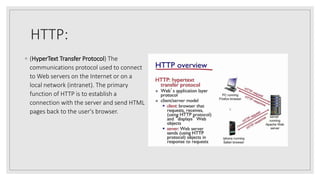
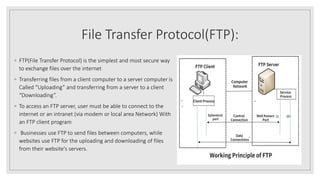
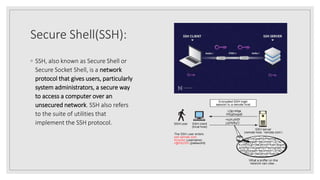
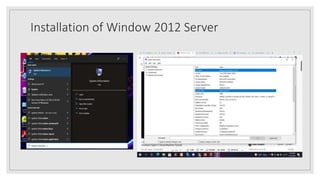
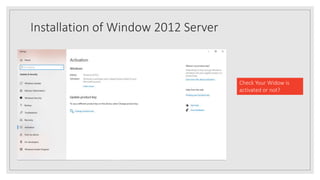
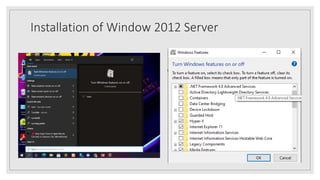
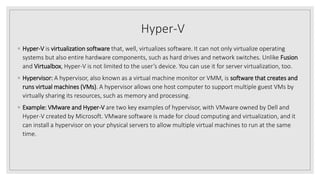
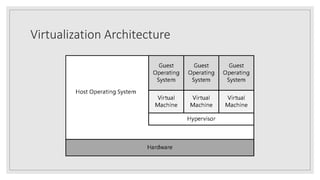
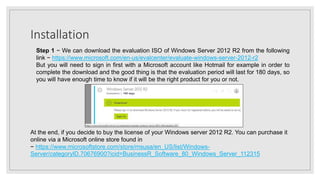
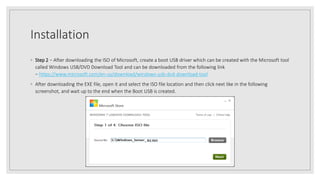
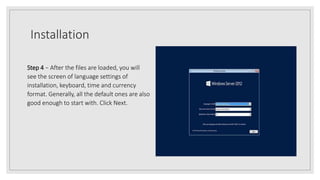
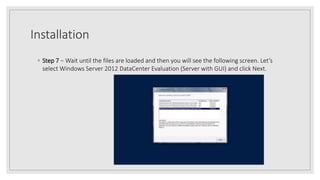
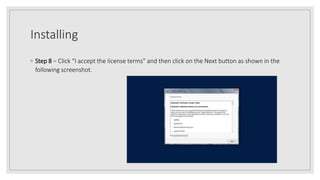
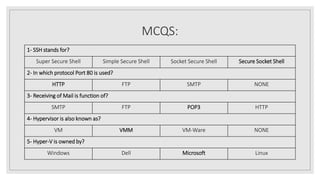
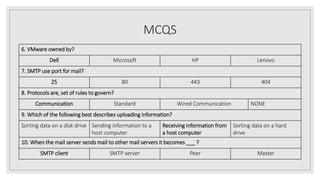
The document outlines key concepts related to Windows Server 2012, including network protocols such as HTTP, FTP, SSH, SMTP, and POP3, which are essential for data communication. It also details the installation process for Windows Server 2012, including system requirements and step-by-step instructions for creating a bootable USB and completing the installation. Additionally, it addresses virtual machines, hypervisors, and provides a series of questions and multiple-choice questions related to the content discussed.