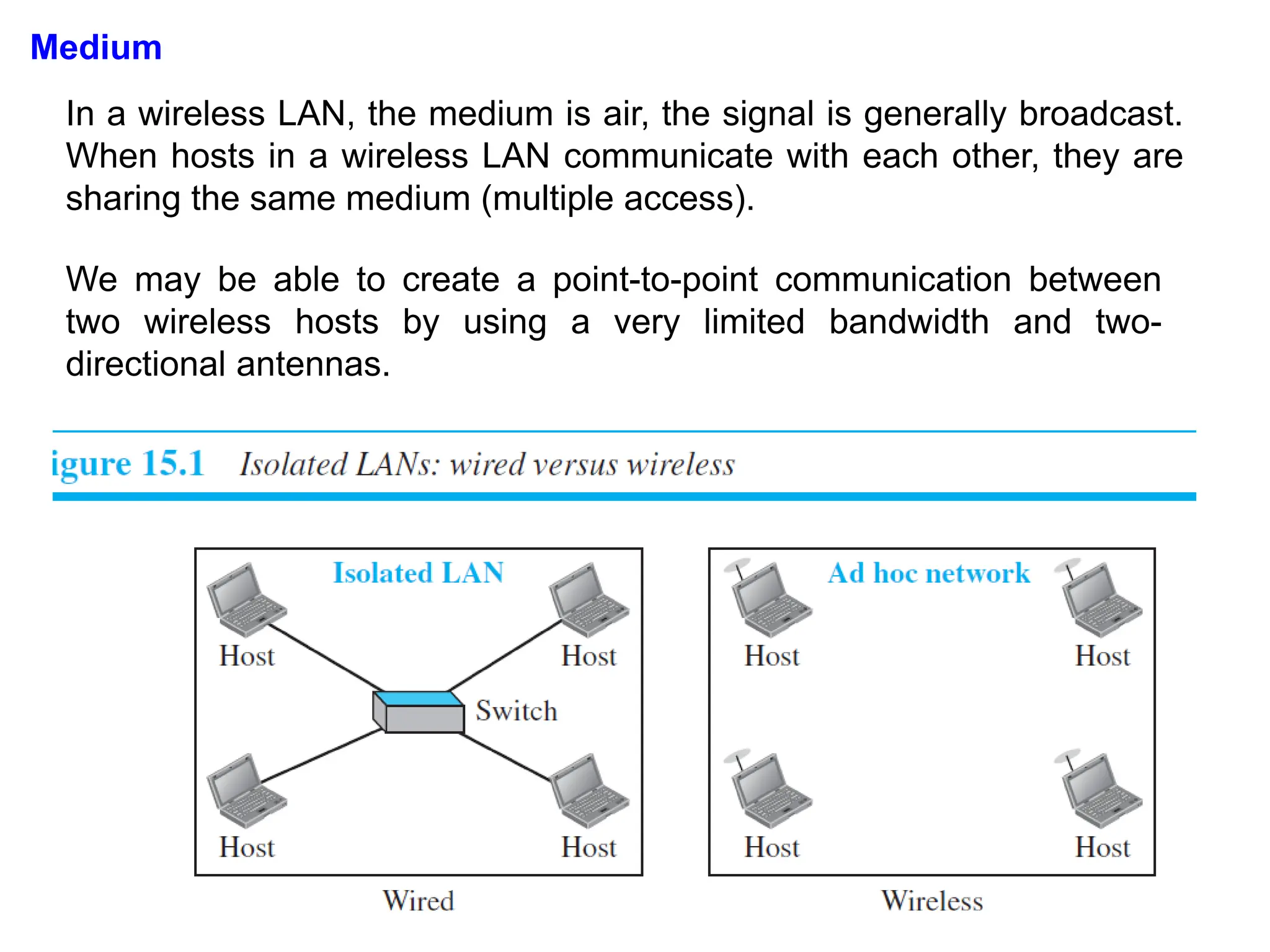
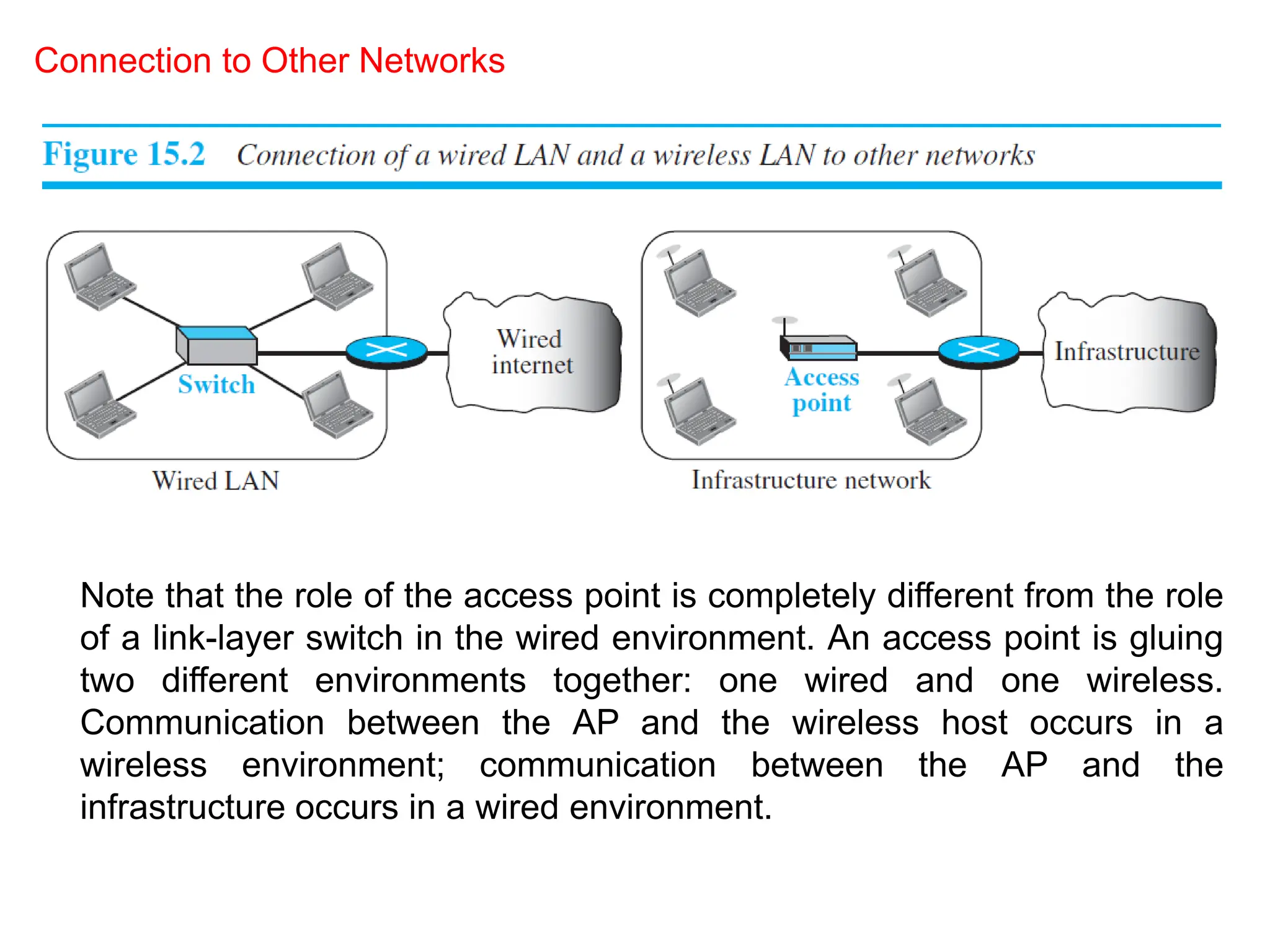
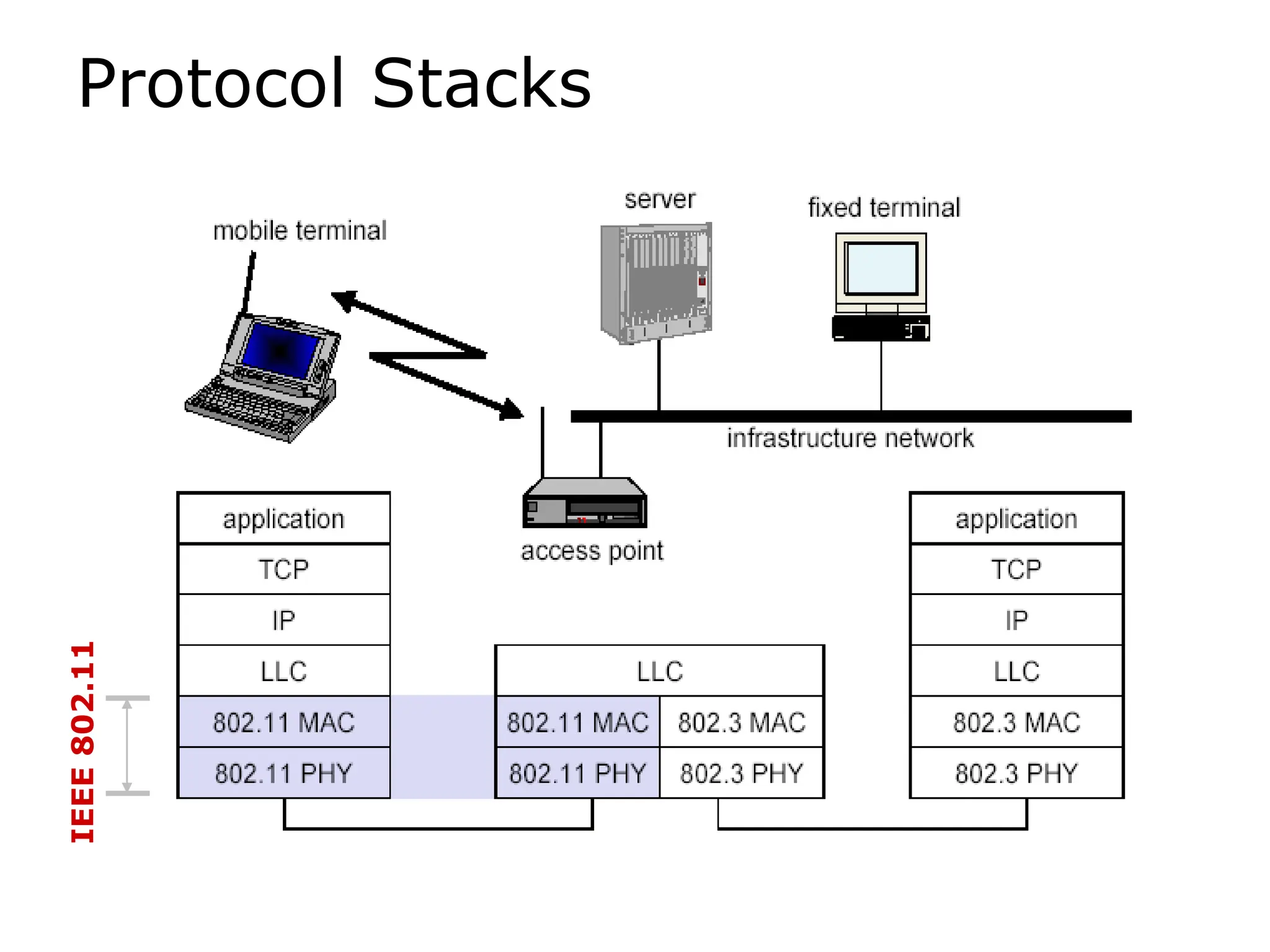
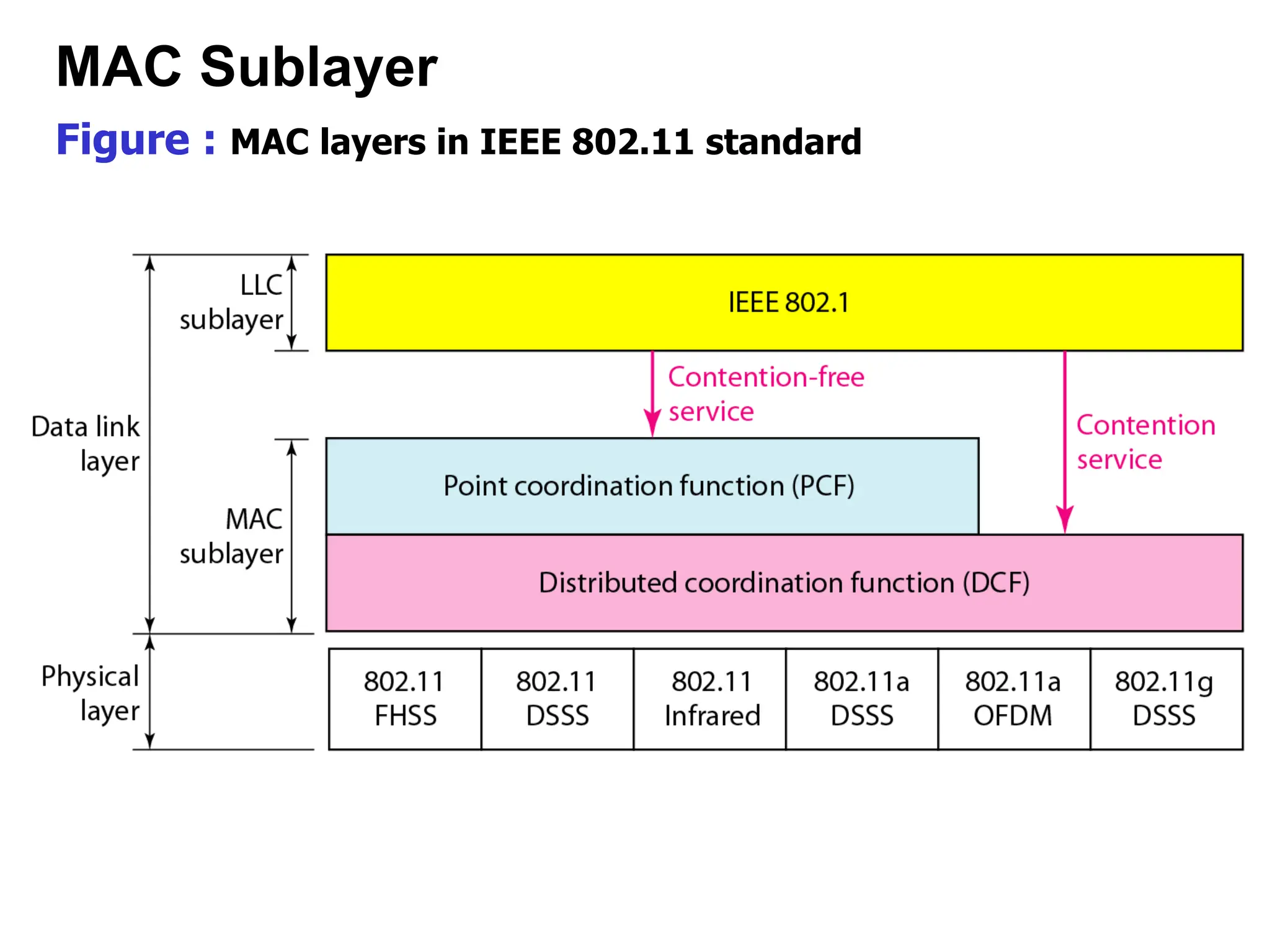
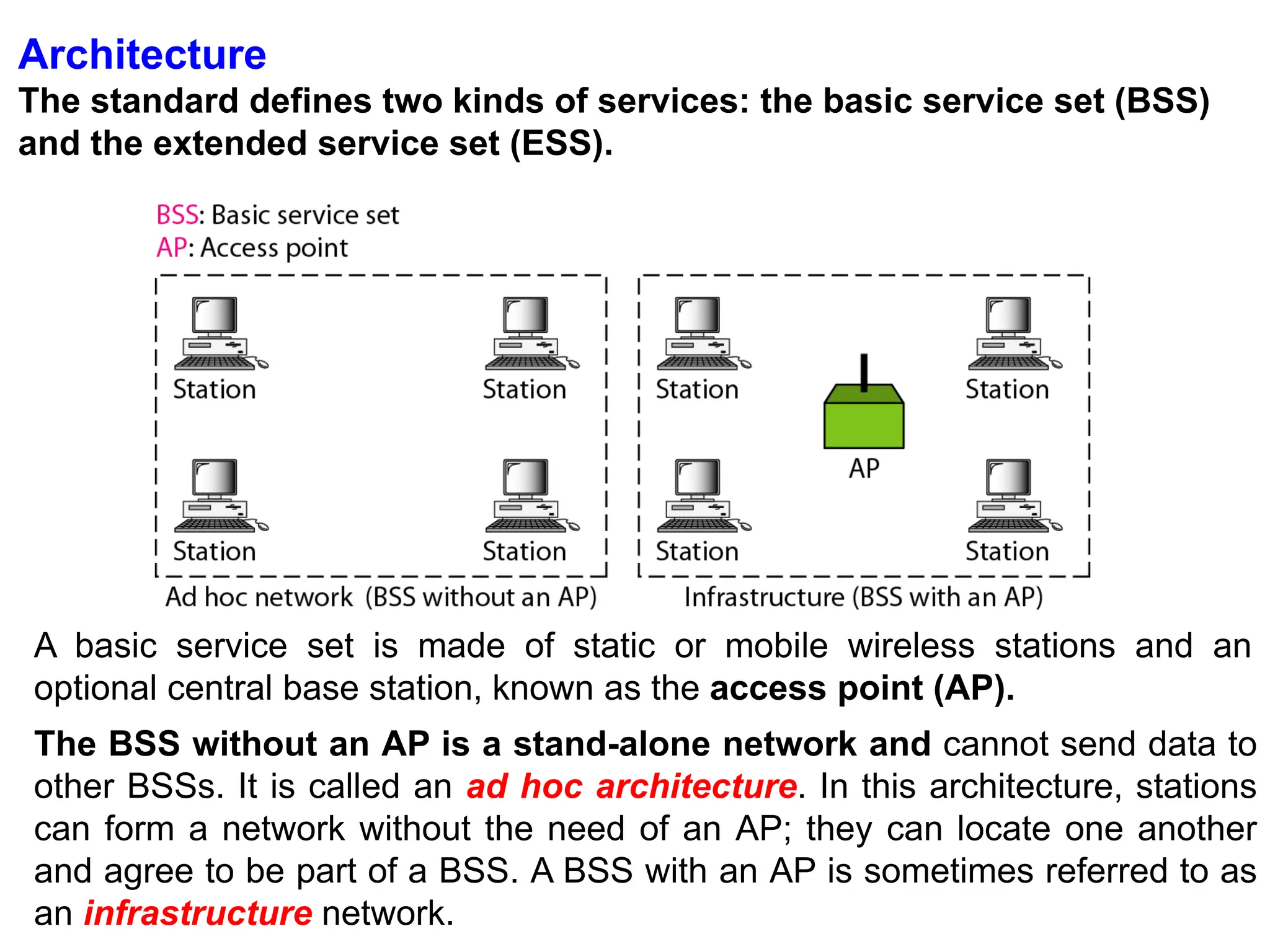
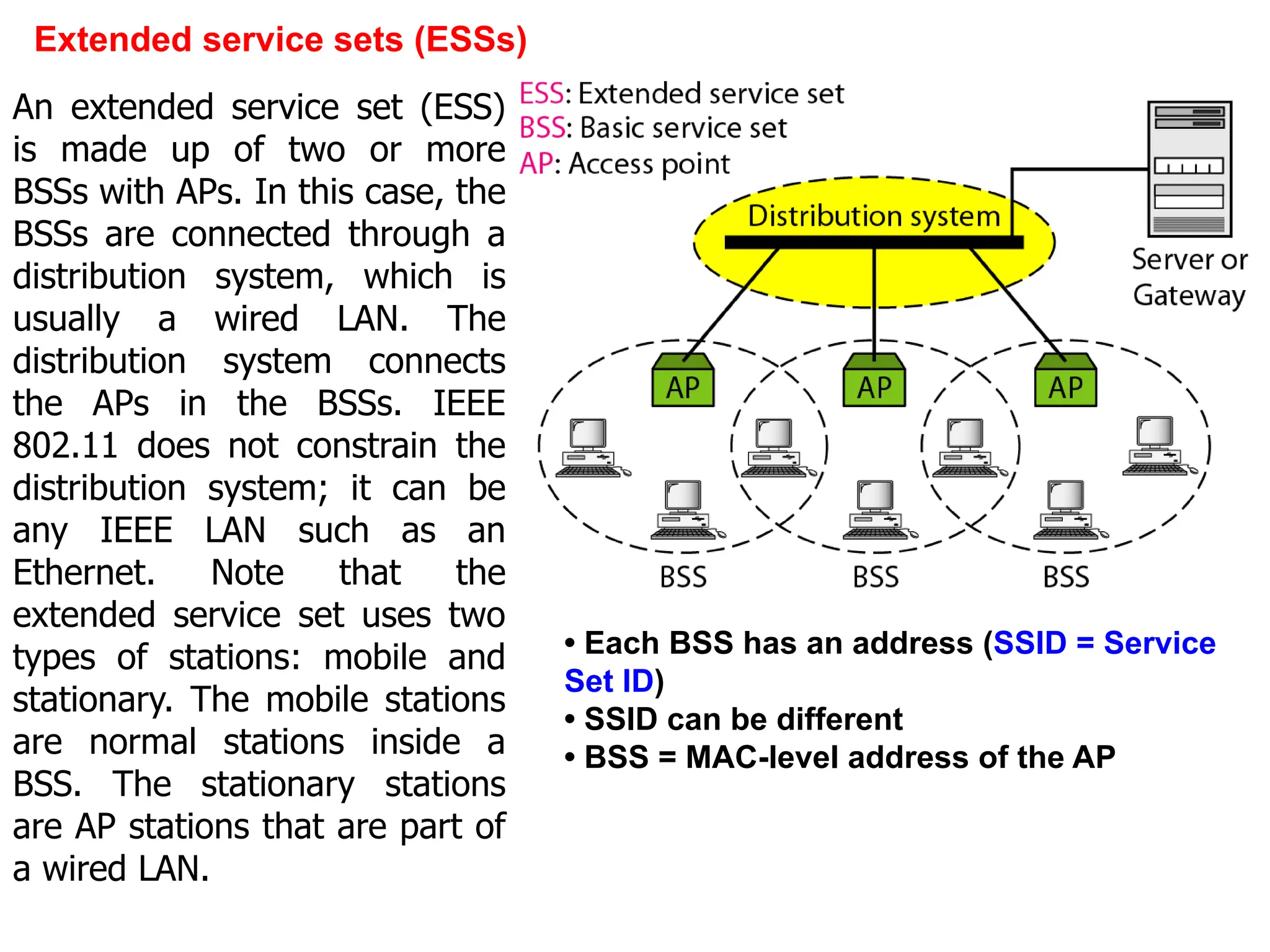
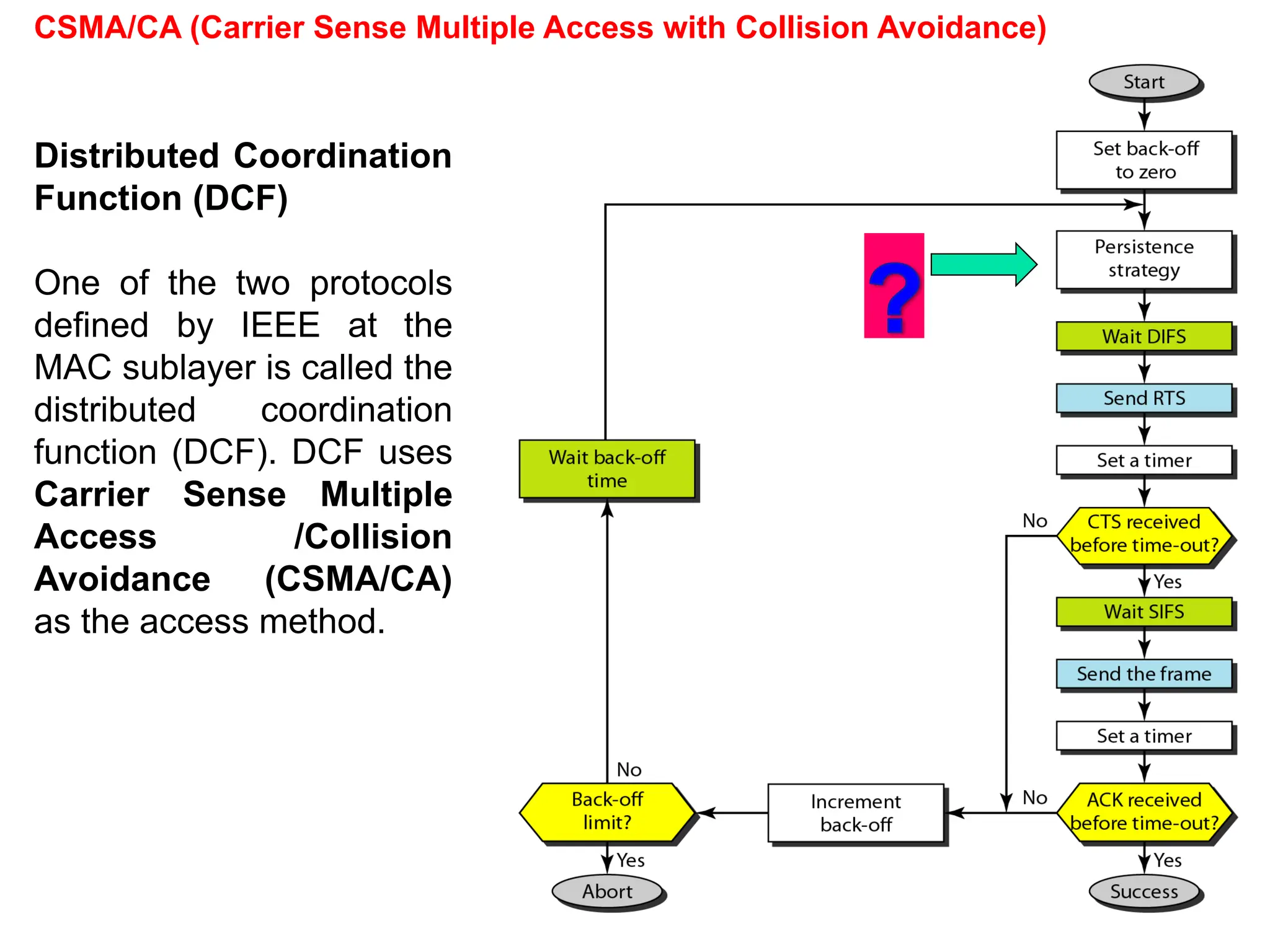
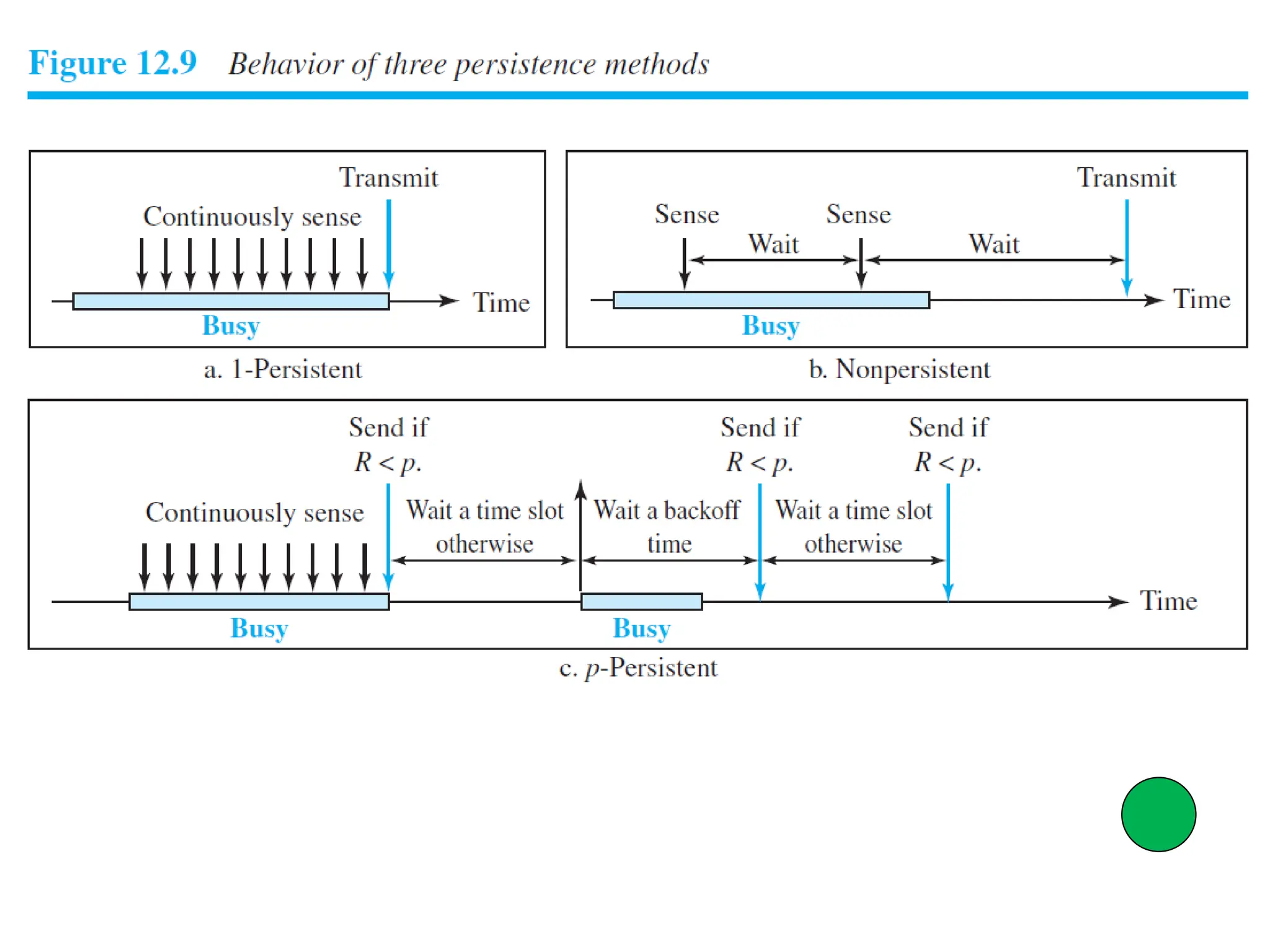
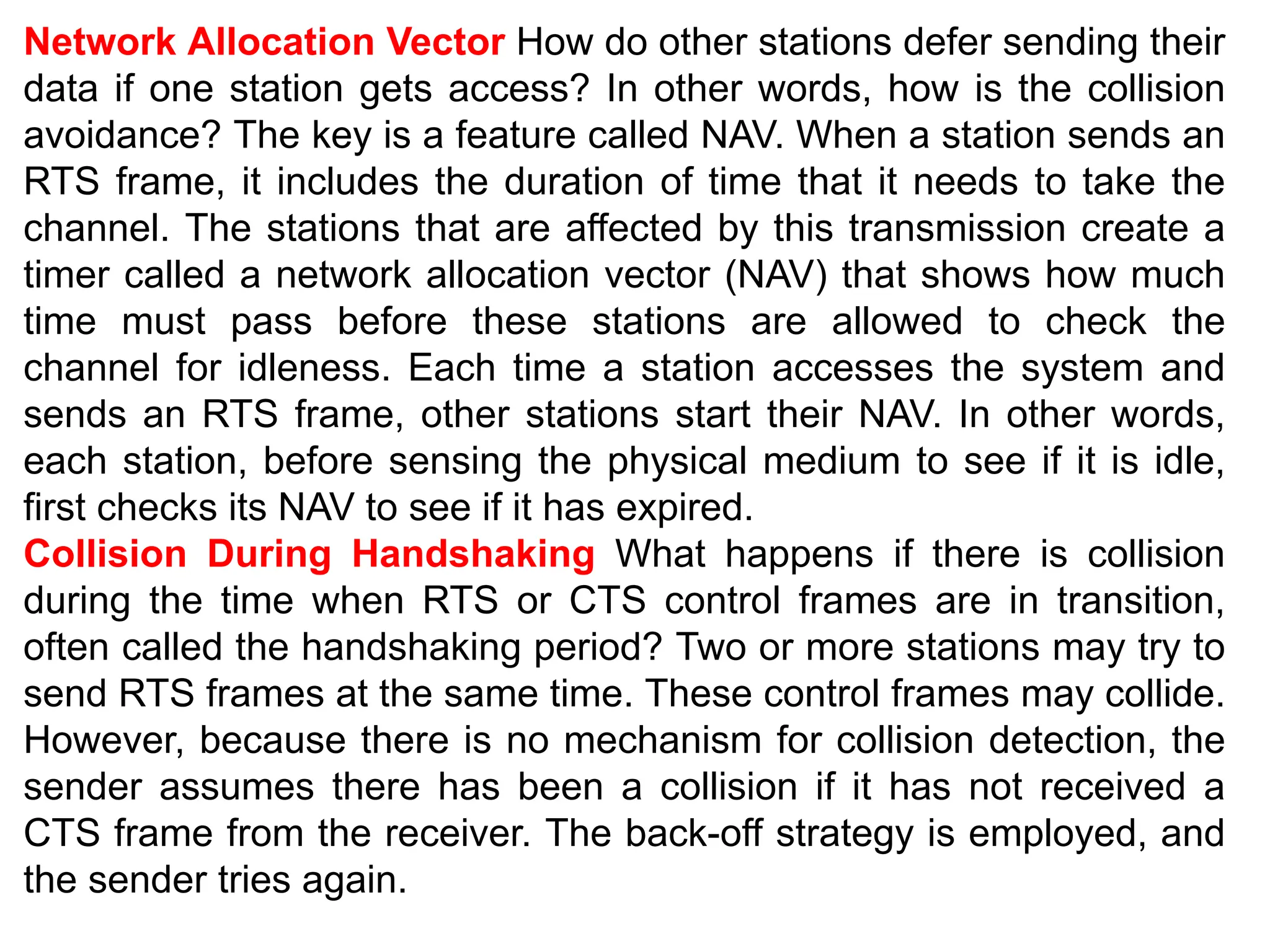
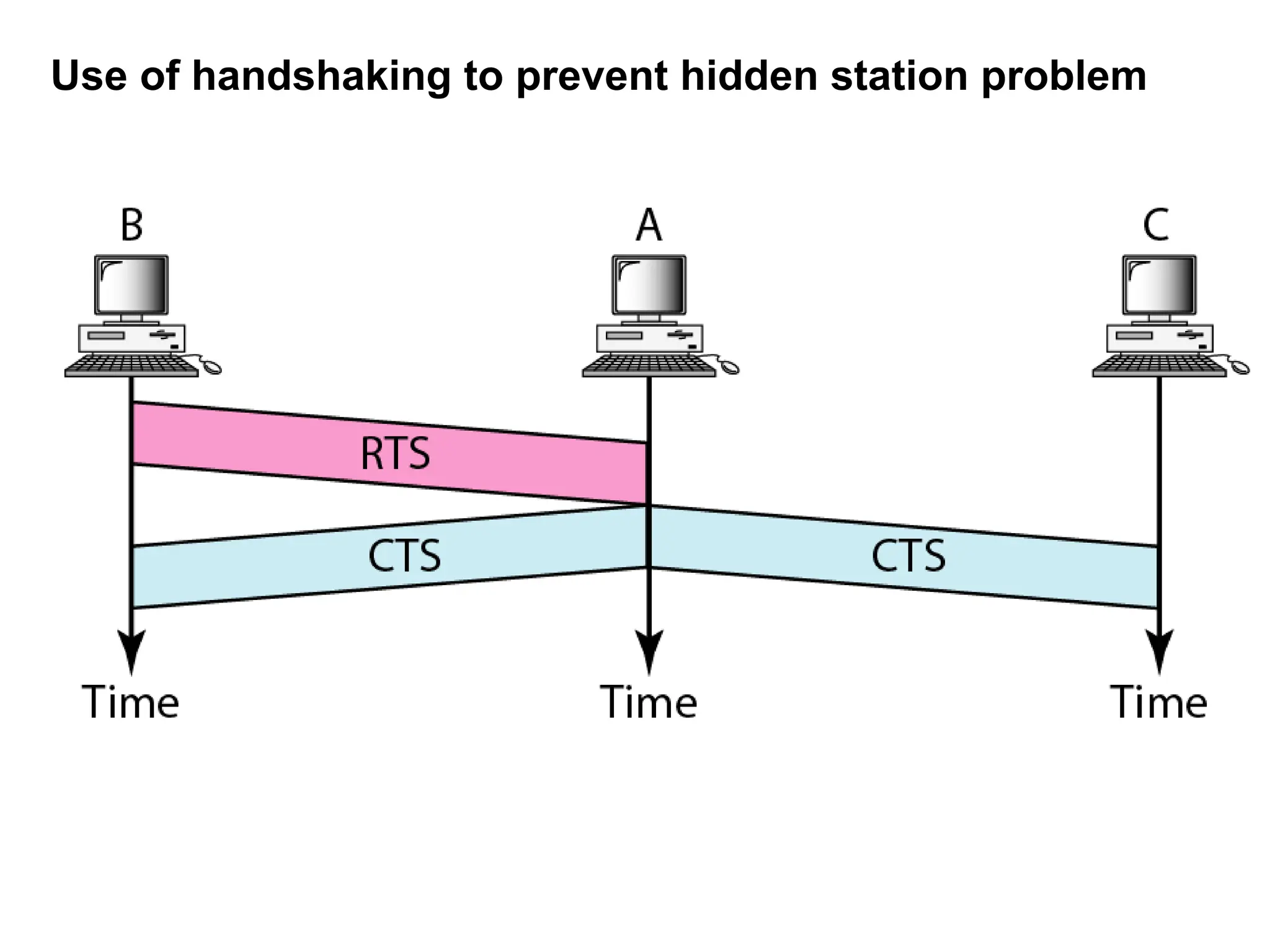
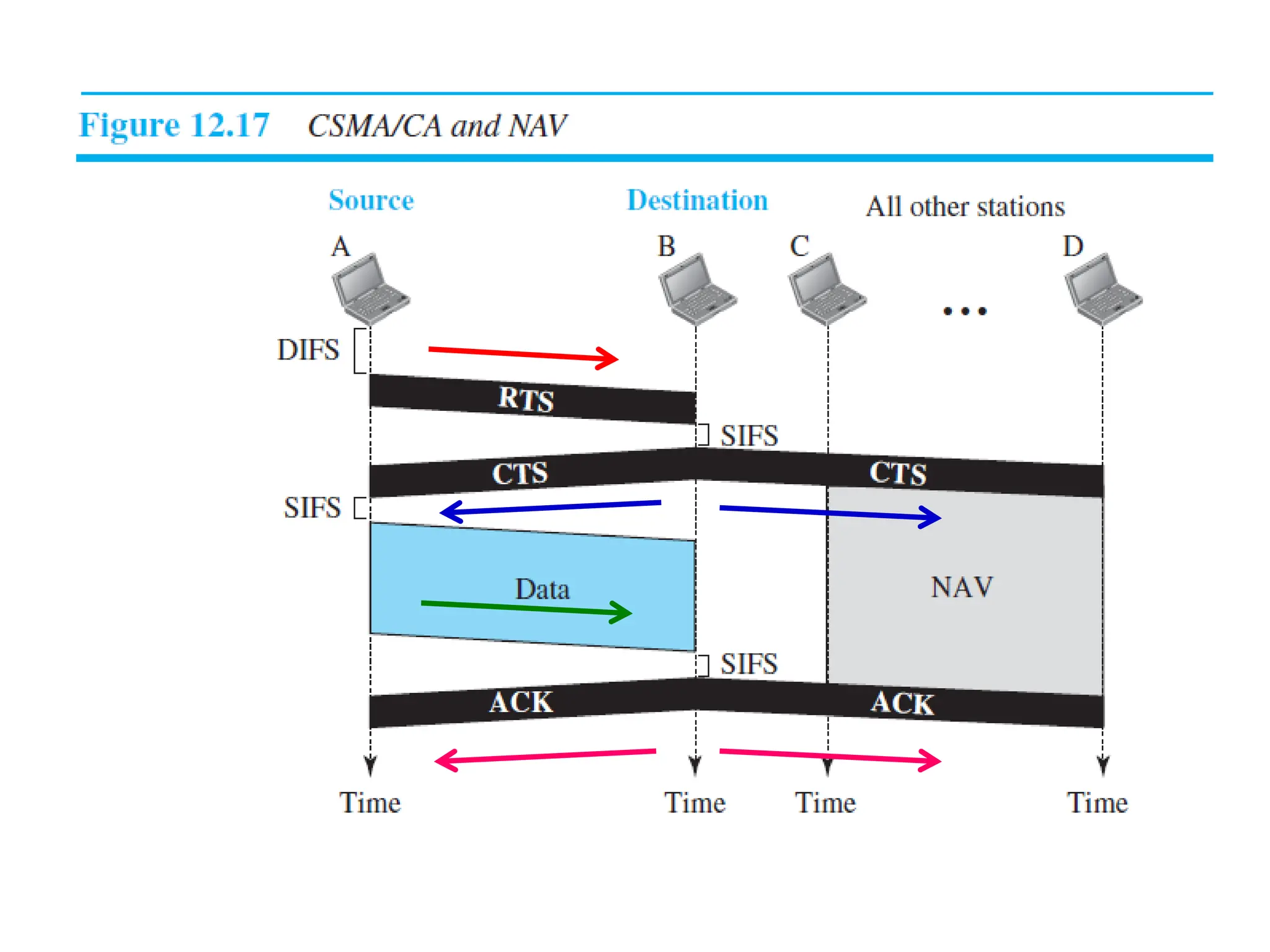
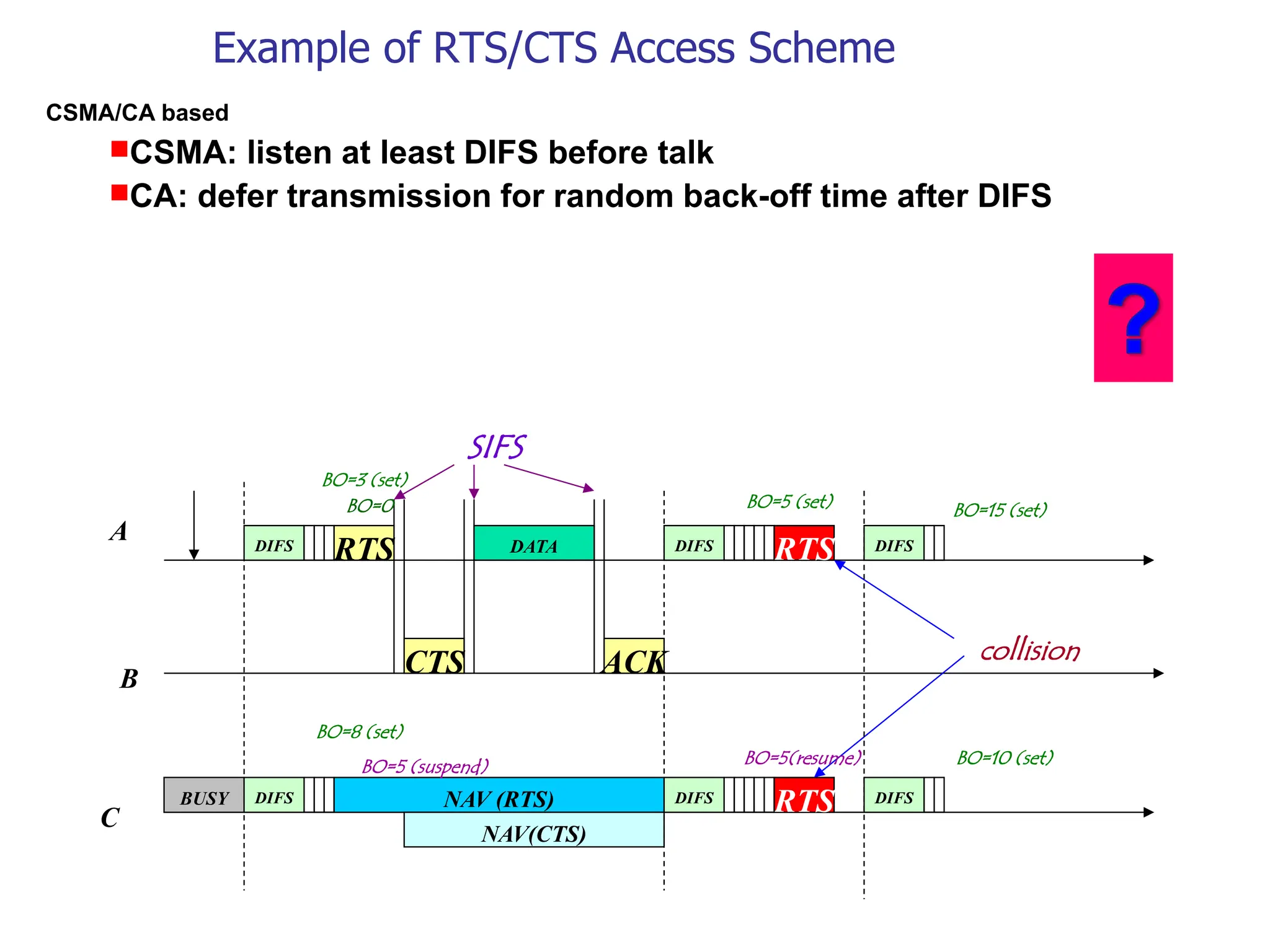
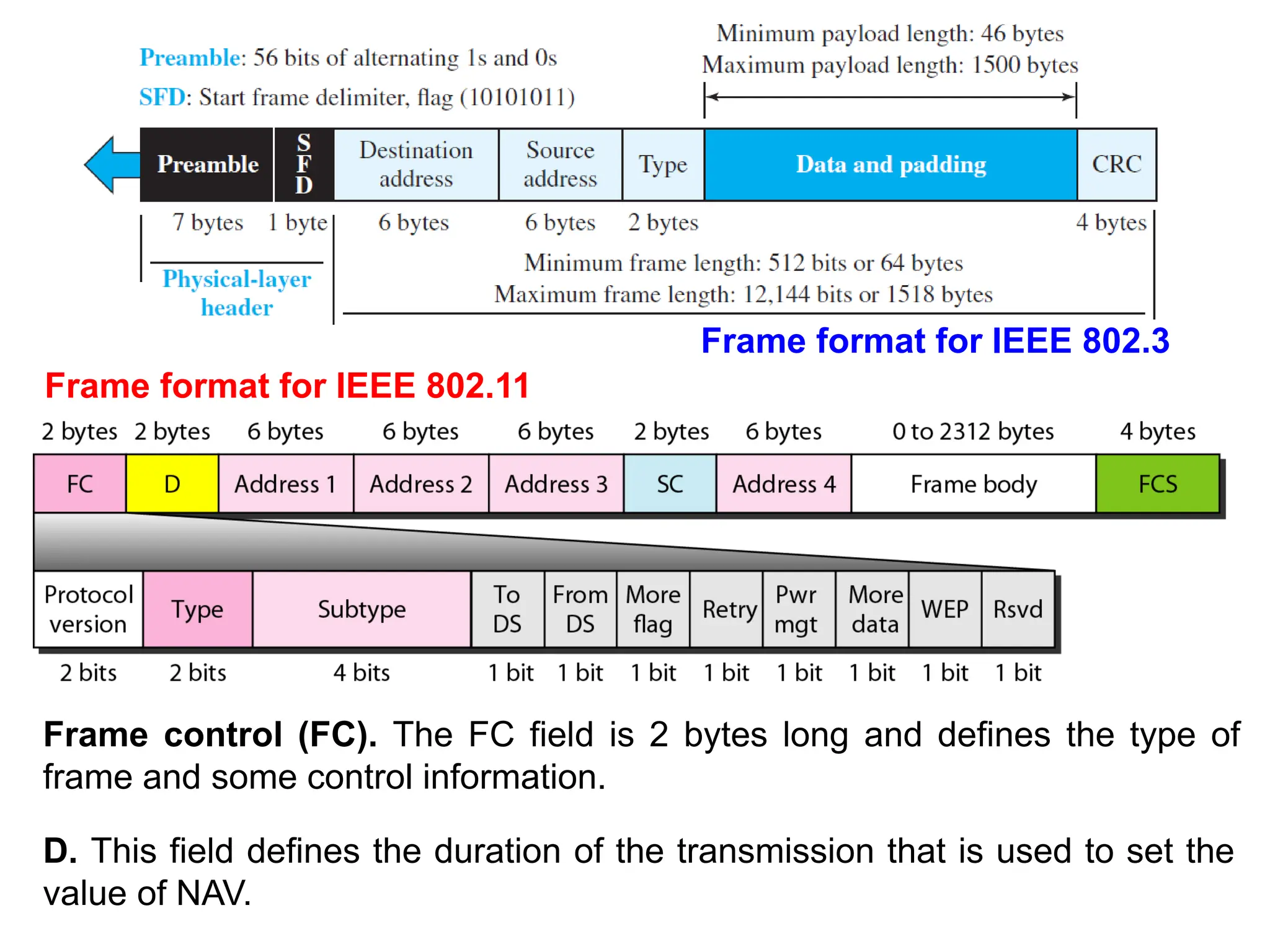
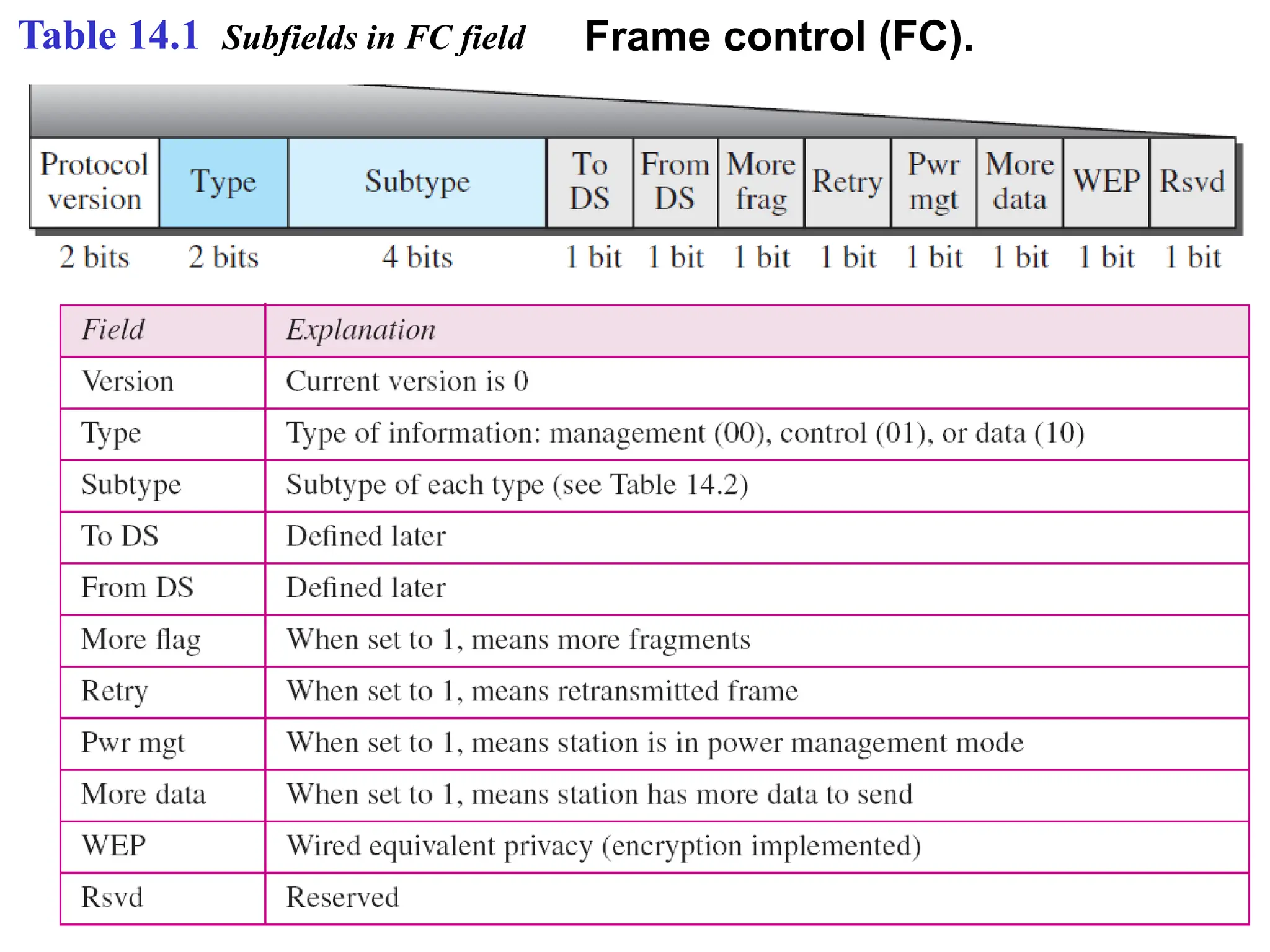
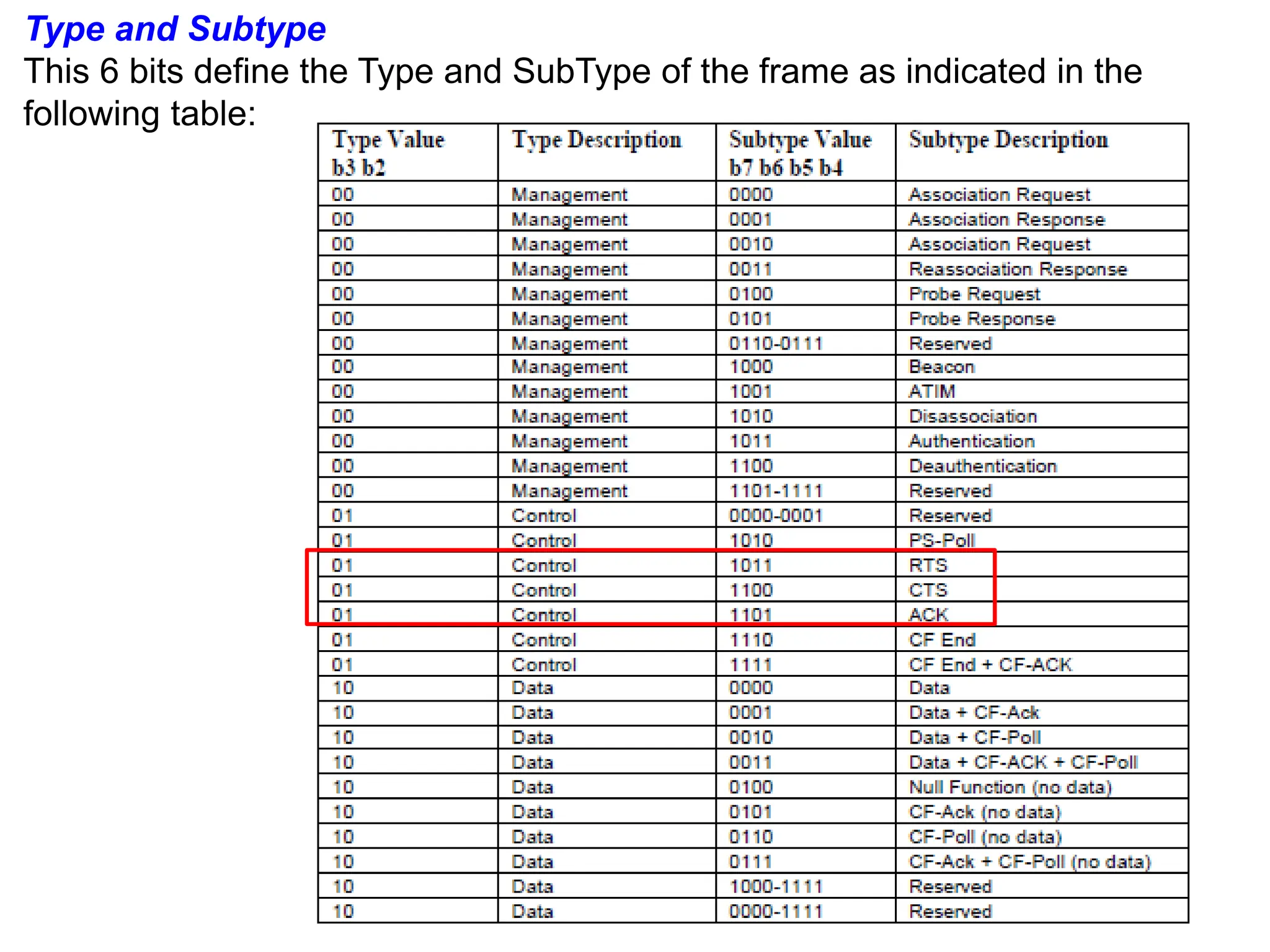
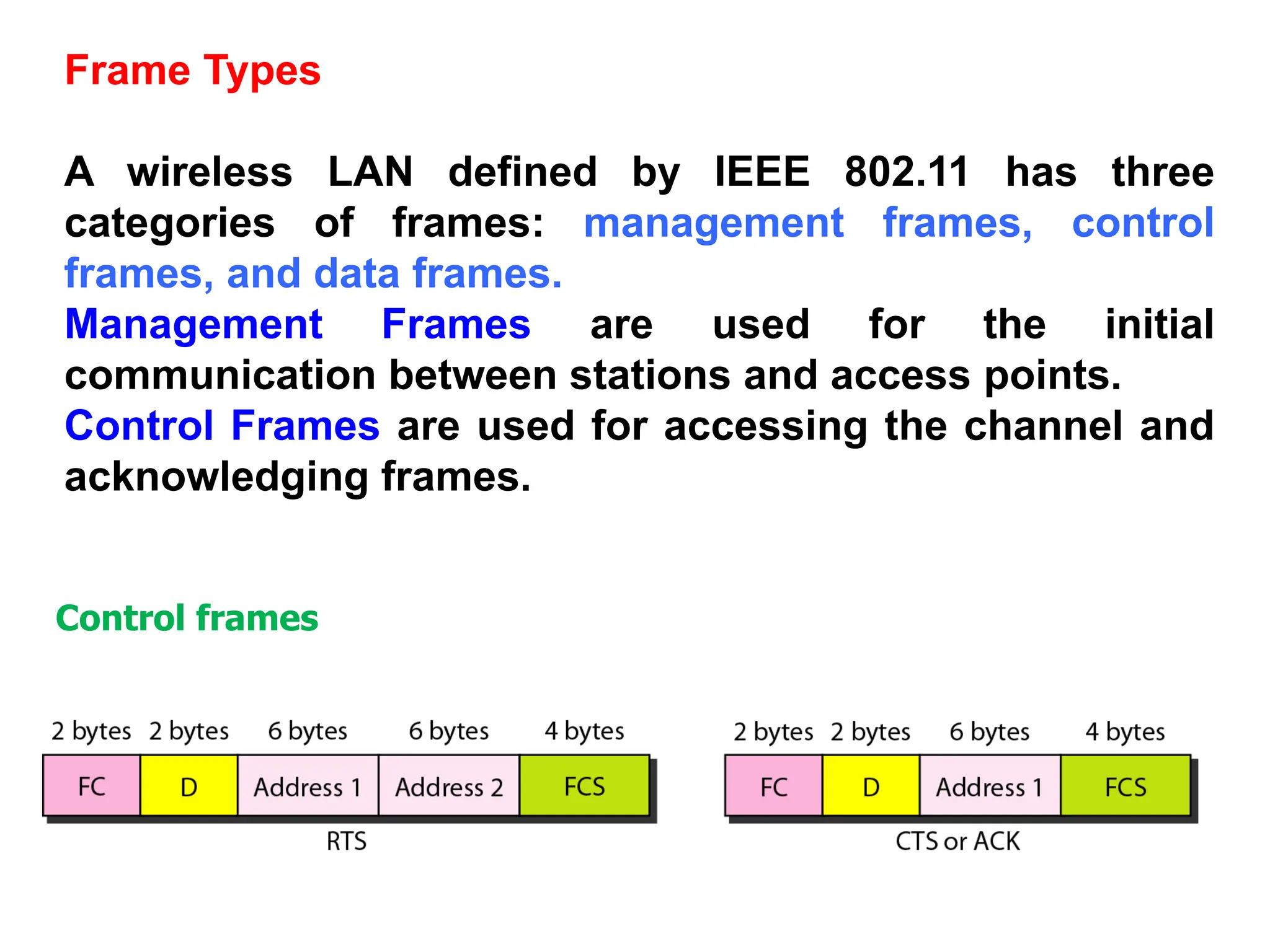
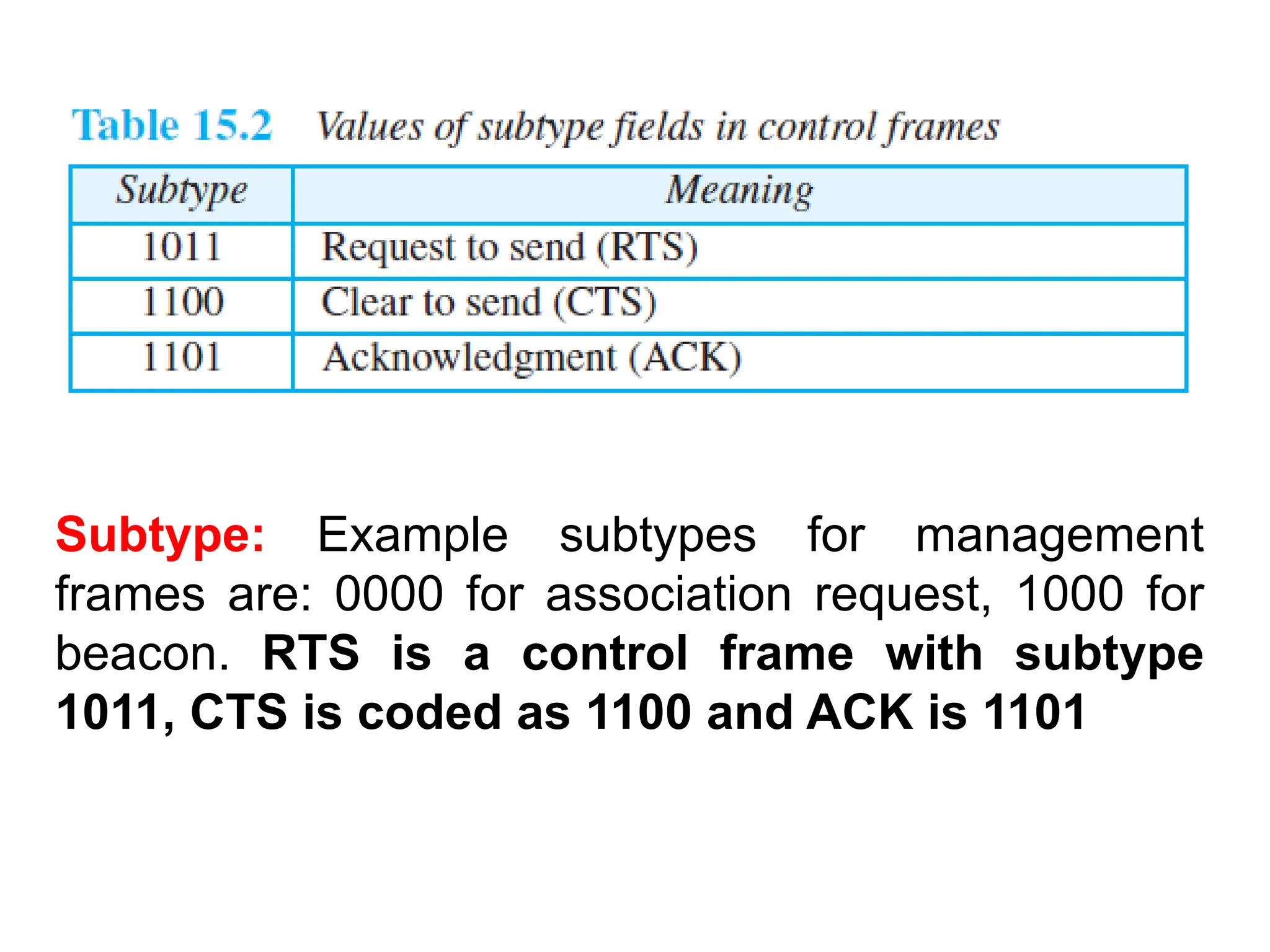
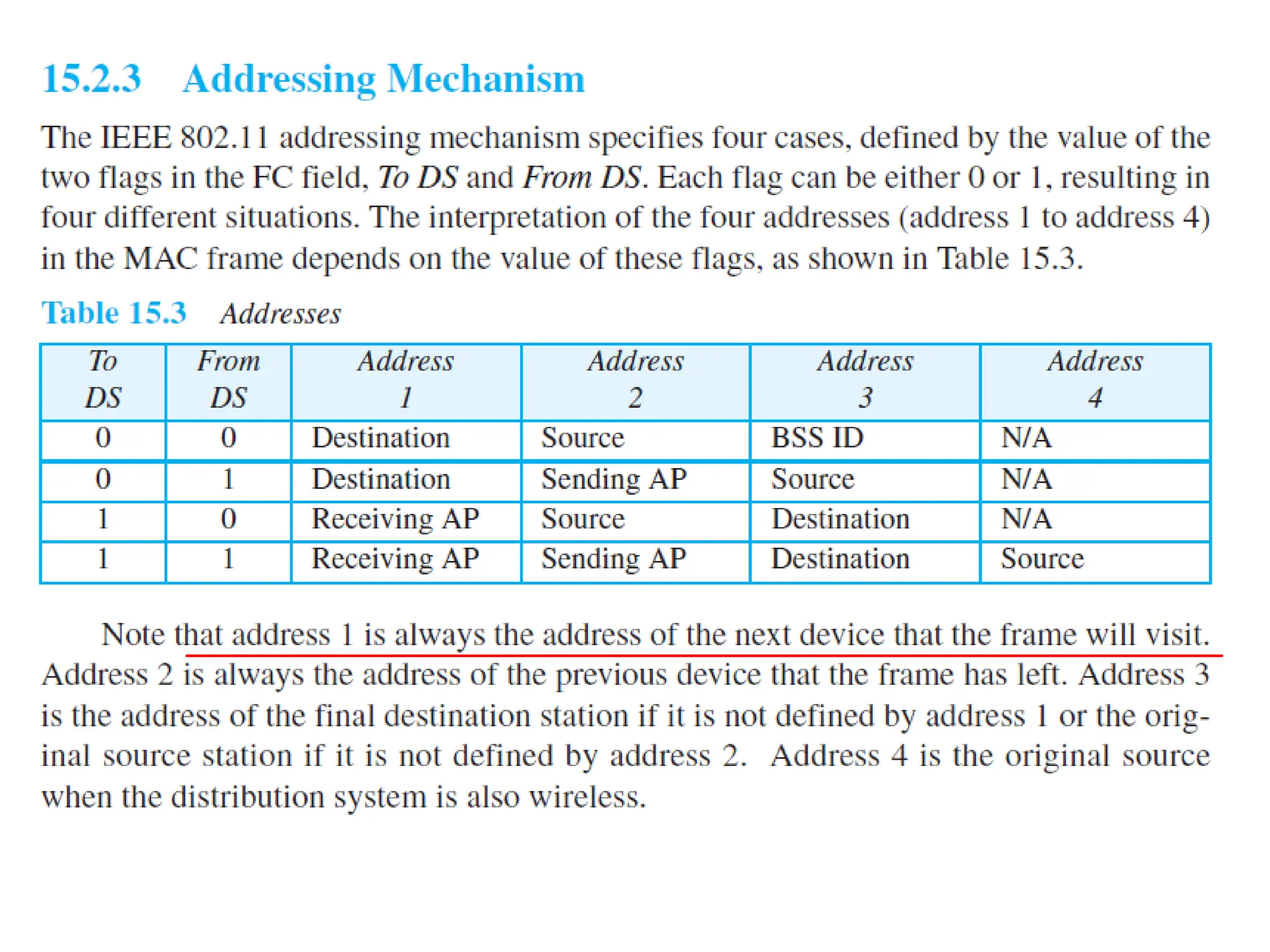
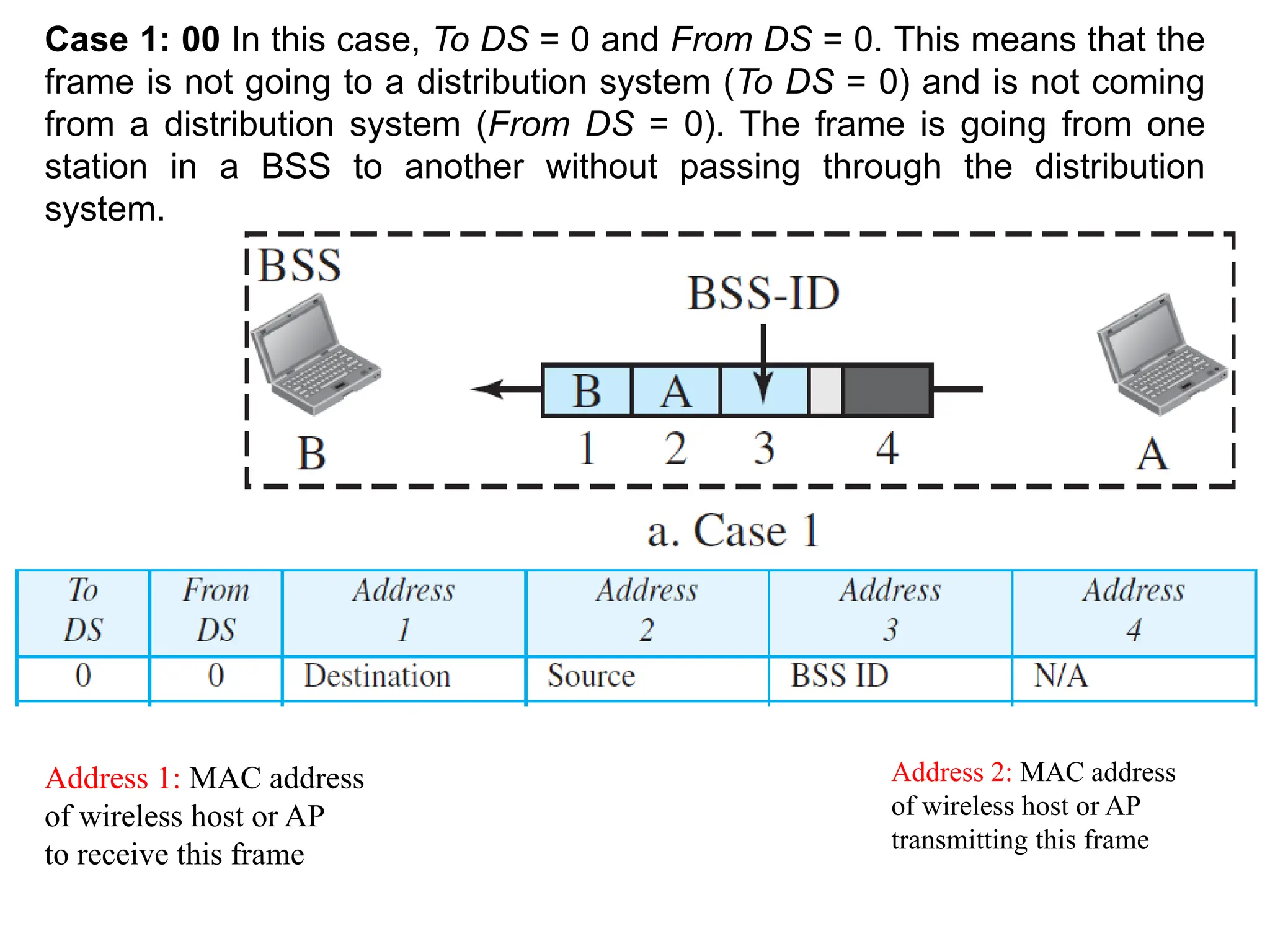
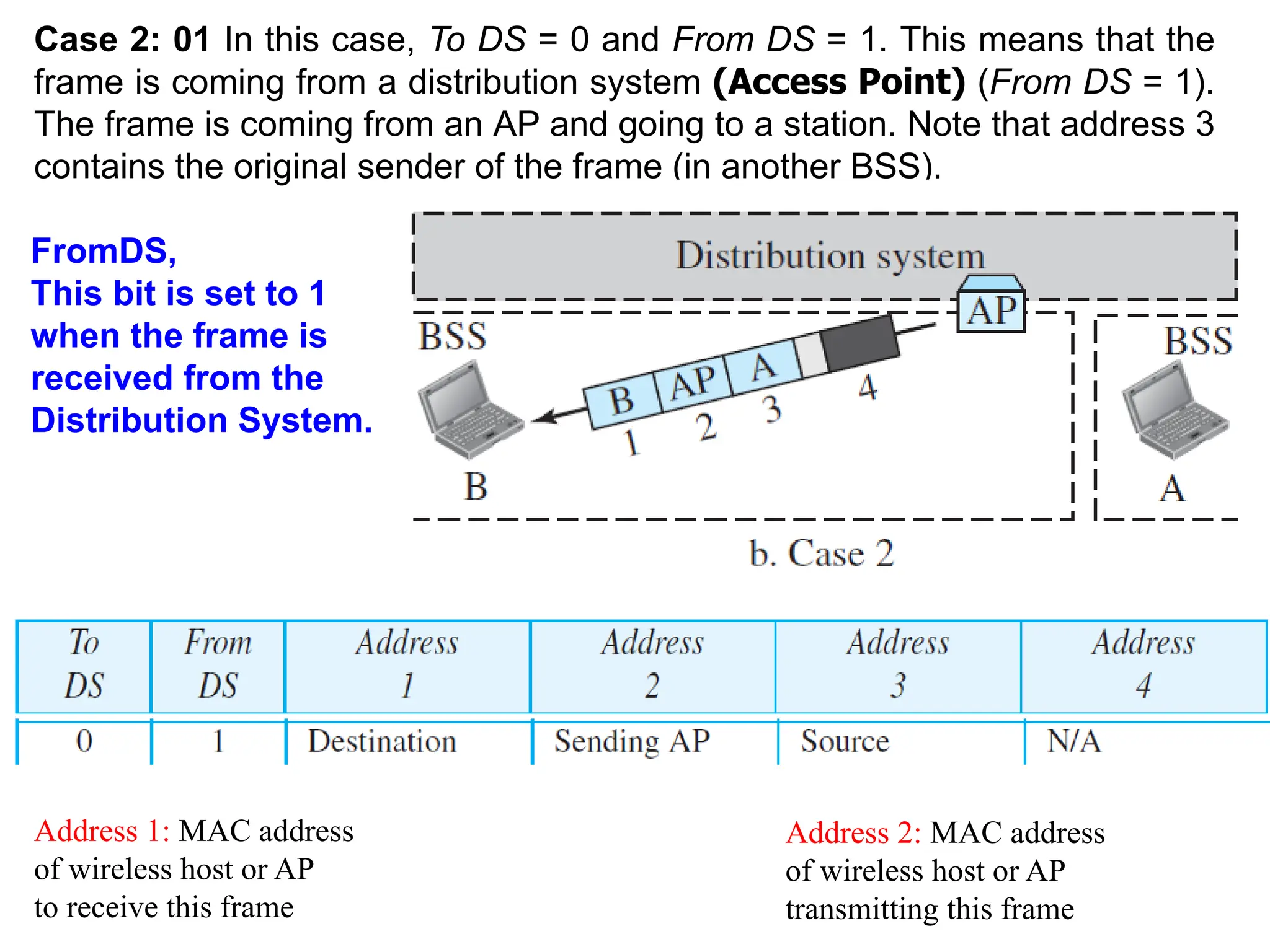
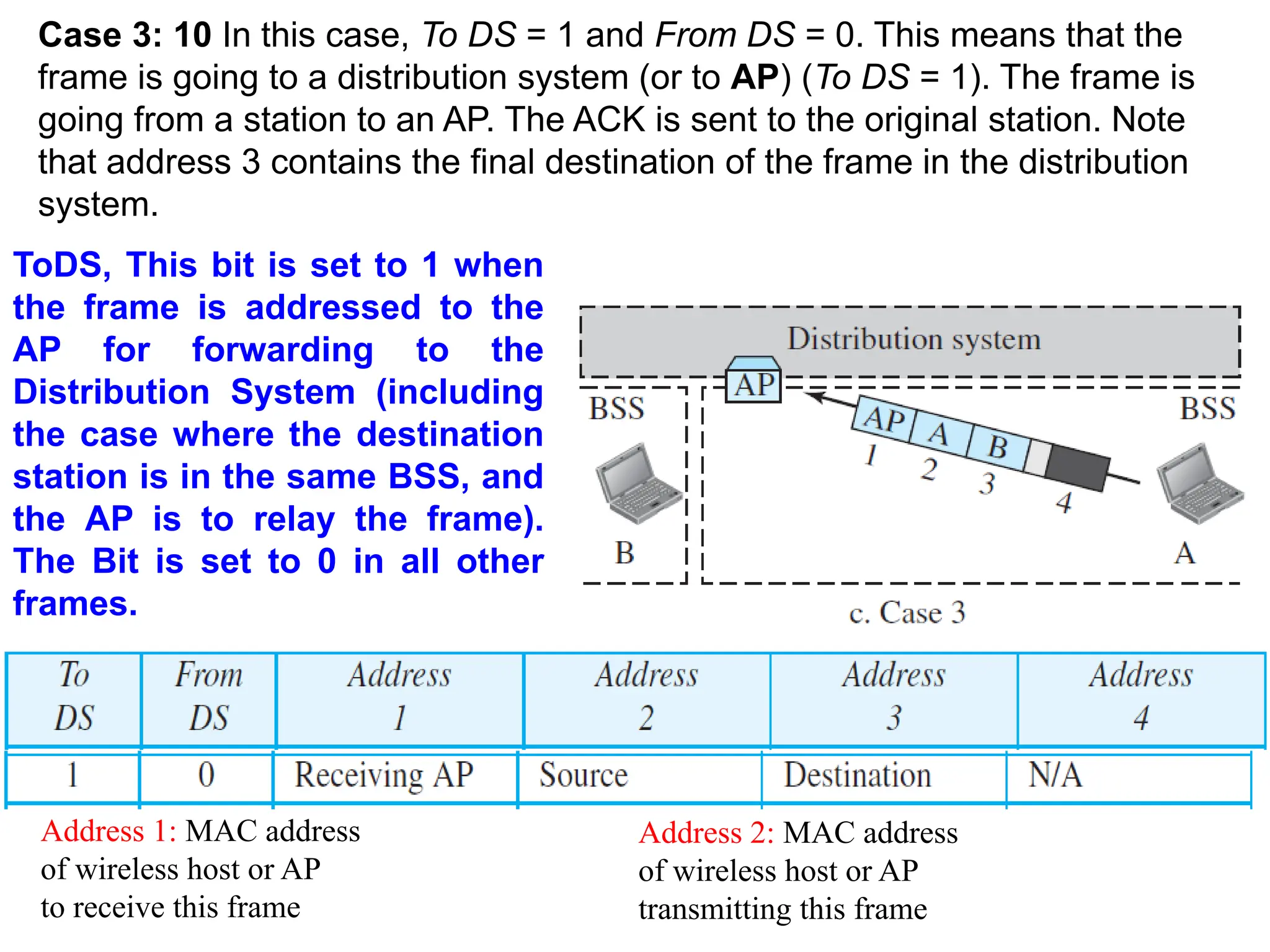
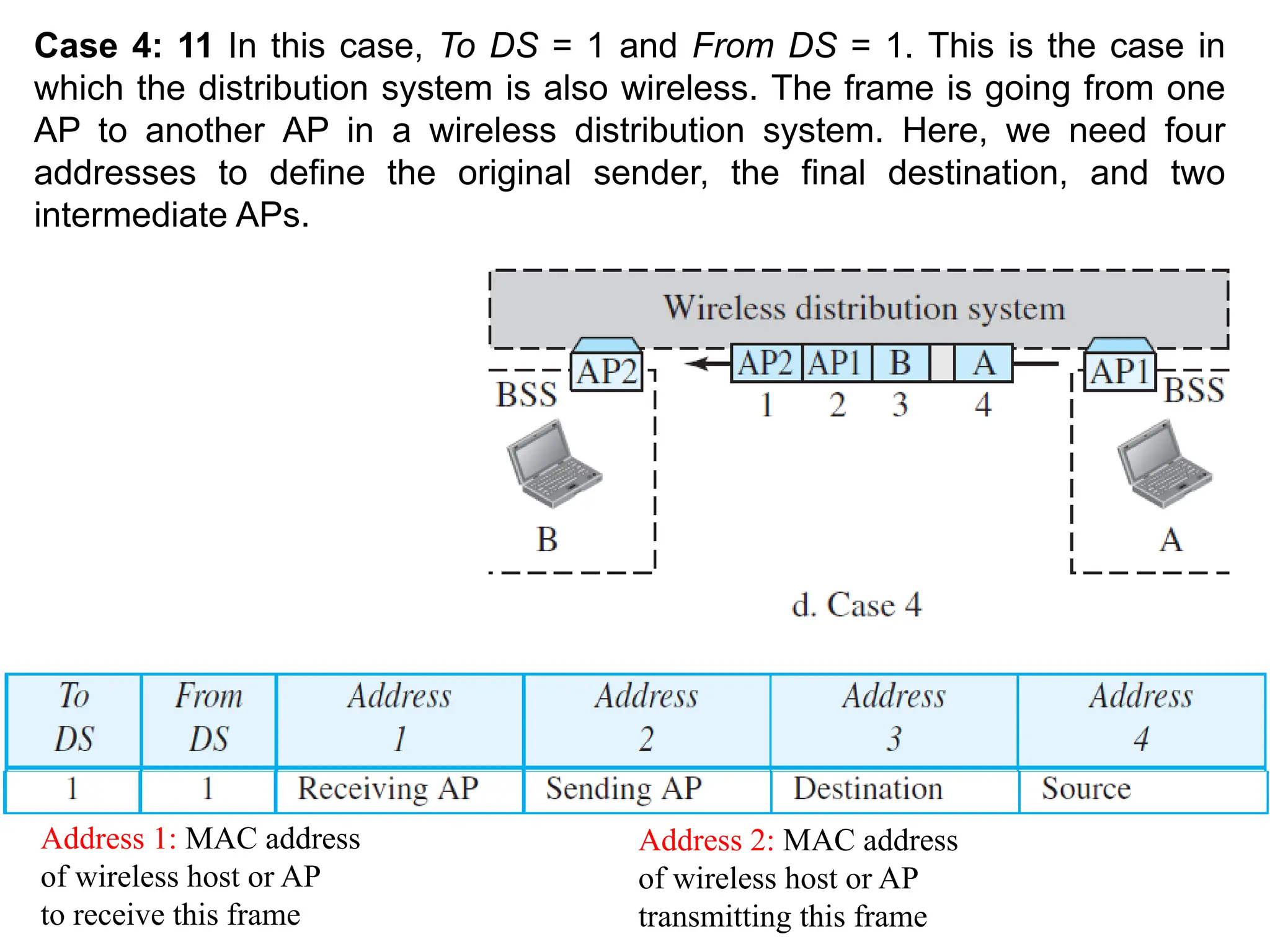
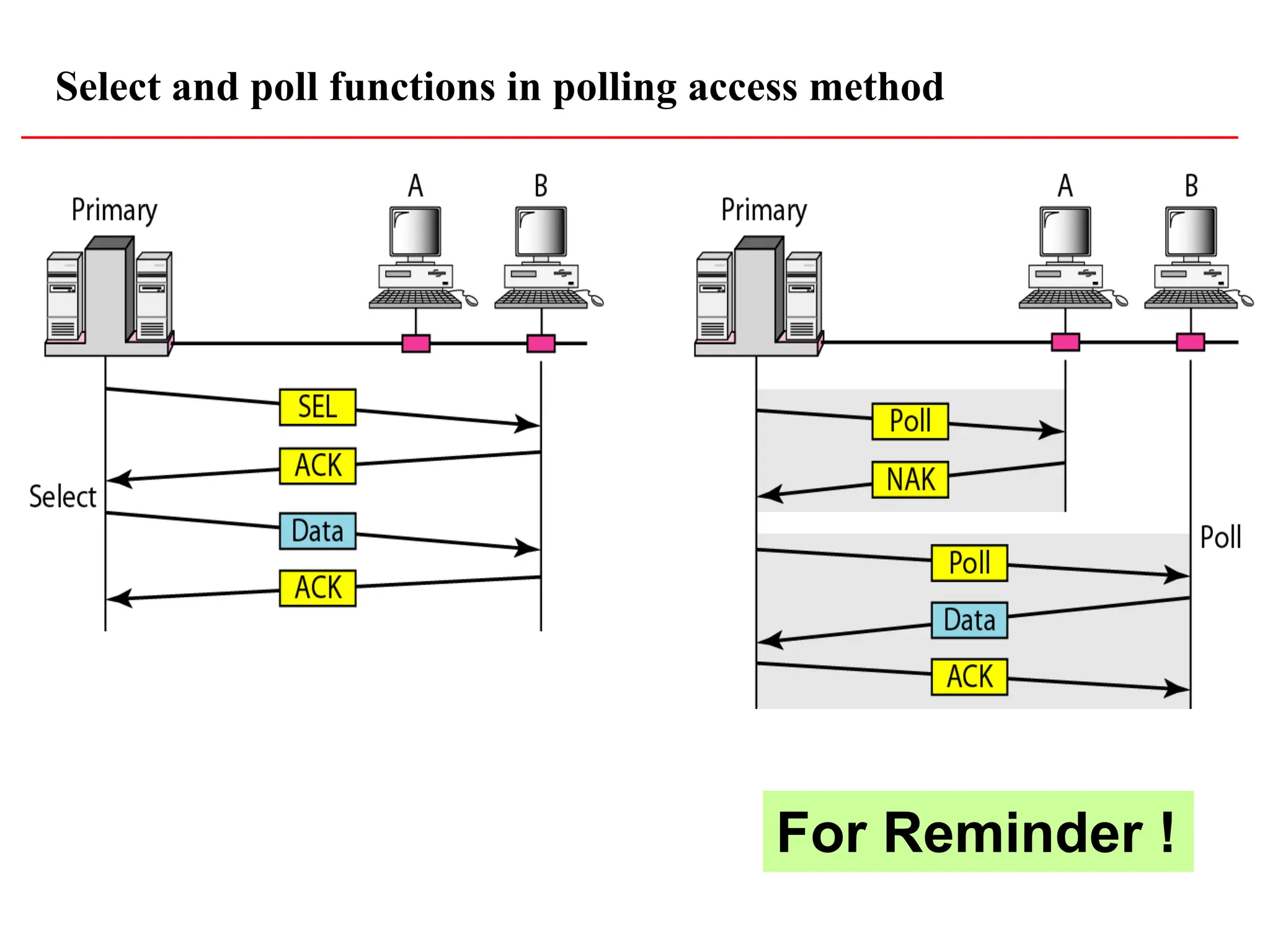
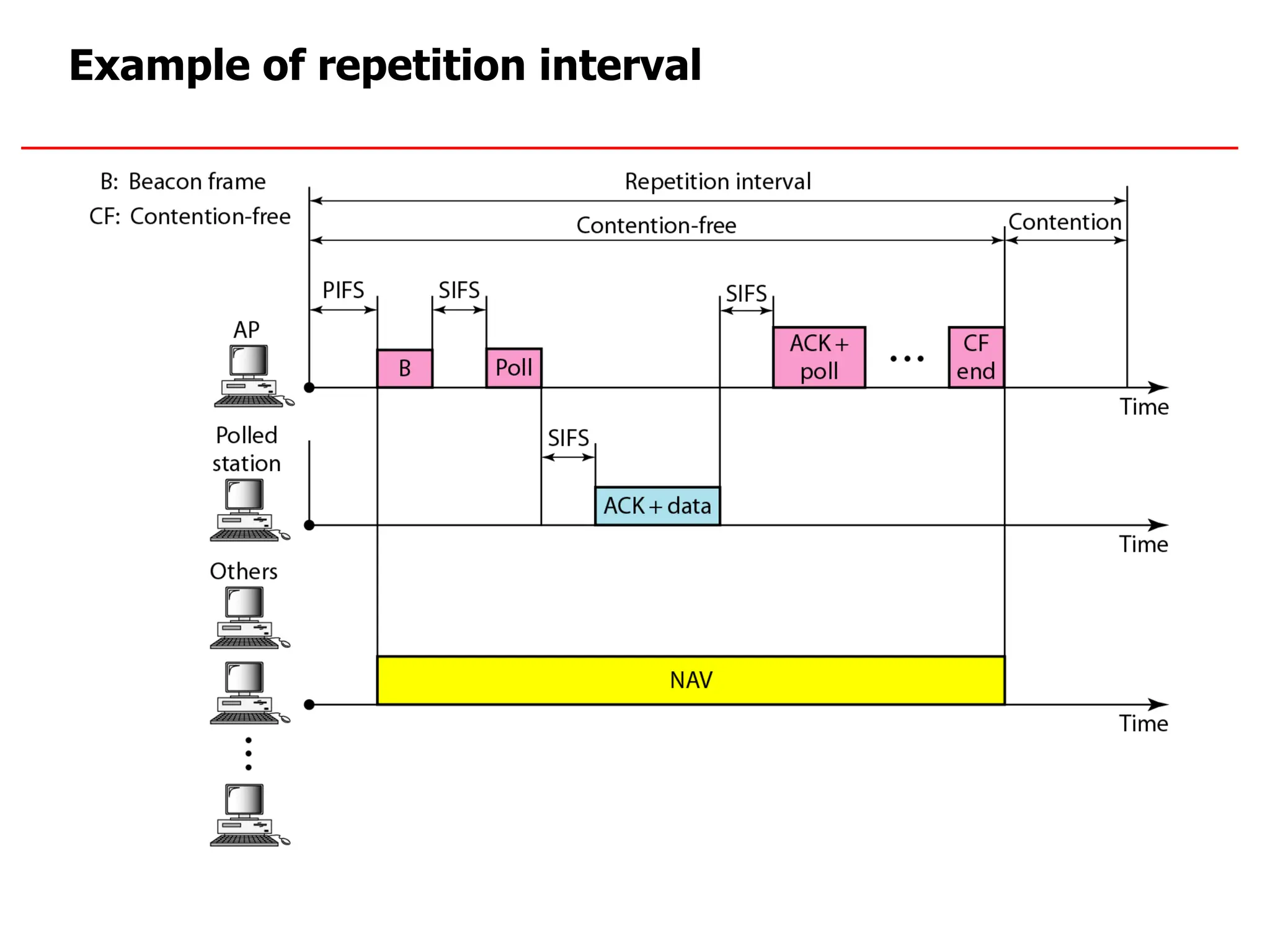
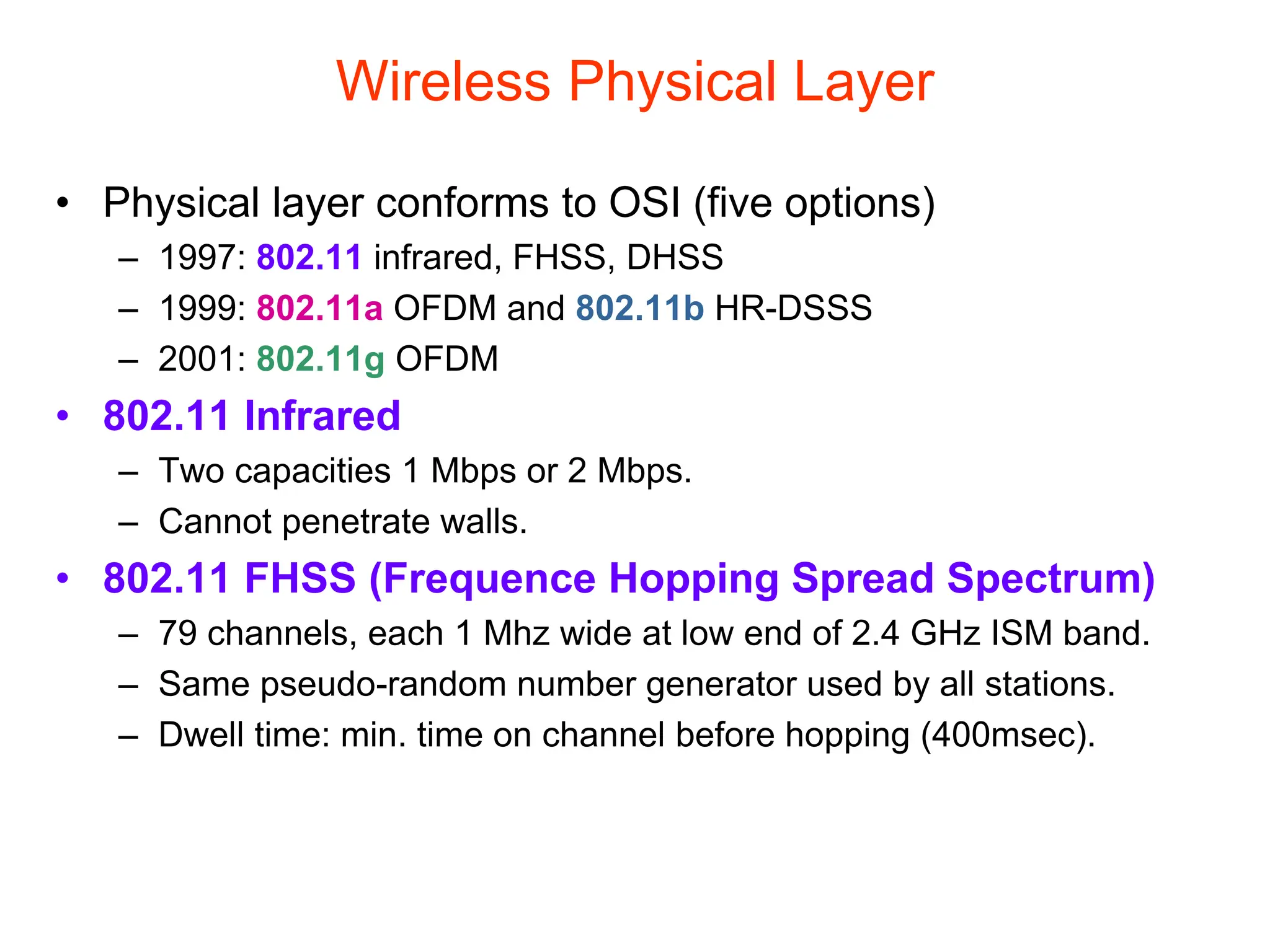
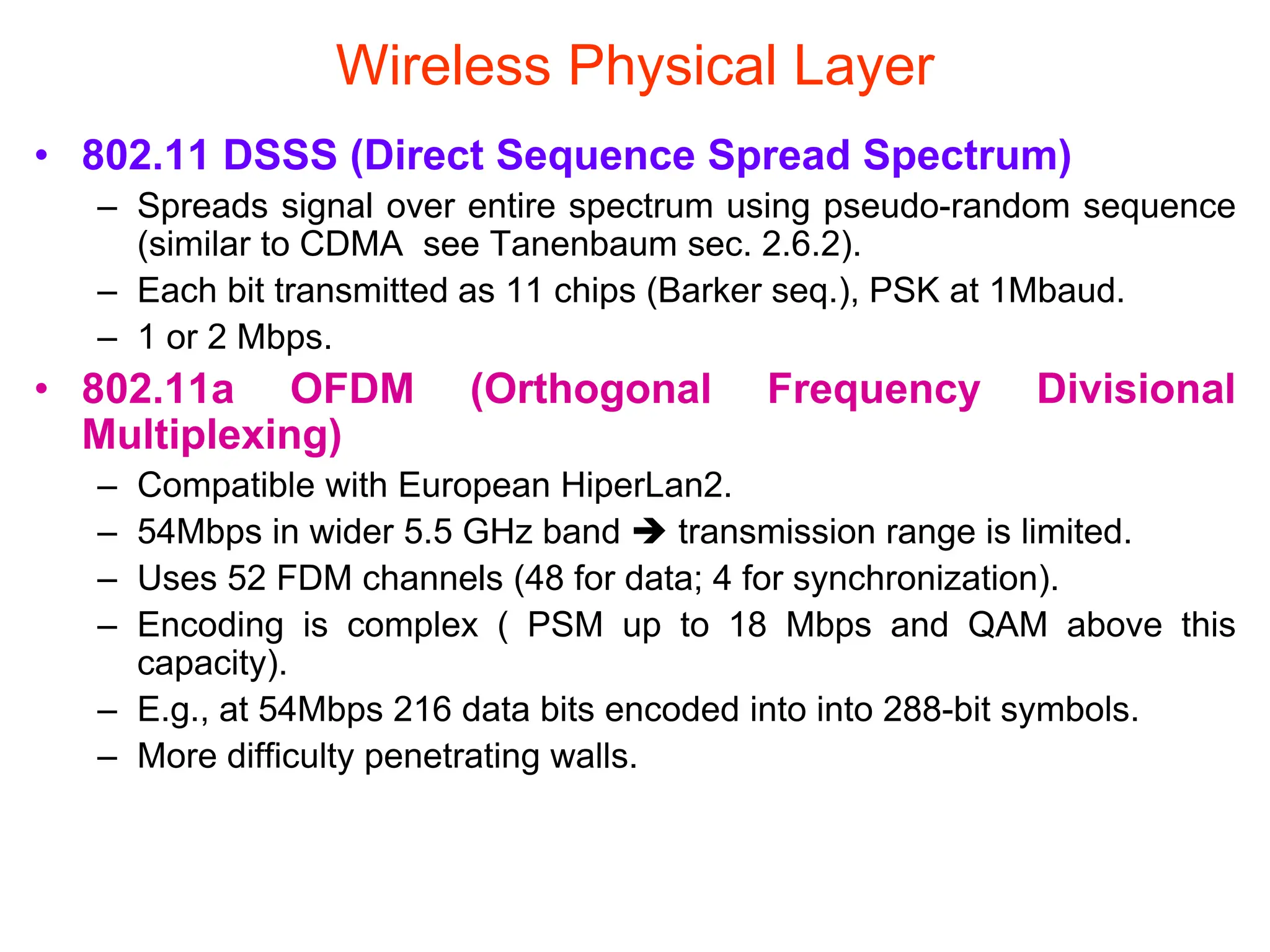
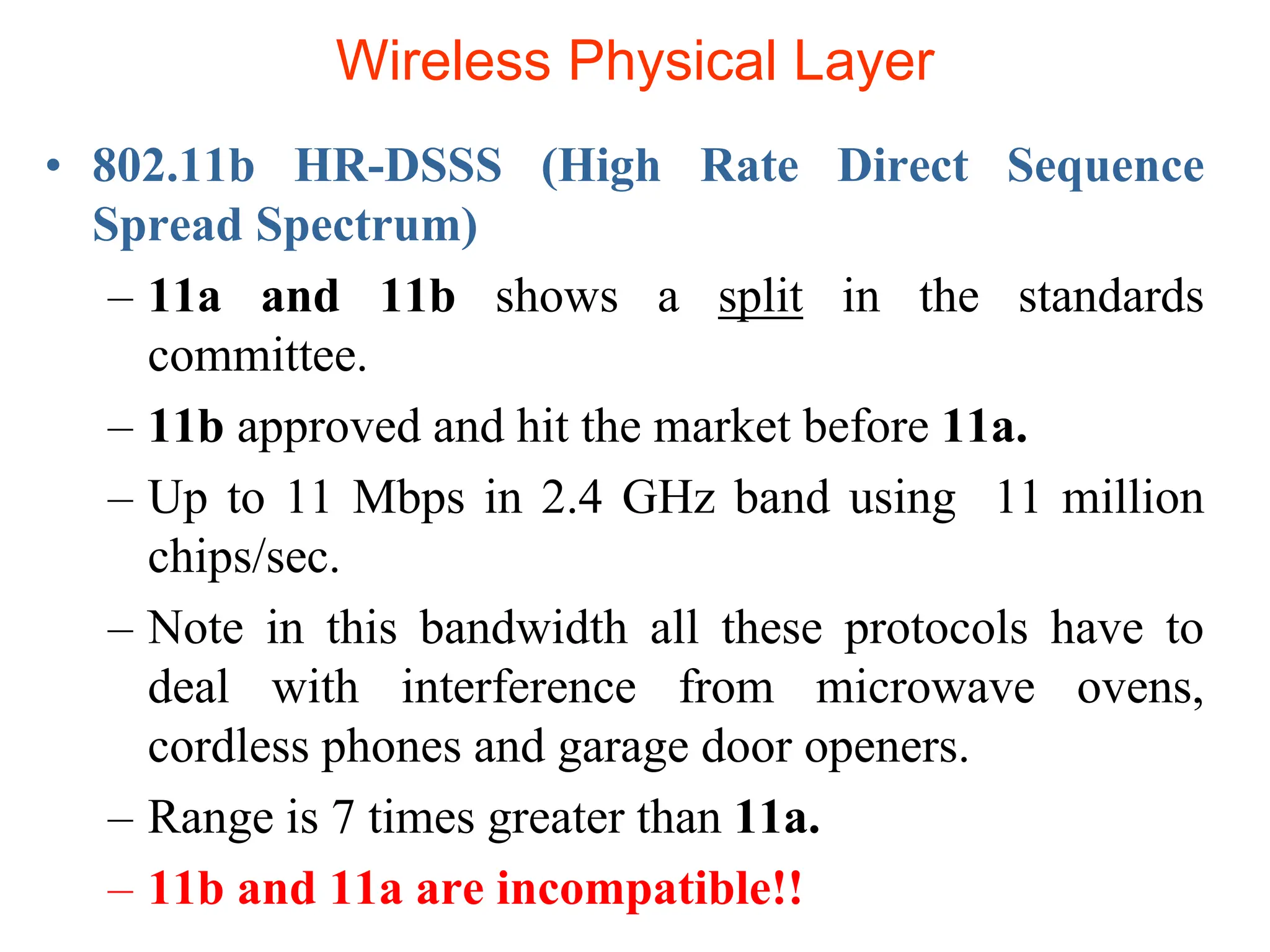
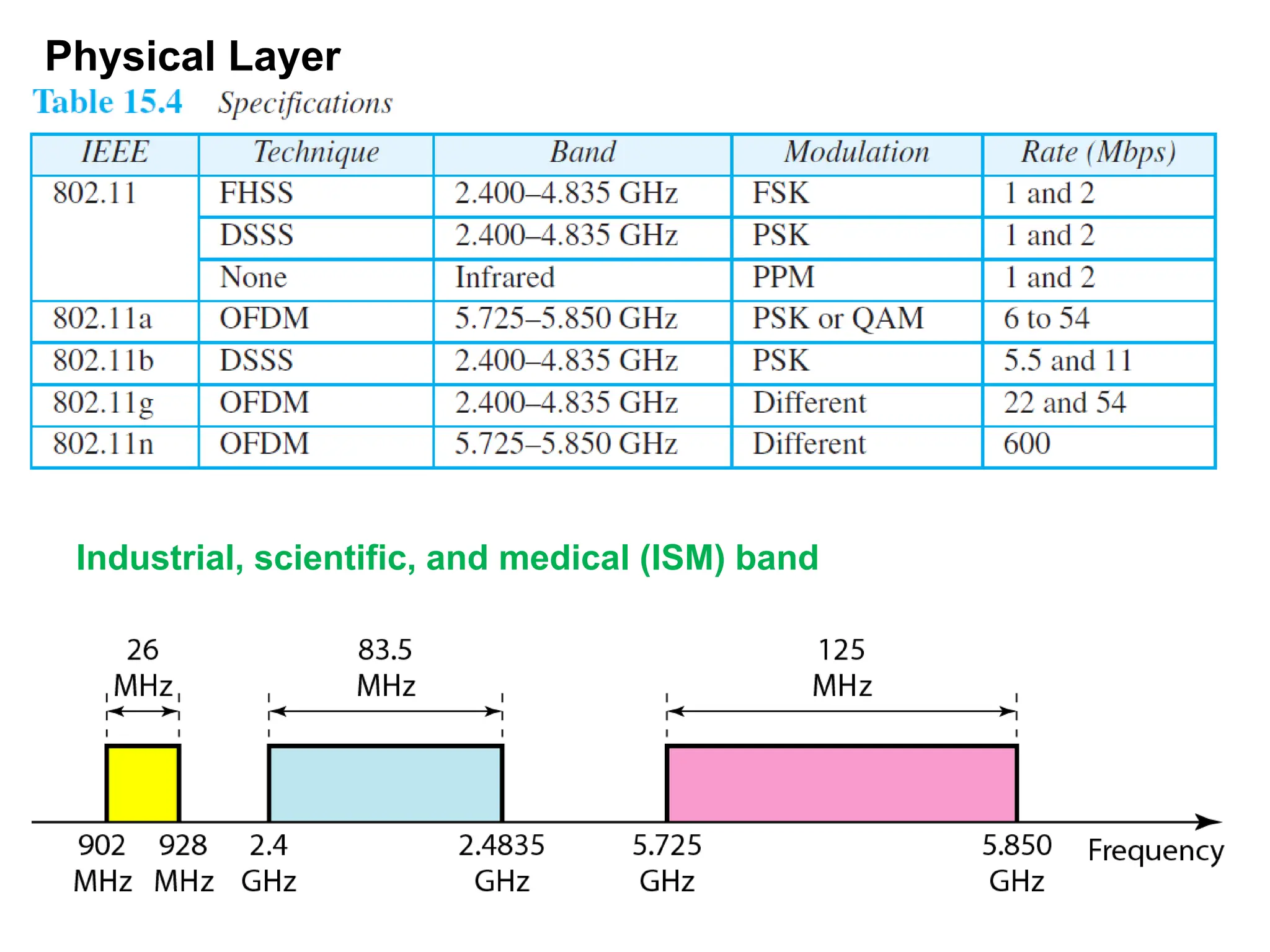
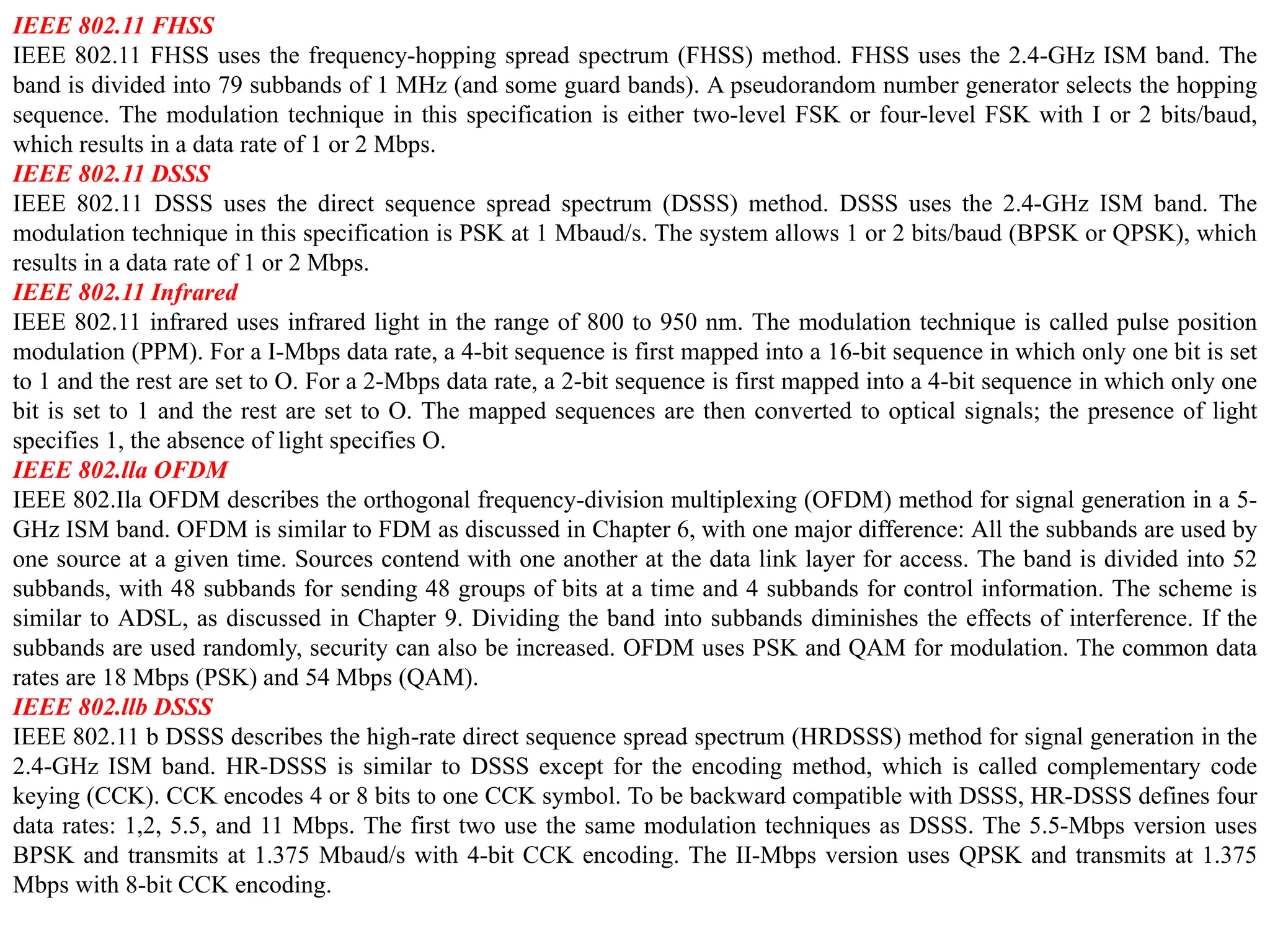
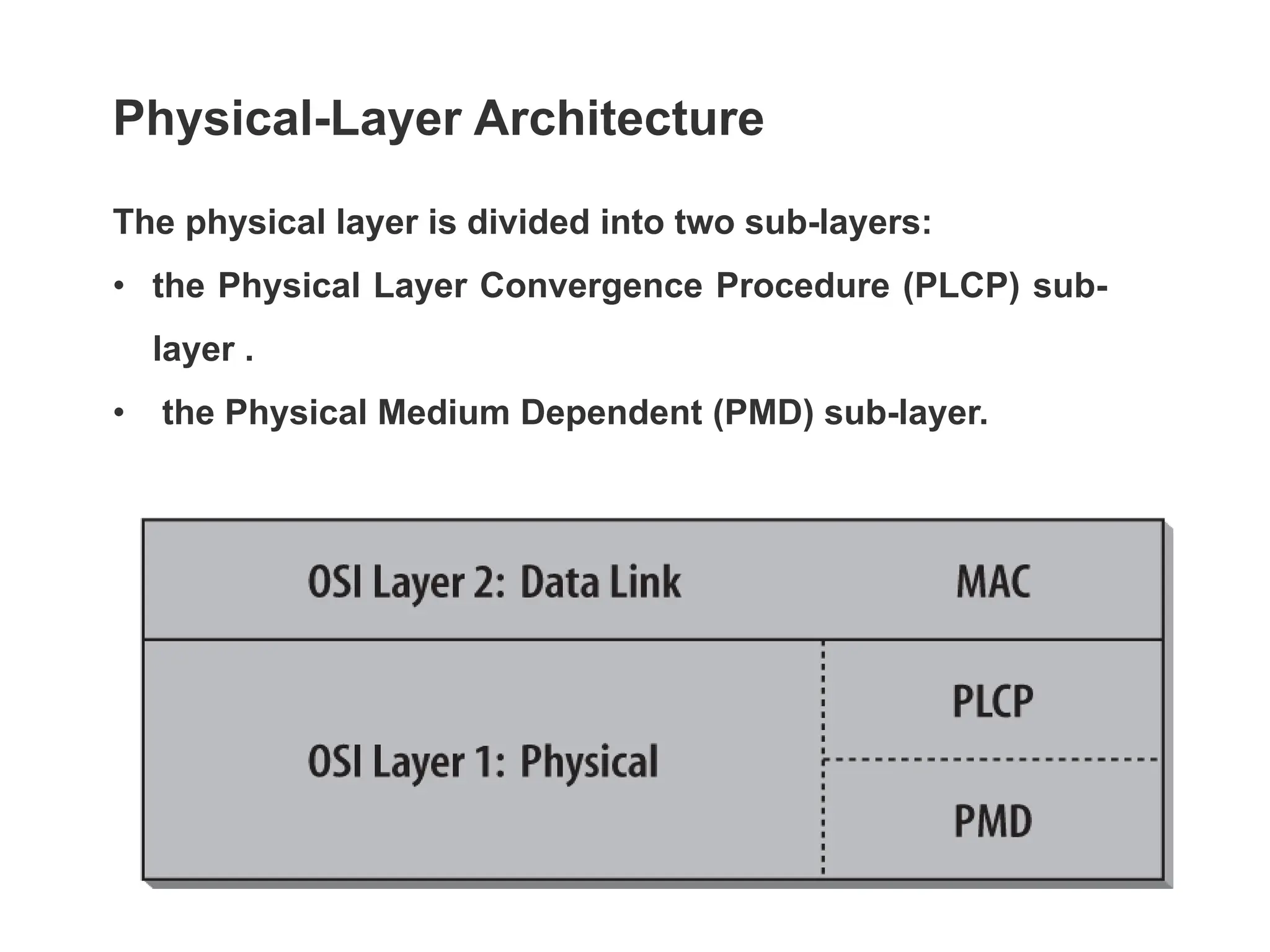
The document discusses the IEEE 802.11 standard for wireless local area networks (WLAN), detailing its architecture, various amendments, functionalities, and protocols such as distributed coordination function (DCF) and point coordination function (PCF). It explains the significance of access points, medium access methods, and collision avoidance protocols in WLAN communication. Additionally, it reviews key features including frequency bands, data rates, and the impact of interference and signal characteristics in wireless networking.