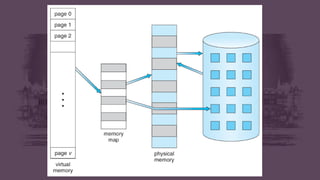
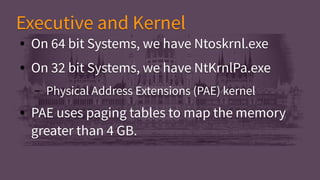
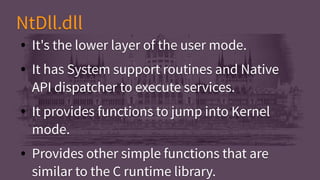
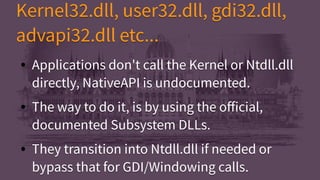
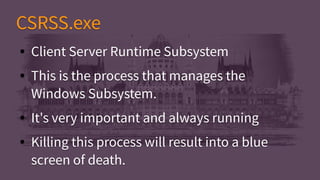
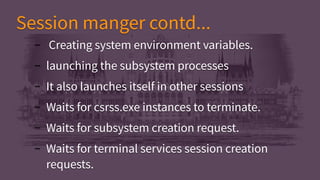
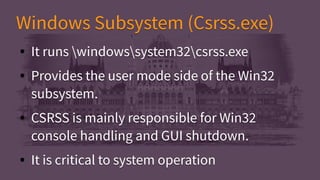
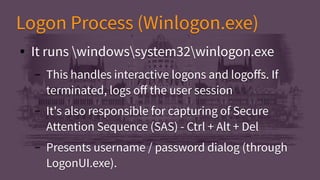
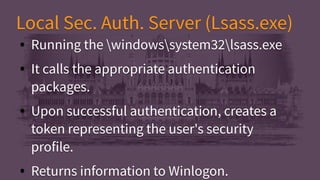
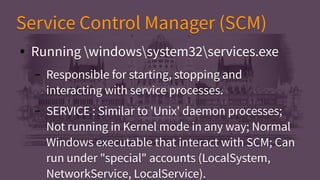
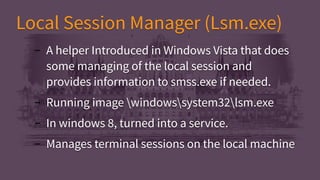
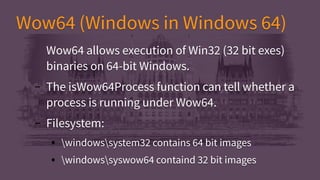
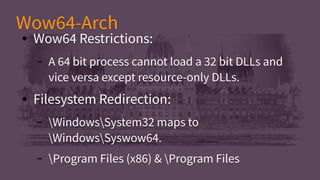
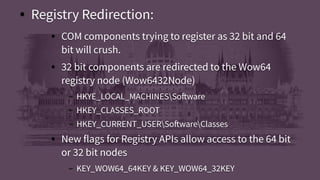
This document provides an introduction and overview of key concepts related to the Windows operating system internals. It discusses basic OS concepts, how Windows is implemented, and a simplified view of its inner workings. The document outlines user mode vs kernel mode, processes and threads, virtual memory, objects and handles, Windows design goals, core system files, the executive and kernel, and important system processes like CSRSS and Winlogon. It also covers symmetric multiprocessing, subsystems, and the Windows in Windows 64 (Wow64) subsystem that allows 32-bit apps to run on 64-bit Windows.